Powerpoint Templates and Google slides for Security Automation Tools
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
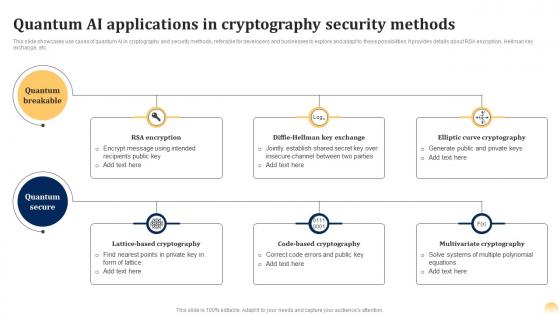 Quantum Cryptography Security Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SS
Quantum Cryptography Security Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SSThis slide showcases use cases of quantum AI in cryptography and security methods, referable for developers and businesses to explore and adapt to these possibilities. It provides details about RSA encryption, Hellman key exchange, etc. Present the topic in a bit more detail with this Quantum Cryptography Security Quantum Ai Fusing Quantum Computing With Intelligent Algorithms AI SS. Use it as a tool for discussion and navigation on Elliptic Curve Cryptography, Code Based Cryptography, Multivariate Cryptography. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Automation Strategies To Enhance Security And Compliance
Cloud Automation Strategies To Enhance Security And ComplianceThis slide represents cloud automation strategies to enhance security and compliance which assists organizations to streamline operations and minimizes manual intervention. It includes cloud automation strategies to enhance security and compliances such as utilize infrastructure as code, etc. Introducing our premium set of slides with name Cloud Automation Strategies To Enhance Security And Compliance. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cloud Consulting Partner, Leverage Automation, Enhance Compliance, Utilize Policy As Tools. So download instantly and tailor it with your information.
-
 Stages Of Cyber Security And Compliance Automation
Stages Of Cyber Security And Compliance AutomationThis slide represents stages of cyber security and compliance automation which assists in cyber risk and policy adherence. It includes stages of cyber security and compliance automation such as initial, developing, define, etc. Presenting our set of slides with name Stages Of Cyber Security And Compliance Automation. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Stages Of Cyber Security, Compliance Automation, Developing, Risk And Policy Adherence.
-
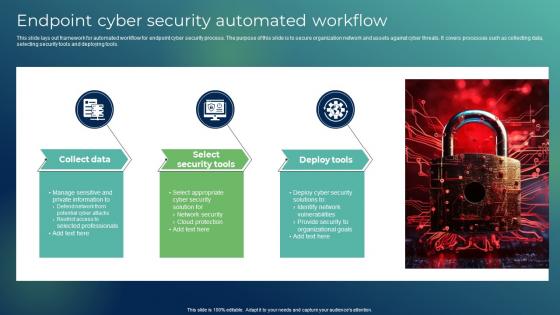 Endpoint Cyber Security Automated Workflow
Endpoint Cyber Security Automated WorkflowThis slide lays out framework for automated workflow for endpoint cyber security process. The purpose of this slide is to secure organization network and assets against cyber threats. It covers processes such as collecting data, selecting security tools and deploying tools. Introducing our premium set of slides with Endpoint Cyber Security Automated Workflow Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Collect Data, Select Security Tools, Deploy Tools So download instantly and tailor it with your information.
-
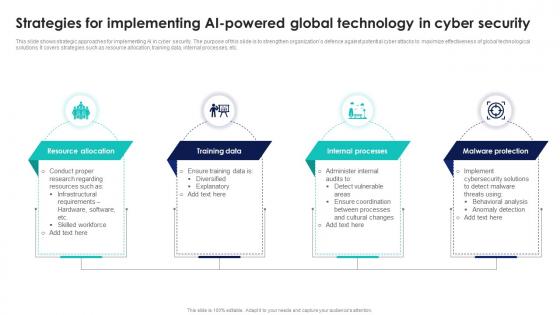 Strategies For Implementing AI Powered Global Technology In Cyber Security
Strategies For Implementing AI Powered Global Technology In Cyber SecurityThis slide shows strategic approaches for implementing AI in cyber security. The purpose of this slide is to strengthen organizations defence against potential cyber attacks to maximize effectiveness of global technological solutions. It covers strategies such as resource allocation, training data, internal processes, etc. Presenting our set of slides with Strategies For Implementing AI Powered Global Technology In Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Resource Allocation, Training Data, Internal Processes.
-
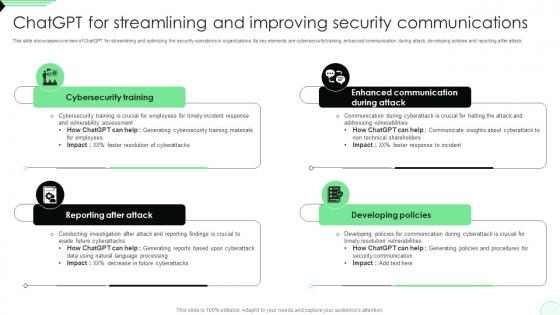 ChatGPT For Streamlining And Improving Security Opportunities And Risks Of ChatGPT AI SS V
ChatGPT For Streamlining And Improving Security Opportunities And Risks Of ChatGPT AI SS VThis slide showcases overview of ChatGPT for streamlining and optimizing the security operations in organizations. Its key elements are cybersecurity training, enhanced communication during attack, developing policies and reporting after attack. Introducing ChatGPT For Streamlining And Improving Security Opportunities And Risks Of ChatGPT AI SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Reporting After Attack, Cybersecurity Training, Developing Policies, using this template. Grab it now to reap its full benefits.
