Powerpoint Templates and Google slides for Plan Attacks
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Cyber Security Attacks Response Plan Powerpoint Presentation Slides V
Cyber Security Attacks Response Plan Powerpoint Presentation Slides VEnthrall your audience with this Cyber Security Attacks Response Plan Powerpoint Presentation Slides. Increase your presentation threshold by deploying this well-crafted template. It acts as a great communication tool due to its well-researched content. It also contains stylized icons, graphics, visuals etc, which make it an immediate attention-grabber. Comprising sixty eight slides, this complete deck is all you need to get noticed. All the slides and their content can be altered to suit your unique business setting. Not only that, other components and graphics can also be modified to add personal touches to this prefabricated set.
-
 Security Plan To Prevent Cyber Attacks Powerpoint Presentation Slides
Security Plan To Prevent Cyber Attacks Powerpoint Presentation SlidesDeliver an informational PPT on various topics by using this Security Plan To Prevent Cyber Attacks Powerpoint Presentation Slides. This deck focuses and implements best industry practices, thus providing a birds-eye view of the topic. Encompassed with forty slides, designed using high-quality visuals and graphics, this deck is a complete package to use and download. All the slides offered in this deck are subjective to innumerable alterations, thus making you a pro at delivering and educating. You can modify the color of the graphics, background, or anything else as per your needs and requirements. It suits every business vertical because of its adaptable layout.
-
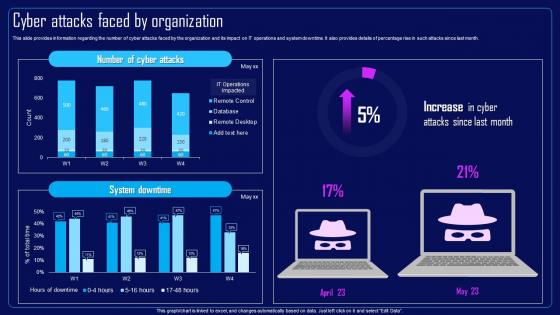 Action Plan To Combat Cyber Crimes Cyber Attacks Faced By Organization
Action Plan To Combat Cyber Crimes Cyber Attacks Faced By OrganizationThis slide provides information regarding the number of cyber attacks faced by the organization and its impact on IT operations and system downtime. It also provides details of percentage rise in such attacks since last month. Deliver an outstanding presentation on the topic using this Action Plan To Combat Cyber Crimes Cyber Attacks Faced By Organization. Dispense information and present a thorough explanation of Cyber Attacks Faced By Organization, IT Operations And System Downtime, Remote Desktop using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
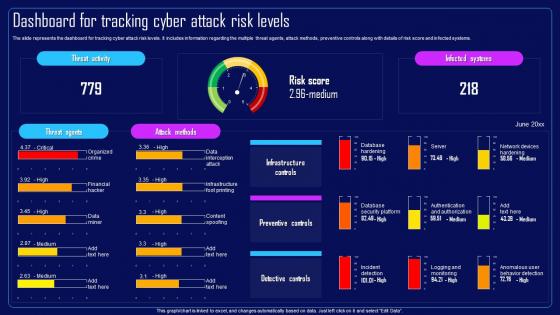 Action Plan To Combat Cyber Crimes Dashboard For Tracking Cyber Attack Risk Levels
Action Plan To Combat Cyber Crimes Dashboard For Tracking Cyber Attack Risk LevelsThe slide represents the dashboard for tracking cyber attack risk levels. It includes information regarding the multiple threat agents, attack methods, preventive controls along with details of risk score and infected systems. Deliver an outstanding presentation on the topic using this Action Plan To Combat Cyber Crimes Dashboard For Tracking Cyber Attack Risk Levels. Dispense information and present a thorough explanation of Dashboard For Tracking, Cyber Attack Risk Levels, Risk Score And Infected Systems, Preventive Controls using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
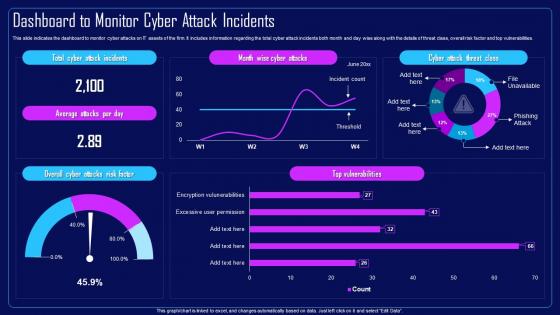 Action Plan To Combat Cyber Crimes Dashboard To Monitor Cyber Attack Incidents
Action Plan To Combat Cyber Crimes Dashboard To Monitor Cyber Attack IncidentsThis slide indicates the dashboard to monitor cyber attacks on IT assets of the firm. It includes information regarding the total cyber attack incidents both month and day wise along with the details of threat class, overall risk factor and top vulnerabilities. Present the topic in a bit more detail with this Action Plan To Combat Cyber Crimes Dashboard To Monitor Cyber Attack Incidents. Use it as a tool for discussion and navigation on Dashboard To Monitor, Cyber Attacks, IT Assets Of The Firm, Risk Factor And Top Vulnerabilities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
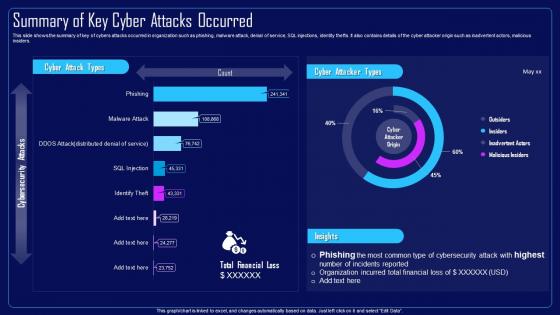 Action Plan To Combat Cyber Crimes Summary Of Key Cyber Attacks Occurred
Action Plan To Combat Cyber Crimes Summary Of Key Cyber Attacks OccurredThis slide shows the summary of key of cybers attacks occurred in organization such as phishing, malware attack, denial of service, SQL injections, identity thefts. It also contains details of the cyber attacker origin such as inadvertent actors, malicious insiders. Present the topic in a bit more detail with this Action Plan To Combat Cyber Crimes Summary Of Key Cyber Attacks Occurred. Use it as a tool for discussion and navigation on Cybers Attacks Occurred In Organization, Malware Attack, Denial Of Service, SQL Injections, Inadvertent Actors, Malicious Insiders. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Compressive Planning Guide Cyber Attacks Faced By Organization
Compressive Planning Guide Cyber Attacks Faced By OrganizationThis slide provides information regarding the number of cyber attacks faced by the organization and its impact on IT operations and system downtime. It also provides details of percentage rise in such attacks since last month. Deliver an outstanding presentation on the topic using this Compressive Planning Guide Cyber Attacks Faced By Organization. Dispense information and present a thorough explanation of Cyber Attacks, IT Operations, System Downtime using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
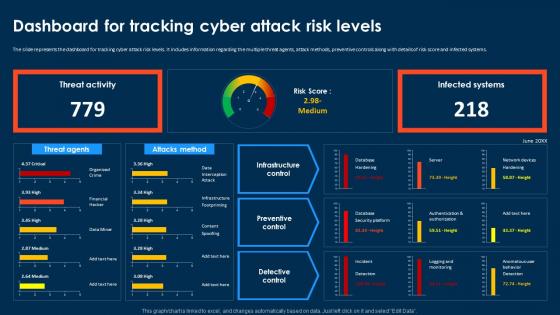 Compressive Planning Guide Dashboard For Tracking Cyber Attack Risk Levels
Compressive Planning Guide Dashboard For Tracking Cyber Attack Risk LevelsThe slide represents the dashboard for tracking cyber attack risk levels. It includes information regarding the multiple threat agents, attack methods, preventive controls along with details of risk score and infected systems. Deliver an outstanding presentation on the topic using this Compressive Planning Guide Dashboard For Tracking Cyber Attack Risk Levels. Dispense information and present a thorough explanation of Dashboard For Tracking, Cyber Attack Risk Levels, Preventive Controls, Risk Score And Infected Systems using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
