Powerpoint Templates and Google slides for Handling Security Logs
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Measures To Handle Crash Of Security Systems At Hotel Training Ppt
Measures To Handle Crash Of Security Systems At Hotel Training PptPresenting Measures to Handle Crash of Security Systems at Hotel. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Multiple Solution To Handle Strategic Retirement Planning To Build Secure Future Fin SS
Multiple Solution To Handle Strategic Retirement Planning To Build Secure Future Fin SSThis slide shows multiple ways which can help individuals to overcome challenges related to healthcare cost. These solutions include cost estimation, consultation, regular health insurance review, etc. Increase audience engagement and knowledge by dispensing information using Multiple Solution To Handle Strategic Retirement Planning To Build Secure Future Fin SS. This template helps you present information on four stages. You can also present information on Cost Estimation, Consultation, Healthy Lifestyle Choices using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
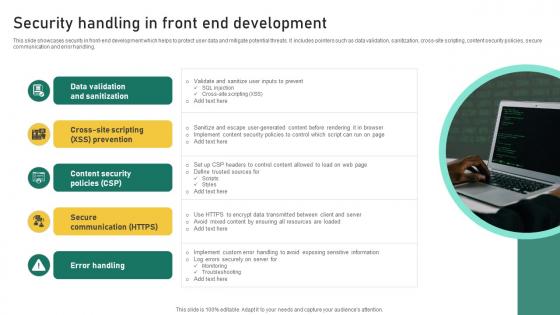 Security Handling In Front End Development
Security Handling In Front End DevelopmentThis slide showcases security in front-end development which helps to protect user data and mitigate potential threats. It includes pointers such as data validation, sanitization, cross-site scripting, content security policies, secure communication and error handling. Presenting our set of slides with Development. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Validation And Sanitization, Content Security Policies, Secure Communication.
-
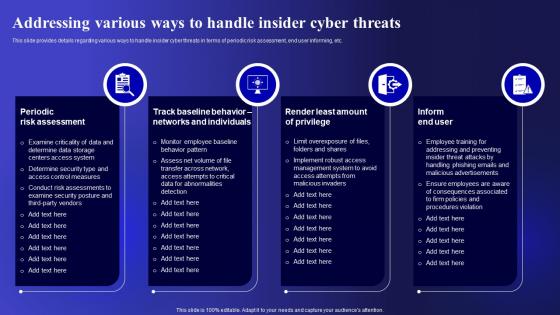 Addressing Various Ways To Handle Cyber Threats Management To Enable Digital Assets Security
Addressing Various Ways To Handle Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding various ways to handle insider cyber threats in terms of periodic risk assessment, end user informing, etc. Present the topic in a bit more detail with this Addressing Various Ways To Handle Cyber Threats Management To Enable Digital Assets Security. Use it as a tool for discussion and navigation on Periodic Risk Assessment, Individuals, Implement. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
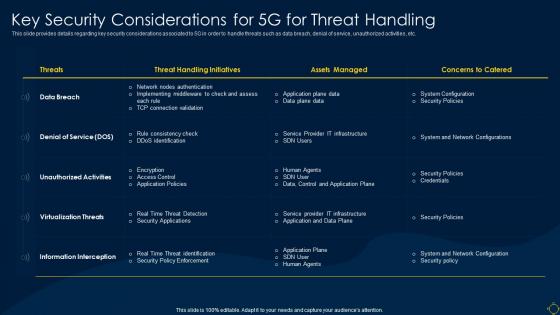 Key Security Considerations For 5g For Threat Handling Deployment Of 5g Wireless System
Key Security Considerations For 5g For Threat Handling Deployment Of 5g Wireless SystemThis slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. Present the topic in a bit more detail with this Key Security Considerations For 5g For Threat Handling Deployment Of 5g Wireless System. Use it as a tool for discussion and navigation on Considerations, Service, Unauthorized. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
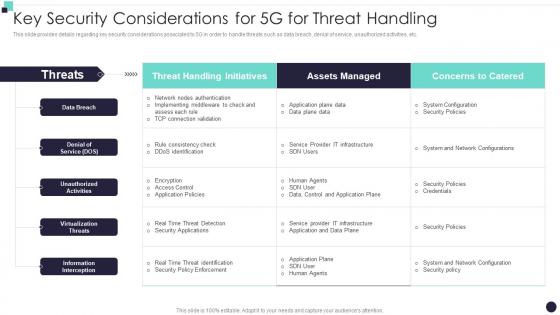 Key Security Considerations For 5G For Threat Handling Building 5G Wireless Mobile Network
Key Security Considerations For 5G For Threat Handling Building 5G Wireless Mobile NetworkThis slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. Present the topic in a bit more detail with this Key Security Considerations For 5G For Threat Handling Building 5G Wireless Mobile Network. Use it as a tool for discussion and navigation on Threat Handling Initiatives, Assets Managed, Denial Of Service. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
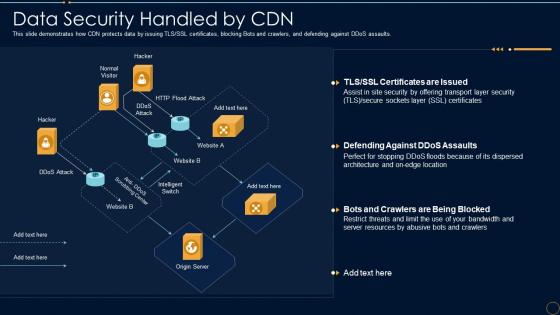 Content Delivery Network It Data Security Handled By Cdn
Content Delivery Network It Data Security Handled By CdnThis slide demonstrates how CDN protects data by issuing TLS or SSL certificates, blocking Bots and crawlers, and defending against DDoS assaults. Deliver an outstanding presentation on the topic using this Content Delivery Network It Data Security Handled By Cdn. Dispense information and present a thorough explanation of Data Security Handled By CDN using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Contingency Plan For Threat Handling In Security Centre Enabling It Intelligence Framework
Contingency Plan For Threat Handling In Security Centre Enabling It Intelligence FrameworkThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations.Present the topic in a bit more detail with this Contingency Plan For Threat Handling In Security Centre Enabling It Intelligence Framework Use it as a tool for discussion and navigation on Local Area Network, Mainframe Systems, Distributes Systems This template is free to edit as deemed fit for your organization. Therefore download it now.
