Powerpoint Templates and Google slides for Encryption Of Data
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Lack Of Encryption As An Information Security Threat Training Ppt
Lack Of Encryption As An Information Security Threat Training PptPresenting Lack of Encryption as an Information Security Threat. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Encryption As A Type Of Application Security Training Ppt
Encryption As A Type Of Application Security Training PptPresenting Encryption as a Type of Application Security. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
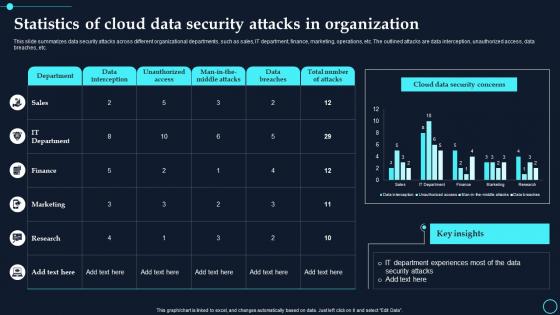 Statistics Of Cloud Data Security Attacks In Organization Cloud Data Encryption
Statistics Of Cloud Data Security Attacks In Organization Cloud Data EncryptionThis slide summarizes data security attacks across different organizational departments, such as sales, IT department, finance, marketing, operations, etc. The outlined attacks are data interception, unauthorized access, data breaches, etc. Deliver an outstanding presentation on the topic using this Statistics Of Cloud Data Security Attacks In Organization Cloud Data Encryption. Dispense information and present a thorough explanation of Data Interception, Unauthorized Access using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
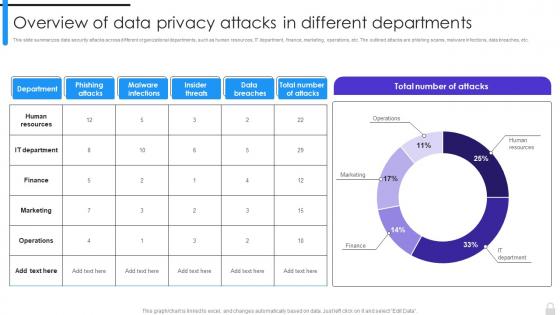 Encryption Implementation Strategies Overview Of Data Privacy Attacks In Different Departments
Encryption Implementation Strategies Overview Of Data Privacy Attacks In Different DepartmentsThis slide summarizes data security attacks across different organizational departments, such as human resources, IT department, finance, marketing, operations, etc. The outlined attacks are phishing scams, malware infections, data breaches, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Overview Of Data Privacy Attacks In Different Departments. Use it as a tool for discussion and navigation on Human Resources, IT Department, Finance, Marketing, Operations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
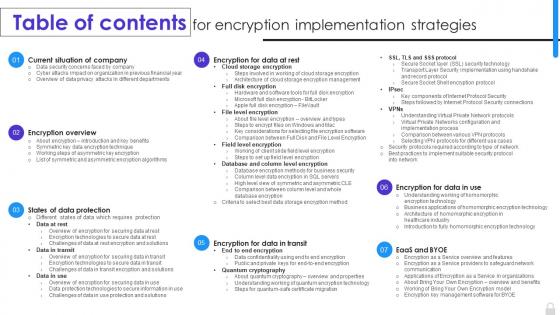 Table Of Contents For Encryption Implementation Strategies Ppt Ideas Examples
Table Of Contents For Encryption Implementation Strategies Ppt Ideas ExamplesIntroducing Table Of Contents For Encryption Implementation Strategies Ppt Ideas Examples to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Encryption Overview, States Of Data Protection, Current Situation Of Company, Encryption Implementation Strategies, using this template. Grab it now to reap its full benefits.
-
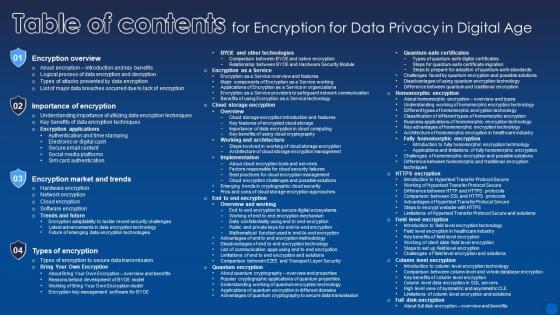 Table Of Contents For Encryption For Data Privacy In Digital Age
Table Of Contents For Encryption For Data Privacy In Digital AgeDeliver an outstanding presentation on the topic using this Table Of Contents For Encryption For Data Privacy In Digital Age. Dispense information and present a thorough explanation of Encryption Overview, Importance Of Encryption, Encryption Market And Trends using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
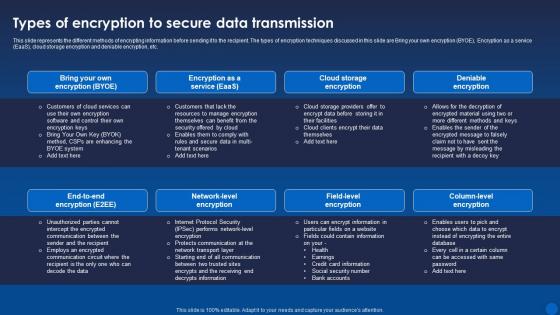 Types Of Encryption To Secure Data Transmission Encryption For Data Privacy In Digital Age It
Types Of Encryption To Secure Data Transmission Encryption For Data Privacy In Digital Age ItThis slide represents the different methods of encrypting information before sending it to the recipient. The types of encryption techniques discussed in this slide are Bring your own encryption BYOE, Encryption as a service EaaS, cloud storage encryption and deniable encryption, etc. Present the topic in a bit more detail with this Types Of Encryption To Secure Data Transmission Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Data Transmission, Encryption, Deniable Encryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
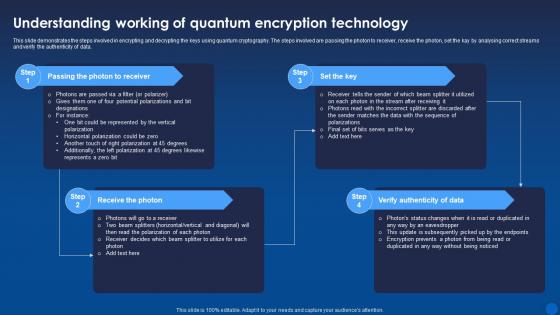 Understanding Working Of Quantum Encryption Technology Encryption For Data Privacy In Digital Age It
Understanding Working Of Quantum Encryption Technology Encryption For Data Privacy In Digital Age ItThis slide demonstrates the steps involved in encrypting and decrypting the keys using quantum cryptography. The steps involved are passing the photon to receiver, receive the photon, set the kay by analysing correct streams and verify the authenticity of data. Increase audience engagement and knowledge by dispensing information using Understanding Working Of Quantum Encryption Technology Encryption For Data Privacy In Digital Age It. This template helps you present information on four stages. You can also present information on Passing The Photon To Receiver, Receive The Photon, Verify Authenticity Of Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
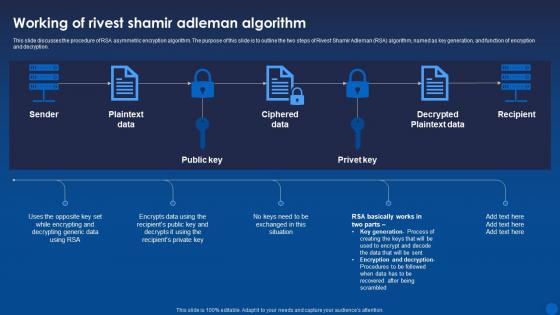 Working Of Rivest Shamir Adleman Algorithm Encryption For Data Privacy In Digital Age It
Working Of Rivest Shamir Adleman Algorithm Encryption For Data Privacy In Digital Age ItThis slide discusses the procedure of RSA asymmetric encryption algorithm. The purpose of this slide is to outline the two steps of Rivest Shamir Adleman RSA algorithm, named as key generation, and function of encryption and decryption. Deliver an outstanding presentation on the topic using this Working Of Rivest Shamir Adleman Algorithm Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Algorithm, Ciphered Data, Decrypted Plaintext Data using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Types Of Encryption For Securing Big Data Analytics
Types Of Encryption For Securing Big Data AnalyticsThis slide highlights the various types of encryption techniques utilized for protecting big data analytics. The purpose of this slide is to help the business safeguard sensitive information for preventing data breaches and information thefts. It includes quantum proof encryption, homomorphic encryption, etc. Introducing our premium set of slides with Types Of Encryption For Securing Big Data Analytics. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Homomorphic Encryption, Differential Privacy. So download instantly and tailor it with your information.