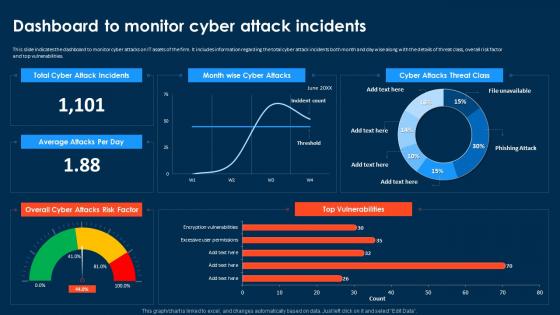 Compressive Planning Guide Dashboard To Monitor Cyber Attack Incidents
Compressive Planning Guide Dashboard To Monitor Cyber Attack IncidentsThis slide indicates the dashboard to monitor cyber attacks on IT assets of the firm. It includes information regarding the total cyber attack incidents both month and day wise along with the details of threat class, overall risk factor and top vulnerabilities. Present the topic in a bit more detail with this Compressive Planning Guide Dashboard To Monitor Cyber Attack Incidents. Use it as a tool for discussion and navigation on Dashboard To Monitor, Cyber Attacks On IT Assets, Top Vulnerabilities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Compressive Planning Guide Summary Of Key Cyber Attacks Occurred
Compressive Planning Guide Summary Of Key Cyber Attacks OccurredThis slide shows the summary of key of cybers attacks occurred in organization such as phishing, malware attack, denial of service, SQL injections, identity thefts. It also contains details of the cyber attacker origin such as inadvertent actors, malicious insiders. Present the topic in a bit more detail with this Compressive Planning Guide Summary Of Key Cyber Attacks Occurred. Use it as a tool for discussion and navigation on Cybers Attacks Occurred, Malware Attack, Denial Of Service, Inadvertent Actors, Malicious Insiders. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
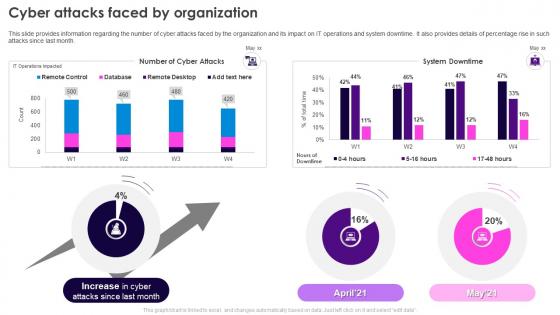 Cyber Attacks Faced By Organization Security Plan To Prevent Cyber
Cyber Attacks Faced By Organization Security Plan To Prevent CyberThis slide provides information regarding the number of cyber attacks faced by the organization and its impact on IT operations and system downtime. It also provides details of percentage rise in such attacks since last month. Present the topic in a bit more detail with this Cyber Attacks Faced By Organization Security Plan To Prevent Cyber. Use it as a tool for discussion and navigation on Cyber Attacks, IT Operations, System Downtime. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Plan To Prevent Cyber Dashboard For Tracking Cyber Attack Risk Levels
Security Plan To Prevent Cyber Dashboard For Tracking Cyber Attack Risk LevelsThe slide represents the dashboard for tracking cyber attack risk levels. It includes information regarding the multiple threat agents, attack methods, preventive controls along with details of risk score and infected systems. Present the topic in a bit more detail with this Security Plan To Prevent Cyber Dashboard For Tracking Cyber Attack Risk Levels. Use it as a tool for discussion and navigation on Infrastructure Controls, Preventive Controls, Detective Controls. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
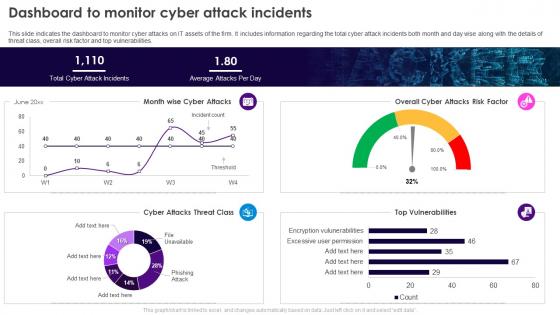 Security Plan To Prevent Cyber Dashboard To Monitor Cyber Attack Incidents
Security Plan To Prevent Cyber Dashboard To Monitor Cyber Attack IncidentsThis slide indicates the dashboard to monitor cyber attacks on IT assets of the firm. It includes information regarding the total cyber attack incidents both month and day wise along with the details of threat class, overall risk factor and top vulnerabilities. Deliver an outstanding presentation on the topic using this Security Plan To Prevent Cyber Dashboard To Monitor Cyber Attack Incidents. Dispense information and present a thorough explanation of Dashboard To Monitor, Cyber Attacks, IT Assets Of The Firm, Risk Factor And Top Vulnerabilities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
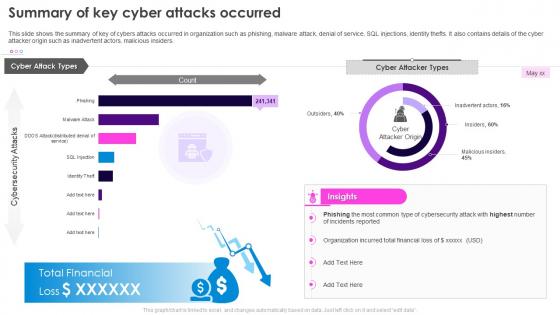 Security Plan To Prevent Cyber Summary Of Key Cyber Attacks Occurred
Security Plan To Prevent Cyber Summary Of Key Cyber Attacks OccurredThis slide shows the summary of key of cybers attacks occurred in organization such as phishing, malware attack, denial of service, SQL injections, identity thefts. It also contains details of the cyber attacker origin such as inadvertent actors, malicious insiders. Present the topic in a bit more detail with this Security Plan To Prevent Cyber Summary Of Key Cyber Attacks Occurred. Use it as a tool for discussion and navigation on Cybers Attacks, Phishing, Malware Attack, Denial Of Service, SQL Injections, Malicious Insiders. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
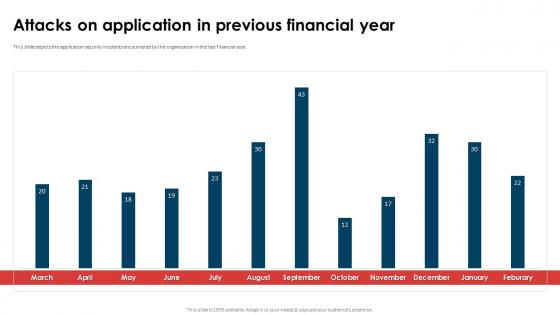 Application Security Implementation Plan Attacks On Application In Previous Financial Year
Application Security Implementation Plan Attacks On Application In Previous Financial YearThis slide depicts the threat scanning dashboard for application security to analyze and monitor vulnerabilities of application. Deliver an outstanding presentation on the topic using this Application Security Implementation Plan Attacks On Application In Previous Financial Year. Dispense information and present a thorough explanation of Attacks On Application, Previous Financial Year, Application Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Attack Prevention Plan In Powerpoint And Google Slides Cpb
Cyber Attack Prevention Plan In Powerpoint And Google Slides CpbPresenting Cyber Attack Prevention Plan In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cyber Attack Prevention Plan. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
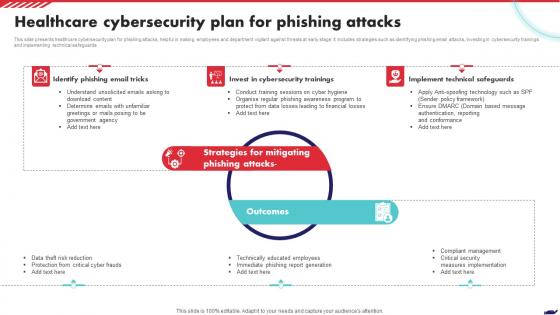 Healthcare Cybersecurity Plan For Phishing Attacks
Healthcare Cybersecurity Plan For Phishing AttacksThis slide presents healthcare cybersecurity plan for phishing attacks, helpful in making employees and department vigilant against threats at early stage. It includes strategies such as identifying phishing email attacks, investing in cybersecurity trainings and implementing technical safeguards Presenting our set of slides with Healthcare Cybersecurity Plan For Phishing Attacks. This exhibits information on Six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Phishing Email Tricks, Cybersecurity Trainings, Technical Safeguards.
