Powerpoint Templates and Google slides for Cybersecurity Implementation
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Implementing cybersecurity management framework powerpoint presentation slides
Implementing cybersecurity management framework powerpoint presentation slidesSlideTeam brings Implementing Cybersecurity Management Framework Powerpoint Presentation Slides. There are 55 visually-gripping PowerPoint templates in this 100% editable deck. Customize font, text, patterns, shapes, colors, orientation, and background as required. Convert the PPT file format into PDF, PNG, and JPG according to your convenience. Use Google slides to view this presentation. It also works well with standard and widescreen resolutions.
-
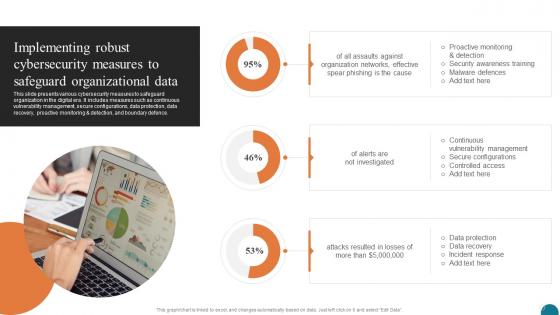 Implementing Robust Cybersecurity Elevating Small And Medium Enterprises Digital Transformation DT SS
Implementing Robust Cybersecurity Elevating Small And Medium Enterprises Digital Transformation DT SSThis slide presents various cybersecurity measures to safeguard organization in the digital era. It includes measures such as continuous vulnerability management, secure configurations, data protection, data recovery, proactive monitoring and detection, and boundary defence. Present the topic in a bit more detail with this Implementing Robust Cybersecurity Elevating Small And Medium Enterprises Digital Transformation DT SS. Use it as a tool for discussion and navigation on Organization Networks, Data Protection, Controlled Access. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
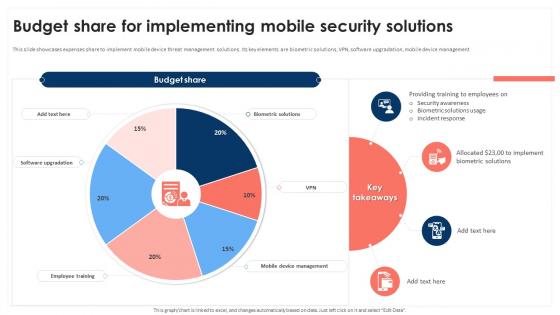 Budget Share For Implementing Mobile Security Solutions Mobile Device Security Cybersecurity SS
Budget Share For Implementing Mobile Security Solutions Mobile Device Security Cybersecurity SSBudget Share For Implementing Mobile Security Solutions Mobile Device Security Cybersecurity SS This slide showcases expenses share to implement mobile device threat management solutions. Its key elements are biometric solutions, VPN, software upgradation, mobile device management Present the topic in a bit more detail with this Biometric Solutions, Security Awareness Use it as a tool for discussion and navigation on Biometric Solutions, Security Awareness This template is free to edit as deemed fit for your organization. Therefore download it now.
-
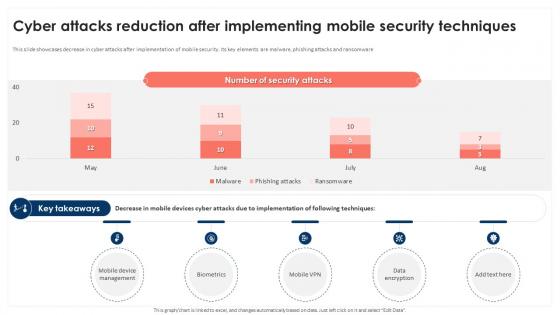 Cyber Attacks Reduction After Implementing Mobile Security Techniques Mobile Device Security Cybersecurity SS
Cyber Attacks Reduction After Implementing Mobile Security Techniques Mobile Device Security Cybersecurity SSThis slide showcases decrease in cyber attacks after implementation of mobile security. Its key elements are malware, phishing attacks and ransomware Deliver an outstanding presentation on the topic using this Cyber Attacks Reduction After Implementing Mobile Security Techniques Mobile Device Security Cybersecurity SS Dispense information and present a thorough explanation of Advanced Persistent Threats, Diverse Cyber Threat Landscape using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
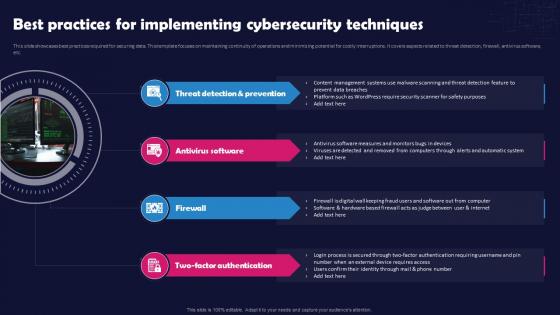 Unlocking The Impact Of Technology Best Practices For Implementing Cybersecurity Techniques
Unlocking The Impact Of Technology Best Practices For Implementing Cybersecurity TechniquesThis slide showcases best practices required for securing data. This template focuses on maintaining continuity of operations and minimizing potential for costly interruptions. It covers aspects related to threat detection, firewall, antivirus software, etc. Increase audience engagement and knowledge by dispensing information using Unlocking The Impact Of Technology Best Practices For Implementing Cybersecurity Techniques. This template helps you present information on four stages. You can also present information on Threat Detection And Prevention, Antivirus Software, Two Factor Authentication, Cybersecurity Techniques using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
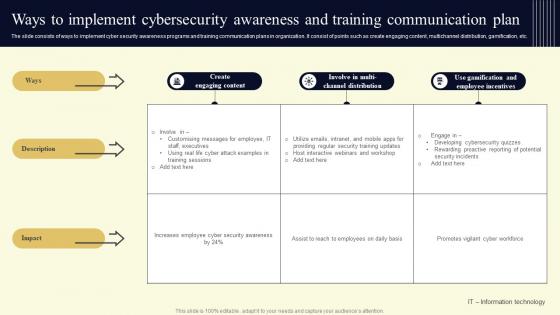 Ways To Implement Cybersecurity Awareness And Training Communication Plan
Ways To Implement Cybersecurity Awareness And Training Communication PlanThe slide consists of ways to implement cyber security awareness programs and training communication plans in organization. It consist of points such as create engaging content, multichannel distribution, gamification, etc. Presenting our well structured Ways To Implement Cybersecurity Awareness And Training Communication Plan. The topics discussed in this slide are Impact, Engaging, Distribution. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Need To Implement IoT Cyber Security Improving IoT Device Cybersecurity IoT SS
Need To Implement IoT Cyber Security Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to exhibit need to implement Internet of Things IoT security in order to avoid cyber attack and minimize losses. The slide covers information about data protection of users, adhering to regulatory standards, limited security of IoT devices, etc. Introducing Need To Implement IoT Cyber Security Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Required, Companies, Potential, using this template. Grab it now to reap its full benefits.
