Powerpoint Templates and Google slides for Security Automation Tools
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
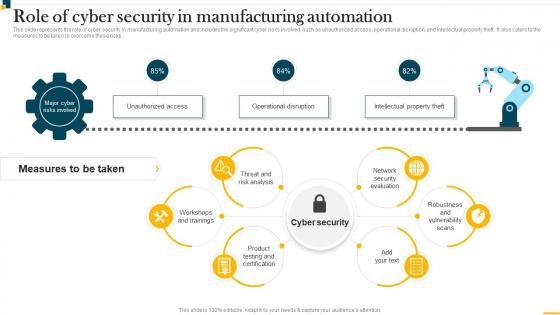 IT In Manufacturing Industry Role Of Cyber Security In Manufacturing Automation
IT In Manufacturing Industry Role Of Cyber Security In Manufacturing AutomationThis slide represents the role of cyber security in manufacturing automation and includes the significant cyber risks involved, such as unauthorized access, operational disruption, and intellectual property theft. It also caters to the measures to be taken to overcome these risks. Present the topic in a bit more detail with this IT In Manufacturing Industry Role Of Cyber Security In Manufacturing Automation. Use it as a tool for discussion and navigation on Threat And Risk Analysis, Network Security Evaluation, Workshops And Trainings. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 AI Security Concerns In Powerpoint And Google Slides Cpb
AI Security Concerns In Powerpoint And Google Slides CpbPresenting AI Security Concerns In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like AI Security Concerns. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
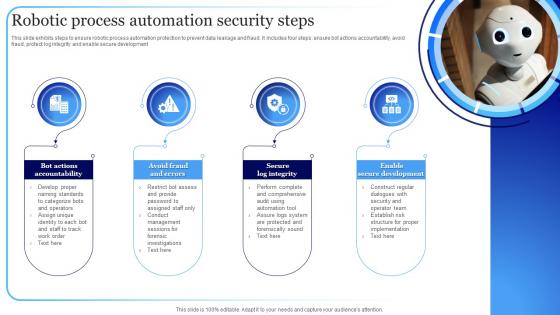 Robotic Process Automation Security Steps
Robotic Process Automation Security StepsThis slide exhibits steps to ensure robotic process automation protection to prevent data leakage and fraud. It includes four steps ensure bot actions accountability, avoid fraud, protect log integrity and enable secure development. Presenting our set of slides with name Robotic Process Automation Security Steps. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Bot Actions Accountability, Avoid Fraud And Errors, Secure Log Integrity.
-
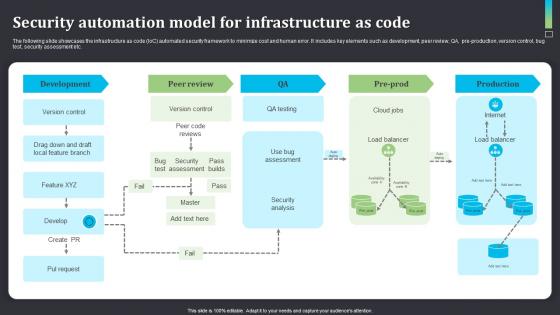 Security Automation Model For Infrastructure As Code
Security Automation Model For Infrastructure As CodeThe following slide showcases the infrastructure as code IoC automated security framework to minimize cost and human error. It includes key elements such as development, peer review, QA, pre production, version control, bug test, security assessment etc. Introducing our Security Automation Model For Infrastructure As Code set of slides. The topics discussed in these slides are Development, Peer Review, Version Control, Production. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Automated Enterprise Security Operation Icon
Automated Enterprise Security Operation IconPresenting our set of slides with Automated Enterprise Security Operation Icon. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Automated Enterprise, Security Operation Icon.
-
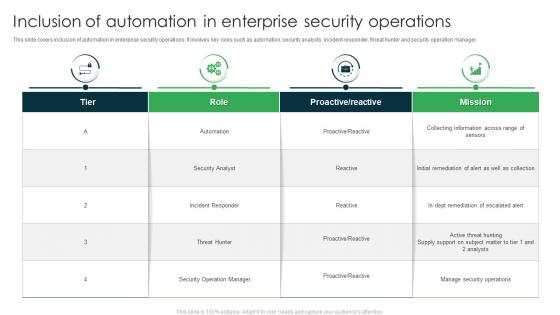 Inclusion Of Automation In Enterprise Security Operations
Inclusion Of Automation In Enterprise Security OperationsThis slide covers inclusion of automation in enterprise security operations. It involves key roles such as automation, security analysts, incident responder, threat hunter and security operation manager. Presenting our well structured Inclusion Of Automation In Enterprise Security Operations. The topics discussed in this slide are Security Analyst, Incident Responder, Security Operation Manager. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
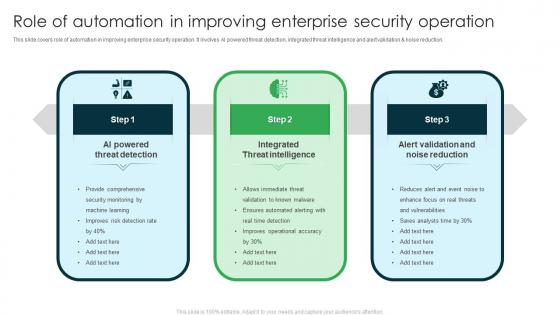 Role Of Automation In Improving Enterprise Security Operation
Role Of Automation In Improving Enterprise Security OperationThis slide covers role of automation in improving enterprise security operation. It involves AI powered threat detection, integrated threat intelligence and alert validation and noise reduction. Presenting our set of slides with Role Of Automation In Improving Enterprise Security Operation. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on AI Powered Threat Detection, Integrated Threat Intelligence, Alert Validation And Noise Reduction.
-
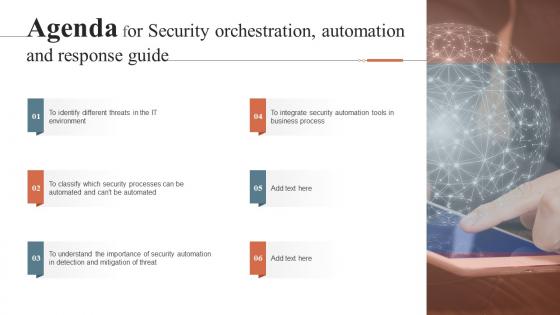 Agenda For Security Orchestration Automation And Response Guide Ppt Gallery Graphics Example
Agenda For Security Orchestration Automation And Response Guide Ppt Gallery Graphics ExampleIntroducing Agenda For Security Orchestration Automation And Response Guide Ppt Gallery Graphics Example to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Security Orchestration, Automation, Response Guide, using this template. Grab it now to reap its full benefits.
