Powerpoint Templates and Google slides for Attacking
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Social Engineering Attack Prevention Techniques Conducting Security Awareness
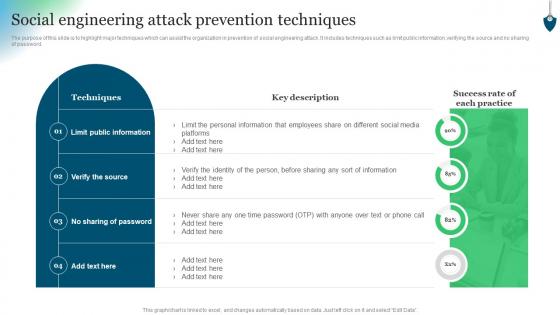
Social Engineering Attack Prevention Techniques Conducting Security AwarenessThe purpose of this slide is to highlight major techniques which can assist the organization in prevention of social engineering attack. It includes techniques such as limit public information, verifying the source and no sharing of password. Present the topic in a bit more detail with this Social Engineering Attack Prevention Techniques Conducting Security Awareness. Use it as a tool for discussion and navigation on Techniques, Limit Public Information, Verify Source. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Determining The Actors Behind Most Significant Cyber Attack Conducting Security Awareness
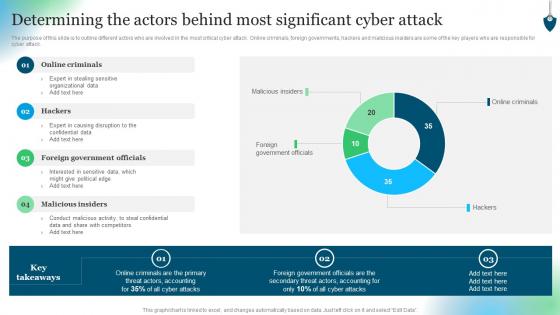
Determining The Actors Behind Most Significant Cyber Attack Conducting Security AwarenessThe purpose of this slide is to outline different actors who are involved in the most critical cyber attack. Online criminals, foreign governments, hackers and malicious insiders are some of the key players who are responsible for cyber attack. Deliver an outstanding presentation on the topic using this Determining The Actors Behind Most Significant Cyber Attack Conducting Security Awareness. Dispense information and present a thorough explanation of Online Criminals, Foreign Government Officials, Malicious Insiders using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Most Common Cyber Attack Faced By Our Employees Conducting Security Awareness
Most Common Cyber Attack Faced By Our Employees Conducting Security AwarenessThe purpose of this slide is to showcase various kind of cyber attack which are currently faced by the employees. The most common cyber attacks are ransomware, password attack, crypto jacking, IoT-based attacks, malware, social engineering attack and business email compromise. Present the topic in a bit more detail with this Most Common Cyber Attack Faced By Our Employees Conducting Security Awareness. Use it as a tool for discussion and navigation on Ransomware, Password Attack, Cryptojacking. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
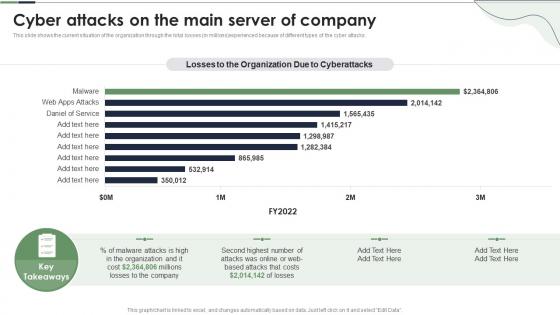 Cyber Attacks On The Main Server Of Company Reverse Proxy Server Ppt Powerpoint Presentation Infographics
Cyber Attacks On The Main Server Of Company Reverse Proxy Server Ppt Powerpoint Presentation InfographicsThis slide shows the current situation of the organization through the total losses in millions experienced because of different types of the cyber attacks. Present the topic in a bit more detail with this Cyber Attacks On The Main Server Of Company Reverse Proxy Server Ppt Powerpoint Presentation Infographics. Use it as a tool for discussion and navigation on Millions Losses, Organization, Cyber Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
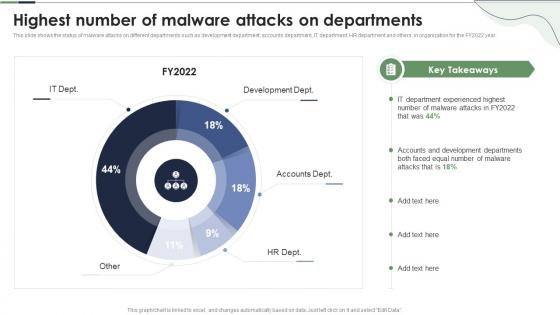 Highest Number Of Malware Attacks On Departments Reverse Proxy Server Ppt Powerpoint Presentation Professional