-
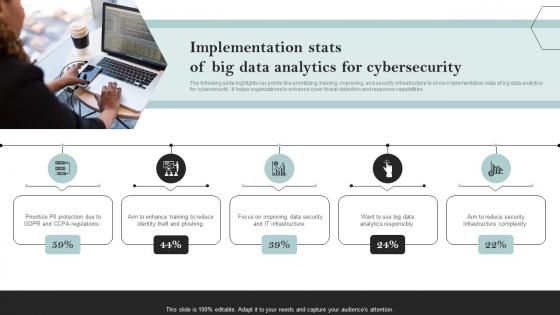 Implementation Stats Of Big Data Analytics For Cybersecurity
Implementation Stats Of Big Data Analytics For CybersecurityThe following slide highlights key points like prioritizing, training, improving, and security infrastructure to show implementation stats of big data analytics for cybersecurity. It helps organizations to enhance cyber threat detection and response capabilities. Introducing our premium set of slides with Implementation Stats Of Big Data Analytics For Cybersecurity. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Regulations, Reduce, Improving. So download instantly and tailor it with your information.
-
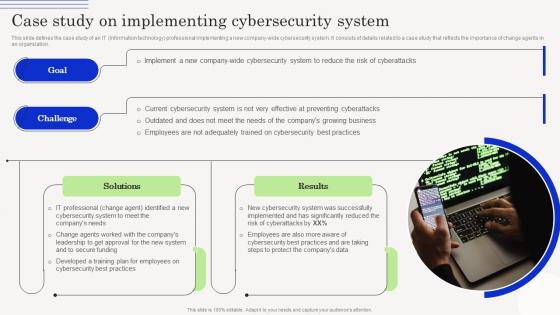 Change Management Agents Driving Case Study On Implementing Cybersecurity System CM SS
Change Management Agents Driving Case Study On Implementing Cybersecurity System CM SSThis slide defines the case study of an IT Information technology professional implementing a new company-wide cybersecurity system. It consists of details related to a case study that reflects the importance of change agents in an organization. Introducing Change Management Agents Driving Case Study On Implementing Cybersecurity System CM SS to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Preventing Cyberattacks, Risk Of Cyberattacks, Cybersecurity System, Adequately Trained, using this template. Grab it now to reap its full benefits.
-
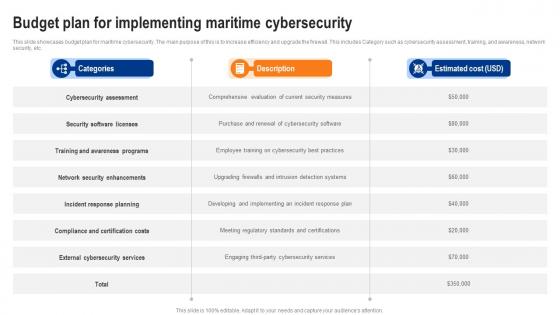 Budget Plan For Implementing Maritime Cybersecurity
Budget Plan For Implementing Maritime CybersecurityThis slide showcases budget plan for maritime cybersecurity. The main purpose of this is to increase efficiency and upgrade the firewall. This includes Category such as cybersecurity assessment, training, and awareness, network security, etc. Introducing our Budget Plan For Implementing Maritime Cybersecurity set of slides. The topics discussed in these slides are Cybersecurity Assessment, Security Software Licenses, Incident Response Planning. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
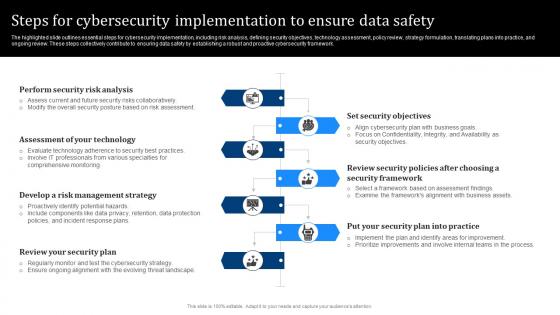 Steps For Cybersecurity Implementation To Ensure Data Safety
Steps For Cybersecurity Implementation To Ensure Data SafetyThe highlighted slide outlines essential steps for cybersecurity implementation, including risk analysis, defining security objectives, technology assessment, policy review, strategy formulation, translating plans into practice, and ongoing review. These steps collectively contribute to ensuring data safety by establishing a robust and proactive cybersecurity framework. Presenting our set of slides with Steps For Cybersecurity Implementation To Ensure Data Safety. This exhibits information on seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Risk Analysis, Management Strategy, Set Security Objectives.
-
 Select Cybersecurity Training Program Courses Implementing Strategies To Mitigate Cyber Security Threats
Select Cybersecurity Training Program Courses Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases the best cybersecurity training courses to educate employees and minimize the possibility of cyber attacks. It includes cloud, disaster recovery, hardware, information security programs, duration, mode and cost Deliver an outstanding presentation on the topic using this Select Cybersecurity Training Program Courses Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Cloud Security, Information Security, Disaster Recovery using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
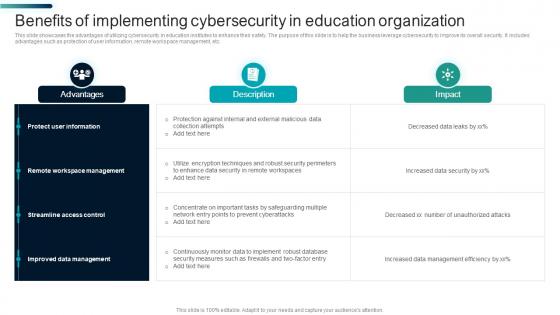 Benefits Of Implementing Cybersecurity In Education Organization
Benefits Of Implementing Cybersecurity In Education OrganizationThis slide showcases the advantages of utilizing cybersecurity in education institutes to enhance their safety. The purpose of this slide is to help the business leverage cybersecurity to improve its overall security. It includes advantages such as protection of user information, remote workspace management, etc. Introducing our Benefits Of Implementing Cybersecurity In Education Organization set of slides. The topics discussed in these slides are Protect User Information, Remote Workspace Management, Streamline Access Control. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
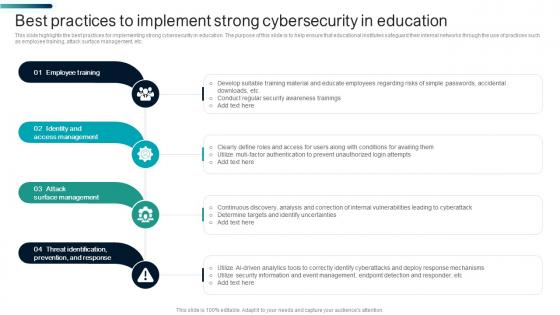 Best Practices To Implement Strong Cybersecurity In Education
Best Practices To Implement Strong Cybersecurity In EducationThis slide highlights the best practices for implementing strong cybersecurity in education. The purpose of this slide is to help ensure that educational institutes safeguard their internal networks through the use of practices such as employee training, attack surface management, etc. Introducing our premium set of slides with Best Practices To Implement Strong Cybersecurity In Education. Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Employee Training, Identity And Access Management, Attack Surface Management. So download instantly and tailor it with your
-
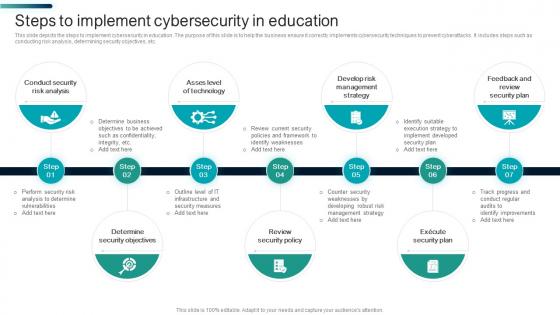 Steps To Implement Cybersecurity In Education
Steps To Implement Cybersecurity In EducationThis slide depicts the steps to implement cybersecurity in education. The purpose of this slide is to help the business ensure it correctly implements cybersecurity techniques to prevent cyberattacks. It includes steps such as conducting risk analysis, determining security objectives, etc. Presenting our set of slides with Steps To Implement Cybersecurity In Education. This exhibits information on Seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Execute Security Plan, Review Security Policy, Review Security Plan
-
 Strategies To Implement Cybersecurity In Education
Strategies To Implement Cybersecurity In EducationThis slide showcases the strategies to implement cybersecurity in education. The purpose of this slide is to help the business manage and ensure cybersecurity is correctly established in an educational institute. It includes strategies such as conducting audits, immediate response to cyber attacks, etc. Introducing our premium set of slides with Strategies To Implement Cybersecurity In Education. Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Rules And Regulations, Technical Control Methods, Cyber Attacks. So download instantly and tailor it with your information.
