Powerpoint Templates and Google slides for Security Breach Icon
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
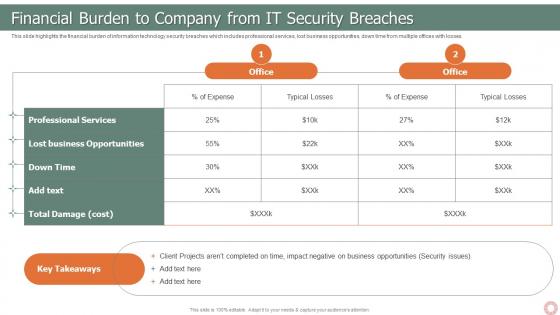 IT Risk Management Strategies Financial Burden To Company From It Security Breaches
IT Risk Management Strategies Financial Burden To Company From It Security BreachesThis slide highlights the financial burden of information technology security breaches which includes professional services, lost business opportunities, down time from multiple offices with losses. Present the topic in a bit more detail with this IT Risk Management Strategies Financial Burden To Company From It Security Breaches. Use it as a tool for discussion and navigation on Professional Services, Lost Business Opportunities, Total Damage. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
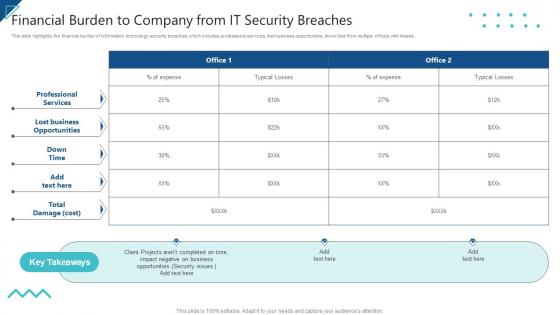 Enterprise Risk Management Financial Burden To Company From IT Security Breaches
Enterprise Risk Management Financial Burden To Company From IT Security BreachesThis slide highlights the financial burden of information technology security breaches which includes professional services, lost business opportunities, down time from multiple offices with losses. Deliver an outstanding presentation on the topic using this Enterprise Risk Management Financial Burden To Company From IT Security Breaches. Dispense information and present a thorough explanation of Professional Services, Lost Business Opportunities, Total Damage using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Impact Of Cyber Security Breach General Consequences Developing Cyber Security Awareness Training
Impact Of Cyber Security Breach General Consequences Developing Cyber Security Awareness TrainingThe purpose of this slide is to outline the impact of cyber security breach on the organization. The cyber attack make a significant impact on reputational damage, intellectual property IP theft, monetary penalty and operational disruption. Introducing Impact Of Cyber Security Breach General Consequences Developing Cyber Security Awareness Training to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Reputational Damage, Operational Disruption, Monetary Penalty, Theft Events, using this template. Grab it now to reap its full benefits.
-
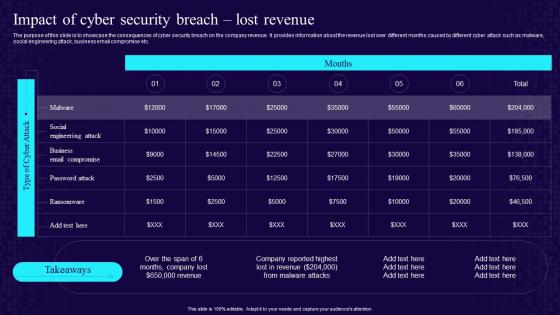 Impact Of Cyber Security Breach Lost Revenue Developing Cyber Security Awareness Training Program
Impact Of Cyber Security Breach Lost Revenue Developing Cyber Security Awareness Training ProgramThe purpose of this slide is to showcase the consequences of cyber security breach on the company revenue. It provides information about the revenue lost over different months caused by different cyber attack such as malware, social engineering attack, business email compromise etc. Deliver an outstanding presentation on the topic using this Impact Of Cyber Security Breach Lost Revenue Developing Cyber Security Awareness Training Program. Dispense information and present a thorough explanation of Cyber Security, Breach, Lost Revenue using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Icon To Reduce Data Breaches
Cyber Security Icon To Reduce Data BreachesIntroducing our premium set of slides with Cyber Security Icon To Reduce Data Breaches. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Reduce Data Breaches, Cyber Security Icon. So download instantly and tailor it with your information.