-
 Cyber Attack Continuity Plan In Powerpoint And Google Slides Cpb
Cyber Attack Continuity Plan In Powerpoint And Google Slides CpbPresenting our Cyber Attack Continuity Plan In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Cyber Attack Continuity Plan. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
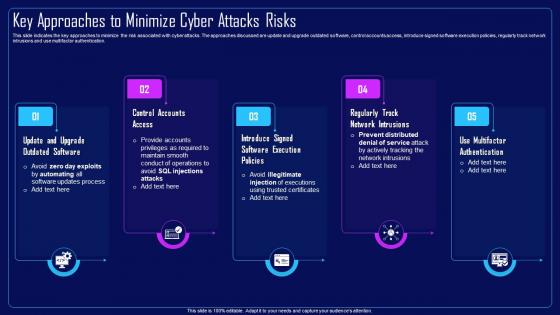 Action Plan To Combat Cyber Crimes Key Approaches To Minimize Cyber Attacks Risks
Action Plan To Combat Cyber Crimes Key Approaches To Minimize Cyber Attacks RisksThis slide indicates the key approaches to minimize the risk associated with cyber attacks. The approaches discussed are update and upgrade outdated software, control accounts access, introduce signed software execution policies, regularly track network intrusions and use multifactor authentication. Introducing Action Plan To Combat Cyber Crimes Key Approaches To Minimize Cyber Attacks Risks to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Regularly Track Network Intrusions, Use Multifactor Authentication, Control Accounts Access, Update And Upgrade Outdated Software, using this template. Grab it now to reap its full benefits.
-
 Action Plan To Combat Cyber Crimes Major Cyber Attacks Faced By Organization
Action Plan To Combat Cyber Crimes Major Cyber Attacks Faced By OrganizationThis purpose of this slide is to showcase the major cyber attacks faced by business organization. The key attacks listed are phishing, malware attack, denial of service attacks, SQL injections, and ransomware. It also provides details regarding the major IT assets impacted and primary objective of each of the attacks. Deliver an outstanding presentation on the topic using this Action Plan To Combat Cyber Crimes Major Cyber Attacks Faced By Organization. Dispense information and present a thorough explanation of Major Cyber Attacks, Malware Attack, Denial Of Service Attacks, SQL Injections, IT Assets using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
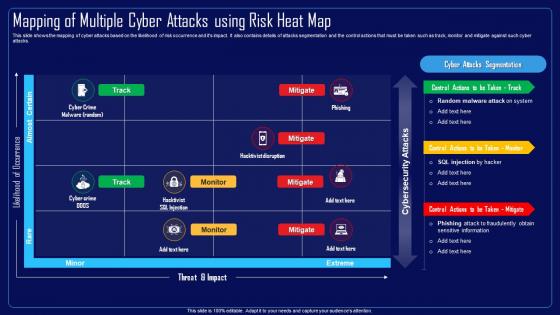 Action Plan To Combat Cyber Crimes Mapping Of Multiple Cyber Attacks Using Risk Heat Map
Action Plan To Combat Cyber Crimes Mapping Of Multiple Cyber Attacks Using Risk Heat MapThis slide shows the mapping of cyber attacks based on the likelihood of risk occurrence and its impact. It also contains details of attacks segmentation and the control actions that must be taken such as track, monitor and mitigate against such cyber attacks. Present the topic in a bit more detail with this Action Plan To Combat Cyber Crimes Mapping Of Multiple Cyber Attacks Using Risk Heat Map. Use it as a tool for discussion and navigation on Mapping Of Multiple Cyber Attacks, Risk Heat Map, Risk Occurrence, Attacks Segmentation And The Control Actions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
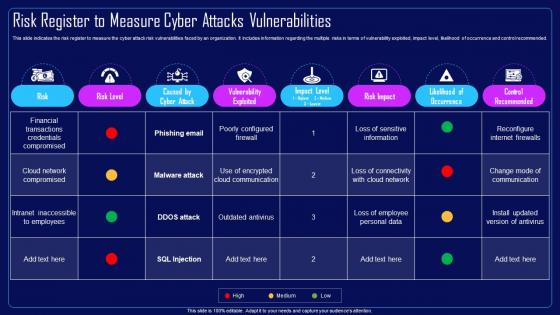 Action Plan To Combat Cyber Crimes Risk Register To Measure Cyber Attacks Vulnerabilities
Action Plan To Combat Cyber Crimes Risk Register To Measure Cyber Attacks VulnerabilitiesThis slide indicates the risk register to measure the cyber attack risk vulnerabilities faced by an organization. It includes information regarding the multiple risks in terms of vulnerability exploited, impact level, likelihood of occurrence and control recommended. Present the topic in a bit more detail with this Action Plan To Combat Cyber Crimes Risk Register To Measure Cyber Attacks Vulnerabilities. Use it as a tool for discussion and navigation on Cloud Network Compromised, Financial Transactions, Credentials Compromised. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Action Plan To Combat Cyber Crimes Strategic Plan To Mitigate Cyber Attacks
Action Plan To Combat Cyber Crimes Strategic Plan To Mitigate Cyber AttacksThe slide indicates the risk mitigation plan for the multiple cyber attacks. It also includes details of cost involved and implementation time required for each mitigation approach. Deliver an outstanding presentation on the topic using this Action Plan To Combat Cyber Crimes Strategic Plan To Mitigate Cyber Attacks. Dispense information and present a thorough explanation of Risk Mitigation Plan, Multiple Cyber Attacks, Mitigation Approach using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Compressive Planning Guide Key Approaches To Minimize Cyber Attacks Risks
Compressive Planning Guide Key Approaches To Minimize Cyber Attacks RisksThis slide indicates the key approaches to minimize the risk associated with cyber attacks. The approaches discussed are update and upgrade outdated software, control accounts access, introduce signed software execution policies, regularly track network intrusions and use multifactor authentication. Increase audience engagement and knowledge by dispensing information using Compressive Planning Guide Key Approaches To Minimize Cyber Attacks Risks. This template helps you present information on five stages. You can also present information on Control Accounts Access, Regularly Track Network Intrusions, Use Multifactor Authentication, Introduce Signed Software Execution Policies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Compressive Planning Guide Major Cyber Attacks Faced By Organization