-
 IoT Device Identity Platform Implementation Internet Of Things IoT Security Cybersecurity SS
IoT Device Identity Platform Implementation Internet Of Things IoT Security Cybersecurity SSThis slide showcases internet of things IoT device identity platform deployment, referable for businesses in developing mitigation process. It provides details about APIs, architecture, device client, etc. Deliver an outstanding presentation on the topic using this IoT Device Identity Platform Implementation Internet Of Things IoT Security Cybersecurity SS. Dispense information and present a thorough explanation of IoT Device, Platform Deployment, Developing Mitigation Process using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
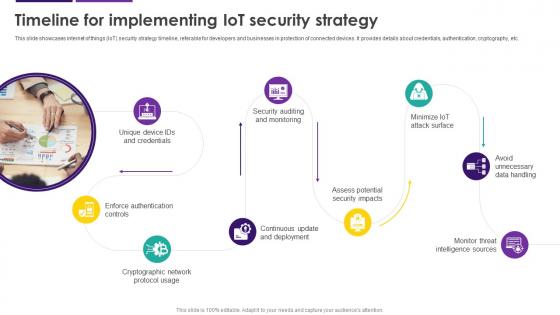 Timeline For Implementing IoT Security Strategy Internet Of Things IoT Security Cybersecurity SS
Timeline For Implementing IoT Security Strategy Internet Of Things IoT Security Cybersecurity SSThis slide showcases internet of things IoT security strategy timeline, referable for developers and businesses in protection of connected devices. It provides details about credentials, authentication, cryptography, etc. Introducing Timeline For Implementing IoT Security Strategy Internet Of Things IoT Security Cybersecurity SS to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Avoid Unnecessary Data Handling, Cryptographic Network Protocol Usage, Enforce Authentication Controls, using this template. Grab it now to reap its full benefits.
-
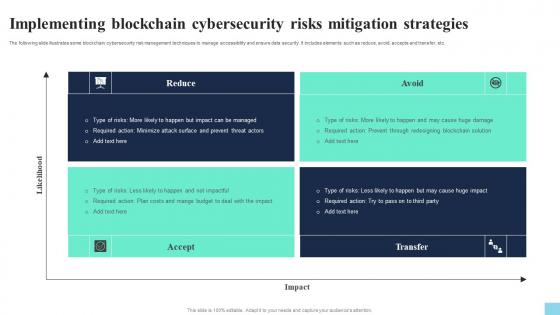 Implementing Blockchain Cybersecurity Risks Mitigation Hands On Blockchain Security Risk BCT SS V
Implementing Blockchain Cybersecurity Risks Mitigation Hands On Blockchain Security Risk BCT SS VThe following slide illustrates some blockchain cybersecurity risk management techniques to manage accessibility and ensure data security. It includes elements such as reduce, avoid, accepts and transfer, etc. Present the topic in a bit more detail with this Implementing Blockchain Cybersecurity Risks Mitigation Hands On Blockchain Security Risk BCT SS V. Use it as a tool for discussion and navigation on Reduce, Accept, Avoid. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Implementing Blockchain Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS V
Implementing Blockchain Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases blockchain cybersecurity threat assessment to determine type and major causes of attacks. It includes elements such as double spending, mining threats, wallet, network, smart contract threats, etc. Introducing Implementing Blockchain Cybersecurity Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Reduce, Accept, Transfer, using this template. Grab it now to reap its full benefits.
-
 Implementing Blockchain Cybersecurity Risks Mitigation Strategies Guide For Blockchain BCT SS V
Implementing Blockchain Cybersecurity Risks Mitigation Strategies Guide For Blockchain BCT SS VThe following slide illustrates some blockchain cybersecurity risk management techniques to manage accessibility and ensure data security. It includes elements such as reduce, avoid, accepts and transfer, etc. Increase audience engagement and knowledge by dispensing information using Implementing Blockchain Cybersecurity Risks Mitigation Strategies Guide For Blockchain BCT SS V This template helps you present information on four stages. You can also present information on Reduce, Avoid, Transfer, Accept using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
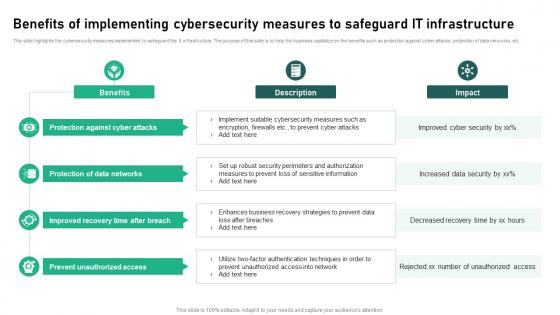 Benefits Of Implementing Cybersecurity Measures To Safeguard It Infrastructure
Benefits Of Implementing Cybersecurity Measures To Safeguard It InfrastructureThis slide highlights the cybersecurity measures implemented to safeguard the It infrastructure. The purpose of this slide is to help the business capitalize on the benefits such as protection against cyber attacks, protection of data networks, etc. Presenting our set of slides with Benefits Of Implementing Cybersecurity Measures To Safeguard It Infrastructure This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Protection Against, Data Networks, Unauthorized Access
-
 Checklist To Implement Opsec Cybersecurity In Organization
Checklist To Implement Opsec Cybersecurity In OrganizationThis slide showcases the checklist to implement opsec cybersecurity in organizations. The purpose of this slide is to help ensure opsec measures are correctly implemented through the use of this checklist. It includes elements such as checklist item, description, etc. Introducing our Checklist To Implement Opsec Cybersecurity In Organization set of slides. The topics discussed in these slides are Information Classification, Access Controls, Communication Security. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
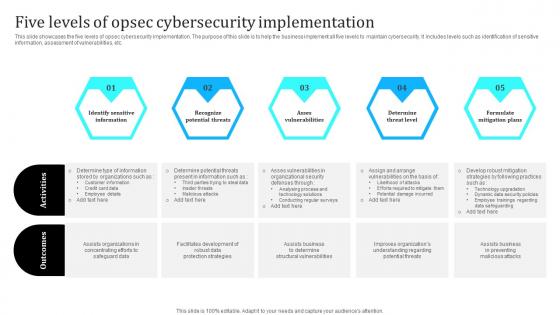 Five Levels Of Opsec Cybersecurity Implementation
Five Levels Of Opsec Cybersecurity ImplementationThis slide showcases the five levels of opsec cybersecurity implementation. The purpose of this slide is to help the business implement all five levels to maintain cybersecurity. It includes levels such as identification of sensitive information, assessment of vulnerabilities, etc. Introducing our premium set of slides with Five Levels Of Opsec Cybersecurity Implementation. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identify Sensitive Information, Recognize Potential Threats, Asses Vulnerabilities . So download instantly and tailor it with your information.
