Powerpoint Templates and Google slides for Data Mitigation
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Data Breach Prevention And Mitigation Strategies For Businesses Powerpoint Presentation Slides
Data Breach Prevention And Mitigation Strategies For Businesses Powerpoint Presentation SlidesThis complete deck covers various topics and highlights important concepts. It has PPT slides which cater to your business needs. This complete deck presentation emphasizes Data Breach Prevention And Mitigation Strategies For Businesses Powerpoint Presentation Slides and has templates with professional background images and relevant content. This deck consists of total of seventy five slides. Our designers have created customizable templates, keeping your convenience in mind. You can edit the color, text and font size with ease. Not just this, you can also add or delete the content if needed. Get access to this fully editable complete presentation by clicking the download button below.
-
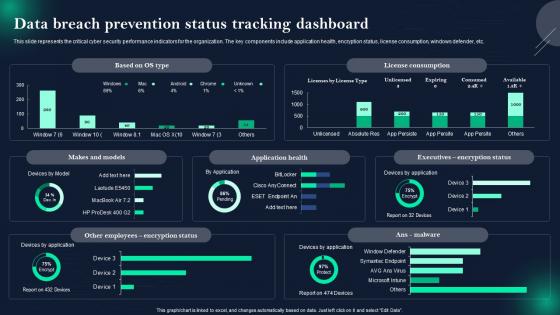 Data Breach Prevention And Mitigation Data Breach Prevention Status Tracking Dashboard
Data Breach Prevention And Mitigation Data Breach Prevention Status Tracking DashboardThis slide represents the critical cyber security performance indicators for the organization. The key components include application health, encryption status, license consumption, windows defender, etc. Present the topic in a bit more detail with this Data Breach Prevention And Mitigation Data Breach Prevention Status Tracking Dashboard. Use it as a tool for discussion and navigation on Critical Cyber Security, Performance Indicators, Encryption Status, License Consumption, Windows Defender. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Breach Prevention And Mitigation Healthcare Data Breaches In Previous Years
Data Breach Prevention And Mitigation Healthcare Data Breaches In Previous YearsThis slide depicts the number of data breaches experienced by large-scale healthcare industries in the last eight years, from 2016 to 2023. The purpose of this slide is to highlight the rise in data breach incidents in these years. Present the topic in a bit more detail with this Data Breach Prevention And Mitigation Healthcare Data Breaches In Previous Years. Use it as a tool for discussion and navigation on Data Breaches Experienced, Large Scale Healthcare Industries, Significant Surge In Healthcare. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Breach Prevention And Mitigation Number Of Data Breaches In Different Sectors
Data Breach Prevention And Mitigation Number Of Data Breaches In Different SectorsThe purpose of this slide is to outline the number of data breach attacks in different sectors from the year 2011 to 2023. The departments covered in this slide are business, medical, educational, government, and financial. Deliver an outstanding presentation on the topic using this Data Breach Prevention And Mitigation Number Of Data Breaches In Different Sectors. Dispense information and present a thorough explanation of Data Breach Attacks, Business, Medical, Educational, Government, Financial using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
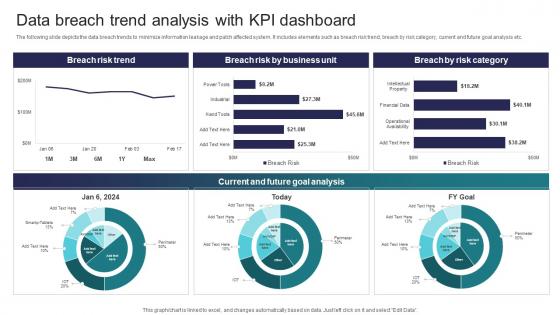 Data Breach Trend Analysis With KPI Dashboard Implementing Strategies To Mitigate Cyber Security Threats
Data Breach Trend Analysis With KPI Dashboard Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts the data breach trends to minimize information leakage and patch affected system. It includes elements such as breach risk trend, breach by risk category, current and future goal analysis etc. Present the topic in a bit more detail with this Data Breach Trend Analysis With KPI Dashboard Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Current And Future Goal Analysis, Breach Risk Trend This template is free to edit as deemed fit for your organization. Therefore download it now.
-
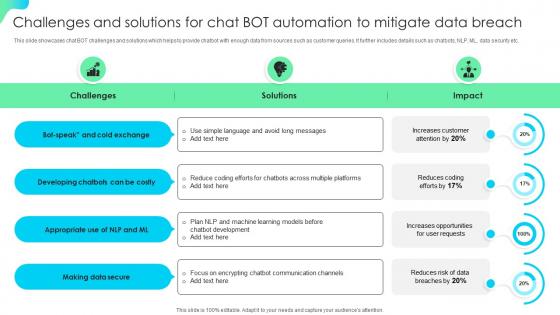 Challenges And Solutions For Chat Bot Automation To Mitigate Data Breach
Challenges And Solutions For Chat Bot Automation To Mitigate Data BreachThis Slide Showcases Chat BOT Challenges And Solutions Which Helps To Provide Chatbot With Enough Data From Sources Such As Customer Queries. It Further Includes Details Such As Chatbots, NLP, ML, Data Security Etc. Introducing Our Challenges And Solutions For Chat Bot Automation To Mitigate Data Breach Set Of Slides. The Topics Discussed In These Slides Are Opportunities, Solutions, Appropriate. This Is An Immediately Available Powerpoint Presentation That Can Be Conveniently Customized. Download It And Convince Your Audience.
-
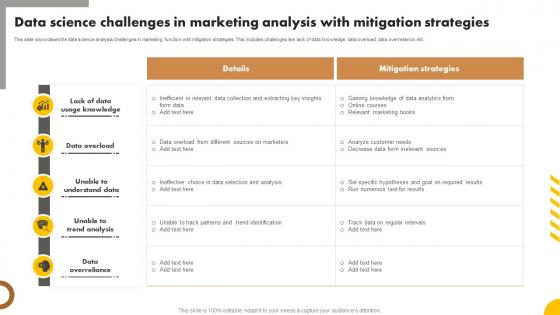 Data Science Challenges In Marketing Analysis With Mitigation Strategies
Data Science Challenges In Marketing Analysis With Mitigation StrategiesThis slide showcases the data science analysis challenges in marketing function with mitigation strategies. This includes challenges like lack of data knowledge, data overload, data overreliance, etc. Presenting our well structured Data Science Challenges In Marketing Analysis With Mitigation Strategies. The topics discussed in this slide are Knowledge, Data, Analysis. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
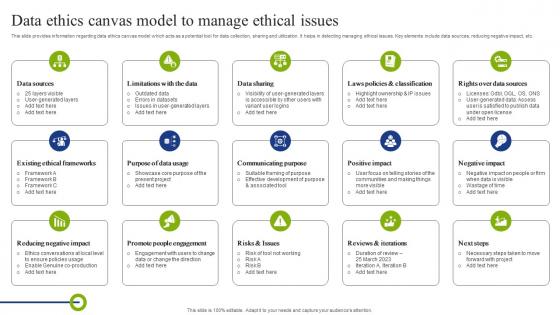 Data Ethics Canvas Model To Manage Ethical Issues Playbook To Mitigate Negative Of Technology
Data Ethics Canvas Model To Manage Ethical Issues Playbook To Mitigate Negative Of TechnologyThis slide provides information regarding data ethics canvas model which acts as a potential tool for data collection, sharing and utilization. It helps in detecting managing ethical issues. Key elements include data sources, reducing negative impact, etc. Introducing Data Ethics Canvas Model To Manage Ethical Issues Playbook To Mitigate Negative Of Technology to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Limitations With The Data, Rights Over Data Sources, Existing Ethical Frameworks, using this template. Grab it now to reap its full benefits.