-
 WIFI Off Wireless Encryption Colored Icon In Powerpoint Pptx Png And Editable Eps Format
WIFI Off Wireless Encryption Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis is a coloured powerpoint icon of a WIFI symbol with a red cross over it, indicating the WIFI is off. Ideal for presentations or documents related to technology, networks and internet security.
-
 WIFI Off Wireless Encryption Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
WIFI Off Wireless Encryption Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint icon is perfect for presentations that need to communicate the concept of WIFI Off. It features a simple, minimalistic design that is easy to recognize and eye catching. The icon is available in both vector and raster formats for easy use.
-
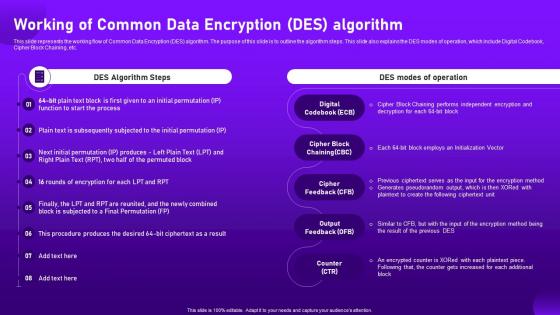 Working Of Common Data Encryption Des Algorithm Cloud Cryptography
Working Of Common Data Encryption Des Algorithm Cloud CryptographyThis slide represents the working flow of Common Data Encryption DES algorithm. The purpose of this slide is to outline the algorithm steps. This slide also explains the DES modes of operation, which include Digital Codebook, Cipher Block Chaining, etc. Deliver an outstanding presentation on the topic using this Working Of Common Data Encryption Des Algorithm Cloud Cryptography. Dispense information and present a thorough explanation of Pseudorandom, Initialization, Independent using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
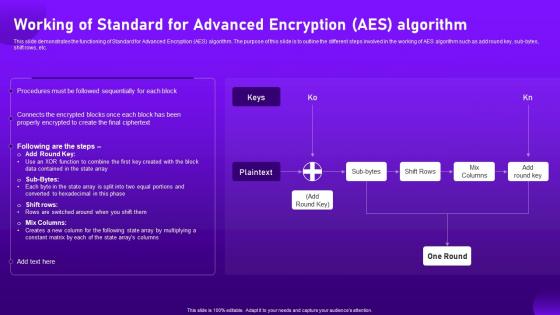 Working Of Standard For Advanced Encryption Aes Algorithm Cloud Cryptography
Working Of Standard For Advanced Encryption Aes Algorithm Cloud CryptographyThis slide demonstrates the functioning of Standard for Advanced Encryption AES algorithm. The purpose of this slide is to outline the different steps involved in the working of AES algorithm such as add round key, sub-bytes, shift rows, etc. Present the topic in a bit more detail with this Working Of Standard For Advanced Encryption Aes Algorithm Cloud Cryptography. Use it as a tool for discussion and navigation on Demonstrates, Encryption, Algorithm. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
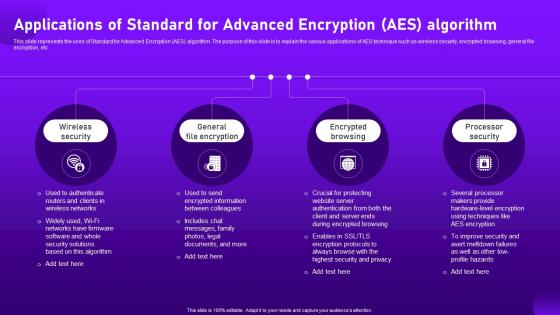 Applications Of Standard For Advanced Encryption Aes Algorithm Cloud Cryptography
Applications Of Standard For Advanced Encryption Aes Algorithm Cloud CryptographyThis slide represents the uses of Standard for Advanced Encryption AES algorithm. The purpose of this slide is to explain the various applications of AES technique such as wireless security, encrypted browsing, general file encryption, etc. Introducing Applications Of Standard For Advanced Encryption Aes Algorithm Cloud Cryptography to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Wireless Security, General File Encryption, Encrypted Browsing, using this template. Grab it now to reap its full benefits.
-
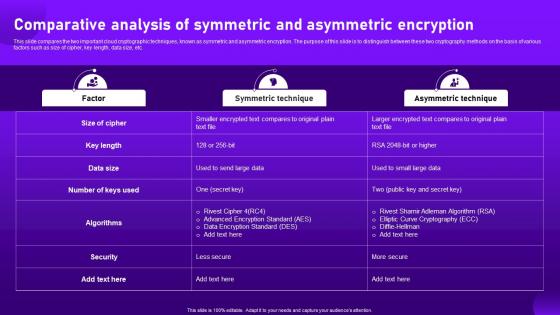 Comparative Analysis Of Symmetric And Asymmetric Encryption Cloud Cryptography
Comparative Analysis Of Symmetric And Asymmetric Encryption Cloud CryptographyThis slide compares the two important cloud cryptographic techniques, known as symmetric and asymmetric encryption. The purpose of this slide is to distinguish between these two cryptography methods on the basis of various factors such as size of cipher, key length, data size, etc. Present the topic in a bit more detail with this Comparative Analysis Of Symmetric And Asymmetric Encryption Cloud Cryptography. Use it as a tool for discussion and navigation on Comparative, Analysis, Asymmetric Encryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
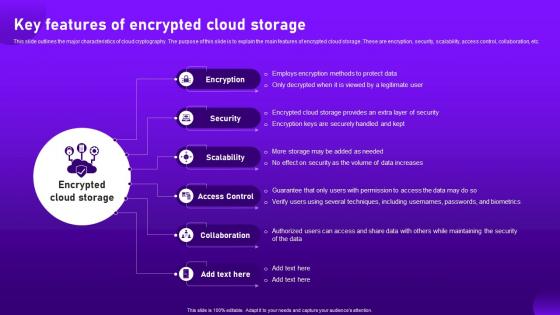 Key Features Of Encrypted Cloud Storage Cloud Cryptography
Key Features Of Encrypted Cloud Storage Cloud CryptographyThis slide outlines the major characteristics of cloud cryptography. The purpose of this slide is to explain the main features of encrypted cloud storage. These are encryption, security, scalability, access control, collaboration, etc. Introducing Key Features Of Encrypted Cloud Storage Cloud Cryptography to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Encryption, Access Control, Collaboration, using this template. Grab it now to reap its full benefits.