-
 Icon For Opsec Cybersecurity Implementation Steps
Icon For Opsec Cybersecurity Implementation StepsIntroducing our premium set of slides with Icon For Opsec Cybersecurity Implementation Steps. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Icon, Cybersecurity, Implementation. So download instantly and tailor it with your information.
-
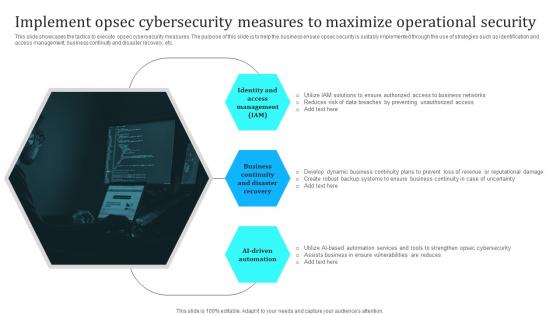 Implement Opsec Cybersecurity Measures To Maximize Operational Security
Implement Opsec Cybersecurity Measures To Maximize Operational SecurityThis slide showcases the tactics to execute opsec cybersecurity measures. The purpose of this slide is to help the business ensure opsec security is suitably implemented through the use of strategies such as identification and access management, business continuity and disaster recovery, etc Introducing our premium set of slides with Implement Opsec Cybersecurity Measures To Maximize Operational Security. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Access Management, Disaster Recovery, AI Driven Automation . So download instantly and tailor it with your information.
-
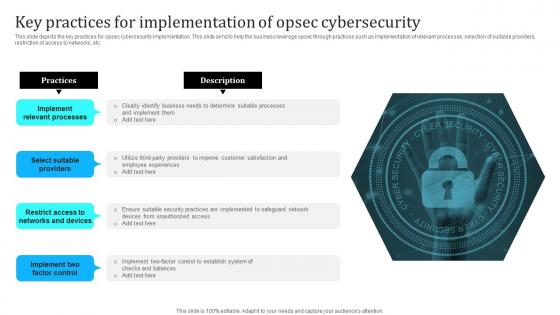 Key Practices For Implementation Of Opsec Cybersecurity
Key Practices For Implementation Of Opsec CybersecurityThis slide depicts the key practices for opsec cybersecurity implementation. This slide aims to help the business leverage opsec through practices such as implementation of relevant processes, selection of suitable providers, restriction of access to networks, etc. Introducing our premium set of slides with Key Practices For Implementation Of Opsec Cybersecurity. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Practices, Description, Networks And Devices. So download instantly and tailor it with your information.
-
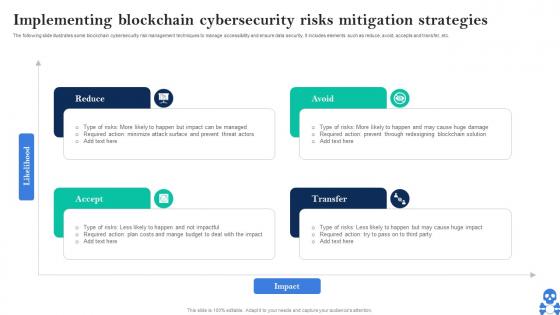 Cyber Threats In Blockchain Implementing Blockchain Cybersecurity Risks Mitigation Strategies BCT SS V
Cyber Threats In Blockchain Implementing Blockchain Cybersecurity Risks Mitigation Strategies BCT SS VThe following slide illustrates some blockchain cybersecurity risk management techniques to manage accessibility and ensure data security. It includes elements such as reduce, avoid, accepts and transfer, etc. Introducing Cyber Threats In Blockchain Implementing Blockchain Cybersecurity Risks Mitigation Strategies BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Reduce, Avoid, Transfer, Accept using this template. Grab it now to reap its full benefits.
-
 Select Cybersecurity Training Program Courses Implementing Cyber Risk Management Process
Select Cybersecurity Training Program Courses Implementing Cyber Risk Management ProcessThe following slide showcases the best cybersecurity training courses to educate employees and minimize the possibility of cyber-attacks. It includes cloud, disaster recovery, hardware, information security programs, duration, mode and cost. Present the topic in a bit more detail with this Select Cybersecurity Training Program Courses Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Course Name, Duration, Mode, Start Date. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
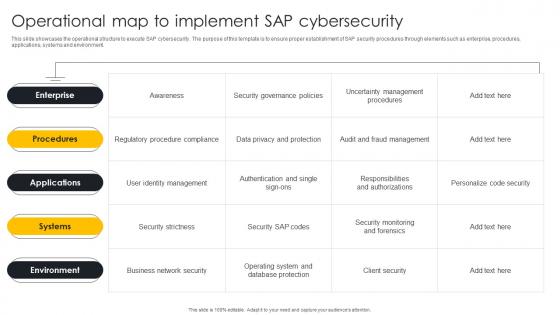 Operational Map To Implement SAP Cybersecurity
Operational Map To Implement SAP CybersecurityThis slide showcases the operational structure to execute SAP cybersecurity. The purpose of this template is to ensure proper establishment of SAP security procedures through elements such as enterprise, procedures, applications, systems and environment. Presenting our well structured Operational Map To Implement SAP Cybersecurity. The topics discussed in this slide are Security Governance Policies, Data Privacy And Protection, Client Security. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
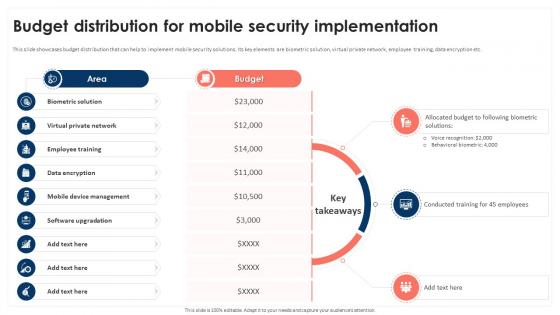 Budget Distribution For Mobile Security Implementation Mobile Device Security Cybersecurity SS
Budget Distribution For Mobile Security Implementation Mobile Device Security Cybersecurity SSThis slide showcases budget distribution that can help to implement mobile security solutions. Its key elements are biometric solution, virtual private network, employee training, data encryption etc. Introducing Budget Distribution For Mobile Security Implementation Mobile Device Security Cybersecurity SS to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Biometric Solution, Virtual Private Network, Employee Training using this template. Grab it now to reap its full benefits.