-
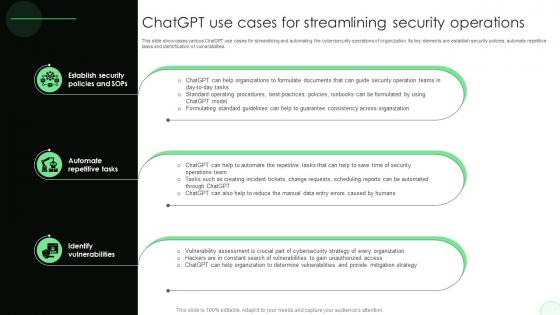 ChatGPT Use Cases For Streamlining Security Opportunities And Risks Of ChatGPT AI SS V
ChatGPT Use Cases For Streamlining Security Opportunities And Risks Of ChatGPT AI SS VThis slide showcases various ChatGPT use cases for streamlining and automating the cybersecurity operations of organization. Its key elements are establish security policies, automate repetitive tasks and identification of vulnerabilities. Increase audience engagement and knowledge by dispensing information using ChatGPT Use Cases For Streamlining Security Opportunities And Risks Of ChatGPT AI SS V. This template helps you present information on three stages. You can also present information on Establish Security Policies And Sops, Automate Repetitive Tasks, Identify Vulnerabilities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
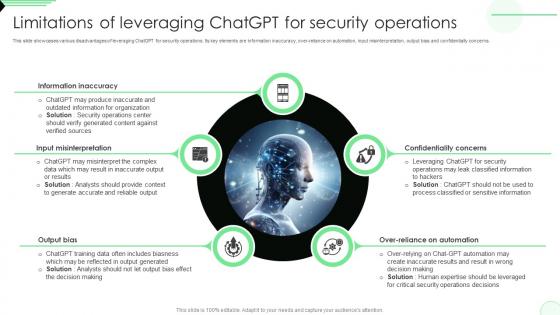 Limitations Of Leveraging ChatGPT For Security Opportunities And Risks Of ChatGPT AI SS V
Limitations Of Leveraging ChatGPT For Security Opportunities And Risks Of ChatGPT AI SS VThis slide showcases various disadvantages of leveraging ChatGPT for security operations. Its key elements are information inaccuracy, over-reliance on automation, input misinterpretation, output bias and confidentially concerns. Introducing Limitations Of Leveraging ChatGPT For Security Opportunities And Risks Of ChatGPT AI SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Confidentiality Concerns, Over-Reliance On Automation, Output Bias, using this template. Grab it now to reap its full benefits.
-
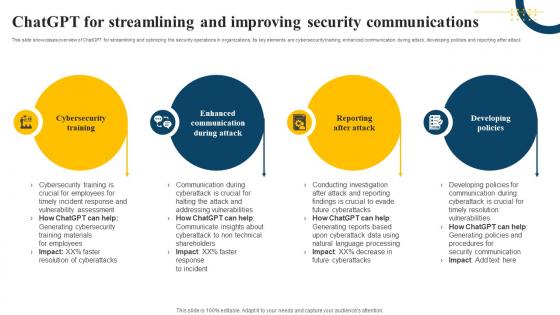 ChatGPT For Streamlining And Improving Security Communications Impact Of Generative AI SS V
ChatGPT For Streamlining And Improving Security Communications Impact Of Generative AI SS VThis slide showcases overview of ChatGPT for streamlining and optimizing the security operations in organizations. Its key elements are cybersecurity training, enhanced communication during attack, developing policies and reporting after attack. Increase audience engagement and knowledge by dispensing information using ChatGPT For Streamlining And Improving Security Communications Impact Of Generative AI SS V. This template helps you present information on four stages. You can also present information on Cybersecurity Training, Enhanced Communication, Reporting After Attack using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 ChatGPT Use Cases For Streamlining Security Operations Impact Of Generative AI SS V
ChatGPT Use Cases For Streamlining Security Operations Impact Of Generative AI SS VThis slide showcases various ChatGPT use cases for streamlining and automating the cybersecurity operations of organization. Its key elements are establish security policies, automate repetitive tasks and identification of vulnerabilities. Increase audience engagement and knowledge by dispensing information using ChatGPT Use Cases For Streamlining Security Operations Impact Of Generative AI SS V. This template helps you present information on three stages. You can also present information on Establish Security, Automate Repetitive Tasks, Identify Vulnerabilities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
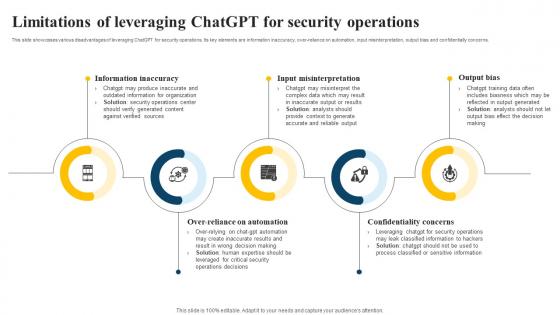 Limitations Of Leveraging ChatGPT For Security Operations Impact Of Generative AI SS V
Limitations Of Leveraging ChatGPT For Security Operations Impact Of Generative AI SS VThis slide showcases various disadvantages of leveraging ChatGPT for security operations. Its key elements are information inaccuracy, over-reliance on automation, input misinterpretation, output bias and confidentially concerns. Increase audience engagement and knowledge by dispensing information using Limitations Of Leveraging ChatGPT For Security Operations Impact Of Generative AI SS V. This template helps you present information on five stages. You can also present information on Information Inaccuracy, Input Misinterpretation, Confidentiality Concerns using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
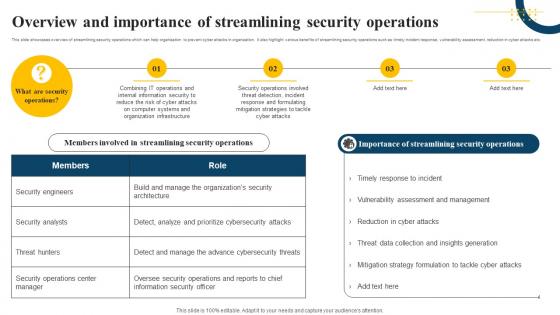 Overview And Importance Of Streamlining Security Operations Impact Of Generative AI SS V
Overview And Importance Of Streamlining Security Operations Impact Of Generative AI SS VThis slide showcases overview of streamlining security operations which can help organization to prevent cyber attacks in organization. It also highlight various benefits of streamlining security operations such as timely incident response, vulnerability assessment, reduction in cyber attacks etc. Increase audience engagement and knowledge by dispensing information using Overview And Importance Of Streamlining Security Operations Impact Of Generative AI SS V. This template helps you present information on four stages. You can also present information on Organization Infrastructure, Cyber Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Impact Of ATP Cyber Security Automation
Impact Of ATP Cyber Security AutomationThis slide depicts the ATP cyber security automation to detect virus. Its aim is to help prevent the virus in the system. This slide includes prevention, detection and mitigate. Presenting our set of slides with name Impact Of ATP Cyber Security Automation. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Prevent, Detec, Mitigate.
