Risk Management PowerPoint Templates, Risk Management PPT Slides
- Sub Categories
-
- 30 60 90 Day Plan
- About Us Company Details
- Action Plan
- Agenda
- Annual Report
- Audit Reports
- Balance Scorecard
- Brand Equity
- Business Case Study
- Business Communication Skills
- Business Plan Development
- Business Problem Solving
- Business Review
- Capital Budgeting
- Career Planning
- Change Management
- Color Palettes
- Communication Process
- Company Location
- Company Vision
- Compare
- Competitive Analysis
- Corporate Governance
- Cost Reduction Strategies
- Custom Business Slides
- Customer Service
- Dashboard
- Data Management
- Decision Making
- Digital Marketing Strategy
- Digital Transformation
- Disaster Management
- Diversity
- Equity Investment
- Financial Analysis
- Financial Services
- Financials
- Growth Hacking Strategy
- Human Resource Management
- Innovation Management
- Interview Process
- Knowledge Management
- Leadership
- Lean Manufacturing
- Legal Law Order
- Management
- Market Segmentation
- Marketing
- Media and Communication
- Meeting Planner
- Mergers and Acquisitions
- Metaverse
- Newspapers
- Operations and Logistics
- Organizational Structure
- Our Goals
- Performance Management
- Pitch Decks
- Pricing Strategies
- Process Management
- Product Development
- Product Launch Ideas
- Product Portfolio
- Project Management
- Purchasing Process
- Quality Assurance
- Quotes and Testimonials
- Real Estate
- Risk Management
- Sales Performance Plan
- Sales Review
- SEO
- Service Offering
- Six Sigma
- Social Media and Network
- Software Development
- Solution Architecture
- Stock Portfolio
- Strategic Management
- Strategic Planning
- Supply Chain Management
- Swimlanes
- System Architecture
- Team Introduction
- Testing and Validation
- Thanks-FAQ
- Time Management
- Timelines Roadmaps
- Value Chain Analysis
- Value Stream Mapping
- Workplace Ethic
-
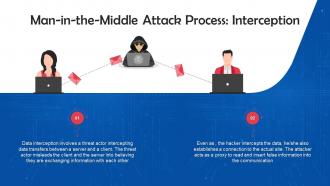 Interception Mode Of Executing Man In The Middle Attacks Training Ppt
Interception Mode Of Executing Man In The Middle Attacks Training PptPresenting Interception Mode of Executing Man in the Middle Attacks. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Decryption To Execute Man In The Middle Attacks Training Ppt
Decryption To Execute Man In The Middle Attacks Training PptPresenting Decryption to Execute Man-in-the-Middle Attacks. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Types Of Man In The Middle Attacks Training Ppt
Types Of Man In The Middle Attacks Training PptPresenting Working of Types of Man in the Middle Attacks. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 IP Spoofing As A Type Of Man In The Middle Attack Training Ppt
IP Spoofing As A Type Of Man In The Middle Attack Training PptPresenting IP Spoofing as a Type of Man in the Middle Attack. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 HTTP Spoofing As A Type Of Man In The Middle Attack Training Ppt
HTTP Spoofing As A Type Of Man In The Middle Attack Training PptPresenting HTTP Spoofing as a Type of Man in the Middle Attack. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 DNS Spoofing As A Type Of Man In The Middle Attack Training Ppt
DNS Spoofing As A Type Of Man In The Middle Attack Training PptPresenting DNS Spoofing as a Type of Man in the Middle Attack. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Email Spoofing As A Type Of Man In The Middle Attack Training Ppt
Email Spoofing As A Type Of Man In The Middle Attack Training PptPresenting Email Spoofing as a Type of Man in the Middle Attack. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 SSL Hijacking As A Type Of Man In The Middle Attack Training Ppt
SSL Hijacking As A Type Of Man In The Middle Attack Training PptPresenting SSL Hijacking as a Type of Man in the Middle Attack. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Session Hijacking As A Type Of Man In The Middle Attack Training Ppt
Session Hijacking As A Type Of Man In The Middle Attack Training PptPresenting Session Hijacking as a Type of Man in the Middle Attack. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Cache Poisoning As A Type Of Man In The Middle Attack Training Ppt
Cache Poisoning As A Type Of Man In The Middle Attack Training PptPresenting Cache Poisoning as a Type of Man in the Middle Attack. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Wi Fi Eavesdropping As A Type Of Man In The Middle Attack Training Ppt
Wi Fi Eavesdropping As A Type Of Man In The Middle Attack Training PptPresenting Wi-Fi Eavesdropping as a Type of Man in the Middle Attack. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
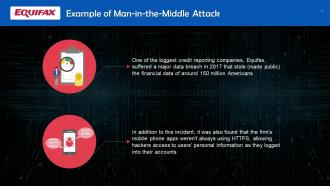 Example Of Man In The Middle Attack Training Ppt
Example Of Man In The Middle Attack Training PptPresenting Example of Man in the Middle Attack. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Prevention Of Man In The Middle Attacks Training Ppt
Prevention Of Man In The Middle Attacks Training PptPresenting Prevention of Man in the Middle Attacks. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Man In The Browser Attacks In Cybersecurity Training Ppt
