Powerpoint Templates and Google slides for Obtaining Hardware
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
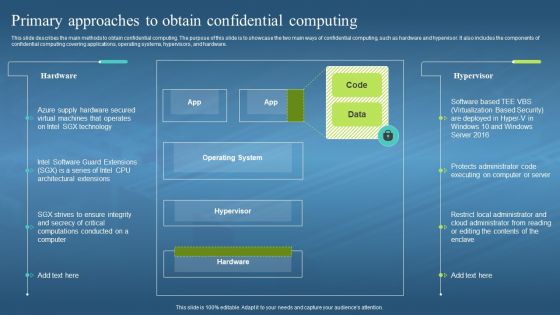 Confidential Computing Hardware Primary Approaches To Obtain Confidential Computing
Confidential Computing Hardware Primary Approaches To Obtain Confidential ComputingThis slide describes the main methods to obtain confidential computing. The purpose of this slide is to showcase the two main ways of confidential computing, such as hardware and hypervisor. It also includes the components of confidential computing covering applications, operating systems, hypervisors, and hardware. Deliver an outstanding presentation on the topic using this Confidential Computing Hardware Primary Approaches To Obtain Confidential Computing. Dispense information and present a thorough explanation of Operating System, Hypervisor, Restrict Local Administrator, Cloud Administrator using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.