-
 Cloud Data Encryption Implementation Plan Table Of Contents
Cloud Data Encryption Implementation Plan Table Of ContentsIncrease audience engagement and knowledge by dispensing information using Cloud Data Encryption Implementation Plan Table Of Contents. This template helps you present information on one stages. You can also present information on Key Challenges, Cloud Data Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
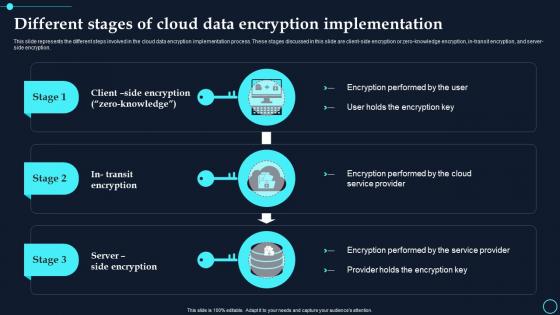 Different Stages Of Cloud Data Encryption Implementation Cloud Data Encryption
Different Stages Of Cloud Data Encryption Implementation Cloud Data EncryptionThis slide represents the different steps involved in the cloud data encryption implementation process. These stages discussed in this slide are client side encryption or zero knowledge encryption, in transit encryption, and server side encryption. Increase audience engagement and knowledge by dispensing information using Different Stages Of Cloud Data Encryption Implementation Cloud Data Encryption. This template helps you present information on three stages. You can also present information on Encryption Performed, Service Provider using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
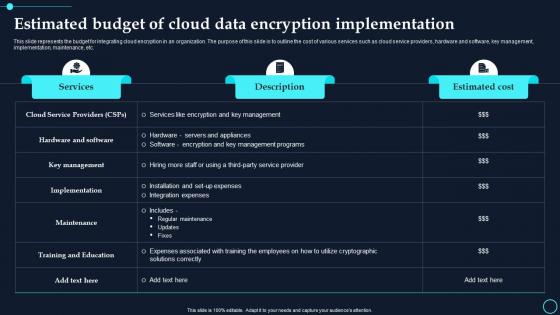 Estimated Budget Of Cloud Data Encryption Implementation Cloud Data Encryption
Estimated Budget Of Cloud Data Encryption Implementation Cloud Data EncryptionThis slide represents the budget for integrating cloud encryption in an organization. The purpose of this slide is to outline the cost of various services such as cloud service providers, hardware and software, key management, implementation, maintenance, etc. Present the topic in a bit more detail with this Estimated Budget Of Cloud Data Encryption Implementation Cloud Data Encryption. Use it as a tool for discussion and navigation on Services, Description. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Impact Of Encryption Implementation On Cloud Security Cloud Data Encryption
Impact Of Encryption Implementation On Cloud Security Cloud Data EncryptionThis slide represents the various factors that showcase the improvement of application security after adopting encryption. The parameters discussed are unauthorized access, data breaches, malware and ransomware, phishing attacks, etc. Deliver an outstanding presentation on the topic using this Impact Of Encryption Implementation On Cloud Security Cloud Data Encryption. Dispense information and present a thorough explanation of Unauthorized Access, Data Breaches using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
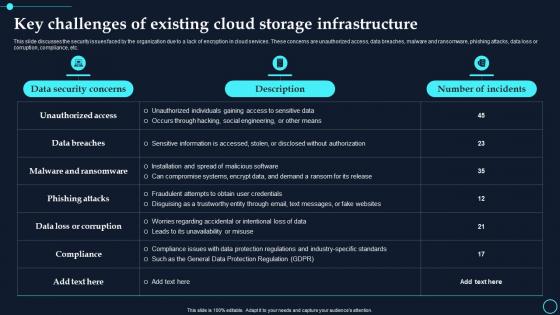 Key Challenges Of Existing Cloud Storage Infrastructure Cloud Data Encryption
Key Challenges Of Existing Cloud Storage Infrastructure Cloud Data EncryptionThis slide discusses the security issues faced by the organization due to a lack of encryption in cloud services. These concerns are unauthorized access, data breaches, malware and ransomware, phishing attacks, data loss or corruption, compliance, etc. Present the topic in a bit more detail with this Key Challenges Of Existing Cloud Storage Infrastructure Cloud Data Encryption. Use it as a tool for discussion and navigation on Data Security Concerns, Description. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
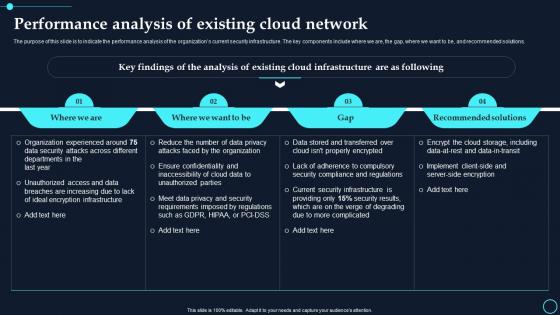 Performance Analysis Of Existing Cloud Network Cloud Data Encryption
Performance Analysis Of Existing Cloud Network Cloud Data EncryptionThe purpose of this slide is to indicate the performance analysis of the organizations current security infrastructure. The key components include where we are, the gap, where we want to be, and recommended solutions. Present the topic in a bit more detail with this Performance Analysis Of Existing Cloud Network Cloud Data Encryption. Use it as a tool for discussion and navigation on Where We Are, Where We Want To Be. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
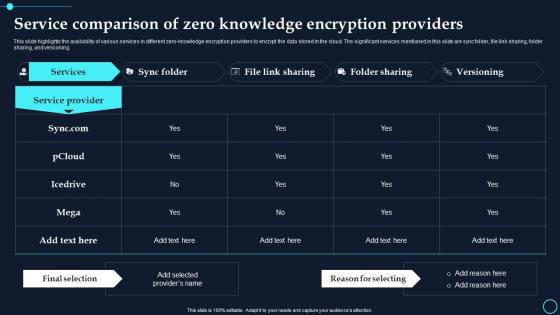 Service Comparison Of Zero Knowledge Encryption Providers Cloud Data Encryption
Service Comparison Of Zero Knowledge Encryption Providers Cloud Data EncryptionThis slide highlights the availability of various services in different zero knowledge encryption providers to encrypt the data stored in the cloud. The significant services mentioned in this slide are sync folder, file link sharing, folder sharing, and versioning. Deliver an outstanding presentation on the topic using this Service Comparison Of Zero Knowledge Encryption Providers Cloud Data Encryption. Dispense information and present a thorough explanation of Service Provider, Services using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Table Of Contents Cloud Data Encryption Implementation Plan
