Phishing Attacks And Strategies To Mitigate Them Powerpoint Presentation Slides
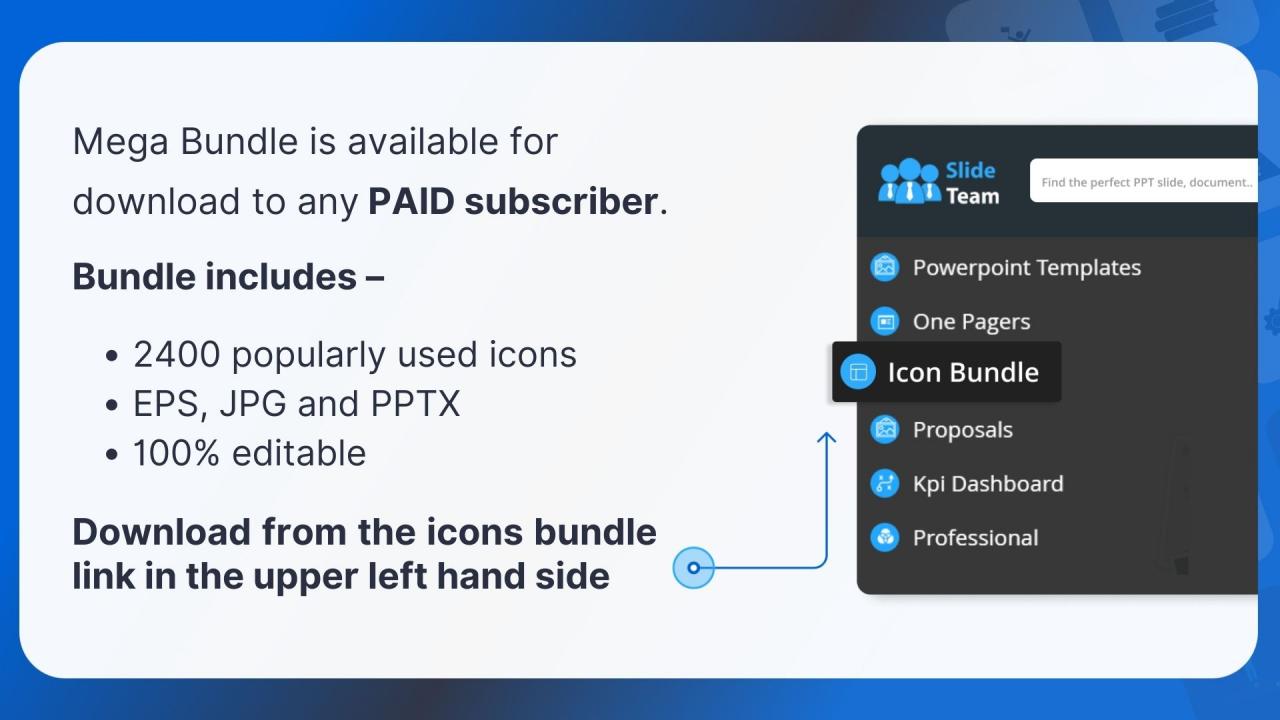
Our Phishing Attacks and Strategies to Mitigate them PowerPoint presentation focuses on phishing attacks, their impact on businesses, and strategies to mitigate them. It explains the working process of cyber phishing attacks. Additionally, the Smishing Attacks PPT delves into the various types of phishing attacks, such as email phishing, spear phishing, whale phishing, vishing, Smishing, angler phishing, pharming, pop-up phishing, clone phishing, Man-in-the-Middle attacks, evil twin scams, watering hole attacks, and search engine phishing. Each type is examined with insights into its distinctive techniques. Moreover, it includes an in-depth module on vishing attacks that explores identity theft and its tactics, presents a multi-layered approach to phishing defenses, and provides guidelines to safeguard against phishing scams effectively. Furthermore, the Spear Phishing deck focuses on phishing awareness training. It presents a well-structured plan to implement phishing awareness campaigns in organizations, along with valuable resources that companies can offer their employees to ensure protection from cybercrime. Lastly, the man-in-the-middle phishing deck incorporates a roadmap, a 30-60-90 days plan, a timeline, a checklist to secure organizations from phishing attacks, and a dashboard to track cyber-attacks efficiently. Get access to this 100 percent editable template now.
You must be logged in to download this presentation.
