Powerpoint Templates and Google slides for Misuse
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
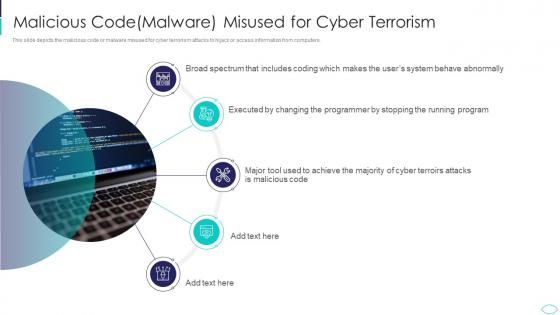 Malicious Codemalware Misused For Cyber Terrorism Cyber Terrorism Attacks
Malicious Codemalware Misused For Cyber Terrorism Cyber Terrorism AttacksThis slide depicts the malicious code or malware misused for cyber terrorism attacks to hijack or access information from computers. Increase audience engagement and knowledge by dispensing information using Malicious Codemalware Misused For Cyber Terrorism Cyber Terrorism Attacks. This template helps you present information on five stages. You can also present information on Malicious Code Malware Misused For Cyber Terrorism using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
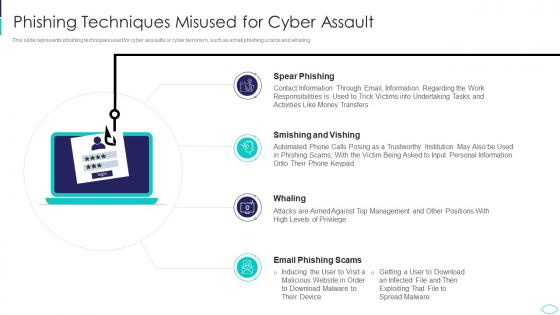 Phishing Techniques Misused For Cyber Assault Cyber Terrorism Attacks
Phishing Techniques Misused For Cyber Assault Cyber Terrorism AttacksThis slide represents phishing techniques used for cyber assaults or cyber terrorism, such as email phishing scams and whaling. Introducing Phishing Techniques Misused For Cyber Assault Cyber Terrorism Attacks to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Phishing Techniques Misused For Cyber Assault, using this template. Grab it now to reap its full benefits.
-
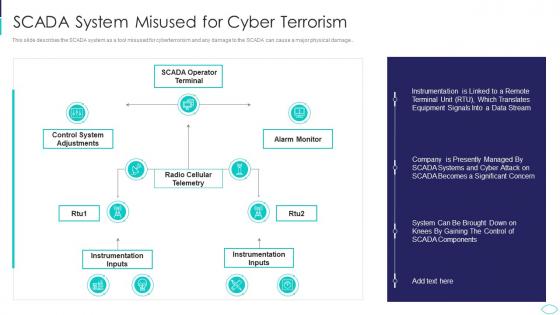 SCADA System Misused For Cyber Terrorism Cyber Terrorism Attacks
SCADA System Misused For Cyber Terrorism Cyber Terrorism AttacksThis slide describes the SCADA system as a tool misused for cyberterrorism and any damage to the SCADA can cause a major physical damage.. Present the topic in a bit more detail with this SCADA System Misused For Cyber Terrorism Cyber Terrorism Attacks. Use it as a tool for discussion and navigation on Scada System Misused For Cyber Terrorism. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
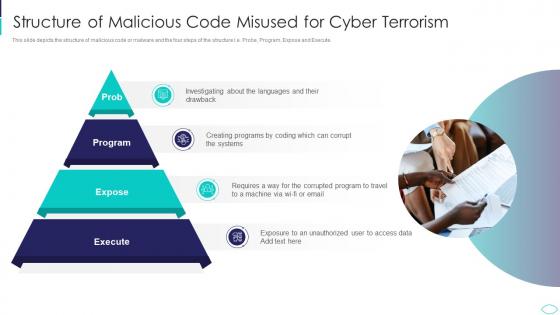 Structure Of Malicious Code Misused Cyber Terrorism Attacks
Structure Of Malicious Code Misused Cyber Terrorism AttacksThis slide depicts the structure of malicious code or malware and the four steps of the structure i.e. Probe, Program, Expose and Execute.Increase audience engagement and knowledge by dispensing information using Structure Of Malicious Code Misused Cyber Terrorism Attacks. This template helps you present information on four stages. You can also present information on Structure Of Malicious Code Misused For Cyber Terrorism using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
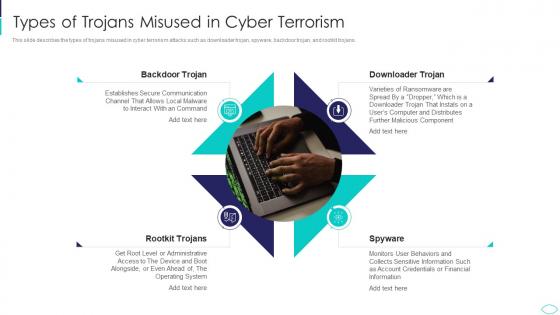 Types Of Trojans Misused In Cyber Terrorism Cyber Terrorism Attacks
