Powerpoint Templates and Google slides for Threat Protection Pillar
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Implementing security management plan to reduce threats and protect sensitive company data complete deck
Implementing security management plan to reduce threats and protect sensitive company data complete deckThis complete deck covers various topics and highlights important concepts. It has PPT slides which cater to your business needs. This complete deck presentation emphasizes Implementing Security Management Plan To Reduce Threats And Protect Sensitive Company Data Complete Deck and has templates with professional background images and relevant content. This deck consists of total of fourty two slides. Our designers have created customizable templates, keeping your convenience in mind. You can edit the colour, text and font size with ease. Not just this, you can also add or delete the content if needed. Get access to this fully editable complete presentation by clicking the download button below.
-
 Advanced Threat Protection Powerpoint Ppt Template Bundles CRP
Advanced Threat Protection Powerpoint Ppt Template Bundles CRPIf you require a professional template with great design, then this Advanced Threat Protection Powerpoint Ppt Template Bundles CRP is an ideal fit for you. Deploy it to enthrall your audience and increase your presentation threshold with the right graphics, images, and structure. Portray your ideas and vision using Twenty slides included in this complete deck. This template is suitable for expert discussion meetings presenting your views on the topic. With a variety of slides having the same thematic representation, this template can be regarded as a complete package. It employs some of the best design practices, so everything is well-structured. Not only this, it responds to all your needs and requirements by quickly adapting itself to the changes you make. This PPT slideshow is available for immediate download in PNG, JPG, and PDF formats, further enhancing its usability. Grab it by clicking the download button.
-
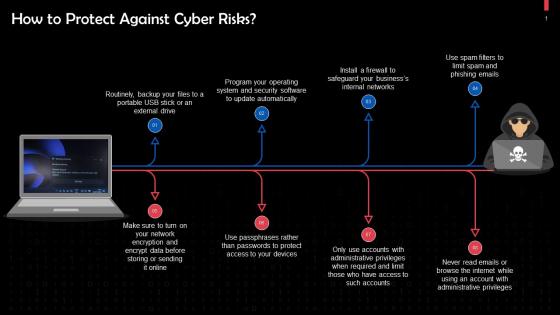 Protection Against Cyber Threats And Attacks Training Ppt
Protection Against Cyber Threats And Attacks Training PptPresenting Protection Against Cyber Threats and Attacks. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Cyber Security Icon Network Protection Threat Server Database Software
Cyber Security Icon Network Protection Threat Server Database SoftwareKeep your audience glued to their seats with professionally designed PPT slides. This deck comprises of total of twelve slides. It has PPT templates with creative visuals and well researched content. Not just this, our PowerPoint professionals have crafted this deck with appropriate diagrams, layouts, icons, graphs, charts and more. This content ready presentation deck is fully editable. Just click the DOWNLOAD button below. Change the colour, text and font size. You can also modify the content as per your need. Get access to this well crafted complete deck presentation and leave your audience stunned.
-
 Protect Against Internal Cyber Threats In Powerpoint And Google Slides Cpb
Protect Against Internal Cyber Threats In Powerpoint And Google Slides CpbPresenting our Protect Against Internal Cyber Threats In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Protect Against Internal Cyber Threats This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
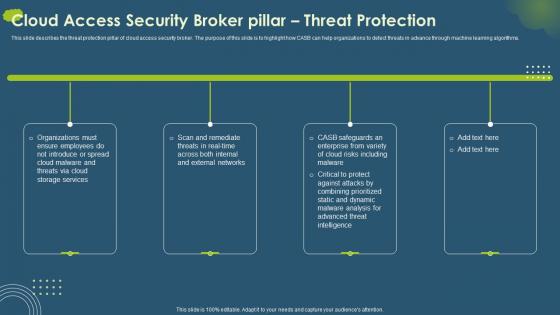 Cloud Access Security Broker CASB V2 Pillar Threat Protection Ppt Icon Introduction
Cloud Access Security Broker CASB V2 Pillar Threat Protection Ppt Icon IntroductionThis slide describes the threat protection pillar of cloud access security broker. The purpose of this slide is to highlight how CASB can help organizations to detect threats in advance through machine learning algorithms. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 Pillar Threat Protection Ppt Icon Introduction. This template helps you present information on four stages. You can also present information on Threat Protection Pillar, Cloud Access Security Broker, Machine Learning Algorithms using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cybersecurity Kpi Icon Showcasing Threat Protection
Cybersecurity Kpi Icon Showcasing Threat ProtectionIntroducing our Cybersecurity Kpi Icon Showcasing Threat Protection set of slides. The topics discussed in these slides are Cybersecurity Kpi Showcasing, Threat Protection. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Comprehensive Guide To Understand Solutions To Protect Bitcoin Against Security Threats Fin SS
Comprehensive Guide To Understand Solutions To Protect Bitcoin Against Security Threats Fin SSThis slide shows solutions to various types of threats associated with Bitcoins security which can be used by individuals to secure their digital currencies. It incudes protection against frauds such as malware attacks, fake wallets, SIM swapping, etc. Introducing Comprehensive Guide To Understand Solutions To Protect Bitcoin Against Security Threats Fin SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Malware Attacks, Social Engineering Attacks, Bitcoin Against Security Threats, using this template. Grab it now to reap its full benefits.