 Impress your
Impress your audience
Editable
of Time
PowerPoint presentation slides
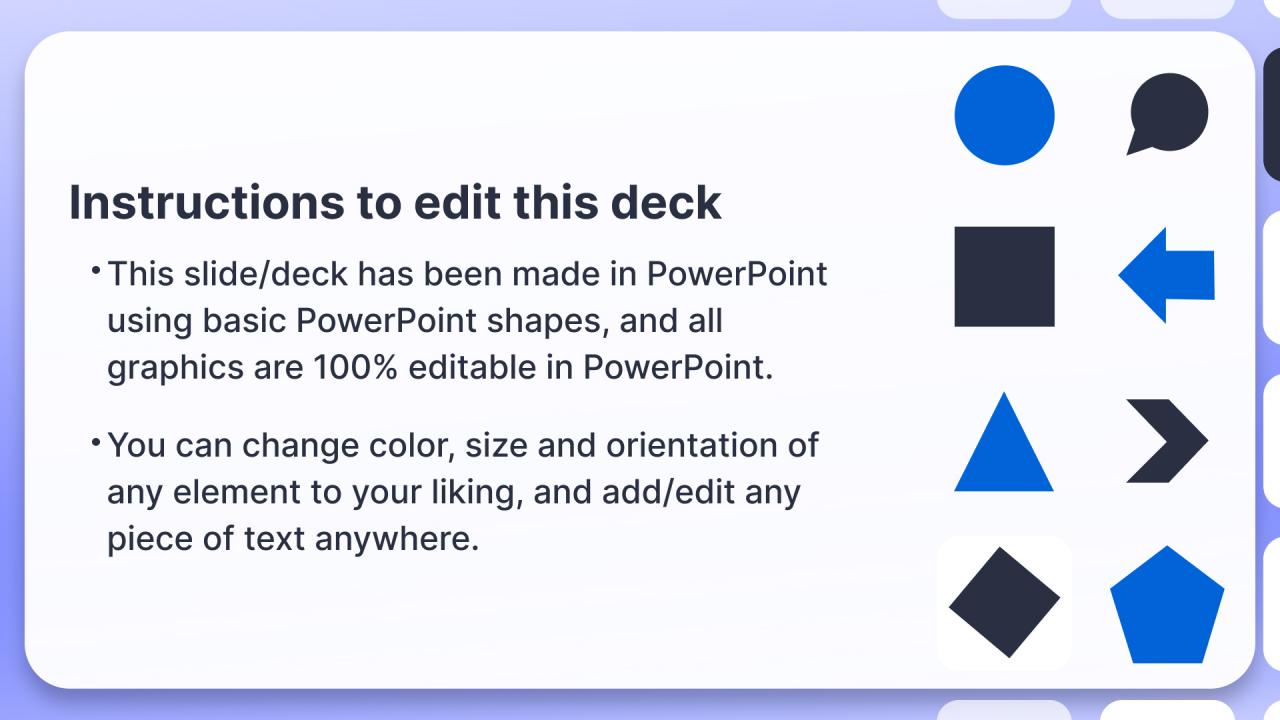
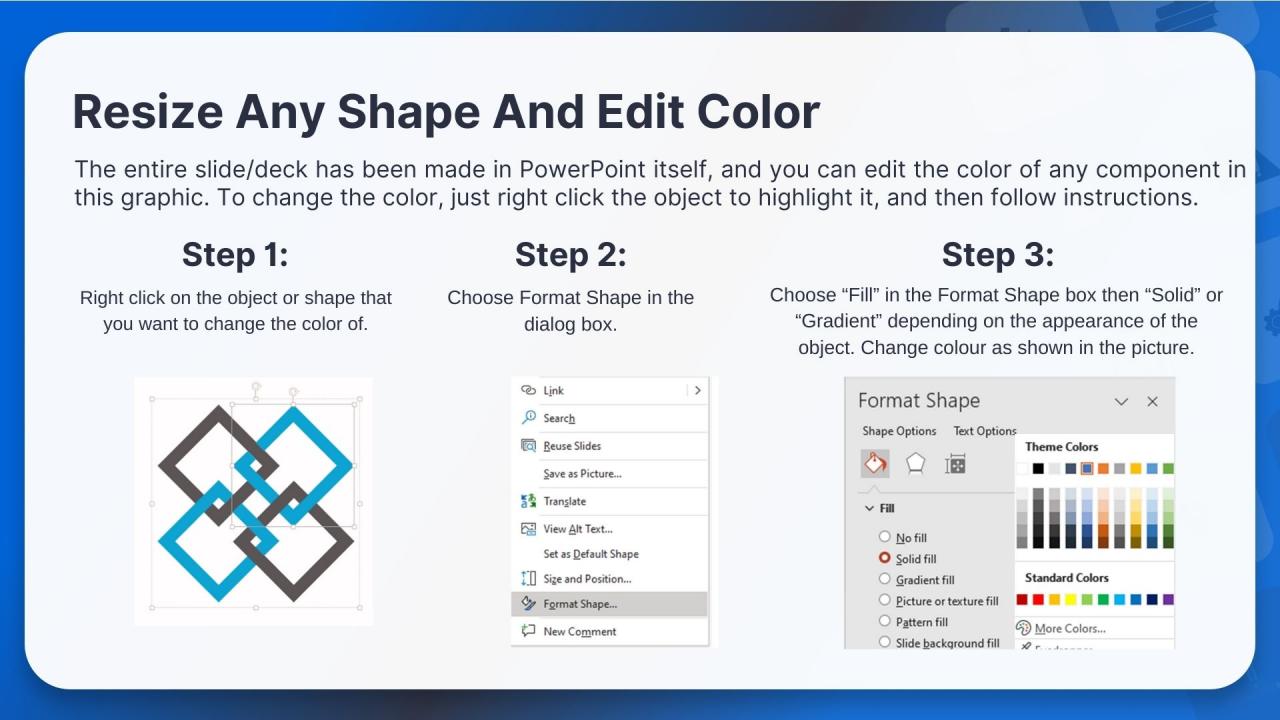
Deliver an informational PPT on various topics by using this Phishing Attacks And Strategies To Mitigate Them Powerpoint Presentation Slides. This deck focuses and implements best industry practices, thus providing a birds-eye view of the topic. Encompassed with one hundred one slides, designed using high-quality visuals and graphics, this deck is a complete package to use and download. All the slides offered in this deck are subjective to innumerable alterations, thus making you a pro at delivering and educating. You can modify the color of the graphics, background, or anything else as per your needs and requirements. It suits every business vertical because of its adaptable layout.
People who downloaded this PowerPoint presentation also viewed the following :
Content of this Powerpoint Presentation
