Powerpoint Templates and Google slides for Security Log Management
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Logging As A Type Of Application Security Training Ppt
Logging As A Type Of Application Security Training PptPresenting Logging as a Type of Application Security. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Security Logo Dollar Symbol Gear Representing Currency
Security Logo Dollar Symbol Gear Representing CurrencyThis complete deck can be used to present to your team. It has PPT slides on various topics highlighting all the core areas of your business needs. This complete deck focuses on Security Logo Dollar Symbol Gear Representing Currency and has professionally designed templates with suitable visuals and appropriate content. This deck consists of total of twelve slides. All the slides are completely customizable for your convenience. You can change the colour, text and font size of these templates. You can add or delete the content if needed. Get access to this professionally designed complete presentation by clicking the download button below.
-
 Warehouse Icon Document Depicting Managing Logistics Security
Warehouse Icon Document Depicting Managing Logistics SecurityDeliver a credible and compelling presentation by deploying this Warehouse Icon Document Depicting Managing Logistics Security. Intensify your message with the right graphics, images, icons, etc. presented in this complete deck. This PPT template is a great starting point to convey your messages and build a good collaboration. The twelve slides added to this PowerPoint slideshow helps you present a thorough explanation of the topic. You can use it to study and present various kinds of information in the form of stats, figures, data charts, and many more. This Warehouse Icon Document Depicting Managing Logistics Security PPT slideshow is available for use in standard and widescreen aspects ratios. So, you can use it as per your convenience. Apart from this, it can be downloaded in PNG, JPG, and PDF formats, all completely editable and modifiable. The most profound feature of this PPT design is that it is fully compatible with Google Slides making it suitable for every industry and business domain.
-
 Logistics framework inventory management cyber security customer data
Logistics framework inventory management cyber security customer dataEngage buyer personas and boost brand awareness by pitching yourself using this prefabricated set. This Logistics Framework Inventory Management Cyber Security Customer Data is a great tool to connect with your audience as it contains high-quality content and graphics. This helps in conveying your thoughts in a well-structured manner. It also helps you attain a competitive advantage because of its unique design and aesthetics. In addition to this, you can use this PPT design to portray information and educate your audience on various topics. With twelve slides, this is a great design to use for your upcoming presentations. Not only is it cost-effective but also easily pliable depending on your needs and requirements. As such color, font, or any other design component can be altered. It is also available for immediate download in different formats such as PNG, JPG, etc. So, without any further ado, download it now.
-
 Strengthening Logistics Security With Patch Management Process
Strengthening Logistics Security With Patch Management ProcessFollowing slide showcases patch management process for enhancing logistics security. The purpose of this template is to help businesses foster secure operations, maintain continuity for activities and uphold customer trust. It includes elements such as long term protection, securing data integrity, etc.Presenting our set of slides with Strengthening Logistics Security With Patch Management Process. This exhibits information on seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Vendor Security Collaboration, Response Preparation, Securing Data Integrity.
-
 Login Authentication Security Illustration
Login Authentication Security IllustrationThis Login icon is a bright and colourful PowerPoint graphic, perfect for adding a modern and professional touch to your presentation. It features a blue and green colour scheme, with a white arrow pointing to the right. Use this icon to signify login, sign in, or access.
-
 Security Protocols Password Login Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Security Protocols Password Login Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon is perfect for making your presentation stand out. It features a login symbol in bright and vivid colours that will draw the attention of your audience. It is easy to use and can be resized to fit your needs. Get creative and make your presentation memorable with this powerpoint icon.
-
 Security Protocols Password Login Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Security Protocols Password Login Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMonotone Powerpoint Icon on Login is a high-quality vector icon designed to be used in presentations, websites, and other digital projects. It features a simple, minimalistic design with a monotone color palette, making it perfect for modern and professional designs.
-
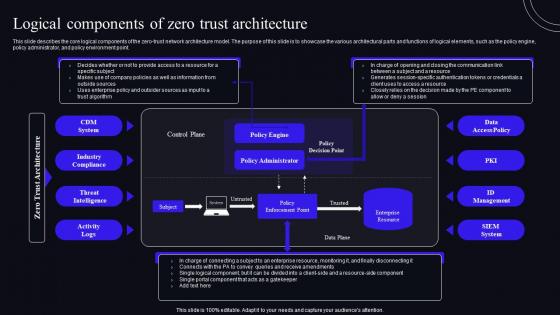 Logical Components Of Zero Trust Architecture Zero Trust Security Model
Logical Components Of Zero Trust Architecture Zero Trust Security ModelThis slide describes the core logical components of the zero-trust network architecture model. The purpose of this slide is to showcase the various architectural parts and functions of logical elements, such as the policy engine, policy administrator, and policy environment point. Deliver an outstanding presentation on the topic using this Logical Components Of Zero Trust Architecture Zero Trust Security Model. Dispense information and present a thorough explanation of Components, Architecture, Threat Intelligence using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
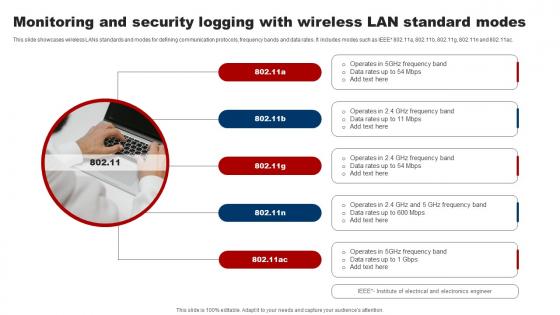 Monitoring And Security Logging With Wireless Lan Standard Modes
Monitoring And Security Logging With Wireless Lan Standard ModesThis slide showcases wireless LANs standards and modes for defining communication protocols, frequency bands and data rates. It includes modes such as IEEE 802.11a, 802.11b, 802.11g, 802.11n and 802.11ac. Introducing our premium set of slides with Monitoring And Security Logging With Wireless Lan Standard Modes. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Monitoring, Security, Standard Modes . So download instantly and tailor it with your information.