Compressive Planning Guide Major Cyber Attacks Faced By OrganizationThis purpose of this slide is to showcase the major cyber attacks faced by business organization. The key attacks listed are phishing, malware attack, denial of service attacks, SQL injections, and ransomware. It also provides details regarding the major IT assets impacted and primary objective of each of the attacks. Present the topic in a bit more detail with this Compressive Planning Guide Major Cyber Attacks Faced By Organization. Use it as a tool for discussion and navigation on Database Servers, Network And Application Infrastructure, Denial Of Service Attack, Malware Attack. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
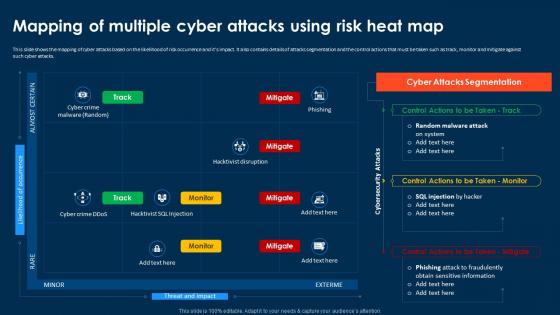 Compressive Planning Guide Mapping Of Multiple Cyber Attacks Using Risk Heat Map
Compressive Planning Guide Mapping Of Multiple Cyber Attacks Using Risk Heat MapThis slide shows the mapping of cyber attacks based on the likelihood of risk occurrence and its impact. It also contains details of attacks segmentation and the control actions that must be taken such as track, monitor and mitigate against such cyber attacks. Deliver an outstanding presentation on the topic using this Compressive Planning Guide Mapping Of Multiple Cyber Attacks Using Risk Heat Map. Dispense information and present a thorough explanation of Cyber Attacks Segmentation, Phishing Attack, Fraudulently Obtain Sensitive Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
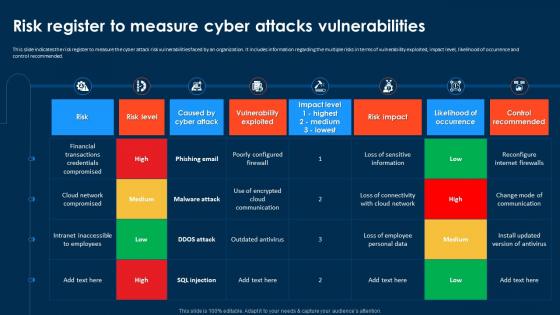 Compressive Planning Guide Risk Register To Measure Cyber Attacks Vulnerabilities
Compressive Planning Guide Risk Register To Measure Cyber Attacks VulnerabilitiesThis slide indicates the risk register to measure the cyber attack risk vulnerabilities faced by an organization. It includes information regarding the multiple risks in terms of vulnerability exploited, impact level, likelihood of occurrence and control recommended. Present the topic in a bit more detail with this Compressive Planning Guide Risk Register To Measure Cyber Attacks Vulnerabilities. Use it as a tool for discussion and navigation on Cyber Attack Risk Vulnerabilities, Vulnerability Exploited, Occurrence And Control Recommended. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Compressive Planning Guide Strategic Plan To Mitigate Cyber Attacks
Compressive Planning Guide Strategic Plan To Mitigate Cyber AttacksThe slide indicates the risk mitigation plan for the multiple cyber attacks. It also includes details of cost involved and implementation time required for each mitigation approach. Deliver an outstanding presentation on the topic using this Compressive Planning Guide Strategic Plan To Mitigate Cyber Attacks. Dispense information and present a thorough explanation of Strategic Plan, Mitigate Cyber Attacks, Risk Mitigation Plan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Agenda For Security Plan To Prevent Cyber Attacks Ppt Icon Design Inspiration
Agenda For Security Plan To Prevent Cyber Attacks Ppt Icon Design InspirationIntroducing Agenda For Security Plan To Prevent Cyber Attacks Ppt Icon Design Inspiration to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Risk Assessment, Attacks Frequency, Assessment Program For Organization, using this template. Grab it now to reap its full benefits.
-
 Icons Slide Security Plan To Prevent Cyber Attacks Ppt Icon Elements
Icons Slide Security Plan To Prevent Cyber Attacks Ppt Icon ElementsPresenting our well crafted Icons Slide Security Plan To Prevent Cyber Attacks Ppt Icon Elements set of slides. The slides include icons that are innovatively designed by our team of experts. The icons are easy to edit so you can conveniently increase or decrease their size without any loss in resolution. Therefore, grab them instantly.
-
 Security Plan To Prevent Cyber Key Approaches To Minimize Cyber Attacks Risks
Security Plan To Prevent Cyber Key Approaches To Minimize Cyber Attacks RisksThis slide indicates the key approaches to minimize the risk associated with cyber attacks. The approaches discussed are update and upgrade outdated software, control accounts access, introduce signed software execution policies, regularly track network intrusions and use multifactor authentication. Increase audience engagement and knowledge by dispensing information using Security Plan To Prevent Cyber Key Approaches To Minimize Cyber Attacks Risks. This template helps you present information on five stages. You can also present information on Use Multifactor Authentication, Regularly Track Network Intrusions, Control Accounts Access using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
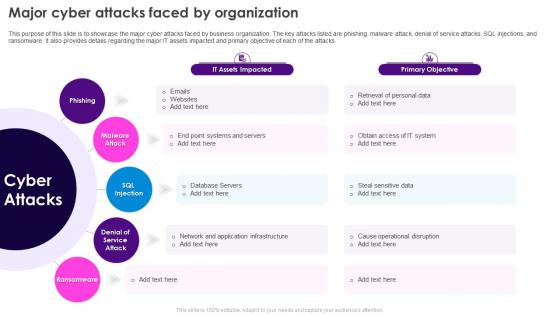 Security Plan To Prevent Cyber Major Cyber Attacks Faced By Organization
Security Plan To Prevent Cyber Major Cyber Attacks Faced By OrganizationThis purpose of this slide is to showcase the major cyber attacks faced by business organization. The key attacks listed are phishing, malware attack, denial of service attacks, SQL injections, and ransomware. It also provides details regarding the major IT assets impacted and primary objective of each of the attacks. Introducing Security Plan To Prevent Cyber Major Cyber Attacks Faced By Organization to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Network And Application Infrastructure, Database Servers, Cause Operational Disruption, using this template. Grab it now to reap its full benefits.
