Powerpoint Templates and Google slides for Access To Data Analytics And AI
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
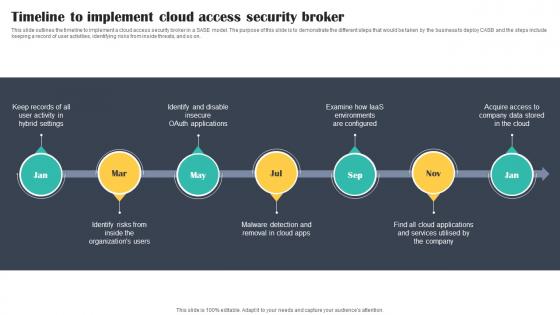 Timeline To Implement Cloud Access Security Broker Cloud Security Model
Timeline To Implement Cloud Access Security Broker Cloud Security ModelThis slide outlines the timeline to implement a cloud access security broker in a SASE model. The purpose of this slide is to demonstrate the different steps that would be taken by the business to deploy CASB and the steps include keeping a record of user activities, identifying risks from inside threats, and so on. Introducing Timeline To Implement Cloud Access Security Broker Cloud Security Model to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Activity, Identify, Removal, using this template. Grab it now to reap its full benefits.
-
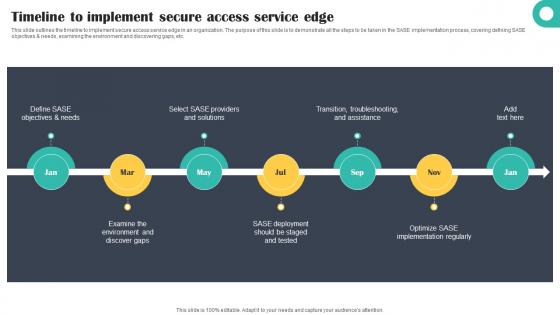 Timeline To Implement Secure Access Service Edge Cloud Security Model
Timeline To Implement Secure Access Service Edge Cloud Security ModelThis slide outlines the timeline to implement secure access service edge in an organization. The purpose of this slide is to demonstrate all the steps to be taken in the SASE implementation process, covering defining SASE objectives and needs, examining the environment and discovering gaps, etc. Increase audience engagement and knowledge by dispensing information using Timeline To Implement Secure Access Service Edge Cloud Security Model. This template helps you present information on seven stages. You can also present information on Objectives, Solutions, Deployment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Openai Api Everything You Need Procedure To Access ChatGPT 4 And ChatGPT 3 APIs ChatGPT SS V
Openai Api Everything You Need Procedure To Access ChatGPT 4 And ChatGPT 3 APIs ChatGPT SS VThis slide showcases process to get access key for OpenAIs ChatGPT-3 and ChatGPT-4 APIs which companies can use as a guide to get easy login and signup procedure. It provides details about client library, installation, switching, etc. Introducing Openai Api Everything You Need Procedure To Access ChatGPT 4 And ChatGPT 3 APIs ChatGPT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Client Library, Installation, Switching, Natural Language Processing, using this template. Grab it now to reap its full benefits.
-
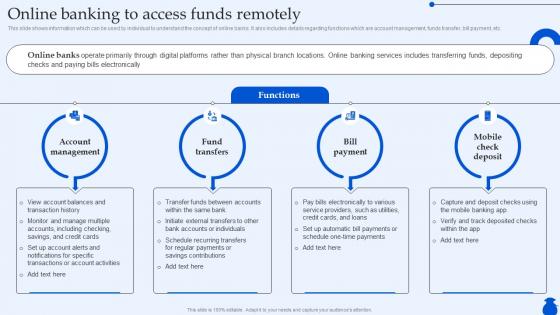 Online Banking To Access Funds Remotely Ultimate Guide To Commercial Fin SS
Online Banking To Access Funds Remotely Ultimate Guide To Commercial Fin SSThis slide shows information which can be used by individual to understand the concept of online banks. It also includes details regarding functions which are account management, funds transfer, bill payment, etc. Introducing Online Banking To Access Funds Remotely Ultimate Guide To Commercial Fin SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Account Management, Fund Transfers, using this template. Grab it now to reap its full benefits.
-
 Fair Access to Healthcare AI Image PowerPoint Presentation PPT ECS
Fair Access to Healthcare AI Image PowerPoint Presentation PPT ECSIntroducing a Visual PPT on Fair Access to Healthcare. Our Presentation Specialists have taken great care in designing each slide in this PowerPoint. Feel free to tailor the content. The PPT Template fits well with any screen size, and it?s also compatible with Google Slides. Download the PPT, and present it confidently.
-
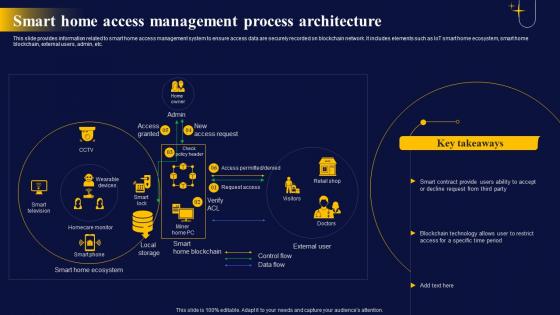 Smart Home Access Management The Ultimate Guide To Blockchain Integration IoT SS
Smart Home Access Management The Ultimate Guide To Blockchain Integration IoT SSThis slide provides information related to smart home access management system to ensure access data are securely recorded on blockchain network. It includes elements such as IoT smart home ecosystem, smart home blockchain, external users, admin, etc. Deliver an outstanding presentation on the topic using this Smart Home Access Management The Ultimate Guide To Blockchain Integration IoT SS. Dispense information and present a thorough explanation of Access, Management, Process using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
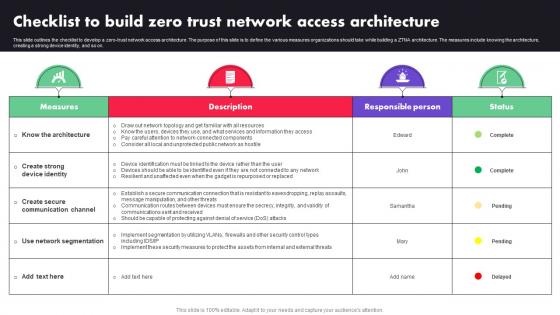 Checklist To Build Zero Trust Network Access Architecture Ppt Diagram Lists
Checklist To Build Zero Trust Network Access Architecture Ppt Diagram ListsThis slide outlines the checklist to develop a zero-trust network access architecture. The purpose of this slide is to define the various measures organizations should take while building a ZTNA architecture. The measures include knowing the architecture, creating a strong device identity, and so on. Deliver an outstanding presentation on the topic using this Checklist To Build Zero Trust Network Access Architecture Ppt Diagram Lists. Dispense information and present a thorough explanation of Public Network, Network Topology, Devices using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
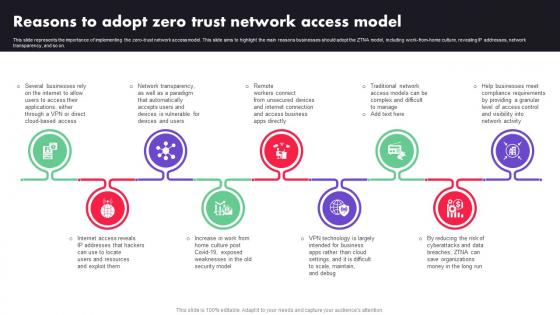 Reasons To Adopt Zero Trust Network Access Model Zero Trust Architecture ZTA
Reasons To Adopt Zero Trust Network Access Model Zero Trust Architecture ZTAThis slide represents the importance of implementing the zero-trust network access model. This slide aims to highlight the main reasons businesses should adopt the ZTNA model, including work-from-home culture, revealing IP addresses, network transparency, and so on. Introducing Reasons To Adopt Zero Trust Network Access Model Zero Trust Architecture ZTA to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Traditional Network, Apps Directly, VPN, using this template. Grab it now to reap its full benefits.