-
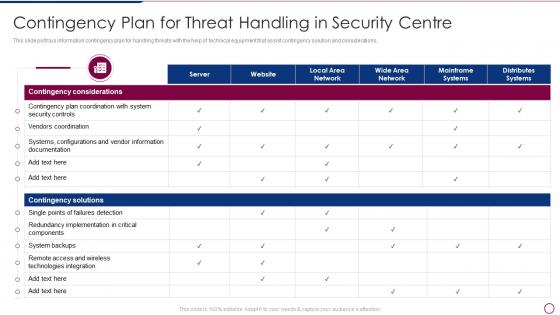 Unlocking Business Infrastructure Capabilities Contingency Plan For Threat Handling In Security Centre
Unlocking Business Infrastructure Capabilities Contingency Plan For Threat Handling In Security CentreThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Deliver an outstanding presentation on the topic using this Unlocking Business Infrastructure Capabilities Contingency Plan For Threat Handling In Security Centre. Dispense information and present a thorough explanation of Contingency Plan For Threat Handling In Security Centre using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
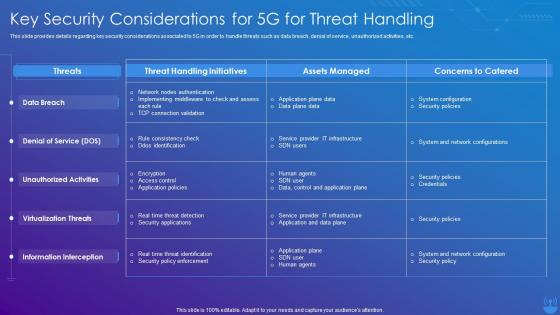 5G Technology Enabling Key Security Considerations For 5G For Threat Handling
5G Technology Enabling Key Security Considerations For 5G For Threat HandlingThis slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. Deliver an outstanding presentation on the topic using this 5G Technology Enabling Key Security Considerations For 5G For Threat Handling. Dispense information and present a thorough explanation of Threat Handling Initiatives, Concerns To Catered, Assets Managed using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
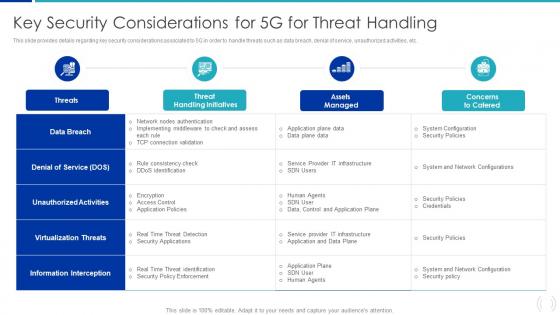 Key Security Considerations For 5G For Threat Handling Proactive Approach For 5G Deployment
Key Security Considerations For 5G For Threat Handling Proactive Approach For 5G DeploymentThis slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. Present the topic in a bit more detail with this Key Security Considerations For 5G For Threat Handling Proactive Approach For 5G Deployment. Use it as a tool for discussion and navigation on Virtualization Threats, Information Interception, Unauthorized Activities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Incident Response Playbook Impact Categories For Effectively Handling Cyber Security Incidents
Incident Response Playbook Impact Categories For Effectively Handling Cyber Security IncidentsMentioned slide provides information about the impact categories which can be used for effectively handling various cyber security incidents. Categories covered are function, information and recoverability impact. Increase audience engagement and knowledge by dispensing information using Incident Response Playbook Impact Categories For Effectively Handling Cyber Security Incidents. This template helps you present information on three stages. You can also present information on Functional Impact, Information Impact, Recoverability Impact using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
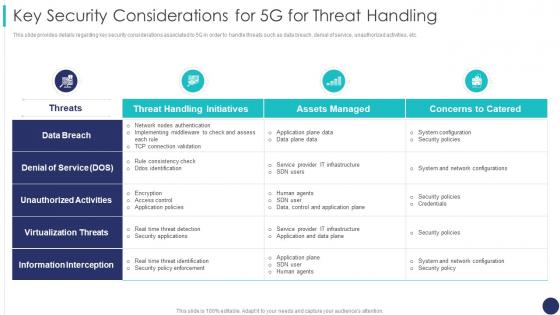 Key Security Considerations For 5g For Threat Handling 5g Mobile Technology Guidelines Operators
Key Security Considerations For 5g For Threat Handling 5g Mobile Technology Guidelines OperatorsThis slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. Deliver an outstanding presentation on the topic using this Key Security Considerations For 5g For Threat Handling 5g Mobile Technology Guidelines Operators. Dispense information and present a thorough explanation of Unauthorized Activities, Virtualization Threats, Information Interception using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 5g Network Architecture Guidelines Key Security Considerations For 5g For Threat Handling
5g Network Architecture Guidelines Key Security Considerations For 5g For Threat HandlingThis slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. Present the topic in a bit more detail with this 5g Network Architecture Guidelines Key Security Considerations For 5g For Threat Handling. Use it as a tool for discussion and navigation on Considerations, Associated, Unauthorized. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
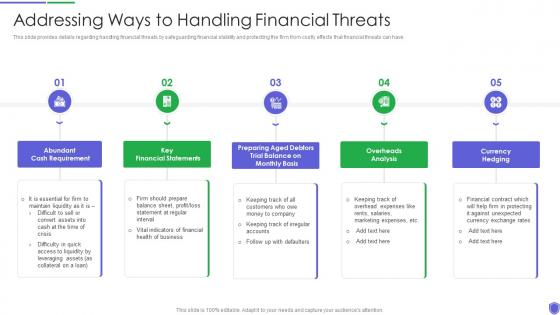 Addressing ways to handling managing critical threat vulnerabilities and security threats
Addressing ways to handling managing critical threat vulnerabilities and security threatsThis slide provides details regarding handling financial threats by safeguarding financial stability and protecting the firm from costly effects that financial threats can have. Introducing Addressing Ways To Handling Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Cash Requirement, Financial Statements, Overheads Analysis, Currency Hedging, using this template. Grab it now to reap its full benefits.