-
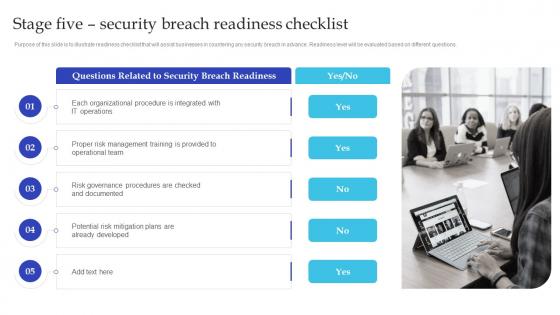 Stage Five Security Breach Readiness Checklist Artificial Intelligence Playbook For Business
Stage Five Security Breach Readiness Checklist Artificial Intelligence Playbook For BusinessPurpose of this slide is to illustrate readiness checklist that will assist businesses in countering any security breach in advance. Readiness level will be evaluated based on different questions. Introducing Stage Five Security Breach Readiness Checklist Artificial Intelligence Playbook For Business to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Organizational Procedure, IT Operations, Operational Team, using this template. Grab it now to reap its full benefits.
-
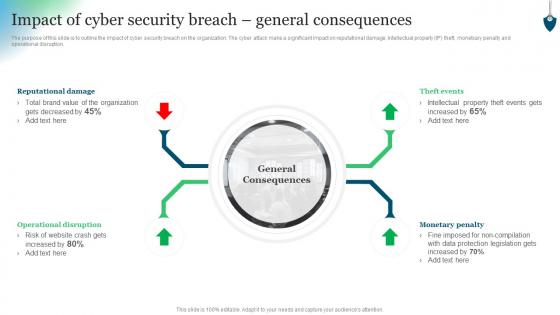 Conducting Security Awareness Impact Of Cyber Security Breach General Consequences
Conducting Security Awareness Impact Of Cyber Security Breach General ConsequencesThe purpose of this slide is to outline the impact of cyber security breach on the organization. The cyber attack make a significant impact on reputational damage, intellectual property IP theft, monetxary penalty and operational disruption. Introducing Conducting Security Awareness Impact Of Cyber Security Breach General Consequences to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Reputational Damage, Operational Disruption, Monetary Penalty, Theft Events, using this template. Grab it now to reap its full benefits.
-
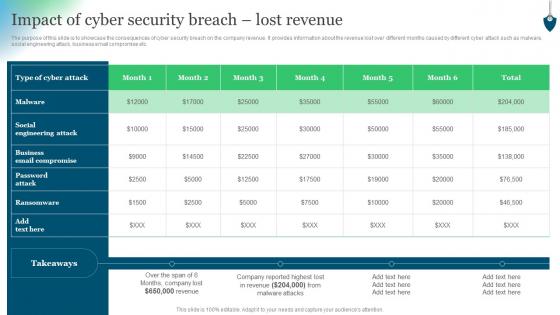 Impact Of Cyber Security Breach Lost Revenue Conducting Security Awareness
Impact Of Cyber Security Breach Lost Revenue Conducting Security AwarenessThe purpose of this slide is to showcase the consequences of cyber security breach on the company revenue. It provides information about the revenue lost over different months caused by different cyber attack such as malware, social engineering attack, business email compromise etc. Present the topic in a bit more detail with this Impact Of Cyber Security Breach Lost Revenue Conducting Security Awareness. Use it as a tool for discussion and navigation on Type Cyber Attack, Social Engineering Attack, Business Email Compromise. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
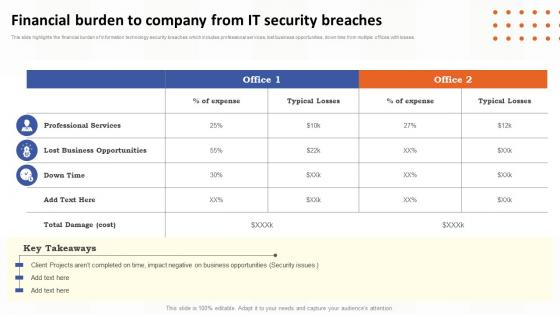 Financial Burden To Company From It Security Breaches Risk Assessment Of It Systems
Financial Burden To Company From It Security Breaches Risk Assessment Of It SystemsThis slide highlights the financial burden of information technology security breaches which includes professional services, lost business opportunities, down time from multiple offices with losses. Deliver an outstanding presentation on the topic using this Financial Burden To Company From It Security Breaches Risk Assessment Of It Systems. Dispense information and present a thorough explanation of Professional Services, Lost Business Opportunities, Financial using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Analyzing The Impact On Assets Due To Information Breach Information Security Risk Management
Analyzing The Impact On Assets Due To Information Breach Information Security Risk ManagementThis slide showcases impact of information breach on different assets which can help organization in formulating risk monitoring policy. Its key components are criterion, criterion weight and information assets. Present the topic in a bit more detail with this Analyzing The Impact On Assets Due To Information Breach Information Security Risk Management. Use it as a tool for discussion and navigation on Impact On Revenue, Analyzing, Information Breach. This template is free to edit as deemed fit for your organization. Therefore download it now
-
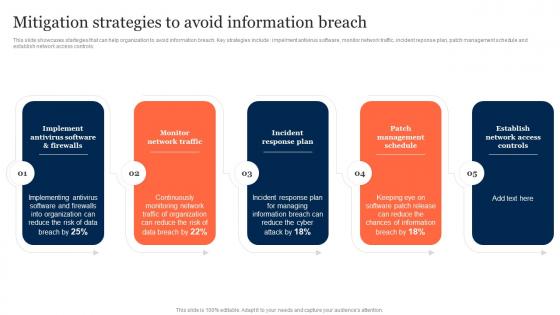 Mitigation Strategies To Avoid Information Breach Information Security Risk Management
Mitigation Strategies To Avoid Information Breach Information Security Risk ManagementThis slide showcases startegies that can help organization to avoid information breach. Key strategies include impelment antivirus software, monitor network traffic, incident reponse plan, patch management schedule and establish network access controls. Introducing Mitigation Strategies To Avoid Information Breach Information Security Risk Management to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispense information on Implement Antivirus Software, Monitor Network Traffic, Incident Response Plan, using this template. Grab it now to reap its full benefits.