-
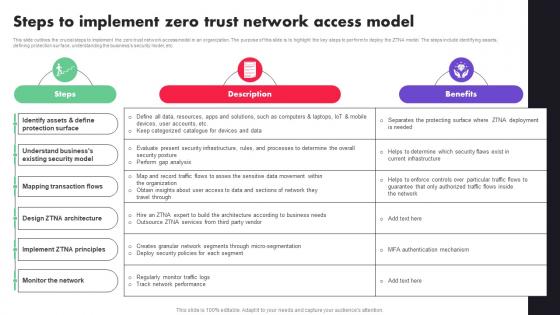 Steps To Implement Zero Trust Network Access Model Zero Trust Architecture ZTA
Steps To Implement Zero Trust Network Access Model Zero Trust Architecture ZTAThis slide outlines the crucial steps to implement the zero trust network access model in an organization. The purpose of this slide is to highlight the key steps to perform to deploy the ZTNA model. The steps include identifying assets, defining protection surface, understanding the businesss security model, etc. Present the topic in a bit more detail with this Steps To Implement Zero Trust Network Access Model Zero Trust Architecture ZTA. Use it as a tool for discussion and navigation on Protection Surface, Security Model, Mapping Transaction Flows. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
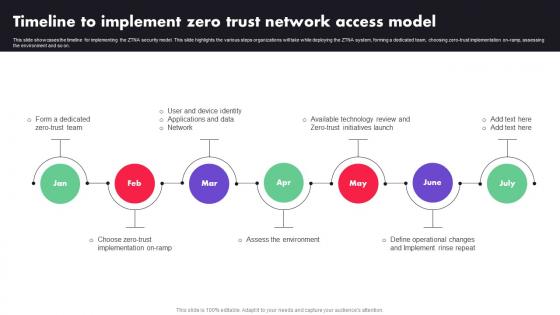 Timeline To Implement Zero Trust Network Access Model Ppt File Designs
Timeline To Implement Zero Trust Network Access Model Ppt File DesignsThis slide showcases the timeline for implementing the ZTNA security model. This slide highlights the various steps organizations will take while deploying the ZTNA system, forming a dedicated team, choosing zero-trust implementation on-ramp, assessing the environment and so on. Introducing Timeline To Implement Zero Trust Network Access Model Ppt File Designs to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Zero Trust Team, Network, Applications, using this template. Grab it now to reap its full benefits.
-
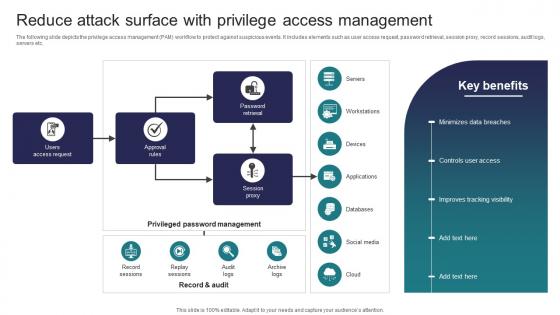 Implementing Strategies To Mitigate Cyber Security Reduce Attack Surface With Privilege Access Management
Implementing Strategies To Mitigate Cyber Security Reduce Attack Surface With Privilege Access ManagementThe following slide depicts the privilege access management PAM workflow to protect against suspicious events. It includes elements such as user access request, password retrieval, session proxy, record sessions, audit logs, servers etc. Present the topic in a bit more detail with this Implementing Strategies To Mitigate Cyber Security Reduce Attack Surface With Privilege Access Management Use it as a tool for discussion and navigation on Access Request, Approval Rules, Session Proxy This template is free to edit as deemed fit for your organization. Therefore download it now.
-
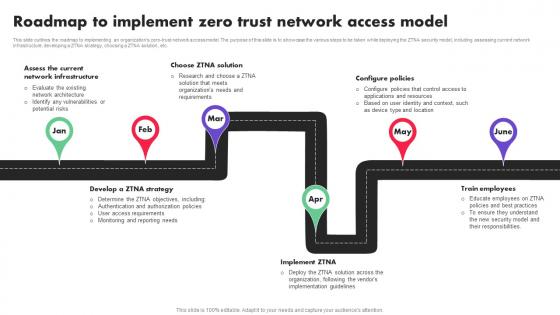 Zero Trust Architecture ZTA Roadmap To Implement Zero Trust Network Access Model
Zero Trust Architecture ZTA Roadmap To Implement Zero Trust Network Access ModelThis slide outlines the roadmap to implementing an organizations zero-trust network access model. The purpose of this slide is to showcase the various steps to be taken while deploying the ZTNA security model, including assessing current network infrastructure, developing a ZTNA strategy, choosing a ZTNA solution, etc. Introducing Zero Trust Architecture ZTA Roadmap To Implement Zero Trust Network Access Model to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Network Infrastructure, Ztna Solution, Configure Policies, using this template. Grab it now to reap its full benefits.
-
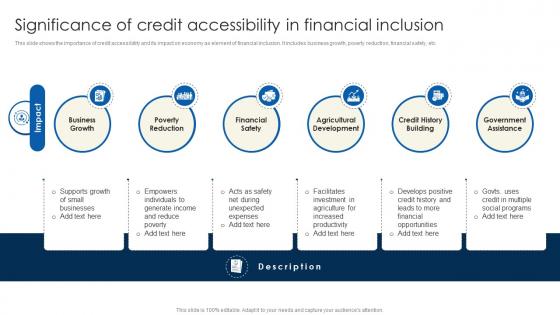 Significance Of Credit Accessibility Financial Inclusion To Promote Economic Fin SS
Significance Of Credit Accessibility Financial Inclusion To Promote Economic Fin SSThis slide shows the importance of credit accessibility and its impact on economy as element of financial inclusion. It includes business growth, poverty reduction, financial safety, etc. Introducing Significance Of Credit Accessibility Financial Inclusion To Promote Economic Fin SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Government Assistance, Poverty Reduction, Business Growth, using this template. Grab it now to reap its full benefits.