-
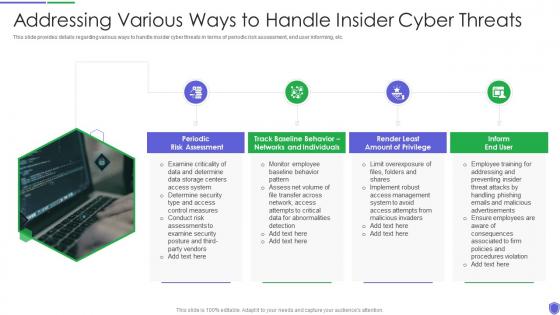 Managing critical threat vulnerabilities and security threats addressing various ways to handle
Managing critical threat vulnerabilities and security threats addressing various ways to handleThis slide provides details regarding various ways to handle insider cyber threats in terms of periodic risk assessment, end user informing, etc. Increase audience engagement and knowledge by dispensing information using Managing Critical Threat Vulnerabilities And Security Threats Addressing Various Ways To Handle. This template helps you present information on four stages. You can also present information on Risk Assessment, End User, Networks And Individuals using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
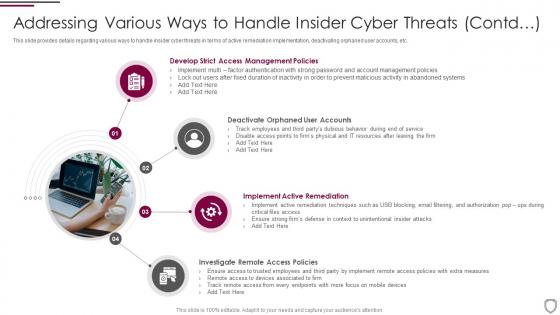 Addressing various ways to handle insider cyber threats corporate security management
Addressing various ways to handle insider cyber threats corporate security managementThis slide provides details regarding various ways to handle insider cyber threats in terms of active remediation implementation, deactivating orphaned user accounts, etc. Introducing Addressing Various Ways To Handle Insider Cyber Threats Corporate Security Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Management Policies, Implement Active Remediation, Investigate Remote Access Policies, Deactivate Orphaned User Accounts, using this template. Grab it now to reap its full benefits.
-
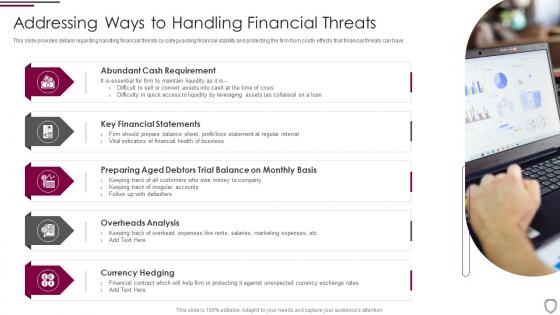 Addressing ways to handling financial threats corporate security management
Addressing ways to handling financial threats corporate security managementThis slide provides details regarding handling financial threats by safeguarding financial stability and protecting the firm from costly effects that financial threats can have. Increase audience engagement and knowledge by dispensing information using Addressing Ways To Handling Financial Threats Corporate Security Management. This template helps you present information on five stages. You can also present information on Abundant Cash Requirement, Key Financial Statements, Overheads Analysis, Currency Hedging using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
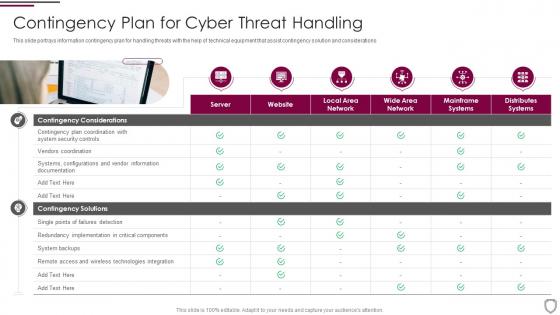 Contingency plan for cyber threat handling corporate security management
Contingency plan for cyber threat handling corporate security managementThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Increase audience engagement and knowledge by dispensing information using Contingency Plan For Cyber Threat Handling Corporate Security Management. This template helps you present information on one stages. You can also present information on Contingency Considerations, Contingency Solutions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
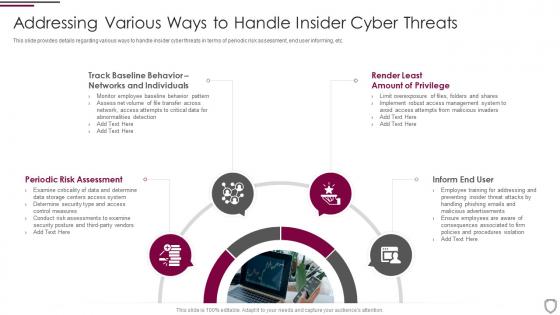 Corporate security management addressing various ways to handle insider cyber threats
Corporate security management addressing various ways to handle insider cyber threatsThis slide provides details regarding various ways to handle insider cyber threats in terms of periodic risk assessment, end user informing, etc. Introducing Corporate Security Management Addressing Various Ways To Handle Insider Cyber Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Periodic Risk Assessment, Inform End User, Render Least, Networks And Individuals, using this template. Grab it now to reap its full benefits.