-
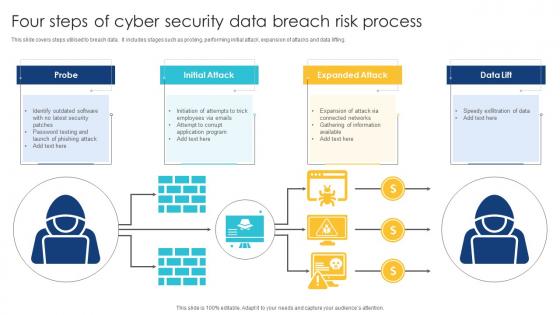 Four Steps Of Cyber Security Data Breach Risk Process
Four Steps Of Cyber Security Data Breach Risk ProcessThis slide covers steps utilised to breach data. It includes stages such as probing, performing initial attack, expansion of attacks and data lifting. Introducing our premium set of slides with name Four Steps Of Cyber Security Data Breach Risk Process. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Initial Attack, Expanded Attack, Breach Risk Process. So download instantly and tailor it with your information.
-
 Cyber Security Data Breach Post Crisis Communication Plan
Cyber Security Data Breach Post Crisis Communication PlanThis slides provide information about post crisis communication plan how to handle it in effective manner. It includes elements such as crisis team, fast, precise, and sincereresponses, clear line of communication and restorative services. Introducing our premium set of slides with Cyber Security Data Breach Post Crisis Communication Plan Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Crisis Team, Clear Line Of Communication, Restorative Services. So download instantly and tailor it with your information.
-
 Security Breaches In Powerpoint And Google Slides Cpb
Security Breaches In Powerpoint And Google Slides CpbPresenting our Security Breaches In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Security Breaches This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cyber Security Breach In Powerpoint And Google Slides Cpb
Cyber Security Breach In Powerpoint And Google Slides CpbPresenting Cyber Security Breach In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cyber Security Breach. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Communicating Large Event Security Plan Breach Icon
Communicating Large Event Security Plan Breach IconIntroducing our Communicating Large Event Security Plan Breach Icon set of slides. The topics discussed in these slides are Communicating Large, Event Security, Plan Breach. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
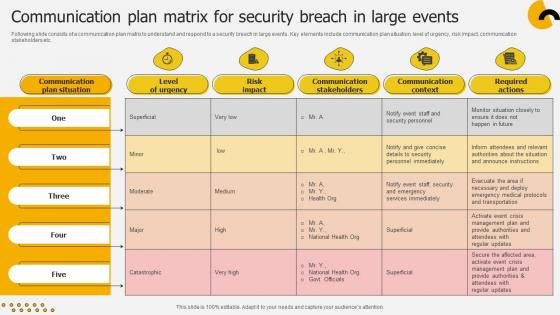 Communication Plan Matrix For Security Breach In Large Events
Communication Plan Matrix For Security Breach In Large EventsFollowing slide consists of a communication plan matrix to understand and respond to a security breach in large events. Key elements include communication plan situation, level of urgency, risk impact, communication stakeholders etc.Introducing our Communication Plan Matrix For Security Breach In Large Events set of slides. The topics discussed in these slides are Communication Plan Situation, Level Urgency, Communication Stakeholders. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Secops Icon To Prevent Security Breaches
Secops Icon To Prevent Security BreachesIntroducing our Secops Icon To Prevent Security Breaches set of slides. The topics discussed in these slides are Secops Icon, Prevent Security Breaches. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
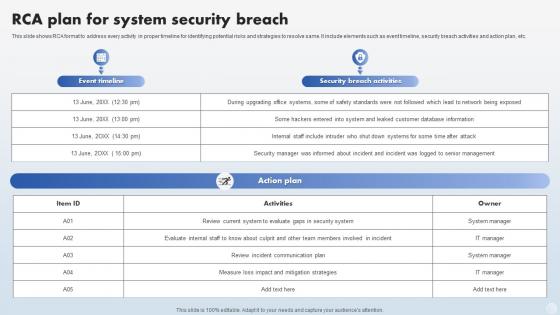 RCA Plan For System Security Breach
RCA Plan For System Security BreachThis slide shows RCA format to address every activity in proper timeline for identifying potential risks and strategies to resolve same. It include elements such as event timeline, security breach activities and action plan, etc.Presenting our well structured RCA Plan For System Security Breach. The topics discussed in this slide are Incident Communication, Evaluate Internal, Mitigation Strategies. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Bank Security Breached Icon Of Identity Fraud
Bank Security Breached Icon Of Identity FraudPresenting our well structured Bank Security Breached Icon Of Identity Fraud. The topics discussed in this slide are Bank Security, Breached Icon, Identity Fraud. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Massive Security Breach In Powerpoint And Google Slides Cpb
Massive Security Breach In Powerpoint And Google Slides CpbPresenting Massive Security Breach In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Massive Security Breach. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Data Breach Security Communication Plan Icon
Data Breach Security Communication Plan IconPresenting our well structured Data Breach Security Communication Plan Icon. The topics discussed in this slide are Data Breach Security, Communication Plan Icon. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Post Credit Breach Cyber Security In Powerpoint And Google Slides Cpb