-
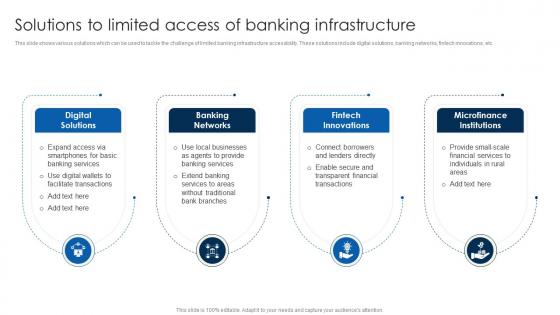 Solutions To Limited Access Of Banking Financial Inclusion To Promote Economic Fin SS
Solutions To Limited Access Of Banking Financial Inclusion To Promote Economic Fin SSThis slide shows various solutions which can be used to tackle the challenge of limited banking infrastructure accessibility. These solutions include digital solutions, banking networks, fintech innovations, etc. Introducing Solutions To Limited Access Of Banking Financial Inclusion To Promote Economic Fin SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Microfinance Institutions, Fintech Innovations, Banking Networks, using this template. Grab it now to reap its full benefits.
-
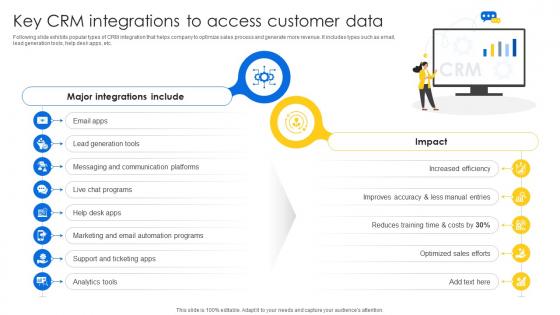 Key CRM Integrations To Access Sales CRM Unlocking Efficiency And Growth SA SS
Key CRM Integrations To Access Sales CRM Unlocking Efficiency And Growth SA SSFollowing slide exhibits popular types of CRM integration that helps company to optimize sales process and generate more revenue. It includes types such as email, lead generation tools, help desk apps, etc. Introducing Key CRM Integrations To Access Sales CRM Unlocking Efficiency And Growth SA SS to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Generation Tools, Communication Platforms, Chat Programs, using this template. Grab it now to reap its full benefits.
-
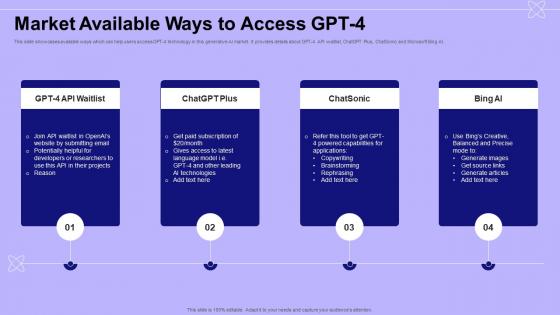 Market Available Ways To Access GPT 4 Introduction To GPT 4 ChatGPT SS
Market Available Ways To Access GPT 4 Introduction To GPT 4 ChatGPT SSThis slide showcases available ways which can help users access GPT-4 technology in this generative AI market. It provides details about GPT-4 API waitlist, ChatGPT Plus, ChatSonic and Microsoft Bing AI. Introducing Market Available Ways To Access GPT 4 Introduction To GPT 4 ChatGPT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Chatsonic, Plus, Bing, using this template. Grab it now to reap its full benefits.
-
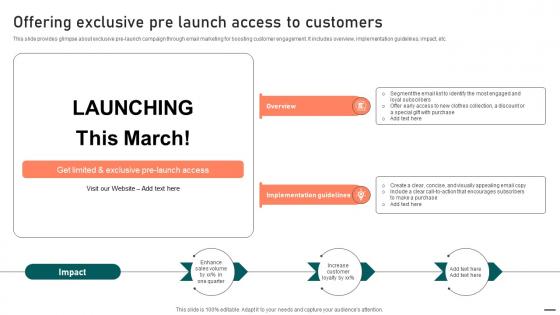 Offering Exclusive Pre Launch Access To Customers Guide To Boost Brand Exposure Strategy SS V
Offering Exclusive Pre Launch Access To Customers Guide To Boost Brand Exposure Strategy SS VThis slide provides glimpse about exclusive pre-launch campaign through email marketing for boosting customer engagement. It includes overview, implementation guidelines, impact, etc. Increase audience engagement and knowledge by dispensing information using Offering Exclusive Pre Launch Access To Customers Guide To Boost Brand Exposure Strategy SS V. This template helps you present information on two stages. You can also present information on Overview, Implementation Guidelines using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
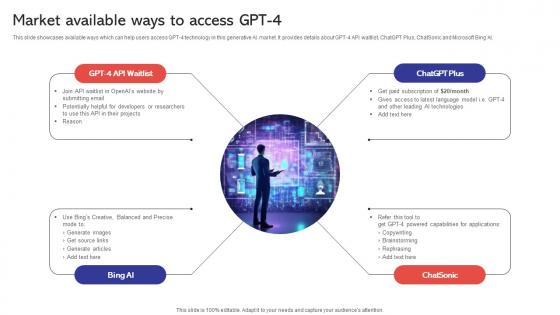 Market Available Ways To Access GPT 4 Capabilities And Use Cases Of GPT4 ChatGPT SS V
Market Available Ways To Access GPT 4 Capabilities And Use Cases Of GPT4 ChatGPT SS VThis slide showcases available ways which can help users access GPT 4 technology in this generative AI market. It provides details about GPT 4 API waitlist, ChatGPT Plus, ChatSonic and Microsoft Bing AI. Introducing Market Available Ways To Access GPT 4 Capabilities And Use Cases Of GPT4 ChatGPT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Email, Developers, Subscription, using this template. Grab it now to reap its full benefits.
-
 Sase Model Approaches To Implement Zero Trust Network Access
Sase Model Approaches To Implement Zero Trust Network AccessThis slide depicts the two primary approaches to implementing zero-trust network access for organizations. The purpose of this slide is to showcase the endpoint-initiated and service-initiated approach of zero-trust network access. It also includes how users access business services and applications in both approaches. Introducing Sase Model Approaches To Implement Zero Trust Network Access to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Service Initiated, Endpoint Initiated, using this template. Grab it now to reap its full benefits.