Table Of Contents Cloud Data Encryption Implementation PlanIncrease audience engagement and knowledge by dispensing information using Table Of Contents Cloud Data Encryption Implementation Plan. This template helps you present information on one stages. You can also present information on Existing Cloud Data, Infrastructure Constituents using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
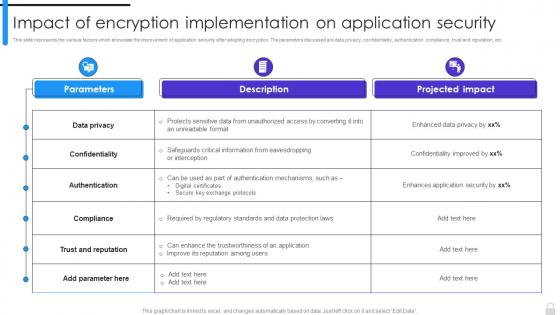 Encryption Implementation Strategies Impact Of Encryption Implementation On Application Security
Encryption Implementation Strategies Impact Of Encryption Implementation On Application SecurityThis slide represents the various factors which showcase the improvement of application security after adopting encryption. The parameters discussed are data privacy, confidentiality, authentication, compliance, trust and reputation, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Impact Of Encryption Implementation On Application Security. Dispense information and present a thorough explanation of Confidentiality, Data Privacy, Trust And Reputation, Application Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
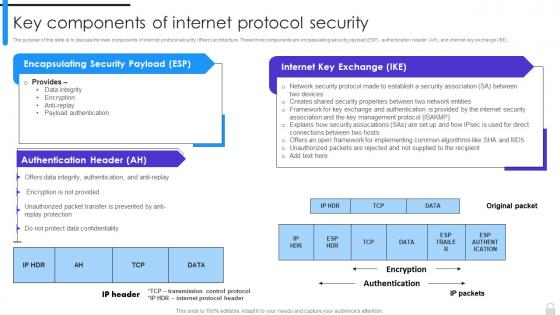 Encryption Implementation Strategies Key Components Of Internet Protocol Security
Encryption Implementation Strategies Key Components Of Internet Protocol SecurityThe purpose of this slide is to discuss the main components of internet protocol security IPsec architecture. These three components are encapsulating security payload ESP, authentication header AH, and internet key exchange IKE. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Key Components Of Internet Protocol Security. Dispense information and present a thorough explanation of Data Integrity, Encryption, Anti Replay, Payload Authentication using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
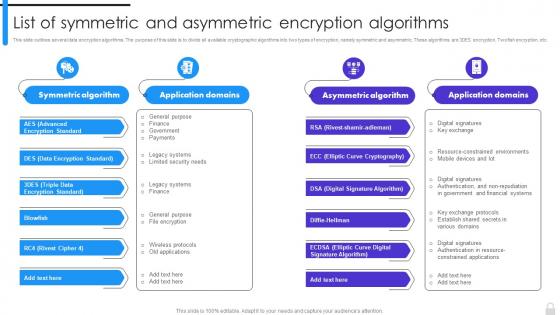 Encryption Implementation Strategies List Of Symmetric And Asymmetric Encryption Algorithms
Encryption Implementation Strategies List Of Symmetric And Asymmetric Encryption AlgorithmsThis slide outlines several data encryption algorithms. The purpose of this slide is to divide all available cryptographic algorithms into two types of encryption, namely symmetric and asymmetric. These algorithms are 3DES encryption, Twofish encryption, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies List Of Symmetric And Asymmetric Encryption Algorithms. Dispense information and present a thorough explanation of Data Encryption Standard, Triple Data Encryption Standard, Digital Signature Algorithm, Elliptic Curve Cryptography using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
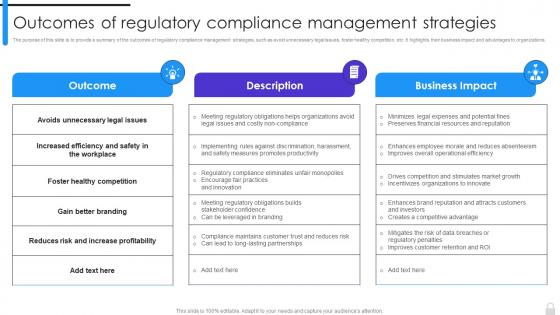 Encryption Implementation Strategies Outcomes Of Regulatory Compliance Management Strategies
Encryption Implementation Strategies Outcomes Of Regulatory Compliance Management StrategiesThe purpose of this slide is to provide a summary of the outcomes of regulatory compliance management strategies, such as avoid unnecessary legal issues, foster healthy competition, etc. It highlights their business impact and advantages to organizations. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Outcomes Of Regulatory Compliance Management Strategies. Dispense information and present a thorough explanation of Foster Healthy Competition, Gain Better Branding, Regulatory Compliance, Management Strategies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
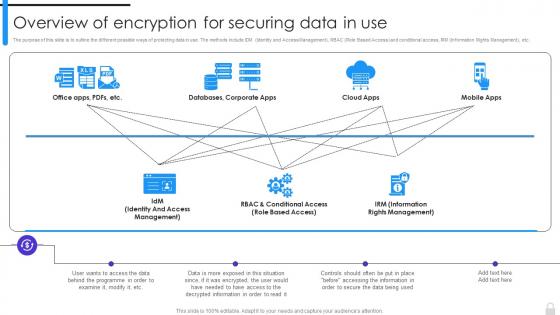 Encryption Implementation Strategies Overview Of Encryption For Securing Data In Use
Encryption Implementation Strategies Overview Of Encryption For Securing Data In UseThe purpose of this slide is to outline the different possible ways of protecting data in use. The methods include IDM Identity and Access Management, RBAC Role Based Access and conditional access, IRM Information Rights Management, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Overview Of Encryption For Securing Data In Use. Dispense information and present a thorough explanation of Information Rights Management, Encryption For Securing Data, Role Based Access using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
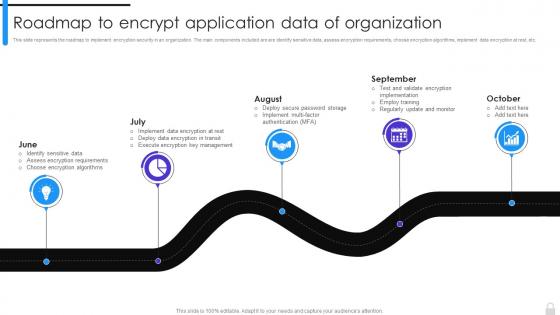 Encryption Implementation Strategies Roadmap To Encrypt Application Data Of Organization
Encryption Implementation Strategies Roadmap To Encrypt Application Data Of OrganizationThis slide represents the roadmap to implement encryption security in an organization. The main components included are are identify sensitive data, assess encryption requirements, choose encryption algorithms, implement data encryption at rest, etc. Introducing Encryption Implementation Strategies Roadmap To Encrypt Application Data Of Organization to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Encryption Security, Identify Sensitive Data, Assess Encryption Requirements, Encryption Algorithms, Implement Data Encryption, using this template. Grab it now to reap its full benefits.
