Powerpoint Templates and Google slides for Data Security Strategy Icon
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Data security it impact on organization after implementing data security strategy
Data security it impact on organization after implementing data security strategyThis slide depicts the impact of data security training on an organization. It also shows how trained employees can reduce cyber attacks in the organization. Deliver an outstanding presentation on the topic using this Data Security IT Impact On Organization After Implementing Data Security Strategy. Dispense information and present a thorough explanation of Phishing, Network Intrusion, Inadvertent Disclosure, System Misconfiguration using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
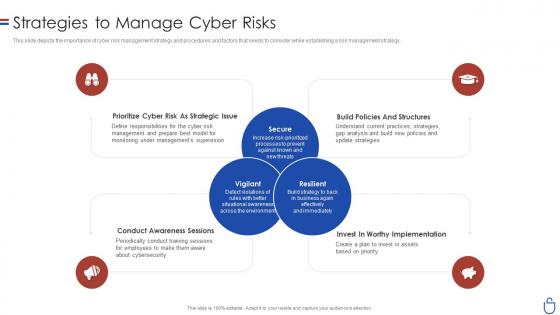 Data security it strategies to manage cyber risks ppt slides clipart images
Data security it strategies to manage cyber risks ppt slides clipart imagesThis slide depicts the importance of cyber risk management strategy and procedures and factors that needs to consider while establishing a risk management strategy. Introducing Data Security IT Strategies To Manage Cyber Risks Ppt Slides Clipart Images to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Prioritize Cyber Risk As Strategic Issue, Conduct Awareness Sessions, Invest Worthy Implementation, Build Policies And Structures, using this template. Grab it now to reap its full benefits.
-
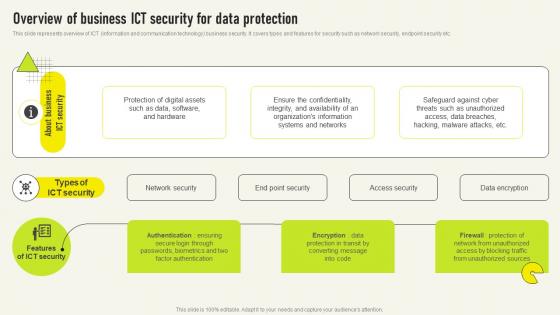 Overview Of Business Ict Security For Data Comprehensive Guide For Deployment Strategy SS V
Overview Of Business Ict Security For Data Comprehensive Guide For Deployment Strategy SS VThis slide represents overview of ICT information and communication technology business security It covers types and features for security such as network security, endpoint security etc Present the topic in a bit more detail with this Overview Of Business Ict Security For Data Comprehensive Guide For Deployment Strategy SS V Use it as a tool for discussion and navigation on Unauthorized Sources, Factor Authentication, Organizations Information This template is free to edit as deemed fit for your organization Therefore download it now
-
 Business Expansion And Data Security Strategy Icon
Business Expansion And Data Security Strategy IconIntroducing our premium set of slides with Business Expansion And Data Security Strategy Icon. Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Business Expansion, Data Security Strategy Icon. So download instantly and tailor it with your information.
-
 Key Strategies To Secure Business Data
Key Strategies To Secure Business DataThis slide showcase strategies that can be used for securing cyberattacks and target organizational data security and access. It includes updating devices, secure iot technology, track cloud storage, train employees and secure network access. Introducing our premium set of slides with Key Strategies To Secure Business Data. Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Updated Devices, Track Cloud Storage, Train Employees. So download instantly and tailor it with your information.
-
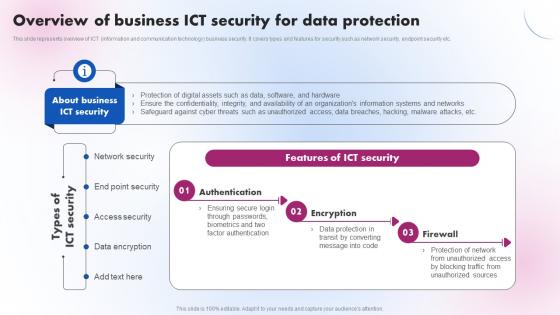 Overview Of Business ICT Security For Data Elivering ICT Services For Enhanced Business Strategy SS V
Overview Of Business ICT Security For Data Elivering ICT Services For Enhanced Business Strategy SS VThis slide represents overview of ICT information and communication technology business security. It covers types and features for security such as network security, endpoint security etc. Increase audience engagement and knowledge by dispensing information using Overview Of Business ICT Security For Data Elivering ICT Services For Enhanced Business Strategy SS V. This template helps you present information on three stages. You can also present information on Authentication, Encryption, Firewall using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
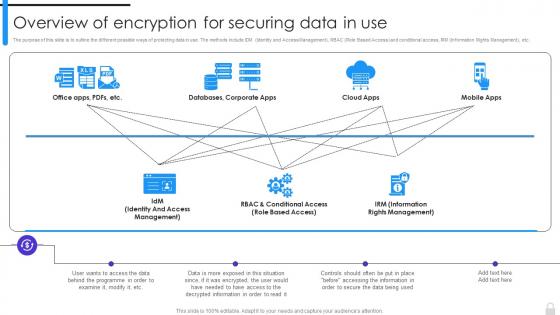 Encryption Implementation Strategies Overview Of Encryption For Securing Data In Use
Encryption Implementation Strategies Overview Of Encryption For Securing Data In UseThe purpose of this slide is to outline the different possible ways of protecting data in use. The methods include IDM Identity and Access Management, RBAC Role Based Access and conditional access, IRM Information Rights Management, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Overview Of Encryption For Securing Data In Use. Dispense information and present a thorough explanation of Information Rights Management, Encryption For Securing Data, Role Based Access using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
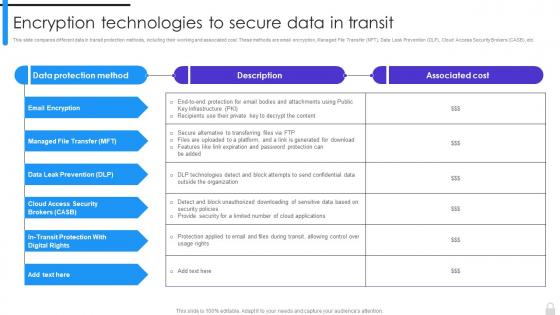 Encryption Technologies To Secure Data In Transit Encryption Implementation Strategies