-
 Advanced Threat Protection Detection Icon
Advanced Threat Protection Detection IconPresenting our set of slides with Advanced Threat Protection Detection Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Protection, Threat, Detection.
-
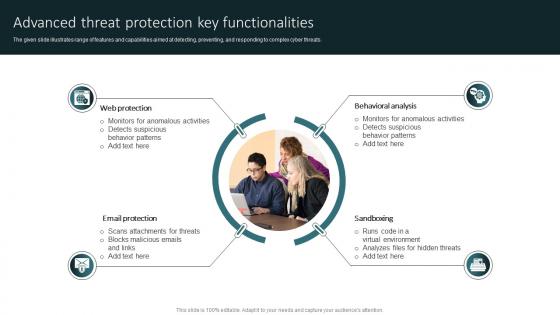 Advanced Threat Protection Key Functionalities
Advanced Threat Protection Key FunctionalitiesThe given slide illustrates range of features and capabilities aimed at detecting, preventing, and responding to complex cyber threats. Introducing our premium set of slides with Advanced Threat Protection Key Functionalities. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Protection, Email, Sandboxing. So download instantly and tailor it with your information.
-
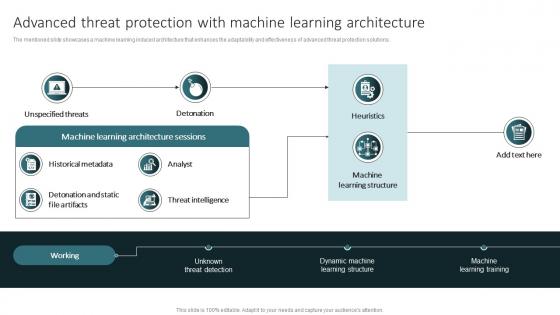 Advanced Threat Protection With Machine Learning Architecture
Advanced Threat Protection With Machine Learning ArchitectureThe mentioned slide showcases a machine learning induced architecture that enhances the adaptability and effectiveness of advanced threat protection solutions. Introducing our Advanced Threat Protection With Machine Learning Architecture set of slides. The topics discussed in these slides are Historical, Intelligence, Learning. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Advantages Of Utilizing Advanced Threat Protection In Cyber Security
Advantages Of Utilizing Advanced Threat Protection In Cyber SecurityThe following slide highlights the possible benefits of implementing advanced threat protection against sophisticated cyber threats and attacks. Presenting our set of slides with Advantages Of Utilizing Advanced Threat Protection In Cyber Security. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security, Analytics, Protection.
-
 Best Advanced Threat Protection Software
Best Advanced Threat Protection SoftwareThe following slide exhibits diverse specialized software that helps in detecting unauthorized, and external attacks to private systems. Introducing our premium set of slides with Best Advanced Threat Protection Software. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Protection, Endpoint, Networks. So download instantly and tailor it with your information.
-
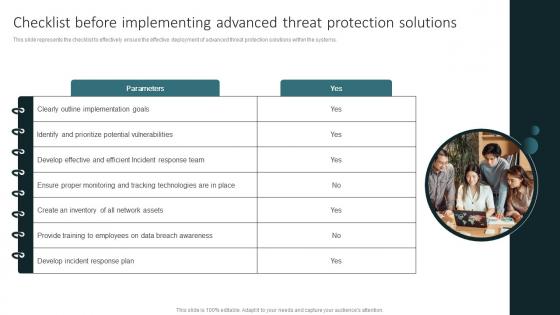 Checklist Before Implementing Advanced Threat Protection Solutions
Checklist Before Implementing Advanced Threat Protection SolutionsThis slide represents the checklist to effectively ensure the effective deployment of advanced threat protection solutions within the systems. Presenting our set of slides with Checklist Before Implementing Advanced Threat Protection Solutions. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Implementing, Advanced, Protection.
-
 Cloud Integration With Advanced Threat Protection Solutions
Cloud Integration With Advanced Threat Protection SolutionsThe mentioned slide outlines key considerations of indulging cloud technology with advanced threat protection to mitigate sophisticated cyber threats effectively. Presenting our set of slides with Cloud Integration With Advanced Threat Protection Solutions. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Machine, Intelligence, Analytics.