-
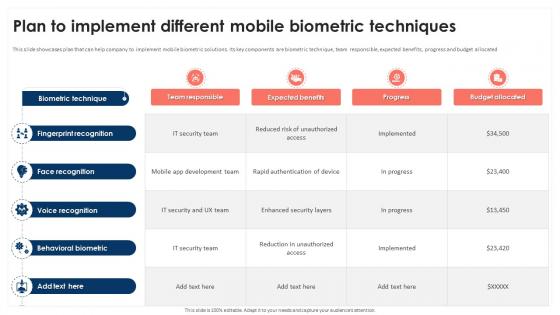 Plan To Implement Different Mobile Biometric Techniques Mobile Device Security Cybersecurity SS
Plan To Implement Different Mobile Biometric Techniques Mobile Device Security Cybersecurity SSThis slide showcases plan that can help company to implement mobile biometric solutions. Its key components are biometric technique, team responsible, expected benefits, progress and budget allocated. Deliver an outstanding presentation on the topic using this Plan To Implement Different Mobile Biometric Techniques Mobile Device Security Cybersecurity SS Dispense information and present a thorough explanation of Policy Development, Choose Solution, Train Users using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
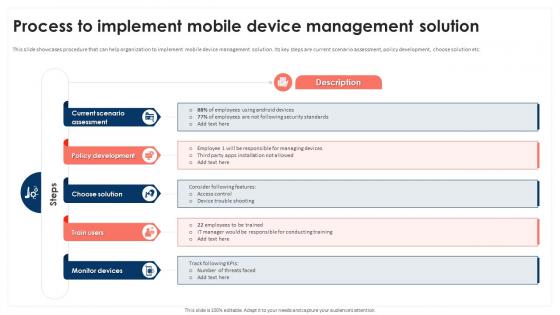 Process To Implement Mobile Device Management Mobile Device Security Cybersecurity SS
Process To Implement Mobile Device Management Mobile Device Security Cybersecurity SSThis slide showcases procedure that can help organization to implement mobile device management solution. Its key steps are current scenario assessment, policy development, choose solution etc. Increase audience engagement and knowledge by dispensing information using Process To Implement Mobile Device Management Mobile Device Security Cybersecurity SS This template helps you present information on Five stages. You can also present information on Estimated Budget, Phase Duration using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
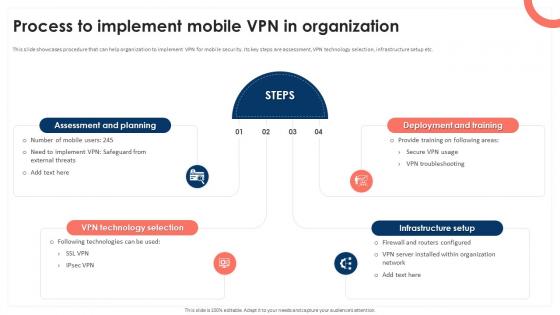 Process To Implement Mobile Vpn In Organization Mobile Device Security Cybersecurity SS
Process To Implement Mobile Vpn In Organization Mobile Device Security Cybersecurity SSThis slide showcases procedure that can help organization to implement VPN for mobile security. Its key steps are assessment, VPN technology selection, infrastructure setup etc. Introducing Process To Implement Mobile Vpn In Organization Mobile Device Security Cybersecurity SS to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Rating, Ideal, Softwares using this template. Grab it now to reap its full benefits.
-
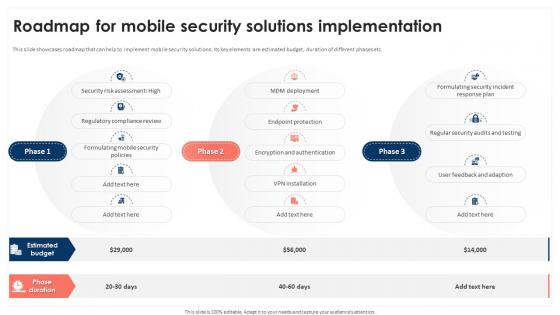 Roadmap For Mobile Security Solutions Implementation Mobile Device Security Cybersecurity SS
Roadmap For Mobile Security Solutions Implementation Mobile Device Security Cybersecurity SSThis slide showcases roadmap that can help to implement mobile security solutions. Its key elements are estimated budget, duration of different phases etc. Present the topic in a bit more detail with this Roadmap For Mobile Security Solutions Implementation Mobile Device Security Cybersecurity SS Use it as a tool for discussion and navigation on Device Security Budget, Device Security Solutions, Techniques Effectiveness This template is free to edit as deemed fit for your organization. Therefore download it now.
-
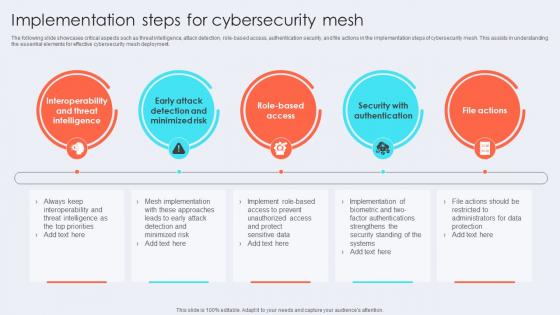 Implementation Steps For Cybersecurity Mesh
Implementation Steps For Cybersecurity MeshThe following slide showcases critical aspects such as threat intelligence, attack detection, role-based access, authentication security, and file actions in the implementation steps of cybersecurity mesh. This assists in understanding the essential elements for effective cybersecurity mesh deployment. Introducing our premium set of slides with Implementation Steps For Cybersecurity Mesh Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Threat Intelligence, Minimized Risk, Security With Authentication. So download instantly and tailor it with your information.
-
 Implementing Cybersecurity In BCP For Enhancing Risk Protection
Implementing Cybersecurity In BCP For Enhancing Risk ProtectionThis slide represents process to implement cybersecurity in business continuity planning BCP for improving company data protection from cyber risks. It includes steps such as conducting business impact analysis, developing risk assessment, maintaining total vison, etc. Presenting our set of slides with Implementing Cybersecurity In BCP For Enhancing Risk Protection This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Maintain Total Vision, Risk Management, Implement Controls
-
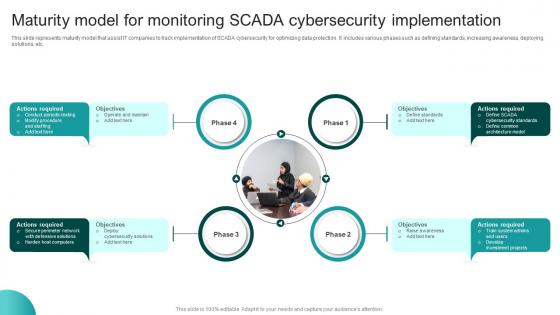 Maturity Model For Monitoring SCADA Cybersecurity Implementation
Maturity Model For Monitoring SCADA Cybersecurity ImplementationThis slide represents maturity model that assist IT companies to track implementation of SCADA cybersecurity for optimizing data protection. It includes various phases such as defining standards, increasing awareness, deploying solutions, etc. Introducing our premium set of slides with Maturity Model For Monitoring SCADA Cybersecurity Implementation Ellicudate the Four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Objectives, Operate And Maintain, Actions Required, Cybersecurity Implementation. So download instantly and tailor it with your information.