Encryption Technologies To Secure Data In Transit Encryption Implementation StrategiesThis slide compares different data in transit protection methods, including their working and associated cost. These methods are email encryption, Managed File Transfer MFT, Data Leak Prevention DLP, Cloud Access Security Brokers CASB, etc. Deliver an outstanding presentation on the topic using this Encryption Technologies To Secure Data In Transit Encryption Implementation Strategies. Dispense information and present a thorough explanation of Managed File Transfer, Cloud Access Security Brokers, Email Encryption, Encryption Technologies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
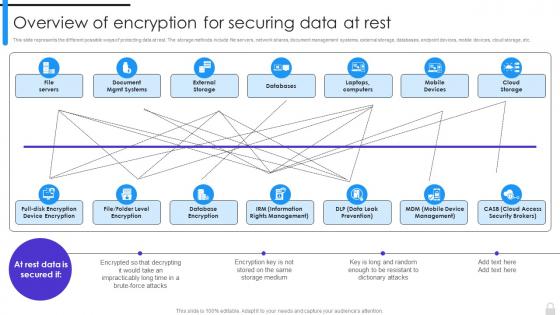 Overview Of Encryption For Securing Data At Rest Encryption Implementation Strategies
Overview Of Encryption For Securing Data At Rest Encryption Implementation StrategiesThis slide represents the different possible ways of protecting data at rest. The storage methods include file servers, network shares, document management systems, external storage, databases, endpoint devices, mobile devices, cloud storage, etc. Present the topic in a bit more detail with this Overview Of Encryption For Securing Data At Rest Encryption Implementation Strategies. Use it as a tool for discussion and navigation on Database Encryption, Information Rights Management, Data Leak Prevention, Mobile Device Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
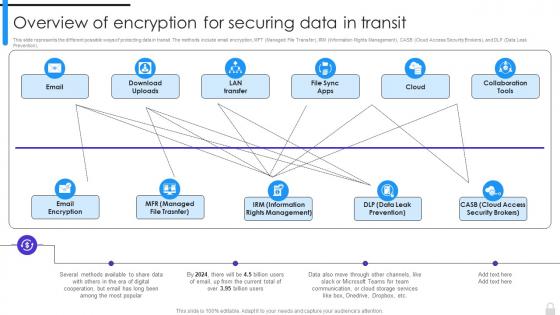 Overview Of Encryption For Securing Data In Transit Encryption Implementation Strategies
Overview Of Encryption For Securing Data In Transit Encryption Implementation StrategiesThis slide represents the different possible ways of protecting data in transit. The methods include email encryption, MFT Managed File Transfer, IRM Information Rights Management, CASB Cloud Access Security Brokers, and DLP Data Leak Prevention. Deliver an outstanding presentation on the topic using this Overview Of Encryption For Securing Data In Transit Encryption Implementation Strategies. Dispense information and present a thorough explanation of Information Rights Management, Data Leak Prevention, Cloud Access Security Brokers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
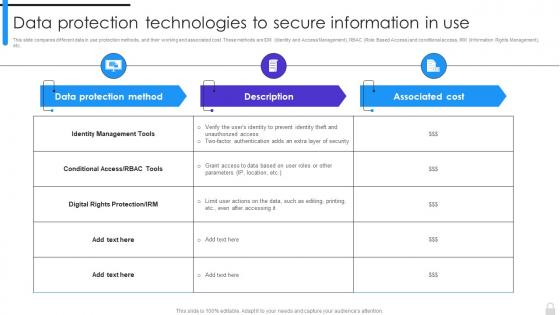 Encryption Implementation Strategies Data Protection Technologies To Secure Information In Use
Encryption Implementation Strategies Data Protection Technologies To Secure Information In UseThis slide compares different data in use protection methods, and their working and associated cost. These methods are IDM Identity and Access Management, RBAC Role Based Access and conditional access, IRM Information Rights Management, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Data Protection Technologies To Secure Information In Use. Use it as a tool for discussion and navigation on Identity Management Tools, Digital Rights Protection, Data Protection Technologies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
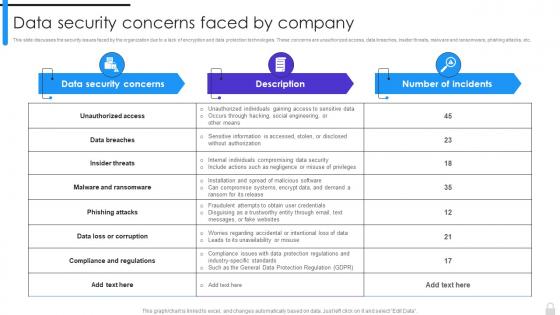 Encryption Implementation Strategies Data Security Concerns Faced By Company
Encryption Implementation Strategies Data Security Concerns Faced By CompanyThis slide discusses the security issues faced by the organization due to a lack of encryption and data protection technologies. These concerns are unauthorized access, data breaches, insider threats, malware and ransomware, phishing attacks, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Data Security Concerns Faced By Company. Dispense information and present a thorough explanation of Data Security Concerns, Phishing Attacks, Data Protection Technologies, Compliance And Regulations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
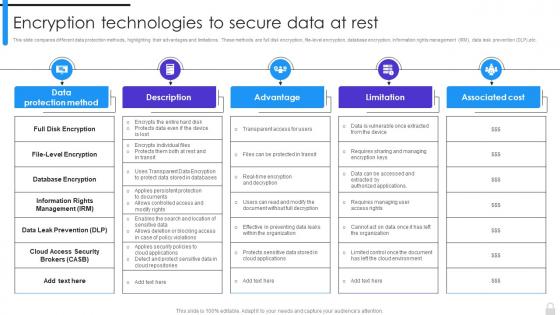 Encryption Implementation Strategies Encryption Technologies To Secure Data At Rest
Encryption Implementation Strategies Encryption Technologies To Secure Data At RestThis slide compares different data protection methods, highlighting their advantages and limitations. These methods are full disk encryption, file-level encryption, database encryption, information rights management IRM, data leak prevention DLP,etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Encryption Technologies To Secure Data At Rest. Dispense information and present a thorough explanation of Information Rights Management, Data Leak Prevention, Full Disk Encryption, Cloud Access Security Brokers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
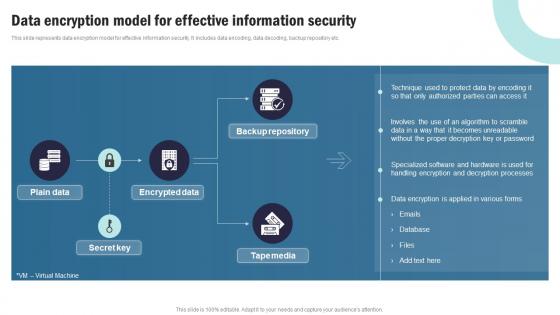 Strategic Plan To Implement Data Encryption Model For Effective Information Security Strategy SS V
Strategic Plan To Implement Data Encryption Model For Effective Information Security Strategy SS VThis slide represents data encryption model for effective information security. It includes data encoding, data decoding, backup repository etc. Present the topic in a bit more detail with this Strategic Plan To Implement Data Encryption Model For Effective Information Security Strategy SS V Use it as a tool for discussion and navigation on Employee Headcount, Average Employee Age, Gender Diversity Ratio This template is free to edit as deemed fit for your organization. Therefore download it now.