-
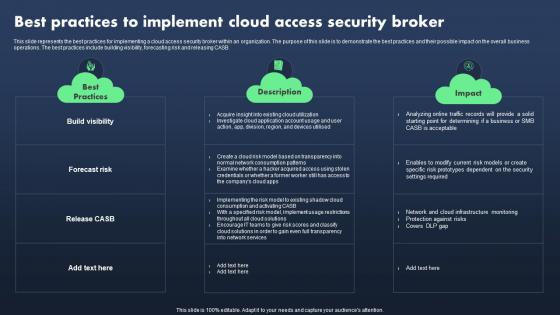 Sase Model Best Practices To Implement Cloud Access Security Broker
Sase Model Best Practices To Implement Cloud Access Security BrokerThis slide represents the best practices for implementing a cloud access security broker within an organization. The purpose of this slide is to demonstrate the best practices and their possible impact on the overall business operations. The best practices include building visibility, forecasting risk and releasing CASB. Present the topic in a bit more detail with this Sase Model Best Practices To Implement Cloud Access Security Broker. Use it as a tool for discussion and navigation on Best Practices, Description, Impact. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Sase Model Budget To Implement Secure Access Service Edge
Sase Model Budget To Implement Secure Access Service EdgeThis slide depicts the budget calculation for implementing a secure access service edge model in an organization. The purpose of this slide is to showcase the estimated and actual cost and variance for SASE model spending. The key components include SD-WAN, SWG, ZTNA, CASB, and FWaaS. Deliver an outstanding presentation on the topic using this Sase Model Budget To Implement Secure Access Service Edge. Dispense information and present a thorough explanation of Components, Estimated Cost, Actual Cost using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Sase Model Checklist To Implement Secure Access Service Edge
Sase Model Checklist To Implement Secure Access Service EdgeDeliver an outstanding presentation on the topic using this Sase Model Checklist To Implement Secure Access Service Edge. Dispense information and present a thorough explanation of Steps, Responsible Person, Status using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Sase Model Introduction To Secure Access Service Edge Sase
Sase Model Introduction To Secure Access Service Edge SaseThis slide represents the introduction of SASE cloud security technology. The purpose of this slide is to demonstrate the core capabilities, benefits and key components of SASE. The key components include SD-WAN, FWaaS, ZTNA, CASB, SWG, and unified management. Present the topic in a bit more detail with this Sase Model Introduction To Secure Access Service Edge Sase. Use it as a tool for discussion and navigation on Key Components, Benefits. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
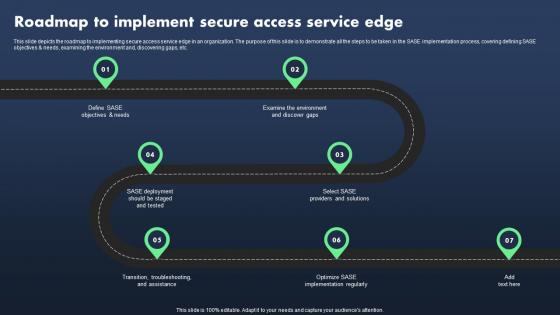 Sase Model Roadmap To Implement Secure Access Service Edge
Sase Model Roadmap To Implement Secure Access Service EdgeThis slide depicts the roadmap to implementing secure access service edge in an organization. The purpose of this slide is to demonstrate all the steps to be taken in the SASE implementation process, covering defining SASE objectives and needs, examining the environment and, discovering gaps, etc. Introducing Sase Model Roadmap To Implement Secure Access Service Edge to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Examine The Environment, Providers And Solutions, Implementation Regularly, using this template. Grab it now to reap its full benefits.
-
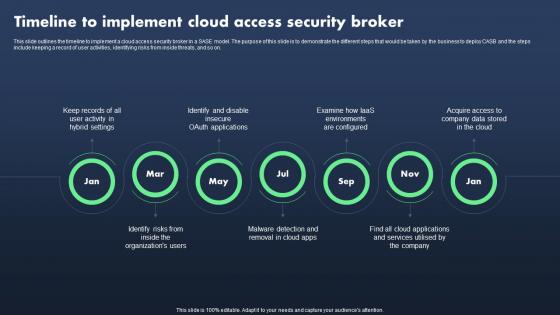 Sase Model Timeline To Implement Cloud Access Security Broker
Sase Model Timeline To Implement Cloud Access Security BrokerThis slide outlines the timeline to implement a cloud access security broker in a SASE model. The purpose of this slide is to demonstrate the different steps that would be taken by the business to deploy CASB and the steps include keeping a record of user activities, identifying risks from inside threats, and so on. Increase audience engagement and knowledge by dispensing information using Sase Model Timeline To Implement Cloud Access Security Broker. This template helps you present information on seven stages. You can also present information on Hybrid Settings, Environments Are Configured, Cloud App using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
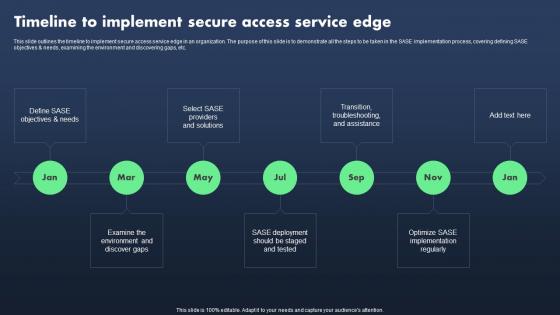 Sase Model Timeline To Implement Secure Access Service Edge
Sase Model Timeline To Implement Secure Access Service EdgeThis slide outlines the timeline to implement secure access service edge in an organization. The purpose of this slide is to demonstrate all the steps to be taken in the SASE implementation process, covering defining SASE objectives and needs, examining the environment and discovering gaps, etc. Introducing Sase Model Timeline To Implement Secure Access Service Edge to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Jan, Mar, May, Jul, using this template. Grab it now to reap its full benefits.
