Powerpoint Templates and Google slides for Security Using
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Network Security Using Secure Web Gateway Powerpoint Presentation Slides
Network Security Using Secure Web Gateway Powerpoint Presentation SlidesDeliver this complete deck to your team members and other collaborators. Encompassed with stylized slides presenting various concepts, this Network Security Using Secure Web Gateway Powerpoint Presentation Slides is the best tool you can utilize. Personalize its content and graphics to make it unique and thought-provoking. All the eighty five slides are editable and modifiable, so feel free to adjust them to your business setting. The font, color, and other components also come in an editable format making this PPT design the best choice for your next presentation. So, download now.
-
 Raising Cyber Security Awareness In Organizations Using Various Tools And Tactics PPT Template Bundles DK MD
Raising Cyber Security Awareness In Organizations Using Various Tools And Tactics PPT Template Bundles DK MDDeliver a credible and compelling presentation by deploying this Raising Cyber Security Awareness In Organizations Using Various Tools And Tactics PPT Template Bundles DK MD. Intensify your message with the right graphics, images, icons, etc. presented in this complete deck. This PPT template is a great starting point to convey your messages and build a good collaboration. The fifteen slides added to this PowerPoint slideshow helps you present a thorough explanation of the topic. You can use it to study and present various kinds of information in the form of stats, figures, data charts, and many more. This Raising Cyber Security Awareness In Organizations Using Various Tools And Tactics PPT Template Bundles DK MD PPT slideshow is available for use in standard and widescreen aspects ratios. So, you can use it as per your convenience. Apart from this, it can be downloaded in PNG, JPG, and PDF formats, all completely editable and modifiable. The most profound feature of this PPT design is that it is fully compatible with Google Slides making it suitable for every industry and business domain.
-
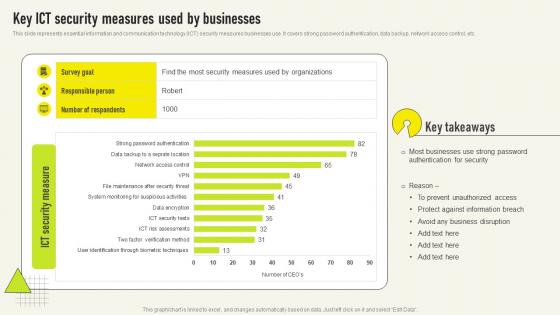 Key Ict Security Measures Used By Comprehensive Guide For Deployment Strategy SS V
Key Ict Security Measures Used By Comprehensive Guide For Deployment Strategy SS VThis slide represents essential information and communication technology ICT security measures businesses use It covers strong password authentication, data backup, network access control, etc Presenting our well structured Key Ict Security Measures Used By Comprehensive Guide For Deployment Strategy SS V The topics discussed in this slide are Authentication Security, Most Businesses, Protect Against This is an instantly available PowerPoint presentation that can be edited conveniently Download it right away and captivate your audience
-
 Different Types Of Secure Web Gateway Deployment Network Security Using Secure Web Gateway
Different Types Of Secure Web Gateway Deployment Network Security Using Secure Web GatewayThis slide demonstrates the various kinds of SWG deployments. The purpose of this slide is to explain the different types of Secure Web Gateway deployment methods such as on-premises deployment, cloud-based deployment and hybrid deployment. Increase audience engagement and knowledge by dispensing information using Different Types Of Secure Web Gateway Deployment Network Security Using Secure Web Gateway. This template helps you present information on three stages. You can also present information on Deployment, Businesses, Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
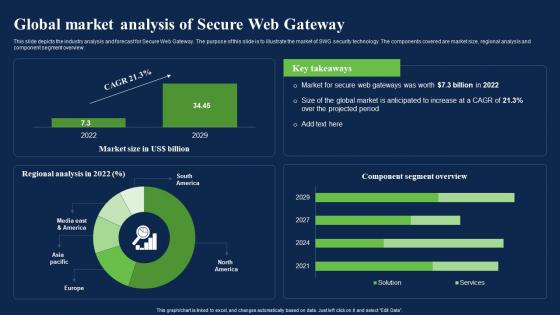 Global Market Analysis Of Secure Web Gateway Network Security Using Secure Web Gateway
Global Market Analysis Of Secure Web Gateway Network Security Using Secure Web GatewayThis slide depicts the industry analysis and forecast for Secure Web Gateway. The purpose of this slide is to illustrate the market of SWG security technology. The components covered are market size, regional analysis and component segment overview. Present the topic in a bit more detail with this Global Market Analysis Of Secure Web Gateway Network Security Using Secure Web Gateway. Use it as a tool for discussion and navigation on Analysis, Overview, Security Technology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Industry Wise Market Segmentation Of Swg Network Security Using Secure Web Gateway
Industry Wise Market Segmentation Of Swg Network Security Using Secure Web GatewayThis slide demonstrates the contribution of different industries in growth of Secure Web Gateway market. The purpose of this slide is to represent the industry wise market share of different sectors such as BFSI, IT and telecom, retail and e-Commerce, etc. Present the topic in a bit more detail with this Industry Wise Market Segmentation Of Swg Network Security Using Secure Web Gateway. Use it as a tool for discussion and navigation on Segmentation, Application, Considerably. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Secure Web Gateway Performance Tracking Dashboard Network Security Using Secure Web Gateway