Man In The Browser Attacks In Cybersecurity Training PptPresenting Man in the Browser Attacks in Cybersecurity. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
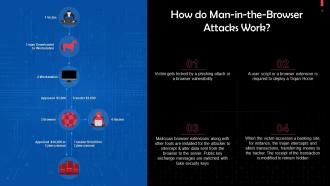 Working Of Man In The Browser Attacks Training Ppt
Working Of Man In The Browser Attacks Training PptPresenting Working of Man in the Browser Attacks. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Examples Of Man In The Browser Attacks Training Ppt
Examples Of Man In The Browser Attacks Training PptPresenting Examples of Man in the Browser Attacks. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Zeus As A Man In The Browser Attack Training Ppt
Zeus As A Man In The Browser Attack Training PptPresenting Zeus as a Man in the Browser Attack. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 SpyEye As A Man In The Browser Attack Training Ppt
SpyEye As A Man In The Browser Attack Training PptPresenting SpyEye as a Man in the Browser Attack. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 OddJob As A Man In The Browser Attack Training Ppt
OddJob As A Man In The Browser Attack Training PptPresenting OddJob as a Man in the Browser Attack. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Key Signs Of Man In The Browser Attacks Training Ppt
Key Signs Of Man In The Browser Attacks Training PptPresenting Key Signs of Man-in-the-Browser Attacks. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Preventing Man In The Browser Attacks Training Ppt
Preventing Man In The Browser Attacks Training PptPresenting Preventing Man-in-the-Browser Attacks. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Spyware Cyber Attack In Cybersecurity Training Ppt
Spyware Cyber Attack In Cybersecurity Training PptPresenting Spyware Cyber Attack in Cybersecurity. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Overview Of Working Of Spyware Training Ppt
Overview Of Working Of Spyware Training PptPresenting Overview of Working of Spyware. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Ways Spyware Infections Can Occur Training Ppt
Ways Spyware Infections Can Occur Training PptPresenting Ways Spyware Infections can Occur. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Different Types Of Spyware Infections Training Ppt
Different Types Of Spyware Infections Training PptPresenting Different Types of Spyware Infections. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
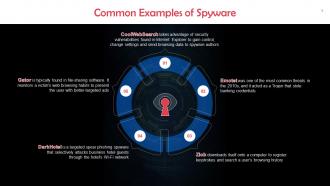 Common Examples Of Spyware Infections Training Ppt
Common Examples Of Spyware Infections Training PptPresenting Common Examples of Spyware Infections. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Ways To Prevent Spyware Infections Training Ppt
Ways To Prevent Spyware Infections Training PptPresenting Ways to Prevent Spyware Infections. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
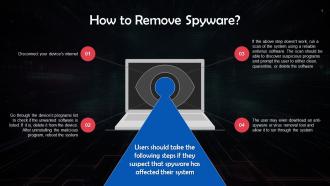 Ways To Remove Spyware Infections Training Ppt
Ways To Remove Spyware Infections Training PptPresenting Ways to Remove Spyware Infections. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Anti Spyware Tools In Cybersecurity Training Ppt
Anti Spyware Tools In Cybersecurity Training PptPresenting Anti Spyware Tools in Cybersecurity. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 The Social Engineering Life Cycle Training Ppt
The Social Engineering Life Cycle Training PptPresenting The Social Engineering Life Cycle. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Baiting As A Social Engineering Technique Training Ppt
Baiting As A Social Engineering Technique Training PptPresenting Baiting as a Social Engineering Technique . This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Pretexting As A Social Engineering Technique Training Ppt
Pretexting As A Social Engineering Technique Training PptPresenting Pretexting as a Social Engineering Technique. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Scareware As A Social Engineering Technique Training Ppt
Scareware As A Social Engineering Technique Training PptPresenting Scareware as a Social Engineering Technique. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Phishing As A Social Engineering Technique Training Ppt
Phishing As A Social Engineering Technique Training PptPresenting Phishing as a Social Engineering Technique. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Watering Hole Attack As A Social Engineering Technique Training Ppt
Watering Hole Attack As A Social Engineering Technique Training PptPresenting Watering Hole Attack as a Social Engineering Technique. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Access Tailgating As A Social Engineering Technique Training Ppt
Access Tailgating As A Social Engineering Technique Training PptPresenting Access Tailgating as a Social Engineering Technique. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Overview Of Unusual Social Engineering Techniques Training Ppt
Overview Of Unusual Social Engineering Techniques Training PptPresenting Overview of Unusual Social Engineering Techniques. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Fax Based Phishing For Social Engineering Training Ppt