-
 Q101 Changemakers Catalysts Organizational Case Study On Implementing Cybersecurity System CM SS V
Q101 Changemakers Catalysts Organizational Case Study On Implementing Cybersecurity System CM SS VThis slide defines the case study of an IT Information technology professional implementing a new company-wide cybersecurity system. It consists of details related to a case study that reflects the importance of change agents in an organization. Introducing Q101 Changemakers Catalysts Organizational Case Study On Implementing Cybersecurity System CM SS V to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Goal, Challenge, Solutions, using this template. Grab it now to reap its full benefits.
-
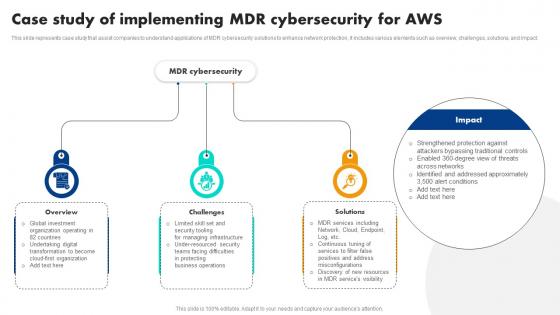 Case Study Of Implementing Mdr Cybersecurity For Aws
Case Study Of Implementing Mdr Cybersecurity For AwsThis slide represents case study that assist companies to understand applications of MDR cybersecurity solutions to enhance network protection, it includes various elements such as overview, challenges, solutions, and impact. Introducing our premium set of slides with Case Study Of Implementing Mdr Cybersecurity For Aws. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Overview, Challenges, Solutions. So download instantly and tailor it with your information.
-
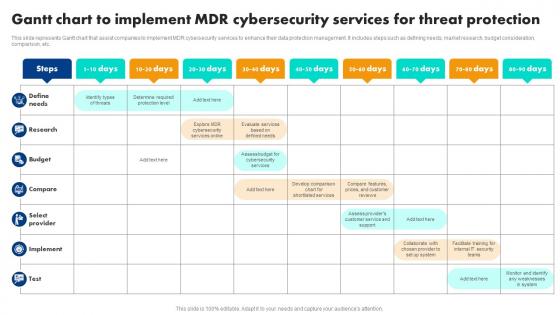 Gantt Chart To Implement Mdr Cybersecurity Services For Threat Protection
Gantt Chart To Implement Mdr Cybersecurity Services For Threat ProtectionThis slide represents Gantt chart that assist companies to implement MDR cybersecurity services to enhance their data protection management. It includes steps such as defining needs, market research, budget consideration, comparison, etc. Introducing our Gantt Chart To Implement Mdr Cybersecurity Services For Threat Protection set of slides. The topics discussed in these slides are Cybersecurity, Services, Threat Protection. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
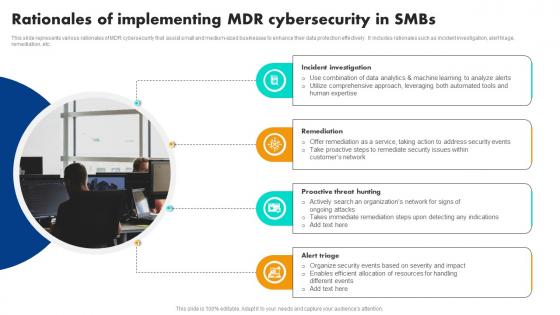 Rationales Of Implementing Mdr Cybersecurity In Smbs
Rationales Of Implementing Mdr Cybersecurity In SmbsThis slide represents various rationales of MDR cybersecurity that assist small and medium-sized businesses to enhance their data protection effectively. It includes rationales such as incident investigation, alert triage, remediation, etc. Presenting our set of slides with Rationales Of Implementing Mdr Cybersecurity In Smbs. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Incident Investigation, Remediation, Proactive Threat Hunting.
-
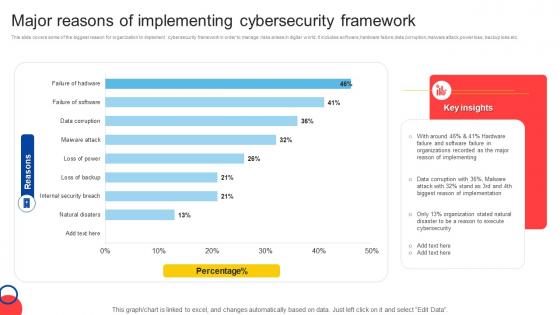 Major Reasons Of Implementing Cybersecurity Framework
Major Reasons Of Implementing Cybersecurity FrameworkThis slide covers some of the biggest reason for organization to implement cybersecurity framework in order to manage risks arises in digital world. It includes software,hardware failure,data corruption,malware attack,power loss, backup loss etc. Introducing our Major Reasons Of Implementing Cybersecurity Framework set of slides. The topics discussed in these slides are Hardware, Software, Cybersecurity. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Implementation Latest Technologies Strategy 3 Establish Cybersecurity In The Banking
Implementation Latest Technologies Strategy 3 Establish Cybersecurity In The BankingThe slide explains the establish cybersecurity strategy of the company. It provides key points such as what to do in the strategy, major reason behind the strategy and key steps required for the strategy. Introducing Implementation Latest Technologies Strategy 3 Establish Cybersecurity In The Banking to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Driven Protection, Technology, Measures, Customers, Research And Development, using this template. Grab it now to reap its full benefits.