Secure Web Gateway Performance Tracking Dashboard Network Security Using Secure Web GatewayThis slide represents a dashboard to maintain the record of various functions of Secure Web Gateway. The main components are top blocked web malware, web usage trend, top web application categories, risky web isolations, etc. Deliver an outstanding presentation on the topic using this Secure Web Gateway Performance Tracking Dashboard Network Security Using Secure Web Gateway. Dispense information and present a thorough explanation of Performance, Dashboard, Applications using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Table Of Contents Network Security Using Secure Web Gateway
Table Of Contents Network Security Using Secure Web GatewayDeliver an outstanding presentation on the topic using this Table Of Contents Network Security Using Secure Web Gateway. Dispense information and present a thorough explanation of Working And Architecture, Architecture, Gateway Technology using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
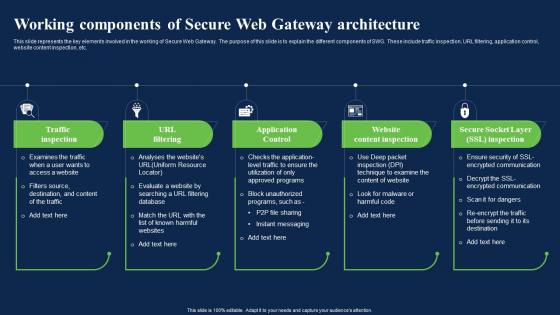 Working Components Of Secure Web Gateway Architecture Network Security Using Secure Web Gateway
Working Components Of Secure Web Gateway Architecture Network Security Using Secure Web GatewayThis slide represents the key elements involved in the working of Secure Web Gateway. The purpose of this slide is to explain the different components of SWG. These include traffic inspection, URL filtering, application control, website content inspection, etc. Increase audience engagement and knowledge by dispensing information using Working Components Of Secure Web Gateway Architecture Network Security Using Secure Web Gateway. This template helps you present information on five stages. You can also present information on Application Control, Website Content Inspection, Gateway Architecture using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
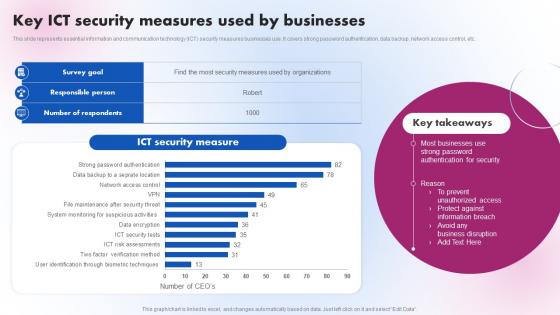 Key ICT Security Measures Used By Businesses Delivering ICT Services For Enhanced Business Strategy SS V
Key ICT Security Measures Used By Businesses Delivering ICT Services For Enhanced Business Strategy SS VThis slide represents essential information and communication technology ICT security measures businesses use. It covers strong password authentication, data backup, network access control, etc. Present the topic in a bit more detail with this Key ICT Security Measures Used By Businesses Delivering ICT Services For Enhanced Business Strategy SS V. Use it as a tool for discussion and navigation on Security Measure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
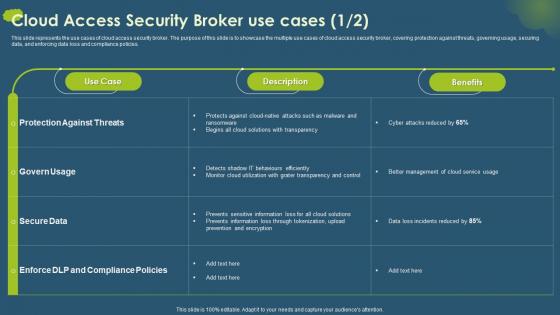 Cloud Access Security Broker CASB V2 Use Cases Ppt Ideas Graphics Download
Cloud Access Security Broker CASB V2 Use Cases Ppt Ideas Graphics DownloadThis slide represents the use cases of cloud access security broker. The purpose of this slide is to showcase the multiple use cases of cloud access security broker, covering protection against threats, governing usage, securing data, and enforcing data loss and compliance policies. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 Use Cases Ppt Ideas Graphics Download. Dispense information and present a thorough explanation of Protection Against Threats, Secure Data, Upload Prevention And Encryption, Cloud Solutions With Transparency using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
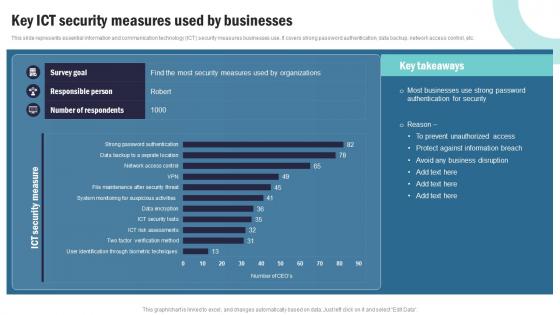 Strategic Plan To Implement Key Ict Security Measures Used By Businesses Strategy SS V
Strategic Plan To Implement Key Ict Security Measures Used By Businesses Strategy SS VThis slide represents essential information and communication technology ICT security measures businesses use. It covers strong password authentication, data backup, network access control, etc. Present the topic in a bit more detail with this Strategic Plan To Implement Key Ict Security Measures Used By Businesses Strategy SS V Use it as a tool for discussion and navigation on Data Sets And Compliance, IT Service Planning This template is free to edit as deemed fit for your organization. Therefore download it now.
-
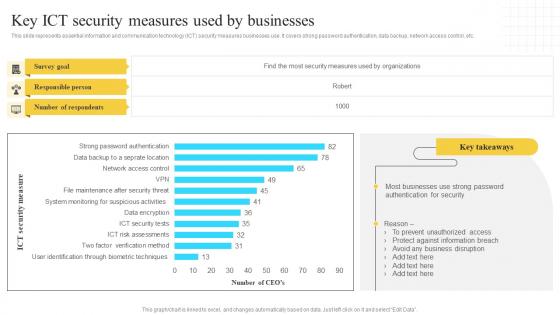 Implementation Of Information Key Ict Security Measures Used By Businesses Strategy SS V
Implementation Of Information Key Ict Security Measures Used By Businesses Strategy SS VThis slide represents essential information and communication technology ICT security measures businesses use. It covers strong password authentication, data backup, network access control, etc. Deliver an outstanding presentation on the topic using this Implementation Of Information Key Ict Security Measures Used By Businesses Strategy SS V. Dispense information and present a thorough explanation of Survey Goal, Responsible Person using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
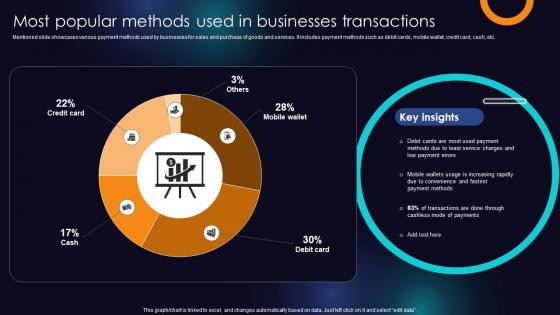 Most Popular Methods Used In Businesses Transactions Enhancing Transaction Security With E Payment
Most Popular Methods Used In Businesses Transactions Enhancing Transaction Security With E PaymentMentioned slide showcases various payment methods used by businesses for sales and purchase of goods and services. It includes payment methods such as debit cards, mobile wallet, credit card, cash, etc. Present the topic in a bit more detail with this Most Popular Methods Used In Businesses Transactions Enhancing Transaction Security With E Payment Use it as a tool for discussion and navigation on Service, Payment, Debit Cards This template is free to edit as deemed fit for your organization. Therefore download it now.