Post Credit Breach Cyber Security In Powerpoint And Google Slides CpbPresenting Post Credit Breach Cyber Security In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Post Credit Breach Cyber Security. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Document Security Breach Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Document Security Breach Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone Powerpoint Icon on Data Breach is a simple yet powerful visual representation of the risks associated with data security. It is perfect for presentations, reports, and other documents to help illustrate the dangers of data breaches. Its minimalistic design ensures it wont take away from the overall message.
-
 Document Security Breach Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Document Security Breach Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone Powerpoint Icon on Data Breach is a simple yet powerful visual representation of the risks associated with data security. It is perfect for presentations, reports, and other documents to help illustrate the dangers of data breaches. Its minimalistic design ensures it wont take away from the overall message.
-
 Amazon map opportunities weekly report breach management social security cpb
Amazon map opportunities weekly report breach management social security cpbThis is an editable four stages graphic that deals with topics like Amazon Map, Opportunities, Weekly Report, Breach Management, Social Security to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Types security breaches ppt powerpoint presentation show slide cpb
Types security breaches ppt powerpoint presentation show slide cpbPresenting this set of slides with name Types Security Breaches Ppt Powerpoint Presentation Show Slide Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Types Security Breaches to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Solutions avoid security breach ppt powerpoint presentation portfolio designs cpb
Solutions avoid security breach ppt powerpoint presentation portfolio designs cpbPresenting this set of slides with name Solutions Avoid Security Breach Ppt Powerpoint Presentation Portfolio Designs Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Solutions Avoid Security Breachto help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Passive active security breach response ppt powerpoint presentation file slide cpb
Passive active security breach response ppt powerpoint presentation file slide cpbPresenting this set of slides with name Passive Active Security Breach Response Ppt Powerpoint Presentation File Slide Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Passive Active Security Breach Response to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Data theft from computer through security breach
Data theft from computer through security breachPresenting this set of slides with name Data Theft From Computer Through Security Breach. This is a one stage process. The stage in this process is Data Theft From Computer Through Security Breach. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Developing firewall to prevent human error for cyber security breaches
Developing firewall to prevent human error for cyber security breachesPresenting this set of slides with name Developing Firewall To Prevent Human Error For Cyber Security Breaches. The topics discussed in these slide is Developing Firewall To Prevent Human Error For Cyber Security Breaches. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Icon of hacker performing cyber attack leading to security breach
Icon of hacker performing cyber attack leading to security breachPresenting this set of slides with name Icon Of Hacker Performing Cyber Attack Leading To Security Breach. This is a three stage process. The stages in this process are Icon Of Hacker Performing Cyber Attack Leading To Security Breach. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
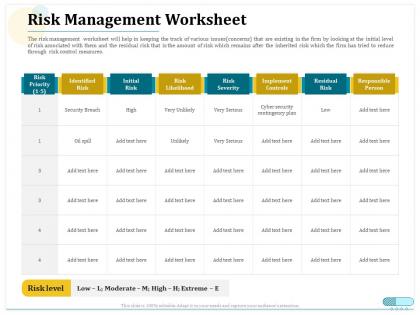 Risk management worksheet security breach ppt powerpoint outline
Risk management worksheet security breach ppt powerpoint outlineThe risk management worksheet will help in keeping the track of various issues concerns that are existing in the firm by looking at the initial level of risk associated with them and the residual risk that is the amount of risk which remains after the inherited risk which the firm has tried to reduce through risk control measures. Presenting this set of slides with name Risk Management Worksheet Security Breach Ppt Powerpoint Outline. The topics discussed in these slides are Risk Management, Worksheet Security, Breach. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Hackers breaching network security through cyber attack
Hackers breaching network security through cyber attackPresenting our set of slides with Web Portal For Providing Job Vacancies Alerts. This exhibits information on two stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Web Portal For Providing Job Vacancies Alerts.