Types Of Trojans Misused In Cyber Terrorism Cyber Terrorism AttacksThis slide describes the types of trojans misused in cyber terrorism attacks such as downloader trojan, spyware, backdoor trojan, and rootkit trojans. Increase audience engagement and knowledge by dispensing information using Types Of Trojans Misused In Cyber Terrorism Cyber Terrorism Attacks. This template helps you present information on four stages. You can also present information on Types Of Trojans Misused In Cyber Terrorism using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Complete Brand Marketing Playbook Company Logo Misuse Brand Playbook
Complete Brand Marketing Playbook Company Logo Misuse Brand PlaybookThis template covers the donts of company logo such as it is not allowed to alter the structure, colour, proportions, elements or the direction of the logo. Deliver an outstanding presentation on the topic using this Complete Brand Marketing Playbook Company Logo Misuse Brand Playbook. Dispense information and present a thorough explanation of Brand Playbook using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Company Logo Misuse Brand Playbook Ppt File Maker
Company Logo Misuse Brand Playbook Ppt File MakerThis template covers the don ts of company logo such as it is not allowed to alter the structure, colour, proportions, elements or the direction of the logo. Introducing Company Logo Misuse Brand Playbook Ppt File Maker to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Transparency, Octothorpe, Location, using this template. Grab it now to reap its full benefits.
-
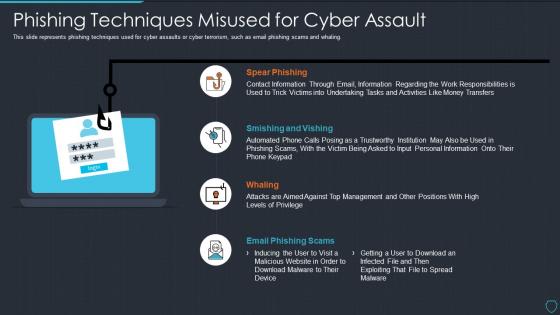 Cyberterrorism it phishing techniques misused for cyber assault
Cyberterrorism it phishing techniques misused for cyber assaultThis slide represents phishing techniques used for cyber assaults or cyber terrorism, such as email phishing scams and whaling. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Phishing Techniques Misused For Cyber Assault. This template helps you present information on four stages. You can also present information on Spear Phishing, Smishing And Vishing, Whaling, Email Phishing Scams using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
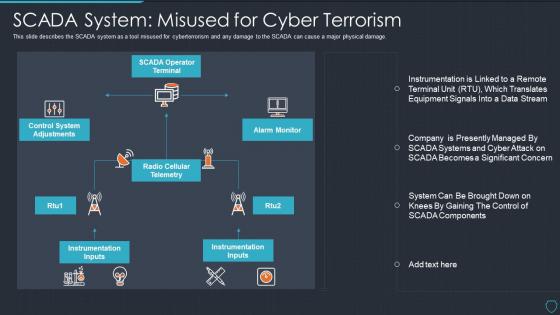 Cyberterrorism it scada system misused for cyber terrorism
Cyberterrorism it scada system misused for cyber terrorismThis slide describes the SCADA system as a tool misused for cyberterrorism and any damage to the SCADA can cause a major physical damage. Introducing Cyberterrorism IT SCADA System Misused For Cyber Terrorism to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on SCADA Operator Terminal, Alarm Monitor, Radio Cellular Telemetry, Control System Adjustments, Instrumentation Inputs, using this template. Grab it now to reap its full benefits.