-
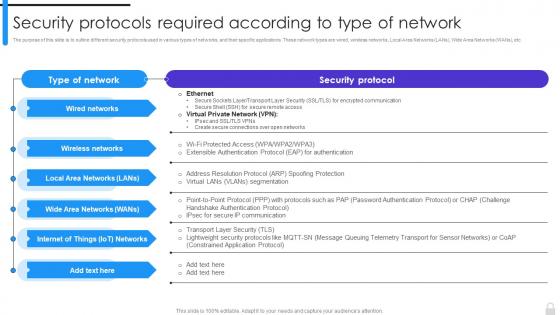 Encryption Implementation Strategies Security Protocols Required According To Type Of Network
Encryption Implementation Strategies Security Protocols Required According To Type Of NetworkThe purpose of this slide is to outline different security protocols used in various types of networks, and their specific applications. These network types are wired, wireless networks, Local Area Networks LANs, Wide Area Networks WANs, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Security Protocols Required According To Type Of Network. Use it as a tool for discussion and navigation on Local Area Networks, Wide Area Networks, Wired Networks, Wireless Networks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
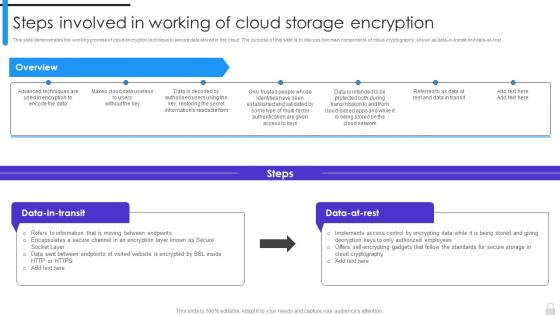 Encryption Implementation Strategies Steps Involved In Working Of Cloud Storage Encryption
Encryption Implementation Strategies Steps Involved In Working Of Cloud Storage EncryptionThis slide demonstrates the working process of cloud encryption technique to secure data stored in the cloud. The purpose of this slide is to discuss two main components of cloud cryptography, known as data-in-transit and data-at-rest. Present the topic in a bit more detail with this Encryption Implementation Strategies Steps Involved In Working Of Cloud Storage Encryption. Use it as a tool for discussion and navigation on Cloud Storage Encryption, Data In Transit, Cloud Cryptography, Cloud Encryption Technique. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
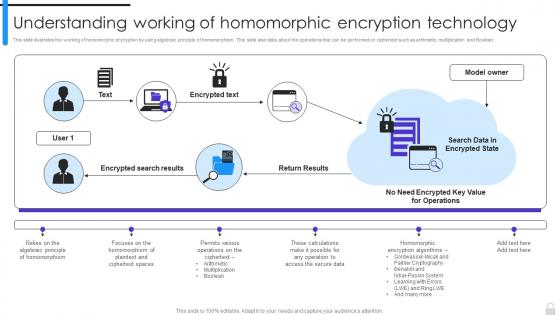 Encryption Implementation Strategies Understanding Working Of Homomorphic Encryption
Encryption Implementation Strategies Understanding Working Of Homomorphic EncryptionThis slide illustrates the working of homomorphic encryption by using algebraic principle of homomorphism. This slide also talks about the operations that can be performed on ciphertext such as arithmetic, multiplication and Boolean. Present the topic in a bit more detail with this Encryption Implementation Strategies Understanding Working Of Homomorphic Encryption. Use it as a tool for discussion and navigation on Encrypted Search Results, Working Of Homomorphic, Encryption Technology, Plaintext And Ciphertext Spaces. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
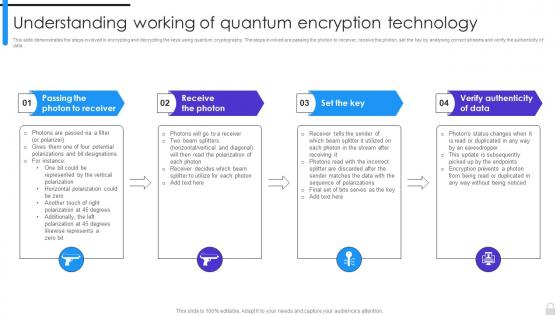 Encryption Implementation Strategies Understanding Working Of Quantum Encryption Technology
Encryption Implementation Strategies Understanding Working Of Quantum Encryption TechnologyThis slide demonstrates the steps involved in encrypting and decrypting the keys using quantum cryptography. The steps involved are passing the photon to receiver, receive the photon, set the kay by analysing correct streams and verify the authenticity of data. Increase audience engagement and knowledge by dispensing information using Encryption Implementation Strategies Understanding Working Of Quantum Encryption Technology. This template helps you present information on four stages. You can also present information on Passing The Photon To Receiver, Verify Authenticity Of Data, Working Of Quantum, Encryption Technology using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
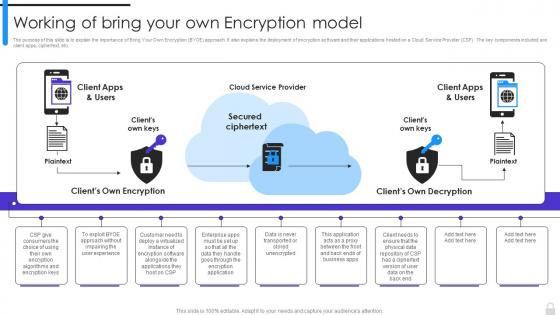 Encryption Implementation Strategies Working Of Bring Your Own Encryption Model
Encryption Implementation Strategies Working Of Bring Your Own Encryption ModelThe purpose of this slide is to explain the importance of Bring Your Own Encryption BYOE approach. It also explains the deployment of encryption software and their applications hosted on a Cloud Service Provider CSP. The key components included are client apps, ciphertext, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Working Of Bring Your Own Encryption Model. Use it as a tool for discussion and navigation on Cloud Service Provider, Own Encryption Model, Secured Ciphertext, Clients Own Encryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
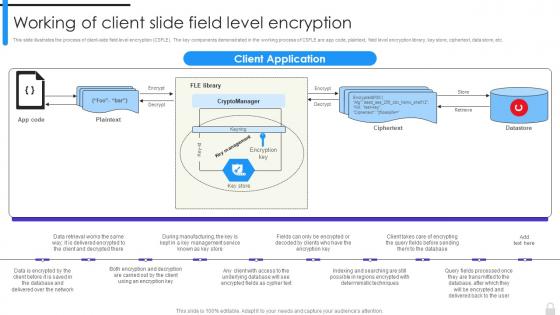 Encryption Implementation Strategies Working Of Client Slide Field Level Encryption
Encryption Implementation Strategies Working Of Client Slide Field Level EncryptionThis slide illustrates the process of client-side field level encryption CSFLE. The key components demonstrated in the working process of CSFLE are app code, plaintext, field level encryption library, key store, ciphertext, data store, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Working Of Client Slide Field Level Encryption. Dispense information and present a thorough explanation of Working Of Client Slide, Field Level Encryption, Ciphertext, Data Store using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
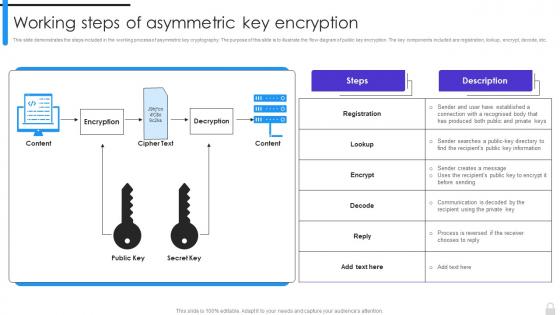 Encryption Implementation Strategies Working Steps Of Asymmetric Key Encryption
Encryption Implementation Strategies Working Steps Of Asymmetric Key EncryptionThis slide demonstrates the steps included in the working process of asymmetric key cryptography. The purpose of this slide is to illustrate the flow diagram of public key encryption. The key components included are registration, lookup, encrypt, decode, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Working Steps Of Asymmetric Key Encryption. Use it as a tool for discussion and navigation on Working Steps Of Asymmetric, Encrypt, Public Key Encryption, Asymmetric Key Cryptography. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
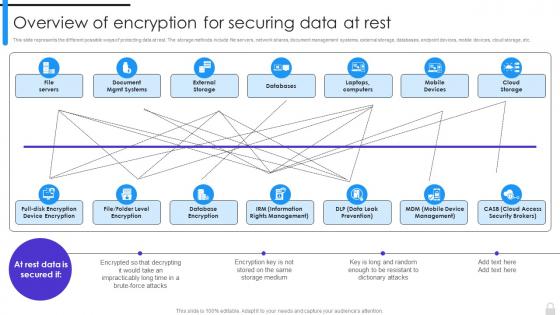 Overview Of Encryption For Securing Data At Rest Encryption Implementation Strategies
Overview Of Encryption For Securing Data At Rest Encryption Implementation StrategiesThis slide represents the different possible ways of protecting data at rest. The storage methods include file servers, network shares, document management systems, external storage, databases, endpoint devices, mobile devices, cloud storage, etc. Present the topic in a bit more detail with this Overview Of Encryption For Securing Data At Rest Encryption Implementation Strategies. Use it as a tool for discussion and navigation on Database Encryption, Information Rights Management, Data Leak Prevention, Mobile Device Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