-
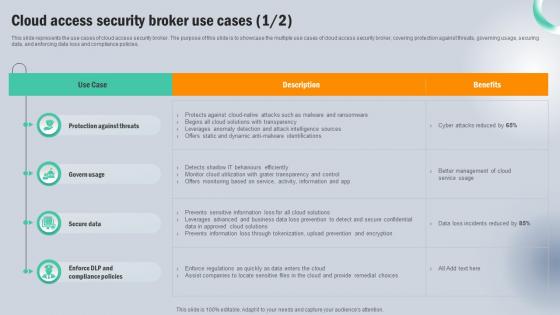 Cloud Access Security Broker Use Cases Next Generation CASB
Cloud Access Security Broker Use Cases Next Generation CASBThis slide represents the use cases of cloud access security broker. The purpose of this slide is to showcase the multiple use cases of cloud access security broker, covering protection against threats, governing usage, securing data, and enforcing data loss and compliance policies. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker Use Cases Next Generation CASB Dispense information and present a thorough explanation of Protection Against Threats, Govern Usage, Secure Data using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
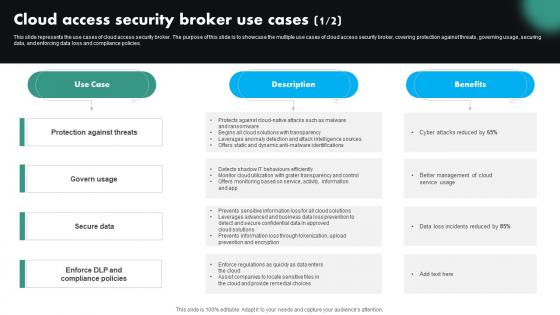 Cloud Access Security Broker Use Cases CASB Cloud Security
Cloud Access Security Broker Use Cases CASB Cloud SecurityThis slide represents the use cases of cloud access security broker. The purpose of this slide is to showcase the multiple use cases of cloud access security broker, covering protection against threats, governing usage, securing data, and enforcing data loss and compliance policies. Present the topic in a bit more detail with this Cloud Access Security Broker Use Cases CASB Cloud Security. Use it as a tool for discussion and navigation on Protection Against Threats, Compliance Policies, Cloud Access Security Broker. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
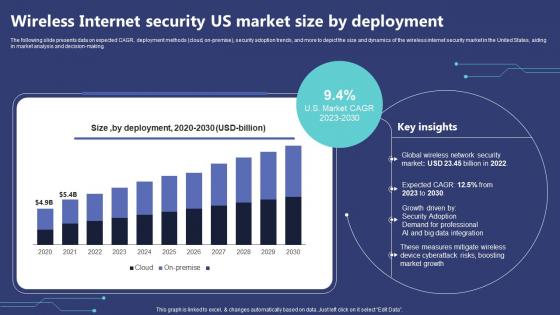 Wireless Internet Security Us Market Size By Deployment
Wireless Internet Security Us Market Size By DeploymentThe following slide presents data on expected CAGR, deployment methods cloud, on-premise, security adoption trends, and more to depict the size and dynamics of the wireless internet security market in the United States, aiding in market analysis and decision-making. Presenting our well structured Wireless Internet Security Us Market Size By Deployment. The topics discussed in this slide are Deployment, Professional, Growth. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
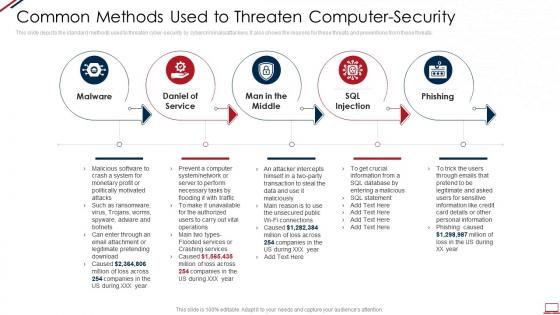 Computer system security common methods used to threaten computer security
Computer system security common methods used to threaten computer securityThis slide depicts the standard methods used to threaten cyber security by cybercriminals or attackers. It also shows the reasons for these threats and preventions from these threats. Increase audience engagement and knowledge by dispensing information using Computer System Security Common Methods Used To Threaten Computer Security. This template helps you present information on five stages. You can also present information on Malware, Daniel Of Service, Man In The Middle, SQL Injection, Phishing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Computer system security how is automation used in computer security
Computer system security how is automation used in computer securityThis slide depicts the cyber protection of an organization through artificial intelligence and how it can be helpful in threat detection, threat response, and human augmentation. Introducing Computer System Security How Is Automation Used In Computer Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Threat Detection, Threat Response, Human Augmentation, using this template. Grab it now to reap its full benefits.
-
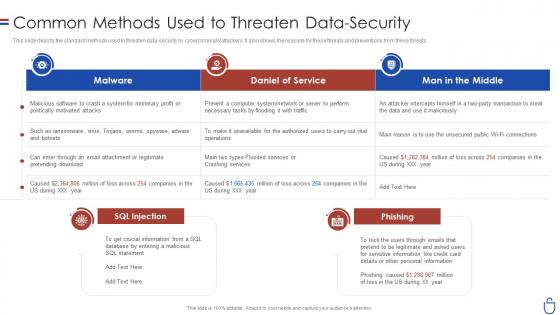 Data security it common methods used to threaten data security
Data security it common methods used to threaten data securityThis slide depicts the standard methods used to threaten data-security by cybercriminals or attackers. It also shows the reasons for these threats and preventions from these threats. Present the topic in a bit more detail with this Data Security IT Common Methods Used To Threaten Data Security. Use it as a tool for discussion and navigation on Malware, Daniel Service, Man Middle, SQL Injection. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data security it how is automation used in data security
Data security it how is automation used in data securityThis slide depicts the cyber protection of an organization through artificial intelligence and how it can be helpful in threat detection, threat response, and human augmentation. Present the topic in a bit more detail with this Data Security IT How Is Automation Used In Data Security. Use it as a tool for discussion and navigation on Threat Detection, Threat Response, Human Augmentation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Contact us in the security guard services proposal ppt slides model
Contact us in the security guard services proposal ppt slides modelPresent the topic in a bit more detail with this Contact Us In The Security Guard Services Proposal Ppt Slides Model. Use it as a tool for discussion and navigation on Contact Us, Security Guard Services. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Our equipments used for security guard services proposal ppt slides background designs
Our equipments used for security guard services proposal ppt slides background designsIntroducing Our Equipments Used For Security Guard Services Proposal Ppt Slides Background Designs to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Surveillance, Technology And Software, Security Trailers, Mobile Phones, using this template. Grab it now to reap its full benefits.