-
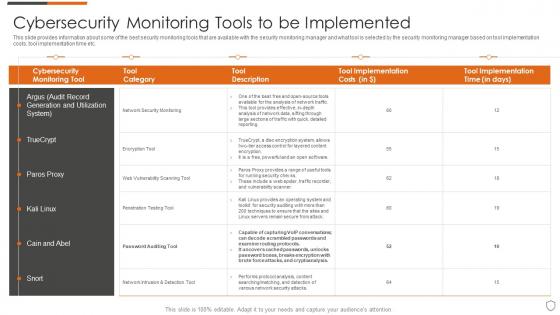 Cybersecurity monitoring tools to be implemented ppt powerpoint presentation file gallery
Cybersecurity monitoring tools to be implemented ppt powerpoint presentation file galleryThis slide provides information about some of the best security monitoring tools that are available with the security monitoring manager and what tool is selected by the security monitoring manager based on tool implementation costs, tool implementation time etc. Present the topic in a bit more detail with this Cybersecurity Monitoring Tools To Be Implemented Ppt Powerpoint Presentation File Gallery. Use it as a tool for discussion and navigation on Cybersecurity Monitoring Tools To Be Implemented. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
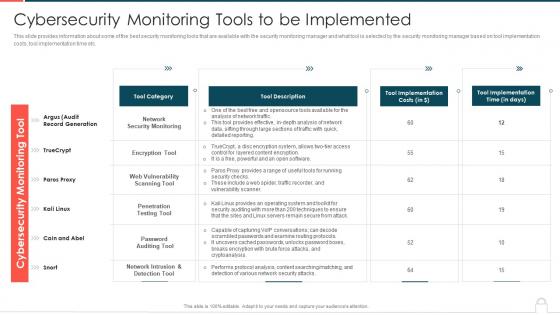 Ways to set up an advanced cybersecurity monitoring plan cybersecurity monitoring tools to be implemented
Ways to set up an advanced cybersecurity monitoring plan cybersecurity monitoring tools to be implementedThis slide provides information about some of the best security monitoring tools that are available with the security monitoring manager and what tool is selected by the security monitoring manager based on tool implementation costs, tool implementation time etc. Present the topic in a bit more detail with this Ways To Set Up An Advanced Cybersecurity Monitoring Plan Cybersecurity Monitoring Tools To Be Implemented. Use it as a tool for discussion and navigation on Tool Category, Tool Description, Tool Implementation Costs, Tool Implementation Time. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cybersecurity Risk Management Implementation Process
Cybersecurity Risk Management Implementation ProcessThe following slide explains implementation method for cybersecurity risk management for the organization to ensure protection of key business data. It includes steps such as categorize, security controls, implementation, assess, etc. Presenting our set of slides with name Cybersecurity Risk Management Implementation Process. This exhibits information on six stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Categorize System, Security Controls, Implementation .
-
 Cybersecurity Risk Management Plan Implementation Stages
Cybersecurity Risk Management Plan Implementation StagesThis slide explains various steps for implementation of cybersecurity risk management plan in the organization to ensure time and budget compliance. It includes elements such as current state analysis, assessment, target state, etc. Presenting our set of slides with name Cybersecurity Risk Management Plan Implementation Stages. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Current State Analysis, Assessment, Target State .
-
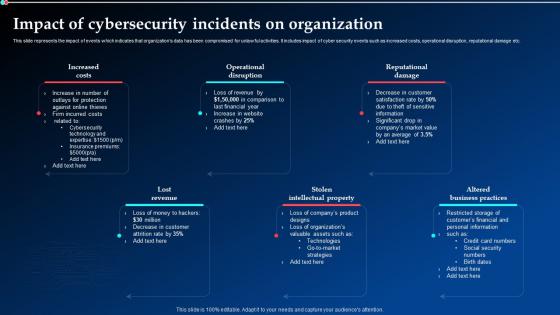 Impact Of Cybersecurity Incidents On Organization Implementing Cyber Security Ppt Topics
Impact Of Cybersecurity Incidents On Organization Implementing Cyber Security Ppt TopicsThis slide represents the impact of events which indicates that organizations data has been compromised for unlawful activities. It includes impact of cyber security events such as increased costs, operational disruption, reputational damage etc. Present the topic in a bit more detail with this Impact Of Cybersecurity Incidents On Organization Implementing Cyber Security Ppt Topics. Use it as a tool for discussion and navigation on Operational Disruption, Reputational Damage, Stolen Intellectual Property. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
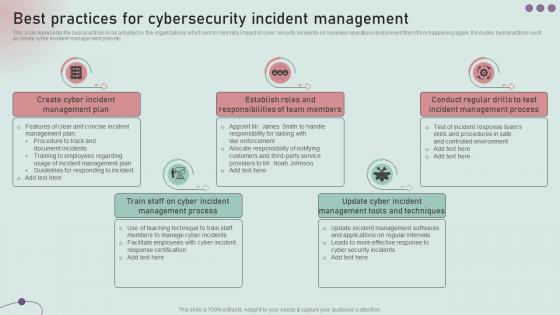 Best Practices For Cybersecurity Incident Management Development And Implementation Of Security
Best Practices For Cybersecurity Incident Management Development And Implementation Of SecurityThis slide represents the best practices to be adopted by the organizations which aim to minimize impact of cyber security incidents on business operations and prevent them from happening again. It includes best practices such as create cyber incident management plan etc. Increase audience engagement and knowledge by dispensing information using Best Practices For Cybersecurity Incident Management Development And Implementation Of Security. This template helps you present information on five stages. You can also present information on Create Cyber Incident, Management Plan, Establish Roles, Responsibilities Of Team Members using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
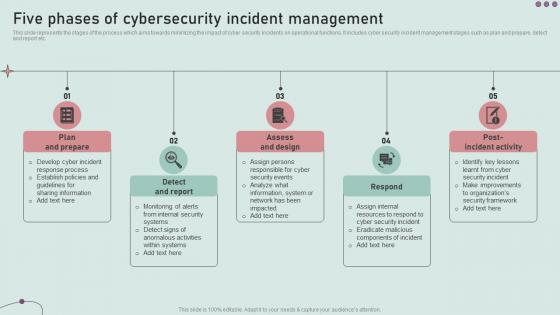 Five Phases Of Cybersecurity Incident Management Development And Implementation Of Security Incident
Five Phases Of Cybersecurity Incident Management Development And Implementation Of Security IncidentThis slide represents the stages of the process which aims towards minimizing the impact of cyber security incidents on operational functions. It includes cyber security incident management stages such as plan and prepare, detect and report etc. Introducing Five Phases Of Cybersecurity Incident Management Development And Implementation Of Security Incident to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Assess And Design, Detect And Report, Plan And Prepare, using this template. Grab it now to reap its full benefits.