Fax Based Phishing For Social Engineering Training PptPresenting Fax Based Phishing for Social Engineering. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Traditional Mail Malware Distribution For Social Engineering Training Ppt
Traditional Mail Malware Distribution For Social Engineering Training PptPresenting Traditional Mail Malware Distribution for Social Engineering. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
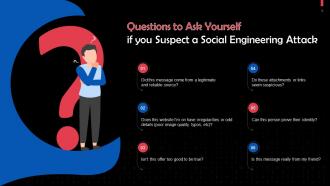 Questions To Ask Yourself If You Suspect A Social Engineering Attack Training Ppt
Questions To Ask Yourself If You Suspect A Social Engineering Attack Training PptPresenting Questions to Ask Yourself if you Suspect a Social Engineering Attack. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Ransomware Attacks In Cybersecurity Training Ppt
Ransomware Attacks In Cybersecurity Training PptPresenting Ransomware Attacks in Cybersecurity. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
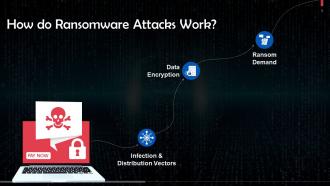 Overview Of Working Of Ransomware Attacks Training Ppt
Overview Of Working Of Ransomware Attacks Training PptPresenting Overview of Working of Ransomware Attacks. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Infection And Distribution Vectors In Ransomware Attacks Training Ppt
Infection And Distribution Vectors In Ransomware Attacks Training PptPresenting Infection and Distribution Vectors in Ransomware Attacks. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
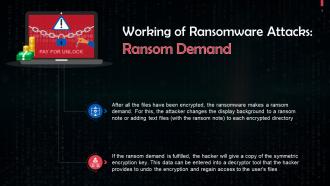 Demand Of Ransom In Ransomware Attacks Training Ppt
Demand Of Ransom In Ransomware Attacks Training PptPresenting Demand of Ransom in Ransomware Attacks. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Overview Of Protection Against Ransomware Attacks Training Ppt
Overview Of Protection Against Ransomware Attacks Training PptPresenting Overview of Protection Against Ransomware Attacks. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
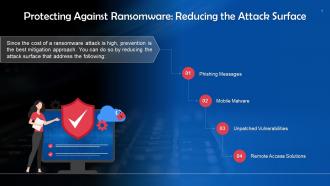 Reducing The Attack Surface To Protect Against Ransomware Attacks Training Ppt
Reducing The Attack Surface To Protect Against Ransomware Attacks Training PptPresenting Reducing the Attack Surface to Protect Against Ransomware Attacks. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Importance Of Deploying Anti Ransomware Solutions Training Ppt
Importance Of Deploying Anti Ransomware Solutions Training PptPresenting Importance of Deploying Anti Ransomware Solutions. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Steps To Remove An Active Ransomware Infection Training Ppt
Steps To Remove An Active Ransomware Infection Training PptPresenting Steps to Remove an Active Ransomware Infection. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Key Statistics On Ransomware Attacks Training Ppt
Key Statistics On Ransomware Attacks Training PptPresenting Key Statistics on Ransomware Attacks. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Trojan Horses In Cybersecurity Training Ppt
Trojan Horses In Cybersecurity Training PptPresenting Trojan Horses in Cybersecurity. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Overview Of Working Of Trojan Horses Training Ppt
Overview Of Working Of Trojan Horses Training PptPresenting Overview of Working of Trojan Horses. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Effect Of Trojan Horse On A System Training Ppt
Effect Of Trojan Horse On A System Training PptPresenting Effect of Trojan Horse on a System. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Is Trojan Horse A Virus Or A Malware Training Ppt
Is Trojan Horse A Virus Or A Malware Training PptPresenting Is Trojan Horse a Virus or a Malware. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
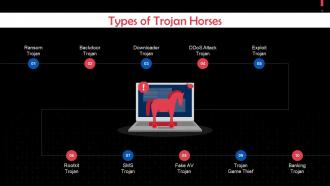 Types Of Trojan Horses Training Ppt
Types Of Trojan Horses Training PptPresenting Types of Trojan Horses. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Common Examples Of Trojan Horses Training Ppt
Common Examples Of Trojan Horses Training PptPresenting Common Examples of Trojan Horses. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
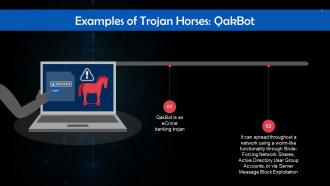 QakBot As An Example Of Trojan Horse Training Ppt
QakBot As An Example Of Trojan Horse Training PptPresenting QakBot as an Example of Trojan Horse. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Andromeda As An Example Of Trojan Horse Training Ppt
Andromeda As An Example Of Trojan Horse Training PptPresenting Andromeda as an Example of Trojan Horse. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Night Spider Zloader As An Example Of Trojan Horse Training Ppt
Night Spider Zloader As An Example Of Trojan Horse Training PptPresenting Night Spider Zloader as an Example of Trojan Horse . This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
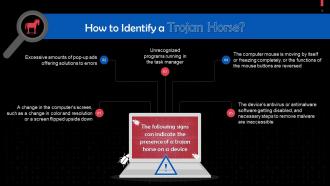 Tips To Identify A Trojan Horse Training Ppt
Tips To Identify A Trojan Horse Training PptPresenting Tips to Identify a Trojan Horse. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Protection Against A Trojan Horse Attack Training Ppt
Protection Against A Trojan Horse Attack Training PptPresenting Protection Against a Trojan Horse Attack. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.