-
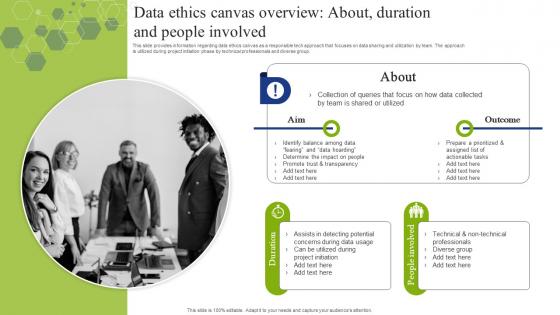 Data Ethics Canvas Overview About Duration And People Playbook To Mitigate Negative Of Technology
Data Ethics Canvas Overview About Duration And People Playbook To Mitigate Negative Of TechnologyThis slide provides information regarding data ethics canvas as a responsible tech approach that focuses on data sharing and utilization by team. The approach is utilized during project initiation phase by technical professionals and diverse group. Increase audience engagement and knowledge by dispensing information using Data Ethics Canvas Overview About Duration And People Playbook To Mitigate Negative Of Technology. This template helps you present information on two stages. You can also present information on Information, Approach, Professionals using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Major Risks And Mitigation Strategies For Cloud Encryption Implementation Cloud Data Encryption
Major Risks And Mitigation Strategies For Cloud Encryption Implementation Cloud Data EncryptionThe purpose of this slide is to discuss the challenges faced while encrypting cloud data. The critical components of this slide are the description of the risk, probability of occurrence, impact on system infrastructure, and possible mitigation strategies. Deliver an outstanding presentation on the topic using this Major Risks And Mitigation Strategies For Cloud Encryption Implementation Cloud Data Encryption. Dispense information and present a thorough explanation of Probability, Impact using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 K81 Data Breach Prevention And Mitigation Strategies For Businesses For Table Of Contents
K81 Data Breach Prevention And Mitigation Strategies For Businesses For Table Of ContentsIntroducing K81 Data Breach Prevention And Mitigation Strategies For Businesses For Table Of Contents to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Data Breach Prevention, Mitigation Strategies For Businesses, Data Loss Prevention Tools, using this template. Grab it now to reap its full benefits.
-
 Data Breach Prevention Strategies For Employees Data Breach Prevention And Mitigation
Data Breach Prevention Strategies For Employees Data Breach Prevention And MitigationThis slide highlights the data breach mitigation measures for workers. These strategies include maintain a record of banking receipts, do not believe everything, be mindful of sharing anything on social media, secure all devices, protect individual accounts, etc. Deliver an outstanding presentation on the topic using this Data Breach Prevention Strategies For Employees Data Breach Prevention And Mitigation. Dispense information and present a thorough explanation of Data Breach Mitigation Measures, Banking Receipts, Social Media, Secure All Devices, Protect Individual Accounts using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Breach Prevention Strategies For Enterprises Data Breach Prevention And Mitigation
Data Breach Prevention Strategies For Enterprises Data Breach Prevention And MitigationThe purpose of this slide is to outline the data breach mitigation strategies for businesses. These include access control, encryption, web security solutions, network security, up-to-date software and hardware, preparation, training employees and users, etc. Present the topic in a bit more detail with this Data Breach Prevention Strategies For Enterprises Data Breach Prevention And Mitigation. Use it as a tool for discussion and navigation on Network Security, Data Loss Prevention, Regularly Perform Patching Activities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Breach Prevention Strategies For Users Data Breach Prevention And Mitigation
Data Breach Prevention Strategies For Users Data Breach Prevention And MitigationThis slide represents the strategies to protect users from data breaches. These include use unique passwords, two-factor authentication, only submit sensitive data on HTTPS websites, software and hardware updates, encrypt hard drives, etc. Deliver an outstanding presentation on the topic using this Data Breach Prevention Strategies For Users Data Breach Prevention And Mitigation. Dispense information and present a thorough explanation of Unusual Email Attachments, Maintain Software And Hardware, Several Online Services using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Breach Response Plan Secure Operations Data Breach Prevention And Mitigation
Data Breach Response Plan Secure Operations Data Breach Prevention And MitigationThis slide represents actions to be taken, the responsible team, the deadline, and tasks for securing operations after a data breach. The action items include secure physical areas, assemble expert team, consult with legal counsel, secure website and contact search engines, etc. Present the topic in a bit more detail with this Data Breach Response Plan Secure Operations Data Breach Prevention And Mitigation. Use it as a tool for discussion and navigation on Assemble Expert Team, Consult With Legal Counsel, Secure Physical Areas. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Icons Slide For Data Breach Prevention And Mitigation Strategies For Businesses
Icons Slide For Data Breach Prevention And Mitigation Strategies For BusinessesPresenting our well crafted Icons Slide For Data Breach Prevention And Mitigation Strategies For Businesses set of slides. The slides include icons that are innovatively designed by our team of experts. The icons are easy to edit so you can conveniently increase or decrease their size without any loss in resolution. Therefore, grab them instantly.
-
 Table Of Contents For Data Breach Prevention And Mitigation Strategies For Businesses
Table Of Contents For Data Breach Prevention And Mitigation Strategies For BusinessesIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Data Breach Prevention And Mitigation Strategies For Businesses. This template helps you present information on ten stages. You can also present information on Data Breach Prevention Tools, Data Breach Response Plan, Prevention And Mitigation, Training And Budget using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Agenda For Data Breach Prevention And Mitigation Strategies For Businesses
Agenda For Data Breach Prevention And Mitigation Strategies For BusinessesIntroducing Agenda For Data Breach Prevention And Mitigation Strategies For Businesses to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Data Exploitation Techniques, Data Breach Prevention, Mitigation Strategies For Businesses, using this template. Grab it now to reap its full benefits.