-
 Cloud computing security breaches ppt powerpoint presentation portfolio maker cpb
Cloud computing security breaches ppt powerpoint presentation portfolio maker cpbPresenting our Cloud Computing Security Breaches Ppt Powerpoint Presentation Portfolio Maker Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Cloud Computing Security Breaches This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Security breaches cloud computing ppt powerpoint presentation icon vector cpb
Security breaches cloud computing ppt powerpoint presentation icon vector cpbPresenting Security Breaches Cloud Computing Ppt Powerpoint Presentation Icon Vector Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Security Breaches Cloud Computing. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Cyber information security laws breaching ppt powerpoint presentation model background image cpb
Cyber information security laws breaching ppt powerpoint presentation model background image cpbPresenting Cyber Information Security Laws Breaching Ppt Powerpoint Presentation Model Background Image Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both 4.3 and 16.9 aspect ratios. It is also a useful set to elucidate topics like Cyber Information Security Laws Breaching. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Icons slide for effective security monitoring plan to eliminate cyber threats and data breaches
Icons slide for effective security monitoring plan to eliminate cyber threats and data breachesIntroducing our well researched set of slides titled Icons Slide For Effective Security Monitoring Plan To Eliminate Cyber Threats And Data Breaches. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
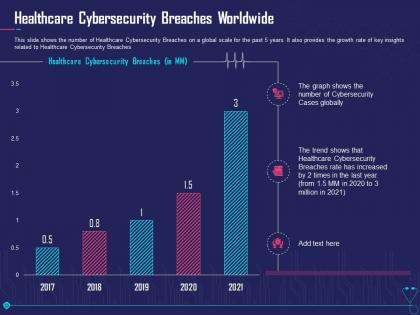 Healthcare cybersecurity breaches worldwide overcome challenge cyber security healthcare
Healthcare cybersecurity breaches worldwide overcome challenge cyber security healthcareThis slide shows the number of Healthcare Cybersecurity Breaches on a global scale for the past 5 years. It also provides the growth rate of key insights related to Healthcare Cybersecurity Breaches. Present the topic in a bit more detail with this Healthcare Cybersecurity Breaches Worldwide Overcome Challenge Cyber Security Healthcare. Use it as a tool for discussion and navigation on Healthcare Cybersecurity Breaches Worldwide. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
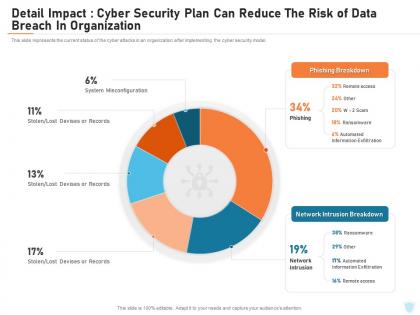 Cyber security it detail impact cyber security plan can reduce the risk of data breach in organization
Cyber security it detail impact cyber security plan can reduce the risk of data breach in organizationThis slide represents the current status of the cyber attacks in an organization after implementing the cyber security model. Deliver an outstanding presentation on the topic using this Cyber Security IT Detail Impact Cyber Security Plan Can Reduce The Risk Of Data Breach In Organization. Dispense information and present a thorough explanation of Detail Impact It Security It Plan Can Reduce The Risk Of Data Breach In Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
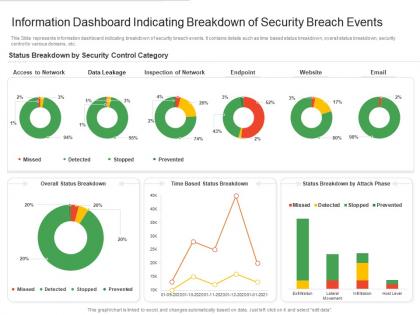 Information dashboard indicating breakdown of security breach events
Information dashboard indicating breakdown of security breach eventsPresenting our well structured Information Dashboard Indicating Breakdown Of Security Breach Events. The topics discussed in this slide are Network, Email, Data. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