-
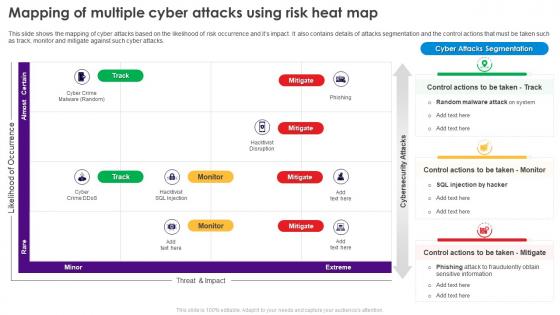 Security Plan To Prevent Cyber Mapping Of Multiple Cyber Attacks Using Risk Heat Map
Security Plan To Prevent Cyber Mapping Of Multiple Cyber Attacks Using Risk Heat MapThis slide shows the mapping of cyber attacks based on the likelihood of risk occurrence and its impact. It also contains details of attacks segmentation and the control actions that must be taken such as track, monitor and mitigate against such cyber attacks. Deliver an outstanding presentation on the topic using this Security Plan To Prevent Cyber Mapping Of Multiple Cyber Attacks Using Risk Heat Map. Dispense information and present a thorough explanation of Cyber Attacks, Risk Occurrence, Attacks Segmentation, Monitor And Mitigate using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
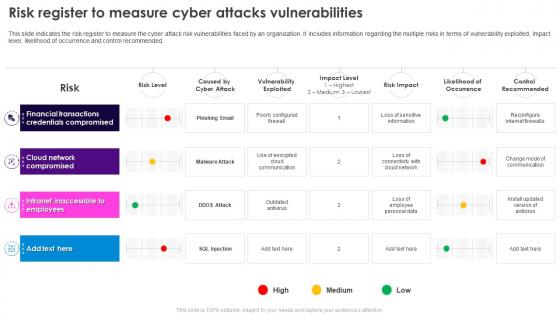 Security Plan To Prevent Cyber Risk Register To Measure Cyber Attacks Vulnerabilities
Security Plan To Prevent Cyber Risk Register To Measure Cyber Attacks VulnerabilitiesThis slide indicates the risk register to measure the cyber attack risk vulnerabilities faced by an organization. It includes information regarding the multiple risks in terms of vulnerability exploited, impact level, likelihood of occurrence and control recommended. Present the topic in a bit more detail with this Security Plan To Prevent Cyber Risk Register To Measure Cyber Attacks Vulnerabilities. Use it as a tool for discussion and navigation on Financial Transactions, Credentials Compromised, Cloud Network, Compromised. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
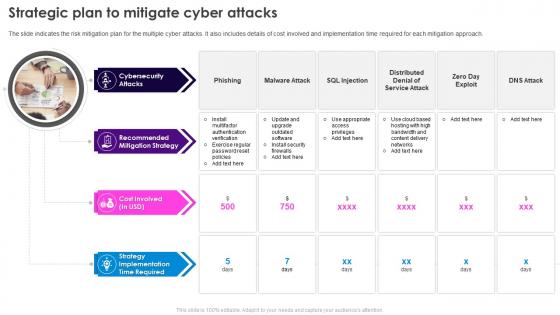 Security Plan To Prevent Cyber Strategic Plan To Mitigate Cyber Attacks
Security Plan To Prevent Cyber Strategic Plan To Mitigate Cyber AttacksThe slide indicates the risk mitigation plan for the multiple cyber attacks. It also includes details of cost involved and implementation time required for each mitigation approach. Increase audience engagement and knowledge by dispensing information using Security Plan To Prevent Cyber Strategic Plan To Mitigate Cyber Attacks. This template helps you present information on four stages. You can also present information on Cybersecurity Attacks, Recommended Mitigation Strategy, Strategy Implementation Time Required using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Table Of Contents For Security Plan To Prevent Cyber Attacks
Table Of Contents For Security Plan To Prevent Cyber AttacksIntroducing Table Of Contents For Security Plan To Prevent Cyber Attacks to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Cybersecurity Risk Assessment Program, Cyber Attacks Identification, Cyber Attacks Faced By Organization, Cyber Attacks Risk Assessment, using this template. Grab it now to reap its full benefits.
-
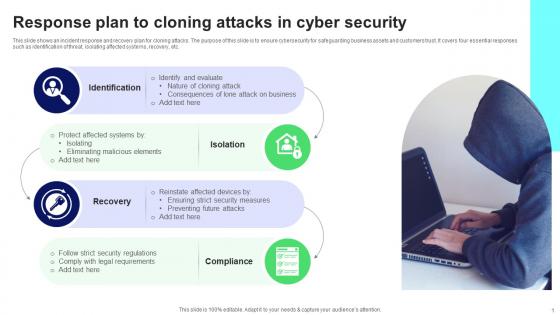 Response Plan To Cloning Attacks In Cyber Security
Response Plan To Cloning Attacks In Cyber SecurityThis slide shows an incident response and recovery plan for cloning attacks. The purpose of this slide is to ensure cybersecurity for safeguarding business assets and customers trust. It covers four essential responses such as identification of threat, isolating affected systems, recovery, etc. Presenting our set of slides with name Response Plan To Cloning Attacks In Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cloning Attack, Malicious Elements, Security Measures.
-
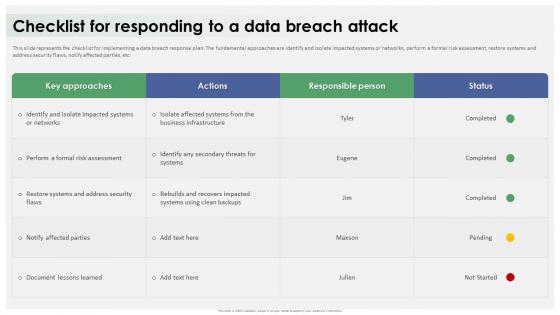 Data Breach Response Plan Checklist For Responding To A Data Breach Attack
Data Breach Response Plan Checklist For Responding To A Data Breach AttackThis slide represents the checklist for implementing a data breach response plan. The fundamental approaches are identify and isolate impacted systems or networks, perform a formal risk assessment, restore systems and address security flaws, notify affected parties, etc. Deliver an outstanding presentation on the topic using this Data Breach Response Plan Checklist For Responding To A Data Breach Attack. Dispense information and present a thorough explanation of Data Breach Response Plan, Fundamental Approaches, Formal Risk Assessment, Restore Systems using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Breach Response Plan Possible Causes Of Data Breach Attack
Data Breach Response Plan Possible Causes Of Data Breach AttackThis slide highlights the reasons behind the success of data breach attack. These include phishing attacks, unpatched software, malware, insider threats, third-party vulnerabilities, SQL Structured Query Language injections, unsecured APIs, etc. Deliver an outstanding presentation on the topic using this Data Breach Response Plan Possible Causes Of Data Breach Attack. Dispense information and present a thorough explanation of Phishing Attacks, Unpatched Software, Third Party Vulnerabilities, Structured Query Language using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
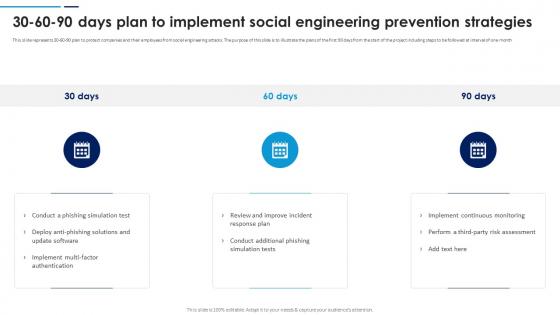 Social Engineering Attacks Prevention 30 60 90 Days Plan To Implement Social Engineering
Social Engineering Attacks Prevention 30 60 90 Days Plan To Implement Social EngineeringThis slide represents 30-60-90 plan to protect companies and their employees from social engineering attacks. The purpose of this slide is to illustrate the plans of the first 90 days from the start of the project including steps to be followed at interval of one month. Introducing Social Engineering Attacks Prevention 30 60 90 Days Plan To Implement Social Engineering to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Phishing Simulation Test, Implement Continuous Monitoring, Third Party Risk Assessment, using this template. Grab it now to reap its full benefits.