-
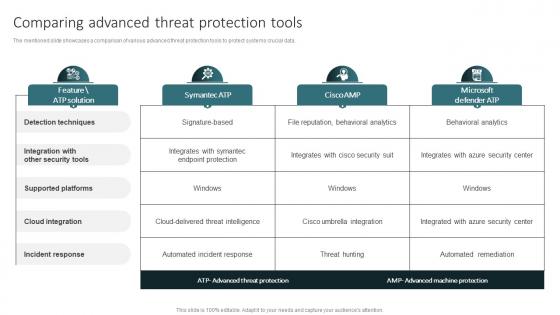 Comparing Advanced Threat Protection Tools
Comparing Advanced Threat Protection ToolsThe mentioned slide showcases a comparison of various advanced threat protection tools to protect systems crucial data. Presenting our well structured Comparing Advanced Threat Protection Tools. The topics discussed in this slide are Techniques, Security, Platforms. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Emerging Trends In Advanced Threat Protection
Emerging Trends In Advanced Threat ProtectionThe purpose of this slide is to exhibit latest trends associated with advanced threat protection such as usage of AI, edge computing security, blockchain for IoT security, etc. Introducing our premium set of slides with Emerging Trends In Advanced Threat Protection. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security, Device, Cybersecurity. So download instantly and tailor it with your information.
-
 Integrating AI With Advanced Threat Protection Icon
Integrating AI With Advanced Threat Protection IconIntroducing our Integrating AI With Advanced Threat Protection Icon set of slides. The topics discussed in these slides are Protection, Threat, Integrating. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
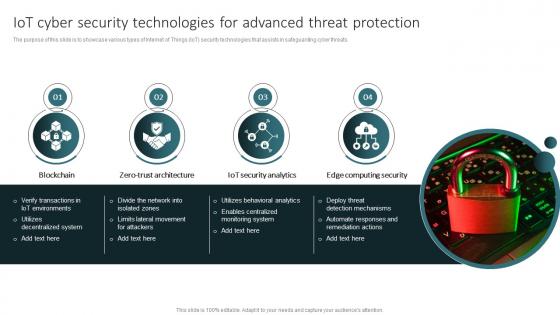 IoT Cyber Security Technologies For Advanced Threat Protection
IoT Cyber Security Technologies For Advanced Threat ProtectionThe purpose of this slide is to showcase various types of Internet of Things IoT security technologies that assists in safeguarding cyber threats. Introducing our premium set of slides with IoT Cyber Security Technologies For Advanced Threat Protection. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Architecture, Security, Computing. So download instantly and tailor it with your information.
-
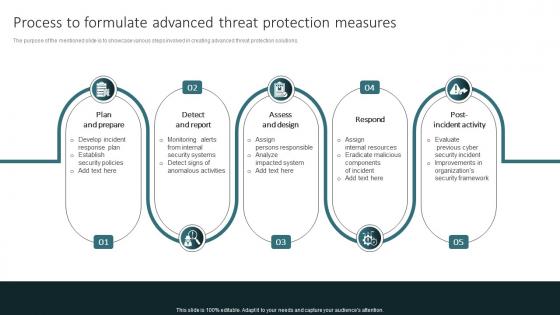 Process To Formulate Advanced Threat Protection Measures
Process To Formulate Advanced Threat Protection MeasuresThe purpose of the mentioned slide is to showcase various steps involved in creating advanced threat protection solutions. Presenting our set of slides with Process To Formulate Advanced Threat Protection Measures. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Prepare, Report, Design.
-
 Real World Example Of Advanced Threat Protection Effectiveness
Real World Example Of Advanced Threat Protection EffectivenessThe mentioned slide showcases real life instances of utilizing advanced threat protection solutions that contribute to a proactive defense strategy. Introducing our premium set of slides with Real World Example Of Advanced Threat Protection Effectiveness. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Ransomware, Destructive, Analytics. So download instantly and tailor it with your information.
-
 Solutions To Overcome Advanced Threat Protection Implementation Challenges
Solutions To Overcome Advanced Threat Protection Implementation ChallengesThe purpose of this slide is to showcase various solutions that assist in resolving issues while implementing advanced threat protection solutions in the systems. Presenting our set of slides with Solutions To Overcome Advanced Threat Protection Implementation Challenges. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Standardization, Security, Physical.