-
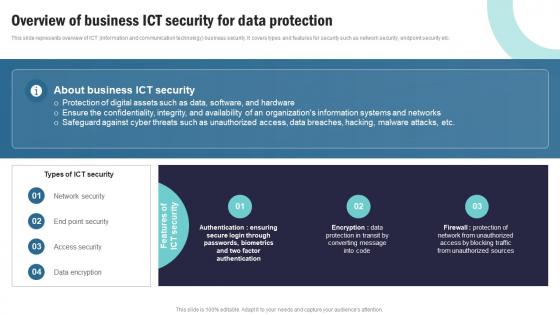 Strategic Plan To Implement Overview Of Business Ict Security For Data Protection Strategy SS V
Strategic Plan To Implement Overview Of Business Ict Security For Data Protection Strategy SS VThis slide represents overview of ICT information and communication technology business security. It covers types and features for security such as network security, endpoint security etc. Introducing Strategic Plan To Implement Overview Of Business Ict Security For Data Protection Strategy SS V to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Incident Management, Request Fulfillment using this template. Grab it now to reap its full benefits.
-
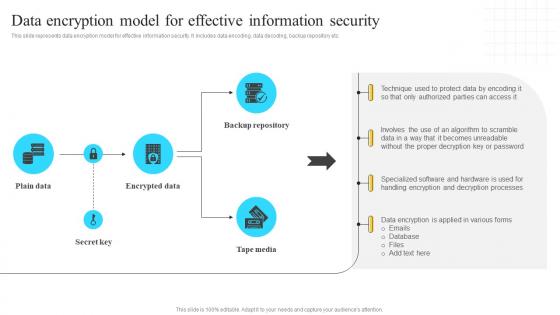 Implementation Of Information Data Encryption Model For Effective Information Security Strategy SS V
Implementation Of Information Data Encryption Model For Effective Information Security Strategy SS VThis slide represents data encryption model for effective information security. It includes data encoding, data decoding, backup repository etc. Present the topic in a bit more detail with this Implementation Of Information Data Encryption Model For Effective Information Security Strategy SS V. Use it as a tool for discussion and navigation on Backup Repository, Encrypted Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
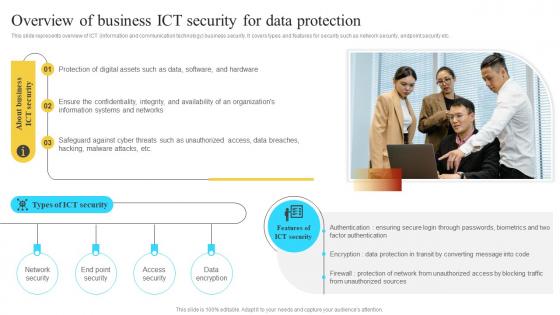 Implementation Of Information Overview Of Business Ict Security For Data Protection Strategy SS V
Implementation Of Information Overview Of Business Ict Security For Data Protection Strategy SS VThis slide represents overview of ICT information and communication technology business security. It covers types and features for security such as network security, endpoint security etc. Introducing Implementation Of Information Overview Of Business Ict Security For Data Protection Strategy SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Protection Of Digital, Safeguard Against Cyber, using this template. Grab it now to reap its full benefits.
-
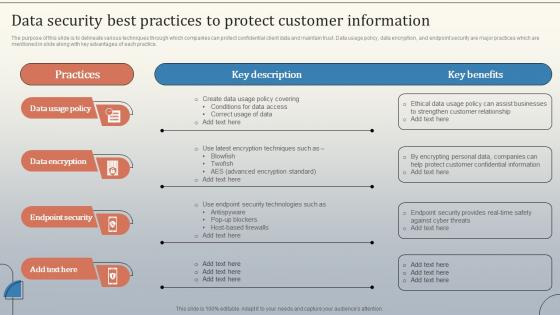 Data Security Best Practices To Protect Customer Database Marketing Strategies MKT SS V
Data Security Best Practices To Protect Customer Database Marketing Strategies MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Introducing Data Security Best Practices To Protect Customer Database Marketing Strategies MKT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Data Usage Policy, Data Encryption, using this template. Grab it now to reap its full benefits.
-
 Fortify Cyber Security By Using Big Data Strategies
Fortify Cyber Security By Using Big Data StrategiesThis slide contains strategies to fortify cyber security using big data. Its aim is to predict future anomalies and detect frauds in cyber security. This slide includes automated monitoring, real time protection. Presenting our set of slides with Fortify Cyber Security By Using Big Data Strategies. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Predict, Detection, Monitoring.
-
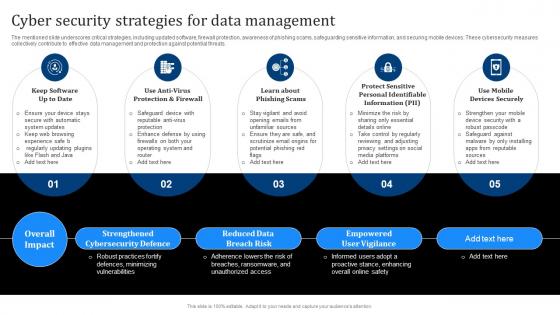 Cyber Security Strategies For Data Management
Cyber Security Strategies For Data ManagementThe mentioned slide underscores critical strategies, including updated software, firewall protection, awareness of phishing scams, safeguarding sensitive information, and securing mobile devices. These cybersecurity measures collectively contribute to effective data management and protection against potential threats. Introducing our premium set of slides with Cyber Security Strategies For Data Management. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Keep Software Up To Date, Reduced Data Breach Risk, Empowered User Vigilance. So download instantly and tailor it with your information.