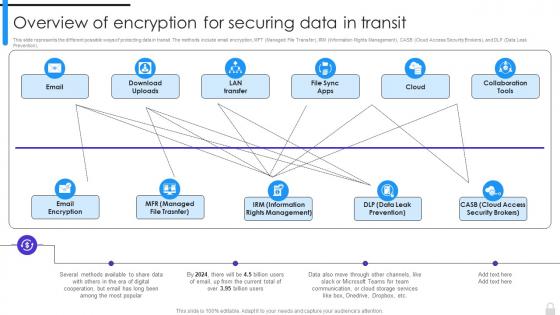 Overview Of Encryption For Securing Data In Transit Encryption Implementation Strategies
Overview Of Encryption For Securing Data In Transit Encryption Implementation StrategiesThis slide represents the different possible ways of protecting data in transit. The methods include email encryption, MFT Managed File Transfer, IRM Information Rights Management, CASB Cloud Access Security Brokers, and DLP Data Leak Prevention. Deliver an outstanding presentation on the topic using this Overview Of Encryption For Securing Data In Transit Encryption Implementation Strategies. Dispense information and present a thorough explanation of Information Rights Management, Data Leak Prevention, Cloud Access Security Brokers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
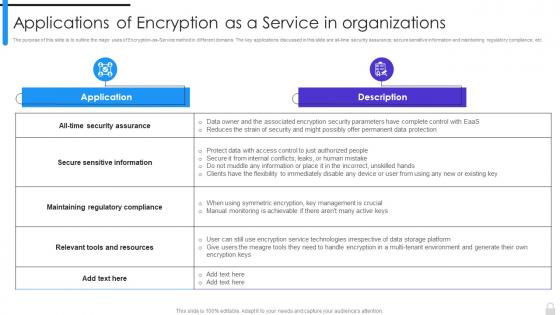 Encryption Implementation Strategies Applications Of Encryption As A Service In Organizations
Encryption Implementation Strategies Applications Of Encryption As A Service In OrganizationsThe purpose of this slide is to outline the major uses of Encryption-as-Service method in different domains. The key applications discussed in this slide are all-time security assurance, secure sensitive information and maintaining regulatory compliance, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Applications Of Encryption As A Service In Organizations. Use it as a tool for discussion and navigation on Secure Sensitive Information, Maintaining Regulatory Compliance, Relevant Tools And Resources. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
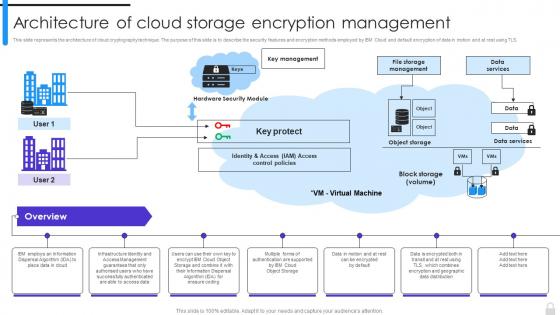 Encryption Implementation Strategies Architecture Of Cloud Storage Encryption Management
Encryption Implementation Strategies Architecture Of Cloud Storage Encryption ManagementThis slide represents the architecture of cloud cryptography technique. The purpose of this slide is to describe the security features and encryption methods employed by IBM Cloud and default encryption of data in motion and at rest using TLS. Introducing Encryption Implementation Strategies Architecture Of Cloud Storage Encryption Management to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Cryptography Technique, Encryption Of Data, Key Management, Cloud Storage Encryption, using this template. Grab it now to reap its full benefits.
-
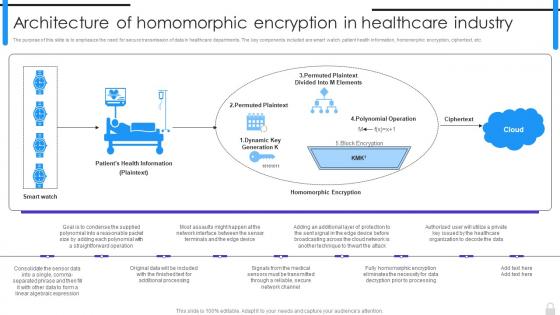 Encryption Implementation Strategies Architecture Of Homomorphic Encryption In Healthcare Industry
Encryption Implementation Strategies Architecture Of Homomorphic Encryption In Healthcare IndustryThe purpose of this slide is to emphasize the need for secure transmission of data in healthcare departments. The key components included are smart watch, patient health information, homomorphic encryption, ciphertext, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Architecture Of Homomorphic Encryption In Healthcare Industry. Dispense information and present a thorough explanation of Architecture Of Homomorphic, Encryption In Healthcare Industry, Patient Health Information, Healthcare Departments using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
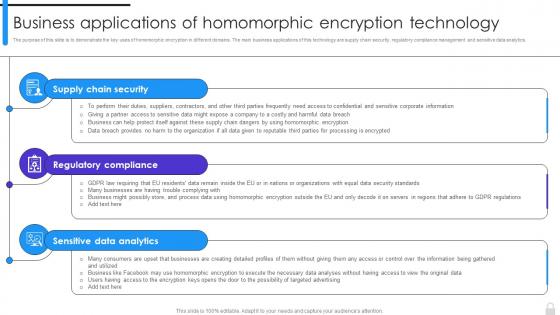 Encryption Implementation Strategies Business Applications Of Homomorphic Encryption Technology
Encryption Implementation Strategies Business Applications Of Homomorphic Encryption TechnologyThe purpose of this slide is to demonstrate the key uses of homomorphic encryption in different domains. The main business applications of this technology are supply chain security, regulatory compliance management and sensitive data analytics. Increase audience engagement and knowledge by dispensing information using Encryption Implementation Strategies Business Applications Of Homomorphic Encryption Technology. This template helps you present information on three stages. You can also present information on Supply Chain Security, Regulatory Compliance, Sensitive Data Analytics, Homomorphic Encryption Technology using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
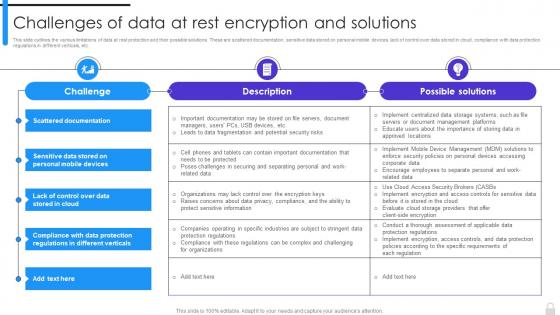 Encryption Implementation Strategies Challenges Of Data At Rest Encryption And Solutions
Encryption Implementation Strategies Challenges Of Data At Rest Encryption And SolutionsThis slide outlines the various limitations of data at rest protection and their possible solutions. These are scattered documentation, sensitive data stored on personal mobile devices, lack of control over data stored in cloud, compliance with data protection regulations in different verticals, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Challenges Of Data At Rest Encryption And Solutions. Use it as a tool for discussion and navigation on Data At Rest Protection, Scattered Documentation, Sensitive Data Stored, Personal Mobile Devices, Data Protection Regulations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
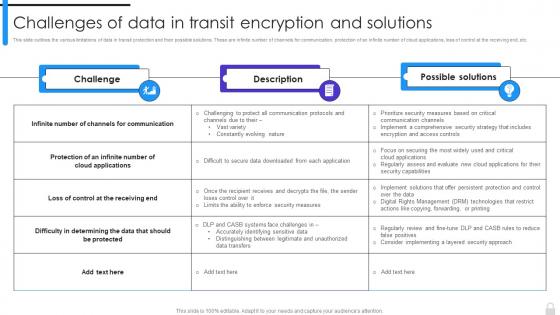 Encryption Implementation Strategies Challenges Of Data In Transit Encryption And Solutions
Encryption Implementation Strategies Challenges Of Data In Transit Encryption And SolutionsThis slide outlines the various limitations of data in transit protection and their possible solutions. These are infinite number of channels for communication, protection of an infinite number of cloud applications, loss of control at the receiving end, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Challenges Of Data In Transit Encryption And Solutions. Dispense information and present a thorough explanation of Data In Transit, Encryption And Solutions, Cloud Applications, Channels For Communication using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
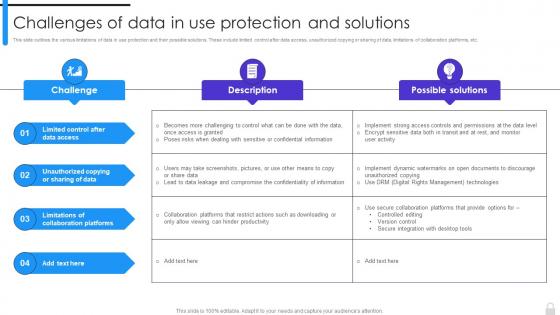 Encryption Implementation Strategies Challenges Of Data In Use Protection And Solutions