-
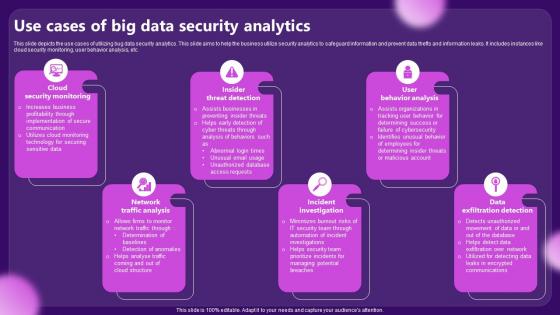 Use Cases Of Big Data Security Analytics
Use Cases Of Big Data Security AnalyticsThis slide depicts the use cases of utilizing bug data security analytics. This slide aims to help the business utilize security analytics to safeguard information and prevent data thefts and information leaks. It includes instances like cloud security monitoring, user behavior analysis, etc. Presenting our set of slides with Use Cases Of Big Data Security Analytics. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cloud Security Monitoring, Insider Threat Detection.
-
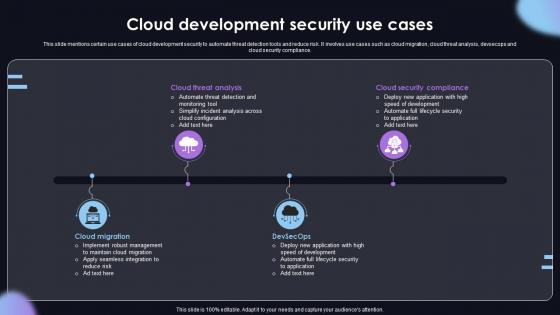 Cloud Development Security Use Cases
Cloud Development Security Use CasesThis slide mentions certain use cases of cloud development security to automate threat detection tools and reduce risk. It involves use cases such as cloud migration, cloud threat analysis, devsecops and cloud security compliance. Introducing our premium set of slides with Cloud Development Security Use Cases. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cloud Threat Analysis, Cloud Migration. So download instantly and tailor it with your information.
-
 Devops Use Cases Icon For Security Services
Devops Use Cases Icon For Security ServicesPresenting our set of slides with Devops Use Cases Icon For Security Services. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Devops Use Cases Icon, Security Services.
-
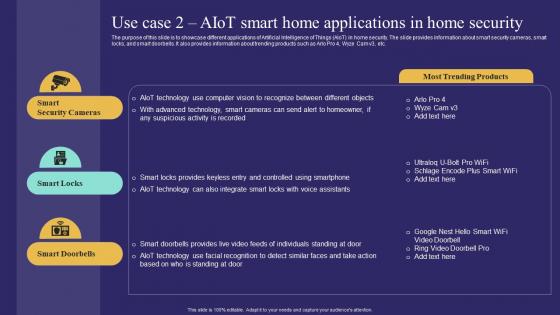 Use Case 2 Aiot Smart Home Applications In Home Security Unlocking Potential Of Aiot IoT SS
Use Case 2 Aiot Smart Home Applications In Home Security Unlocking Potential Of Aiot IoT SSThe purpose of this slide is to showcase different applications of Artificial Intelligence of Things AIoT in home security. The slide provides information about smart security cameras, smart locks, and smart doorbells. It also provides information about trending products such as Arlo Pro 4, Wyze Cam v3, etc. Increase audience engagement and knowledge by dispensing information using Use Case 2 Aiot Smart Home Applications In Home Security Unlocking Potential Of Aiot IoT SS. This template helps you present information on three stages. You can also present information on Smart Security Cameras, Smart Locks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Security Enhancement Using Hashing Cloud Cryptography
Cloud Security Enhancement Using Hashing Cloud CryptographyThis slide talks about the various applications of hash algorithm in cloud cryptography. The purpose of this slide is to explain how hash technique can help in providing security in cloud computing. These are password storage, data integrity, digital signatures, etc. Increase audience engagement and knowledge by dispensing information using Cloud Security Enhancement Using Hashing Cloud Cryptography. This template helps you present information on four stages. You can also present information on Data Integrity, Digital Signatures, Password Storage using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cryptographic Algorithms Used In Data Security Cloud Cryptography
Cryptographic Algorithms Used In Data Security Cloud CryptographyThis slide talks about algorithms used for implementing cryptography in data security. The purpose of this slide is to explain the different implementation steps. The techniques discussed are RSA Rivest, Shamir, Adleman cryptographic algorithm and Data Encryption Standard algorithm. Deliver an outstanding presentation on the topic using this Cryptographic Algorithms Used In Data Security Cloud Cryptography. Dispense information and present a thorough explanation of Cryptographic, Algorithms, Data Encryption Standard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Key Uses And Applications Of Cryptographic Security Cloud Cryptography
Key Uses And Applications Of Cryptographic Security Cloud CryptographyThis slide outlines the various uses of cryptography. The purpose of this slide is to elaborate the key applications of cryptography. These are computer security, digital currencies, web surfing security, electronic signatures, authentication, cryptocurrencies, etc. Increase audience engagement and knowledge by dispensing information using Key Uses And Applications Of Cryptographic Security Cloud Cryptography. This template helps you present information on nine stages. You can also present information on Computer Security, Digital Currencies, Web Surfing Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
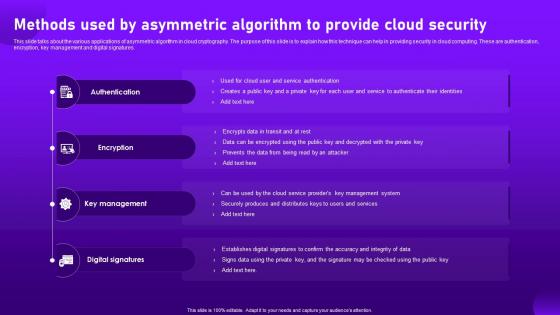 Methods Used By Asymmetric Algorithm To Provide Cloud Security Cloud Cryptography
Methods Used By Asymmetric Algorithm To Provide Cloud Security Cloud CryptographyThis slide talks about the various applications of asymmetric algorithm in cloud cryptography. The purpose of this slide is to explain how this technique can help in providing security in cloud computing. These are authentication, encryption, key management and digital signatures. Introducing Methods Used By Asymmetric Algorithm To Provide Cloud Security Cloud Cryptography to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Authentication, Key Management, Digital Signatures, using this template. Grab it now to reap its full benefits.