-
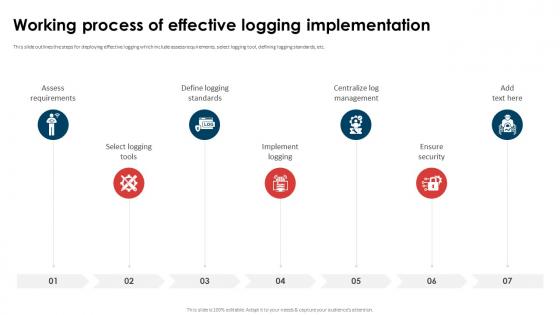 Application Security Implementation Plan Working Process Of Effective Logging Implementation
Application Security Implementation Plan Working Process Of Effective Logging ImplementationThis slide outlines the steps for deploying effective logging which include assess requirements, select logging tool, defining logging standards, etc. Introducing Application Security Implementation Plan Working Process Of Effective Logging Implementation to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Ensure Security, Centralize Log Management, Define Logging Standards, Select Logging Tools, using this template. Grab it now to reap its full benefits.
-
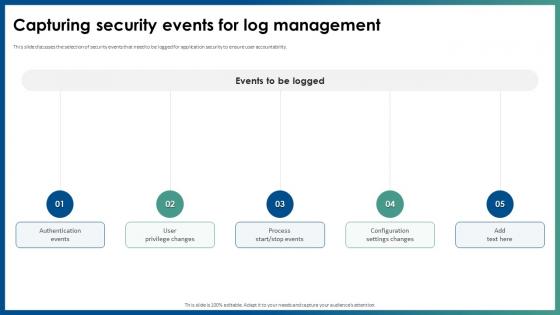 Capturing Security Events For Log Management Application Security
Capturing Security Events For Log Management Application SecurityThis slide discusses the selection of security events that need to be logged for application security to ensure user accountability. Introducing Capturing Security Events For Log Management Application Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Authentication Events, User Privilege Changes, Configuration Settings Changes, using this template. Grab it now to reap its full benefits.
-
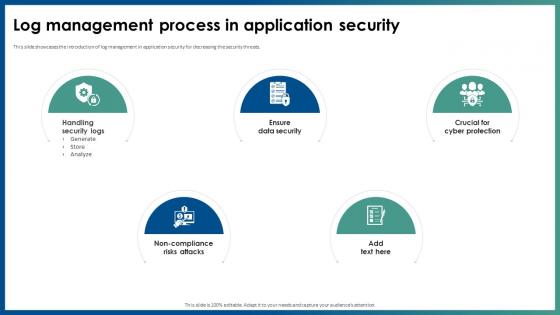 Log Management Process In Application Security
Log Management Process In Application SecurityThis slide showcases the introduction of log management in application security for decreasing the security threats. Increase audience engagement and knowledge by dispensing information using Log Management Process In Application Security. This template helps you present information on five stages. You can also present information on Handling Security Logs, Non Compliance Risks Attacks, Ensure Data Security, Log Management Process using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Security Log Management Best Practices Application Security
Security Log Management Best Practices Application SecurityThis slide highlights the best approaches of logging implementation which include preventing inappropriate actions, employ logging tools, etc. Increase audience engagement and knowledge by dispensing information using Security Log Management Best Practices Application Security. This template helps you present information on five stages. You can also present information on Scrutinize Admin And Operators, Prevent Inappropriate Actions, Ensure Authorized Activities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Web security login form image
Web security login form imagePresenting this set of slides with name Web Security Login Form Image. This is a one stage process. The stages in this process are Web Security, Computer, Networking. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
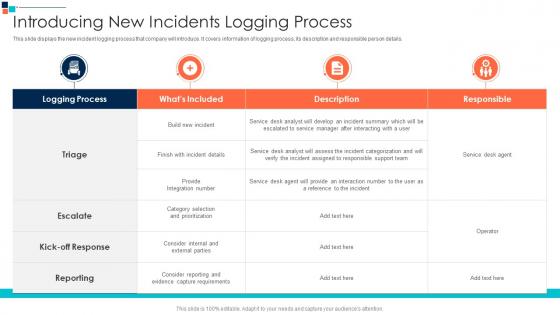 Introducing New Incidents Logging Process Introducing A Risk Based Approach To Cyber Security
Introducing New Incidents Logging Process Introducing A Risk Based Approach To Cyber SecurityThis slide displays the new incident logging process that company will introduce. It covers information of logging process, its description and responsible person details.Present the topic in a bit more detail with this Introducing New Incidents Logging Process Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on Category Selection, Assigned To Responsible, Provide An Interaction This template is free to edit as deemed fit for your organization. Therefore download it now.