-
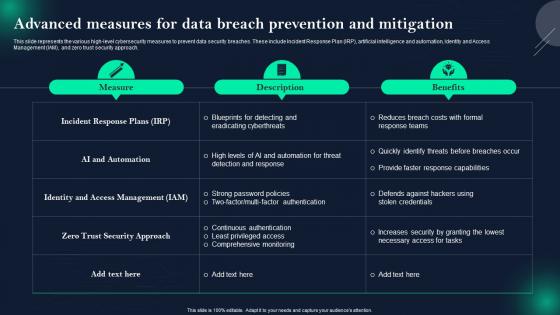 Data Breach Prevention Advanced Measures For Data Breach Prevention And Mitigation
Data Breach Prevention Advanced Measures For Data Breach Prevention And MitigationThis slide represents the various high-level cybersecurity measures to prevent data security breaches. These include Incident Response Plan IRP, artificial intelligence and automation, Identity and Access Management IAM, and zero trust security approach. Deliver an outstanding presentation on the topic using this Data Breach Prevention Advanced Measures For Data Breach Prevention And Mitigation. Dispense information and present a thorough explanation of Incident Response Plans, AI And Automation, Zero Trust Security Approach using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Breach Prevention And Mitigation Checklist For Responding To A Data Breach Attack
Data Breach Prevention And Mitigation Checklist For Responding To A Data Breach AttackThis slide represents the checklist for implementing a data breach response plan. The fundamental approaches are identify and isolate impacted systems or networks, perform a formal risk assessment, restore systems and address security flaws, notify affected parties, etc. Present the topic in a bit more detail with this Data Breach Prevention And Mitigation Checklist For Responding To A Data Breach Attack. Use it as a tool for discussion and navigation on Data Breach Response Plan, Fundamental Approaches, Systems Or Networks, Perform A Formal Risk Assessment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Breach Prevention And Mitigation Common Data Breach Attack Vectors
Data Breach Prevention And Mitigation Common Data Breach Attack VectorsThis slide represents several data breach attack vectors. The main components are stolen or compromised credentials, social engineering attacks, ransomware, system vulnerabilities, human error and IT failures, physical or site security errors, etc. Deliver an outstanding presentation on the topic using this Data Breach Prevention And Mitigation Common Data Breach Attack Vectors. Dispense information and present a thorough explanation of Brute Force Attacks, Purchasing Stolen Credentials, Phishing Scams, Fraudulent Emails, Deceptive Websites using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Breach Prevention And Mitigation Data Breach Attacks Experienced By Major Business
Data Breach Prevention And Mitigation Data Breach Attacks Experienced By Major BusinessThis slide highlights the top data breach victims based on different industrial sectors. These industries include email service providers, social media websites, online auction websites, retail services, government agencies, file-sharing and hosting services, etc. Present the topic in a bit more detail with this Data Breach Prevention And Mitigation Data Breach Attacks Experienced By Major Business. Use it as a tool for discussion and navigation on Heartland Payment Systems, Email Service Provider, Social Media Website, Online Auction Website. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Breach Prevention And Mitigation Data Breach Awareness Training Program
Data Breach Prevention And Mitigation Data Breach Awareness Training ProgramThis slide represents the training program for data breach awareness which will help organizations to prevent various cyber security scams. The purpose of this slide is to outline the mode, cost, agenda, and schedule for the training programs. Deliver an outstanding presentation on the topic using this Data Breach Prevention And Mitigation Data Breach Awareness Training Program. Dispense information and present a thorough explanation of Phishing Emails And Social Engineering, Data Breaches And Cybersecurity, Data Privacy Regulations And Compliance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Breach Prevention And Mitigation Data Breach Response Plan Fix Vulnerabilities
Data Breach Prevention And Mitigation Data Breach Response Plan Fix VulnerabilitiesThis slide represents actions to be taken, the responsible team, the deadline, and tasks for fixing vulnerabilities after a data breach. The action items include assessing Service Providers access privileges, reviewing network segmentation, monitoring, etc. Deliver an outstanding presentation on the topic using this Data Breach Prevention And Mitigation Data Breach Response Plan Fix Vulnerabilities. Dispense information and present a thorough explanation of Collaborate With Forensics Experts, Review Network Segmentation, Communicate Transparently using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Breach Prevention And Mitigation Data Exploitation Methods Used By Criminals
Data Breach Prevention And Mitigation Data Exploitation Methods Used By CriminalsThis slide discusses the exploitation of data after stealing it from authorized resources. These methods include opening new credit cards, withdrawing money from accounts, filing fraudulent tax returns, medical treatment using insurance, using credit card rewards, etc. Present the topic in a bit more detail with this Data Breach Prevention And Mitigation Data Exploitation Methods Used By Criminals. Use it as a tool for discussion and navigation on File Fraudulent Tax Returns, Withdraw Money From Accounts, Medical Treatment Using Insurance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
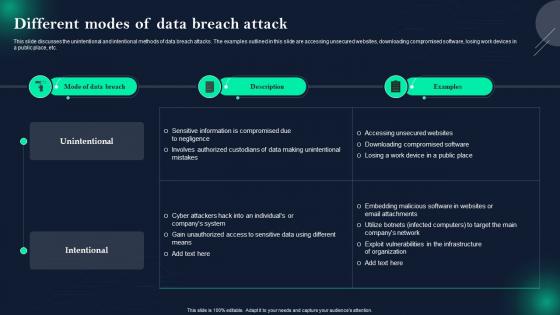 Data Breach Prevention And Mitigation Different Modes Of Data Breach Attack
Data Breach Prevention And Mitigation Different Modes Of Data Breach AttackThis slide discusses the unintentional and intentional methods of data breach attacks. The examples outlined in this slide are accessing unsecured websites, downloading compromised software, losing work devices in a public place, etc. Deliver an outstanding presentation on the topic using this Data Breach Prevention And Mitigation Different Modes Of Data Breach Attack. Dispense information and present a thorough explanation of Unintentional And Intentional Methods, Data Breach Attacks, Unsecured Websites, Downloading Compromised Software, Losing Work Devices using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Breach Prevention And Mitigation Major Types Of Data Security Breaches
