Powerpoint Templates and Google slides for Identify Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Identifying Information Assets For Operational Security Training Ppt
Identifying Information Assets For Operational Security Training PptPresenting Identifying Information Assets for Operational Security. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Identifying Threats For Operational Security Training Ppt
Identifying Threats For Operational Security Training PptPresenting Identifying Threats for Operational Security. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Identifying Vulnerabilities For Operational Security Training Ppt
Identifying Vulnerabilities For Operational Security Training PptPresenting Identifying Vulnerabilities for Operational Security. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
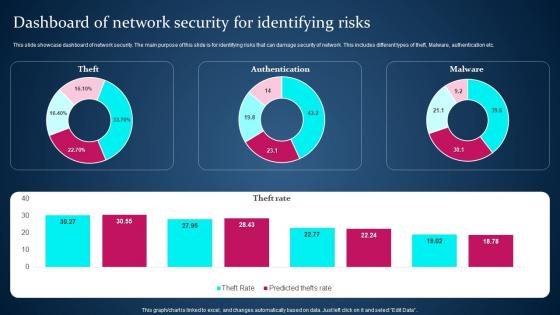 Dashboard Of Network Security For Identifying Risks
Dashboard Of Network Security For Identifying RisksThis slide showcase dashboard of network security. The main purpose of this slide is for identifying risks that can damage security of network. This includes different types of theft, Malware, authentication etc. Introducing our Dashboard Of Network Security For Identifying Risks set of slides. The topics discussed in these slides are Authentication, Theft Rate. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Identify Type Of Cybersecurity Risks And Attacks Improving Cyber Security Risks Management
Identify Type Of Cybersecurity Risks And Attacks Improving Cyber Security Risks ManagementThe following slide showcases the various types of cyber-attacks faced by employees to determine and formulate action plan. It includes elements such as malware, ransomware, man in the middle, phishing, denial of service etc. Introducing Identify Type Of Cybersecurity Risks And Attacks Improving Cyber Security Risks Management to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Spear Phishing, Advanced Persistent Threats, Ransomware, Phishing, using this template. Grab it now to reap its full benefits.
-
 Identify Function Activities In Cyber Security Framework
Identify Function Activities In Cyber Security FrameworkThis slide is an introduction to the key activities of identify function in cyber security framework which includes identify physical and software assets. Increase audience engagement and knowledge by dispensing information using Identify Function Activities In Cyber Security Framework. This template helps you present information on five stages. You can also present information on Identify Physical And Software Assets, Assess Asset Vulnerabilities, Conduct Risk Response Activities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
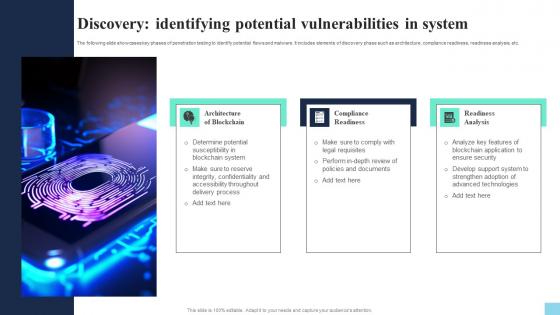 Discovery Identifying Potential Vulnerabilities In System Hands On Blockchain Security Risk BCT SS V
Discovery Identifying Potential Vulnerabilities In System Hands On Blockchain Security Risk BCT SS VThe following slide showcases key phases of penetration testing to identify potential flaws and malware. It includes elements of discovery phase such as architecture, compliance readiness, readiness analysis, etc. Introducing Discovery Identifying Potential Vulnerabilities In System Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Architecture Of Blockchain, Compliance Readiness, Readiness Analysis, using this template. Grab it now to reap its full benefits.