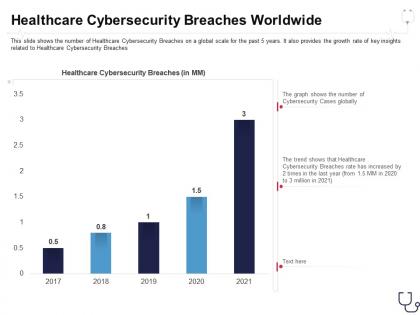 Healthcare cybersecurity breaches worldwide overcome the it security
Healthcare cybersecurity breaches worldwide overcome the it securityThis slide shows the number of Healthcare Cybersecurity Breaches on a global scale for the past 5 years. It also provides the growth rate of key insights related to Healthcare Cybersecurity Breaches Deliver an outstanding presentation on the topic using this Healthcare Cybersecurity Breaches Worldwide Overcome The It Security. Dispense information and present a thorough explanation of Healthcare Cybersecurity Breaches Worldwide using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Causes security breaches order ppt powerpoint presentation icon example topics cpb
Causes security breaches order ppt powerpoint presentation icon example topics cpbPresenting Causes Security Breaches Order Ppt Powerpoint Presentation Icon Example Topics Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Causes Security Breaches Order. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
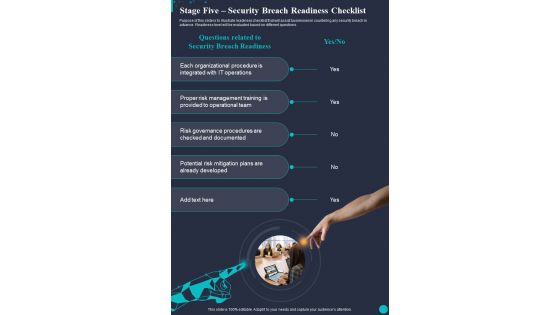 Stage Five Security Breach Readiness Checklist One Pager Sample Example Document
Stage Five Security Breach Readiness Checklist One Pager Sample Example DocumentThis is a reformattable One Pager titled Stage Five Security Breach Readiness Checklist One Pager Sample Example Document. It is crafted with high-quality visuals available for immediate download in A4 size. Everything that this template offers can be accessed in different formats and ratios, including Google Slides and PowerPoint.
-
 Cloud security threats contract breaches with clients cloud security it ppt grid
Cloud security threats contract breaches with clients cloud security it ppt gridThis slide defines the contract breaches with clients and customers that could be the biggest threat to the organizational data.Introducing Cloud Security Threats Contract Breaches With Clients Cloud Security IT Ppt Grid to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Against The Organization, Information Could, Access To Sensitive, using this template. Grab it now to reap its full benefits.
-
 Cyber security breach icon with laptop
Cyber security breach icon with laptopPresenting our set of slides with Cyber Security Breach Icon With Laptop. This exhibits information on three stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Breach Icon With Laptop.
-
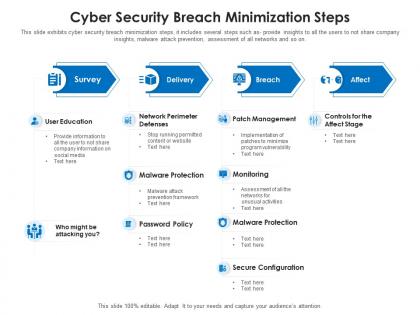 Cyber security breach minimization steps
Cyber security breach minimization stepsThis slide exhibits cyber security breach minimization steps, it includes several steps such as- provide insights to all the users to not share company insights, malware attack prevention, assessment of all networks and so on. Introducing our Cyber Security Breach Minimization Steps set of slides. The topics discussed in these slides are Survey, Delivery, Breach, Affect. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
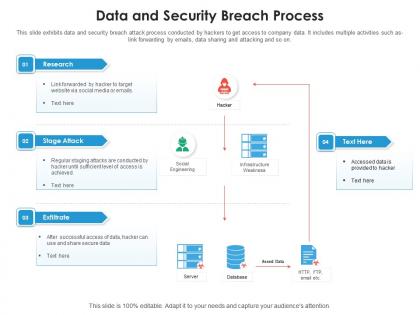 Data and security breach process