-
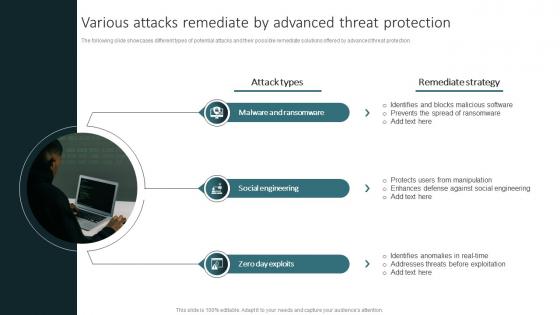 Various Attacks Remediate By Advanced Threat Protection
Various Attacks Remediate By Advanced Threat ProtectionThe following slide showcases different types of potential attacks and their possible remediate solutions offered by advanced threat protection. Introducing our premium set of slides with Various Attacks Remediate By Advanced Threat Protection. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Ransomware, Engineering, Exploits. So download instantly and tailor it with your information.
-
 Cloud Based Advanced Threat Protection Icon
Cloud Based Advanced Threat Protection IconIntroducing our premium set of slides with Cloud Based Advanced Threat Protection Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Protection, Cloud, Advanced. So download instantly and tailor it with your information.
-
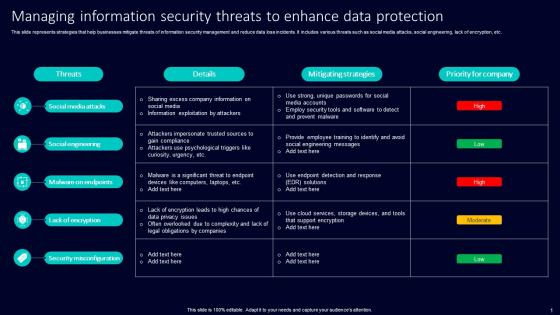 Managing Information Security Threats To Enhance Data Protection
Managing Information Security Threats To Enhance Data ProtectionThis slide represents strategies that help businesses mitigate threats of information security management and reduce data loss incidents. It includes various threats such as social media attacks, social engineering, lack of encryption, etc. Presenting our well structured Managing Information Security Threats To Enhance Data Protection. The topics discussed in this slide are Social Media Attacks, Social Engineering, Malware On Endpoints. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Icon For Cyber Protection With Threat Analytics
Icon For Cyber Protection With Threat AnalyticsIntroducing our premium set of slides with Icon For Cyber Protection With Threat Analytics. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Security, Threat Analytics, Icon. So download instantly and tailor it with your information.
-
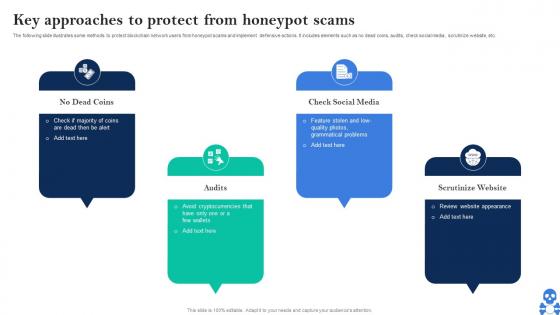 Cyber Threats In Blockchain Key Approaches To Protect From Honeypot Scams BCT SS V
Cyber Threats In Blockchain Key Approaches To Protect From Honeypot Scams BCT SS VThe following slide illustrates some methods to protect blockchain network users from honeypot scams and implement defensive actions. It includes elements such as no dead coins, audits, check social media, scrutinize website, etc. Introducing Cyber Threats In Blockchain Key Approaches To Protect From Honeypot Scams BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on No Dead Coins, Check Social Media, Scrutinize Website using this template. Grab it now to reap its full benefits.