-
 Methods To Identify Crypto Phishing Scams Hands On Blockchain Security Risk BCT SS V
Methods To Identify Crypto Phishing Scams Hands On Blockchain Security Risk BCT SS VThe following slide illustrates various methods to determine blockchain phishing attack and safeguard confidential information. It includes elements such as copycatting, spellings, ambiguous links, using public email ID, disordered content etc. Increase audience engagement and knowledge by dispensing information using Methods To Identify Crypto Phishing Scams Hands On Blockchain Security Risk BCT SS V. This template helps you present information on five stages. You can also present information on Copycatting, Spelling, Ambiguous Links using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Discovery Identifying Potential Securing Blockchain Transactions A Beginners Guide BCT SS V
Discovery Identifying Potential Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases key phases of penetration testing to identify potential flaws and malware. It includes elements of discovery phase such as architecture, compliance readiness, readiness analysis, etc. Increase audience engagement and knowledge by dispensing information using Discovery Identifying Potential Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on three stages. You can also present information on Architecture Blockchain, Compliance Readiness, Readiness Analysis using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
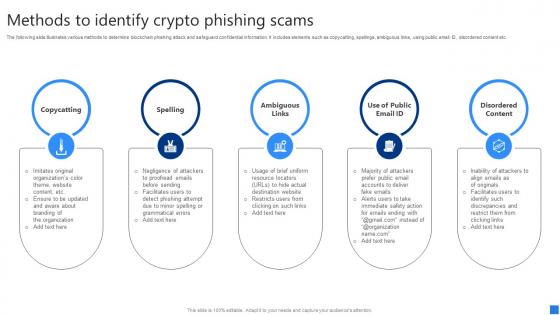 Methods To Identify Crypto Securing Blockchain Transactions A Beginners Guide BCT SS V
Methods To Identify Crypto Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide illustrates various methods to determine blockchain phishing attack and safeguard confidential information. It includes elements such as copycatting, spellings, ambiguous links, using public email ID, disordered content etc. Introducing Methods To Identify Crypto Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Copycatting, Spelling, Ambiguous Links, using this template. Grab it now to reap its full benefits.
-
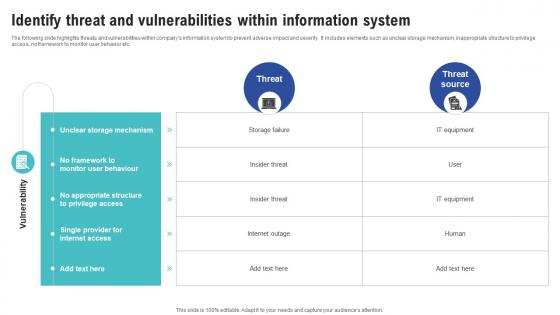 Identify Threat And Vulnerabilities Within Information System Creating Cyber Security Awareness
Identify Threat And Vulnerabilities Within Information System Creating Cyber Security AwarenessThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Deliver an outstanding presentation on the topic using this Identify Threat And Vulnerabilities Within Information System Creating Cyber Security Awareness Dispense information and present a thorough explanation of Unclear Storage Mechanism, Monitor User Behaviour, No Appropriate Structure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
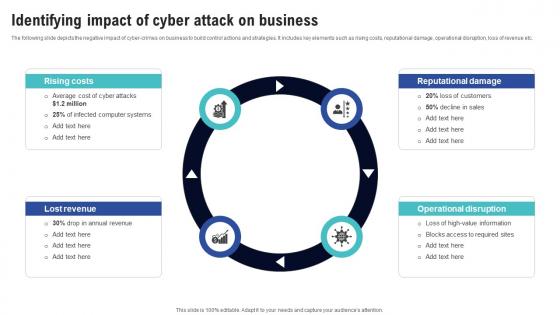 Identifying Impact Of Cyber Attack On Business Creating Cyber Security Awareness
Identifying Impact Of Cyber Attack On Business Creating Cyber Security AwarenessThe following slide depicts the negative impact of cyber-crimes on business to build control actions and strategies. It includes key elements such as rising costs, reputational damage, operational disruption, loss of revenue etc. Increase audience engagement and knowledge by dispensing information using Identifying Impact Of Cyber Attack On Business Creating Cyber Security Awareness This template helps you present information on Four stages. You can also present information on Small Size, Ransomware Attack, Cyber Attacks, Security Precautionary Measures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