Data and security breach processThis slide exhibits data and security breach attack process conducted by hackers to get access to company data. It includes multiple activities such as- link forwarding by emails, data sharing and attacking and so on. Introducing our Data And Security Breach Process set of slides. The topics discussed in these slides are Research, Stage Attack, Exfiltrate. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
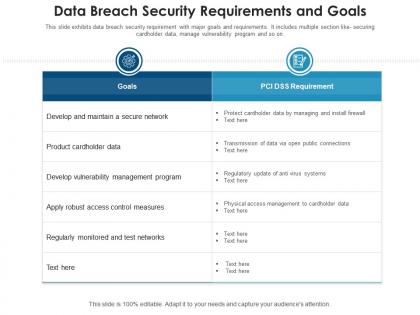 Data breach security requirements and goals
Data breach security requirements and goalsThis slide exhibits data breach security requirement with major goals and requirements. It includes multiple section like securing cardholder data, manage vulnerability program and so on. Introducing our Data Breach Security Requirements And Goals set of slides. The topics discussed in these slides are Goals, Measures, Management, Secure Network, Product. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
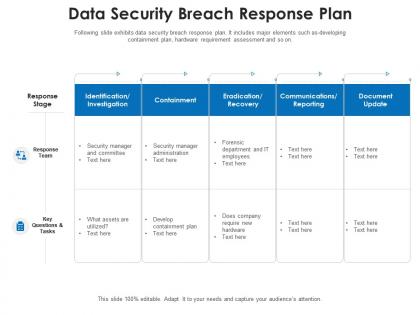 Data security breach response plan
Data security breach response planFollowing slide exhibits data security breach response plan. It includes major elements such as-developing containment plan, hardware requirement assessment and so on. Introducing our Data Security Breach Response Plan set of slides. The topics discussed in these slides are Response Stage, Response Team, Key Questions And Tasks. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Data security breach steps with customer centric approach
Data security breach steps with customer centric approachData security breach steps with customer centric approach. It includes 5 steps such as- proactive and preventive analysis, data protection as the default and so on. Presenting our set of slides with Data Security Breach Steps With Customer Centric Approach. This exhibits information on five stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Minimization, Security, Data Protection, Proactive And Preventive.
-
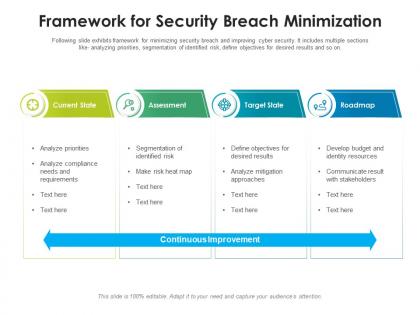 Framework for security breach minimization
Framework for security breach minimizationFollowing slide exhibits framework for minimizing security breach and improving cyber security. It includes multiple sections like analyzing priorities, segmentation of identified risk, define objectives for desired results and so on. Introducing our Framework For Security Breach Minimization set of slides. The topics discussed in these slides are Current State, Assessment, Target State, Roadmap. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
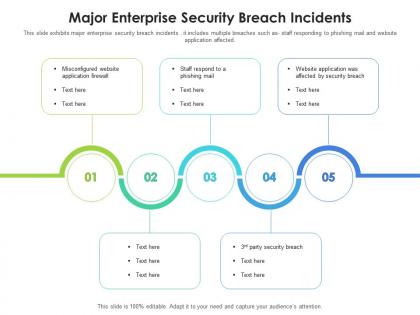 Major enterprise security breach incidents
Major enterprise security breach incidentsThis slide exhibits major enterprise security breach incidents . it includes multiple breaches such as staff responding to phishing mail and website application affected. Presenting our set of slides with Major Enterprise Security Breach Incidents. This exhibits information on five stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Major Enterprise Security Breach Incidents.
-
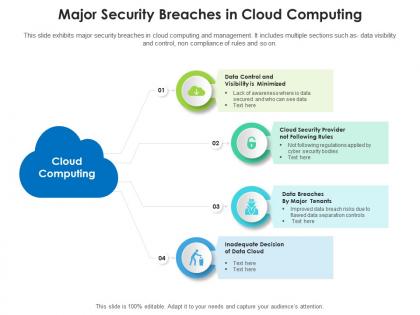 Major security breaches in cloud computing
Major security breaches in cloud computingThis slide exhibits major security breaches in cloud computing and management. It includes multiple sections such as data visibility and control, non compliance of rules and so on. Presenting our set of slides with Major Security Breaches In Cloud Computing. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Cloud, Major Tenants, Cloud Security, Data Control, Management.