Slide 1: This slide introduces Phishing Attacks and Strategies to Mitigate them. State your company name and begin.
Slide 2: This is an Agenda slide. State your agendas here.
Slide 3: This slide shows Table of Content for the presentation.
Slide 4: This slide continues showing Table of Content for the presentation.
Slide 5: This slide shows title for topics that are to be covered next in the template.
Slide 6: This slide demonstrates the overview of cyber phishing attacks and presents the effectiveness of phishing scams.
Slide 7: This slide describes the ways utilized by phishers to attack victims.
Slide 8: This slide presents the implementation and working of phishing attacks explaining how are cyber phishing scams conducted.
Slide 9: This slide demonstrates the working flow of a phishing attack it outlines various phases of phishing scams.
Slide 10: This slide outlines the amount of money lost by well-reputed companies due to phishing scams.
Slide 11: This slide explains the impact of phishing scams on organizations.
Slide 12: This slide also explains the impact of phishing scams on organizations.
Slide 13: This slide outlines the various reasons responsible for businesses to fall victim to different phishing attacks.
Slide 14: This slide represents the statistics of most targeted industries of phishing scams.
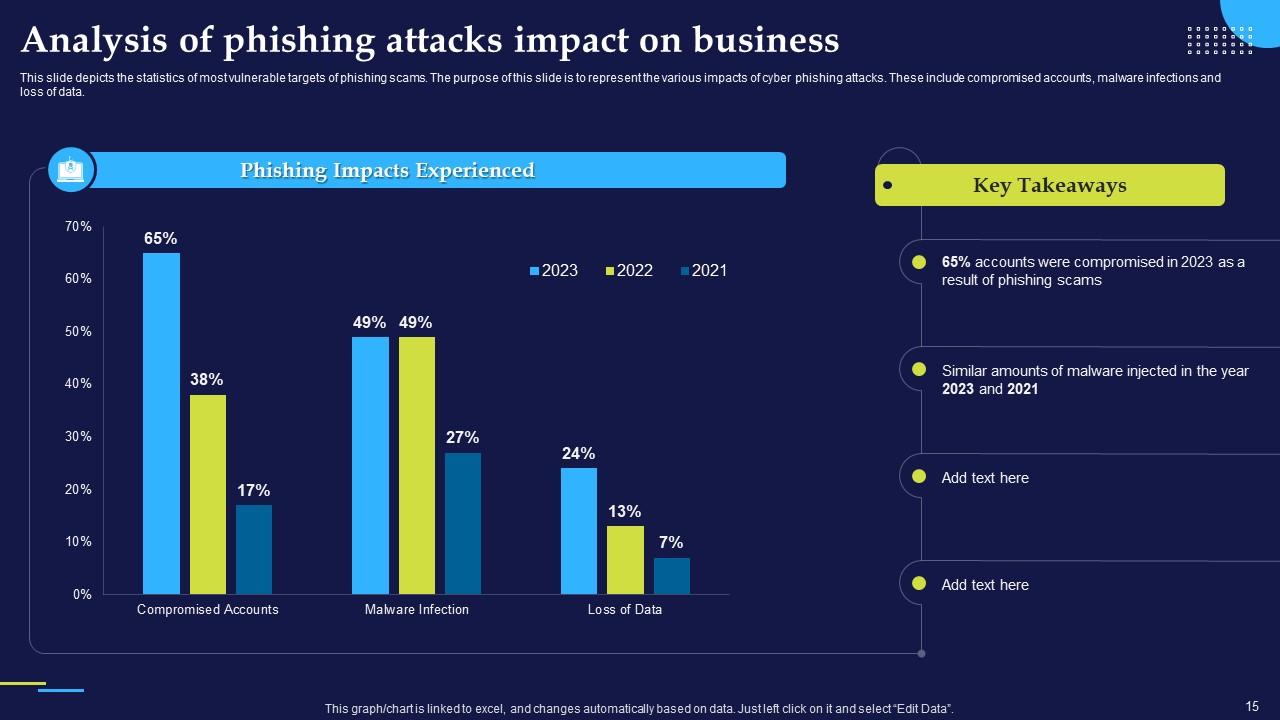
Slide 15: This slide depicts the statistics of most vulnerable targets of phishing scams.
Slide 16: This slide shows title for topics that are to be covered next in the template.
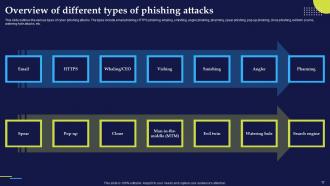
Slide 17: This slide outlines the various types of cyber phishing attacks including email phishing, HTTPS phishing, whaling and more.
Slide 18: This slide shows title for topics that are to be covered next in the template.
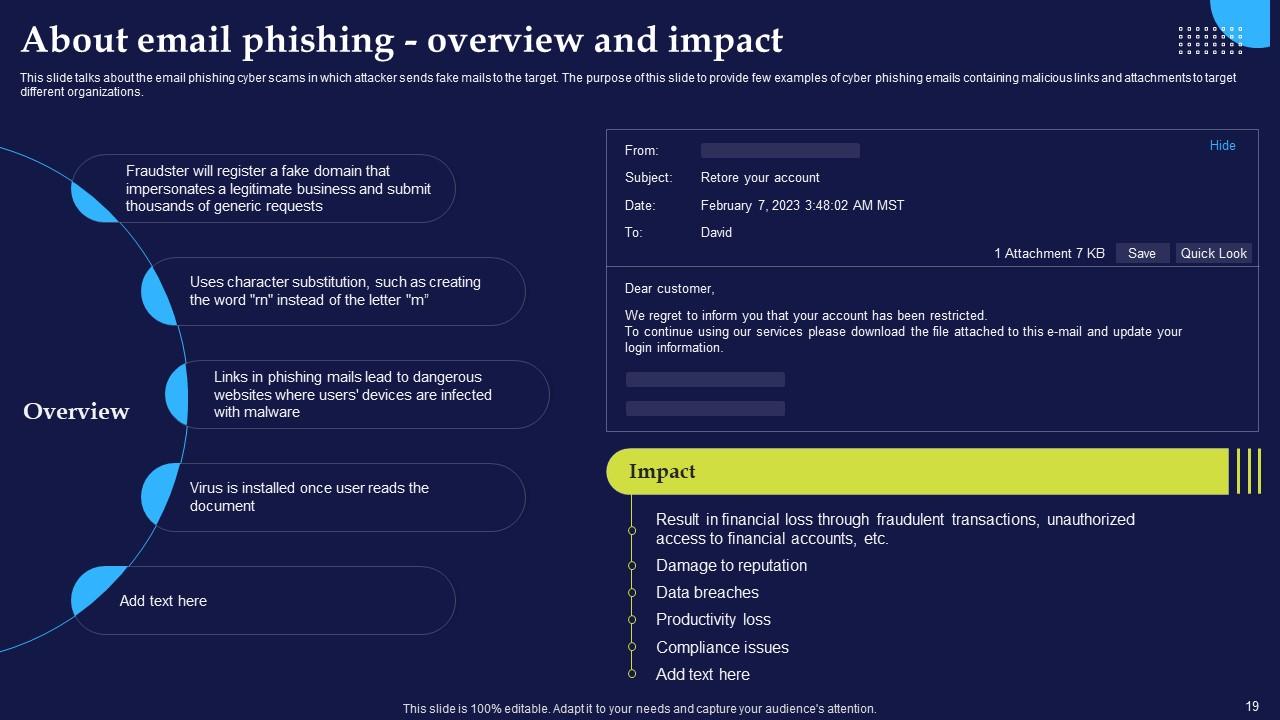
Slide 19: This slide presents an email phishing cyber scams in which attacker sends fake mails to the target.