-
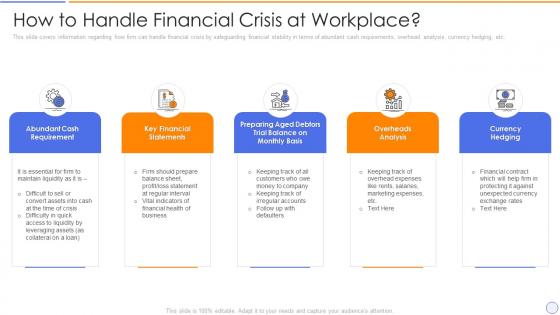 Building organizational security strategy plan handle financial crisis at workplace
Building organizational security strategy plan handle financial crisis at workplaceThis slide covers information regarding how firm can handle financial crisis by safeguarding financial stability in terms of abundant cash requirements, overhead analysis, currency hedging, etc. Introducing Building Organizational Security Strategy Plan Handle Financial Crisis At Workplace to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Information, Safeguarding, Financial, using this template. Grab it now to reap its full benefits.
-
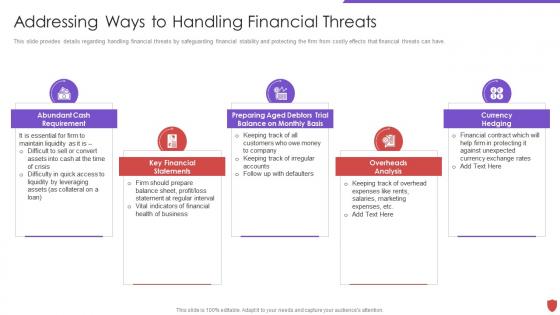 Addressing ways to handling financial threats cyber security risk management
Addressing ways to handling financial threats cyber security risk managementThis slide provides details regarding handling financial threats by safeguarding financial stability and protecting the firm from costly effects that financial threats can have. Introducing Addressing Ways To Handling Financial Threats Cyber Security Risk Management to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Abundant Cash Requirement, Key Financial Statements, Preparing Aged Debtors Trial Balance, using this template. Grab it now to reap its full benefits.
-
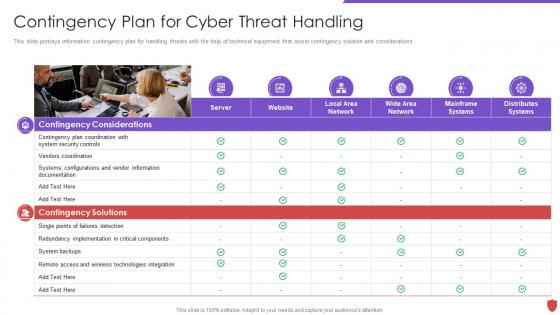 Cyber security risk management contingency plan for cyber threat handling
Cyber security risk management contingency plan for cyber threat handlingThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Introducing Cyber Security Risk Management Contingency Plan For Cyber Threat Handling to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Contingency Solutions, Contingency Considerations, System Backups, Vendors Coordination, using this template. Grab it now to reap its full benefits.
-
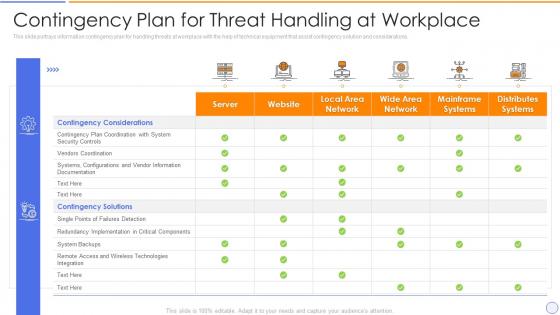 Building organizational security strategy plan contingency plan for threat handling at workplace
Building organizational security strategy plan contingency plan for threat handling at workplaceThis slide portrays information contingency plan for handling threats at workplace with the help of technical equipment that assist contingency solution and considerations. Present the topic in a bit more detail with this Building Organizational Security Strategy Plan Contingency Plan For Threat Handling At Workplace. Use it as a tool for discussion and navigation on Workplace, Information, Equipment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
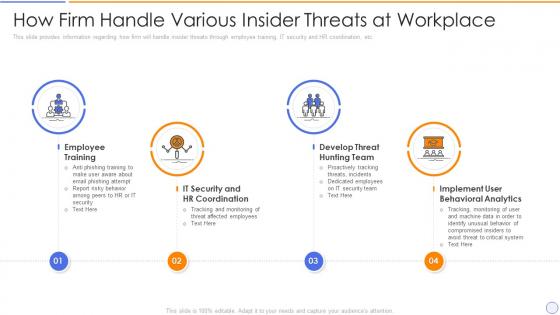 Building organizational security strategy plan how firm handle various insider threats at workplace
Building organizational security strategy plan how firm handle various insider threats at workplaceThis slide provides information regarding how firm will handle insider threats through employee training, IT security and HR coordination, etc. Introducing Building Organizational Security Strategy Plan How Firm Handle Various Insider Threats At Workplace to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Workplace, Information, Coordination, using this template. Grab it now to reap its full benefits.