-
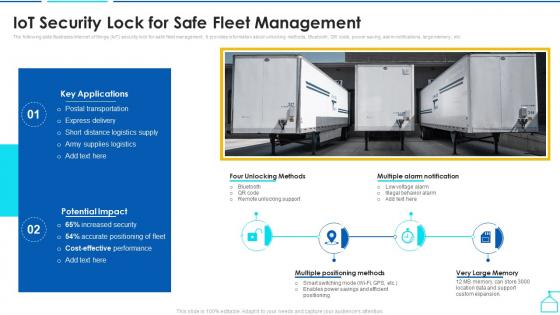 Iot Security Lock For Safe Fleet Management Enabling Smart Shipping And Logistics Through Iot
Iot Security Lock For Safe Fleet Management Enabling Smart Shipping And Logistics Through IotThe following slide illustrates internet of things IoT security lock for safe fleet management. It provides information about unlocking methods, Bluetooth, QR code, power saving, alarm notifications, large memory, etc. Present the topic in a bit more detail with this Iot Security Lock For Safe Fleet Management Enabling Smart Shipping And Logistics Through Iot. Use it as a tool for discussion and navigation on Management, Key Applications, Potential Impact. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
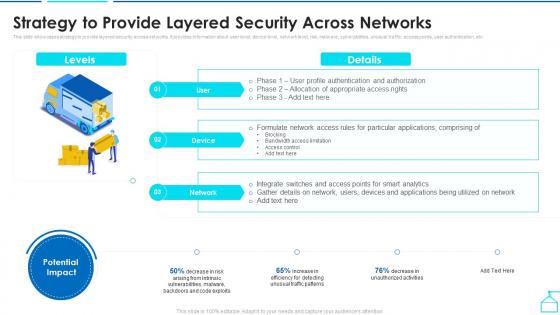 Strategy To Provide Layered Security Across Networks Enabling Smart Shipping And Logistics Through Iot
Strategy To Provide Layered Security Across Networks Enabling Smart Shipping And Logistics Through IotThis slide showcases strategy to provide layered security across networks. It provides information about user level, device level, network level, risk, malware, vulnerabilities, unusual traffic, access points, user authentication, etc. Deliver an outstanding presentation on the topic using this Strategy To Provide Layered Security Across Networks Enabling Smart Shipping And Logistics Through Iot. Dispense information and present a thorough explanation of Applications, Bandwidth Access Limitation, Strategy using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
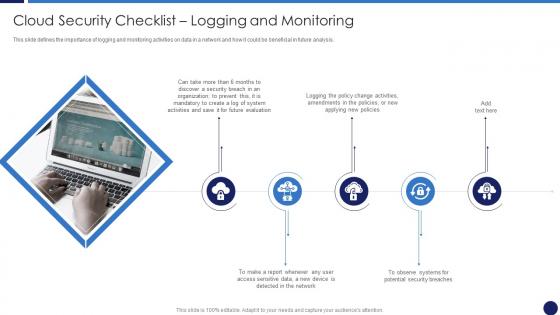 Cloud Security Checklist Logging And Monitoring Cloud Data Protection
Cloud Security Checklist Logging And Monitoring Cloud Data ProtectionThis slide defines the importance of logging and monitoring activities on data in a network and how it could be beneficial in future analysis. Increase audience engagement and knowledge by dispensing information using Cloud Security Checklist Logging And Monitoring Cloud Data Protection. This template helps you present information on five stages. You can also present information on Organization, Network, Security using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
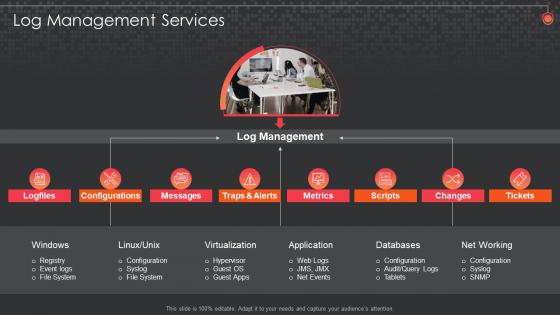 Log Management Services Siem For Security Analysis
Log Management Services Siem For Security AnalysisIntroducing Log Management Services Siem For Security Analysis to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Configurations, Databases, Management, using this template. Grab it now to reap its full benefits.
-
 Siem For Security Analysis Information And Event Management Logging Process
Siem For Security Analysis Information And Event Management Logging ProcessThis slide covers the process of SIEM which cover 4 steps of logging process such as data collection, normalization and aggregation, data discover, and alerts investigation Introducing Siem For Security Analysis Information And Event Management Logging Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Information, Management, Process, using this template. Grab it now to reap its full benefits.