-
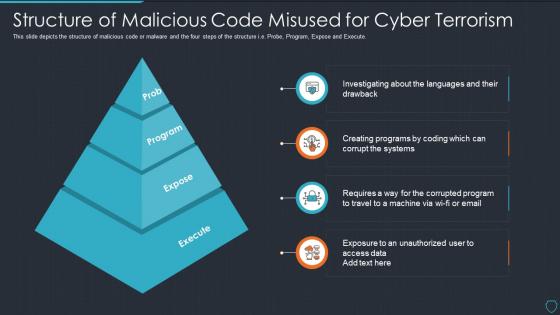 Cyberterrorism it structure of malicious code misused for cyber terrorism
Cyberterrorism it structure of malicious code misused for cyber terrorismThis slide depicts the structure of malicious code or malware and the four steps of the structure i.e. Probe, Program, Expose and Execute. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Structure Of Malicious Code Misused For Cyber Terrorism. This template helps you present information on four stages. You can also present information on Prob, Program, Expose, Execute using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
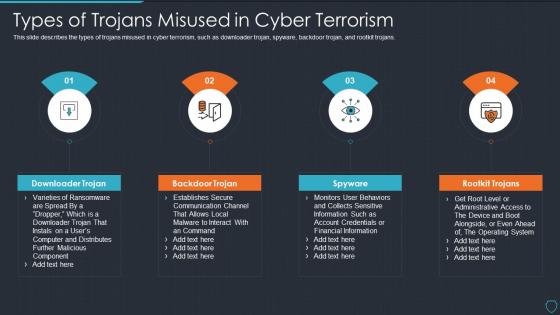 Cyberterrorism it types of trojans misused in cyber terrorism ppt slides tips
Cyberterrorism it types of trojans misused in cyber terrorism ppt slides tipsThis slide describes the types of trojans misused in cyber terrorism, such as downloader trojan, spyware, backdoor trojan, and rootkit trojans. Introducing Cyberterrorism IT Types Of Trojans Misused In Cyber Terrorism Ppt Slides Tips to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Downloader Trojan, Backdoor Trojan, Spyware, Rootkit Trojans, using this template. Grab it now to reap its full benefits.
-
 Branding Guidelines Playbook Company Logo Misuse Brand Playbook
Branding Guidelines Playbook Company Logo Misuse Brand PlaybookThis template covers the donts of company logo such as it is not allowed to alter the structure, colour, proportions, elements or the direction of the logo. Deliver an outstanding presentation on the topic using this Branding Guidelines Playbook Company Logo Misuse Brand Playbook. Dispense information and present a thorough explanation of Do Not Shuffle Colours Of Octothorpe, Do Not Use Different Colors, Do Not Alter The Logo Transparency using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Company Logo Misuse Brand Strategy Playbook Ppt Structure
Company Logo Misuse Brand Strategy Playbook Ppt StructureThis template covers the donts of company logo such as it is not allowed to alter the structure, colour, proportions, elements or the direction of the logo. Introducing Company Logo Misuse Brand Strategy Playbook Ppt Structure to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Company Logo Misuse, Brand Strategy Playbook, using this template. Grab it now to reap its full benefits.
-
 Company Logo Misuse Brand Playbook Employer Brand Playbook
Company Logo Misuse Brand Playbook Employer Brand PlaybookThis template covers the donts of company logo such as it is not allowed to alter the structure, colour, proportions, elements or the direction of the logo. Introducing Company Logo Misuse Brand Playbook Employer Brand Playbook to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Location, Outline Logotype, using this template. Grab it now to reap its full benefits.