-
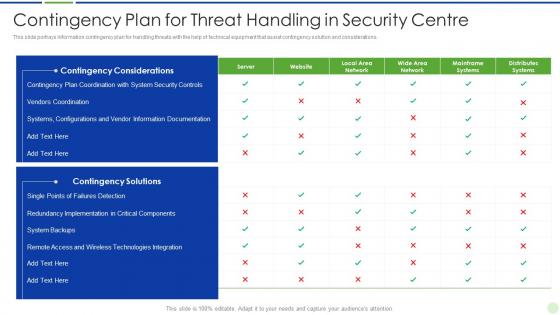 Implementing advanced analytics system at workplace contingency plan for threat handling security
Implementing advanced analytics system at workplace contingency plan for threat handling securityThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Deliver an outstanding presentation on the topic using this Implementing Advanced Analytics System At Workplace Contingency Plan For Threat Handling Security. Dispense information and present a thorough explanation of Contingency Plan For Threat Handling In Security Centre using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
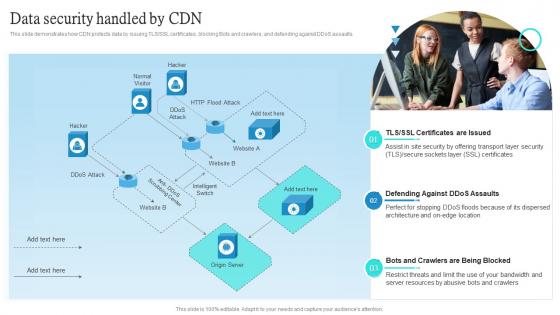 Data Security Handled By CDN Ppt Powerpoint Presentation Outline Influencers
Data Security Handled By CDN Ppt Powerpoint Presentation Outline InfluencersThis slide demonstrates how CDN protects data by issuing TLS or SSL certificates, blocking Bots and crawlers, and defending against DDoS assaults. Increase audience engagement and knowledge by dispensing information using Data Security Handled By CDN Ppt Powerpoint Presentation Outline Influencers. This template helps you present information on three stages. You can also present information on Layer Security, Server Resources, Restrict Threats using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
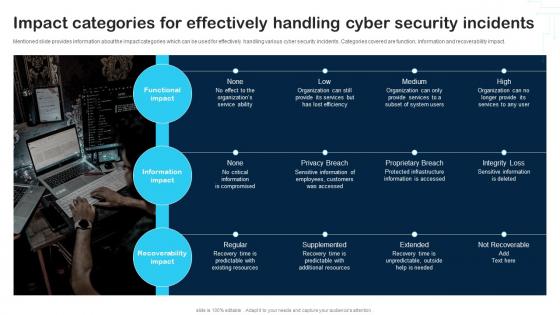 Impact Categories For Effectively Handling Cyber Security Incidents Cybersecurity Incident And Vulnerability
Impact Categories For Effectively Handling Cyber Security Incidents Cybersecurity Incident And VulnerabilityMentioned slide provides information about the impact categories which can be used for effectively handling various cyber security incidents. Categories covered are function, information and recoverability impact. Increase audience engagement and knowledge by dispensing information using Impact Categories For Effectively Handling Cyber Security Incidents Cybersecurity Incident And Vulnerability. This template helps you present information on three stages. You can also present information on Functional Impact, Information Impact, Recoverability Impact using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Determining Roles And Responsibilities For Risk Handling Unified Endpoint Security
Determining Roles And Responsibilities For Risk Handling Unified Endpoint SecurityThis slide provides information regarding the roles and responsibilities of management in handling mobile device security risks. Key people involved in risk handling are chief risk officer, chief information security officer, senior management and executives and line managers. Introducing Determining Roles And Responsibilities For Risk Handling Unified Endpoint Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Chief Information, Executive Management, Development Implementation, using this template. Grab it now to reap its full benefits.
-
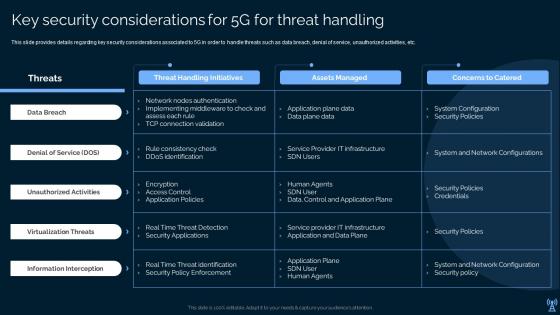 Key Security Considerations For 5g For Threat Handling Leading And Preparing For 5g World
Key Security Considerations For 5g For Threat Handling Leading And Preparing For 5g WorldPresent the topic in a bit more detail with this Key Security Considerations For 5g For Threat Handling Leading And Preparing For 5g World. Use it as a tool for discussion and navigation on Data Breach, Denial Of Service, Unauthorized Activities . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
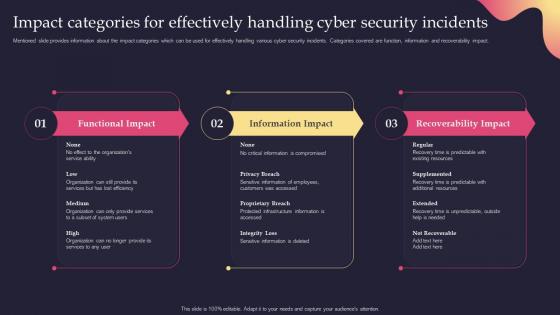 Security Incident Response Playbook Impact Categories For Effectively Handling Cyber Security Incidents
Security Incident Response Playbook Impact Categories For Effectively Handling Cyber Security IncidentsMentioned slide provides information about the impact categories which can be used for effectively handling various cyber security incidents. Categories covered are function, information and recoverability impact. Present the topic in a bit more detail with this Security Incident Response Playbook Impact Categories For Effectively Handling Cyber Security Incidents. Use it as a tool for discussion and navigation on Categories, Effectively, Information Impact. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
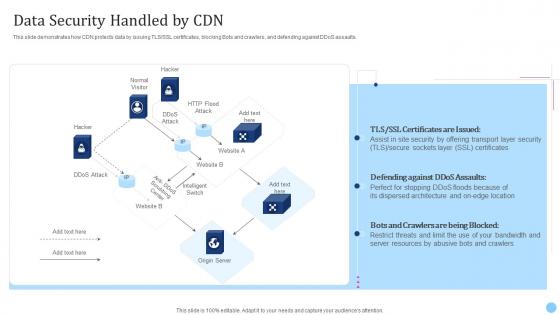 Data Security Handled By Cdn Cdn Edge Server Ppt Styles Graphics Design
Data Security Handled By Cdn Cdn Edge Server Ppt Styles Graphics DesignThis slide demonstrates how CDN protects data by issuing TLS or SSL certificates, blocking Bots and crawlers, and defending against DDoS assaults. Present the topic in a bit more detail with this Data Security Handled By Cdn Cdn Edge Server Ppt Styles Graphics Design. Use it as a tool for discussion and navigation on Certificates, Server, Resources. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
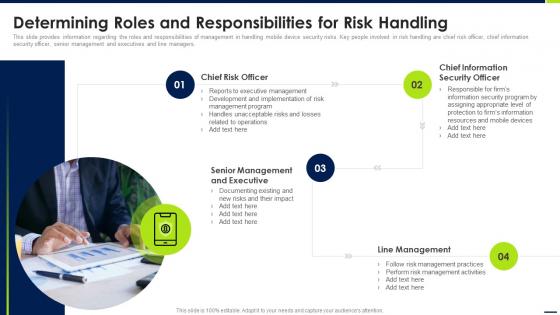 Determining Roles And Responsibilities For Risk Handling Android Device Security Management
Determining Roles And Responsibilities For Risk Handling Android Device Security ManagementThis slide provides information regarding the roles and responsibilities of management in handling mobile device security risks. Key people involved in risk handling are chief risk officer, chief information security officer, senior management and executives and line managers. Introducing Determining Roles And Responsibilities For Risk Handling Android Device Security Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Line Management, Senior Management, Chief Information Security Officer, using this template. Grab it now to reap its full benefits.