-
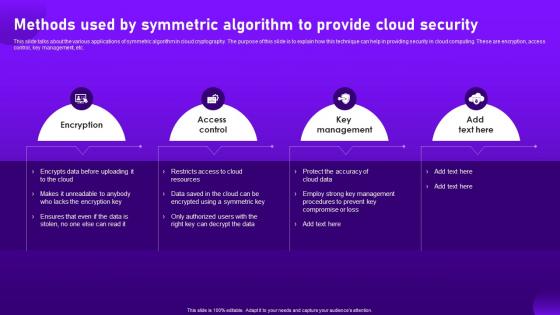 Methods Used By Symmetric Algorithm To Provide Cloud Security Cloud Cryptography
Methods Used By Symmetric Algorithm To Provide Cloud Security Cloud CryptographyThis slide talks about the various applications of symmetric algorithm in cloud cryptography. The purpose of this slide is to explain how this technique can help in providing security in cloud computing. These are encryption, access control, key management, etc. Increase audience engagement and knowledge by dispensing information using Methods Used By Symmetric Algorithm To Provide Cloud Security Cloud Cryptography. This template helps you present information on four stages. You can also present information on Encryption, Access Control, Key Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Most Commonly Types Of Ict Securities Used Comprehensive Guide For Deployment Strategy SS V
Most Commonly Types Of Ict Securities Used Comprehensive Guide For Deployment Strategy SS VThis slide represents various types of information and communication technology ICT securities used by businesses It covers network security, endpoint security, access security, and data encryption Increase audience engagement and knowledge by dispensing information using Most Commonly Types Of Ict Securities Used Comprehensive Guide For Deployment Strategy SS V This template helps you present information on four stages You can also present information on Network Security, End Point Security, Access Security using this PPT design This layout is completely editable so personaize it now to meet your audiences expectations
-
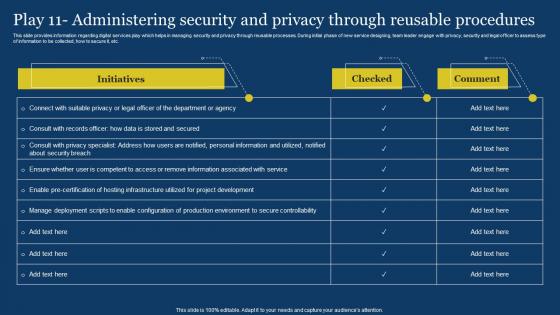 US Digital Services Management Play 11 Administering Security And Privacy Through ReUSable
US Digital Services Management Play 11 Administering Security And Privacy Through ReUSableThis slide provides information regarding digital services play which helps in managing security and privacy through reUSable processes. During initial phase of new service designing, team leader engage with privacy, security and legal officer to assess type of information to be collected, how to secure it, etc. Deliver an outstanding presentation on the topic USing this US Digital Services Management Play 11 Administering Security And Privacy Through ReUSable Dispense information and present a thorough explanation of Department Or Agency, Secure Controllability USing the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
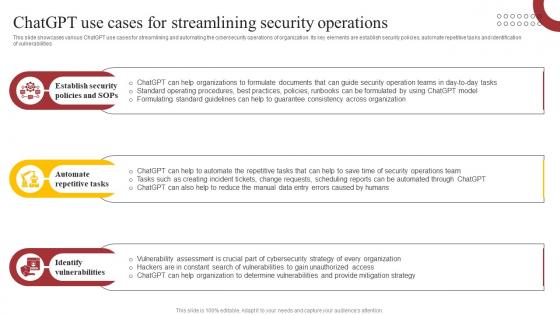 ChatGPT Use Cases For Streamlining Security How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SS
ChatGPT Use Cases For Streamlining Security How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SSThis slide showcases various ChatGPT use cases for streamlining and automating the cybersecurity operations of organization. Its key elements are establish security policies, automate repetitive tasks and identification of vulnerabilities Increase audience engagement and knowledge by dispensing information using ChatGPT Use Cases For Streamlining Security How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SS. This template helps you present information on three stages. You can also present information on Security, Policies, Repetitive using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
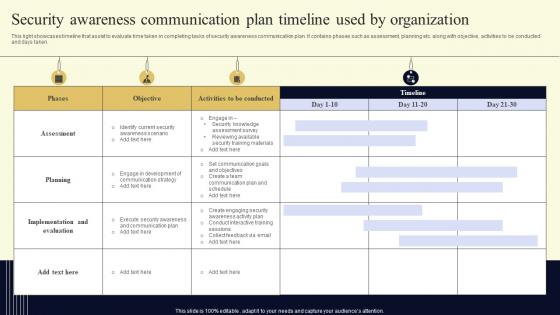 Security Awareness Communication Plan Timeline Used By Organization
Security Awareness Communication Plan Timeline Used By OrganizationThis light showcases timeline that assist to evaluate time taken in completing tasks of security awareness communication plan. It contains phases such as assessment, planning etc. along with objective, activities to be conducted and days taken. Presenting our well structured Security Awareness Communication Plan Timeline Used By Organization. The topics discussed in this slide are Security, Communication, Organization. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Plan Useful Data Backup Schedule Improving Cyber Security Risks Management
Plan Useful Data Backup Schedule Improving Cyber Security Risks ManagementThe following slide showcases the monthly calendar for data backup to advance cybersecurity protection and loss of information. It mainly includes techniques such as fully and incremental data backup etc. Present the topic in a bit more detail with this Plan Useful Data Backup Schedule Improving Cyber Security Risks Management. Use it as a tool for discussion and navigation on Incremental Backup, Plan Useful, Data Backup Schedule. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
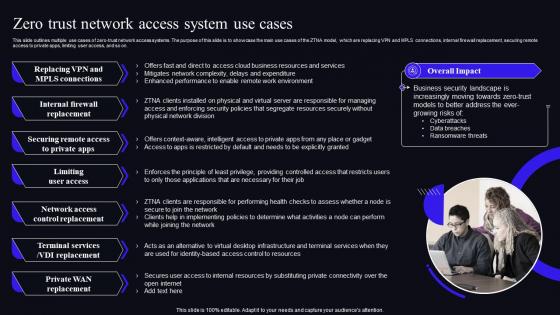 F1590 Zero Trust Network Access System Use Cases Zero Trust Security Model