-
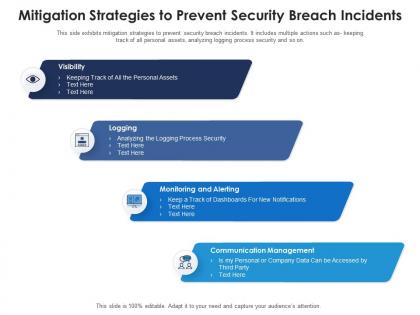 Mitigation strategies to prevent security breach incidents
Mitigation strategies to prevent security breach incidentsThis side exhibits mitigation strategies to prevent security breach incidents. It includes multiple actions such as- keeping track of all personal assets, analyzing logging process security and so on. Presenting our set of slides with Mitigation Strategies To Prevent Security Breach Incidents. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Visibility, Logging, Monitoring And Alerting, Communication Management.
-
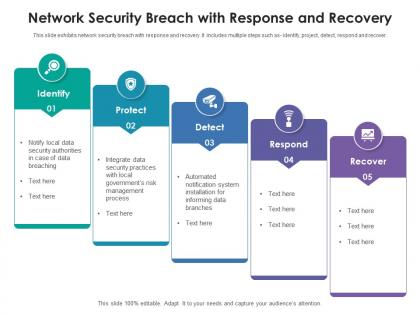 Network security breach with response and recovery
Network security breach with response and recoveryThis slide exhibits network security breach with response and recovery .It includes multiple steps such as- identify, project, detect, respond and recover. Introducing our Network Security Breach With Response And Recovery set of slides. The topics discussed in these slides are Identify, Protect, Detect, Respond, Recover. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
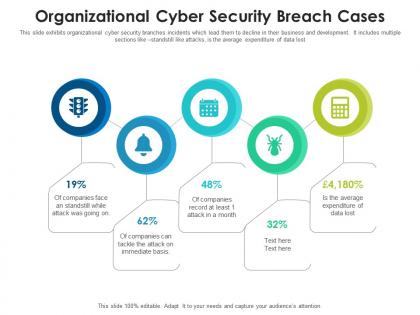 Organizational cyber security breach cases
Organizational cyber security breach casesThis slide exhibits organizational cyber security branches incidents which lead them to decline in their business and development. It includes multiple sections like standstill like attacks, is the average expenditure of data lost. Presenting our set of slides with Organizational Cyber Security Breach Cases. This exhibits information on five stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Organizational Cyber Security Breach Cases.
-
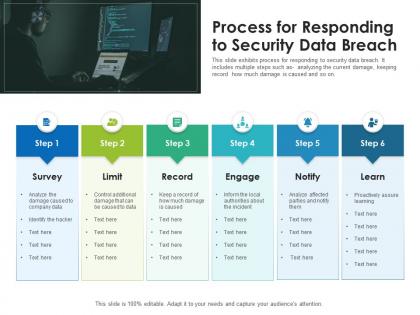 Process for responding to security data breach
Process for responding to security data breachThis slide exhibits process for responding to security data breach. It includes multiple steps such as- analyzing the current damage, keeping record how much damage is caused and so on. Introducing our Process For Responding To Security Data Breach set of slides. The topics discussed in these slides are Survey, Limit, Learn, Engage, Record. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
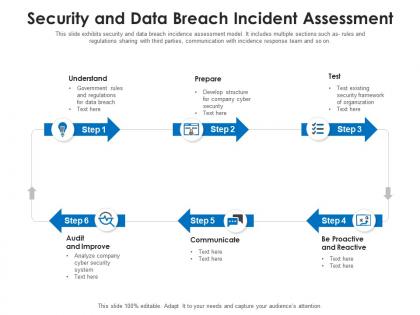 Security and data breach incident assessment
Security and data breach incident assessmentThis slide exhibits security and data breach incidence assessment model. It includes multiple sections such as- rules and regulations sharing with third parties, communication with incidence response team and so on. Presenting our set of slides with Security And Data Breach Incident Assessment. This exhibits information on six stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Survey, Limit, Learn, Engage, Record.
-
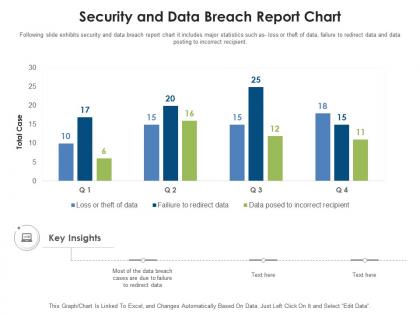 Security and data breach report chart
Security and data breach report chartFollowing slide exhibits security and data breach report chart it includes major statistics such as- loss or theft of data, failure to redirect data and data posting to incorrect recipient. Introducing our Security And Data Breach Report Chart set of slides. The topics discussed in these slides are Security And Data Breach Report Chart. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.