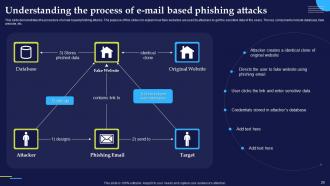
Slide 20: This slide demonstrates the procedure of email-based phishing attacks and explains how fake websites are used by attackers to get sensitive data.
Slide 21: This slide presents the warning signs that can help the user to recognize phishing email.
Slide 22: This slide shows title for topics that are to be covered next in the template.
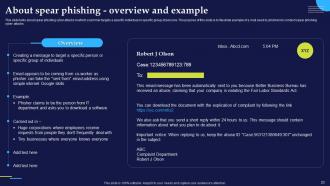
Slide 23: This slide presents spear phishing cyber attacks in which scammer targets a specific individual or specific group of persons.
Slide 24: This slide illustrates the structure of spear phishing attack and explains the working flow of spear phishing attack.
Slide 25: This slide presents various methods of identifying spear phishing cyber attacks
Slide 26: This slide illustrates the steps to be taken immediately after falling for a spear phishing scam.
Slide 27: This slide shows title for topics that are to be covered next in the template.
Slide 28: This slide presents the whaling phishing attack which is also known as CEO fraud.
Slide 29: This slide displays various methods of identifying whale phishing cyber attacks.
Slide 30: This slide shows title for topics that are to be covered next in the template.
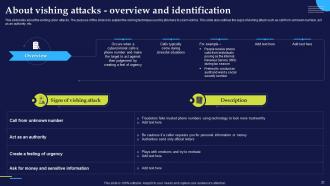
Slide 31: This slide presents the vishing cyber attacks and explains the vishing technique used by phishers to scam victims.
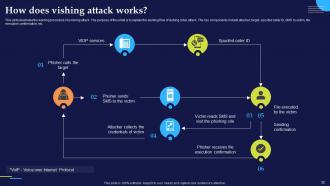
Slide 32: This slide illustrates the working procedure of a vishing attack and explains the working flow of vishing cyber attack.
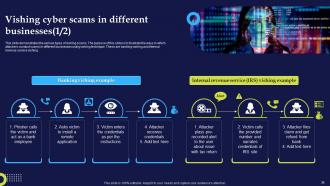
Slide 33: This slide presents the various types of vishing cyber attacks and explains different techniques of vishing scams used by the attackers to scam users.
Slide 34: This slide demonstrates the various types of vishing scams.
Slide 35: This slide also demonstrates the various types of vishing scams.
Slide 36: This slide presents the ways to protect users from vishing attacks.
Slide 37: This slide describes techniques which can help in protecting organizations from phishing and vishing attacks.
Slide 38: This slide shows title for topics that are to be covered next in the template.
Slide 39: This slide presents the smishing cyber attacks conducted by sending text messages to the targets.
Slide 40: This slide describes the various methods of identifying smishing cyber attacks.
Slide 41: This slide displays the various types of smishing cyber attacks.
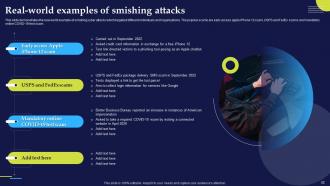
Slide 42: This slide demonstrates the real-world example of smishing cyber attacks which targeted different individuals and organizations.
Slide 43: This slide shows title for topics that are to be covered next in the template.
Slide 44: This slide presents the angler phishing attacks conducted on internet using social media platforms.
Slide 45: This slide displays the various methods of identifying angler phishing cyber attacks.
Slide 46: This slide shows title for topics that are to be covered next in the template.
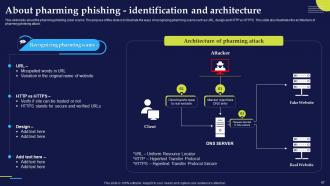
Slide 47: This slide presents the pharming phishing cyber scams and illustrate the ways of recognizing pharming scams such as URL, design and HTTP vs HTTPS.