Encryption Implementation Strategies Challenges Of Data In Use Protection And SolutionsThis slide outlines the various limitations of data in use protection and their possible solutions. These include limited control after data access, unauthorized copying or sharing of data, limitations of collaboration platforms, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Challenges Of Data In Use Protection And Solutions. Use it as a tool for discussion and navigation on Limitations Of Collaboration Platforms, Unauthorized Copying Or Sharing Of Data, Limited Control After Data Access. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
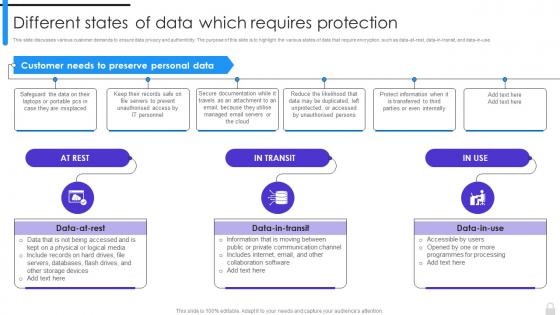 Encryption Implementation Strategies Different States Of Data Which Requires Protection
Encryption Implementation Strategies Different States Of Data Which Requires ProtectionThis slide discusses various customer demands to ensure data privacy and authenticity. The purpose of this slide is to highlight the various states of data that require encryption, such as data-at-rest, data-in-transit, and data-in-use. Introducing Encryption Implementation Strategies Different States Of Data Which Requires Protection to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Customer Demands, Data Privacy And Authenticity, Require Encryption, Collaboration Software, using this template. Grab it now to reap its full benefits.
-
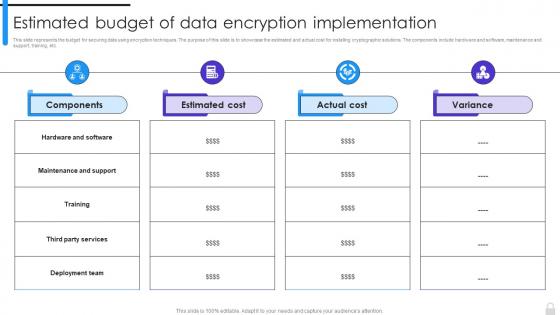 Encryption Implementation Strategies Estimated Budget Of Data Encryption Implementation
Encryption Implementation Strategies Estimated Budget Of Data Encryption ImplementationThis slide represents the budget for securing data using encryption techniques. The purpose of this slide is to showcase the estimated and actual cost for installing cryptographic solutions. The components include hardware and software, maintenance and support, training, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Estimated Budget Of Data Encryption Implementation. Use it as a tool for discussion and navigation on Maintenance And Support, Deployment Team, Data Encryption, Estimated Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Implementation Strategies For Table Of Contents Ppt Ideas Templates
Encryption Implementation Strategies For Table Of Contents Ppt Ideas TemplatesIntroducing Encryption Implementation Strategies For Table Of Contents Ppt Ideas Templates to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Safeguard Network Communication, Encryption Key Management Software, Applications Of Encryption As A Service, using this template. Grab it now to reap its full benefits.
-
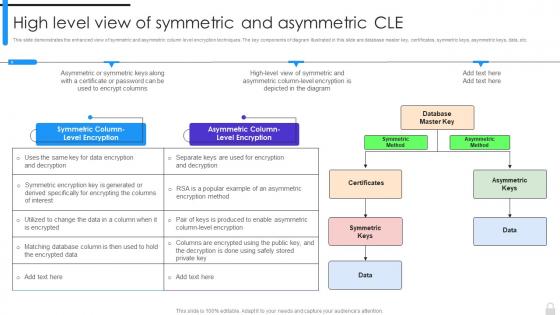 Encryption Implementation Strategies High Level View Of Symmetric And Asymmetric Cle
Encryption Implementation Strategies High Level View Of Symmetric And Asymmetric CleThis slide demonstrates the enhanced view of symmetric and asymmetric column level encryption techniques. The key components of diagram illustrated in this slide are database master key, certificates, symmetric keys, asymmetric keys, data, etc. Introducing Encryption Implementation Strategies High Level View Of Symmetric And Asymmetric Cle to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Symmetric Method, Asymmetric Method, Asymmetric Column Level Encryption, Symmetric Column Level Encryption, using this template. Grab it now to reap its full benefits.
-
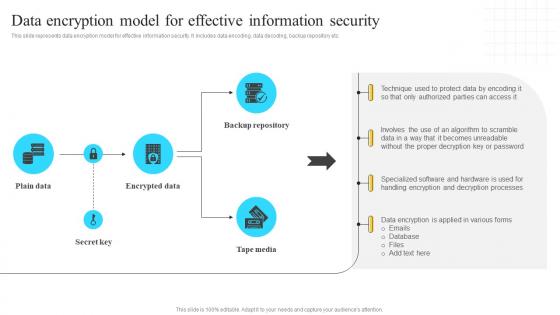 Implementation Of Information Data Encryption Model For Effective Information Security Strategy SS V
Implementation Of Information Data Encryption Model For Effective Information Security Strategy SS VThis slide represents data encryption model for effective information security. It includes data encoding, data decoding, backup repository etc. Present the topic in a bit more detail with this Implementation Of Information Data Encryption Model For Effective Information Security Strategy SS V. Use it as a tool for discussion and navigation on Backup Repository, Encrypted Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
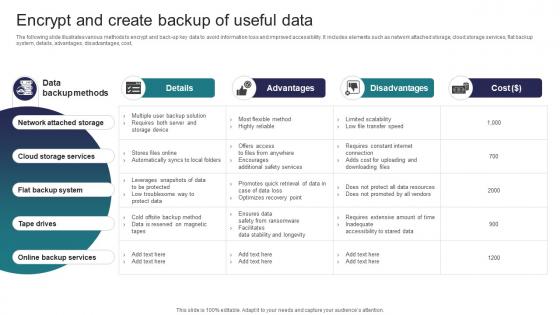 Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security Threats
Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide illustrates various methods to encrypt and back up key data to avoid information loss and improved accessibility. It includes elements such as network attached storage, cloud storage services, flat backup system, details, advantages, disadvantages, cost, Deliver an outstanding presentation on the topic using this Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Network Attached Storage, Cloud Storage Services, Flat Backup System using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
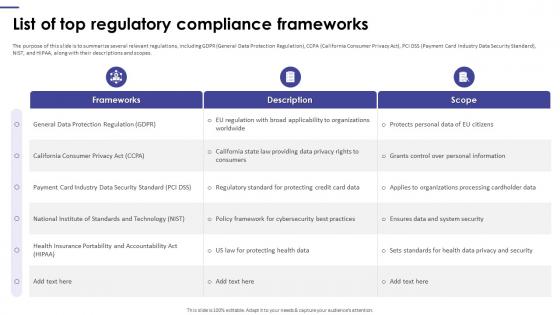 List Of Top Regulatory Compliance Frameworks Encryption Framework Upgradation Proposal
List Of Top Regulatory Compliance Frameworks Encryption Framework Upgradation ProposalThe purpose of this slide is to summarize several relevant regulations, including GDPR General Data Protection Regulation, CCPA California Consumer Privacy Act, PCI DSS Payment Card Industry Data Security Standard, NIST, and HIPAA, along with their descriptions and scopes. Deliver an outstanding presentation on the topic using this List Of Top Regulatory Compliance Frameworks Encryption Framework Upgradation Proposal. Dispense information and present a thorough explanation of General Data Protection Regulation, California Consumer Privacy Act, Industry Data Security Standard, Ensures Data And System Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
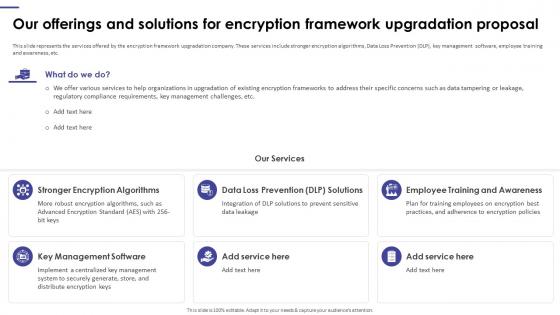 Our Offerings And Solutions For Encryption Framework Upgradation Proposal
Our Offerings And Solutions For Encryption Framework Upgradation ProposalThis slide represents the services offered by the encryption framework upgradation company. These services include stronger encryption algorithms, Data Loss Prevention DLP, key management software, employee training and awareness, etc. Introducing Our Offerings And Solutions For Encryption Framework Upgradation Proposal to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Stronger Encryption Algorithms, Employee Training And Awareness, Key Management Software, Encryption Framework Upgradation Proposal, using this template. Grab it now to reap its full benefits.