-
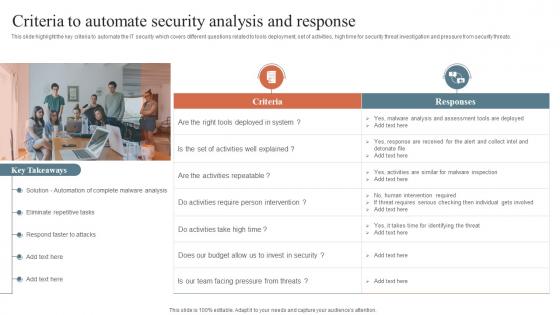 Criteria To Automate Security Analysis And Response Security Orchestration Automation
Criteria To Automate Security Analysis And Response Security Orchestration AutomationThis slide highlight the key criteria to automate the IT security which covers different questions related to tools deployment, set of activities, high time for security threat investigation and pressure from security threats. Increase audience engagement and knowledge by dispensing information using Criteria To Automate Security Analysis And Response Security Orchestration Automation. This template helps you present information on one stages. You can also present information on Malware Analysis, Eliminate Repetitive Tasks, Respond Faster To Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
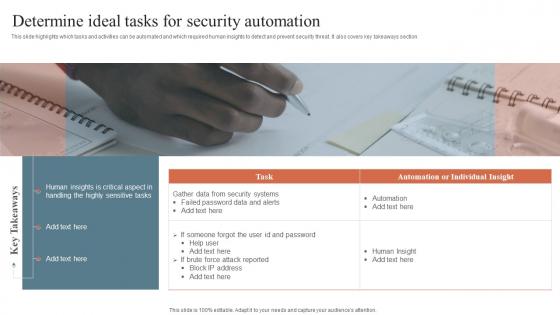 Determine Ideal Tasks For Security Automation Security Orchestration Automation And Response Guide
Determine Ideal Tasks For Security Automation Security Orchestration Automation And Response GuideThis slide highlights which tasks and activities can be automated and which required human insights to detect and prevent security threat. It also covers key takeaways section. Introducing Determine Ideal Tasks For Security Automation Security Orchestration Automation And Response Guide to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Determine Ideal, Tasks For Security, Automation, using this template. Grab it now to reap its full benefits.
-
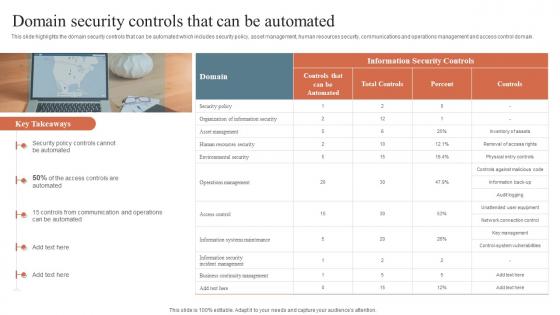 Domain Security Controls That Can Be Automated Security Orchestration Automation And Response Guide
Domain Security Controls That Can Be Automated Security Orchestration Automation And Response GuideThis slide highlights the domain security controls that can be automated which includes security policy, asset management, human resources security, communications and operations management and access control domain. Increase audience engagement and knowledge by dispensing information using Domain Security Controls That Can Be Automated Security Orchestration Automation And Response Guide. This template helps you present information on one stages. You can also present information on Security Policy, Communication And Operations, Security Controls using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
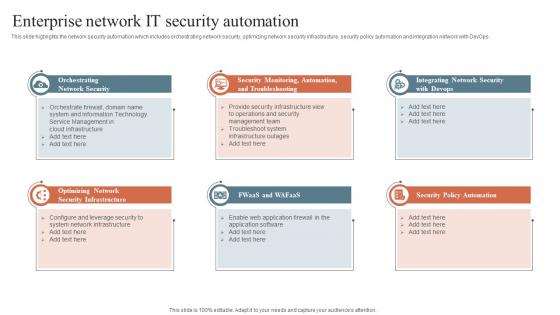 Enterprise Network It Security Automation Security Orchestration Automation And Response Guide
Enterprise Network It Security Automation Security Orchestration Automation And Response GuideThis slide highlights the network security automation which includes orchestrating network security, optimizing network security infrastructure, security policy automation and integration network with DevOps. Introducing Enterprise Network It Security Automation Security Orchestration Automation And Response Guide to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Network Security, Security Infrastructure, Security Policy Automation, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Security Orchestration Automation And Response Guide Ppt Gallery File Formats
Icons Slide For Security Orchestration Automation And Response Guide Ppt Gallery File FormatsIntroducing our well researched set of slides titled Icons Slide For Security Orchestration Automation And Response Guide Ppt Gallery File Formats. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
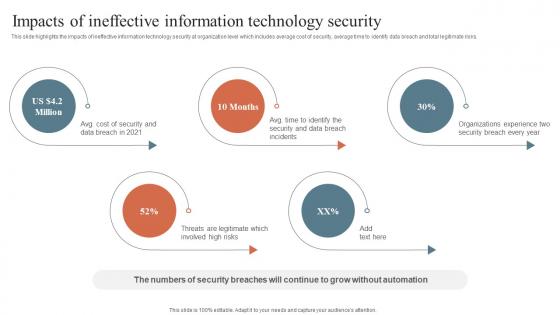 Impacts Of Ineffective Information Technology Security Security Orchestration Automation
Impacts Of Ineffective Information Technology Security Security Orchestration AutomationThis slide highlights the impacts of ineffective information technology security at organization level which includes average cost of security, average time to identify data breach and total legitimate risks. Introducing Impacts Of Ineffective Information Technology Security Security Orchestration Automation to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Impacts Of Ineffective, Information Technology, Security, using this template. Grab it now to reap its full benefits.