Highest Number Of Malware Attacks On Departments Reverse Proxy Server Ppt Powerpoint Presentation ProfessionalThis slide shows the status of malware attacks on different departments such as development department, accounts department, IT department, HR department and others, in organization for the FY2022 year. Present the topic in a bit more detail with this Highest Number Of Malware Attacks On Departments Reverse Proxy Server Ppt Powerpoint Presentation Professional. Use it as a tool for discussion and navigation on Highest Number, Development Dept, Accounts Dept. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
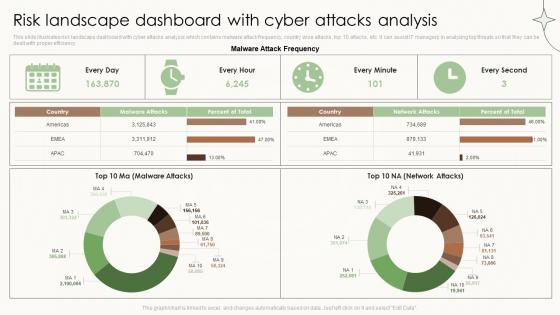 Risk Landscape Dashboard With Cyber Attacks Analysis
Risk Landscape Dashboard With Cyber Attacks AnalysisThis slide illustrates risk landscape dashboard with cyber attacks analysis which contains malware attack frequency, country wise attacks, top 10 attacks, etc. It can assist IT managers in analyzing top threats so that they can be dealt with proper efficiency. Introducing our Risk Landscape Dashboard With Cyber Attacks Analysis set of slides. The topics discussed in these slides are Risk Landscape Icon, Financial Threat. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
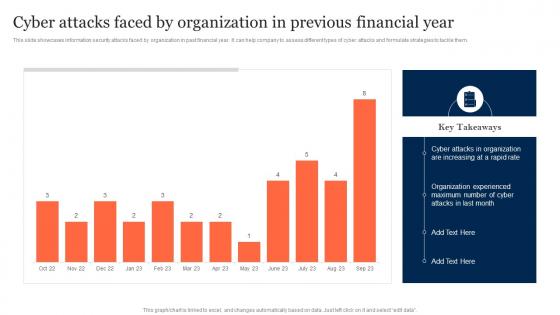 Cyber Attacks Faced By Organization In Previous Information Security Risk Management
Cyber Attacks Faced By Organization In Previous Information Security Risk ManagementThis slide showcases information security attacks faced by organization in past financial year. It can help company to assess different types of cyber attacks and formulate strategies to tackle them. Deliver an outstanding presentation on the topic using this Cyber Attacks Faced By Organization In Previous Information Security Risk Management. Dispense information and present a thorough explanation of Cyber Attacks Faced, Organization, Previous Financial Year using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
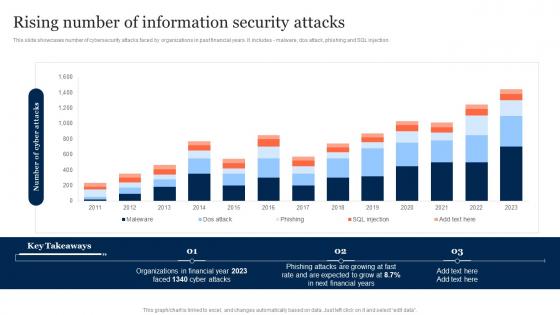 Rising Number Of Information Security Attacks Information Security Risk Management
Rising Number Of Information Security Attacks Information Security Risk ManagementThis slide showcases number of cybersecurity attacks faced by organizations in past financial years. It includes malware, dos attack, phishing and SQL injection. Present the topic in a bit more detail with this Rising Number Of Information Security Attacks Information Security Risk Management. Use it as a tool for discussion and navigation on Rising Number, Information Security Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now
-
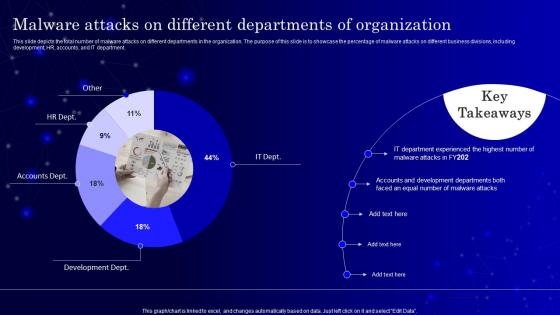 SecOps Malware Attacks On Different Departments Of Organization Ppt Portrait
SecOps Malware Attacks On Different Departments Of Organization Ppt PortraitThis slide depicts the total number of malware attacks on different departments in the organization. The purpose of this slide is to showcase the percentage of malware attacks on different business divisions, including development, HR, accounts, and IT department. Present the topic in a bit more detail with this SecOps Malware Attacks On Different Departments Of Organization Ppt Portrait. Use it as a tool for discussion and navigation on It Department, Accounts Development. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