-
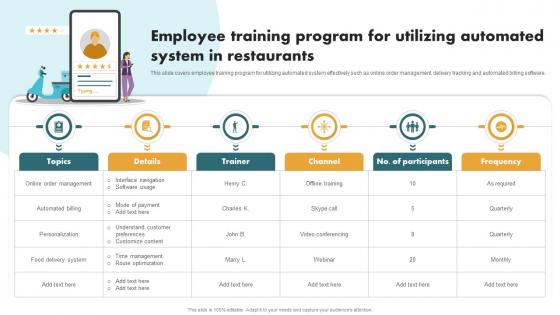 Securing Food Safety In Online Employee Training Program For Utilizing Automated
Securing Food Safety In Online Employee Training Program For Utilizing AutomatedThis slide covers employee training program for utilizing automated system effectively such as online order management, delivery tracking and automated billing software. Introducing Securing Food Safety In Online Employee Training Program For Utilizing Automated to increase your presentation threshold. Encompassed with Six stages, this template is a great option to educate and entice your audience. Dispence information on Online Order Management, Automated Billing, Personalization, Food Delivery System, using this template. Grab it now to reap its full benefits.
-
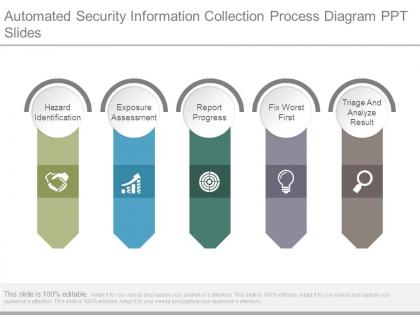 Automated security information collection process diagram ppt slides
Automated security information collection process diagram ppt slidesPresenting automated security information collection process diagram ppt slides. This is a automated security information collection process diagram ppt slides. This is a five stage process. The stages in this process are hazard identification, exposure assessment, report progress, fix worst first, triage and analyze result.
-
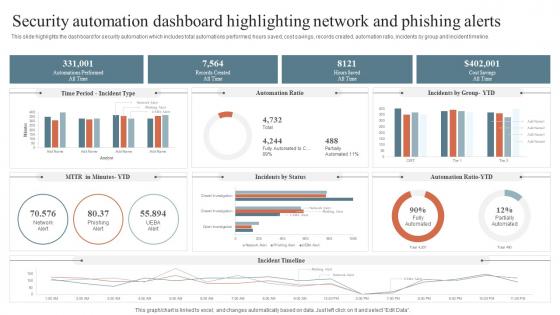 Security Automation Dashboard Highlighting Network And Phishing Alerts Security Orchestration Automation
Security Automation Dashboard Highlighting Network And Phishing Alerts Security Orchestration AutomationThis slide highlights the dashboard for security automation which includes total automations performed, hours saved, cost savings, records created, automation ratio, incidents by group and incident timeline. Deliver an outstanding presentation on the topic using this Security Automation Dashboard Highlighting Network And Phishing Alerts Security Orchestration Automation. Dispense information and present a thorough explanation of Security Automation, Dashboard Highlighting, Network And Phishing Alerts using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Time To Fix Security Threat With Manual Testing Security Orchestration Automation And Response Guide
Time To Fix Security Threat With Manual Testing Security Orchestration Automation And Response GuideThis slide highlights the time to fix the security threat and error with manual testing in bar graph format. It covers key takeaways which explains how much percent of error are fixed in 1 to 3 hour, 3 to 6 hour and working day etc. Present the topic in a bit more detail with this Time To Fix Security Threat With Manual Testing Security Orchestration Automation And Response Guide. Use it as a tool for discussion and navigation on Time To Fix, Security Threat, Manual Testing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Key Statistics Of It Security Automation System
Key Statistics Of It Security Automation SystemThe following slide highlights critical statistics of security automation in the IT industry. The statistics mentioned in the slide are alert processing, IR processing and preventing security exposures to network. Introducing our Key Statistics Of It Security Automation System set of slides. The topics discussed in these slides are Key Statistics, IT Security, Automation System. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
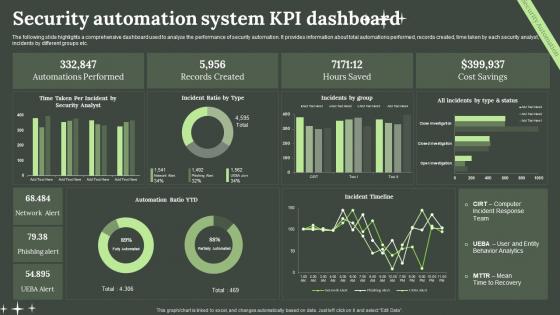 Security Automation System KPI Dashboard
Security Automation System KPI DashboardThe following slide highlights a comprehensive dashboard used to analyze the performance of security automation. It provides information about total automations performed, records created, time taken by each security analyst, incidents by different groups etc. Introducing our Security Automation System KPI Dashboard set of slides. The topics discussed in these slides are Security, Automation System, KPI Dashboard. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Statistics Showing Impact Of Security Automation System