-
 Data Misuse Examples In Powerpoint And Google Slides Cpb
Data Misuse Examples In Powerpoint And Google Slides CpbPresenting our Data Misuse Examples In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Data Misuse Examples This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Risks involved in holding company including power misuse
Risks involved in holding company including power misusePresenting this set of slides with name Risks Involved In Holding Company Including Power Misuse. This is a six stage process. The stages in this process are Holding Company, Business Strategies, Business Objectives. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Drugs and alcohol misuse ppt powerpoint presentation outline infographic template
Drugs and alcohol misuse ppt powerpoint presentation outline infographic templatePresenting this set of slides with name Drugs And Alcohol Misuse Ppt Powerpoint Presentation Outline Infographic Template. The topics discussed in these slides are Drugs And Alcohol Misuse. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
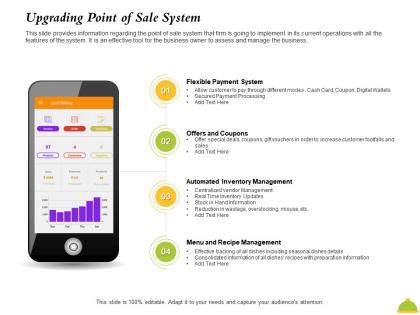 Upgrading point of sale system misuse ppt powerpoint presentation ideas clipart images
Upgrading point of sale system misuse ppt powerpoint presentation ideas clipart imagesThis slide provides information regarding the point of sale system that firm is going to implement in its current operations with all the features of the system. It is an effective tool for the business owner to assess and manage the business. Presenting this set of slides with name Upgrading Point Of Sale System Misuse Ppt Powerpoint Presentation Ideas Clipart Images. This is a four stage process. The stages in this process are Payment System, Automated Inventory Management, Recipe Management. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Company Logo Misuse Brand Playbook One Pager Sample Example Document
Company Logo Misuse Brand Playbook One Pager Sample Example DocumentThis is a One Pager titled Company Logo Misuse Brand Playbook One Pager Sample Example Document featuring A4 size content and graphics. It is designed in PowerPoint by an expert and is 100 percent editable. You can also access it with Google Slides.
-
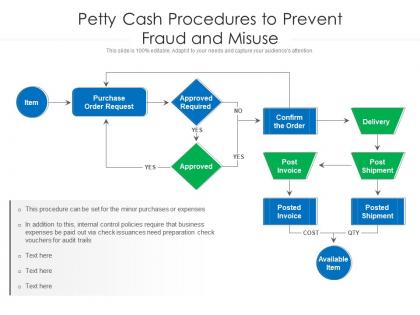 Petty cash procedures to prevent fraud and misuse
Petty cash procedures to prevent fraud and misusePresenting our well-structured Petty Cash Procedures To Prevent Fraud And Misuse. The topics discussed in this slide are Purchase, Business, Expenses. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
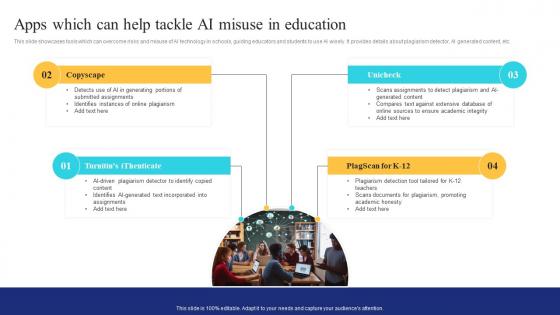 Apps Can Help Tackle Ai Misuse In Education Ai In Education Transforming Teaching And Learning AI SS
Apps Can Help Tackle Ai Misuse In Education Ai In Education Transforming Teaching And Learning AI SSThis slide showcases tools which can overcome risks and misuse of AI technology in schools, guiding educators and students to use AI wisely. It provides details about plagiarism detector, AI generated content, etc. Increase audience engagement and knowledge by dispensing information using Apps Can Help Tackle Ai Misuse In Education Ai In Education Transforming Teaching And Learning AI SS. This template helps you present information on four stages. You can also present information on Documents, Plagiarism, Promoting using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.