-
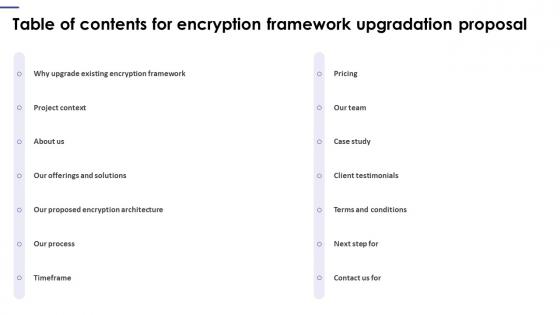 Table Of Contents For Encryption Framework Upgradation Proposal
Table Of Contents For Encryption Framework Upgradation ProposalIntroducing Table Of Contents For Encryption Framework Upgradation Proposal to increase your presentation threshold. Encompassed with fourteen stages, this template is a great option to educate and entice your audience. Dispence information on Client Testimonials, Existing Encryption Framework, Terms And Conditions, Our Team, using this template. Grab it now to reap its full benefits.
-
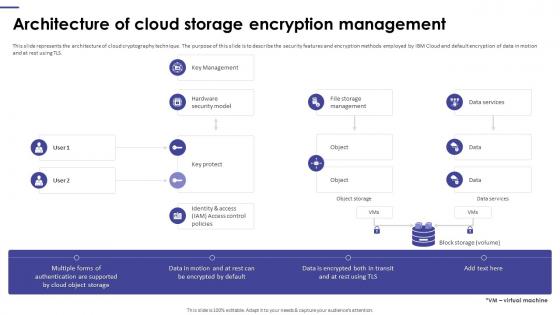 Encryption Framework Upgradation Proposal Architecture Of Cloud Storage Encryption Management
Encryption Framework Upgradation Proposal Architecture Of Cloud Storage Encryption ManagementPresent the topic in a bit more detail with this Encryption Framework Upgradation Proposal Architecture Of Cloud Storage Encryption Management. Use it as a tool for discussion and navigation on Architecture Of Cloud Storage, Encryption Management, Cloud Cryptography Technique. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
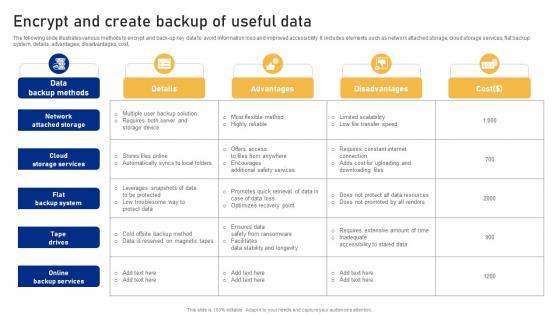 Encrypt And Create Backup Of Useful Data Cyber Risk Assessment
Encrypt And Create Backup Of Useful Data Cyber Risk AssessmentThe following slide illustrates various methods to encrypt and back-up key data to avoid information loss and improved accessibility. It includes elements such as network attached storage, cloud storage services, flat backup system, details, advantages, disadvantages, cost, Deliver an outstanding presentation on the topic using this Encrypt And Create Backup Of Useful Data Cyber Risk Assessment Dispense information and present a thorough explanation of Network Attached, Backup System, Backup Services using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
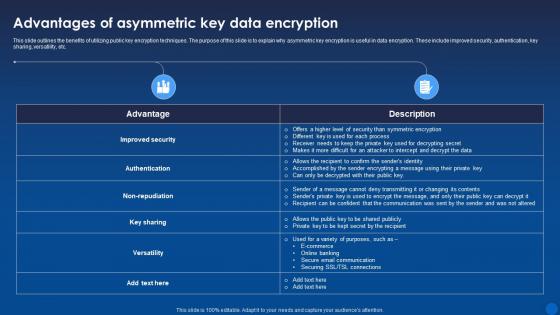 Advantages Of Asymmetric Key Data Encryption Encryption For Data Privacy In Digital Age It
Advantages Of Asymmetric Key Data Encryption Encryption For Data Privacy In Digital Age ItThis slide outlines the benefits of utilizing public key encryption techniques. The purpose of this slide is to explain why asymmetric key encryption is useful in data encryption. These include improved security, authentication, key sharing, versatility, etc. Deliver an outstanding presentation on the topic using this Advantages Of Asymmetric Key Data Encryption Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Accomplished, Communication, Asymmetric using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
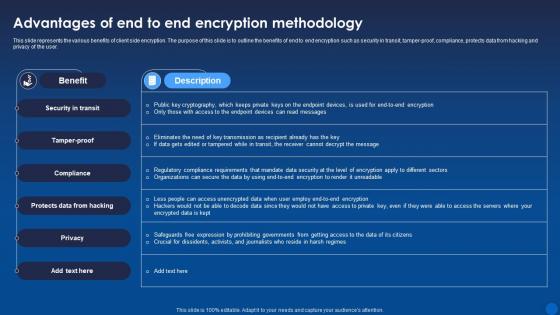 Advantages Of End To End Encryption Methodology Encryption For Data Privacy In Digital Age It
Advantages Of End To End Encryption Methodology Encryption For Data Privacy In Digital Age ItThis slide represents the various benefits of client side encryption. The purpose of this slide is to outline the benefits of end to end encryption such as security in transit, tamper-proof, compliance, protects data from hacking and privacy of the user. Present the topic in a bit more detail with this Advantages Of End To End Encryption Methodology Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Protects Data From Hacking, Security In Transit, Compliance. This template is free to edit as deemed fit for your organization. Therefore download it now.