Statistics Showing Impact Of Security Automation SystemThe following slide highlights key statistics of security automation of an organization. Information covered in this slide is related to current level of security automation such as high, medium, low and none. Introducing our Statistics Showing Impact Of Security Automation System set of slides. The topics discussed in these slides are Statistics Showing Impact, Security Automation System. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
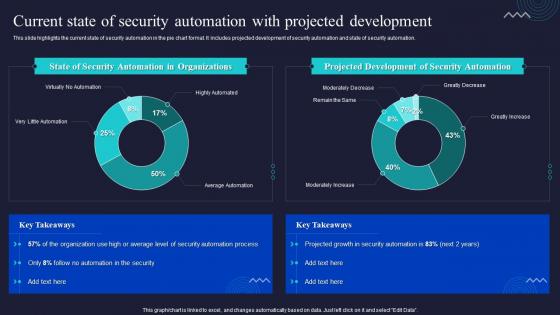 Current State Of Security Automation With Projected Development Enabling Automation In Cyber Security
Current State Of Security Automation With Projected Development Enabling Automation In Cyber SecurityThis slide highlights the current state of security automation in the pie chart format. It includes projected development of security automation and state of security automation. Deliver an outstanding presentation on the topic using this Current State Of Security Automation With Projected Development Enabling Automation In Cyber Security. Dispense information and present a thorough explanation of Automation, Development, Organizations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
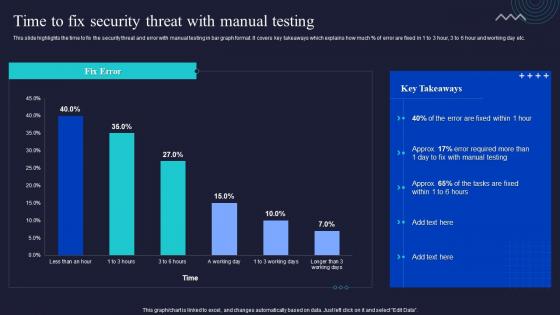 Enabling Automation In Cyber Security Operations Time To Fix Security Threat With Manual Testing
Enabling Automation In Cyber Security Operations Time To Fix Security Threat With Manual TestingThis slide highlights the time to fix the security threat and error with manual testing in bar graph format. It covers key takeaways which explains how much percent of error are fixed in 1 to 3 hour, 3 to 6 hour and working day etc. Present the topic in a bit more detail with this Enabling Automation In Cyber Security Operations Time To Fix Security Threat With Manual Testing. Use it as a tool for discussion and navigation on Manual, Testing, Security Threat. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
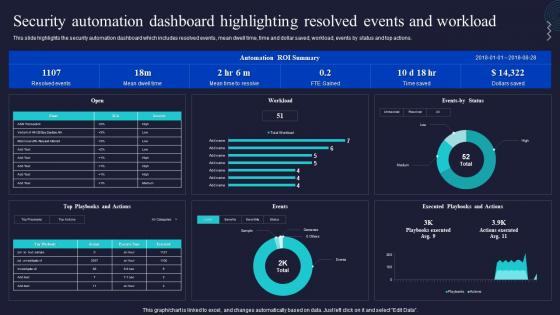 Security Automation Dashboard Highlighting Resolved Events And Workload Enabling Automation In Cyber Security
Security Automation Dashboard Highlighting Resolved Events And Workload Enabling Automation In Cyber SecurityThis slide highlights the security automation dashboard which includes resolved events, mean dwell time, time and dollar saved, workload, events by status and top actions. Deliver an outstanding presentation on the topic using this Security Automation Dashboard Highlighting Resolved Events And Workload Enabling Automation In Cyber Security. Dispense information and present a thorough explanation of Dashboard, Security Automation, Workload using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
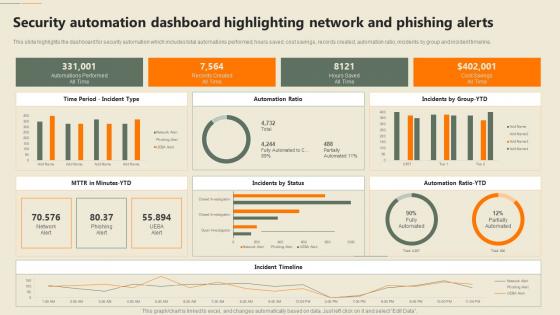 F652 Security Automation In Information Technology Security Automation Dashboard Highlighting Phishing
F652 Security Automation In Information Technology Security Automation Dashboard Highlighting PhishingThis slide highlights the dashboard for security automation which includes total automations performed, hours saved, cost savings, records created, automation ratio, incidents by group and incident timeline. Present the topic in a bit more detail with this F652 Security Automation In Information Technology Security Automation Dashboard Highlighting Phishing. Use it as a tool for discussion and navigation on Automation, Dashboard, Phishing Alerts. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
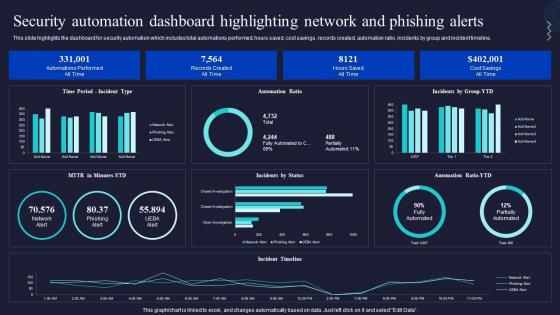 Security Automation Dashboard Highlighting Network Enabling Automation In Cyber Security Operations