-
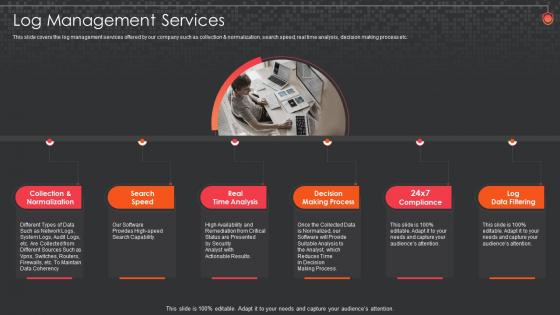 Siem For Security Analysis Log Management Services
Siem For Security Analysis Log Management ServicesThis slide covers the log management services offered by our company such as collection and normalization, search speed, real time analysis, decision making process etc. Increase audience engagement and knowledge by dispensing information using Siem For Security Analysis Log Management Services. This template helps you present information on six stages. You can also present information on Log Management Services using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
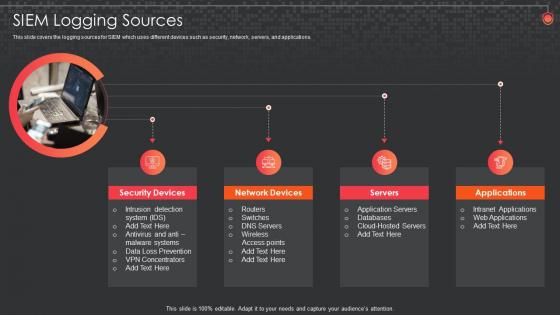 Siem For Security Analysis Logging Sources
Siem For Security Analysis Logging SourcesThis slide covers the logging sources for SIEM which uses different devices such as security, network, servers, and applications. Introducing Siem For Security Analysis Logging Sources to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Siem Logging Sources, using this template. Grab it now to reap its full benefits.
-
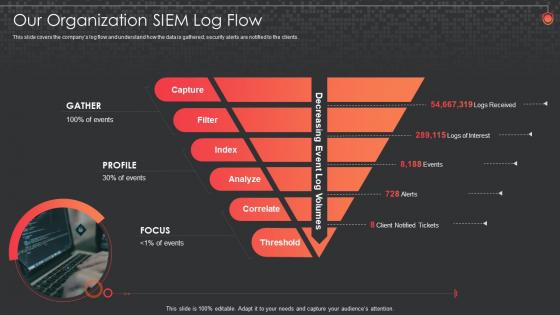 Siem For Security Analysis Organization Siem Log Flow
Siem For Security Analysis Organization Siem Log FlowThis slide covers the companys log flow and understand how the data is gathered, security alerts are notified to the clients. Increase audience engagement and knowledge by dispensing information using Siem For Security Analysis Organization Siem Log Flow. This template helps you present information on five stages. You can also present information on Our Organization Siem Log Flow using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
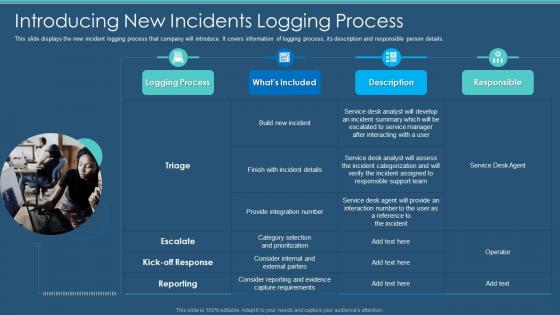 Information Security Program Cybersecurity Introducing New Incidents Logging Process
Information Security Program Cybersecurity Introducing New Incidents Logging ProcessThis slide displays the new incident logging process that company will introduce. It covers information of logging process, its description and responsible person details. Present the topic in a bit more detail with this Information Security Program Cybersecurity Introducing New Incidents Logging Process. Use it as a tool for discussion and navigation on Introducing New Incidents Logging Process. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
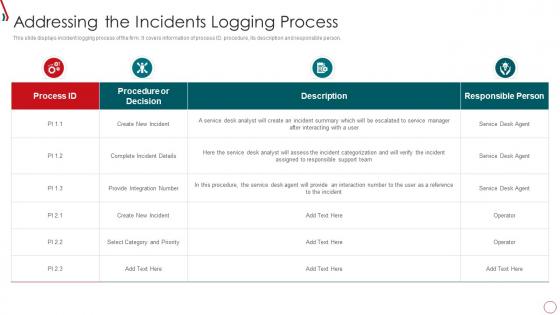 Risk Management Framework For Information Security Addressing The Incidents Logging
Risk Management Framework For Information Security Addressing The Incidents LoggingThis slide displays incident logging process of the firm. It covers information of process ID, procedure, its description and responsible person. Deliver an outstanding presentation on the topic using this Risk Management Framework For Information Security Addressing The Incidents Logging. Dispense information and present a thorough explanation of Create New Incident, Complete Incident Details, Provide Integration Number using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
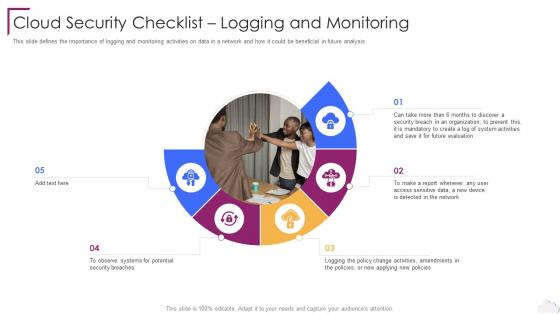 Cloud Security Checklist Logging And Monitoring Cloud Computing Security
Cloud Security Checklist Logging And Monitoring Cloud Computing SecurityThis slide defines the importance of logging and monitoring activities on data in a network and how it could be beneficial in future analysis. Increase audience engagement and knowledge by dispensing information using Cloud Security Checklist Logging And Monitoring Cloud Computing Security. This template helps you present information on five stages. You can also present information on Future Evaluation, Organization, Policy Change Activities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Security Checklist Logging And Monitoring Cloud Information Security
Cloud Security Checklist Logging And Monitoring Cloud Information SecurityThis slide defines the importance of logging and monitoring activities on data in a network and how it could be beneficial in future analysis.Increase audience engagement and knowledge by dispensing information using Cloud Security Checklist Logging And Monitoring Cloud Information Security This template helps you present information on five stages. You can also present information on Data Supposed, Malware Mechanisms, Security Precautions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Weapon And Logistics Vehicle Details Security Guard Service Company Profile
Weapon And Logistics Vehicle Details Security Guard Service Company ProfileIntroducing Weapon And Logistics Vehicle Details Security Guard Service Company Profile to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Weapon Detail, Logistics Vehicle Detail, using this template. Grab it now to reap its full benefits.
