Powerpoint Templates and Google slides for Security Layer With Fingerprints
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
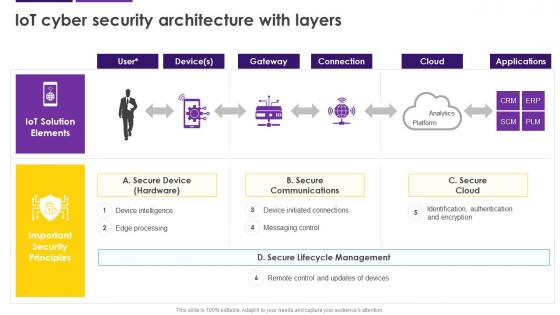 IoT Cyber Security Architecture With Layers Internet Of Things IoT Security Cybersecurity SS
IoT Cyber Security Architecture With Layers Internet Of Things IoT Security Cybersecurity SSDeliver an outstanding presentation on the topic using this IoT Cyber Security Architecture With Layers Internet Of Things IoT Security Cybersecurity SS. Dispense information and present a thorough explanation of Secure Communications, Secure Cloud, Secure Device, Messaging Control using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
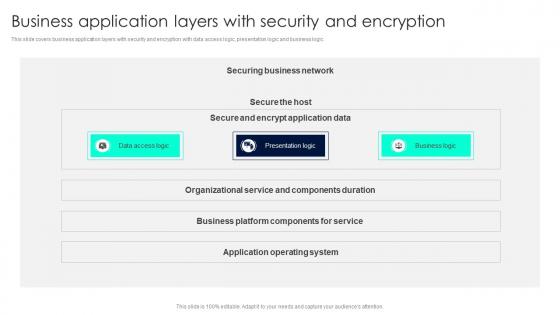 Business Application Layers With Security And Encryption
Business Application Layers With Security And EncryptionThis slide covers business application layers with security and encryption with data access logic, presentation logic and business logic. Presenting our well structured Business Application Layers With Security And Encryption. The topics discussed in this slide are Business Application, Layers Security, Encryption. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
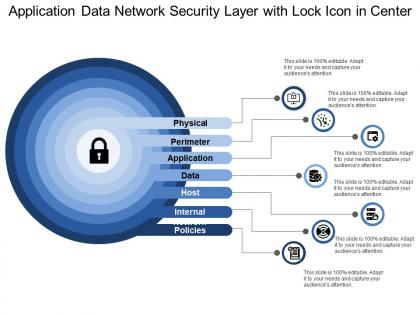 Application data network security layer with lock icon in center
Application data network security layer with lock icon in centerPresenting this set of slides with name - Application Data Network Security Layer With Lock Icon In Center. This is a stage process. The stages in this process are Security Layers, Safety Layers, Protection Layers.
-
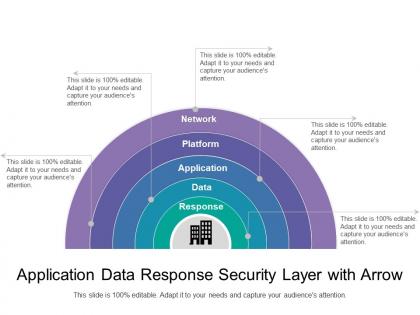 Application data response security layer with arrow
Application data response security layer with arrowPresenting this set of slides with name - Application Data Response Security Layer With Arrow. This is a five stage process. The stages in this process are Security Layers, Safety Layers, Protection Layers.
-
 Multiple security layers with key icon
Multiple security layers with key iconPresenting this set of slides with name - Multiple Security Layers With Key Icon. This is a three stage process. The stages in this process are Security Layers, Safety Layers, Protection Layers.
-
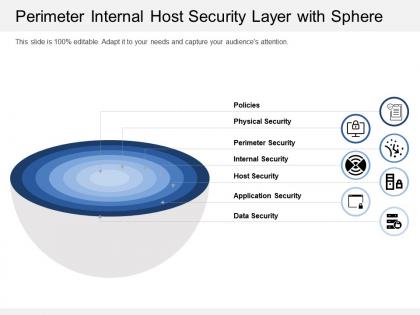 Perimeter internal host security layer with sphere
Perimeter internal host security layer with spherePresenting this set of slides with name - Perimeter Internal Host Security Layer With Sphere. This is a seven stage process. The stages in this process are Security Layers, Safety Layers, Protection Layers.
-
 Security layer icon with arrows and monitor with lock
Security layer icon with arrows and monitor with lockPresenting this set of slides with name - Security Layer Icon With Arrows And Monitor With Lock. This is a one stage process. The stages in this process are Security Layers, Safety Layers, Protection Layers.
-
 Security layer icon with boxes and lock in center
Security layer icon with boxes and lock in centerPresenting this set of slides with name - Security Layer Icon With Boxes And Lock In Center. This is a one stage process. The stages in this process are Security Layers, Safety Layers, Protection Layers.
-
 Security layer icon with three rows and lock icon
Security layer icon with three rows and lock iconPresenting this set of slides with name - Security Layer Icon With Three Rows And Lock Icon. This is a one stage process. The stages in this process are Security Layers, Safety Layers, Protection Layers.
-
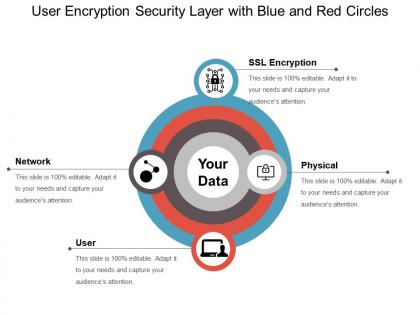 User encryption security layer with blue and red circles
User encryption security layer with blue and red circlesPresenting this set of slides with name - User Encryption Security Layer With Blue And Red Circles. This is a four stage process. The stages in this process are Security Layers, Safety Layers, Protection Layers.
-
 Verified encrypted data security layer with arrows
Verified encrypted data security layer with arrowsPresenting this set of slides with name - Verified Encrypted Data Security Layer With Arrows. This is a six stage process. The stages in this process are Security Layers, Safety Layers, Protection Layers.
-
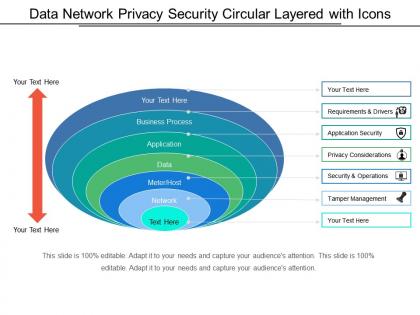 Data network privacy security circular layered with icons
Data network privacy security circular layered with iconsPresenting this set of slides with name - Data Network Privacy Security Circular Layered With Icons. This is a six stage process. The stages in this process are Circular Layered, Circle Layered, Cyclic Layered.