Data Breach Prevention And Mitigation Major Types Of Data Security BreachesThis slide discusses the significant categories of information loss. The purpose of this slide is to describe several types of data security breaches. These include human error, device loss, cyberattacks, internal breaches, etc. Deliver an outstanding presentation on the topic using this Data Breach Prevention And Mitigation Major Types Of Data Security Breaches. Dispense information and present a thorough explanation of Social Engineering Attacks, IT Team Misconfiguring Servers, Disgruntled Employees, Gain Unauthorized Access using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
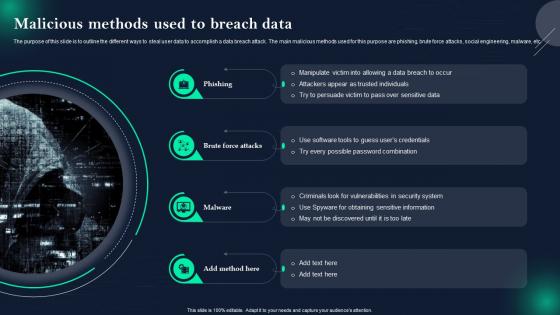 Data Breach Prevention And Mitigation Malicious Methods Used To Breach Data
Data Breach Prevention And Mitigation Malicious Methods Used To Breach DataThe purpose of this slide is to outline the different ways to steal user data to accomplish a data breach attack. The main malicious methods used for this purpose are phishing, brute force attacks, social engineering, malware, etc. Increase audience engagement and knowledge by dispensing information using Data Breach Prevention And Mitigation Malicious Methods Used To Breach Data. This template helps you present information on four stages. You can also present information on Criminals Look For Vulnerabilities, Possible Password Combination, Social Engineering, Malware using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data Breach Prevention And Mitigation Overview Of Various Targets Of Data Breach
Data Breach Prevention And Mitigation Overview Of Various Targets Of Data BreachThis slide represents information about several data breach targets and types of data compromised. These targets are organizations and businesses, government agencies, healthcare providers, financial institutions, individuals, websites, online platforms, etc. Present the topic in a bit more detail with this Data Breach Prevention And Mitigation Overview Of Various Targets Of Data Breach. Use it as a tool for discussion and navigation on Organizations And Businesses, Healthcare Providers, Educational Institutions, Websites And Online Platforms. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
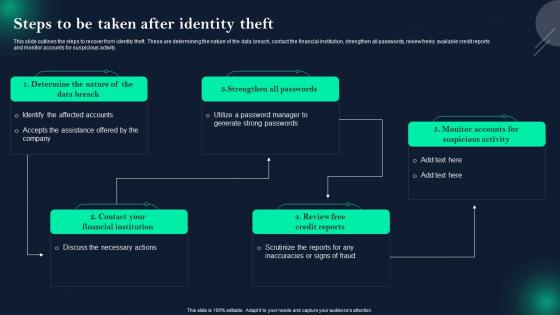 Data Breach Prevention And Mitigation Steps To Be Taken After Identity Theft
Data Breach Prevention And Mitigation Steps To Be Taken After Identity TheftThis slide outlines the steps to recover from identity theft. These are determining the nature of the data breach, contact the financial institution, strengthen all passwords, review freely available credit reports and monitor accounts for suspicious activity. Deliver an outstanding presentation on the topic using this Data Breach Prevention And Mitigation Steps To Be Taken After Identity Theft. Dispense information and present a thorough explanation of Strengthen All Passwords, Review Free Credit Reports, Contact Your Financial Institution using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
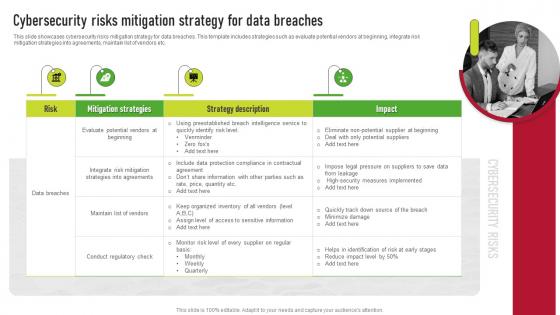 Cybersecurity Risks Mitigation Strategy For Data Breaches Supplier Risk Management
Cybersecurity Risks Mitigation Strategy For Data Breaches Supplier Risk ManagementThis slide showcases cybersecurity risks mitigation strategy for data breaches. This template includes strategies such as evaluate potential vendors at beginning, integrate risk mitigation strategies into agreements, maintain list of vendors etc. Introducing Cybersecurity Risks Mitigation Strategy For Data Breaches Supplier Risk Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Mitigation Strategies, Strategy Description, Risk, using this template. Grab it now to reap its full benefits.
-
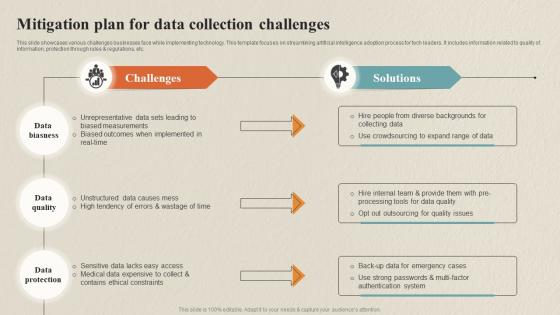 Mitigation Plan For Data Collection Challenges Data Collection Process For Omnichannel
Mitigation Plan For Data Collection Challenges Data Collection Process For OmnichannelThis slide showcases various challenges businesses face while implementing technology. This template focuses on streamlining artificial intelligence adoption process for tech leaders. It includes information related to quality of information, protection through rules regulations, etc.Deliver an outstanding presentation on the topic using this Mitigation Plan For Data Collection Challenges Data Collection Process For Omnichannel. Dispense information and present a thorough explanation of Unrepresentative Data, Biased Measurements, Ethical Constraints using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
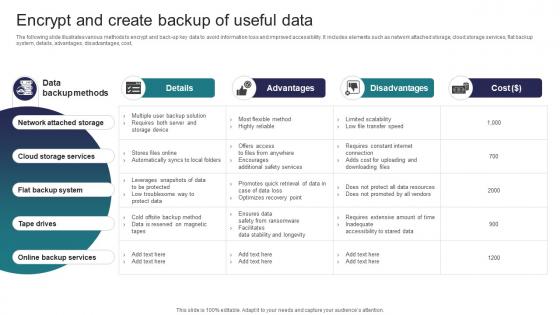 Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security Threats
Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide illustrates various methods to encrypt and back up key data to avoid information loss and improved accessibility. It includes elements such as network attached storage, cloud storage services, flat backup system, details, advantages, disadvantages, cost, Deliver an outstanding presentation on the topic using this Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Network Attached Storage, Cloud Storage Services, Flat Backup System using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
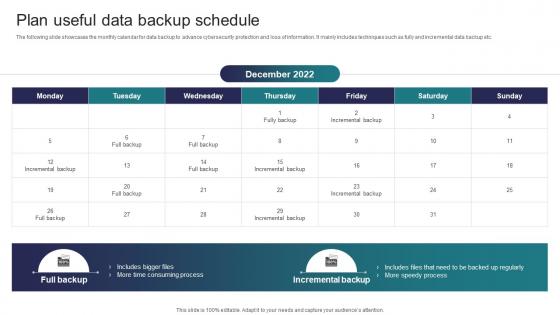 Plan Useful Data Backup Schedule Implementing Strategies To Mitigate Cyber Security Threats
Plan Useful Data Backup Schedule Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases the monthly calendar for data backup to advance cybersecurity protection and loss of information. It mainly includes techniques such as fully and incremental data backup etc. Increase audience engagement and knowledge by dispensing information using Plan Useful Data Backup Schedule Implementing Strategies To Mitigate Cyber Security Threats This template helps you present information on one stages. You can also present information on Time Consuming Process, Speedy Process, Incremental Backup using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
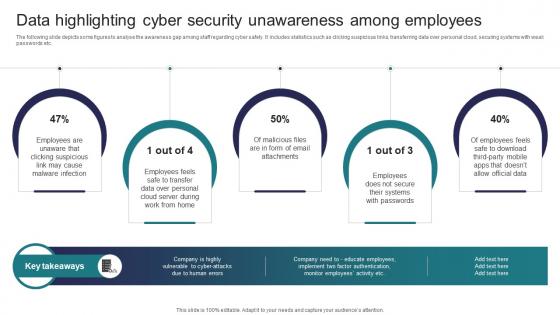 Implementing Strategies To Mitigate Cyber Security Data Highlighting Cyber Security Unawareness Among
Implementing Strategies To Mitigate Cyber Security Data Highlighting Cyber Security Unawareness AmongThe following slide depicts some figures to analyse the awareness gap among staff regarding cyber safety. It includes statistics such as clicking suspicious links, transferring data over personal cloud, securing systems with weak passwords etc. Introducing Implementing Strategies To Mitigate Cyber Security Data Highlighting Cyber Security Unawareness Among to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Email Attachments, Systems, Employees using this template. Grab it now to reap its full benefits.