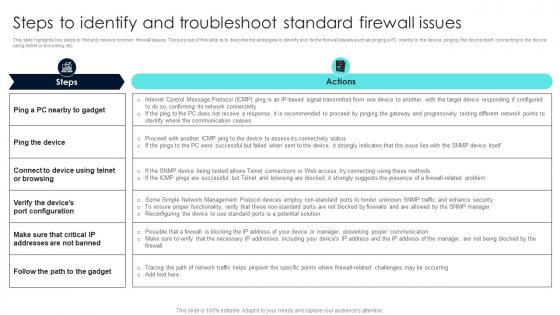 Firewall Network Security Steps To Identify And Troubleshoot Standard Firewall Issues
Firewall Network Security Steps To Identify And Troubleshoot Standard Firewall IssuesThis slide highlights key steps to find and resolve common firewall issues. The purpose of this slide is to describe the strategies to identify and fix the firewall issues such as pinging a PC nearby to the device, pinging the device itself, connecting to the device using telnet or browsing, etc. Deliver an outstanding presentation on the topic using this Firewall Network Security Steps To Identify And Troubleshoot Standard Firewall Issues Dispense information and present a thorough explanation of Nearby To Gadget, Path To The Gadget using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
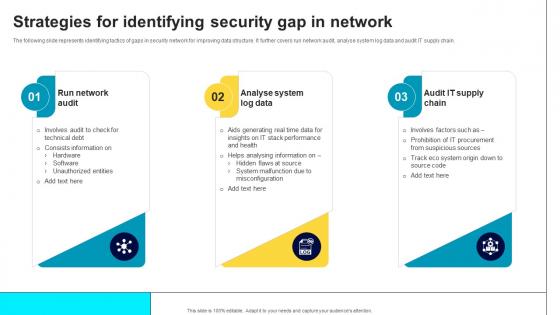 Strategies For Identifying Security Gap In Network
Strategies For Identifying Security Gap In NetworkThe following slide represents identifying tactics of gaps in security network for improving data structure. It further covers run network audit, analyse system log data and audit IT supply chain. Introducing our Strategies For Identifying Security Gap In Network set of slides. The topics discussed in these slides are Run Network Audit, Analyse System Log Data, Audit IT Supply Chain. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Triage Cyber Security To Identify Cyber Threats Icon
Triage Cyber Security To Identify Cyber Threats IconIntroducing our premium set of slides with name Triage Cyber Security To Identify Cyber Threats Icon Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Triage Cyber Security, Identify Cyber Threats Icon. So download instantly and tailor it with your information.
-
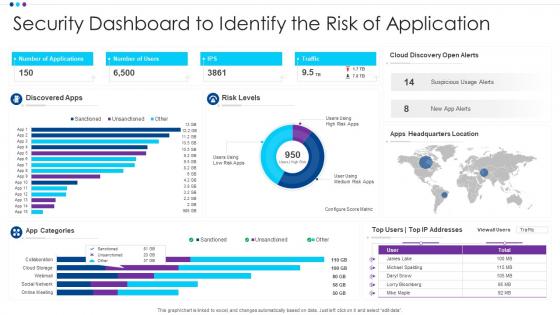 Security Dashboard To Identify The Risk Of Application
Security Dashboard To Identify The Risk Of ApplicationIntroducing our Security Dashboard To Identify The Risk Of Application set of slides. The topics discussed in these slides are App Categories, Discovered Apps, Risk Levels. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Kpi for average backup time security controls risks identified powerpoint slide
Kpi for average backup time security controls risks identified powerpoint slidePresenting kpi for average backup time security controls risks identified powerpoint slide. This presentation slide shows three Key Performance Indicators or KPIs in a Dashboard style design. The first KPI that can be shown is Average Time Between Tests of Backup. The second KPI is Proportion of Information Security Risks for Which Satisfactory Controls Have Been Fully Implemented and the third is Relative Proportions of Risks Identified. These KPI Powerpoint graphics are all data driven,and the shape automatically adjusts according to your data. Just right click on the KPI graphic,enter the right value and the shape will adjust automatically. Make a visual impact with our KPI slides.