Security Automation Dashboard Highlighting Network Enabling Automation In Cyber Security OperationsThis slide highlights the dashboard for security automation which includes total automations performed, hours saved, cost savings, records created, automation ratio, incidents by group and incident timeline. Present the topic in a bit more detail with this Security Automation Dashboard Highlighting Network Enabling Automation In Cyber Security Operations. Use it as a tool for discussion and navigation on Automation, Dashboard, Highlighting. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
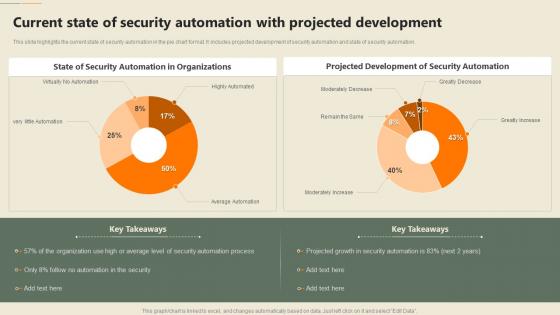 Security Automation In Information Technology Current State Of Security Automation With Projected Development
Security Automation In Information Technology Current State Of Security Automation With Projected DevelopmentThis slide highlights the current state of security automation in the pie chart format. It includes projected development of security automation and state of security automation. Deliver an outstanding presentation on the topic using this Security Automation In Information Technology Current State Of Security Automation With Projected Development. Dispense information and present a thorough explanation of Projected Development, Security Automation, Organizations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
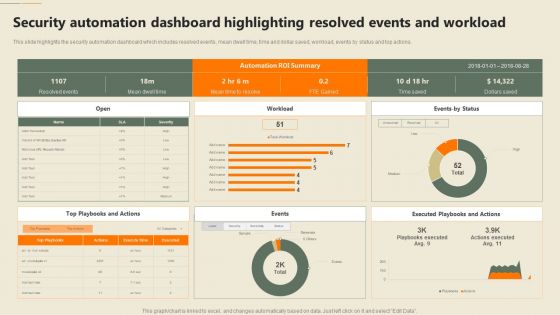 Security Automation Dashboard Highlighting Resolved Events Security Automation In Information Technology
Security Automation Dashboard Highlighting Resolved Events Security Automation In Information TechnologyThis slide highlights the security automation dashboard which includes resolved events, mean dwell time, time and dollar saved, workload, events by status and top actions. Deliver an outstanding presentation on the topic using this Security Automation Dashboard Highlighting Resolved Events Security Automation In Information Technology. Dispense information and present a thorough explanation of Automation, Dashboard, Workload using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
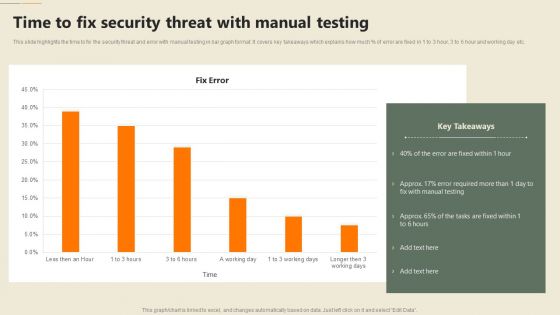 Security Automation In Information Technology Time To Fix Security Threat With Manual Testing
Security Automation In Information Technology Time To Fix Security Threat With Manual TestingThis slide highlights the time to fix the security threat and error with manual testing in bar graph format. It covers key takeaways which explains how much percent of error are fixed in 1 to 3 hour, 3 to 6 hour and working day etc. Deliver an outstanding presentation on the topic using this Security Automation In Information Technology Time To Fix Security Threat With Manual Testing. Dispense information and present a thorough explanation of Security, Threat, Manual Testing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
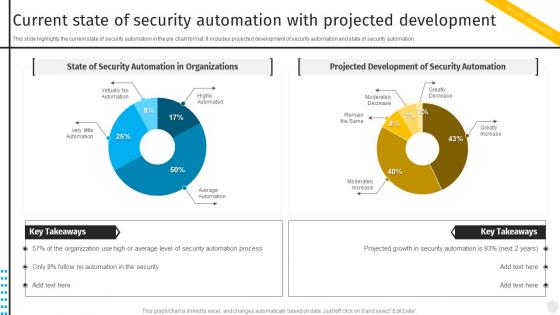 Current State Of Security Automation Projected Security Automation To Investigate And Remediate Cyberthreats
Current State Of Security Automation Projected Security Automation To Investigate And Remediate CyberthreatsThis slide highlights the current state of security automation in the pie chart format. It includes projected development of security automation and state of security automation. Deliver an outstanding presentation on the topic using this Current State Of Security Automation Projected Security Automation To Investigate And Remediate Cyberthreats. Dispense information and present a thorough explanation of Automation, Development, Process using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
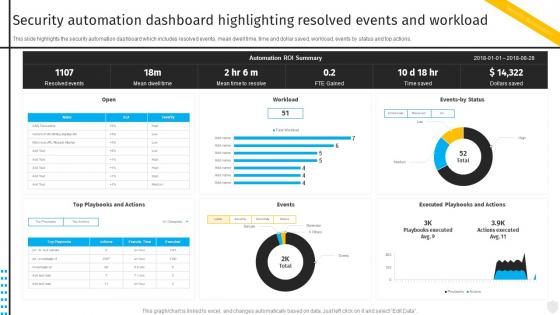 Security Automation Dashboard Highlighting Resolved Security Automation To Investigate And Remediate Cyberthreats
Security Automation Dashboard Highlighting Resolved Security Automation To Investigate And Remediate CyberthreatsThis slide highlights the security automation dashboard which includes resolved events, mean dwell time, time and dollar saved, workload, events by status and top actions. Present the topic in a bit more detail with this Security Automation Dashboard Highlighting Resolved Security Automation To Investigate And Remediate Cyberthreats. Use it as a tool for discussion and navigation on Automation, Dashboard, Workload. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