-
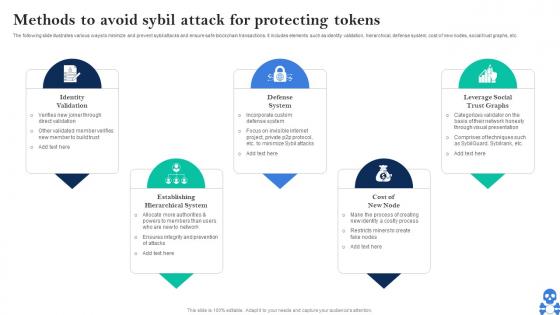 Cyber Threats In Blockchain Methods To Avoid Sybil Attack For Protecting Tokens BCT SS V
Cyber Threats In Blockchain Methods To Avoid Sybil Attack For Protecting Tokens BCT SS VThe following slide illustrates various ways to minimize and prevent sybil attacks and ensure safe blockchain transactions. It includes elements such as identity validation, hierarchical, defense system, cost of new nodes, social trust graphs, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Methods To Avoid Sybil Attack For Protecting Tokens BCT SS V This template helps you present information on Five stages. You can also present information on Identity Validation, Defense System, Cost Of New Node using this PPT design. This layout is completely editable so personaize it now
-
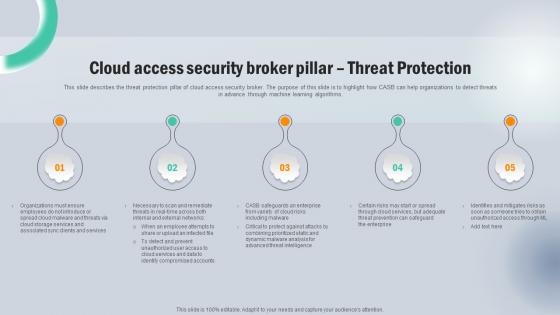 Cloud Access Security Broker Pillar Threat Protection Next Generation CASB
Cloud Access Security Broker Pillar Threat Protection Next Generation CASBThis slide describes the threat protection pillar of cloud access security broker. The purpose of this slide is to highlight how CASB can help organizations to detect threats in advance through machine learning algorithms. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker Pillar Threat Protection Next Generation CASB This template helps you present information on five stages. You can also present information on Services, Cloud Storage, Compromised Accounts using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Access Security Broker Pillar Threat Protection CASB Cloud Security
Cloud Access Security Broker Pillar Threat Protection CASB Cloud SecurityThis slide describes the threat protection pillar of cloud access security broker. The purpose of this slide is to highlight how CASB can help organizations to detect threats in advance through machine learning algorithms. Introducing Cloud Access Security Broker Pillar Threat Protection CASB Cloud Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Access Security Broker Pillar, Threat Protection Pillar, Machine Learning Algorithms, using this template. Grab it now to reap its full benefits.
-
 Firewall Security Icon Protecting From Cyber Threats
Firewall Security Icon Protecting From Cyber ThreatsIntroducing our Firewall Security Icon Protecting From Cyber Threats set of slides. The topics discussed in these slides are Firewall Security, Protecting. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
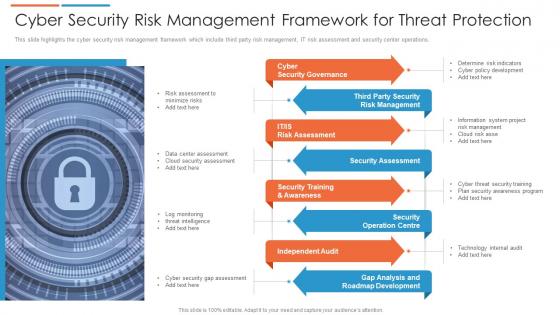 Cyber security risk management framework for threat protection
Cyber security risk management framework for threat protectionThis slide highlights the cyber security risk management framework which include third party risk management, IT risk assessment and security center operations. Presenting our set of slides with Cyber Security Risk Management Framework For Threat Protection. This exhibits information on eight stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Governance, Security Assessment, Independent Audit.
-
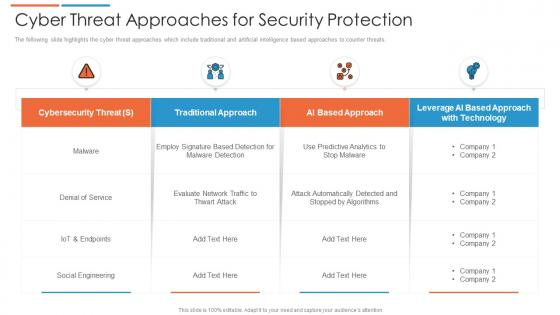 Cyber threat approaches for security protection
Cyber threat approaches for security protectionThe following slide highlights the cyber threat approaches which include traditional and artificial intelligence based approaches to counter threats. Presenting our well structured Cyber Threat Approaches For Security Protection. The topics discussed in this slide are Cybersecurity Threat, Social Engineering, Traditional Approach. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
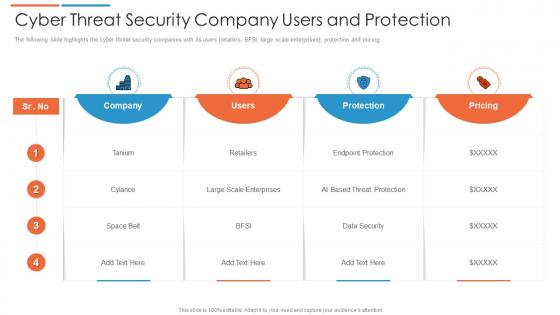 Cyber threat security company users and protection
Cyber threat security company users and protectionThe following slide highlights the cyber threat security companies with its users retailers, BFSI, large scale enterprises, protection and pricing. Introducing our Cyber Threat Security Company Users And Protection set of slides. The topics discussed in these slides are Pricing, Company, Users. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
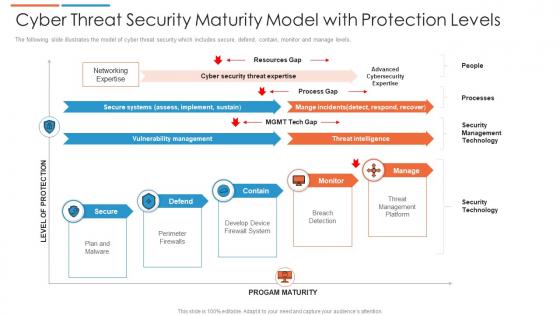 Cyber threat security maturity model with protection levels
Cyber threat security maturity model with protection levelsThe following slide illustrates the model of cyber threat security which includes secure, defend, contain, monitor and manage levels. Presenting our well structured Cyber Threat Security Maturity Model With Protection Levels. The topics discussed in this slide are Security Management Technology, Threat Management Platform, Threat Intelligence. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cyber threat strategies for security protection
Cyber threat strategies for security protectionThis slide highlights the cyber threat strategies that include risk assessment, phishing program, software protocols and end point protection. Presenting our set of slides with Cyber Threat Strategies For Security Protection. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Phishing Program, Software Protocols, End Point Protection.