-
 Criticality Assessment Of Identified Assets Introducing A Risk Based Approach To Cyber Security
Criticality Assessment Of Identified Assets Introducing A Risk Based Approach To Cyber SecurityFollowing slide demonstrates the asset criticality of identified system components. It covers details such as major components used along with criticality rating and failure cost.Deliver an outstanding presentation on the topic using this Criticality Assessment Of Identified Assets Introducing A Risk Based Approach To Cyber Security Dispense information and present a thorough explanation of Infrastructure Hardware, Routers And Switches, Server Computers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
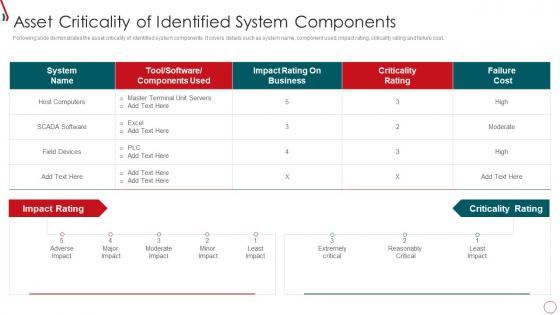 Risk Management Framework For Information Security Asset Criticality Of Identified System
Risk Management Framework For Information Security Asset Criticality Of Identified SystemFollowing slide demonstrates the asset criticality of identified system components. It covers details such as system name, component used, impact rating, criticality rating and failure cost. Present the topic in a bit more detail with this Risk Management Framework For Information Security Asset Criticality Of Identified System. Use it as a tool for discussion and navigation on Host Computers, Impact Rating, Criticality Rating, Failure Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
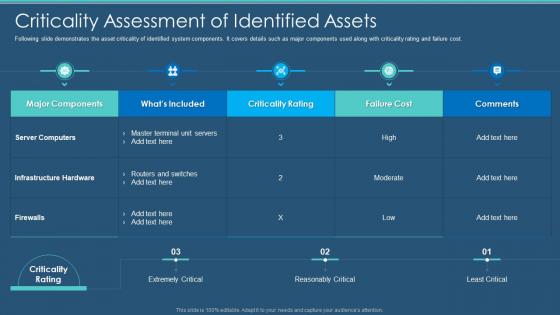 Cybersecurity Criticality Assessment Of Identified Assets Information Security Program
Cybersecurity Criticality Assessment Of Identified Assets Information Security ProgramFollowing slide demonstrates the asset criticality of identified system components. It covers details such as major components used along with criticality rating and failure cost. Present the topic in a bit more detail with this Cybersecurity Criticality Assessment Of Identified Assets Information Security Program. Use it as a tool for discussion and navigation on Criticality Assessment Of Identified Assets. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
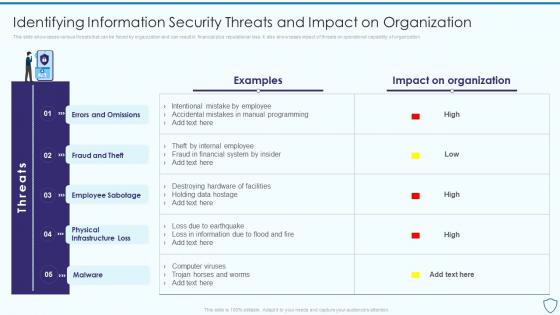 Identifying Information Security Threats And Risk Assessment And Management Plan For Information Security
Identifying Information Security Threats And Risk Assessment And Management Plan For Information SecurityThis slide showcases various threats that can be faced by organization and can result in financial plus reputational loss. It also showcases impact of threats on operational capability of organization Deliver an outstanding presentation on the topic using this Identifying Information Security Threats And Risk Assessment And Management Plan For Information Security. Dispense information and present a thorough explanation of Organization, Errors And Omissions, Employee Sabotage using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
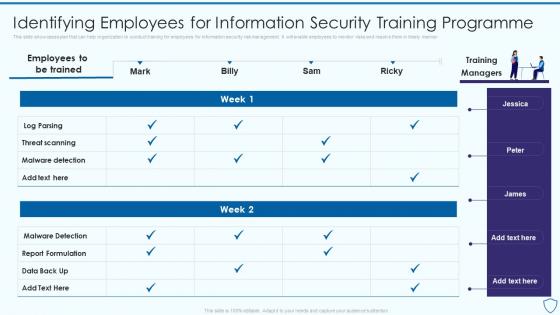 Risk Assessment And Management Plan For Information Security Identifying Employees For Information
Risk Assessment And Management Plan For Information Security Identifying Employees For InformationThis slide showcases plan that can help organization to conduct training for employees for information security risk management. It will enable employees to monitor risks and resolve them in timely manner Present the topic in a bit more detail with this Risk Assessment And Management Plan For Information Security Identifying Employees For Information. Use it as a tool for discussion and navigation on Information, Programme, Identifying. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
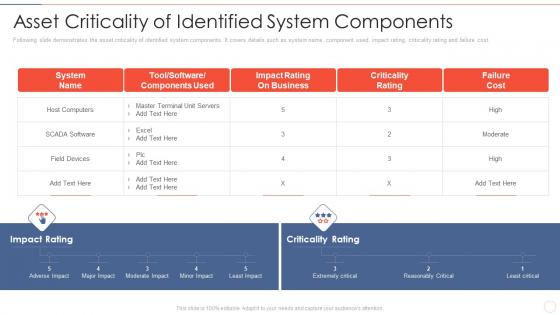 Effective information security asset criticality of identified system components
Effective information security asset criticality of identified system componentsFollowing slide demonstrates the asset criticality of identified system components. It covers details such as system name, component used, impact rating, criticality rating and failure cost. Deliver an outstanding presentation on the topic using this Effective Information Security Asset Criticality Of Identified System Components. Dispense information and present a thorough explanation of Host Computers, Impact Rating, Business, Criticality Rating using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
