Powerpoint Templates and Google slides for Ransomware Incident Mitigation
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Ransomware Incident Mitigation Icon For Ensuring Cyber Security
Ransomware Incident Mitigation Icon For Ensuring Cyber SecurityIntroducing our premium set of slides with Ransomware Incident Mitigation Icon For Ensuring Cyber Security Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Ransomware Incident Mitigation, Icon For Ensuring Cyber Security. So download instantly and tailor it with your information.
-
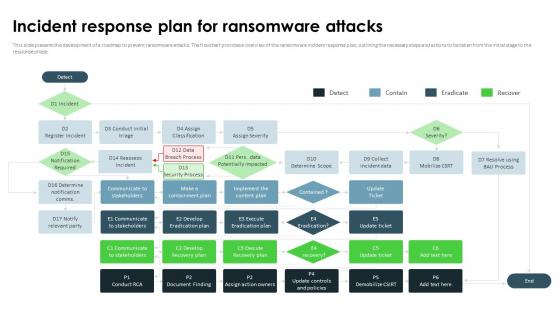 Ransomware In Digital Age Incident Response Plan For Ransomware Attacks
Ransomware In Digital Age Incident Response Plan For Ransomware AttacksThis slide presents the development of a roadmap to prevent ransomware attacks. The flowchart provides a overview of the ransomware incident response plan, outlining the necessary steps and actions to be taken from the initial stage to the response phase. Present the topic in a bit more detail with this Ransomware In Digital Age Incident Response Plan For Ransomware Attacks. Use it as a tool for discussion and navigation on Development Of A Roadmap, Prevent Ransomware Attacks, Communicate To Stakeholders. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
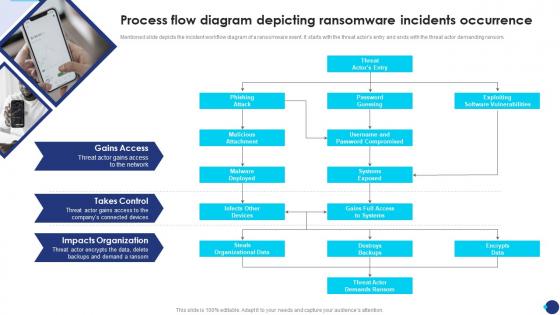 Incident Response Playbook Process Flow Diagram Depicting Ransomware Incidents Occurrence
Incident Response Playbook Process Flow Diagram Depicting Ransomware Incidents OccurrenceMentioned slide depicts the incident workflow diagram of a ransomware event. It starts with the threat actors entry and ends with the threat actor demanding ransom. Introducing Incident Response Playbook Process Flow Diagram Depicting Ransomware Incidents Occurrence to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Phishing Attack, Malicious Attachment, Malware Deployed, using this template. Grab it now to reap its full benefits.
-
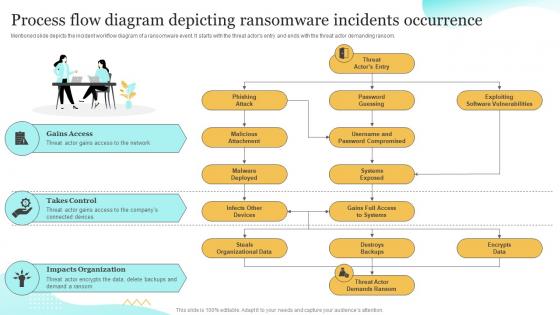 Process Flow Diagram Depicting Ransomware Upgrading Cybersecurity With Incident Response Playbook
Process Flow Diagram Depicting Ransomware Upgrading Cybersecurity With Incident Response PlaybookMentioned slide depicts the incident workflow diagram of a ransomware event. It starts with the threat actors entry and ends with the threat actor demanding ransom. Deliver an outstanding presentation on the topic using this Process Flow Diagram Depicting Ransomware Upgrading Cybersecurity With Incident Response Playbook. Dispense information and present a thorough explanation of Compromised, Exploiting, Software Vulnerabilities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
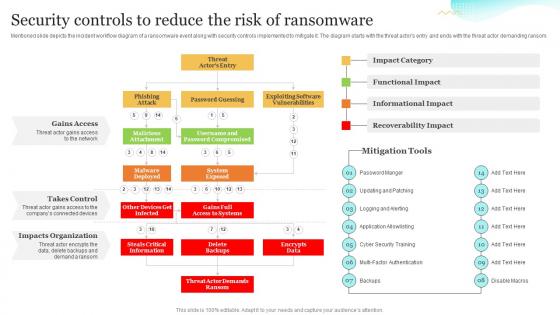 Security Controls To Reduce The Risk Of Ransomware Upgrading Cybersecurity With Incident Response Playbook
Security Controls To Reduce The Risk Of Ransomware Upgrading Cybersecurity With Incident Response PlaybookMentioned slide depicts the incident workflow diagram of a ransomware event along with security controls implemented to mitigate it. The diagram starts with the threat actors entry and ends with the threat actor demanding ransom. Present the topic in a bit more detail with this Security Controls To Reduce The Risk Of Ransomware Upgrading Cybersecurity With Incident Response Playbook. Use it as a tool for discussion and navigation on Ransomware, Informational Impact, Recoverability Impact. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