F1590 Zero Trust Network Access System Use Cases Zero Trust Security ModelThis slide outlines multiple use cases of zero-trust network access systems. The purpose of this slide is to showcase the main use cases of the ZTNA model, which are replacing VPN and MPLS connections, internal firewall replacement, securing remote access to private apps, limiting user access, and so on. Present the topic in a bit more detail with this F1590 Zero Trust Network Access System Use Cases Zero Trust Security Model. Use it as a tool for discussion and navigation on Internal Firewall Replacement, Limiting User Access, Network Access Control Replacement. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
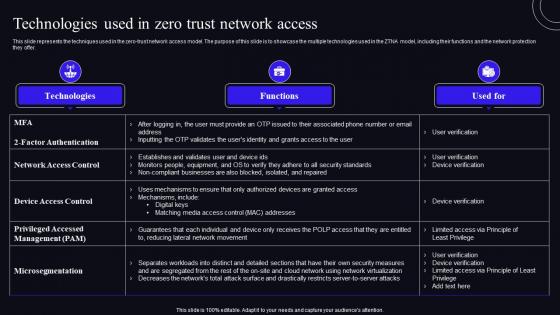 Technologies Used In Zero Trust Network Access Zero Trust Security Model
Technologies Used In Zero Trust Network Access Zero Trust Security ModelThis slide represents the techniques used in the zero-trust network access model. The purpose of this slide is to showcase the multiple technologies used in the ZTNA model, including their functions and the network protection they offer. Deliver an outstanding presentation on the topic using this Technologies Used In Zero Trust Network Access Zero Trust Security Model. Dispense information and present a thorough explanation of Technologies, Techniques, Protection using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
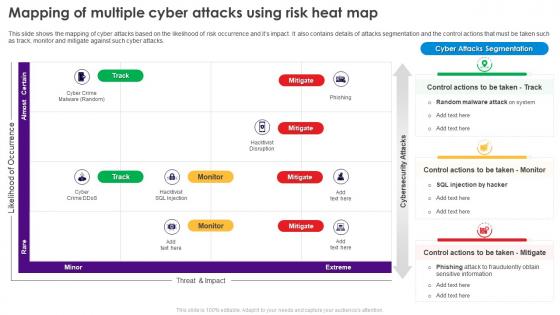 Security Plan To Prevent Cyber Mapping Of Multiple Cyber Attacks Using Risk Heat Map
Security Plan To Prevent Cyber Mapping Of Multiple Cyber Attacks Using Risk Heat MapThis slide shows the mapping of cyber attacks based on the likelihood of risk occurrence and its impact. It also contains details of attacks segmentation and the control actions that must be taken such as track, monitor and mitigate against such cyber attacks. Deliver an outstanding presentation on the topic using this Security Plan To Prevent Cyber Mapping Of Multiple Cyber Attacks Using Risk Heat Map. Dispense information and present a thorough explanation of Cyber Attacks, Risk Occurrence, Attacks Segmentation, Monitor And Mitigate using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 30 60 90 Days Plan To Integrate Secure Web Network Network Security Using Secure Web Gateway
30 60 90 Days Plan To Integrate Secure Web Network Network Security Using Secure Web GatewayThis slide represents 30-60-90 plan to implement Secure Web Gateway into firm. The purpose of this slide is to illustrate the plans of the first 90 days from the start, including steps to be followed at interval of one month. Introducing 30 60 90 Days Plan To Integrate Secure Web Network Network Security Using Secure Web Gateway to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Compatible, Performance, Production, using this template. Grab it now to reap its full benefits.
-
 Agenda Network Security Using Secure Web Gateway
Agenda Network Security Using Secure Web GatewayIncrease audience engagement and knowledge by dispensing information using Agenda Network Security Using Secure Web Gateway. This template helps you present information on seven stages. You can also present information on Protection, Businesses, Deployment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
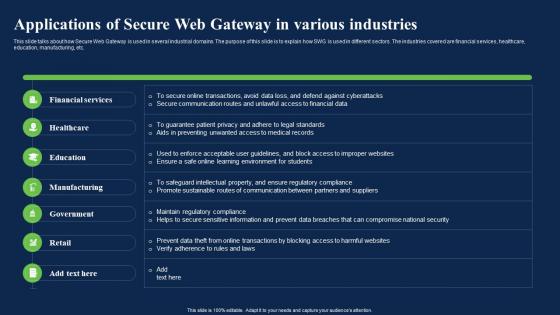 Applications Of Secure Web Gateway In Various Industries Network Security Using Secure Web Gateway
Applications Of Secure Web Gateway In Various Industries Network Security Using Secure Web GatewayThis slide talks about how Secure Web Gateway is used in several industrial domains. The purpose of this slide is to explain how SWG is used in different sectors. The industries covered are financial services, healthcare, education, manufacturing, etc. Present the topic in a bit more detail with this Applications Of Secure Web Gateway In Various Industries Network Security Using Secure Web Gateway. Use it as a tool for discussion and navigation on Applications, Financial Services, Education. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
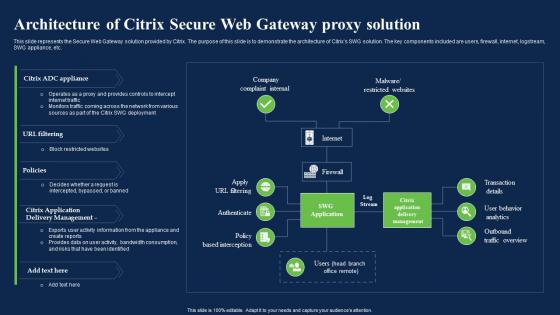 Architecture Of Citrix Secure Web Gateway Proxy Solution Network Security Using Secure Web Gateway
Architecture Of Citrix Secure Web Gateway Proxy Solution Network Security Using Secure Web GatewayThis slide represents the Secure Web Gateway solution provided by Citrix. The purpose of this slide is to demonstrate the architecture of Citrixs SWG solution. The key components included are users, firewall, internet, logstream, SWG appliance, etc. Deliver an outstanding presentation on the topic using this Architecture Of Citrix Secure Web Gateway Proxy Solution Network Security Using Secure Web Gateway. Dispense information and present a thorough explanation of Architecture, Company Complaint Internal, Malware Restricted Websites using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
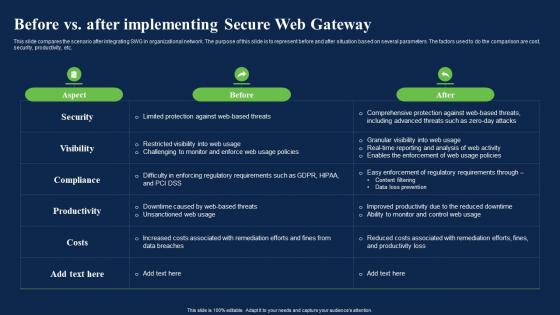 Before Vs After Implementing Secure Web Gateway Network Security Using Secure Web Gateway