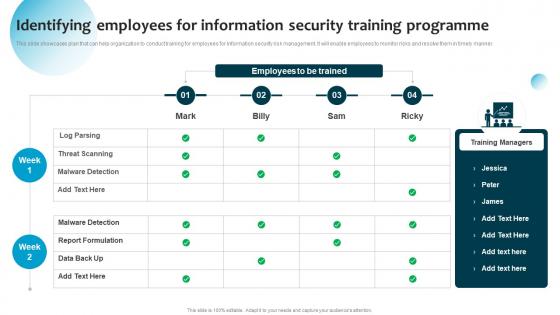 Identifying Employees For Information Security Training Information System Security And Risk Administration
Identifying Employees For Information Security Training Information System Security And Risk AdministrationThis slide showcases plan that can help organization to conduct training for employees for information security risk management. It will enable employees to monitor risks and resolve them in timely manner. Present the topic in a bit more detail with this Identifying Employees For Information Security Training Information System Security And Risk Administration. Use it as a tool for discussion and navigation on Threat Scanning, Malware Detection, Report Formulation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
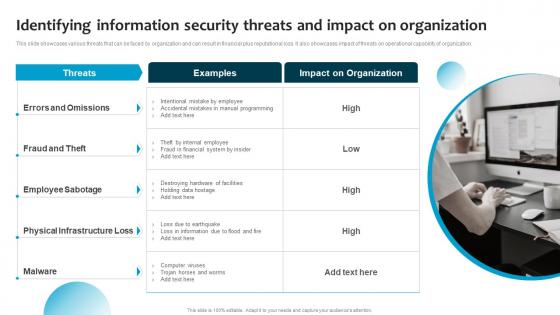 Information System Security And Risk Administration Plan Identifying Information Security Threats And Impact
Information System Security And Risk Administration Plan Identifying Information Security Threats And ImpactThis slide showcases various threats that can be faced by organization and can result in financial plus reputational loss. It also showcases impact of threats on operational capability of organization. Increase audience engagement and knowledge by dispensing information using Information System Security And Risk Administration Plan Identifying Information Security Threats And Impact. This template helps you present information on one stages. You can also present information on Employee Sabotage, Physical Infrastructure Loss, Threats using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cybersecurity Risk Analysis And Management Plan Identifying Employees For Information Security
Cybersecurity Risk Analysis And Management Plan Identifying Employees For Information SecurityThis slide showcases plan that can help organization to conduct training for employees for information security risk management. It will enable employees to monitor risks and resolve them in timely manner Deliver an outstanding presentation on the topic using this Cybersecurity Risk Analysis And Management Plan Identifying Employees For Information Security. Dispense information and present a thorough explanation of Identifying, Information, Training Programme using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Identifying Information Security Threats And Impact Cybersecurity Risk Analysis And Management Plan
Identifying Information Security Threats And Impact Cybersecurity Risk Analysis And Management PlanThis slide showcases various threats that can be faced by organization and can result in financial plus reputational loss. It also showcases impact of threats on operational capability of organization Present the topic in a bit more detail with this Identifying Information Security Threats And Impact Cybersecurity Risk Analysis And Management Plan. Use it as a tool for discussion and navigation on Identifying, Information, Organization. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
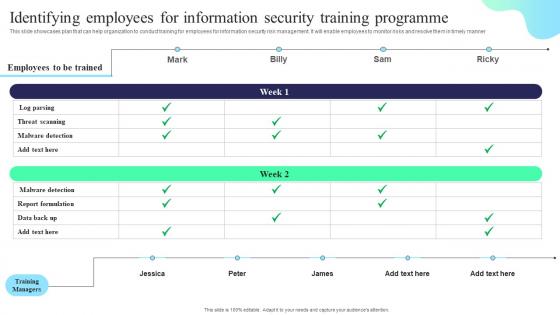 Identifying Employees For Information Security Training Formulating Cybersecurity Plan
Identifying Employees For Information Security Training Formulating Cybersecurity PlanThis slide showcases plan that can help organization to conduct training for employees for information security risk management. It will enable employees to monitor risks and resolve them in timely manner. Deliver an outstanding presentation on the topic using this Identifying Employees For Information Security Training Formulating Cybersecurity Plan. Dispense information and present a thorough explanation of Threat Scanning, Report Formulation, Training Programme using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Identifying Information Security Threats And Impact Formulating Cybersecurity Plan
Identifying Information Security Threats And Impact Formulating Cybersecurity PlanThis slide showcases various threats that can be faced by organization and can result in financial plus reputational loss. It also showcases impact of threats on operational capability of organization. Introducing Identifying Information Security Threats And Impact Formulating Cybersecurity Plan to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Errors And Omissions, Fraud And Theft, Employee Sabotage, using this template. Grab it now to reap its full benefits.