Slide 48: This slide demonstrates the different types pf pharming phishing scams. The primary types include malware-based pharming and DNS pharming.
Slide 49: This slide shows title for topics that are to be covered next in the template.
Slide 50: This slide presents the pop-up phishing attacks conducted by sending pop-up messages to the targets.
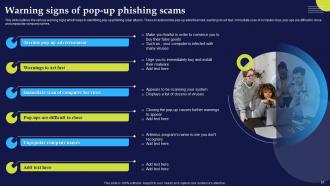
Slide 51: This slide outlines the various warning signs which helps in identifying pop-up phishing cyber attacks.
Slide 52: This slide shows title for topics that are to be covered next in the template.
Slide 53: This slide presents the clone phishing cyber attacks in which attacker sends duplicate mails to the organizations.
Slide 54: This slide demonstrates the various examples of clone phishing cyber scams.
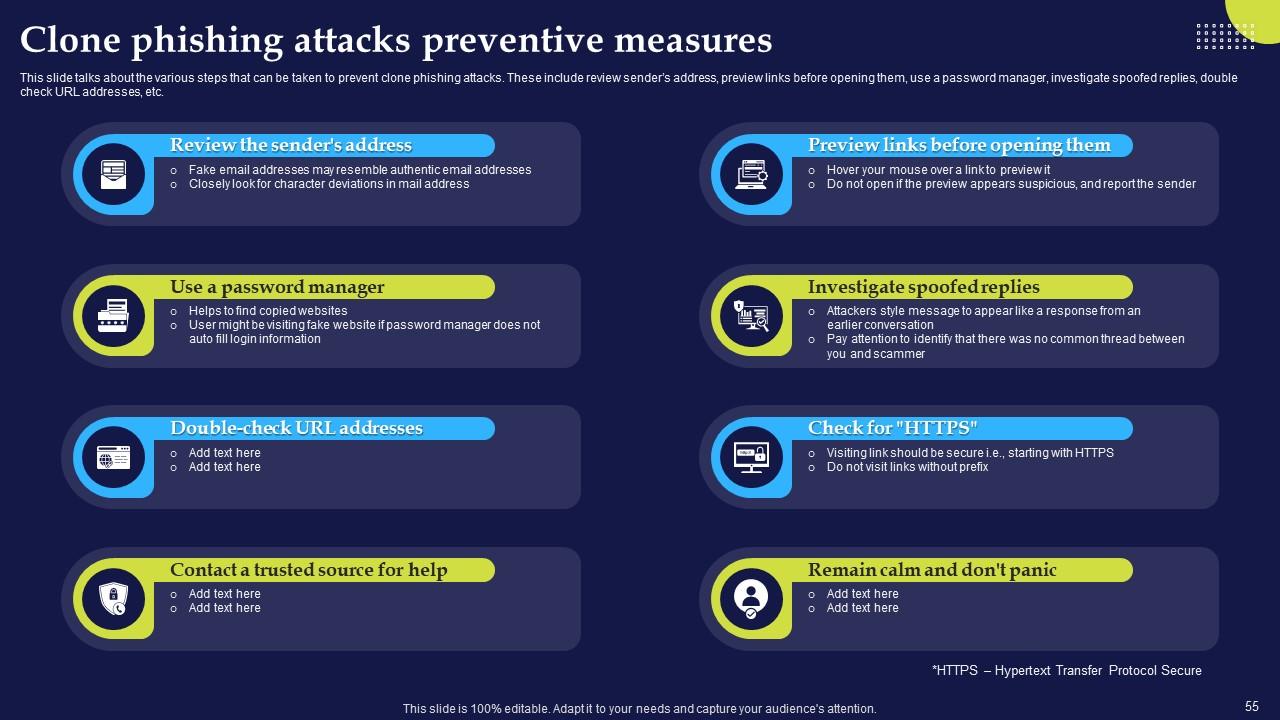
Slide 55: This slide displays the various steps that can be taken to prevent clone phishing attacks.
Slide 56: This slide shows title for topics that are to be covered next in the template.
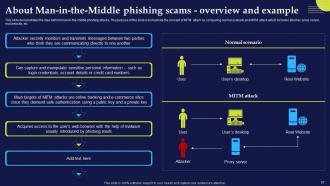
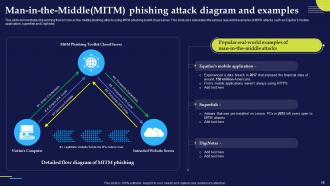
Slide 57: This slide demonstrates the idea behind man-in-the-middle phishing attacks.