-
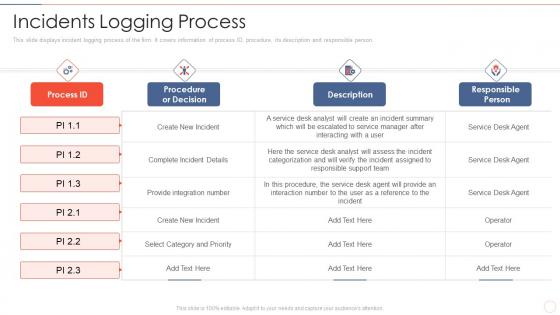 Effective information security incidents logging process
Effective information security incidents logging processThis slide displays incident logging process of the firm. It covers information of process ID, procedure, its description and responsible person. Present the topic in a bit more detail with this Effective Information Security Incidents Logging Process. Use it as a tool for discussion and navigation on Complete Incident Details, Select Category And Priority, Provide Integration Number. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
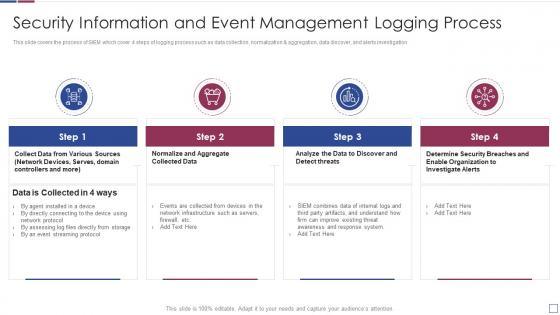 Information and event management logging process real time analysis of security alerts
Information and event management logging process real time analysis of security alertsThis slide covers the process of SIEM which cover 4 steps of logging process such as data collection, normalization and aggregation, data discover, and alerts investigation Present the topic in a bit more detail with this Information And Event Management Logging Process Real Time Analysis Of Security Alerts. Use it as a tool for discussion and navigation on Information, Management, Process. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
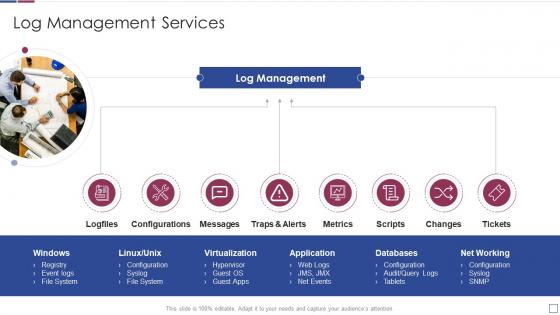 Log management services real time analysis of security alerts
Log management services real time analysis of security alertsIncrease audience engagement and knowledge by dispensing information using Log Management Services Real Time Analysis Of Security Alerts. This template helps you present information on eight stages. You can also present information on Configurations, Application, Virtualization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
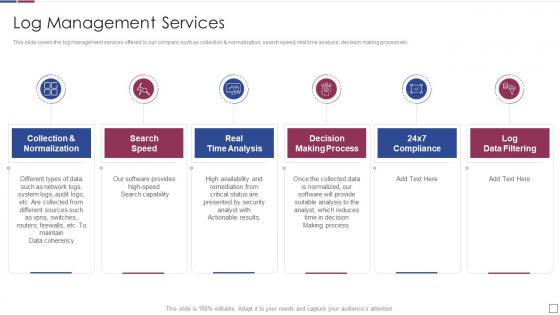 Real time analysis of security alerts log management services
Real time analysis of security alerts log management servicesThis slide covers the log management services offered by our company such as collection and normalization, search speed, real time analysis, decision making process etc. Introducing Real Time Analysis Of Security Alerts Log Management Services to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Normalization, Analysis, Process, using this template. Grab it now to reap its full benefits.