-
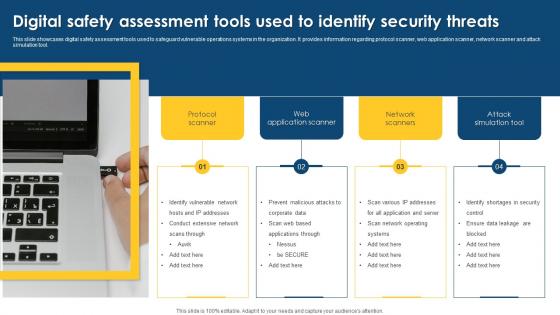 Digital Safety Assessment Tools Used To Identify Security Threats
Digital Safety Assessment Tools Used To Identify Security ThreatsThis slide showcases digital safety assessment tools used to safeguard vulnerable operations systems in the organization. It provides information regarding protocol scanner, web application scanner, network scanner and attack simulation tool. Presenting our well structured Digital Safety Assessment Tools Used To Identify Security Threats. The topics discussed in this slide are Assessment, Application, Identify Vulnerable. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Security Incident Response Playbook Asset Criticality Of Identified System Components
Security Incident Response Playbook Asset Criticality Of Identified System ComponentsMentioned slide demonstrates the asset criticality of identified system components. It includes information of system name, component used, impact rating, criticality rating and failure cost. Present the topic in a bit more detail with this Security Incident Response Playbook Asset Criticality Of Identified System Components. Use it as a tool for discussion and navigation on Identified, Components, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
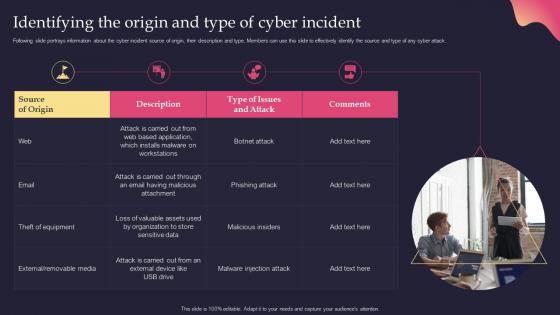 Security Incident Response Playbook Identifying The Origin And Type Of Cyber Incident
Security Incident Response Playbook Identifying The Origin And Type Of Cyber IncidentFollowing slide portrays information about the cyber incident source of origin, their description and type. Members can use this slide to effectively identify the source and type of any cyber attack. Present the topic in a bit more detail with this Security Incident Response Playbook Identifying The Origin And Type Of Cyber Incident. Use it as a tool for discussion and navigation on Identifying, Information, Description. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
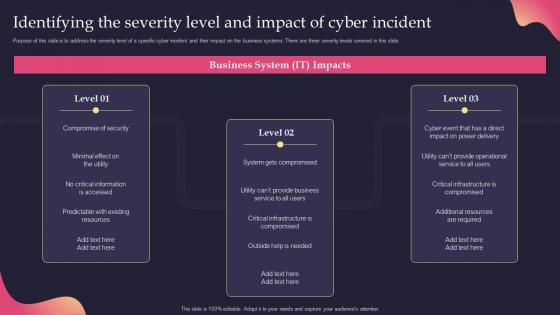 Security Incident Response Playbook Identifying The Severity Level And Impact Of Cyber Incident
Security Incident Response Playbook Identifying The Severity Level And Impact Of Cyber IncidentPurpose of this slide is to address the severity level of a specific cyber incident and their impact on the business systems. There are three severity levels covered in this slide. Deliver an outstanding presentation on the topic using this Security Incident Response Playbook Identifying The Severity Level And Impact Of Cyber Incident. Dispense information and present a thorough explanation of Identifying, Compromised, Business using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Identifying Employees For Information Information Security Risk Management
Identifying Employees For Information Information Security Risk ManagementThis slide showcases plan that can help organization to conduct training for employees for information security risk management. It will enable employees to monitor risks and resolve them in timely manner. Introducing Identifying Employees For Information Information Security Risk Management to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispense information on Threat Scanning, Identifying Employees, Security Training Programme, using this template. Grab it now to reap its full benefits.