-
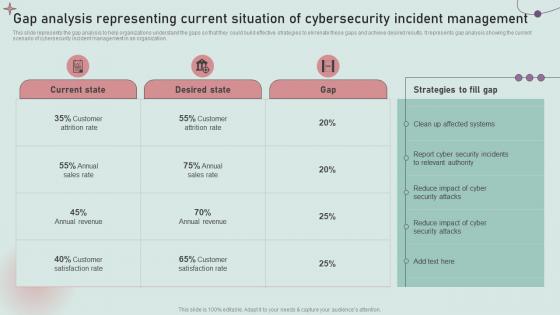 Gap Analysis Representing Current Situation Of Cybersecurity Development And Implementation Of Security
Gap Analysis Representing Current Situation Of Cybersecurity Development And Implementation Of SecurityThis slide represents the gap analysis to help organizations understand the gaps so that they could build effective strategies to eliminate these gaps and achieve desired results. It represents gap analysis showing the current scenario of cybersecurity incident management in an organization. Deliver an outstanding presentation on the topic using this Gap Analysis Representing Current Situation Of Cybersecurity Development And Implementation Of Security. Dispense information and present a thorough explanation of Report Cyber Security Incidents, Relevant Authority using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
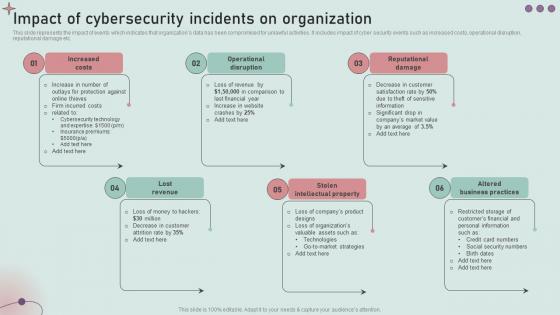 Impact Of Cybersecurity Incidents On Organization Development And Implementation Of Security Incident
Impact Of Cybersecurity Incidents On Organization Development And Implementation Of Security IncidentThis slide represents the impact of events which indicates that organizations data has been compromised for unlawful activities. It includes impact of cyber security events such as increased costs, operational disruption, reputational damage etc. Increase audience engagement and knowledge by dispensing information using Impact Of Cybersecurity Incidents On Organization Development And Implementation Of Security Incident. This template helps you present information on five stages. You can also present information on Increased Costs, Operational Disruption, Reputational Damage using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
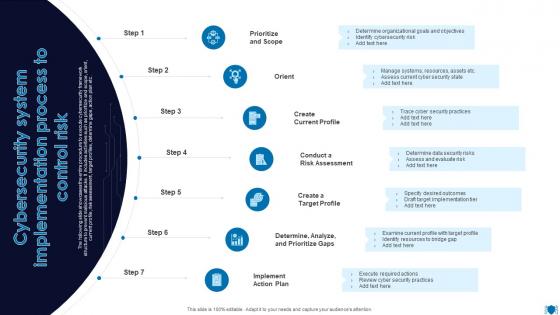 Cybersecurity System Implementation Process To Control Risk
Cybersecurity System Implementation Process To Control RiskThe following slide showcases the entire procedure to execute cybersecurity framework structure to prevent malicious attacks. It includes activities such as prioritize and scope, orient, current profile, risk assessment, target profiles, determine gaps, action plan etc. Presenting our set of slides with Cybersecurity System Implementation Process To Control Risk. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Create Current Profile, Determine, Analyze, Prioritize Gaps.
-
 Cybersecurity System Implementation Timeline With Capability And Initiatives
Cybersecurity System Implementation Timeline With Capability And InitiativesThe following slide showcases the information security framework execution timeline to safeguard companys reputation and manage IT infrastructure. It includes elements such as capability, initiatives, deploying security cloud, assessing asset criticality, optimizing patching posture etc. Introducing our Cybersecurity System Implementation Timeline With Capability And Initiatives set of slides. The topics discussed in these slides are Identify, Protect, Detect. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
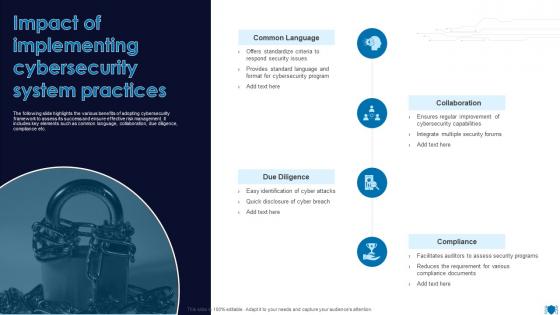 Impact Of Implementing Cybersecurity System Practices
Impact Of Implementing Cybersecurity System PracticesThe following slide highlights the various benefits of adopting cybersecurity framework to assess its success and ensure effective risk management. It includes key elements such as common language, collaboration, due diligence, compliance etc. Introducing our premium set of slides with Impact Of Implementing Cybersecurity System Practices. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Common Language, Collaboration, Due Diligence. So download instantly and tailor it with your information.
-
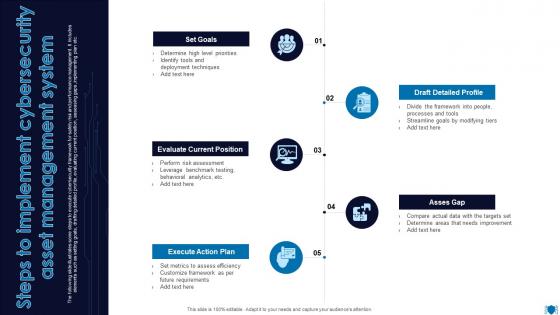 Steps To Implement Cybersecurity Asset Management System
Steps To Implement Cybersecurity Asset Management SystemThe following slide illustrates some steps to execute cybersecurity framework for safety risk and performance management. It includes elements such as setting goals, drafting detailed profile, evaluating current position, assessing gaps, implementing plan etc. Presenting our set of slides with Steps To Implement Cybersecurity Asset Management System. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Evaluate Current Position, Execute Action Plan, Asses Gap.
-
 Cybersecurity Risk Assessment Cyber Security Risk Assessment Program Implementation Impact
Cybersecurity Risk Assessment Cyber Security Risk Assessment Program Implementation ImpactThe purpose of the following slide is to highlight the impact of impact of risk assessment on cyber crime attacks. It compares the number of security incident occurred in two consecutive months and highlight the prevailing trend in terms of going up, remaining same or going down. Present the topic in a bit more detail with this Cybersecurity Risk Assessment Cyber Security Risk Assessment Program Implementation Impact. Use it as a tool for discussion and navigation on Cyber Security, Risk Assessment, Program Implementation, Impact On Attacks Frequency. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Ultimate Guide For Blockchain Implementing Blockchain Cybersecurity Risks Mitigation BCT SS
Ultimate Guide For Blockchain Implementing Blockchain Cybersecurity Risks Mitigation BCT SSThe following slide illustrates some blockchain cybersecurity risk management techniques to manage accessibility and ensure data security. It includes elements such as reduce, avoid, accepts and transfer, etc. Increase audience engagement and knowledge by dispensing information using Ultimate Guide For Blockchain Implementing Blockchain Cybersecurity Risks Mitigation BCT SS This template helps you present information on Four stages. You can also present information on Reduce, Avoid, Accept, Transfer using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
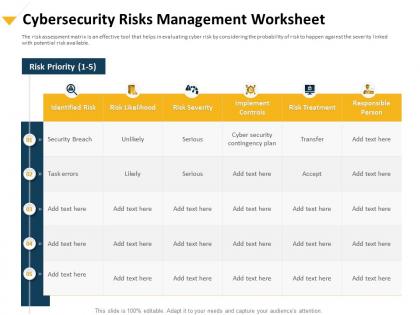 Cybersecurity risks management worksheet implement controls ppt portfolio
Cybersecurity risks management worksheet implement controls ppt portfolioThe risk assessment matrix is an effective tool that helps in evaluating cyber risk by considering the probability of risk to happen against the severity linked with potential risk available. Presenting this set of slides with name Cybersecurity Risks Management Worksheet Implement Controls Ppt Portfolio. The topics discussed in these slides are Cybersecurity Risks, Management, Worksheet, Implement Controls. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.