-
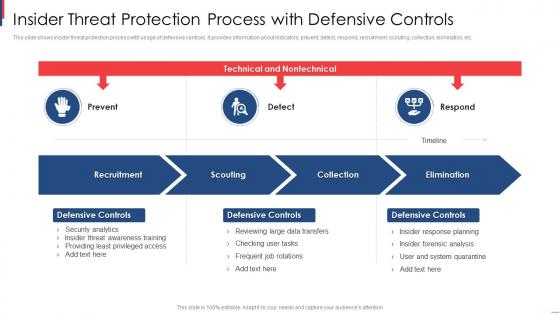 Insider Threat Protection Process With Defensive Controls
Insider Threat Protection Process With Defensive ControlsThis slide shows insider threat protection process with usage of defensive controls. It provides information about indicators, prevent, detect, respond, recruitment, scouting, collection, elimination, etc. Introducing our premium set of slides with Insider Threat Protection Process With Defensive Controls. Elucidate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Recruitment, Scouting, Collection, Elimination. So download instantly and tailor it with your information.
-
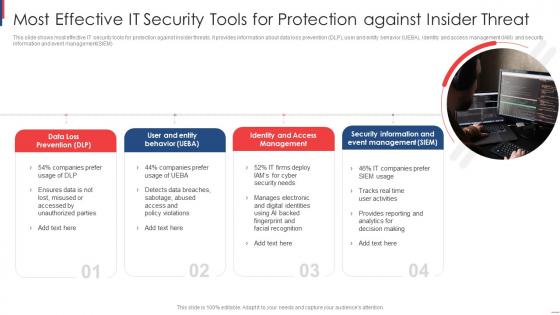 Most Effective It Security Tools For Protection Against Insider Threat
Most Effective It Security Tools For Protection Against Insider ThreatThis slide shows most effective IT security tools for protection against insider threats. It provides information about data loss prevention DLP, user and entity behavior UEBA, identity and access management IAM and security information and event management SIEM Introducing our premium set of slides with Most Effective It Security Tools For Protection Against Insider Threat. Elucidate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Loss Prevention, User Entity Behavior, Identity Access Management. So download instantly and tailor it with your information.
-
 Cloud Security Threat Protection Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Cloud Security Threat Protection Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Cloud security threat protection colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Cloud Security Threat Protection Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Cloud Security Threat Protection Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Cloud security threat protection monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Cloud Security Risks Or Threats Cloud Data Protection
Cloud Security Risks Or Threats Cloud Data ProtectionThis slide represents the list of threats or risks that can impact the security of a cloud these risks include loss of intellectual property, compliance violations, malware attacks, and so on. Increase audience engagement and knowledge by dispensing information using Cloud Security Risks Or Threats Cloud Data Protection. This template helps you present information on eight stages. You can also present information on Revenue Losses, Compliance Violations, Loss Of Data using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Cloud Security Threats Compliance Violations Cloud Data Protection
Cloud Security Threats Compliance Violations Cloud Data ProtectionThis slide depicts the value of compliance violations threat of cloud security in a business and how fast an organization can switch to a non-compliance state. Introducing Cloud Security Threats Compliance Violations Cloud Data Protection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Authentication Procedures, Business, Organizations, using this template. Grab it now to reap its full benefits.