-
 Real time analysis of security alerts logging sources
Real time analysis of security alerts logging sourcesThis slide covers the logging sources for SIEM which uses different devices such as security, network, servers, and applications. Increase audience engagement and knowledge by dispensing information using Real Time Analysis Of Security Alerts Logging Sources. This template helps you present information on four stages. You can also present information on Siem Logging Sources using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
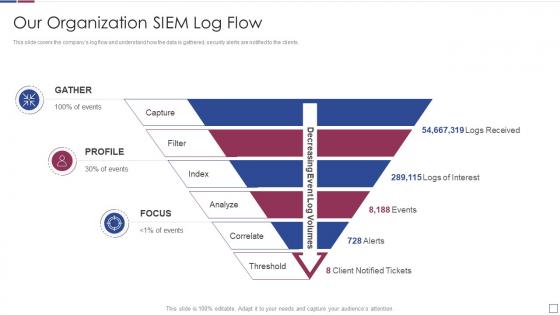 Real time analysis of security alerts organization siem log flow
Real time analysis of security alerts organization siem log flowThis slide covers the companys log flow and understand how the data is gathered, security alerts are notified to the clients. Deliver an outstanding presentation on the topic using this Real Time Analysis Of Security Alerts Organization Siem Log Flow. Dispense information and present a thorough explanation of Our Organization Siem Log Flow using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
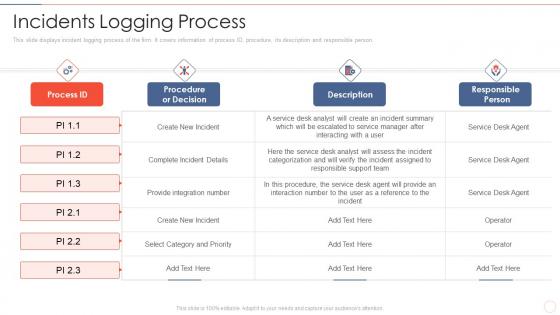 Incidents logging process effective information security risk management process
Incidents logging process effective information security risk management processThis slide displays incident logging process of the firm. It covers information of process ID, procedure, its description and responsible person.Deliver an outstanding presentation on the topic using this Incidents Logging Process Effective Information Security Risk Management Process. Dispense information and present a thorough explanation of Select Category And Priority, Procedure, The Service, Responsible Person using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
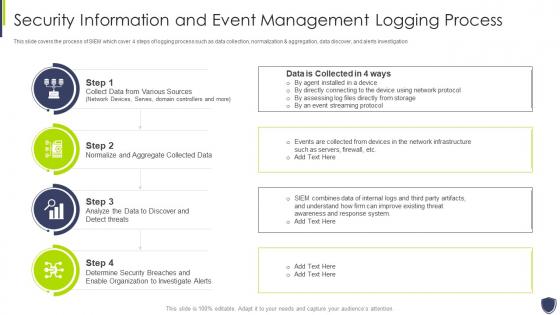 Improve it security with vulnerability information and event management logging process
Improve it security with vulnerability information and event management logging processThis slide covers the process of SIEM which cover 4 steps of logging process such as data collection, normalization and aggregation, data discover, and alerts investigation Introducing Improve It Security With Vulnerability Information And Event Management Logging Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Information, Management, Process, using this template. Grab it now to reap its full benefits.
-
 Improve it security with vulnerability management log management services
Improve it security with vulnerability management log management servicesThis slide covers the log management services offered by our company such as collection and normalization, search speed, real time analysis, decision making process etc. Introducing Improve It Security With Vulnerability Management Log Management Services to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Collection And Normalization, Search Speed, Real Time Analysis, using this template. Grab it now to reap its full benefits.
-
 Improve it security with vulnerability management logging sources
Improve it security with vulnerability management logging sourcesThis slide covers the logging sources for SIEM which uses different devices such as security, network, servers, and applications. Increase audience engagement and knowledge by dispensing information using Improve It Security With Vulnerability Management Logging Sources. This template helps you present information on four stages. You can also present information on Security Devices, Network Devices, Servers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
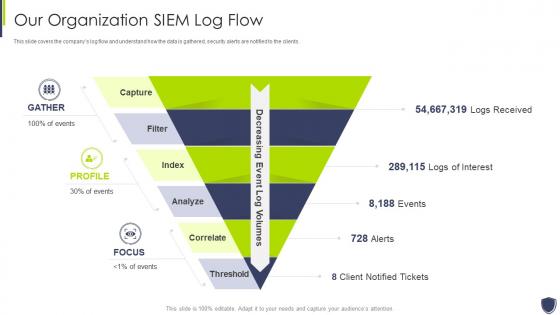 Improve it security with vulnerability management organization siem log flow
Improve it security with vulnerability management organization siem log flowThis slide covers the companys log flow and understand how the data is gathered, security alerts are notified to the clients. Introducing Improve It Security With Vulnerability Management Organization Siem Log Flow to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Our Organization Siem Log Flow, using this template. Grab it now to reap its full benefits.