Slide 58: This slide presents the working flow of man-in-the-middle phishing attacks using MITM phishing toolkit cloud server.
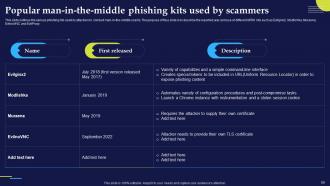
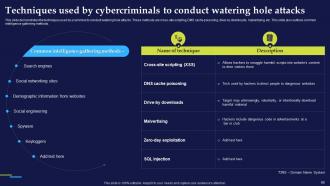
Slide 59: This slide outlines the various phishing kits used by attackers to conduct man-in-the-middle scams.
Slide 60: This slide illustrates the process of executing man-in-the-middle cyber attacks.
Slide 61: This slide outlines the various methods of preventing man-in-the-middle cyber attacks.
Slide 62: This slide shows title for topics that are to be covered next in the template.
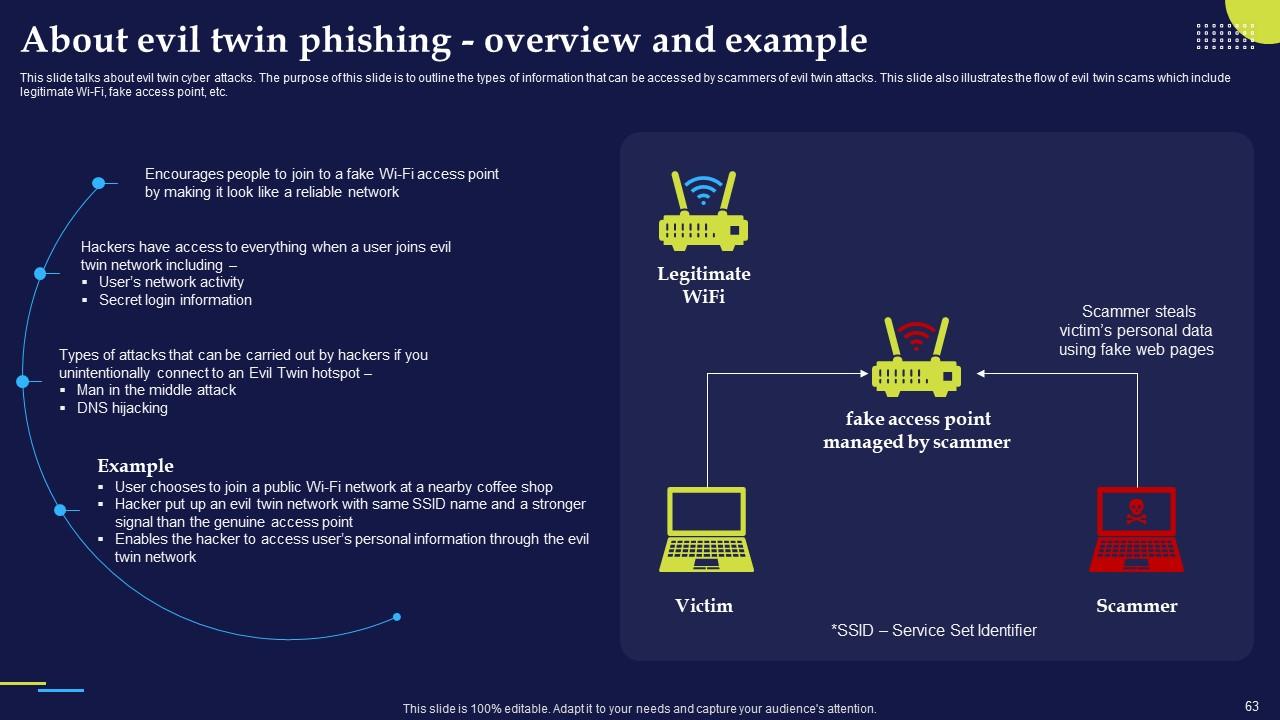
Slide 63: This slide presents evil twin cyber attacks and outlines the types of information that can be accessed by scammers of evil twin attacks.
Slide 64: This slide represents the working of evil twin phishing attacks.
Slide 65: This slide outlines the various preventive measures to avoid evil twin attacks.
Slide 66: This slide shows title for topics that are to be covered next in the template.
Slide 67: This slide presents the watering hole phishing attacks which trick the victim to do activities compromising their personal data.