-
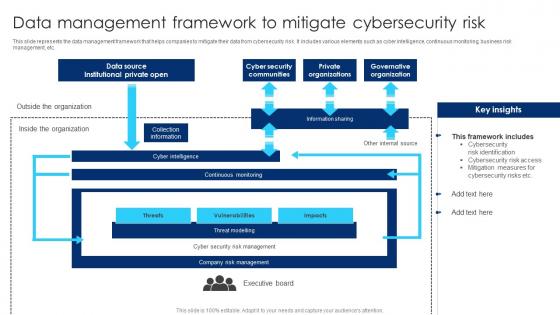 Data Management Framework To Mitigate Cybersecurity Risk
Data Management Framework To Mitigate Cybersecurity RiskThis slide represents the data management framework that helps companies to mitigate their data from cybersecurity risk. It includes various elements such as cyber intelligence, continuous monitoring, business risk management, etc. Presenting our well structured Data Management Framework To Mitigate Cybersecurity Risk. The topics discussed in this slide are Cyber Security Communities, Private Organizations, Collection Information. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
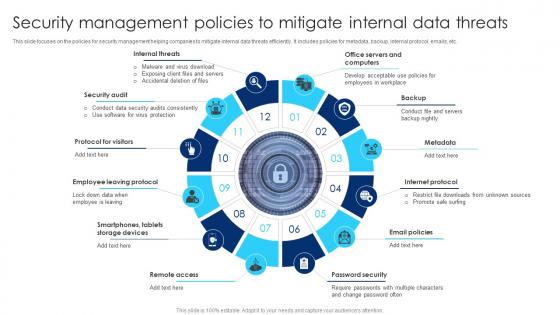 Security Management Policies To Mitigate Internal Data Threats
Security Management Policies To Mitigate Internal Data ThreatsThis slide focuses on the policies for security management helping companies to mitigate internal data threats efficiently. It includes policies for metadata, backup, internal protocol, emails, etc. Introducing our premium set of slides with Security Management Policies To Mitigate Internal Data Threats. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Protocol For Visitors, Internet Protocol, Security Audit. So download instantly and tailor it with your information.
-
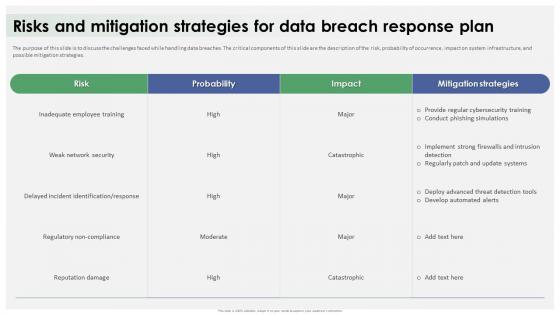 Data Breach Response Plan Risks And Mitigation Strategies For Data Breach Response Plan
Data Breach Response Plan Risks And Mitigation Strategies For Data Breach Response PlanThe purpose of this slide is to discuss the challenges faced while handling data breaches. The critical components of this slide are the description of the risk, probability of occurrence, impact on system infrastructure, and possible mitigation strategies. Deliver an outstanding presentation on the topic using this Data Breach Response Plan Risks And Mitigation Strategies For Data Breach Response Plan. Dispense information and present a thorough explanation of Inadequate Employee Training, Weak Network Security, Regulatory Non Compliance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
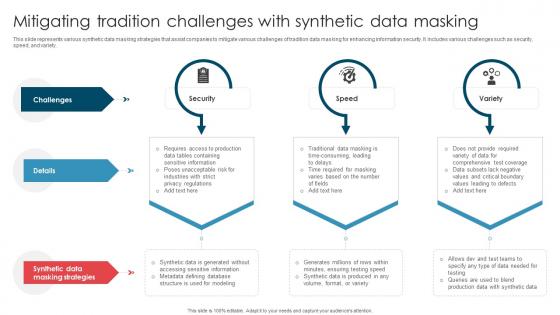 Mitigating Tradition Challenges With Synthetic Data Masking
Mitigating Tradition Challenges With Synthetic Data MaskingThis slide represents various synthetic data masking strategies that assist companies to mitigate various challenges of tradition data masking for enhancing information security. It includes various challenges such as security, speed, and variety. Introducing our Mitigating Tradition Challenges With Synthetic Data Masking set of slides. The topics discussed in these slides are Challenges, Security, Speed, Variety.This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
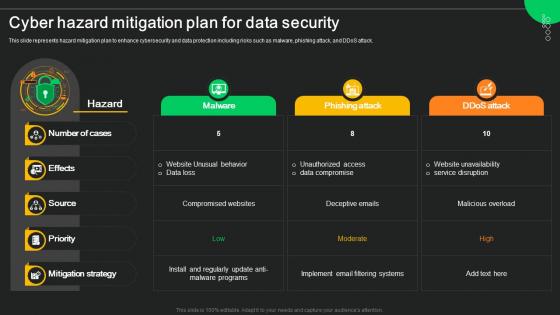 Cyber Hazard Mitigation Plan For Data Security
Cyber Hazard Mitigation Plan For Data SecurityThis slide represents hazard mitigation plan to enhance cybersecurity and data protection including risks such as malware, phishing attack, and DDoS attack. Presenting our well structured Cyber Hazard Mitigation Plan For Data Security. The topics discussed in this slide are Malware, Phishing Attack, Ddos Attack. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
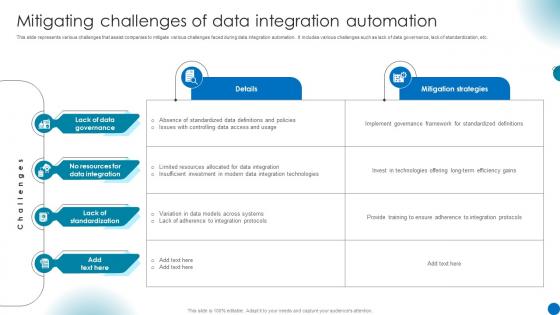 Mitigating Challenges Of Data Integration Automation
Mitigating Challenges Of Data Integration AutomationThis slide represents various challenges that assist companies to mitigate various challenges faced during data integration automation. It includes various challenges such as lack of data governance, lack of standardization, etc. Presenting our well structured Mitigating Challenges Of Data Integration Automation The topics discussed in this slide are Data Governance, Data Integration, Mitigation Strategies. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
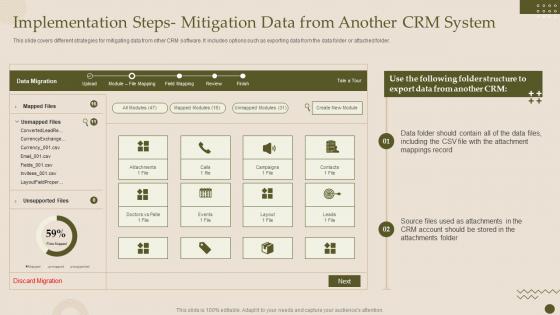 Implementation Steps Mitigation Data From Another Crm System Crm Software Deployment Guide