-
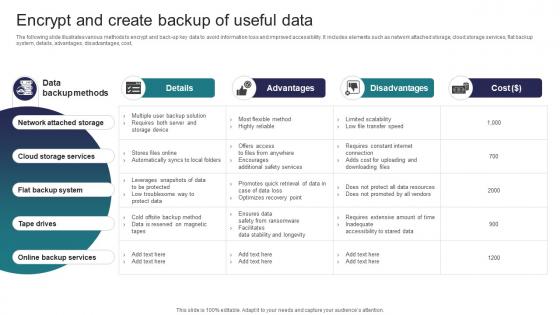 Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security Threats
Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide illustrates various methods to encrypt and back up key data to avoid information loss and improved accessibility. It includes elements such as network attached storage, cloud storage services, flat backup system, details, advantages, disadvantages, cost, Deliver an outstanding presentation on the topic using this Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Network Attached Storage, Cloud Storage Services, Flat Backup System using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
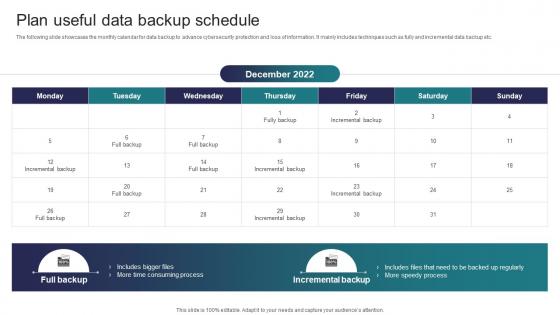 Plan Useful Data Backup Schedule Implementing Strategies To Mitigate Cyber Security Threats
Plan Useful Data Backup Schedule Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases the monthly calendar for data backup to advance cybersecurity protection and loss of information. It mainly includes techniques such as fully and incremental data backup etc. Increase audience engagement and knowledge by dispensing information using Plan Useful Data Backup Schedule Implementing Strategies To Mitigate Cyber Security Threats This template helps you present information on one stages. You can also present information on Time Consuming Process, Speedy Process, Incremental Backup using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
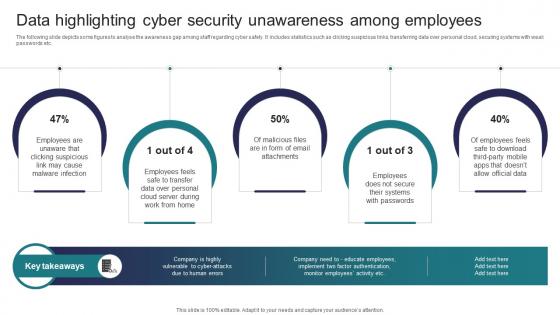 Implementing Strategies To Mitigate Cyber Security Data Highlighting Cyber Security Unawareness Among
Implementing Strategies To Mitigate Cyber Security Data Highlighting Cyber Security Unawareness AmongThe following slide depicts some figures to analyse the awareness gap among staff regarding cyber safety. It includes statistics such as clicking suspicious links, transferring data over personal cloud, securing systems with weak passwords etc. Introducing Implementing Strategies To Mitigate Cyber Security Data Highlighting Cyber Security Unawareness Among to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Email Attachments, Systems, Employees using this template. Grab it now to reap its full benefits.
-
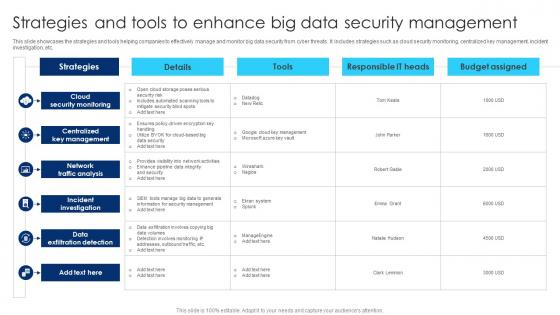 Strategies And Tools To Enhance Big Data Security Management
Strategies And Tools To Enhance Big Data Security ManagementThis slide showcases the strategies and tools helping companies to effectively manage and monitor big data security from cyber threats. It includes strategies such as cloud security monitoring, centralized key management, incident investigation, etc. Introducing our Strategies And Tools To Enhance Big Data Security Management set of slides. The topics discussed in these slides are Cloud Security Monitoring, Centralized Key Management, Network Traffic Analysis. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
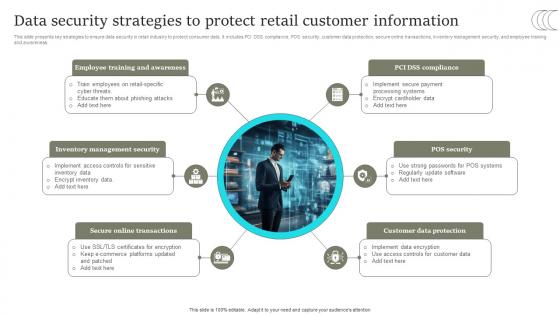 Data Security Strategies To Protect Retail Customer Comprehensive Retail Transformation DT SS
Data Security Strategies To Protect Retail Customer Comprehensive Retail Transformation DT SSThis slide presents key strategies to ensure data security in retail industry to protect consumer data. It includes PCI DSS compliance, POS security, customer data protection, secure online transactions, inventory management security, and employee training and awareness. Present the topic in a bit more detail with this Data Security Strategies To Protect Retail Customer Comprehensive Retail Transformation DT SS. Use it as a tool for discussion and navigation on Online Transactions, Customer Data Protection, POS Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Security Strategies To Protect Retail Customer Digital Transformation Of Retail DT SS
Data Security Strategies To Protect Retail Customer Digital Transformation Of Retail DT SSThis slide presents key strategies to ensure data security in retail industry to protect consumer data. It includes PCI DSS compliance, POS security, customer data protection, secure online transactions, inventory management security, and employee training and awareness. Increase audience engagement and knowledge by dispensing information using Data Security Strategies To Protect Retail Customer Digital Transformation Of Retail DT SS This template helps you present information on six stages. You can also present information on Customer Data Protection, Online Transactions, Management Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
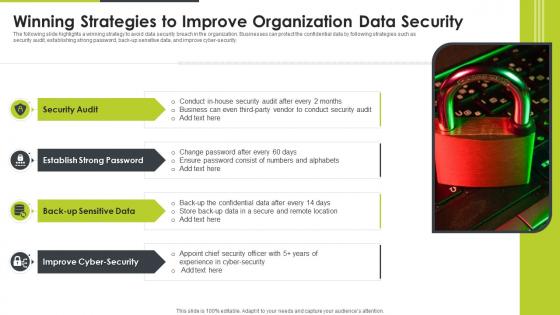 Winning Strategies To Improve Organization Data Security
Winning Strategies To Improve Organization Data SecurityThe following slide highlights a winning strategy to avoid data security breach in the organization. Businesses can protect the confidential data by following strategies such as security audit, establishing strong password, back up sensitive data, and improve cyber-security. Introducing our premium set of slides with Winning Strategies To Improve Organization Data Security. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security Audit, Improve Cyber Security, Back Up Sensitive Data. So download instantly and tailor it with your information.