-
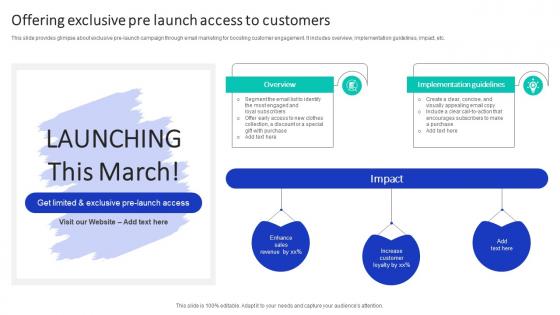 Offering Exclusive Pre Launch Access To Efficient Marketing Campaign Plan Strategy SS V
Offering Exclusive Pre Launch Access To Efficient Marketing Campaign Plan Strategy SS VThis slide provides glimpse about exclusive pre launch campaign through email marketing for boosting customer engagement. It includes overview, implementation guidelines, impact, etc. Increase audience engagement and knowledge by dispensing information using Offering Exclusive Pre Launch Access To Efficient Marketing Campaign Plan Strategy SS V. This template helps you present information on three stages. You can also present information on Enhance, Revenue, Customer using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
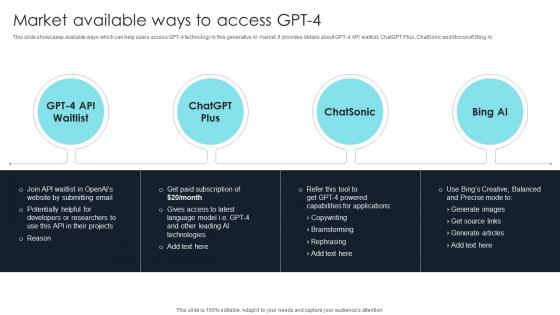 How To Use Gpt4 For Your Business Market Available Ways To Access Gpt 4 ChatGPT SS V
How To Use Gpt4 For Your Business Market Available Ways To Access Gpt 4 ChatGPT SS VThis slide showcases available ways which can help users access GPT-4 technology in this generative AI market. It provides details about GPT-4 API waitlist, ChatGPT Plus, ChatSonic and Microsoft Bing AI. Present the topic in a bit more detail with this How To Use Gpt4 For Your Business Market Available Ways To Access Gpt 4 ChatGPT SS V. Use it as a tool for discussion and navigation on Potentially, Applications, Technologies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Market Available Ways To Access Gpt 4 Gpt 4 Everything You Need To Know ChatGPT SS V
Market Available Ways To Access Gpt 4 Gpt 4 Everything You Need To Know ChatGPT SS VThis slide showcases available ways which can help users access GPT-4 technology in this generative AI market. It provides details about GPT-4 API waitlist, ChatGPT Plus, ChatSonic and Microsoft Bing AI. Increase audience engagement and knowledge by dispensing information using Market Available Ways To Access Gpt 4 Gpt 4 Everything You Need To Know ChatGPT SS V. This template helps you present information on four stages. You can also present information on Potentially, Applications, Technologies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Checklist To Build Zero Trust Network Access Architecture Identity Defined Networking
Checklist To Build Zero Trust Network Access Architecture Identity Defined NetworkingThis slide outlines the checklist to develop a zero-trust network access architecture. The purpose of this slide is to define the various measures organizations should take while building a ZTNA architecture. The measures include knowing the architecture, creating a strong device identity, and so on. Deliver an outstanding presentation on the topic using this Checklist To Build Zero Trust Network Access Architecture Identity Defined Networking Dispense information and present a thorough explanation of Device Identity, Communication Channel, Network Segmentation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
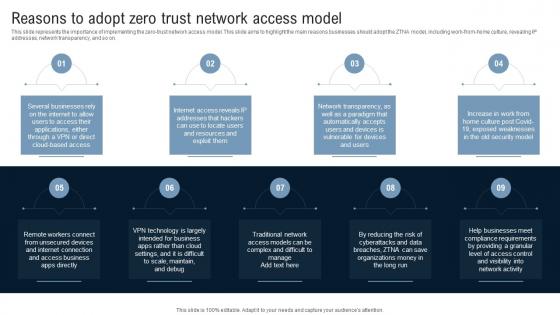 Reasons To Adopt Zero Trust Network Access Model Identity Defined Networking
Reasons To Adopt Zero Trust Network Access Model Identity Defined NetworkingThis slide represents the importance of implementing the zero-trust network access model. This slide aims to highlight the main reasons businesses should adopt the ZTNA model, including work-from-home culture, revealing IP addresses, network transparency, and so on. Introducing Reasons To Adopt Zero Trust Network Access Model Identity Defined Networking to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Devices, Access Business, Network Activity using this template. Grab it now to reap its full benefits.
-
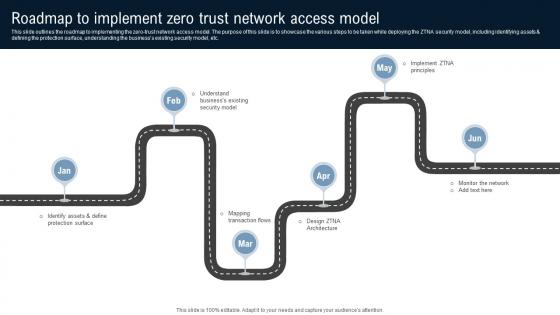 Roadmap To Implement Zero Trust Network Access Model Identity Defined Networking
Roadmap To Implement Zero Trust Network Access Model Identity Defined NetworkingThis slide outlines the roadmap to implementing the zero-trust network access model. The purpose of this slide is to showcase the various steps to be taken while deploying the ZTNA security model, including identifying assets and defining the protection surface, understanding the businesss existing security model, etc. Introducing Roadmap To Implement Zero Trust Network Access Model Identity Defined Networking to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Architecture, Monitor The Network, Businesss Existing using this template. Grab it now to reap its full benefits.
-
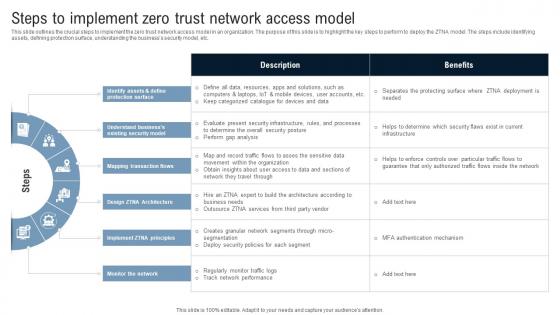 Steps To Implement Zero Trust Network Access Model Identity Defined Networking
Steps To Implement Zero Trust Network Access Model Identity Defined NetworkingThis slide outlines the crucial steps to implement the zero trust network access model in an organization. The purpose of this slide is to highlight the key steps to perform to deploy the ZTNA model. The steps include identifying assets, defining protection surface, understanding the businesss security model, etc. Present the topic in a bit more detail with this Steps To Implement Zero Trust Network Access Model Identity Defined Networking Use it as a tool for discussion and navigation on Mapping Transaction, Monitor The Network, Protection Surface This template is free to edit as deemed fit for your organization. Therefore download it now.
-
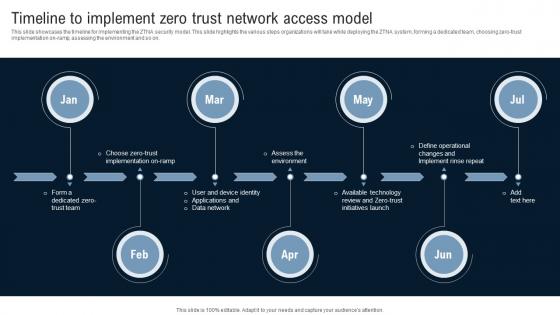 Timeline To Implement Zero Trust Network Access Model Identity Defined Networking
Timeline To Implement Zero Trust Network Access Model Identity Defined NetworkingThis slide showcases the timeline for implementing the ZTNA security model. This slide highlights the various steps organizations will take while deploying the ZTNA system, forming a dedicated team, choosing zero-trust implementation on-ramp, assessing the environment and so on. Introducing Timeline To Implement Zero Trust Network Access Model Identity Defined Networking to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Assess The Environment, Data Network, Timeline using this template. Grab it now to reap its full benefits.