-
 Determining Roles And Responsibilities For Risk Handling Enterprise Mobile Security For On Device
Determining Roles And Responsibilities For Risk Handling Enterprise Mobile Security For On DeviceThis slide provides information regarding the roles and responsibilities of management in handling mobile device security risks. Key people involved in risk handling are chief risk officer, chief information security officer, senior management and executives and line managers. Increase audience engagement and knowledge by dispensing information using Determining Roles And Responsibilities For Risk Handling Enterprise Mobile Security For On Device. This template helps you present information on five stages. You can also present information on Security Program, Information Resources, Management Activities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
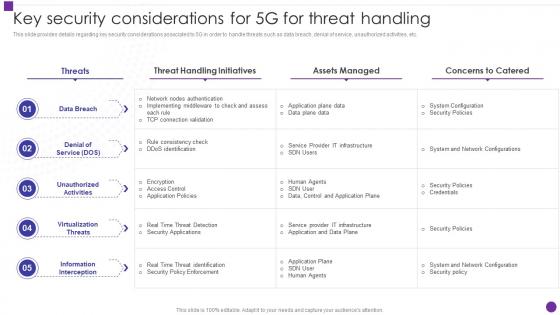 Key Security Considerations For 5g For Threat Handling Developing 5g Transformative Technology
Key Security Considerations For 5g For Threat Handling Developing 5g Transformative TechnologyThis slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. Deliver an outstanding presentation on the topic using this Key Security Considerations For 5g For Threat Handling Developing 5g Transformative Technology. Dispense information and present a thorough explanation of Considerations, Unauthorized Activities, Unauthorized Activities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
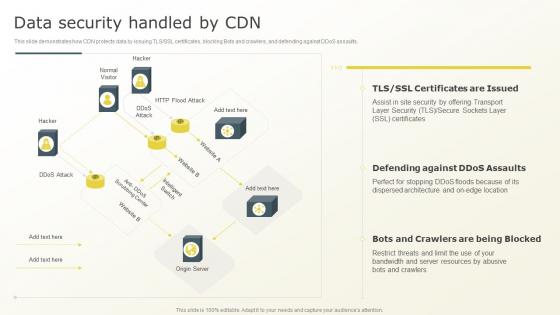 Data Security Handled By CDN Content Distribution Network Ppt Powerpoint Presentation File Example
Data Security Handled By CDN Content Distribution Network Ppt Powerpoint Presentation File ExampleThis slide demonstrates how CDN protects data by issuing TLS or SSL certificates, blocking Bots and crawlers, and defending against DDoS assaults.Present the topic in a bit more detail with this Data Security Handled By CDN Content Distribution Network Ppt Powerpoint Presentation File Example. Use it as a tool for discussion and navigation on Defending Against, Perfect For Stopping, Dispersed Architecture. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
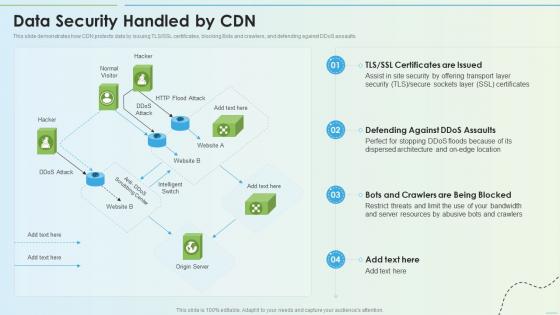 Data Security Handled By Cdn Delivery Network Ppt Slides Infographics
Data Security Handled By Cdn Delivery Network Ppt Slides InfographicsThis slide demonstrates how CDN protects data by issuing TLS or SSL certificates, blocking Bots and crawlers, and defending against DDoS assaults. Deliver an outstanding presentation on the topic using this Data Security Handled By Cdn Delivery Network Ppt Slides Infographics. Dispense information and present a thorough explanation of Resources, Location, Certificates using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Incident Handling Checklist Ppt Powerpoint Presentation Model Introduction
Cyber Security Incident Handling Checklist Ppt Powerpoint Presentation Model IntroductionThis slide represents the checklist to ensure activities to effectively handle and manage cyber security incidents. It includes details related to detection and analysis, containment, eradication and recovery and post incident activity. Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Handling Checklist Ppt Powerpoint Presentation Model Introduction. This template helps you present information on one stage. You can also present information on Detection And Analysis, Containment, Eradication And Recovery using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