Implementation Steps Mitigation Data From Another Crm System Crm Software Deployment GuideThis slide covers different strategies for mitigating data from other CRM software. It includes options such as exporting data from the data folder or attached folder. Deliver an outstanding presentation on the topic using this Implementation Steps Mitigation Data From Another Crm System Crm Software Deployment Guide. Dispense information and present a thorough explanation of Mitigation, Implementation, Attachment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
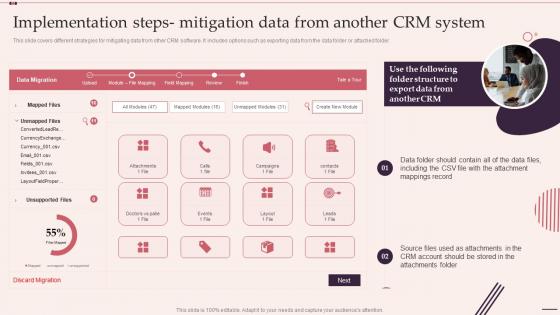 F505 Implementation Steps Mitigation Data From Another Customer Relationship Management System
F505 Implementation Steps Mitigation Data From Another Customer Relationship Management SystemThis slide covers different strategies for mitigating data from other CRM software. It includes options such as exporting data from the data folder or attached folder. Deliver an outstanding presentation on the topic using this F505 Implementation Steps Mitigation Data From Another Customer Relationship Management System. Dispense information and present a thorough explanation of Implementation, Mitigation, Attachment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
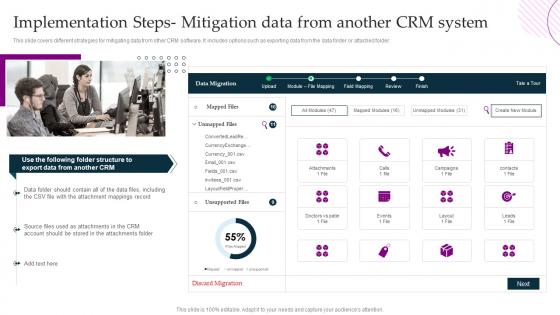 Crm Platform Implementation Plan Implementation Steps Mitigation Data From Another Crm System
Crm Platform Implementation Plan Implementation Steps Mitigation Data From Another Crm SystemThis slide covers different strategies for mitigating data from other CRM software. It includes options such as exporting data from the data folder or attached folder. Present the topic in a bit more detail with thisCrm Platform Implementation Plan Implementation Steps Mitigation Data From Another Crm System. Use it as a tool for discussion and navigation on Implementation, Mitigation, Strategies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 F451 Implementation Steps Mitigation Data From Another Crm System Crm Implementation Process
F451 Implementation Steps Mitigation Data From Another Crm System Crm Implementation ProcessThis slide covers different strategies for mitigating data from other CRM software. It includes options such as exporting data from the data folder or attached folder. Deliver an outstanding presentation on the topic using this F451 Implementation Steps Mitigation Data From Another Crm System Crm Implementation Process. Dispense information and present a thorough explanation of Mitigation, Attachment, Implementation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
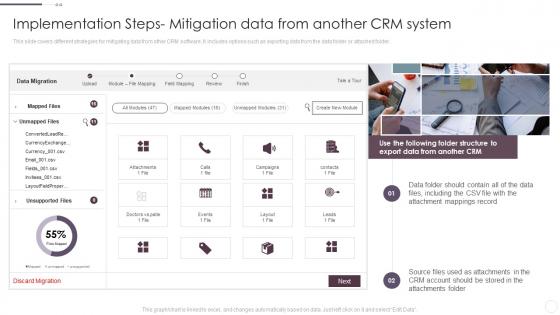 Implementation Steps Mitigation Data From Another Crm System Implementation Guide For Businesses
Implementation Steps Mitigation Data From Another Crm System Implementation Guide For BusinessesThis slide covers different strategies for mitigating data from other CRM software. It includes options such as exporting data from the data folder or attached folder. Present the topic in a bit more detail with this Implementation Steps Mitigation Data From Another Crm System Implementation Guide For Businesses. Use it as a tool for discussion and navigation on Implementation, Mitigation, Attachment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
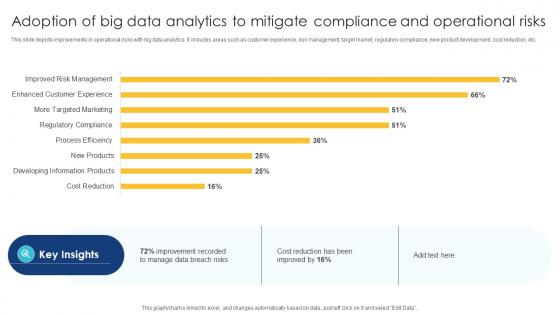 Adoption Of Big Data Analytics To Mitigate Compliance And Operational Risks
Adoption Of Big Data Analytics To Mitigate Compliance And Operational RisksThis slide depicts improvements in operational risks with big data analytics. It includes areas such as customer experience, risk management, target market, regulatory compliance, new product development, cost reduction, etc. Introducing our Adoption Of Big Data Analytics To Mitigate Compliance And Operational Risks set of slides. The topics discussed in these slides are Adoption Of Big Data, Analytics To Mitigate, Compliance And Operational Risks. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
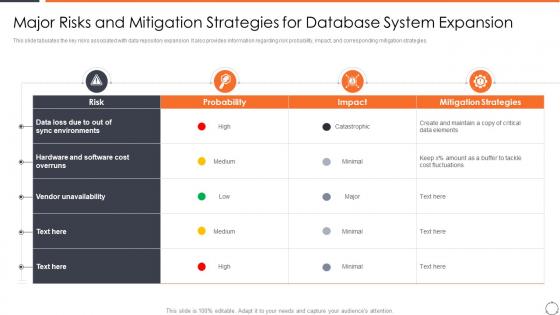 Major Risks And Mitigation Strategies Horizontal Scaling Approach Data Management System
Major Risks And Mitigation Strategies Horizontal Scaling Approach Data Management SystemThis slide tabulates the key risks associated with data repository expansion. It also provides information regarding risk probability, impact, and corresponding mitigation strategies. Present the topic in a bit more detail with this Major Risks And Mitigation Strategies Horizontal Scaling Approach Data Management System. Use it as a tool for discussion and navigation on Major Risks And Mitigation Strategies For Database System Expansion. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