-
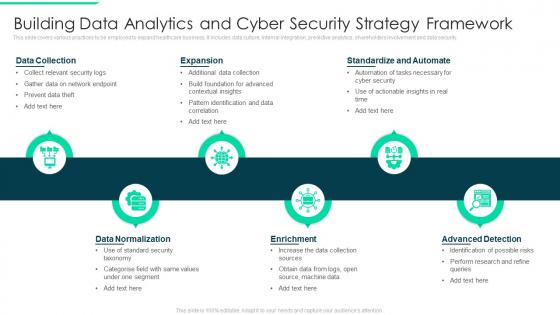 Building Data Analytics And Cyber Security Strategy Framework
Building Data Analytics And Cyber Security Strategy FrameworkThis slide covers various practices to be employed to expand healthcare business. It includes data culture, internal integration, predictive analytics, shareholders involvement and data security. Introducing our premium set of slides with Building Data Analytics And Cyber Security Strategy Framework. Elucidate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Collection, Data Normalization, Expansion. So download instantly and tailor it with your information.
-
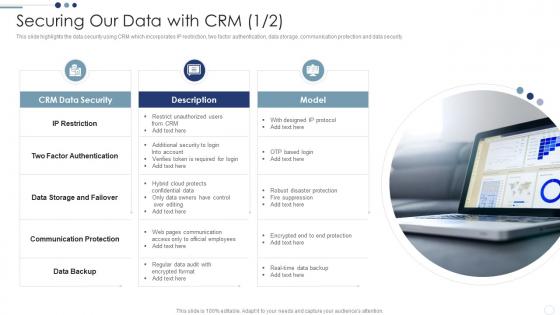 Securing Our Data With CRM Customer Relationship Management Deployment Strategy
Securing Our Data With CRM Customer Relationship Management Deployment StrategyThis slide highlights the data security using CRM which incorporates IP restriction, two factor authentication, data storage, communication protection and data security.Increase audience engagement and knowledge by dispensing information using Securing Our Data With CRM Customer Relationship Management Deployment Strategy This template helps you present information on three stages. You can also present information on Factor Authentication, Storage And Failover, Communication Protection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
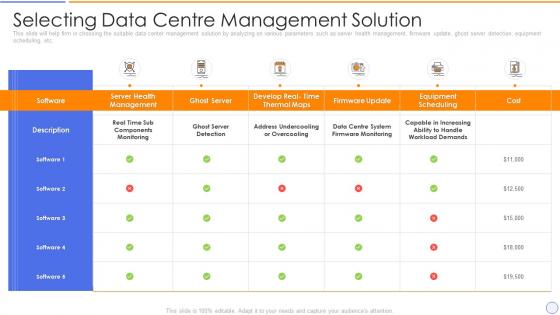 Building organizational security strategy plan selecting data centre management solution
Building organizational security strategy plan selecting data centre management solutionThis slide will help firm in choosing the suitable data center management solution by analyzing on various parameters such as server health management, firmware update, ghost server detection, equipment scheduling, etc. Deliver an outstanding presentation on the topic using this Building Organizational Security Strategy Plan Selecting Data Centre Management Solution. Dispense information and present a thorough explanation of Equipment, Management, Solution using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
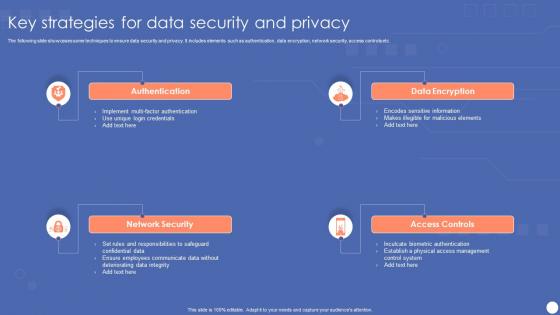 Key Strategies For Data Security And Privacy
Key Strategies For Data Security And PrivacyThe following slide showcases some techniques to ensure data security and privacy. It includes elements such as authentication, data encryption, network security, access controls etc. Introducing our premium set of slides with name Key Strategies For Data Security And Privacy. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Authentication, Network Security, Data Encryption, Access Controls. So download instantly and tailor it with your information.
-
 Security Fundamentals For Cloud Data Storage Strategy
Security Fundamentals For Cloud Data Storage StrategyThis slide provides security fundamentals for cloud data storage to provide safe access to files by avoiding hackers and malware. It covers six fundamentals redundance and availability, ensure and monitor data security, permissions, unique naming and encryption Presenting our set of slides with Security Fundamentals For Cloud Data Storage Strategy. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security, Fundamentals, Strategy.