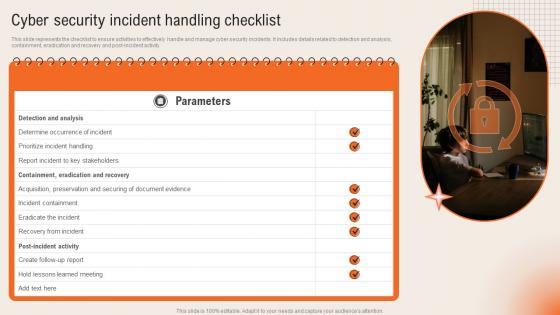 Cyber Security Incident Handling Checklist Deploying Computer Security Incident Management
Cyber Security Incident Handling Checklist Deploying Computer Security Incident ManagementThis slide represents the checklist to ensure activities to effectively handle and manage cyber security incidents. It includes details related to detection and analysis, containment, eradication and recovery and post incident activity.Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Handling Checklist Deploying Computer Security Incident Management. This template helps you present information on one stage. You can also present information on Containment Eradication, Acquisition Preservation, Incident Containment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
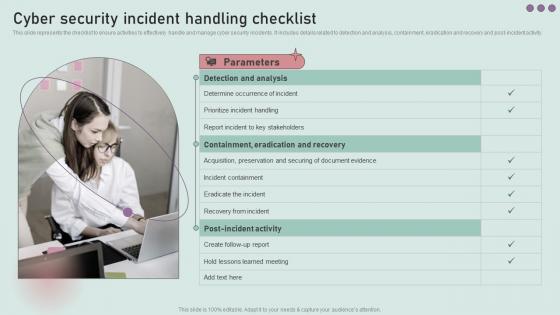 Cyber Security Incident Handling Checklist Development And Implementation Of Security
Cyber Security Incident Handling Checklist Development And Implementation Of SecurityThis slide represents the checklist to ensure activities to effectively handle and manage cyber security incidents. It includes details related to detection and analysis, containment, eradication and recovery and post incident activity. Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Handling Checklist Development And Implementation Of Security. This template helps you present information on three stages. You can also present information on Detection And Analysis, Prioritize Incident Handling, Incident Containment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
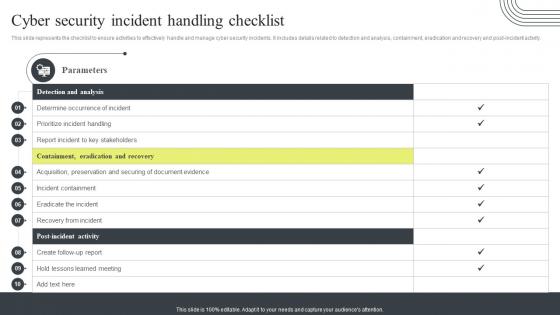 Cyber Security Incident Handling Checklist Cyber Security Attacks Response Plan
Cyber Security Incident Handling Checklist Cyber Security Attacks Response PlanThis slide represents the checklist to ensure activities to effectively handle and manage cyber security incidents. It includes details related to detection and analysis, containment, eradication and recovery and post incident activity. Present the topic in a bit more detail with this Cyber Security Incident Handling Checklist Cyber Security Attacks Response Plan. Use it as a tool for discussion and navigation on Containment, Eradication And Recovery, Detection And Analysis, Handling Checklist Acquisition. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Incident Handling Checklist Incident Response Strategies Deployment
Cyber Security Incident Handling Checklist Incident Response Strategies DeploymentThis slide represents the checklist to ensure activities to effectively handle and manage cyber security incidents. It includes details related to detection and analysis, containment, eradication and recovery and post incident activity. Introducing Cyber Security Incident Handling Checklist Incident Response Strategies Deployment to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Parameters, Analysis, Containment, using this template. Grab it now to reap its full benefits.
-
 Safety Guidelines For Handling Power Tools Best Practices For Workplace Security
Safety Guidelines For Handling Power Tools Best Practices For Workplace SecurityThis slide highlights the safety guidelines which showcases the general precautions while handling power tools to prevent accidents. It also highlights on different personal protective equipment while using toolsIntroducing Safety Guidelines For Handling Power Tools Best Practices For Workplace Security to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Chemical Hazards, Respiratory Training, Lockout Training, using this template. Grab it now to reap its full benefits.