-
 Cloud Security Threats Contract Breaches With Clients Cloud Data Protection
Cloud Security Threats Contract Breaches With Clients Cloud Data ProtectionThis slide defines the contract breaches with clients and customers that could be the biggest threat to the organizational data. Increase audience engagement and knowledge by dispensing information using Cloud Security Threats Contract Breaches With Clients Cloud Data Protection. This template helps you present information on four stages. You can also present information on Business Partners, Organization, Cloud using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
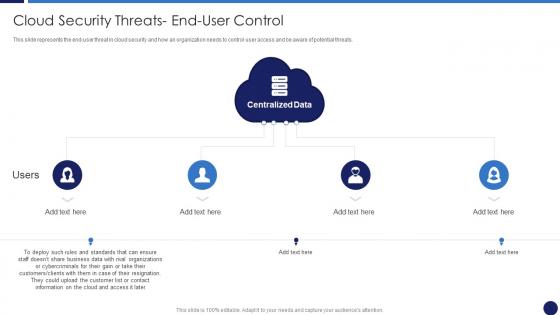 Cloud Security Threats End User Control Cloud Data Protection
Cloud Security Threats End User Control Cloud Data ProtectionThis slide represents the end-user threat in cloud security and how an organization needs to control user access and be aware of potential threats. Introducing Cloud Security Threats End User Control Cloud Data Protection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Business Data, Customers, Centralized Data, using this template. Grab it now to reap its full benefits.
-
 Cloud Security Threats Loss Of Data Cloud Data Protection
Cloud Security Threats Loss Of Data Cloud Data ProtectionThis slide represents the data loss threat of cloud security it is essential to secure organization data and create backups. Increase audience engagement and knowledge by dispensing information using Cloud Security Threats Loss Of Data Cloud Data Protection. This template helps you present information on four stages. You can also present information on Storage Locations, Organization, Strategies using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
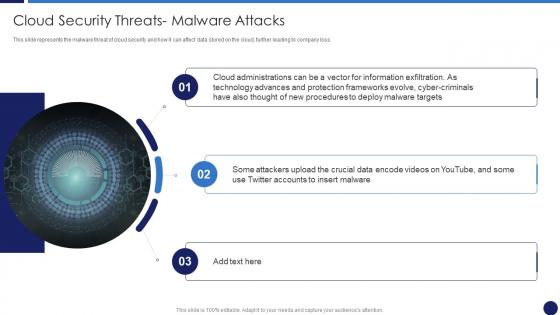 Cloud Security Threats Malware Attacks Cloud Data Protection
Cloud Security Threats Malware Attacks Cloud Data ProtectionThis slide represents the malware threat of cloud security and how it can affect data stored on the cloud, further leading to company loss. Introducing Cloud Security Threats Malware Attacks Cloud Data Protection to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispense information on Frameworks, Targets, Technology, using this template. Grab it now to reap its full benefits.
-
 Cloud Security Threats Revenue Losses Cloud Data Protection
Cloud Security Threats Revenue Losses Cloud Data ProtectionThis slide represents the revenue loss threat of cloud security and how an organization could lose customers trust and loyalty when it doesnt have a good recovery plan. Increase audience engagement and knowledge by dispensing information using Cloud Security Threats Revenue Losses Cloud Data Protection. This template helps you present information on five stages. You can also present information on Organizations Could, Revenue, Customers using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Cloud Security Threats Shared Vulnerabilities Cloud Data Protection
Cloud Security Threats Shared Vulnerabilities Cloud Data ProtectionThis slide describes how organizations and providers share vulnerabilities of a system, so each party must take precautions to protect data. Introducing Cloud Security Threats Shared Vulnerabilities Cloud Data Protection to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispense information on Secure Cloud Data, Organizations, Data Security, using this template. Grab it now to reap its full benefits.
-
 Outsider Threat Protection Ppt Powerpoint Presentation Ideas File Formats Cpb
Outsider Threat Protection Ppt Powerpoint Presentation Ideas File Formats CpbPresenting our Outsider Threat Protection Ppt Powerpoint Presentation Ideas File Formats Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Outsider Threat Protection. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
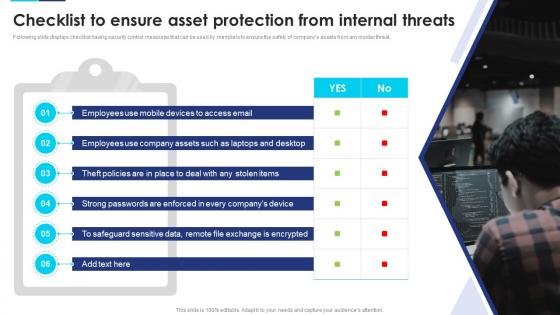 Incident Response Playbook Checklist To Ensure Asset Protection From Internal Threats
Incident Response Playbook Checklist To Ensure Asset Protection From Internal ThreatsFollowing slide displays checklist having security control measures that can be used by members to ensure the safety of companys assets from any insider threat. Introducing Incident Response Playbook Checklist To Ensure Asset Protection From Internal Threats to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Mobile Devices, Company Assets, Employees, using this template. Grab it now to reap its full benefits.