-
 Market Available Ways To Access GPT 4 How To Use GPT4 For Content Writing ChatGPT SS V
Market Available Ways To Access GPT 4 How To Use GPT4 For Content Writing ChatGPT SS VThis slide showcases available ways which can help users access GPT-4 technology in this generative AI market. It provides details about GPT-4 API waitlist, ChatGPT Plus, ChatSonic and Microsoft Bing AI. Introducing Market Available Ways To Access GPT 4 How To Use GPT4 For Content Writing ChatGPT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Waitlist, Chatsonic, Bing, using this template. Grab it now to reap its full benefits.
-
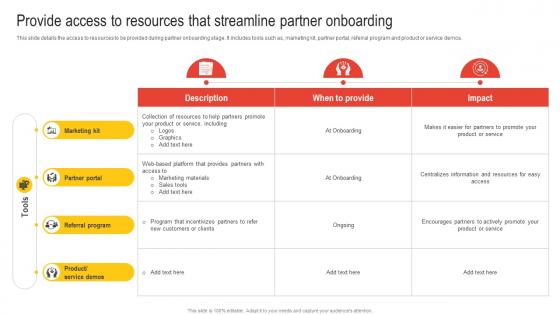 Provide Access To Resources That Streamline Partner Onboarding Nurturing Relationships
Provide Access To Resources That Streamline Partner Onboarding Nurturing RelationshipsThis slide details the access to resources to be provided during partner onboarding stage. It includes tools such as, marketing kit, partner portal, referral program and product or service demos. Deliver an outstanding presentation on the topic using this Provide Access To Resources That Streamline Partner Onboarding Nurturing Relationships Dispense information and present a thorough explanation of Marketing Kit, Partner Portal, Referral Program using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
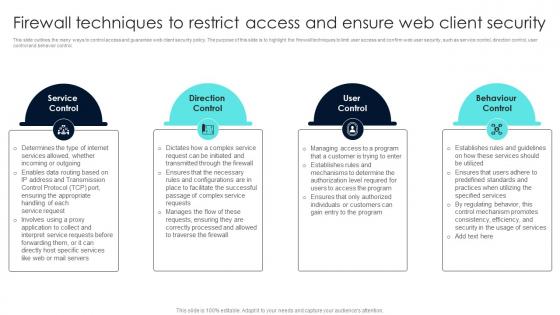 Firewall Network Security Firewall Techniques To Restrict Access And Ensure Web Client Security
Firewall Network Security Firewall Techniques To Restrict Access And Ensure Web Client SecurityThis slide outlines the many ways to control access and guarantee web client security policy. The purpose of this slide is to highlight the firewall techniques to limit user access and confirm web user security, such as service control, direction control, user control and behavior control. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Firewall Techniques To Restrict Access And Ensure Web Client Security This template helps you present information on Four stages. You can also present information on Market By Deployment, Market By Solution using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
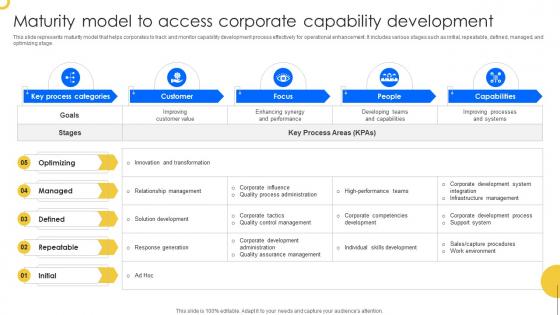 Maturity Model To Access Corporate Capability Development
Maturity Model To Access Corporate Capability DevelopmentThis slide represents maturity model that helps corporates to track and monitor capability development process effectively for operational enhancement. It includes various stages such as initial, repeatable, defined, managed, and optimizing stage. Introducing our Maturity Model To Access Corporate Capability Development set of slides. The topics discussed in these slides are Optimizing, Managed, Repeatable. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Best Practices To Implement Cloud Access Security Broker Next Generation CASB
Best Practices To Implement Cloud Access Security Broker Next Generation CASBThis slide represents the best practices for implementing a cloud access security broker within an organization. The purpose of this slide is to demonstrate the best practices and their possible impact on the overall business operations. The best practices include building visibility, forecasting risk and releasing CASB. Deliver an outstanding presentation on the topic using this Best Practices To Implement Cloud Access Security Broker Next Generation CASB Dispense information and present a thorough explanation of Build Visibility, Forecast Risk, Release CASB, Best Practices using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
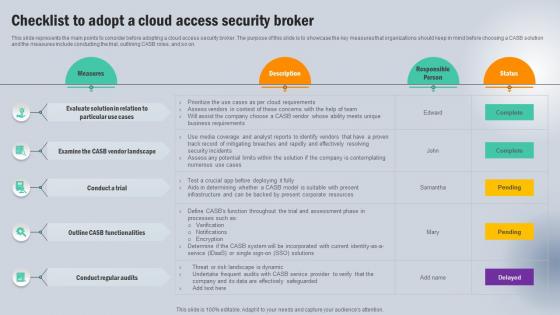 Checklist To Adopt A Cloud Access Security Broker Next Generation CASB
Checklist To Adopt A Cloud Access Security Broker Next Generation CASBThis slide represents the main points to consider before adopting a cloud access security broker. The purpose of this slide is to showcase the key measures that organizations should keep in mind before choosing a CASB solution and the measures include conducting the trial, outlining CASB roles, and so on. Deliver an outstanding presentation on the topic using this Checklist To Adopt A Cloud Access Security Broker Next Generation CASB Dispense information and present a thorough explanation of Vendor Landscape, Conduct A Trial, Functionalities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Steps To Deploy Cloud Access Security Broker Next Generation CASB
Steps To Deploy Cloud Access Security Broker Next Generation CASBThis slide outlines the steps to implement a cloud access security broker in an organization. The purpose of this slide is to showcase the various steps to keep in mind while deploying a CASB model into a business and the steps include the deployment path, deployment model and releasing model. Introducing Steps To Deploy Cloud Access Security Broker Next Generation CASB to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Deployment Location, Deployment Model, Release Model using this template. Grab it now to reap its full benefits.
-
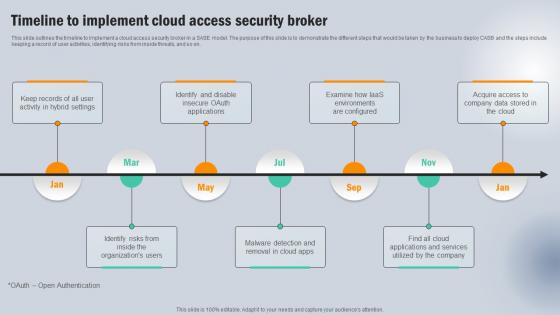 Timeline To Implement Cloud Access Security Broker Next Generation CASB
Timeline To Implement Cloud Access Security Broker Next Generation CASBThis slide outlines the timeline to implement a cloud access security broker in a SASE model. The purpose of this slide is to demonstrate the different steps that would be taken by the business to deploy CASB and the steps include keeping a record of user activities, identifying risks from inside threats, and so on. Introducing Timeline To Implement Cloud Access Security Broker Next Generation CASB to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Acquire Access , Company, Applications And Services using this template. Grab it now to reap its full benefits.