-
 Log management services improve it security with vulnerability management
Log management services improve it security with vulnerability managementIncrease audience engagement and knowledge by dispensing information using Log Management Services Improve It Security With Vulnerability Management. This template helps you present information on eight stages. You can also present information on Virtualization, Application, Databases using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Log management services security information and event management
Log management services security information and event managementThis slide covers the log management services offered by our company such as collection and normalization, search speed, real time analysis, decision making process etc. Increase audience engagement and knowledge by dispensing information using Log Management Services Security Information And Event Management. This template helps you present information on six stages. You can also present information on Log Management Services Security Information And Event Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
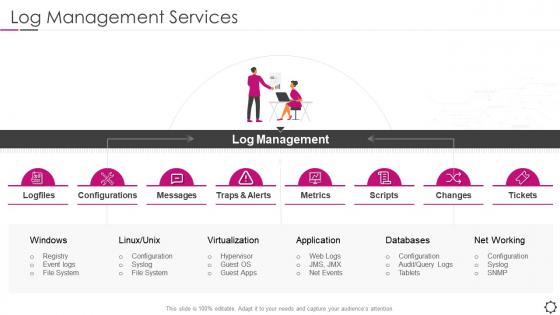 Security information and event management log management metrics
Security information and event management log management metricsIncrease audience engagement and knowledge by dispensing information using Security Information And Event Management Log Management Metrics. This template helps you present information on eight stages. You can also present information on Configurations, Virtualization, Application using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
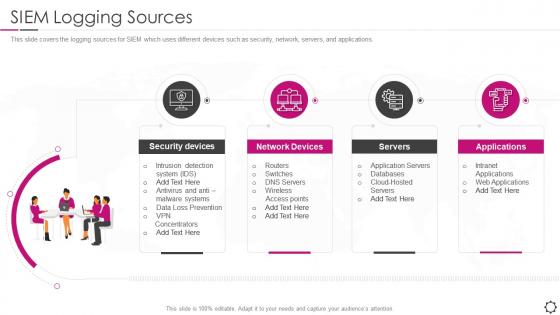 Security information and event management siem logging sources
Security information and event management siem logging sourcesThis slide covers the logging sources for SIEM which uses different devices such as security, network, servers, and applications. Increase audience engagement and knowledge by dispensing information using Security Information And Event Management SIEM Logging Sources. This template helps you present information on four stages. You can also present information on Security Devices, Network Devices, Servers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
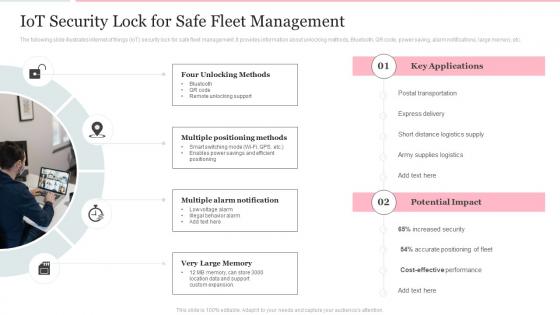 Iot Security Lock For Safe Fleet Management Deploying Internet Logistics Efficient Operations
Iot Security Lock For Safe Fleet Management Deploying Internet Logistics Efficient OperationsThe following slide illustrates internet of things IoT security lock for safe fleet management. It provides information about unlocking methods, Bluetooth, QR code, power saving, alarm notifications, large memory, etc. Introducing Iot Security Lock For Safe Fleet Management Deploying Internet Logistics Efficient Operations to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Four Unlocking Methods, Multiple Positioning Methods, Multiple Alarm Notification, using this template. Grab it now to reap its full benefits.
-
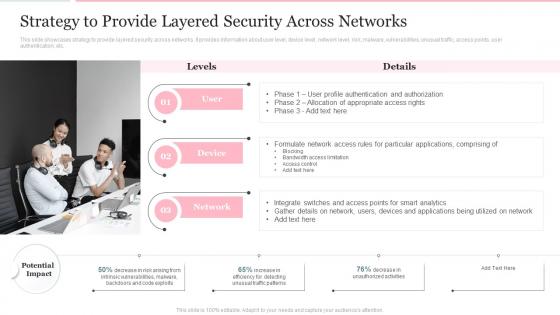 Strategy To Provide Layered Security Across Networks Deploying Internet Logistics Efficient Operations
Strategy To Provide Layered Security Across Networks Deploying Internet Logistics Efficient OperationsThis slide showcases strategy to provide layered security across networks. It provides information about user level, device level, network level, risk, malware, vulnerabilities, unusual traffic, access points, user authentication, etc. Deliver an outstanding presentation on the topic using this Strategy To Provide Layered Security Across Networks Deploying Internet Logistics Efficient Operations. Dispense information and present a thorough explanation of Strategy, Information, Authentication using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security Incident Response Playbook Addressing The Cyber Incident Logging Process
Security Incident Response Playbook Addressing The Cyber Incident Logging ProcessThis slide displays logging process for a cyber incident logging. It covers information about process ID, procedure, its description and owner details. Deliver an outstanding presentation on the topic using this Security Incident Response Playbook Addressing The Cyber Incident Logging Process. Dispense information and present a thorough explanation of Process, Information, Procedure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Weapon And Logistics Vehicle Details Security And Manpower Services Company Profile
Weapon And Logistics Vehicle Details Security And Manpower Services Company ProfileThis slide highlights the security company weapon and logistics vehicle details which includes repeater, MG16, doble cabin car, bullet proof vehicle, and patrolling vehicle. Present the topic in a bit more detail with this Weapon And Logistics Vehicle Details Security And Manpower Services Company Profile. Use it as a tool for discussion and navigation on Weapon Detail, Logistics Vehicle Detail. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
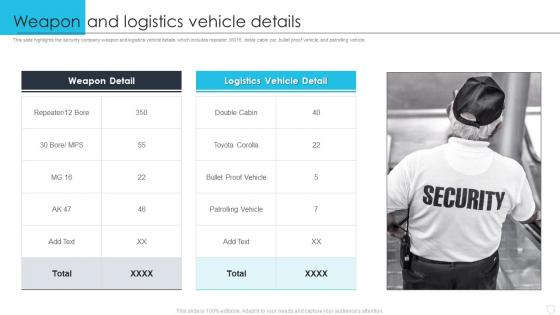 Weapon And Logistics Vehicle Details Manpower Security Services Company Profile
Weapon And Logistics Vehicle Details Manpower Security Services Company ProfileThis slide highlights the security company weapon and logistics vehicle details which includes repeater, MG16, doble cabin car, bullet proof vehicle, and patrolling vehicle. Deliver an outstanding presentation on the topic using this Weapon And Logistics Vehicle Details Manpower Security Services Company Profile. Dispense information and present a thorough explanation of Logistics, Security Company, Patrolling Vehicle using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