-
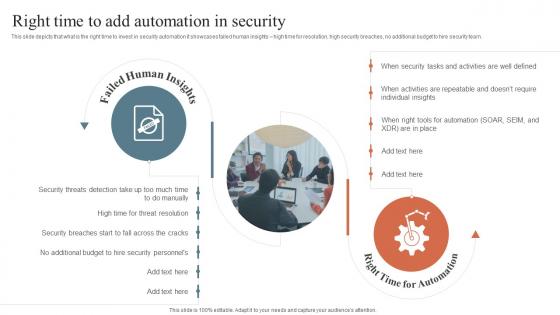 Right Time To Add Automation In Security Security Orchestration Automation And Response Guide
Right Time To Add Automation In Security Security Orchestration Automation And Response GuideThis slide depicts that what is the right time to invest in security automation it showcases failed human insights high time for resolution, high security breaches, no additional budget to hire security team. Introducing Right Time To Add Automation In Security Security Orchestration Automation And Response Guide to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Failed Human Insights, Right Time For Automation, Automation In Security, using this template. Grab it now to reap its full benefits.
-
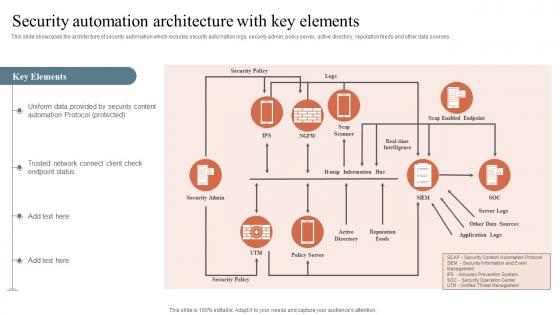 Security Automation Architecture With Key Elements Security Orchestration Automation And Response
Security Automation Architecture With Key Elements Security Orchestration Automation And ResponseThis slide showcases the architecture of security automation which includes security automation logs, security admin, policy server, active directory, reputation feeds and other data sources. Deliver an outstanding presentation on the topic using this Security Automation Architecture With Key Elements Security Orchestration Automation And Response. Dispense information and present a thorough explanation of Security Automation, Architecture, Trusted Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
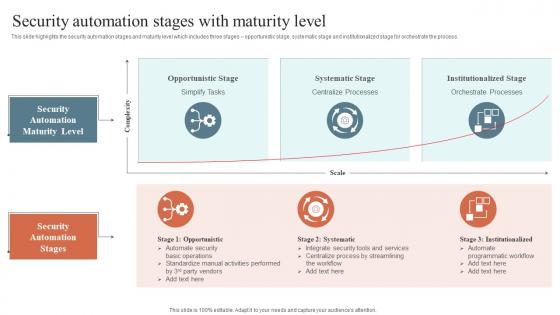 Security Automation Stages With Maturity Level Security Orchestration Automation And Response Guide
Security Automation Stages With Maturity Level Security Orchestration Automation And Response GuideThis slide highlights the security automation stages and maturity level which includes three stages opportunistic stage, systematic stage and institutionalized stage for orchestrate the process. Increase audience engagement and knowledge by dispensing information using Security Automation Stages With Maturity Level Security Orchestration Automation And Response Guide. This template helps you present information on two stages. You can also present information on Opportunistic Stage, Systematic Stage, Institutionalized Stage using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
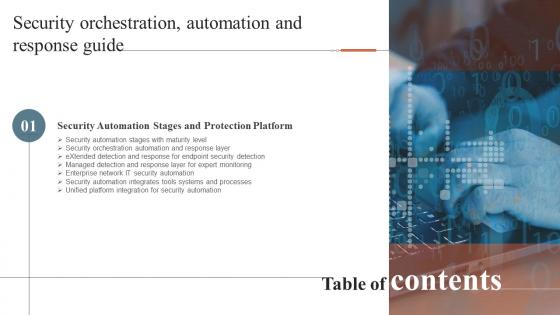 Security Orchestration Automation And Response Guide For Table Of Contents Ppt Gallery Format
Security Orchestration Automation And Response Guide For Table Of Contents Ppt Gallery FormatIntroducing Security Orchestration Automation And Response Guide For Table Of Contents Ppt Gallery Format to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Security Orchestration, Automation, Response Guide, using this template. Grab it now to reap its full benefits.
-
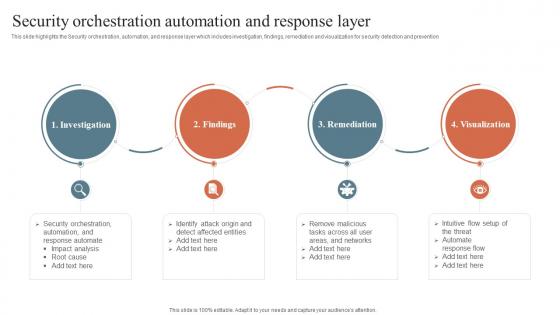 Security Orchestration Automation And Response Layer Security Orchestration Automation
Security Orchestration Automation And Response Layer Security Orchestration AutomationThis slide highlights the Security orchestration, automation, and response layer which includes investigation, findings, remediation and visualization for security detection and prevention. Increase audience engagement and knowledge by dispensing information using Security Orchestration Automation And Response Layer Security Orchestration Automation. This template helps you present information on four stages. You can also present information on Investigation, Remediation, Visualization, Findings using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
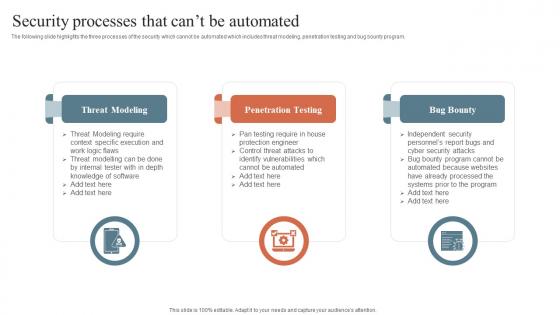 Security Processes That Cant Be Automated Security Orchestration Automation And Response Guide
Security Processes That Cant Be Automated Security Orchestration Automation And Response GuideThe following slide highlights the three processes of the security which cannot be automated which includes threat modeling, penetration testing and bug bounty program. Introducing Security Processes That Cant Be Automated Security Orchestration Automation And Response Guide to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Threat Modeling, Penetration Testing, Bug Bounty, using this template. Grab it now to reap its full benefits.