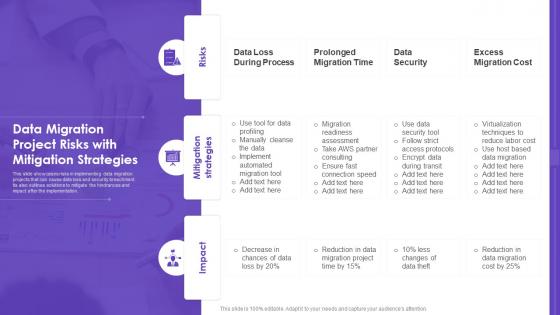 Data Migration Project Risks With Mitigation Strategies
Data Migration Project Risks With Mitigation StrategiesThis slide showcases risks in implementing data migration projects that can cause data loss and security breachment. Its also outlines solutions to mitigate the hindrances and impact after the implementation. Presenting our well structured Data Migration Project Risks With Mitigation Strategies. The topics discussed in this slide are Mitigation Strategies, Migration Time, Data Security. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Data storage system optimization action plan major risks and mitigation strategies for database system expansion
Data storage system optimization action plan major risks and mitigation strategies for database system expansionThis slide tabulates the key risks associated with data repository expansion. It also provides information regarding risk probability, impact, and corresponding mitigation strategies. Deliver an outstanding presentation on the topic using this Data Storage System Optimization Action Plan Major Risks And Mitigation Strategies For Database System Expansion. Dispense information and present a thorough explanation of Mitigation, Strategies, Database using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Scale out strategy for data inventory system major risks and mitigation strategies
Scale out strategy for data inventory system major risks and mitigation strategiesPresent the topic in a bit more detail with this Scale Out Strategy For Data Inventory System Major Risks And Mitigation Strategies. Use it as a tool for discussion and navigation on Environments, Strategies, Expansion. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
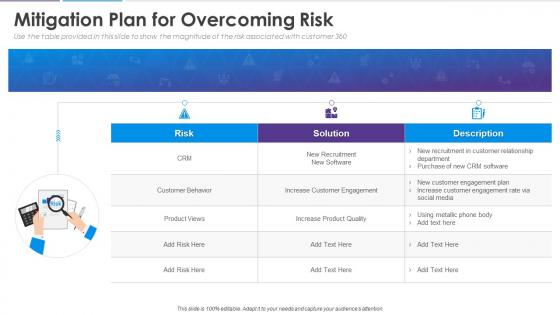 Analyzing customer journey and data from 360 degree mitigation plan for overcoming risk
Analyzing customer journey and data from 360 degree mitigation plan for overcoming riskUse the table provided in this slide to show the magnitude of the risk associated with customer 360 Deliver an outstanding presentation on the topic using this Analyzing Customer Journey And Data From 360 Degree Mitigation Plan For Overcoming Risk. Dispense information and present a thorough explanation of Mitigation Plan For Overcoming Risk using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
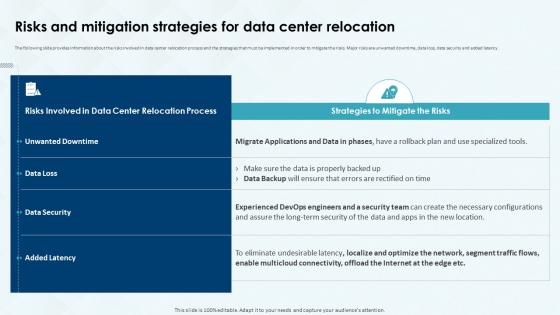 Risks And Mitigation Strategies For Data Center Relocation Costs And Benefits Of Data Center
Risks And Mitigation Strategies For Data Center Relocation Costs And Benefits Of Data CenterThe following slide provides information about the risks involved in data center relocation process and the strategies that must be implemented in order to mitigate the risks. Major risks are unwanted downtime, data loss, data security and added latency. Deliver an outstanding presentation on the topic using this Risks And Mitigation Strategies For Data Center Relocation Costs And Benefits Of Data Center. Dispense information and present a thorough explanation of Risks And Mitigation, Strategies, Data Center Relocation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Existing Data Center Assessment And Process Risks And Mitigation Strategies For Data Center Relocation
Existing Data Center Assessment And Process Risks And Mitigation Strategies For Data Center RelocationThe following slide provides information about the risks involved in data center relocation process and the strategies that must be implemented in order to mitigate the risks. Major risks are unwanted downtime, data loss, data security and added latency. Deliver an outstanding presentation on the topic using this Existing Data Center Assessment And Process Risks And Mitigation Strategies For Data Center Relocation. Dispense information and present a thorough explanation of Risks And Mitigation, Data Center Relocation, Multicloud Connectivity using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