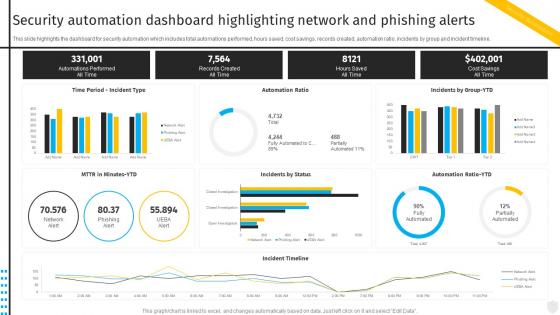 Security Automation To Investigate And Remediate Cyberthreats Security Automation Dashboard Highlighting Network
Security Automation To Investigate And Remediate Cyberthreats Security Automation Dashboard Highlighting NetworkThis slide highlights the dashboard for security automation which includes total automations performed, hours saved, cost savings, records created, automation ratio, incidents by group and incident timeline. Present the topic in a bit more detail with this Security Automation To Investigate And Remediate Cyberthreats Security Automation Dashboard Highlighting Network. Use it as a tool for discussion and navigation on Automation, Dashboard, Incident Timeline. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
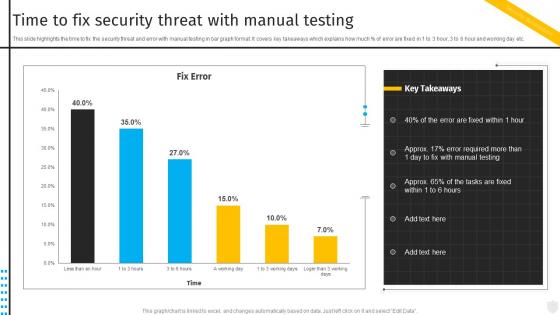 Time To Fix Security Threat With Manual Testing Security Automation To Investigate And Remediate Cyberthreats
Time To Fix Security Threat With Manual Testing Security Automation To Investigate And Remediate CyberthreatsThis slide highlights the time to fix the security threat and error with manual testing in bar graph format. It covers key takeaways which explains how much percent of error are fixed in 1 to 3 hour, 3 to 6 hour and working day etc. Deliver an outstanding presentation on the topic using this Time To Fix Security Threat With Manual Testing Security Automation To Investigate And Remediate Cyberthreats. Dispense information and present a thorough explanation of Security, Threat, Manual Testing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
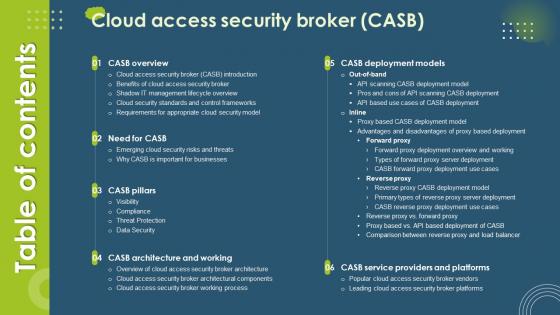 Table Of Contents Cloud Access Security Broker CASB Ppt Visual Aids Diagrams
Table Of Contents Cloud Access Security Broker CASB Ppt Visual Aids DiagramsIntroducing Table Of Contents Cloud Access Security Broker CASB Ppt Visual Aids Diagrams. to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Casb Overview, Need For Casb, Casb Pillars, using this template. Grab it now to reap its full benefits.
-
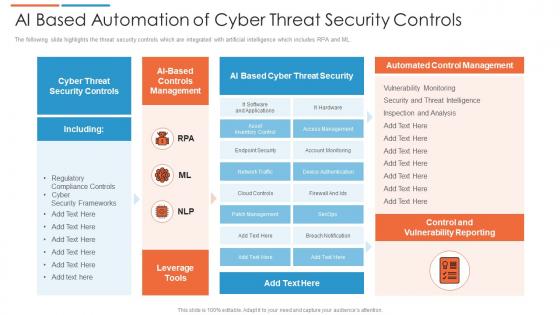 Ai based automation of cyber threat security controls
Ai based automation of cyber threat security controlsThe following slide highlights the threat security controls which are integrated with artificial intelligence which includes RPA and ML. Introducing our AI Based Automation Of Cyber Threat Security Controls set of slides. The topics discussed in these slides are Cyber Threat Security, Automated Control Management, Control And Vulnerability Reporting. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Eliminating Manual Security Processes Through Automation Risk Based Methodology To Cyber
Eliminating Manual Security Processes Through Automation Risk Based Methodology To CyberMentioned slide displays the workflow process of how company will eliminate its existing manual security processes through automation tools.Present the topic in a bit more detail with this Eliminating Manual Security Processes Through Automation Risk Based Methodology To Cyber Use it as a tool for discussion and navigation on Manual Vulnerability, Scanning And Resolution, Vulnerability Scanning This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Technology Security How Is Automation Used In Information Technology Security
Information Technology Security How Is Automation Used In Information Technology SecurityThis slide depicts the cyber protection of an organization through artificial intelligence and how it can be helpful in threat detection, threat response, and human augmentation. Introducing Information Technology Security How Is Automation Used In Information Technology Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Threat Detection, Threat Response, Human Augmentation, using this template. Grab it now to reap its full benefits.