-
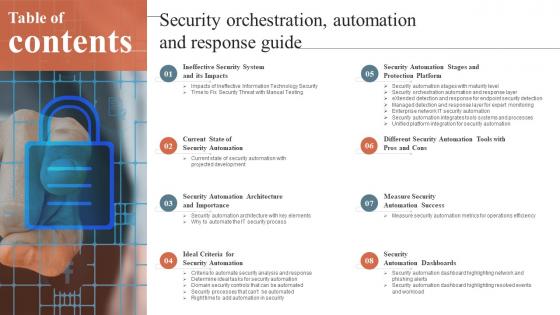 Table Of Contents For Security Orchestration Automation And Response Guide Ppt Gallery Gridlines
Table Of Contents For Security Orchestration Automation And Response Guide Ppt Gallery GridlinesIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Security Orchestration Automation And Response Guide Ppt Gallery Gridlines. This template helps you present information on eight stages. You can also present information on Measure Security, Automation Success, Security Automation Dashboards using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
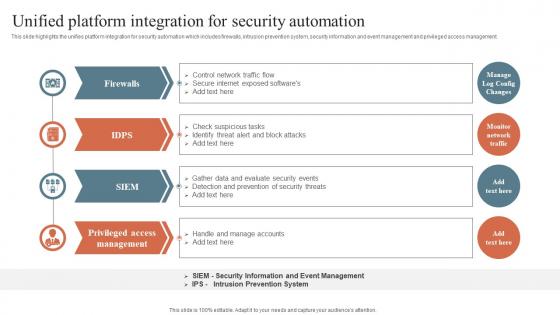 Unified Platform Integration For Security Automation Security Orchestration Automation And Response
Unified Platform Integration For Security Automation Security Orchestration Automation And ResponseThis slide highlights the unifies platform integration for security automation which includes firewalls, intrusion prevention system, security information and event management and privileged access management. Introducing Unified Platform Integration For Security Automation Security Orchestration Automation And Response to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Unified Platform, Integration For Security, Privileged Access, using this template. Grab it now to reap its full benefits.
-
 Why To Automate The It Security Process Security Orchestration Automation And Response Guide
Why To Automate The It Security Process Security Orchestration Automation And Response GuideThis slide highlights the benefits or importance of automation security process which includes better threat detection, faster containment, improve productivity, admin role delegation and incident response. Increase audience engagement and knowledge by dispensing information using Why To Automate The It Security Process Security Orchestration Automation And Response Guide. This template helps you present information on five stages. You can also present information on Better Threat Detection, Faster Containment, Improve Productivity using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
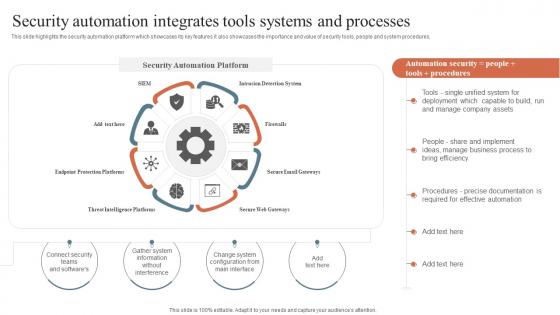 Security Orchestration Automation Security Automation Integrates Tools Systems And Processes
Security Orchestration Automation Security Automation Integrates Tools Systems And ProcessesThis slide highlights the different security automation tools which incudes robotic process automation. Security orchestration, automation and response, extended detection and SIEM. Deliver an outstanding presentation on the topic using this Security Orchestration Automation Security Automation Integrates Tools Systems And Processes. Dispense information and present a thorough explanation of Security Automation, Robotic Process, Security Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security Orchestration Automation And Response Different Security Automation Tools With Pros And Cons
Security Orchestration Automation And Response Different Security Automation Tools With Pros And ConsThis slide highlights the security automation platform which showcases its key features it also showcases the importance and value of security tools, people and system procedures. Introducing Security Orchestration Automation And Response Different Security Automation Tools With Pros And Cons to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Security Automation, Integrates Tools, Systems And Processes, using this template. Grab it now to reap its full benefits.
-
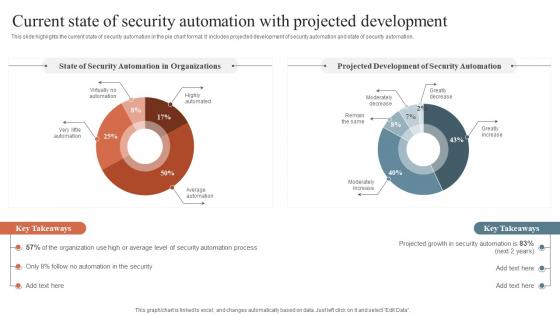 Security Orchestration Automation Current State Of Security Automation With Projected Development
Security Orchestration Automation Current State Of Security Automation With Projected DevelopmentThis slide highlights the different security automation tools which incudes robotic process automation. Security orchestration, automation and response, extended detection and SIEM. Present the topic in a bit more detail with this Security Orchestration Automation Current State Of Security Automation With Projected Development. Use it as a tool for discussion and navigation on Security Information, Event Management, Security Orchestration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
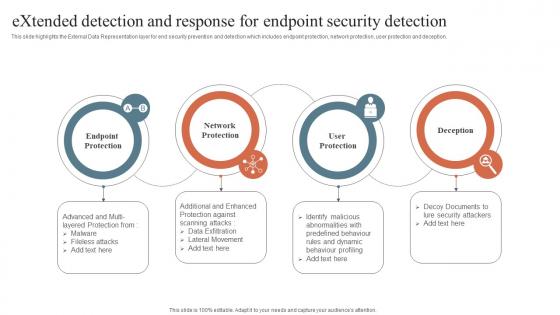 Security Orchestration Automation Extended Detection And Response For Endpoint Security Detection
Security Orchestration Automation Extended Detection And Response For Endpoint Security DetectionThis slide highlights the External Data Representation layer for end security prevention and detection which includes endpoint protection, network protection, user protection and deception. Introducing Security Orchestration Automation Extended Detection And Response For Endpoint Security Detection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Network Protection, Endpoint Protection, User Protection, using this template. Grab it now to reap its full benefits.