-
 Application Security Implementation Plan Steps To Deploy Efficient Access Control
Application Security Implementation Plan Steps To Deploy Efficient Access ControlThis slide discusses the process phases of implementing access control which include taking inventory of systems, examining staffs, etc. Introducing Application Security Implementation Plan Steps To Deploy Efficient Access Control to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Establish Roles, Resist Sporadic Adjustments, Examine The Staff, Take Inventory Of Systems, using this template. Grab it now to reap its full benefits.
-
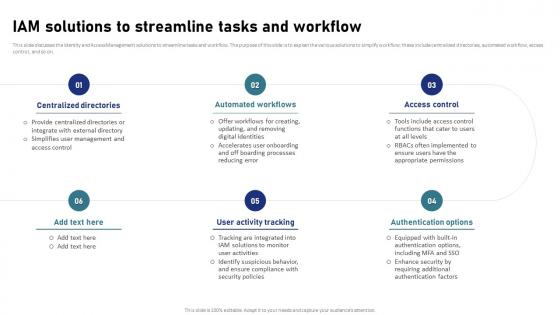 IAM Process For Effective Access IAM Solutions To Streamline Tasks And Workflow
IAM Process For Effective Access IAM Solutions To Streamline Tasks And WorkflowThis slide discusses the Identity and Access Management solutions to streamline tasks and workflow. The purpose of this slide is to explain the various solutions to simplify workflow these include centralized directories, automated workflow, access control, and so on. Increase audience engagement and knowledge by dispensing information using IAM Process For Effective Access IAM Solutions To Streamline Tasks And Workflow. This template helps you present information on six stages. You can also present information on Centralized Directories, Automated Workflows, Authentication Options using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
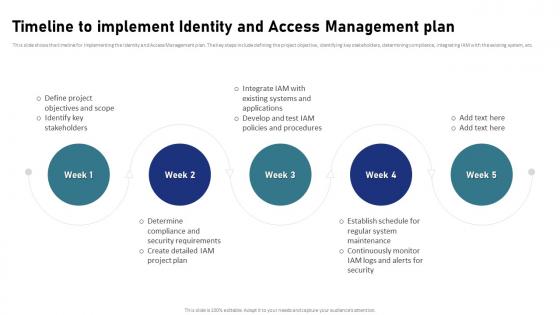 IAM Process For Effective Access Timeline To Implement Identity And Access Management Plan
IAM Process For Effective Access Timeline To Implement Identity And Access Management PlanThis slide shows the timeline for implementing the Identity and Access Management plan. The key steps include defining the project objective, identifying key stakeholders, determining compliance, integrating IAM with the existing system, etc. Introducing IAM Process For Effective Access Timeline To Implement Identity And Access Management Plan to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Timeline To Implement Identity, Access Management Plan, Regular System Maintenance, using this template. Grab it now to reap its full benefits.
-
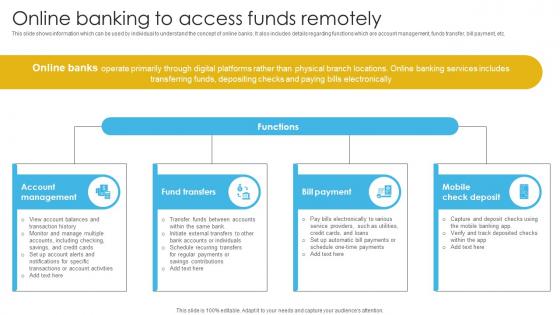 Complete Guide To Commercial Online Banking To Access Funds Remotely Fin SS V
Complete Guide To Commercial Online Banking To Access Funds Remotely Fin SS VThis slide shows information which can be used by individual to understand the concept of online banks. It also includes details regarding functions which are account management, funds transfer, bill payment, etc. Introducing Complete Guide To Commercial Online Banking To Access Funds Remotely Fin SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Account Management, Bill Payment, Mobile Check Deposit, Fund Transfers, using this template. Grab it now to reap its full benefits.
-
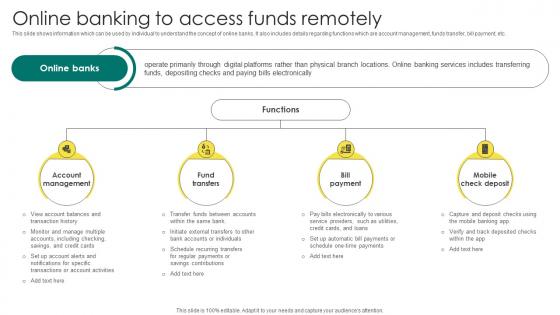 Everything About Commercial Banking Online Banking To Access Funds Remotely Fin SS V
Everything About Commercial Banking Online Banking To Access Funds Remotely Fin SS VThis slide shows information which can be used by individual to understand the concept of online banks. It also includes details regarding functions which are account management, funds transfer, bill payment, etc. Increase audience engagement and knowledge by dispensing information using Everything About Commercial Banking Online Banking To Access Funds Remotely Fin SS V. This template helps you present information on four stages. You can also present information on Account Management, Fund Transfers, Bill Payment, Mobile Check Deposit using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Best Practices To Implement Cloud Access Security Broker CASB Cloud Security
Best Practices To Implement Cloud Access Security Broker CASB Cloud SecurityThis slide represents the best practices for implementing a cloud access security broker within an organization. The purpose of this slide is to demonstrate the best practices and their possible impact on the overall business operations. The best practices include building visibility, forecasting risk and releasing CASB. Deliver an outstanding presentation on the topic using this Best Practices To Implement Cloud Access Security Broker CASB Cloud Security. Dispense information and present a thorough explanation of Cloud Access Security Broker, Business Operations, Building Visibility, Forecasting Risk using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Checklist To Adopt A Cloud Access Security Broker CASB Cloud Security
Checklist To Adopt A Cloud Access Security Broker CASB Cloud SecurityThis slide represents the main points to consider before adopting a cloud access security broker. The purpose of this slide is to showcase the key measures that organizations should keep in mind before choosing a CASB solution and the measures include conducting the trial, outlining CASB roles, and so on. Deliver an outstanding presentation on the topic using this Checklist To Adopt A Cloud Access Security Broker CASB Cloud Security. Dispense information and present a thorough explanation of Cloud Access Security Broker, Contemplating Numerous, Threat Or Risk Landscape Is Dynamic using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
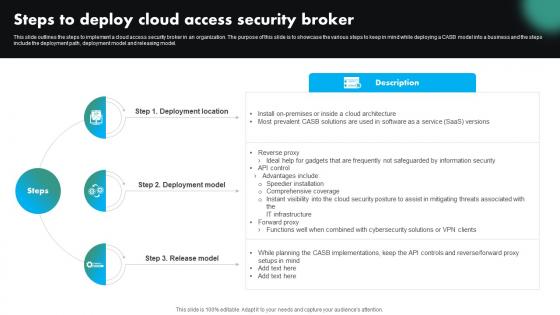 Steps To Deploy Cloud Access Security Broker CASB Cloud Security
Steps To Deploy Cloud Access Security Broker CASB Cloud SecurityThis slide outlines the steps to implement a cloud access security broker in an organization. The purpose of this slide is to showcase the various steps to keep in mind while deploying a CASB model into a business and the steps include the deployment path, deployment model and releasing model. Deliver an outstanding presentation on the topic using this Steps To Deploy Cloud Access Security Broker CASB Cloud Security. Dispense information and present a thorough explanation of Deployment Location, Deployment Model, Release Model, Cloud Access Security Broker using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
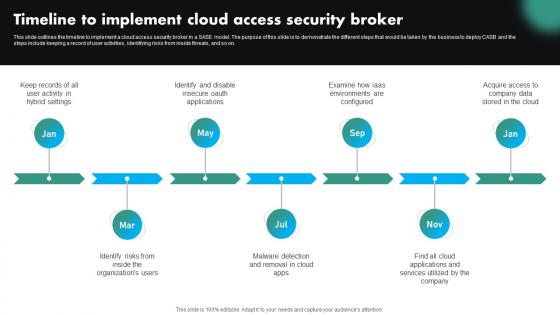 Timeline To Implement Cloud Access Security Broker CASB Cloud Security
Timeline To Implement Cloud Access Security Broker CASB Cloud SecurityThis slide outlines the timeline to implement a cloud access security broker in a SASE model. The purpose of this slide is to demonstrate the different steps that would be taken by the business to deploy CASB and the steps include keeping a record of user activities, identifying risks from inside threats, and so on. Introducing Timeline To Implement Cloud Access Security Broker CASB Cloud Security to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Access Security Broker, Identifying Risks, Malware Detection, Identify Risks, using this template. Grab it now to reap its full benefits.