-
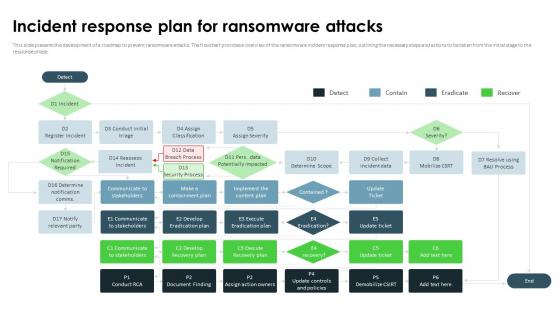 Ransomware In Digital Age Incident Response Plan For Ransomware Attacks
Ransomware In Digital Age Incident Response Plan For Ransomware AttacksThis slide presents the development of a roadmap to prevent ransomware attacks. The flowchart provides a overview of the ransomware incident response plan, outlining the necessary steps and actions to be taken from the initial stage to the response phase. Present the topic in a bit more detail with this Ransomware In Digital Age Incident Response Plan For Ransomware Attacks. Use it as a tool for discussion and navigation on Development Of A Roadmap, Prevent Ransomware Attacks, Communicate To Stakeholders. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
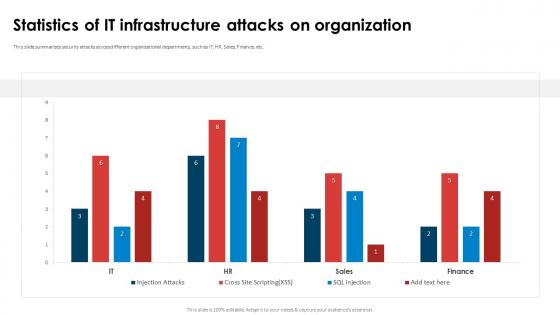 Application Security Implementation Plan Statistics Of It Infrastructure Attacks On Organization
Application Security Implementation Plan Statistics Of It Infrastructure Attacks On OrganizationThis slide summarizes security attacks across different organizational departments, such as IT, HR, Sales, Finance, etc. Deliver an outstanding presentation on the topic using this Application Security Implementation Plan Statistics Of IT Infrastructure Attacks On Organization. Dispense information and present a thorough explanation of Statistics Of IT Infrastructure, Attacks On Organization, Organizational Departments, Finance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
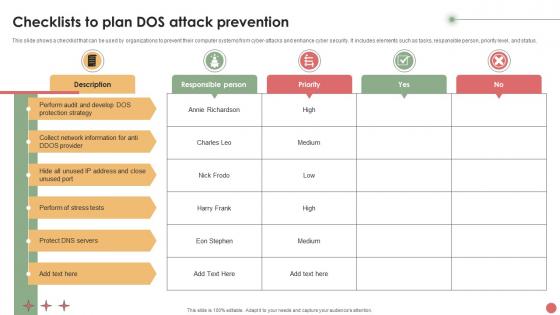 Checklists To Plan DOS Attack Prevention
Checklists To Plan DOS Attack PreventionThis slide shows a checklist that can be used by organizations to prevent their computer systems from cyber-attacks and enhance cyber security. It includes elements such as tasks, responsible person, priority level, and status. Presenting our well structured Checklists To Plan DOS Attack Prevention. The topics discussed in this slide are Responsible Person, Priority, High. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
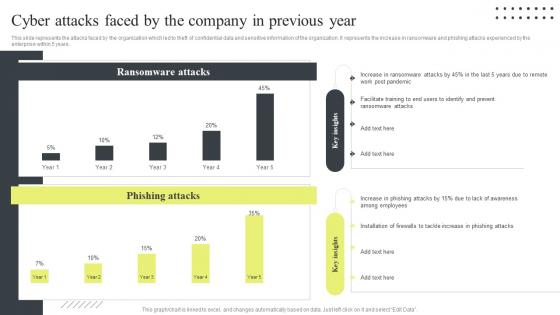 Cyber Security Attacks Response Plan Cyber Attacks Faced By The Company In Previous Year
Cyber Security Attacks Response Plan Cyber Attacks Faced By The Company In Previous YearThis slide represents the attacks faced by the organization which led to theft of confidential data and sensitive information of the organization. It represents the increase in ransomware and phishing attacks experienced by the enterprise within 5 years. Deliver an outstanding presentation on the topic using this Cyber Security Attacks Response Plan Cyber Attacks Faced By The Company In Previous Year. Dispense information and present a thorough explanation of Ransomware Attacks, Phishing Attacks, Post Pandemic using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
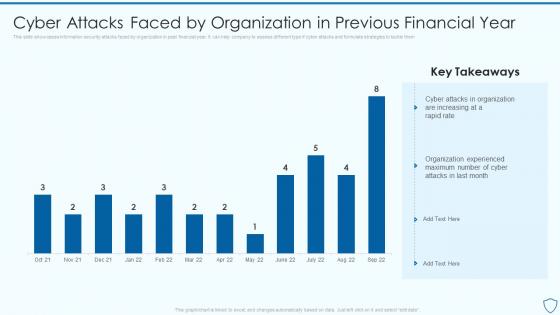 Cyber Attacks Faced By Organization In Risk Assessment And Management Plan For Information Security
Cyber Attacks Faced By Organization In Risk Assessment And Management Plan For Information SecurityThis slide showcases information security attacks faced by organization in past financial year. It can help company to assess different type if cyber attacks and formulate strategies to tackle them Present the topic in a bit more detail with this Cyber Attacks Faced By Organization In Risk Assessment And Management Plan For Information Security. Use it as a tool for discussion and navigation on Experienced, Organization, Financial. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
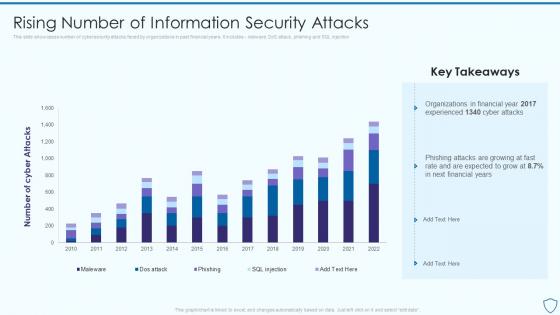 Rising Number Of Information Security Attacks Risk Assessment And Management Plan For Information Security
Rising Number Of Information Security Attacks Risk Assessment And Management Plan For Information SecurityThis slide showcases number of cybersecurity attacks faced by organizations in past financial years. It includes malware, DoS attack, phishing and SQL injection Present the topic in a bit more detail with this Rising Number Of Information Security Attacks Risk Assessment And Management Plan For Information Security. Use it as a tool for discussion and navigation on Organizations, Information, Cybersecurity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
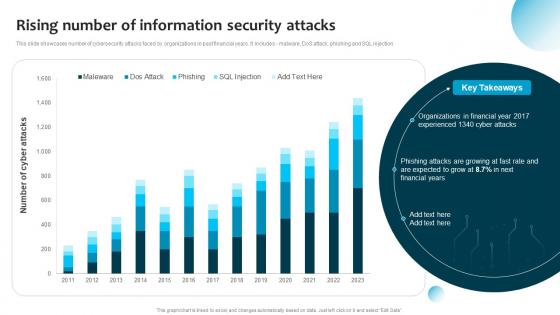 Rising Number Of Information Security Attacks Information System Security And Risk Administration Plan