-
 Computer security incident handling ppt powerpoint presentation infographics vector cpb
Computer security incident handling ppt powerpoint presentation infographics vector cpbPresenting this set of slides with name Computer Security Incident Handling Ppt Powerpoint Presentation Infographics Vector Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Computer Security Incident Handling to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Determining roles and responsibilities for risk handling security ppt file design
Determining roles and responsibilities for risk handling security ppt file designThis slide provides information regarding the roles and responsibilities of management in handling cyber security risks. Key people involved in risk handling are chief risk officer chief information security officer senior management and executives and line managers. Presenting this set of slides with name Determining Roles And Responsibilities For Risk Handling Security Ppt File Design. This is a one stage process. The stages in this process are Chief Risk Officer, Chief Information Security Officer, Senior Management And Executive, Line Management. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
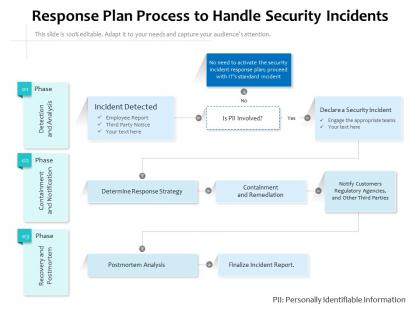 Response plan process to handle security incidents
Response plan process to handle security incidentsIntroducing our Response Plan Process To Handle Security Incidents set of slides. The topics discussed in these slides are Strategy, Analysis, Remediation. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Operator icon handling data center security
Operator icon handling data center securityIntroducing our Operator Icon Handling Data Center Security set of slides. The topics discussed in these slides are Operator Icon Handling Data Center Security. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
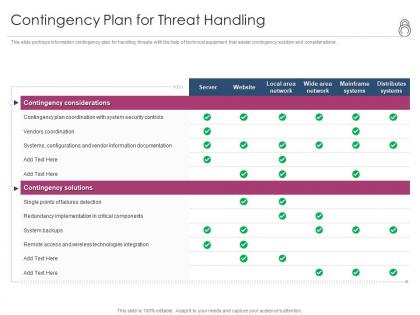 Enhanced security event management contingency plan for threat handling ppt powerpoint file
Enhanced security event management contingency plan for threat handling ppt powerpoint fileThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Present the topic in a bit more detail with this Enhanced Security Event Management Contingency Plan For Threat Handling Ppt Powerpoint File. Use it as a tool for discussion and navigation on Contingency Considerations, Mainframe Systems, Security, Implementation, Technologies Integration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
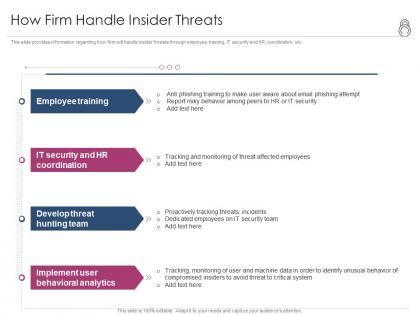 Enhanced security event management how firm handle insider threats ppt powerpoint slides tips
Enhanced security event management how firm handle insider threats ppt powerpoint slides tipsThis slide provides information regarding how firm will handle insider threats through employee training, IT security and HR coordination, etc. Introducing Enhanced Security Event Management How Firm Handle Insider Threats Ppt Powerpoint Slides Tips to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Employee Training, It Security And Hr Coordination, Develop Threat Hunting Team, Implement User Behavioral Analytics, using this template. Grab it now to reap its full benefits.
-
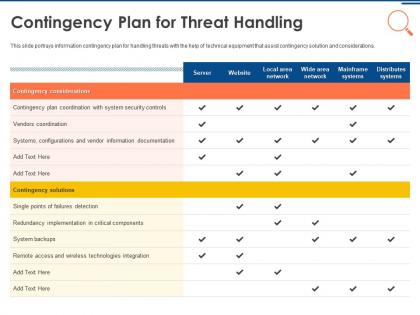 It security operations contingency plan for threat handling ppt powerpoint design ideas
It security operations contingency plan for threat handling ppt powerpoint design ideasThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Present the topic in a bit more detail with this IT Security Operations Contingency Plan For Threat Handling Ppt Powerpoint Design Ideas. Use it as a tool for discussion and navigation on Contingency Considerations, Mainframe Systems, Security, Implementation, Technologies Integration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 It security operations how firm handle insider threats ppt powerpoint file gallery
It security operations how firm handle insider threats ppt powerpoint file galleryThis slide provides information regarding how firm will handle insider threats through employee training, IT security and HR coordination, etc. Introducing IT Security Operations How Firm Handle Insider Threats Ppt Powerpoint File Gallery to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Employee Training, It Security And Hr Coordination, Develop Threat Hunting Team, Implement User Behavioral Analytics, using this template. Grab it now to reap its full benefits.
-
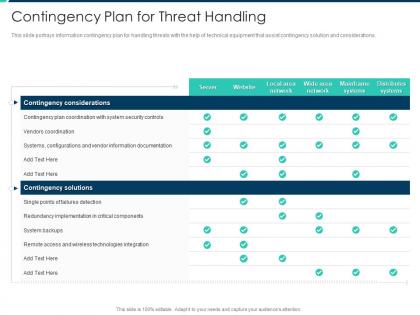 Contingency plan for threat handling security operations integration ppt diagrams
Contingency plan for threat handling security operations integration ppt diagramsThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Deliver an outstanding presentation on the topic using this Contingency Plan For Threat Handling Security Operations Integration Ppt Diagrams. Dispense information and present a thorough explanation of Contingency Considerations, Contingency Solutions, Redundancy Implementation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 How firm handle insider threats security operations integration ppt topics
How firm handle insider threats security operations integration ppt topicsThis slide provides information regarding how firm will handle insider threats through employee training, IT security and HR coordination, etc. Increase audience engagement and knowledge by dispensing information using How Firm Handle Insider Threats Security Operations Integration Ppt Topics. This template helps you present information on four stages. You can also present information on Employee Training, Develop Threat Hunting Team, Implement User Behavioral Analytics using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
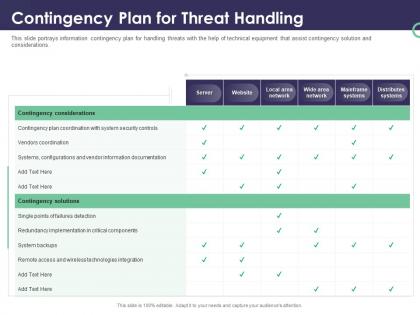 Enterprise security operations contingency plan for threat handling ppt powerpoint structure
Enterprise security operations contingency plan for threat handling ppt powerpoint structureThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Present the topic in a bit more detail with this Enterprise Security Operations Contingency Plan For Threat Handling Ppt Powerpoint Structure. Use it as a tool for discussion and navigation on Contingency Considerations, Mainframe Systems, Security, Implementation, Technologies Integration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Enterprise security operations how firm handle insider threats ppt powerpoint presentation model
Enterprise security operations how firm handle insider threats ppt powerpoint presentation modelThis slide provides information regarding how firm will handle insider threats through employee training, IT security and HR coordination, etc. Introducing Enterprise Security Operations How Firm Handle Insider Threats Ppt Powerpoint Presentation Model to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Employee Training, It Security And Hr Coordination, Develop Threat Hunting Team, Implement User Behavioral Analytics, using this template. Grab it now to reap its full benefits.