-
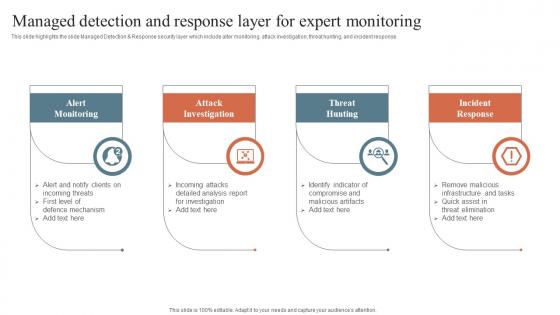 Security Orchestration Automation Managed Detection And Response Layer For Expert Monitoring
Security Orchestration Automation Managed Detection And Response Layer For Expert MonitoringThis slide highlights the slide Managed Detection and Response security layer which include alter monitoring, attack investigation, threat hunting, and incident response. Increase audience engagement and knowledge by dispensing information using Security Orchestration Automation Managed Detection And Response Layer For Expert Monitoring. This template helps you present information on four stages. You can also present information on Alert Monitoring, Attack Investigation, Threat Hunting using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
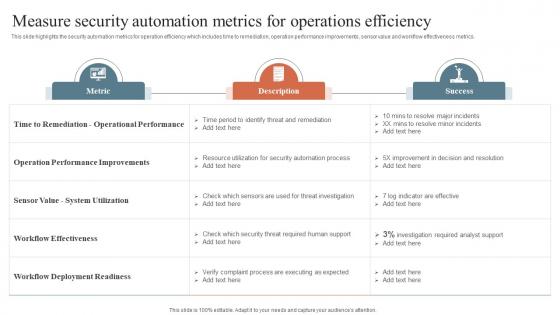 Security Orchestration Automation Measure Security Automation Metrics For Operations Efficiency
Security Orchestration Automation Measure Security Automation Metrics For Operations EfficiencyThis slide highlights the security automation metrics for operation efficiency which includes time to remediation, operation performance improvements, sensor value and workflow effectiveness metrics. Present the topic in a bit more detail with this Security Orchestration Automation Measure Security Automation Metrics For Operations Efficiency. Use it as a tool for discussion and navigation on Operational Performance, Deployment Readiness, System Utilization. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
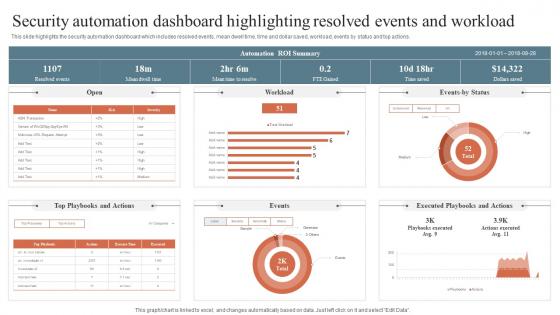 Security Orchestration Security Automation Dashboard Highlighting Resolved Events And Workload
Security Orchestration Security Automation Dashboard Highlighting Resolved Events And WorkloadThis slide highlights the security automation platform which showcases its key features it also showcases the importance and value of security tools, people and system procedures. Introducing Security Orchestration Security Automation Dashboard Highlighting Resolved Events And Workload to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Endpoint Protection Platforms, Secure Email Gateways, Intrusion Detection System, using this template. Grab it now to reap its full benefits.
-
 Use Of Artificial Intelligence AI In Cyber Security To Enhance Safety
Use Of Artificial Intelligence AI In Cyber Security To Enhance SafetyThis slide covers use of artificial intelligence in cyber security to enhance safety. It involves uses such as detecting new threats, battling bots, breach risk prediction and better end point protection. Introducing our premium set of slides with name Use Of Artificial Intelligence AI In Cyber Security To Enhance Safety. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Countering Bots, Breach Risk Prediction, Better Endpoint Protection. So download instantly and tailor it with your information.
-
 About Us Security Automation To Investigate And Remediate Cyberthreats
About Us Security Automation To Investigate And Remediate CyberthreatsIntroducing About Us Security Automation To Investigate And Remediate Cyberthreats to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on About Us, using this template. Grab it now to reap its full benefits.
-
 Financial Security Automation To Investigate And Remediate Cyberthreats
Financial Security Automation To Investigate And Remediate CyberthreatsIncrease audience engagement and knowledge by dispensing information using Financial Security Automation To Investigate And Remediate Cyberthreats. This template helps you present information on three stages. You can also present information on Financial using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Our Mission Security Automation To Investigate And Remediate Cyberthreats
Our Mission Security Automation To Investigate And Remediate CyberthreatsIntroducing Our Mission Security Automation To Investigate And Remediate Cyberthreats to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Our Mission, using this template. Grab it now to reap its full benefits.
-
 Quotes Security Automation To Investigate And Remediate Cyberthreats
Quotes Security Automation To Investigate And Remediate CyberthreatsIncrease audience engagement and knowledge by dispensing information using Quotes Security Automation To Investigate And Remediate Cyberthreats. This template helps you present information on one stages. You can also present information on Quotes using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Thanks For Watching Security Automation To Investigate And Remediate Cyberthreats
Thanks For Watching Security Automation To Investigate And Remediate CyberthreatsIntroducing Thanks For Watching Security Automation To Investigate And Remediate Cyberthreats to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Thanks For Watching, using this template. Grab it now to reap its full benefits.
-
 Automation Icon To Improve Cyber Security
Automation Icon To Improve Cyber SecurityPresenting our set of slides with name Automation Icon To Improve Cyber Security. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Automation Icon, Improve Cyber Security.