-
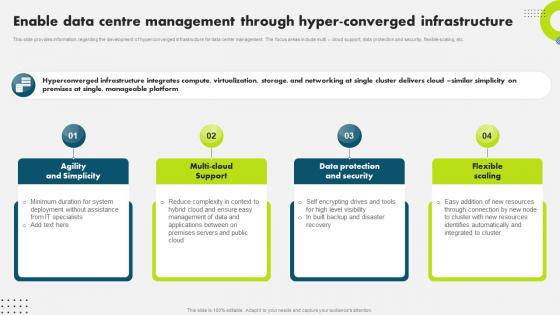 Enable Data Centre Management Through Hyper Strategic Plan To Secure It Infrastructure Strategy SS V
Enable Data Centre Management Through Hyper Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding the development of hyperconverged infrastructure for data center management. The focus areas include multi cloud support, data protection and security, flexible scaling, etc. Present the topic in a bit more detail with this Enable Data Centre Management Through Hyper Strategic Plan To Secure It Infrastructure Strategy SS V. Use it as a tool for discussion and navigation on Management, Infrastructure, Agility And Simplicity . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
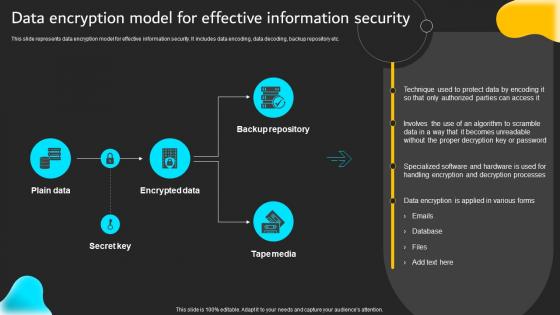 Data Encryption Model For Effective Information Security Strategy SS
Data Encryption Model For Effective Information Security Strategy SSThis slide represents data encryption model for effective information security. It includes data encoding, data decoding, backup repository etc.Present the topic in a bit more detail with this Data Encryption Model For Effective Information Security Strategy SS. Use it as a tool for discussion and navigation on Backup Repository, Encrypted Data, Proper Decryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
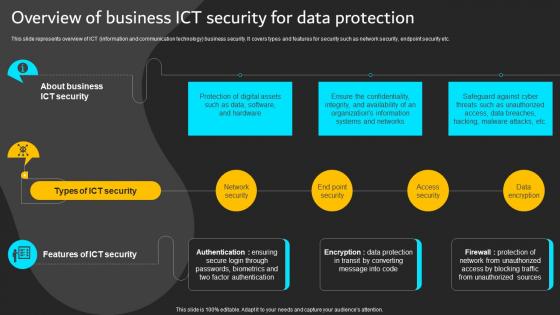 Overview Of Business ICT Security Data Protection Implementation ICT Strategic Plan Strategy SS
Overview Of Business ICT Security Data Protection Implementation ICT Strategic Plan Strategy SSThis slide represents overview of ICT information and communication technology business security. It covers types and features for security such as network security, endpoint security etc.Present the topic in a bit more detail with this Overview Of Business ICT Security Data Protection Implementation ICT Strategic Plan Strategy SS. Use it as a tool for discussion and navigation on Factor Authentication, Organizations Information, Ensure Confidentiality. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
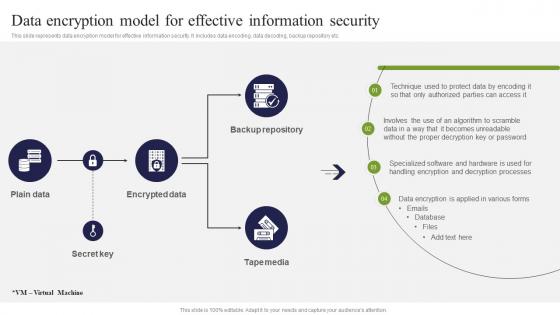 Data Encryption Model For Effective Information Security ICT Strategic Framework Strategy SS V
Data Encryption Model For Effective Information Security ICT Strategic Framework Strategy SS VThis slide represents data encryption model for effective information security. It includes data encoding, data decoding, backup repository etc. Deliver an outstanding presentation on the topic using this Data Encryption Model For Effective Information Security ICT Strategic Framework Strategy SS V. Dispense information and present a thorough explanation of Encrypted Data, Backup Repository, Tape Media, Secret Key using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
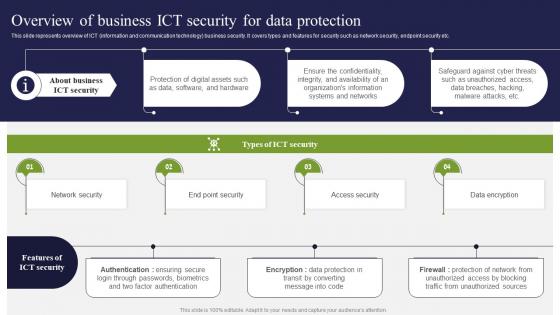 Overview Of Business ICT Security For Data Protection ICT Strategic Framework Strategy SS V
Overview Of Business ICT Security For Data Protection ICT Strategic Framework Strategy SS VThis slide represents overview of ICT information and communication technology business security. It covers types and features for security such as network security, endpoint security etc. Present the topic in a bit more detail with this Overview Of Business ICT Security For Data Protection ICT Strategic Framework Strategy SS V. Use it as a tool for discussion and navigation on Network Security, Access Security, Data Encryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data security strategies powerpoint ideas
Data security strategies powerpoint ideasIntroducing data security strategies PPT design. Fully regulated PowerPoint template quite reasonable for the management professionals and business specialists. Extensive scope for reviving the dummy data and can add company logo, trademark etc. Reconvert able background PPT images, subject matter, designs, context etc. according to need. Versant with all Google Slides and other system applications. Can be easily projected over wide screen with exceptional picture quality.
-
 Enterprise security strategy roadmap data architecture business analytics
Enterprise security strategy roadmap data architecture business analyticsPresenting this set of slides with name - Enterprise Security Strategy Roadmap Data Architecture Business Analytics. This is an editable four stages graphic that deals with topics like Enterprise Security, Strategy Roadmap, Data Architecture, Business Analytics to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
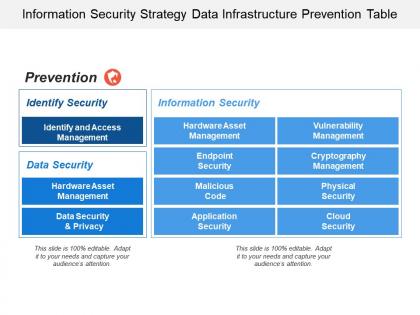 Information security strategy data infrastructure prevention table
Information security strategy data infrastructure prevention tablePresenting this set of slides with name - Information Security Strategy Data Infrastructure Prevention Table. This is a two stage process. The stages in this process are Information Security Strategy, Information Security Plan, Information Protection Strategy.