Rising Number Of Information Security Attacks Information System Security And Risk Administration PlanThis slide showcases number of cybersecurity attacks faced by organizations in past financial years. It includes malware, DoS attack, phishing and SQL injection. Deliver an outstanding presentation on the topic using thisRising Number Of Information Security Attacks Information System Security And Risk Administration Plan. Dispense information and present a thorough explanation of Financial Years, Cyber Attacks, Information Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Rising Number Of Information Security Attacks Cybersecurity Risk Analysis And Management Plan
Rising Number Of Information Security Attacks Cybersecurity Risk Analysis And Management PlanThis slide showcases number of cybersecurity attacks faced by organizations in past financial years. It includes malware, DoS attack, phishing and SQL injection Present the topic in a bit more detail with this Rising Number Of Information Security Attacks Cybersecurity Risk Analysis And Management Plan. Use it as a tool for discussion and navigation on Information, Security Attacks, Organizations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
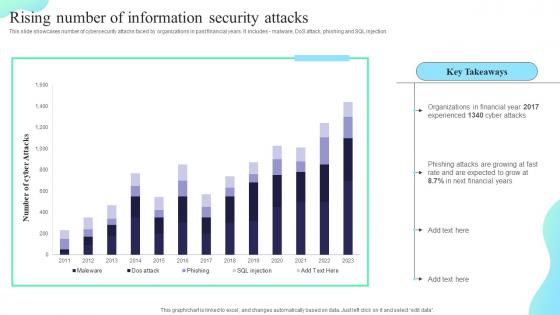 Rising Number Of Information Security Attacks Formulating Cybersecurity Plan
Rising Number Of Information Security Attacks Formulating Cybersecurity PlanThis slide showcases number of cybersecurity attacks faced by organizations in past financial years. It includes malware, DoS attack, phishing and SQL injection. Deliver an outstanding presentation on the topic using this Rising Number Of Information Security Attacks Formulating Cybersecurity Plan. Dispense information and present a thorough explanation of Rising Number, Information Security, Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
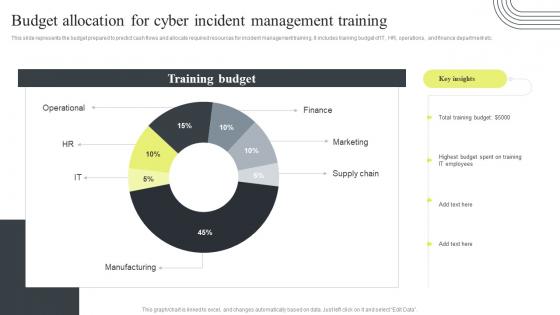 Cyber Security Attacks Response Plan Budget Allocation For Cyber Incident Management Training
Cyber Security Attacks Response Plan Budget Allocation For Cyber Incident Management TrainingThis slide represents the budget prepared to predict cash flows and allocate required resources for incident management training. It includes training budget of IT, HR, operations, and finance department etc. Deliver an outstanding presentation on the topic using this Cyber Security Attacks Response Plan Budget Allocation For Cyber Incident Management Training. Dispense information and present a thorough explanation of Budget Allocation, Cyber Incident Management, Training using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
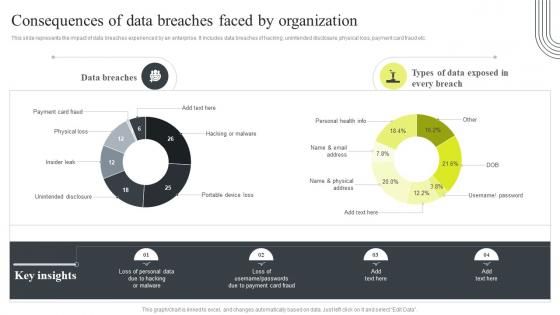 Cyber Security Attacks Response Plan Consequences Of Data Breaches Faced By Organization
Cyber Security Attacks Response Plan Consequences Of Data Breaches Faced By OrganizationThis slide represents the impact of data breaches experienced by an enterprise. It includes data breaches of hacking, unintended disclosure, physical loss, payment card fraud etc. Present the topic in a bit more detail with this Cyber Security Attacks Response Plan Consequences Of Data Breaches Faced By Organization. Use it as a tool for discussion and navigation on Consequences, Data Breaches, Unintended Disclosure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
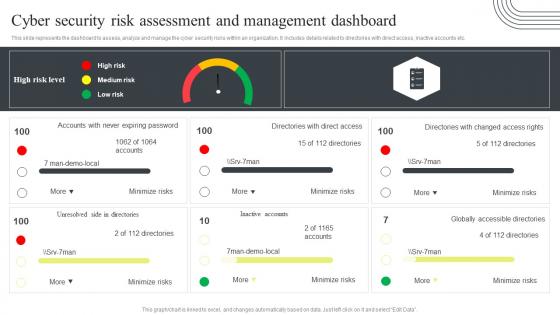 Cyber Security Attacks Response Plan Cyber Security Risk Assessment And Management Dashboard
Cyber Security Attacks Response Plan Cyber Security Risk Assessment And Management DashboardThis slide represents the dashboard to assess, analyze and manage the cyber security risks within an organization. It includes details related to directories with direct access, inactive accounts etc. Deliver an outstanding presentation on the topic using this Cyber Security Attacks Response Plan Cyber Security Risk Assessment And Management Dashboard. Dispense information and present a thorough explanation of Cyber Security, Risk Assessment, Management Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
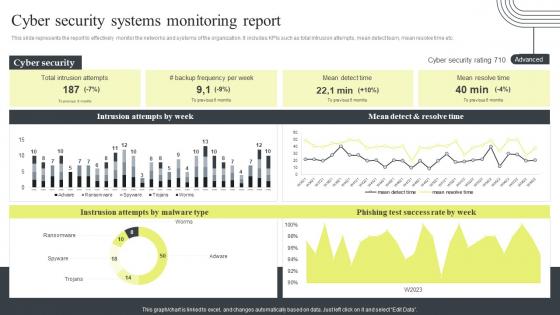 Cyber Security Attacks Response Plan Cyber Security Systems Monitoring Report
Cyber Security Attacks Response Plan Cyber Security Systems Monitoring ReportThis slide represents the report to effectively monitor the networks and systems of the organization. It includes KPIs such as total intrusion attempts, mean detect team, mean resolve time etc. Present the topic in a bit more detail with this Cyber Security Attacks Response Plan Cyber Security Systems Monitoring Report. Use it as a tool for discussion and navigation on Cyber Security Systems, Monitoring Report, Mean Detect And Resolve Time. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Attacks Response Plan Cyber Supply Chain Risk Management Dashboard