-
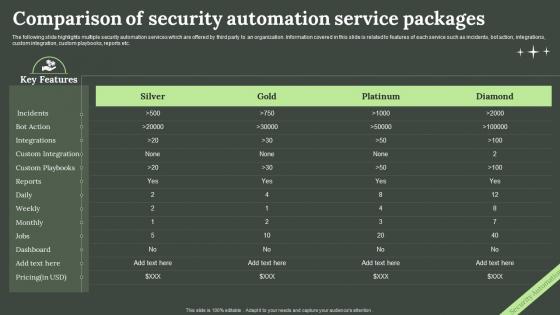 Comparison Of Security Automation Service Packages
Comparison Of Security Automation Service PackagesThe following slide highlights multiple security automation services which are offered by third party to an organization. Information covered in this slide is related to features of each service such as incidents, bot action, integrations, custom integration, custom playbooks, reports etc. Introducing our Comparison Of Security Automation Service Packages set of slides. The topics discussed in these slides are Comparison, Security Automation Service, Packages. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
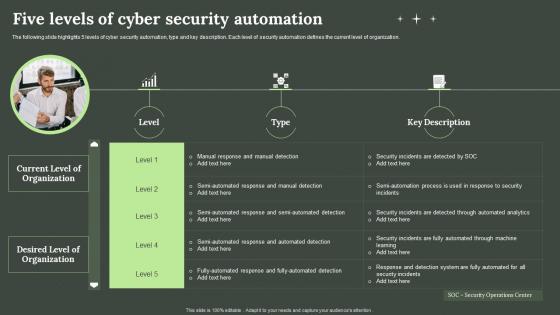 Five Levels Of Cyber Security Automation
Five Levels Of Cyber Security AutomationThe following slide highlights 5 levels of cyber security automation, type and key description. Each level of security automation defines the current level of organization. Presenting our well-structured Five Levels Of Cyber Security Automation. The topics discussed in this slide are Five Levels, Cyber Security Automation. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
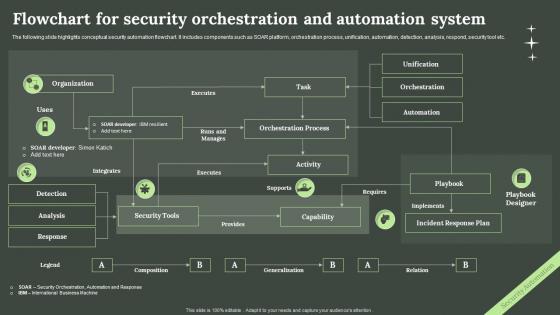 Flowchart For Security Orchestration And Automation System
Flowchart For Security Orchestration And Automation SystemThe following slide highlights conceptual security automation flowchart. It includes components such as SOAR platform, orchestration process, unification, automation, detection, analysis, respond, security tool etc. Introducing our Flowchart For Security Orchestration And Automation System set of slides. The topics discussed in these slides are Organization, Task, Provides, Capability, Requires. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
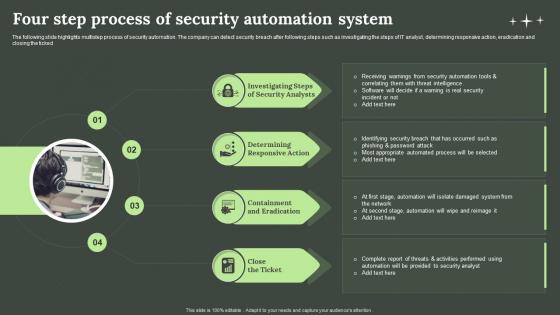 Four Step Process Of Security Automation System
Four Step Process Of Security Automation SystemThe following slide highlights multistep process of security automation. The company can detect security breach after following steps such as investigating the steps of IT analyst, determining responsive action, eradication and closing the ticked Presenting our set of slides with name Four Step Process Of Security Automation System. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Investigating Steps, Security Analysts, Eradication.
-
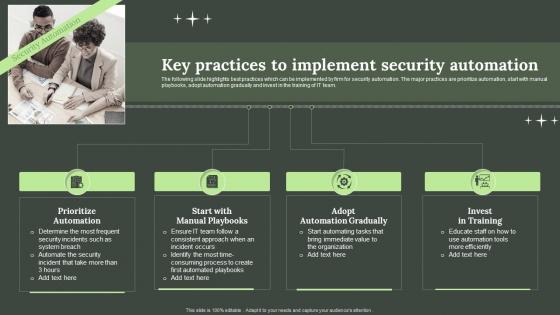 Key Practices To Implement Security Automation
Key Practices To Implement Security AutomationThe following slide highlights best practices which can be implemented by firm for security automation. The major practices are prioritize automation, start with manual playbooks, adopt automation gradually and invest in the training of IT team. Introducing our premium set of slides with Key Practices To Implement Security Automation. Elucidate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Prioritize Automation, Start Manual Playbooks, Adopt Automation Gradually. So download instantly and tailor it with your information.
-
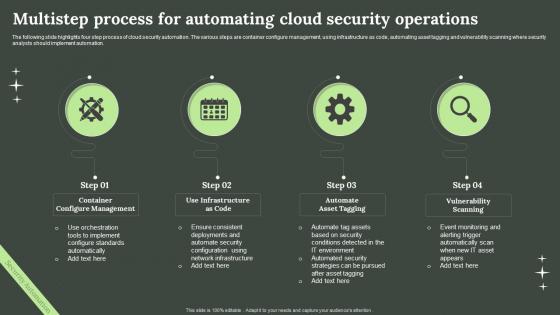 Multistep Process For Automating Cloud Security Operations
Multistep Process For Automating Cloud Security OperationsThe following slide highlights four step process of cloud security automation. The various steps are container configure management, using infrastructure as code, automating asset tagging and vulnerability scanning where security analysts should implement automation. Introducing our premium set of slides with Multistep Process For Automating Cloud Security Operations. Elucidate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Container Configure Management, Infrastructure As Code, Vulnerability Scanning. So download instantly and tailor it with your information.
-
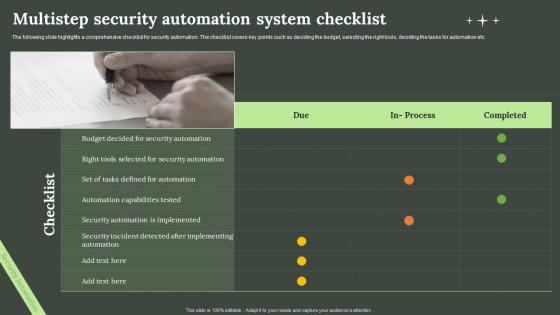 Multistep Security Automation System Checklist
Multistep Security Automation System ChecklistThe following slide highlights a comprehensive checklist for security automation. The checklist covers key points such as deciding the budget, selecting the right tools, deciding the tasks for automation etc. Presenting our set of slides with name Multistep Security Automation System Checklist. This exhibits information on one stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Multistep, Security Automation System, Checklist.
