Key Pillars Of Identification And Access Management Strategy
This slide shows main features of an effective IAM strategy. The purpose of this strategy is to highlight major components of IAM strategy. It include features such as provisioning identities, access security certification and security management , etc.
You must be logged in to download this presentation.
 Impress your
Impress your audience
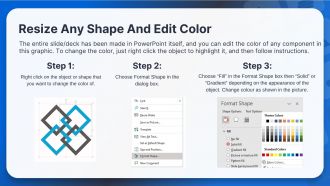
Editable
of Time
PowerPoint presentation slides
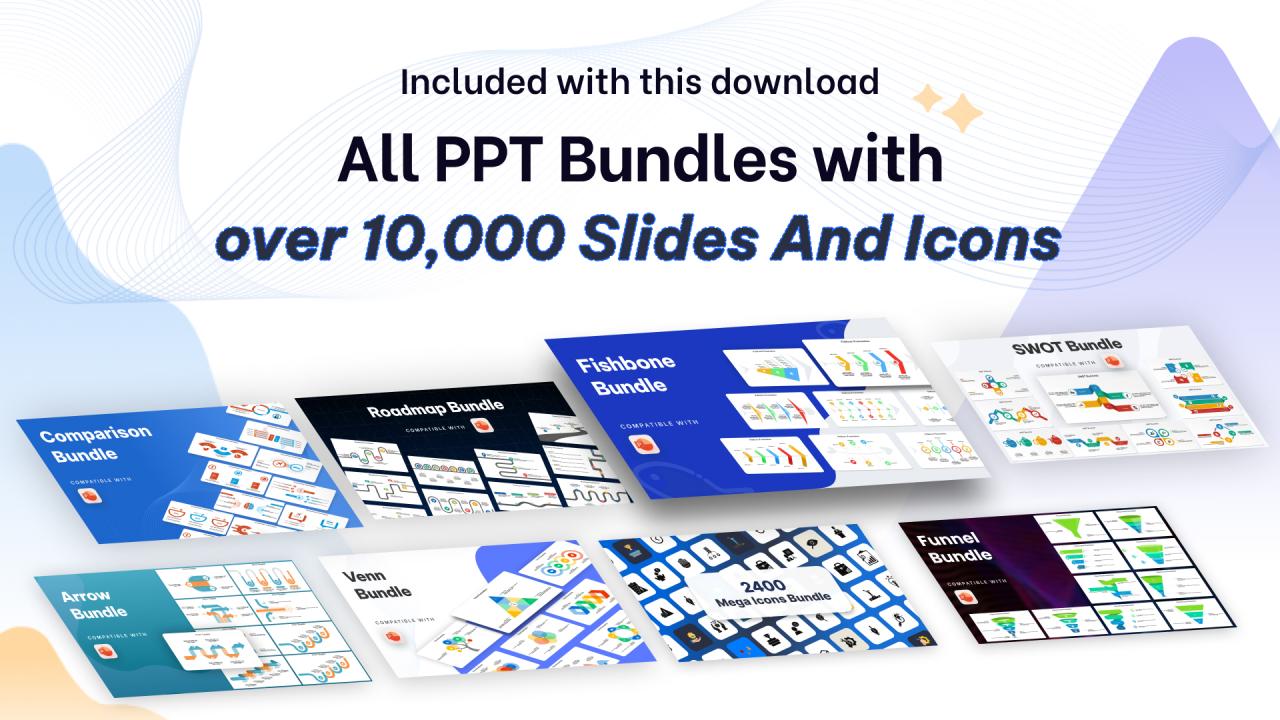
This slide shows main features of an effective IAM strategy. The purpose of this strategy is to highlight major components of IAM strategy. It include features such as provisioning identities, access security certification and security management , etc. Introducing our premium set of slides with Key Pillars Of Identification And Access Management Strategy. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identities, Certification, Management. So download instantly and tailor it with your information.
People who downloaded this PowerPoint presentation also viewed the following :
Key Pillars Of Identification And Access Management Strategy with all 6 slides:
Use our Key Pillars Of Identification And Access Management Strategy to effectively help you save your valuable time. They are readymade to fit into any presentation structure.
-
The design is clean-cut, modern, and sleek, keeping the users' needs in mind. The multiple uses make this product worth every penny!
-
Requested a complete pitch deck. Delivered immediately and with high quality well researched content.