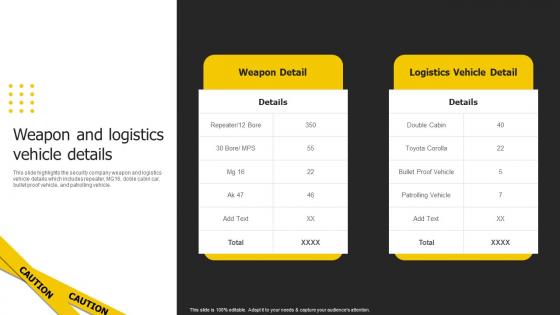 Weapon And Logistics Vehicle Details Security Services Business Profile Ppt Slides
Weapon And Logistics Vehicle Details Security Services Business Profile Ppt SlidesThis slide highlights the security company weapon and logistics vehicle details which includes repeater, MG16, doble cabin car, bullet proof vehicle, and patrolling vehicle. Deliver an outstanding presentation on the topic using this Weapon And Logistics Vehicle Details Security Services Business Profile Ppt Slides. Dispense information and present a thorough explanation of Weapon Detail, Logistics Vehicle Detail using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 IOT Security Lock For Safe Fleet Management Using IOT Technologies For Better Logistics
IOT Security Lock For Safe Fleet Management Using IOT Technologies For Better LogisticsThe following slide illustrates internet of things IoT security lock for safe fleet management. It provides information about unlocking methods, Bluetooth, QR code, power saving, alarm notifications, large memory, etc. Present the topic in a bit more detail with this IOT Security Lock For Safe Fleet Management Using IOT Technologies For Better Logistics. Use it as a tool for discussion and navigation on Multiple Positioning, Multiple Alarm, Behavior Alarm. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
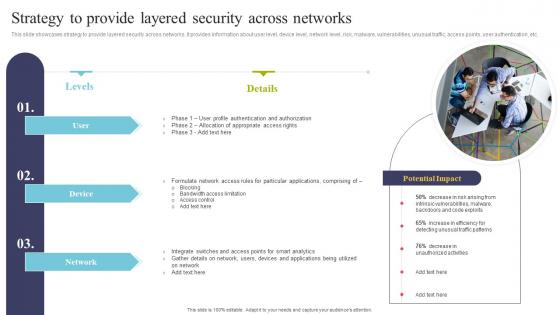 Strategy To Provide Layered Security Across Networks Using IOT Technologies For Better Logistics
Strategy To Provide Layered Security Across Networks Using IOT Technologies For Better LogisticsThis slide showcases strategy to provide layered security across networks. It provides information about user level, device level, network level, risk, malware, vulnerabilities, unusual traffic, access points, user authentication, etc. Present the topic in a bit more detail with this Strategy To Provide Layered Security Across Networks Using IOT Technologies For Better Logistics. Use it as a tool for discussion and navigation on Profile Authentication, Allocation Appropriate, Particular Applications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Mobile location call center logs weather data advance security
Mobile location call center logs weather data advance securityPresenting this set of slides with name - Mobile Location Call Center Logs Weather Data Advance Security. This is an editable six stages graphic that deals with topics like Mobile Location, Call Center Logs, Weather Data, Advance Security to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Global security cross reference manual sources logical view
Global security cross reference manual sources logical viewPresenting this set of slides with name - Global Security Cross Reference Manual Sources Logical View. This is an editable three stages graphic that deals with topics like -to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Secured login database security protection ppt icons graphics
Secured login database security protection ppt icons graphicsPresenting secured login database security protection ppt icons graphics. This Power Point icon template diagram has been crafted with graphic of login, database and security icons. This icon PPT diagram contains the concept of security and protection. Use this icon PPT diagram for business and data related presentations.
-
 Login screen and credit card security powerpoint templates ppt themes and graphics 0113
Login screen and credit card security powerpoint templates ppt themes and graphics 0113We are proud to present our login screen and credit card security powerpoint templates ppt themes and graphics 0113. Our information technology powerpoint templates come in all colours shades and hues. They help highlight every nuance of your views. Our communication powerpoint templates will fulfill your every need. Use them and effectively satisfy the desires of your audience.
-
 Touch screen login security powerpoint templates and powerpoint backgrounds 0211
Touch screen login security powerpoint templates and powerpoint backgrounds 0211Microsoft PowerPoint Template and Background with brass key protruding out of a silver touch screen tablet computer
-
 Security log management process ppt powerpoint presentation professional graphics cpb
Security log management process ppt powerpoint presentation professional graphics cpbPresenting this set of slides with name Security Log Management Process Ppt Powerpoint Presentation Professional Graphics Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Security Log Management Process to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Security introduction log analytics ppt powerpoint presentation file introduction cpb
Security introduction log analytics ppt powerpoint presentation file introduction cpbPresenting this set of slides with name Security Introduction Log Analytics Ppt Powerpoint Presentation File Introduction Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Security Introduction Log Analytics to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Networked application login security ppt powerpoint presentation show template cpb
Networked application login security ppt powerpoint presentation show template cpbPresenting this set of slides with name Networked Application Login Security Ppt Powerpoint Presentation Show Template Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Networked Application Login Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.