-
 Roles And Responsibilities Of Security Automation Team
Roles And Responsibilities Of Security Automation TeamThe following slide highlights key responsibilities of the security automation team with the position level and requirements. The various positions mentioned in the slide are security engineer, senior security engineer, distinguished security engineer and security automation manager. Introducing our Roles And Responsibilities Of Security Automation Team set of slides. The topics discussed in these slides are Security Engineer, Responsibilities, Position, Requirements. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Security Automation System Icon With Gear
Security Automation System Icon With GearIntroducing our premium set of slides with Security Automation System Icon With Gear. Elucidate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security, Automation System Icon, Gear. So download instantly and tailor it with your information.
-
 Security Automation Tools With Functions And Cost
Security Automation Tools With Functions And CostThe following slide highlights various tools that can assist company to automate security process. The various tools could be Robotic process automation security orchestration, automation and response and extended detection Introducing our premium set of slides with Security Automation Tools With Functions And Cost. Elucidate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Expected Cost, Key Functions. So download instantly and tailor it with your information.
-
 Agenda Enabling Automation In Cyber Security Operations Ppt Slides Background Images
Agenda Enabling Automation In Cyber Security Operations Ppt Slides Background ImagesIntroducing Agenda Enabling Automation In Cyber Security Operations Ppt Slides Background Images to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Environment, Business, Process, using this template. Grab it now to reap its full benefits.
-
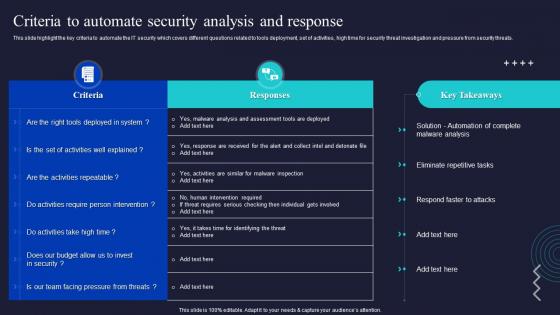 Criteria To Automate Security Analysis And Response Enabling Automation In Cyber Security Operations
Criteria To Automate Security Analysis And Response Enabling Automation In Cyber Security OperationsThis slide highlight the key criteria to automate the IT security which covers different questions related to tools deployment, set of activities, high time for security threat investigation and pressure from security threats. Present the topic in a bit more detail with this Criteria To Automate Security Analysis And Response Enabling Automation In Cyber Security Operations. Use it as a tool for discussion and navigation on Intervention, Malware Analysis, Automate. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
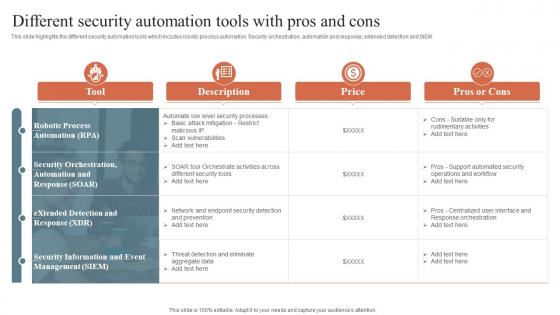
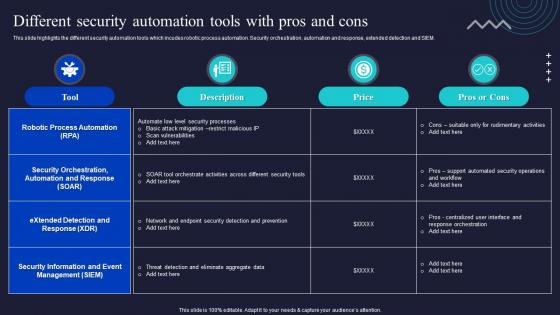 Different Security Automation Tools With Pros And Cons Enabling Automation In Cyber Security Operations
Different Security Automation Tools With Pros And Cons Enabling Automation In Cyber Security OperationsThis slide highlights the different security automation tools which incudes robotic process automation. Security orchestration, automation and response, extended detection and SIEM. Present the topic in a bit more detail with this Different Security Automation Tools With Pros And Cons Enabling Automation In Cyber Security Operations. Use it as a tool for discussion and navigation on Security Information, Management, Automation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
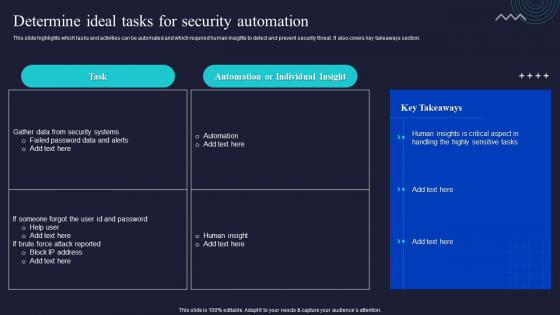 Enabling Automation In Cyber Security Operations Determine Ideal Tasks For Security Automation
Enabling Automation In Cyber Security Operations Determine Ideal Tasks For Security AutomationThis slide highlights which tasks and activities can be automated and which required human insights to detect and prevent security threat. It also covers key takeaways section. Deliver an outstanding presentation on the topic using this Enabling Automation In Cyber Security Operations Determine Ideal Tasks For Security Automation. Dispense information and present a thorough explanation of Automation, Individual, Takeaways Section using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
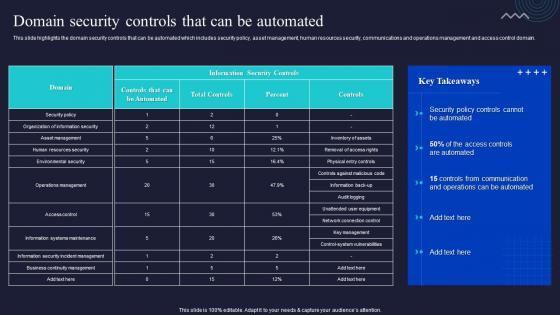 Enabling Automation In Cyber Security Operations Domain Security Controls That Can Be Automated
Enabling Automation In Cyber Security Operations Domain Security Controls That Can Be AutomatedThis slide highlights the domain security controls that can be automated which includes security policy, asset management, human resources security, communications and operations management and access control domain. Present the topic in a bit more detail with this Enabling Automation In Cyber Security Operations Domain Security Controls That Can Be Automated. Use it as a tool for discussion and navigation on Communication, Management, Human Resources. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Enabling Automation In Cyber Security Operations Table Of Contents Ppt Slides Infographic Template