Slide 68: This slide represents the working process of watering hole phishing attacks.
Slide 69: This slide demonstrates the techniques used by scammers to conduct watering hole attacks.
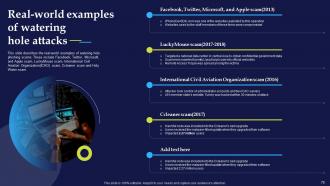
Slide 70: This slide describes the real-world examples of watering hole phishing scams.
Slide 71: This slide outlines the various preventive measures to avoid watering hole phishing attacks.
Slide 72: This slide shows title for topics that are to be covered next in the template.
Slide 73: This slide presents search engine phishing scams and explains how phishers use their own-built websites to trick victims.
Slide 74: This slide describes various tricks utilized by fraudulent websites to scam the visitors.
Slide 75: This slide shows title for topics that are to be covered next in the template.
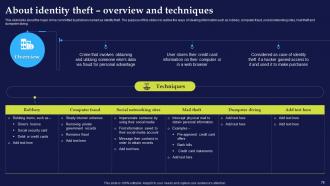
Slide 76: This slide presents major crime committed by phishers named as identity theft.
Slide 77: This slide shows title for topics that are to be covered next in the template.
Slide 78: This slide demonstrates the different tools provided by Google to prevent and report cyber phishing scams.
Slide 79: This slide shows title for topics that are to be covered next in the template.
Slide 80: This slide outlines the various preventive measures to stay safe from phishing attacks.
Slide 81: This slide shows title for topics that are to be covered next in the template.
Slide 82: This slide represents the multi-layered approach to phishing defenses.
Slide 83: This slide shows title for topics that are to be covered next in the template.
Slide 84: This slide demonstrates the resources and training that can be provided by companies to their staff.
Slide 85: This slide represents the training program for employees which will help them to prevent various cyber security scams in business.
Slide 86: This slide presents the working of phishing training programs for organizations.
Slide 87: This slide outlines the benefits of comprehensive training programs in organizations.
Slide 88: This slide presents the measures for successful phishing awareness campaign.
Slide 89: This slide shows title for topics that are to be covered next in the template.
Slide 90: This slide outlines the steps to be taken to protect the organization and its employees from phishing attacks.
Slide 91: This slide shows title for topics that are to be covered next in the template.
Slide 92: This slide represents 30-60-90 plan to protect companies and their employees from phishing attacks.
Slide 93: This slide shows title for topics that are to be covered next in the template.
Slide 94: This slide presents the timeline to protect organizations from phishing for different organizations.
Slide 95: This slide shows title for topics that are to be covered next in the template.
Slide 96: This slide represents the roadmap to prevent phishing attacks in organizations.
Slide 97: This slide shows title for topics that are to be covered next in the template.
Slide 98: This slide represents the dashboard to track cyber phishing attacks.
Slide 99: This slide also represents the dashboard to track cyber phishing attacks.
Slide 100: This slide shows all the icons included in the presentation.
Slide 101: This is a Thank You slide with address, contact numbers and email address.
Phishing Attacks And Strategies To Mitigate Them Powerpoint Presentation Slides with all 106 slides:
Use our Phishing Attacks And Strategies To Mitigate Them Powerpoint Presentation Slides to effectively help you save your valuable time. They are readymade to fit into any presentation structure.
FAQs
Phishing is a type of cyber attack where malicious actors impersonate legitimate entities to deceive individuals into revealing sensitive information, such as login credentials, credit card numbers, or personal data. This information is then used for fraudulent purposes.
Phishing attacks can occur through various channels, including email, text messages (SMS), phone calls, or even social media. Attackers often craft convincing messages or websites that appear genuine to trick victims into disclosing their sensitive information.
Common signs of a phishing attempt include misspelled URLs, generic or suspicious email addresses, urgent or threatening language, requests for personal or financial information, and unsolicited attachments or links. Always be cautious of unexpected communication.
To protect against phishing attacks, individuals should be cautious when interacting with unsolicited messages or requests. Verify the sender's identity, avoid clicking on suspicious links or downloading attachments from unknown sources, and regularly update passwords. Consider using security software and enabling multi-factor authentication (MFA) for added protection.
Organizations can defend against phishing attacks by implementing robust email filtering and security solutions, conducting regular employee training on recognizing phishing attempts, establishing incident response plans, and regularly patching and updating software to address vulnerabilities. Additionally, organizations should promote a culture of cybersecurity awareness among employees.
-
Unique research projects to present in meeting.
-
Time saving slide with creative ideas. Help a lot in quick presentations..