-
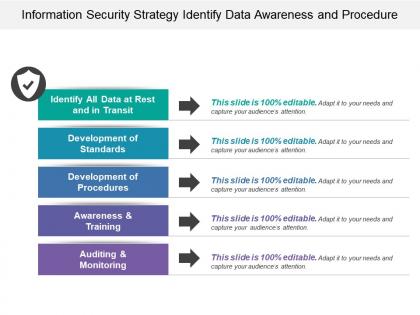 Information security strategy identify data awareness and procedure
Information security strategy identify data awareness and procedurePresenting this set of slides with name - Information Security Strategy Identify Data Awareness And Procedure. This is a five stage process. The stages in this process are Information Security Strategy, Information Security Plan, Information Protection Strategy.
-
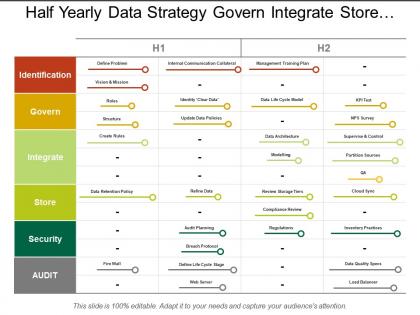 Half yearly data strategy govern integrate store security swim lane
Half yearly data strategy govern integrate store security swim lanePresenting this set of slides with name - Half Yearly Data Strategy Govern Integrate Store Security Swim Lane. This is a two stage process. The stages in this process are Data Management For Data Strategy Swim Lane, Data Management For Data Plan Swim Lane, Data Management For Data Approach Swim Lane.
-
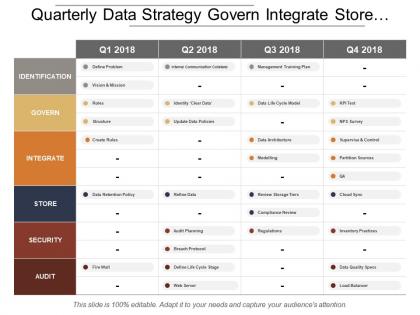 Quarterly data strategy govern integrate store security swim lane
Quarterly data strategy govern integrate store security swim lanePresenting this set of slides with name - Quarterly Data Strategy Govern Integrate Store Security Swim Lane. This is a four stage process. The stages in this process are Data Management For Data Strategy Swim Lane, Data Management For Data Plan Swim Lane, Data Management For Data Approach Swim Lane.
-
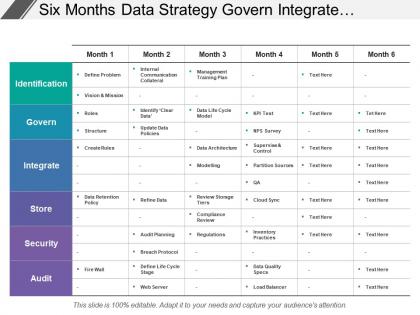 Six months data strategy govern integrate store security swim lane
Six months data strategy govern integrate store security swim lanePresenting this set of slides with name - Six Months Data Strategy Govern Integrate Store Security Swim Lane. This is a six stage process. The stages in this process are Data Management For Data Strategy Swim Lane, Data Management For Data Plan Swim Lane, Data Management For Data Approach Swim Lane.
-
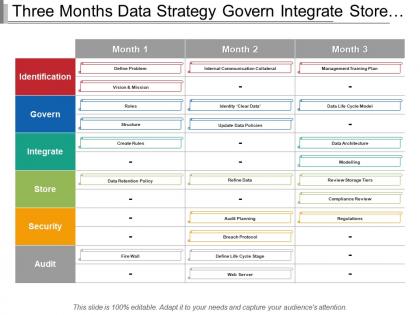 Three months data strategy govern integrate store security swim lane
Three months data strategy govern integrate store security swim lanePresenting this set of slides with name - Three Months Data Strategy Govern Integrate Store Security Swim Lane. This is a three stage process. The stages in this process are Data Management For Data Strategy Swim Lane, Data Management For Data Plan Swim Lane, Data Management For Data Approach Swim Lane.
-
 Yearly data strategy govern integrate store security swim lane
Yearly data strategy govern integrate store security swim lanePresenting this set of slides with name - Yearly Data Strategy Govern Integrate Store Security Swim Lane. This is a five stage process. The stages in this process are Data Management For Data Strategy Swim Lane, Data Management For Data Plan Swim Lane, Data Management For Data Approach Swim Lane.
-
 Finance business collaboration corporate business data security business strategy cpb
Finance business collaboration corporate business data security business strategy cpbPresenting this set of slides with name - Finance Business Collaboration Corporate Business Data Security Business Strategy Cpb. This is an editable three stages graphic that deals with topics like Finance, Business, Collaboration, Corporate, Business, Data, Security, Business, Strategy to help convey your message better graphically. This product is a premium product available for immediate download,and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Security consulting data web strategy generate traffic services partners ppt icons graphics
Security consulting data web strategy generate traffic services partners ppt icons graphicsPresenting security consulting data web strategy generate traffic services partners ppt icons graphics. This Power Point icon template diagram has been crafted with graphic of four technical icons. This icon template contains the concept of generating traffic and web consulation.Use this icon template for business and technology related presentations.