-
 Accessibility Of ChatGPT Platform For Query Resolution Top Generative AI Tools To Look For AI SS V
Accessibility Of ChatGPT Platform For Query Resolution Top Generative AI Tools To Look For AI SS VThis slide provides information regarding usage of ChatGPT platform for query resolution, as it offers free review model to users, and they need to register prior to functioning on it. The registered users can then initiate a conversation with the model by feeding queries in the system. Present the topic in a bit more detail with this Accessibility Of ChatGPT Platform For Query Resolution Top Generative AI Tools To Look For AI SS V. Use it as a tool for discussion and navigation on Introductory Page, Conversation Box, Free Review Model. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
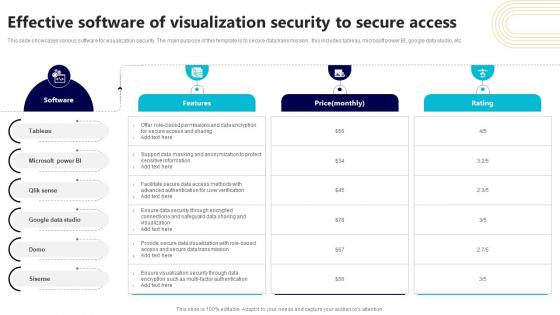 Effective Software Of Visualization Security To Secure Access
Effective Software Of Visualization Security To Secure AccessThis slide showcases various software for visualization security. The main purpose of this template is to secure data transmission . this includes tableau, microsoft power BI, google data studio, etc. Presenting our well structured Effective Software Of Visualization Security To Secure Access. The topics discussed in this slide are Microsoft Power, Google Data Studio, Secure Access. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
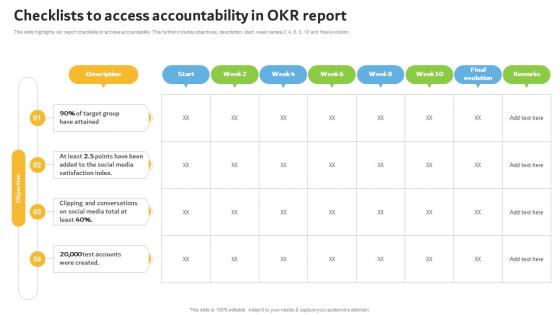 Checklists To Access Accountability In Okr Report
Checklists To Access Accountability In Okr ReportThis slide highlights okr report checklists to access accountability. This further includes objectives, description, start, week names 2, 4, 6, 8, 10 and final evolution. Introducing our Checklists To Access Accountability In Okr Report set of slides. The topics discussed in these slides are Accountability, Conversations, Satisfaction. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Access to real time reporting powerpoint slides background
Access to real time reporting powerpoint slides backgroundPresenting access to real time reporting powerpoint slides background. This is a access to real time reporting powerpoint slides background. This is a three stage process. The stages in this process are increase employee satisfaction, access to real time reporting, secure company assists.
-
 Easy access to social media powerpoint layout
Easy access to social media powerpoint layoutPresenting easy access to social media powerpoint layout. This is a easy access to social media powerpoint layout. This is a four stage process. The stages in this process are shop, marketing, movies, email.
-
 Access to information ppt background template
Access to information ppt background templatePresenting access to information ppt background template. This is a access to information ppt background template. This is a four stage process. The stages in this process are ict hubs, internet connectivity, trend watching, access to information trademarks, database rights.
-
 Access to information ppt design templates
Access to information ppt design templatesPresenting access to information ppt design templates. This is a access to information ppt design templates. This is a four stage process. The stages in this process are web integration, open data catalogue, community engagement framework, oversight and control functions, access to information.
-
 1213 business ppt diagram 2 steps to access the market powerpoint template
1213 business ppt diagram 2 steps to access the market powerpoint templateWe are proud to present our 1213 business ppt diagram 2 steps to access the market powerpoint template. Our Arrows Power Point Templates Are Topically Designed To Provide An Attractive Backdrop To Any Subject. Use Them To Look Like A Presentation Pro. Use Our Business Power Point Templates To Effectively Help You Save Your Valuable Time. They Are Readymade To Fit Into Any Presentation Structure.
-
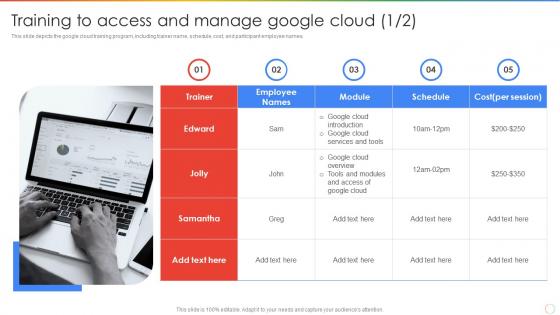 Training To Access And Manage Google Cloud Ppt Powerpoint Presentation Outline Introduction
Training To Access And Manage Google Cloud Ppt Powerpoint Presentation Outline IntroductionThis slide depicts the google cloud training program, including trainer name, schedule, cost, and participant employee names. Introducing Training To Access And Manage Google Cloud Ppt Powerpoint Presentation Outline Introduction to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Training To Access, Manage Google Cloud, using this template. Grab it now to reap its full benefits.