Enabling Automation In Cyber Security Operations Table Of Contents Ppt Slides Infographic TemplateDeliver an outstanding presentation on the topic using this Enabling Automation In Cyber Security Operations Table Of Contents Ppt Slides Infographic Template. Dispense information and present a thorough explanation of Protection Platform, Security Automation, Processes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
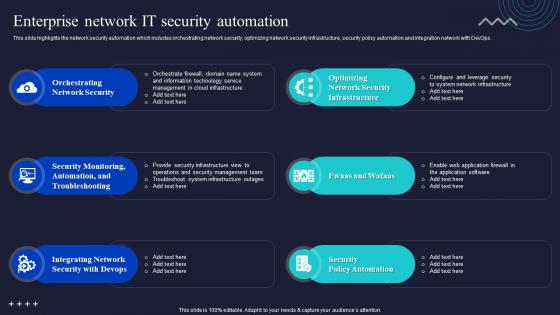 Enterprise Network It Security Automation Enabling Automation In Cyber Security Operations
Enterprise Network It Security Automation Enabling Automation In Cyber Security OperationsThis slide highlights the network security automation which includes orchestrating network security, optimizing network security infrastructure, security policy automation and integration network with DevOps. Deliver an outstanding presentation on the topic using this Enterprise Network It Security Automation Enabling Automation In Cyber Security Operations. Dispense information and present a thorough explanation of Orchestrating Network Security, Troubleshooting, Integrating Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
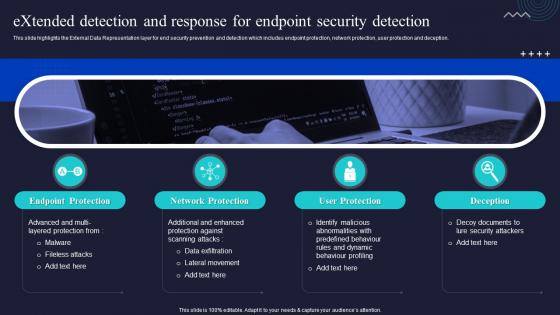 Extended Detection And Response For Endpoint Security Enabling Automation In Cyber Security Operations
Extended Detection And Response For Endpoint Security Enabling Automation In Cyber Security OperationsThis slide highlights the External Data Representation layer for end security prevention and detection which includes endpoint protection, network protection, user protection and deceptio Increase audience engagement and knowledge by dispensing information using Extended Detection And Response For Endpoint Security Enabling Automation In Cyber Security Operations. This template helps you present information on four stages. You can also present information on Endpoint Protection, Network Protection, User Protection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons Slide For Enabling Automation In Cyber Security Operations Ppt Slides Background Designs
Icons Slide For Enabling Automation In Cyber Security Operations Ppt Slides Background DesignsDeliver an outstanding presentation on the topic using this Icons Slide For Enabling Automation In Cyber Security Operations Ppt Slides Background Designs. Dispense information and present a thorough explanation of Icons using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
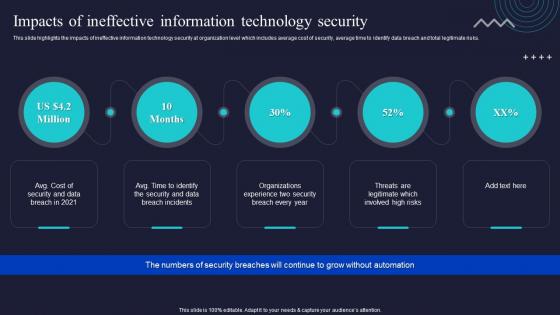 Impacts Of Ineffective Information Technology Security Enabling Automation In Cyber Security Operations
Impacts Of Ineffective Information Technology Security Enabling Automation In Cyber Security OperationsThis slide highlights the impacts of ineffective information technology security at organization level which includes average cost of security, average time to identify data breach and total legitimate risks. Increase audience engagement and knowledge by dispensing information using Impacts Of Ineffective Information Technology Security Enabling Automation In Cyber Security Operations. This template helps you present information on four stages. You can also present information on Ineffective, Information, Technology using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Managed Detection And Response Layer For Expert Monitoring Enabling Automation In Cyber Security Operations
Managed Detection And Response Layer For Expert Monitoring Enabling Automation In Cyber Security OperationsThis slide highlights the slide Managed Detection and Response security layer which include alter monitoring, attack investigation, threat hunting, and incident response. Introducing Managed Detection And Response Layer For Expert Monitoring Enabling Automation In Cyber Security Operations to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Alert Monitoring, Attack Investigation, Threat Hunting, using this template. Grab it now to reap its full benefits.
-
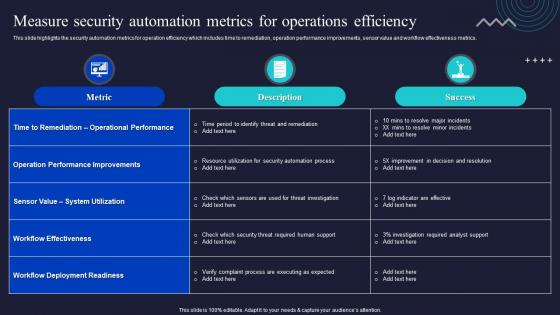 Measure Security Automation Metrics For Operations Efficiency Enabling Automation In Cyber Security Operations
Measure Security Automation Metrics For Operations Efficiency Enabling Automation In Cyber Security OperationsThis slide highlights the security automation metrics for operation efficiency which includes time to remediation, operation performance improvements, sensor value and workflow effectiveness metrics. Present the topic in a bit more detail with this Measure Security Automation Metrics For Operations Efficiency Enabling Automation In Cyber Security Operations. Use it as a tool for discussion and navigation on Automation, Operations, Efficiency. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Right Time To Add Automation In Security Enabling Automation In Cyber Security Operations
Right Time To Add Automation In Security Enabling Automation In Cyber Security OperationsThis slide depicts that what is the right time to invest in security automation it showcases failed human insights high time for resolution, high security breaches, no additional budget to hire security team. Present the topic in a bit more detail with this Right Time To Add Automation In Security Enabling Automation In Cyber Security Operations. Use it as a tool for discussion and navigation on Resolution, Automation, Human Insights. This template is free to edit as deemed fit for your organization. Therefore download it now.