Cyber Security Attacks Response Plan Cyber Supply Chain Risk Management DashboardThis slide shows the dashboard representing details related to management of supply chain risks by the incident management team. It includes details related to KPIs such as policy and compliance, resource security hygiene etc. Present the topic in a bit more detail with this Cyber Security Attacks Response Plan Cyber Supply Chain Risk Management Dashboard. Use it as a tool for discussion and navigation on Cyber Supply Chain, Risk Management, Dashboard, Regulatory Compliance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Attacks Response Plan Enterprise Cyber Risk Management Dashboard
Cyber Security Attacks Response Plan Enterprise Cyber Risk Management DashboardThis slide represents the key metrics dashboard representing details related to management of cyber security incidents by an enterprise. It includes key performance indicators such as risk analysis progress, risk rating breakdown etc. Deliver an outstanding presentation on the topic using this Cyber Security Attacks Response Plan Enterprise Cyber Risk Management Dashboard. Dispense information and present a thorough explanation of Enterprise Cyber, Risk Management, Dashboard, Action Plan Breakdown using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
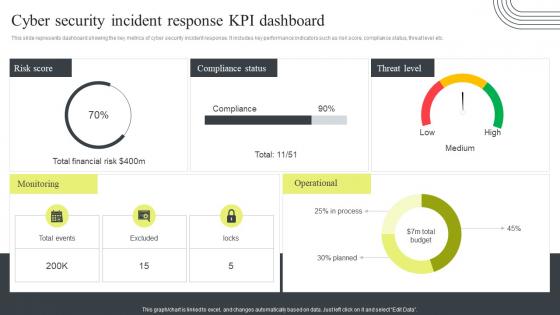 Cyber Security Incident Response Kpi Dashboard Cyber Security Attacks Response Plan
Cyber Security Incident Response Kpi Dashboard Cyber Security Attacks Response PlanThis slide represents dashboard showing the key metrics of cyber security incident response. It includes key performance indicators such as risk score, compliance status, threat level etc. Present the topic in a bit more detail with this Cyber Security Incident Response Kpi Dashboard Cyber Security Attacks Response Plan. Use it as a tool for discussion and navigation on Cyber Security, Incident Response, KPI Dashboard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
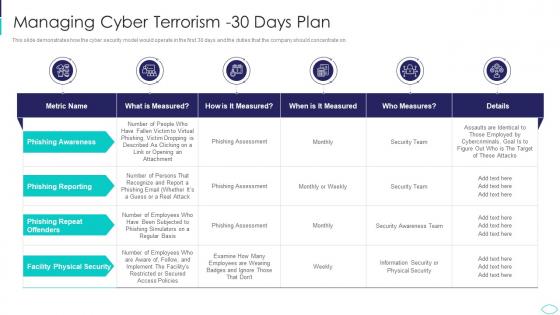 A57 Managing Cyber Terrorism 30 Days Plan Cyber Terrorism Attacks
A57 Managing Cyber Terrorism 30 Days Plan Cyber Terrorism AttacksThis slide demonstrates how the cyber security model would operate in the first 30 days and the duties that the company should concentrate on.Present the topic in a bit more detail with this A57 Managing Cyber Terrorism 30 Days Plan Cyber Terrorism Attacks. Use it as a tool for discussion and navigation on Managing Cyber Terrorism 30 Days Plan. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
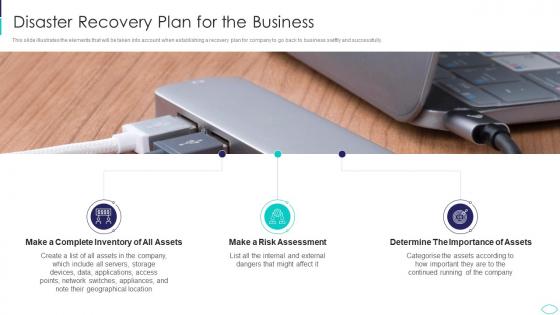 Disaster Recovery Plan For The Business Cyber Terrorism Attacks
Disaster Recovery Plan For The Business Cyber Terrorism AttacksThis slide illustrates the elements that will be taken into account when establishing a recovery plan for company to go back to business swiftly and successfully. Increase audience engagement and knowledge by dispensing information using Disaster Recovery Plan For The Business Cyber Terrorism Attacks. This template helps you present information on three stages. You can also present information on Inventory, Assets, Assessment, Importance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
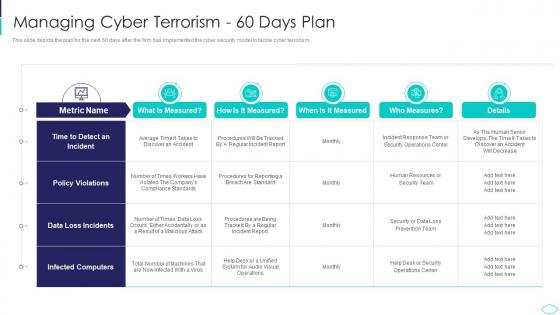 Managing Cyber Terrorism 60 Days Plan Cyber Terrorism Attacks
Managing Cyber Terrorism 60 Days Plan Cyber Terrorism AttacksThis slide depicts the plan for the next 60 days after the firm has implemented the cyber security model to tackle cyber terrorism. Deliver an outstanding presentation on the topic using this Managing Cyber Terrorism 60 Days Plan Cyber Terrorism Attacks. Dispense information and present a thorough explanation of Managing Cyber Terrorism 60 Days Plan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
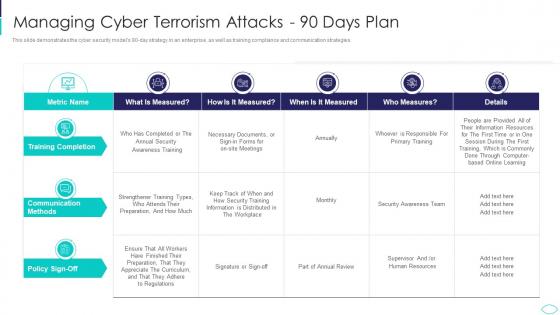 Managing Cyber Terrorism Attacks 90 Days Plan Cyber Terrorism Attacks
Managing Cyber Terrorism Attacks 90 Days Plan Cyber Terrorism AttacksThis slide demonstrates the cyber security models 90 day strategy in an enterprise, as well as training compliance and communication strategies. Deliver an outstanding presentation on the topic using this Managing Cyber Terrorism Attacks 90 Days Plan Cyber Terrorism Attacks. Dispense information and present a thorough explanation of Managing Cyber Terrorism Attacks 90 Days Plan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.