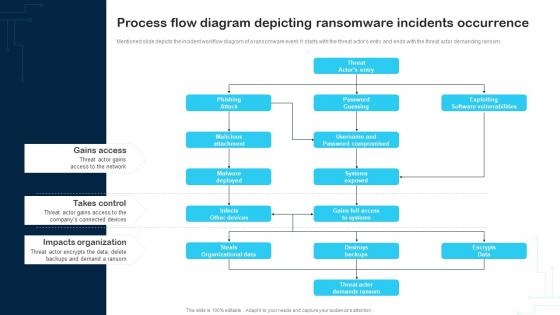 Process Flow Diagram Depicting Ransomware Incidents Occurrence Cybersecurity Incident And Vulnerability
Process Flow Diagram Depicting Ransomware Incidents Occurrence Cybersecurity Incident And VulnerabilityMentioned slide depicts the incident workflow diagram of a ransomware event. It starts with the threat actors entry and ends with the threat actor demanding ransom. Deliver an outstanding presentation on the topic using this Process Flow Diagram Depicting Ransomware Incidents Occurrence Cybersecurity Incident And Vulnerability. Dispense information and present a thorough explanation of Gains Access, Takes Control, Impacts Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
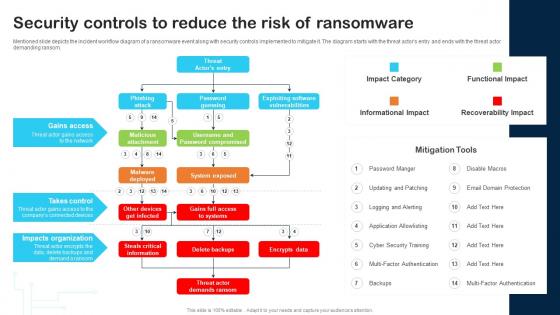 Security Controls To Reduce The Risk Of Ransomware Cybersecurity Incident And Vulnerability
Security Controls To Reduce The Risk Of Ransomware Cybersecurity Incident And VulnerabilityMentioned slide depicts the incident workflow diagram of a ransomware event along with security controls implemented to mitigate it. The diagram starts with the threat actors entry and ends with the threat actor demanding ransom. Deliver an outstanding presentation on the topic using this Security Controls To Reduce The Risk Of Ransomware Cybersecurity Incident And Vulnerability. Dispense information and present a thorough explanation of Gains Access, Takes Control, Impacts Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
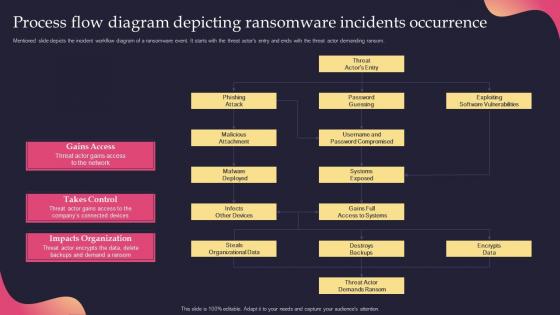 Process Flow Diagram Depicting Ransomware Incidents Occurrence Security Incident Response Playbook
Process Flow Diagram Depicting Ransomware Incidents Occurrence Security Incident Response PlaybookMentioned slide depicts the incident workflow diagram of a ransomware event. It starts with the threat actors entry and ends with the threat actor demanding ransom. Deliver an outstanding presentation on the topic using this Process Flow Diagram Depicting Ransomware Incidents Occurrence Security Incident Response Playbook. Dispense information and present a thorough explanation of Process, Ransomware, Occurrence using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
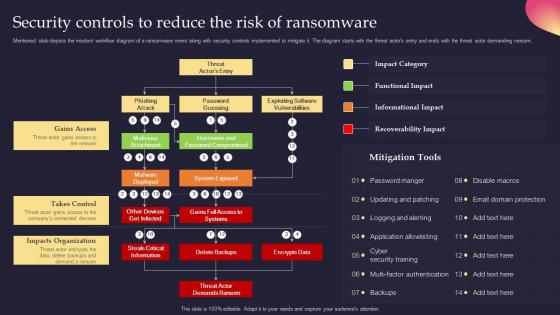 Security Controls To Reduce The Risk Of Ransomware Security Incident Response Playbook
Security Controls To Reduce The Risk Of Ransomware Security Incident Response PlaybookMentioned slide depicts the incident workflow diagram of a ransomware event along with security controls implemented to mitigate it. The diagram starts with the threat actors entry and ends with the threat actor demanding ransom. Present the topic in a bit more detail with this Security Controls To Reduce The Risk Of Ransomware Security Incident Response Playbook. Use it as a tool for discussion and navigation on Ransomwarem, Impacts Organization, Encrypts Data. This template is free to edit as deemed fit for your organization. Therefore download it now.