-
 Identifying Information Security Threats And Impact Information Security Risk Management
Identifying Information Security Threats And Impact Information Security Risk ManagementThis slide showcases various threats that can be faced by organization and can result in financial plus reputational loss. It also showcases impact of threats on operational capability of organization. Increase audience engagement and knowledge by dispensing information using Identifying Information Security Threats And Impact Information Security Risk Management. This template helps you present information on one stage. You can also present information on Errors And Omissions, Employee Sabotage, Physical Infrastructure Loss using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
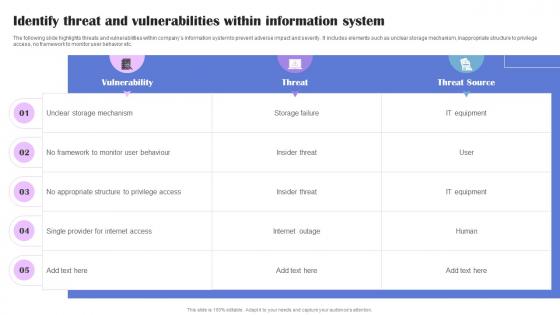 Identify Threat And Generating Security Awareness Among Employees To Reduce
Identify Threat And Generating Security Awareness Among Employees To ReduceThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Deliver an outstanding presentation on the topic using this Identify Threat And Generating Security Awareness Among Employees To Reduce Dispense information and present a thorough explanation of Unclear Storage Mechanism, Monitor User Behaviour using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
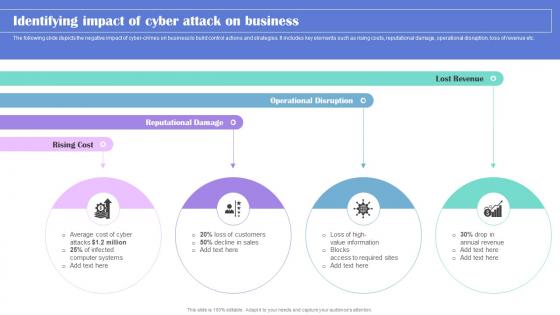 Identifying Impact Of Generating Security Awareness Among Employees To Reduce
Identifying Impact Of Generating Security Awareness Among Employees To ReduceThe following slide depicts the negative impact of cyber crimes on business to build control actions and strategies. It includes key elements such as rising costs, reputational damage, operational disruption, loss of revenue etc. Introducing Identifying Impact Of Generating Security Awareness Among Employees To Reduce to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Rising Cost, Reputational Damage using this template. Grab it now to reap its full benefits.
-
 Steps To Identify Organization Hazards And Risks Best Practices For Workplace Security
Steps To Identify Organization Hazards And Risks Best Practices For Workplace SecurityThis slide highlights the four steps to identify the organization risks which includes determine potential hazards, decide which employee at risk, evaluate risks with record findings and review.Deliver an outstanding presentation on the topic using this Steps To Identify Organization Hazards And Risks Best Practices For Workplace Security. Dispense information and present a thorough explanation of Assistance Necessary, Assist Workers, Provide Consulting using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
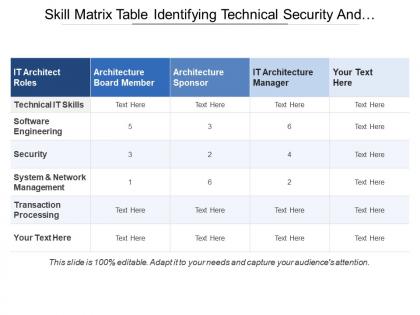 Skill matrix table identifying technical security and transaction processing
Skill matrix table identifying technical security and transaction processingPresenting this set of slides with name - Skill Matrix Table Identifying Technical Security And Transaction Processing. This is a three stage process. The stages in this process are Skill Matrix, Skill Mapping, Intelligence.
-
 Information security strategy identify data awareness and procedure
Information security strategy identify data awareness and procedurePresenting this set of slides with name - Information Security Strategy Identify Data Awareness And Procedure. This is a five stage process. The stages in this process are Information Security Strategy, Information Security Plan, Information Protection Strategy.