-
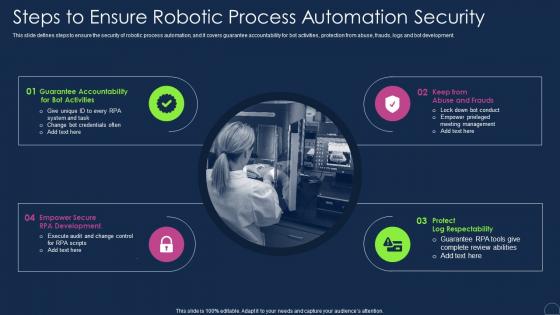 Steps To Ensure Robotic Process Automation Security Robotic Process Automation Types
Steps To Ensure Robotic Process Automation Security Robotic Process Automation TypesThis slide defines steps to ensure the security of robotic process automation, and it covers guarantee accountability for bot activities, protection from abuse, frauds, logs and bot development. Increase audience engagement and knowledge by dispensing information using Steps To Ensure Robotic Process Automation Security Robotic Process Automation Types. This template helps you present information on four stages. You can also present information on Process, Automation, Accountability using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Home Security Monitoring Ppt Powerpoint Presentation Gallery Aids Cpb
Home Security Monitoring Ppt Powerpoint Presentation Gallery Aids CpbPresenting Home Security Monitoring Ppt Powerpoint Presentation Gallery Aids Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Home Security Monitoring. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now
-
 Ai Transformation Playbook Stage Five Security Breach Readiness Checklist
Ai Transformation Playbook Stage Five Security Breach Readiness ChecklistPurpose of this slide is to illustrate readiness checklist that will assist businesses in countering any security breach in advance. Readiness level will be evaluated based on different questions.Present the topic in a bit more detail with this Ai Transformation Playbook Stage Five Security Breach Readiness Checklist Use it as a tool for discussion and navigation on Proper Risk Management, Each Organizational, Governance Procedures This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Access Control Methods Information Security Ppt Powerpoint Presentation Pictures Visual Aids Cpb
Access Control Methods Information Security Ppt Powerpoint Presentation Pictures Visual Aids CpbPresenting our Access Control Methods Information Security Ppt Powerpoint Presentation Pictures Visual Aids Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Access Control Methods Information Security. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
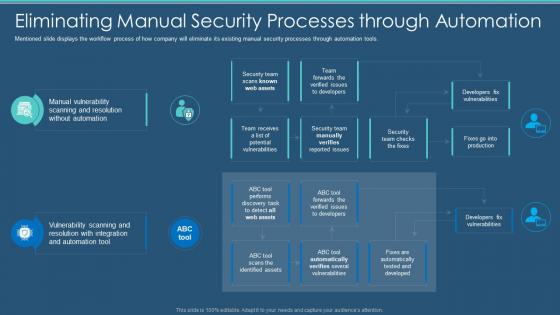 Information Security Program Eliminating Manual Security Processes Through Automation
Information Security Program Eliminating Manual Security Processes Through AutomationMentioned slide displays the workflow process of how company will eliminate its existing manual security processes through automation tools. Deliver an outstanding presentation on the topic using this Information Security Program Eliminating Manual Security Processes Through Automation. Dispense information and present a thorough explanation of Processes, Automation, Vulnerabilities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
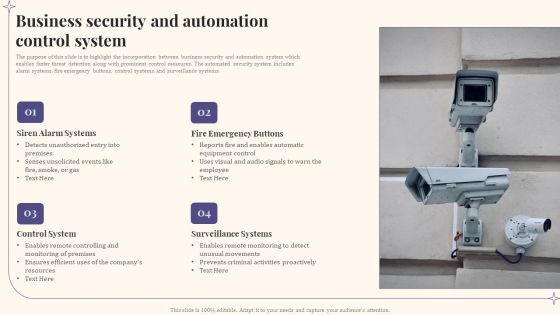 Business Security And Automation Control System
Business Security And Automation Control SystemThe purpose of this slide is to highlight the incorporation between business security and automation system which enables faster threat detection along with prominent control measures. The automated security system includes alarm systems, fire emergency buttons, control systems, and surveillance systems. Introducing our Business Security And Automation Control System set of slides. The topics discussed in these slides are Siren Alarm Systems, Fire Emergency Buttons, Control System. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Mobile Banking Application Security Ppt Powerpoint Presentation Visual Aids Infographics Cpb
Mobile Banking Application Security Ppt Powerpoint Presentation Visual Aids Infographics CpbPresenting our Mobile Banking Application Security Ppt Powerpoint Presentation Visual Aids Infographics Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Mobile Banking Application Security. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
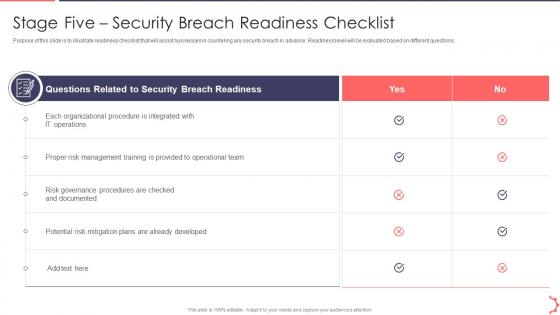 Stage Five Security Breach Readiness AI Playbook Accelerate Digital Transformation
Stage Five Security Breach Readiness AI Playbook Accelerate Digital TransformationPurpose of this slide is to illustrate readiness checklist that will assist businesses in countering any security breach in advance. Readiness level will be evaluated based on different questions.Present the topic in a bit more detail with this Stage Five Security Breach Readiness AI Playbook Accelerate Digital Transformation . Use it as a tool for discussion and navigation on Stage Five Security Breach Readiness Checklist . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security Deposit Accounting Ppt Powerpoint Presentation Visual Aids Layouts Cpb
Security Deposit Accounting Ppt Powerpoint Presentation Visual Aids Layouts CpbPresenting Security Deposit Accounting Ppt Powerpoint Presentation Visual Aids Layouts Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Security Deposit Accounting. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Information Security How Is Automation Used In Information Security
Information Security How Is Automation Used In Information SecurityThis slide depicts the cyber protection of an organization through artificial intelligence and how it can be helpful in threat detection, threat response, and human augmentation. Increase audience engagement and knowledge by dispensing information using Information Security How Is Automation Used In Information Security. This template helps you present information on three stages. You can also present information on Threat Detection, Human Augmentation, Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Automatic Technology Steps To Ensure Robotic Process Automation Security
Automatic Technology Steps To Ensure Robotic Process Automation SecurityThis slide defines steps to ensure the security of robotic process automation, and it covers guarantee accountability for bot activities, protection from abuse, frauds, logs and bot development. Introducing Automatic Technology Steps To Ensure Robotic Process Automation Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Guarantee Accountability, Protect Log Respectability, RPA Development, using this template. Grab it now to reap its full benefits.