Before Vs After Implementing Secure Web Gateway Network Security Using Secure Web GatewayThis slide compares the scenario after integrating SWG in organizational network. The purpose of this slide is to represent before and after situation based on several parameters. The factors used to do the comparison are cost, security, productivity, etc. Present the topic in a bit more detail with this Before Vs After Implementing Secure Web Gateway Network Security Using Secure Web Gateway. Use it as a tool for discussion and navigation on Productivity, Enforcement, Requirements. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Best Practices For Secure Web Gateway Implementation Network Security Using Secure Web Gateway
Best Practices For Secure Web Gateway Implementation Network Security Using Secure Web GatewayThis slide outlines various measures to be taken to maintain and enhance the functionality of Secure Web Gateway. The purpose of this slide is to demonstrate best practices for SWG. These are perform a risk assessment, deploy safe setups, monitor and analyse traffic, etc. Deliver an outstanding presentation on the topic using this Best Practices For Secure Web Gateway Implementation Network Security Using Secure Web Gateway. Dispense information and present a thorough explanation of Implementation, Assessment, Functionality using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
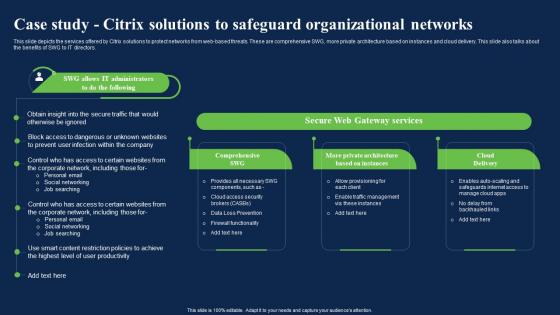 Case Study Citrix Solutions To Safeguard Network Security Using Secure Web Gateway
Case Study Citrix Solutions To Safeguard Network Security Using Secure Web GatewayThis slide depicts the services offered by Citrix solutions to protect networks from web-based threats. These are comprehensive SWG, more private architecture based on instances and cloud delivery. This slide also talks about the benefits of SWG to IT directors. Present the topic in a bit more detail with this Case Study Citrix Solutions To Safeguard Network Security Using Secure Web Gateway. Use it as a tool for discussion and navigation on Organizational, Solutions, Architecture. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Checklist To Implement Secure Web Gateway Network Security Using Secure Web Gateway
Checklist To Implement Secure Web Gateway Network Security Using Secure Web GatewayThis slide represents the checklist to implement Secure Web Gateway for application security. The key components included are determine use case, select best solution, plan deployment, configure solution, test and improve, roll out and monitor. Deliver an outstanding presentation on the topic using this Checklist To Implement Secure Web Gateway Network Security Using Secure Web Gateway. Dispense information and present a thorough explanation of Configure Solution, Plan Deployment, Application Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
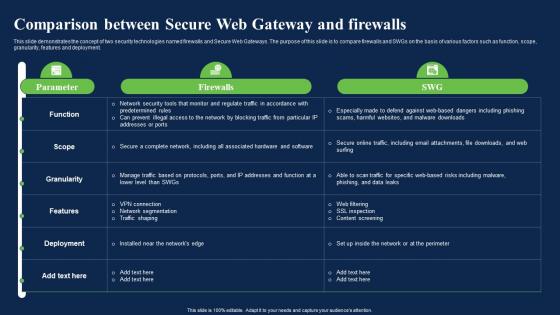 Comparison Between Secure Web Gateway And Firewalls Network Security Using Secure Web Gateway
Comparison Between Secure Web Gateway And Firewalls Network Security Using Secure Web GatewayThis slide demonstrates the concept of two security technologies named firewalls and Secure Web Gateways. The purpose of this slide is to compare firewalls and SWGs on the basis of various factors such as function, scope, granularity, features and deployment. Present the topic in a bit more detail with this Comparison Between Secure Web Gateway And Firewalls Network Security Using Secure Web Gateway. Use it as a tool for discussion and navigation on Comparison, Deployment, Technologies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Comparison Secure Web Gateway And Cloud Network Security Using Secure Web Gateway
Comparison Secure Web Gateway And Cloud Network Security Using Secure Web GatewayThis slide demonstrates the concept of cloud security gateways and Secure Web Gateways. The purpose of this slide is to compare cloud security gateways and SWGs on the basis of various factors such as scope, deployment, architecture, features and cost. Deliver an outstanding presentation on the topic using this Comparison Secure Web Gateway And Cloud Network Security Using Secure Web Gateway. Dispense information and present a thorough explanation of Deployment, Architecture, Comparison using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
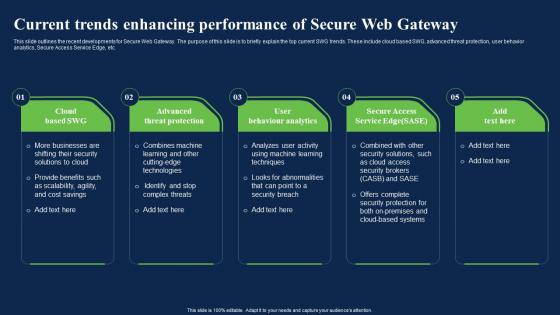 Current Trends Enhancing Performance Of Network Security Using Secure Web Gateway
Current Trends Enhancing Performance Of Network Security Using Secure Web GatewayThis slide outlines the recent developments for Secure Web Gateway. The purpose of this slide is to briefly explain the top current SWG trends. These include cloud based SWG, advanced threat protection, user behavior analytics, Secure Access Service Edge, etc. Introducing Current Trends Enhancing Performance Of Network Security Using Secure Web Gateway to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Analyzes, Performance, Developments, using this template. Grab it now to reap its full benefits.