-
 Determine security variances identify environment exceptions identify necessary roles
Determine security variances identify environment exceptions identify necessary rolesPresenting this set of slides with name - Determine Security Variances Identify Environment Exceptions Identify Necessary Roles. This is an editable eight stages graphic that deals with topics like Determine Security Variances, Identify Environment Exceptions, Identify Necessary Roles to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Ecommerce business plan identifying security services and web design
Ecommerce business plan identifying security services and web designPresenting this set of slides with name - Ecommerce Business Plan Identifying Security Services And Web Design. This is a seven stage process. The stages in this process are Ecommerce Business Plan, Ecommerce Business Strategy, Ecommerce Business Approach.
-
 Identify development needs physiological job security personal growth
Identify development needs physiological job security personal growthPresenting this set of slides with name - Identify Development Needs Physiological Job Security Personal Growth. This is a five stage process. The stages in this process are Physiological, Job Security, Belonging, Self Esteem, Personal Growth.
-
 Identify development needs personal growth job security
Identify development needs personal growth job securityPresenting this set of slides with name - Identify Development Needs Personal Growth Job Security. This is a five stage process. The stages in this process are Physiological, Job Security, Belonging, Self Esteem, Personal Growth.
-
 Information security identifying vulnerabilities ppt powerpoint presentation file model cpb
Information security identifying vulnerabilities ppt powerpoint presentation file model cpbPresenting this set of slides with name Information Security Identifying Vulnerabilities Ppt Powerpoint Presentation File Model Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Information Security Identifying Vulnerabilities to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
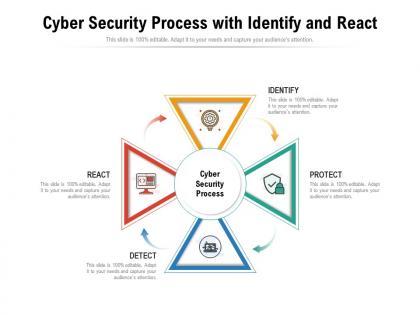 Cyber security process with identify and react
Cyber security process with identify and reactPresenting this set of slides with name Cyber Security Process With Identify And React. This is a four stage process. The stages in this process are Identify, Protect, Detect, React. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
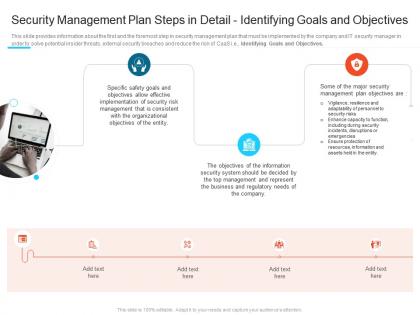 Identifying goals and objectives steps set up advanced security management plan ppt professional
Identifying goals and objectives steps set up advanced security management plan ppt professionalThis slide provides information about the first and the foremost step in security management plan that must be implemented by the company and IT security manager in order to solve potential insider threats, external security breaches and reduce the risk of CaaS i.e. Identifying Goals and Objectives. Introducing Identifying Goals And Objectives Steps Set Up Advanced Security Management Plan Ppt Professional to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Security Management Plan Steps In Detail - Identifying Goals And Objectives, using this template. Grab it now to reap its full benefits.
-
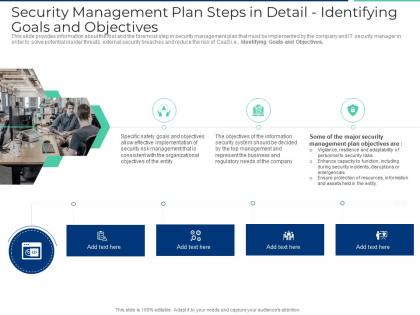 Security management plan steps in detail identifying goals and objectives ppt visuals
Security management plan steps in detail identifying goals and objectives ppt visualsThis slide provides information about the first and the foremost step in security management plan that must be implemented by the company and IT security manager in order to solve potential insider threats, external security breaches and reduce the risk of CaaS i.e. Identifying Goals and Objectives. Increase audience engagement and knowledge by dispensing information using Security Management Plan Steps In Detail Identifying Goals And Objectives Ppt Visuals. This template helps you present information on three stages. You can also present information on Management Plan, Security System, Risk Management, Safety Goals, Organizational Objectives using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.