-
 Steps to ensure automation security ppt powerpoint presentation portfolio maker
Steps to ensure automation security ppt powerpoint presentation portfolio makerThis slide defines steps to ensure the security of robotic process automation, and it covers guarantee accountability for bot activities, protection from abuse, frauds, logs and bot development. Increase audience engagement and knowledge by dispensing information using Steps To Ensure Automation Security Ppt Powerpoint Presentation Portfolio Maker. This template helps you present information on four stages. You can also present information on Guarantee Accountability, Protect Log Respectability, RPA Development using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Automating threat identification security information and event management
Automating threat identification security information and event managementIncrease audience engagement and knowledge by dispensing information using Automating Threat Identification Security Information And Event Management. This template helps you present information on four stages. You can also present information on Information, Management, Compliance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Automating threat identification table of contents security information and event management
Automating threat identification table of contents security information and event managementIncrease audience engagement and knowledge by dispensing information using Automating Threat Identification Table Of Contents Security Information And Event Management. This template helps you present information on eleven stages. You can also present information on Company Overview, Management, Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
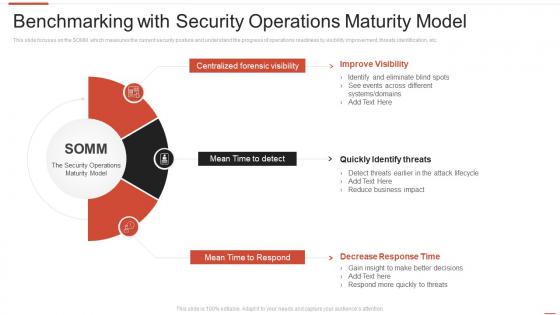 Benchmarking with security operations maturity model automating threat identification
Benchmarking with security operations maturity model automating threat identificationThis slide focuses on the SOMM which measures the current security posture and understand the progress of operations readiness by visibility improvement, threats identification, etc. Introducing Benchmarking With Security Operations Maturity Model Automating Threat Identification to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Centralized Forensic Visibility, Mean Time To Detect, Mean Time To Respond, using this template. Grab it now to reap its full benefits.
-
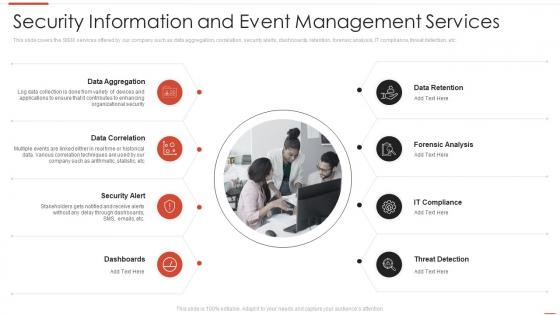 Security information and event management services automating threat identification
Security information and event management services automating threat identificationThis slide covers the SIEM services offered by our company such as data aggregation, correlation, security alerts, dashboards, retention, forensic analysis, IT compliance, threat detection, etc. Increase audience engagement and knowledge by dispensing information using Security Information And Event Management Services Automating Threat Identification. This template helps you present information on eight stages. You can also present information on Data Aggregation, Data Correlation, Security Alert using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 4 steps of rpa security for process automation improvement
4 steps of rpa security for process automation improvementPresenting our set of slides with 4 Steps Of RPA Security For Process Automation Improvement. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Ensure Accountability, Protect Log Integrity, Enable Secure RPA Development.
-
 Brand monitoring cyber security ppt powerpoint presentation visual aids pictures cpb
Brand monitoring cyber security ppt powerpoint presentation visual aids pictures cpbPresenting our Brand Monitoring Cyber Security Ppt Powerpoint Presentation Visual Aids Pictures Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Brand Monitoring Cyber Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Economic security unemployment ppt powerpoint presentation visual aids slides cpb
Economic security unemployment ppt powerpoint presentation visual aids slides cpbPresenting Economic Security Unemployment Ppt Powerpoint Presentation Visual Aids Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Economic Security Unemployment. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Deferred social security benefits ppt powerpoint presentation visual aids example file cpb
Deferred social security benefits ppt powerpoint presentation visual aids example file cpbPresenting our Deferred Social Security Benefits Ppt Powerpoint Presentation Visual Aids Example File Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Deferred Social Security Benefits. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 How is automation used in electronic information security
How is automation used in electronic information securityThis slide depicts the cyber protection of an organization through artificial intelligence and how it can be helpful in threat detection, threat response, and human augmentation. Increase audience engagement and knowledge by dispensing information using How Is Automation Used In Electronic Information Security. This template helps you present information on three stages. You can also present information on Threat Detection, Threat Response, Human Augmentation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Network Security How Is Automation Used In Networksecurity
Network Security How Is Automation Used In NetworksecurityThis slide depicts the network protection of an organization through artificial intelligence and how it can be helpful in threat detection, threat response, and human augmentation. Increase audience engagement and knowledge by dispensing information using Network Security How Is Automation Used In Networksecurity. This template helps you present information on three stages. You can also present information on Threat Detection, Threat Response, Human Detection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Meet Our Team Information System Security And Risk Administration Plan Ppt Styles Visual Aids
Meet Our Team Information System Security And Risk Administration Plan Ppt Styles Visual AidsIntroducing Meet Our Team Information System Security And Risk Administration Plan Ppt Styles Visual Aids to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Meet Our Team, using this template. Grab it now to reap its full benefits.
-
 Steps For Information Security Risk Management Ppt Powerpoint Presentation File Aids
Steps For Information Security Risk Management Ppt Powerpoint Presentation File AidsThis slide steps which can help organization to implement information security risk management program in organization. Its key steps are identify, protect, detect and respond. Increase audience engagement and knowledge by dispensing information using Steps For Information Security Risk Management Ppt Powerpoint Presentation File Aids. This template helps you present information on five stages. You can also present information on Protect, Respond, Detect using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.