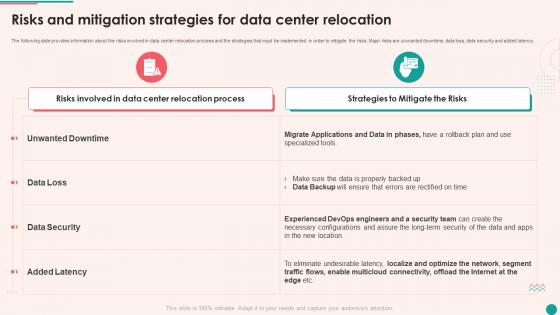
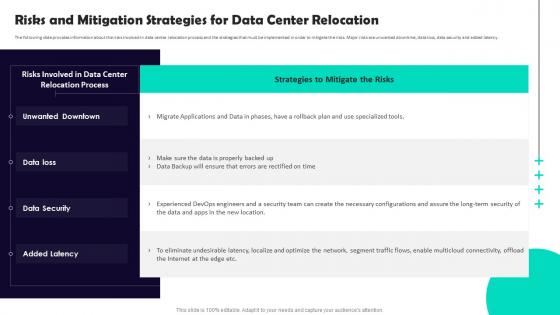 Data Center Relocation Process Risks And Mitigation Strategies For Data Center Relocation
Data Center Relocation Process Risks And Mitigation Strategies For Data Center RelocationThe following slide provides information about the risks involved in data center relocation process and the strategies that must be implemented in order to mitigate the risks. Major risks are unwanted downtime, data loss, data security and added latency. Present the topic in a bit more detail with this Data Center Relocation Process Risks And Mitigation Strategies For Data Center Relocation. Use it as a tool for discussion and navigation on Unwanted Downtown, Data Loss, Data Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
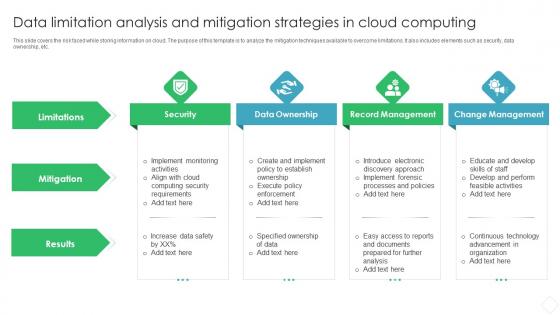 Data Limitation Analysis And Mitigation Strategies In Cloud Computing
Data Limitation Analysis And Mitigation Strategies In Cloud ComputingThis slide covers the risk faced while storing information on cloud. The purpose of this template is to analyze the mitigation techniques available to overcome limitations. It also includes elements such as security, data. Presenting our set of slides with name Data Limitation Analysis And Mitigation Strategies In Cloud Computing. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security, Data Ownership, Record Management.
-
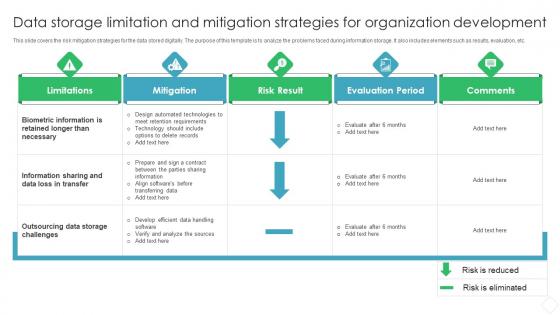 Data Storage Limitation And Mitigation Strategies For Organization Development
Data Storage Limitation And Mitigation Strategies For Organization DevelopmentThis slide covers the risk mitigation strategies for the data stored digitally. The purpose of this template is to analyze the problems faced during information storage. It also includes elements such as results, evaluation, etc. Presenting our well structured Data Storage Limitation And Mitigation Strategies For Organization Development. The topics discussed in this slide are Limitations, Mitigation, Risk Result. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
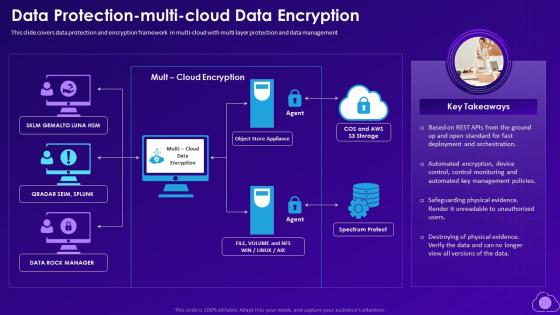 Data Protection Multi Cloud Data Encryption Mitigating Multi Cloud Complexity With Managed Services
Data Protection Multi Cloud Data Encryption Mitigating Multi Cloud Complexity With Managed ServicesThis slide covers data protection and encryption framework in multi cloud with multi layer protection and data management. Increase audience engagement and knowledge by dispensing information using Data Protection Multi Cloud Data Encryption Mitigating Multi Cloud Complexity With Managed Services. This template helps you present information on one stages. You can also present information on Spectrum Protect, Data Rock Manager, Object Store Appliance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
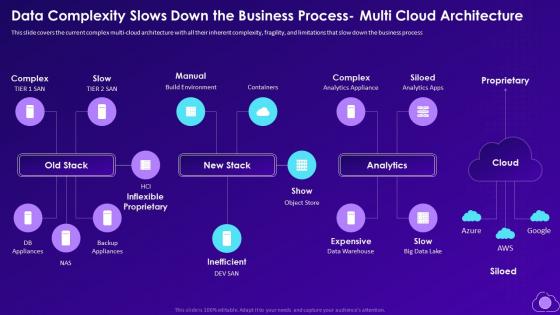 Mitigating Multi Cloud Complexity Data Complexity Slows Down The Business Process Multi Cloud Architecture
Mitigating Multi Cloud Complexity Data Complexity Slows Down The Business Process Multi Cloud ArchitectureThis slide covers the current complex multi cloud architecture with all their inherent complexity, fragility, and limitations that slow down the business process. Present the topic in a bit more detail with this Mitigating Multi Cloud Complexity Data Complexity Slows Down The Business Process Multi Cloud Architecture. Use it as a tool for discussion and navigation on Build Environment, Analytics Appliance, Inflexible Proprietary. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Migration Challenges With Mitigation Strategies
Data Migration Challenges With Mitigation StrategiesThe given below slide highlights the major challenges in migrating data from one system to another. It includes activities such as data quality concerns, inaccessibility of data along with mitigation techniques etc. Introducing our Data Migration Challenges With Mitigation Strategies set of slides. The topics discussed in these slides are Data Quality Concerns, Data Reconciliation, Inappropriate Data, Target System. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.