-
 Defining your data security strategy plan ppt powerpoint presentation styles
Defining your data security strategy plan ppt powerpoint presentation stylesPresenting this set of slides with name Defining Your Data Security Strategy Plan Ppt Powerpoint Presentation Styles. This is a two stage process. The stages in this process are Data Security Incident, Security Strategy Elements, Assigning Responsibility, Plan. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Defining your data security strategy ppt powerpoint presentation inspiration aids
Defining your data security strategy ppt powerpoint presentation inspiration aidsPresenting this set of slides with name Defining Your Data Security Strategy Ppt Powerpoint Presentation Inspiration Aids. This is a three stage process. The stages in this process are Identify All The It Assets In Your Network, Assess Your Risks, Set Up Policies For Managing Information Access. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Keys to data security strategy ppt powerpoint presentation styles examples
Keys to data security strategy ppt powerpoint presentation styles examplesPresenting this set of slides with name Keys To Data Security Strategy Ppt Powerpoint Presentation Styles Examples. This is a three stage process. The stages in this process are Security, Storage, Data. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
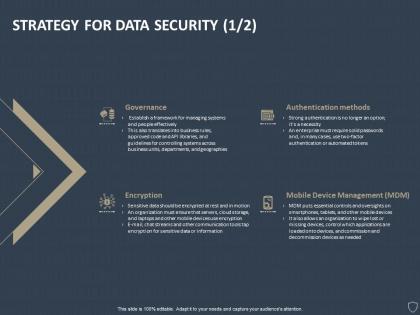 Strategy for data security encryption ppt powerpoint presentation slides format
Strategy for data security encryption ppt powerpoint presentation slides formatPresenting this set of slides with name Strategy For Data Security Encryption Ppt Powerpoint Presentation Slides Format. The topics discussed in these slides are Governance, Authentication Methods, Encryption, Mobile Device Management. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
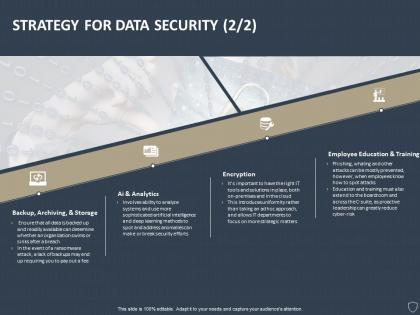 Strategy for data security governance ppt powerpoint presentation pictures grid
Strategy for data security governance ppt powerpoint presentation pictures gridPresenting this set of slides with name Strategy For Data Security Governance Ppt Powerpoint Presentation Pictures Grid. This is a four stage process. The stages in this process are Backup, Archiving, And Storage, Ai And Analytics, Encryption, Employee Education And Training. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
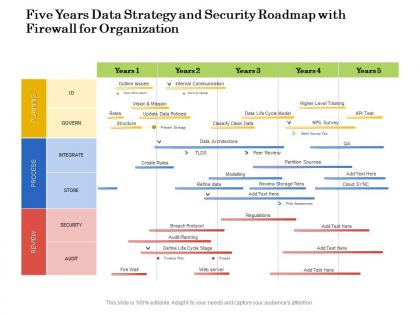 Five years data strategy and security roadmap with firewall for organization
Five years data strategy and security roadmap with firewall for organizationPresenting Five Years Data Strategy And Security Roadmap With Firewall For Organization PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
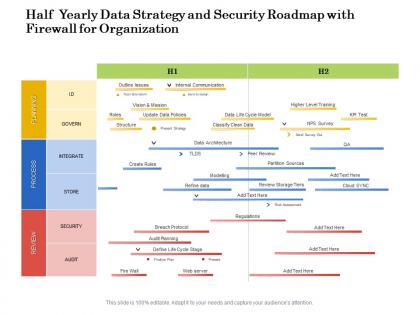 Half yearly data strategy and security roadmap with firewall for organization
Half yearly data strategy and security roadmap with firewall for organizationPresenting Half Yearly Data Strategy And Security Roadmap With Firewall For Organization PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
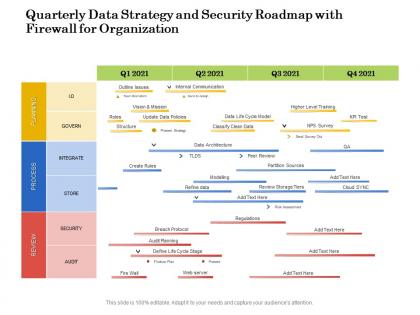 Quarterly data strategy and security roadmap with firewall for organization
Quarterly data strategy and security roadmap with firewall for organizationPresenting Quarterly Data Strategy And Security Roadmap With Firewall For Organization PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
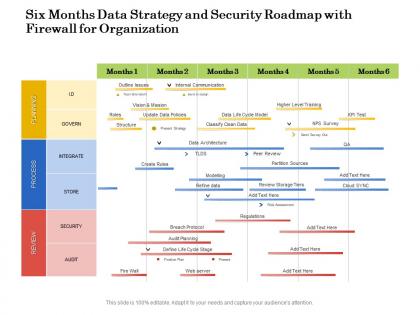 Six months data strategy and security roadmap with firewall for organization
Six months data strategy and security roadmap with firewall for organizationPresenting Six Months Data Strategy And Security Roadmap With Firewall For Organization PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
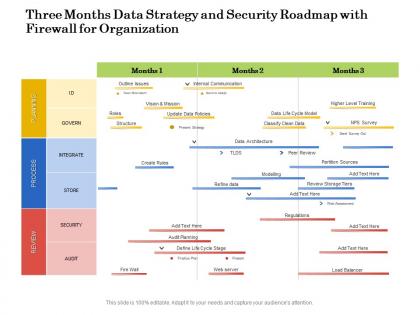 Three months data strategy and security roadmap with firewall for organization
Three months data strategy and security roadmap with firewall for organizationPresenting Three Months Data Strategy And Security Roadmap With Firewall For Organization PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
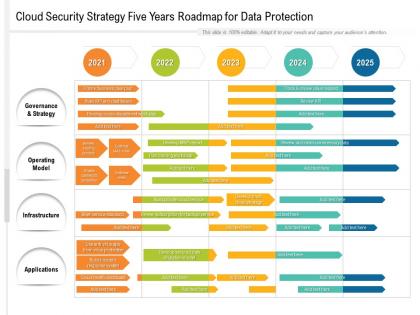 Cloud security strategy five years roadmap for data protection
Cloud security strategy five years roadmap for data protectionPresenting Cloud Security Strategy Five Years Roadmap For Data Protection PowerPoint slide. This PPT slide is available at 4,3 and 16,9 aspect ratios. You can download this PPT theme in various formats like PDF, PNG, and JPG. This PowerPoint template is completely editable and you can modify the font size, font type, and shapes as per your requirements. Our PPT layout is compatible with Google Slides.
-
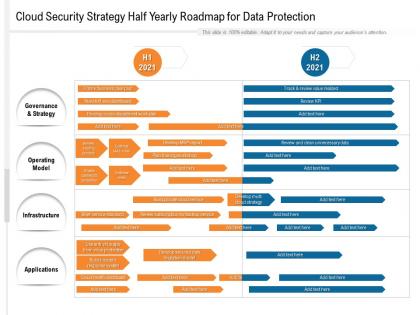 Cloud security strategy half yearly roadmap for data protection
Cloud security strategy half yearly roadmap for data protectionPresenting Cloud Security Strategy Half Yearly Roadmap For Data Protection PowerPoint slide. This PPT presentation is Google Slides compatible hence it is easily accessible. This PPT theme is available in both 4,3 and 16,9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color, and shapes as per your requirements. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.