-
 Insider threat protection ppt powerpoint presentation professional graphic images cpb
Insider threat protection ppt powerpoint presentation professional graphic images cpbPresenting our Insider Threat Protection Ppt Powerpoint Presentation Professional Graphic Images Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Insider Threat Protection This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Threat Protection Sources Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Threat Protection Sources Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Threat protection sources colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Threat Protection Sources Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Threat Protection Sources Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Threat protection sources monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
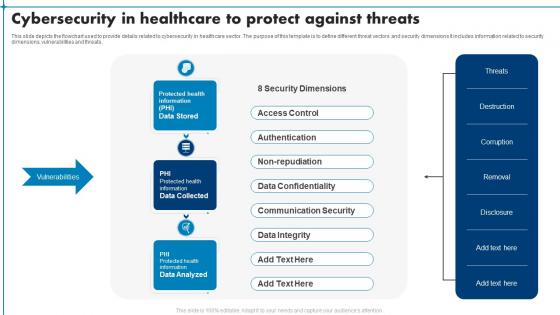 Cybersecurity In Healthcare To Protect Against Threats
Cybersecurity In Healthcare To Protect Against ThreatsThis slide depicts the flowchart used to provide details related to cybersecurity in healthcare sector. The purpose of this template is to define different threat vectors and security dimensions It includes information related to security dimensions, vulnerabilities and threats. Presenting our well structured Cybersecurity In Healthcare To Protect Against Threats. The topics discussed in this slide are Access Control, Data Confidentiality, Communication Security. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Insider Threat Mitigation And Protection Process
Insider Threat Mitigation And Protection ProcessThis slide includes steps to identify, manage and mitigate potential cyber threats. It includes four steps define, detect, assess and manage. Introducing our premium set of slides with name Insider Threat Mitigation And Protection Process. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Detect, Manage, Assess, Define. So download instantly and tailor it with your information.
-
 Checklist To Ensure Asset Protection From Internal Threats Cybersecurity Incident And Vulnerability
Checklist To Ensure Asset Protection From Internal Threats Cybersecurity Incident And VulnerabilityFollowing slide displays checklist having security control measures that can be used by members to ensure the safety of companys assets from any insider threat. Introducing Checklist To Ensure Asset Protection From Internal Threats Cybersecurity Incident And Vulnerability to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Employees, Email, Mobile Devices, using this template. Grab it now to reap its full benefits.
-
 Checklist To Ensure Asset Protection From Internal Threats Security Incident Response Playbook
Checklist To Ensure Asset Protection From Internal Threats Security Incident Response PlaybookFollowing slide displays checklist having security control measures that can be used by members to ensure the safety of companys assets from any insider threat. Deliver an outstanding presentation on the topic using this Checklist To Ensure Asset Protection From Internal Threats Security Incident Response Playbook. Dispense information and present a thorough explanation of Protection, Measures, Ensure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Visibility And Threat Data Protection Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Visibility And Threat Data Protection Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis colourful PowerPoint icon depicts visibility and threat detection, helping you to clearly identify any potential threats and take appropriate action. It is an effective visual aid for presentations, making it easier to explain complex concepts in a simple and straightforward way.
-
 Visibility And Threat Data Protection Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Visibility And Threat Data Protection Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone powerpoint icon is perfect for presentations on Visibility and Threat Detection. It features a silhouette of a person with a magnifying glass, representing the need to identify potential risks and threats. This icon is sure to help communicate your message in a visually appealing way.
-
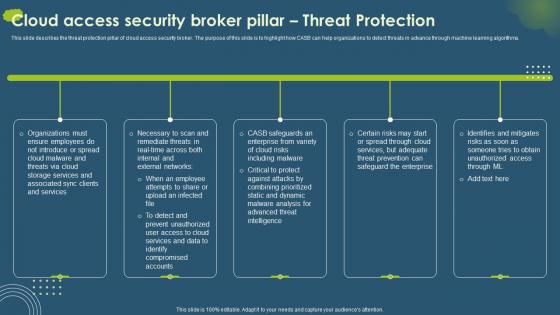 Cloud Access Security Broker Pillar Threat Protection Ppt Infographics Slide Download
Cloud Access Security Broker Pillar Threat Protection Ppt Infographics Slide DownloadThis slide describes the threat protection pillar of cloud access security broker. The purpose of this slide is to highlight how CASB can help organizations to detect threats in advance through machine learning algorithms. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker Pillar Threat Protection Ppt Infographics Slide Download. This template helps you present information on five stages. You can also present information on Organizations, Necessary, Safeguards using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.