-
 Estimated Budget Of Secure Web Gateway Network Security Using Secure Web Gateway
Estimated Budget Of Secure Web Gateway Network Security Using Secure Web GatewayThis slide represents the budget of integrating Secure Web Gateway in organization. The purpose of this slide is to showcase the estimated and actual cost for installing SWG. These include hardware and software, maintenance and support, training, etc. Present the topic in a bit more detail with this Estimated Budget Of Secure Web Gateway Network Security Using Secure Web Gateway. Use it as a tool for discussion and navigation on Organization, Represents, Maintenance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
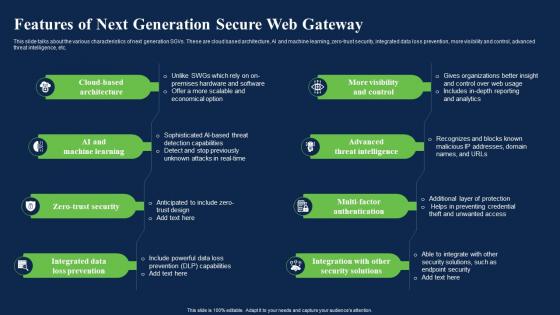 Features Of Next Generation Secure Web Gateway Network Security Using Secure Web Gateway
Features Of Next Generation Secure Web Gateway Network Security Using Secure Web GatewayThis slide talks about the various characteristics of next generation SGVs. These are cloud based architecture, AI and machine learning, zero-trust security, integrated data loss prevention, more visibility and control, advanced threat intelligence, etc. Introducing Features Of Next Generation Secure Web Gateway Network Security Using Secure Web Gateway to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Based Architecture, Integrated Data Loss Prevention, Multi Factor Authentication, using this template. Grab it now to reap its full benefits.
-
 Future Of Secure Web Gateway Technology Network Security Using Secure Web Gateway
Future Of Secure Web Gateway Technology Network Security Using Secure Web GatewayThis slide talks about the future of Secure Web Gateway security technology. The purpose of this slide is to explain how SWG can lead the cyber security market in future as more businesses are migrating to the cloud. Increase audience engagement and knowledge by dispensing information using Future Of Secure Web Gateway Technology Network Security Using Secure Web Gateway. This template helps you present information on five stages. You can also present information on Predicted, Investment, Technology using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons Slide Network Security Using Secure Web Gateway
Icons Slide Network Security Using Secure Web GatewayDeliver an outstanding presentation on the topic using this Icons Slide Network Security Using Secure Web Gateway. Dispense information and present a thorough explanation of Icons using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Impact Of Secure Web Gateway On Application Security Network Security Using Secure Web Gateway
Impact Of Secure Web Gateway On Application Security Network Security Using Secure Web GatewayThis slide represents the various factors which showcase the improvement of application security after adopting SWG. The parameters discussed are enhanced protection against web-based attacks, content filtering, policy enforcement, Data Loss Prevention, etc. Present the topic in a bit more detail with this Impact Of Secure Web Gateway On Application Security Network Security Using Secure Web Gateway. Use it as a tool for discussion and navigation on Enforcement, Application, Prevention. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
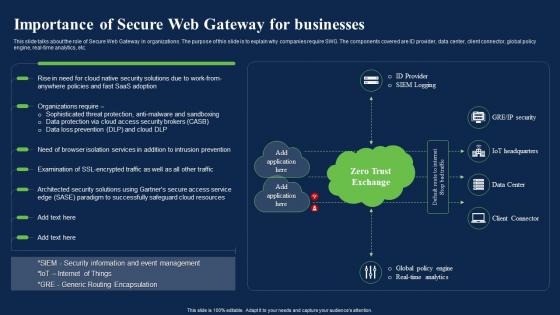 Importance Of Secure Web Gateway For Businesses Network Security Using Secure Web Gateway
Importance Of Secure Web Gateway For Businesses Network Security Using Secure Web GatewayThis slide talks about the role of Secure Web Gateway in organizations. The purpose of this slide is to explain why companies require SWG. The components covered are ID provider, data center, client connector, global policy engine, real-time analytics, etc. Deliver an outstanding presentation on the topic using this Importance Of Secure Web Gateway For Businesses Network Security Using Secure Web Gateway. Dispense information and present a thorough explanation of Businesses, Encapsulation, Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
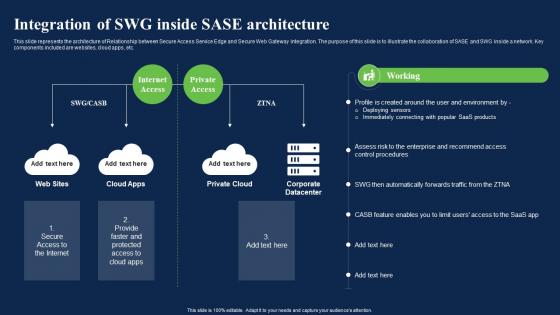 Integration Of Swg Inside Sase Architecture Network Security Using Secure Web Gateway
Integration Of Swg Inside Sase Architecture Network Security Using Secure Web GatewayThis slide represents the architecture of Relationship between Secure Access Service Edge and Secure Web Gateway integration. The purpose of this slide is to illustrate the collaboration of SASE and SWG inside a network. Key components included are websites, cloud apps, etc. Deliver an outstanding presentation on the topic using this Integration Of Swg Inside Sase Architecture Network Security Using Secure Web Gateway. Dispense information and present a thorough explanation of Architecture, Integration, Environment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Introduction To Next Generation Secure Web Gateway Network Security Using Secure Web Gateway
Introduction To Next Generation Secure Web Gateway Network Security Using Secure Web GatewayThis slide demonstrates the concept of Next Generation Secure Web Gateway solution. The purpose of this slide is to provide an overview of next generation SGVs. This slide also talks about the need of this security technology for cloud applications. Present the topic in a bit more detail with this Introduction To Next Generation Secure Web Gateway Network Security Using Secure Web Gateway. Use it as a tool for discussion and navigation on Businesses, Capabilities, Sophisticated. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Introduction To Secure Web Gateway Technology Network Security Using Secure Web Gateway
Introduction To Secure Web Gateway Technology Network Security Using Secure Web GatewayThis slide talks about the network security solution called Secure Web Gateway. The purpose of this slide is to outline the various benefits of SWG. This slide also represents different working components of SWG such as traffic inspection, malware protection, etc. Deliver an outstanding presentation on the topic using this Introduction To Secure Web Gateway Technology Network Security Using Secure Web Gateway. Dispense information and present a thorough explanation of Introduction, Technology, Overview using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.