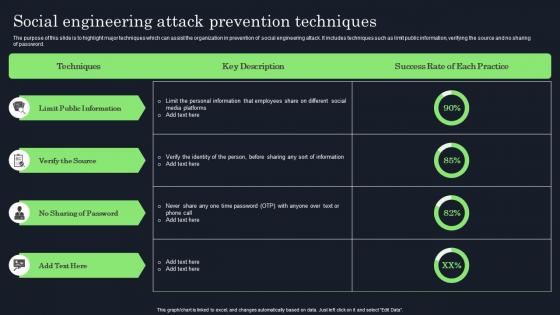 Social Engineering Attack Prevention Techniques Raising Cyber Security Awareness In Organizations
Social Engineering Attack Prevention Techniques Raising Cyber Security Awareness In OrganizationsThe purpose of this slide is to highlight major techniques which can assist the organization in prevention of social engineering attack. It includes techniques such as limit public information, verifying the source and no sharing of password. Present the topic in a bit more detail with this Social Engineering Attack Prevention Techniques Raising Cyber Security Awareness In Organizations. Use it as a tool for discussion and navigation on Verify The Source, Sharing Of Password, Public Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
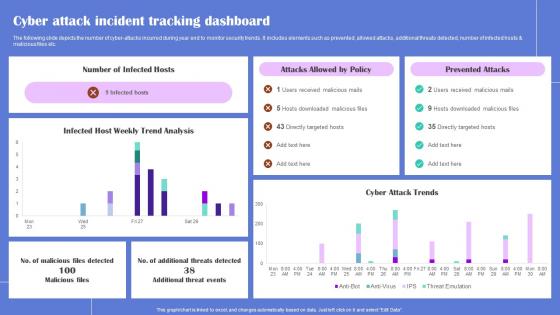 Cyber Attack Incident Generating Security Awareness Among Employees To Reduce
Cyber Attack Incident Generating Security Awareness Among Employees To ReduceThe following slide depicts the number of cyber attacks incurred during year end to monitor security trends. It includes elements such as prevented, allowed attacks, additional threats detected, number of infected hosts and malicious files etc. Present the topic in a bit more detail with this Cyber Attack Incident Generating Security Awareness Among Employees To Reduce Use it as a tool for discussion and navigation on Infected Hosts, Prevented Attacks This template is free to edit as deemed fit for your organization. Therefore download it now.
-
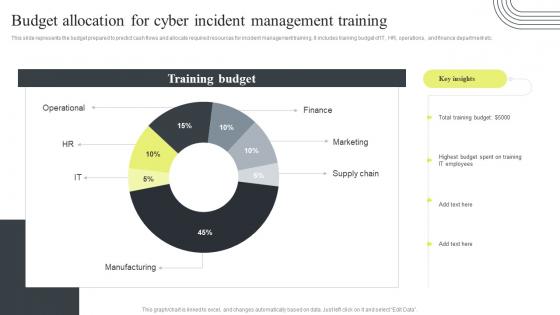 Cyber Security Attacks Response Plan Budget Allocation For Cyber Incident Management Training
Cyber Security Attacks Response Plan Budget Allocation For Cyber Incident Management TrainingThis slide represents the budget prepared to predict cash flows and allocate required resources for incident management training. It includes training budget of IT, HR, operations, and finance department etc. Deliver an outstanding presentation on the topic using this Cyber Security Attacks Response Plan Budget Allocation For Cyber Incident Management Training. Dispense information and present a thorough explanation of Budget Allocation, Cyber Incident Management, Training using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
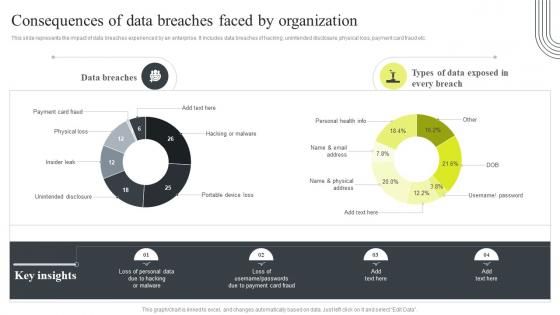 Cyber Security Attacks Response Plan Consequences Of Data Breaches Faced By Organization
Cyber Security Attacks Response Plan Consequences Of Data Breaches Faced By OrganizationThis slide represents the impact of data breaches experienced by an enterprise. It includes data breaches of hacking, unintended disclosure, physical loss, payment card fraud etc. Present the topic in a bit more detail with this Cyber Security Attacks Response Plan Consequences Of Data Breaches Faced By Organization. Use it as a tool for discussion and navigation on Consequences, Data Breaches, Unintended Disclosure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
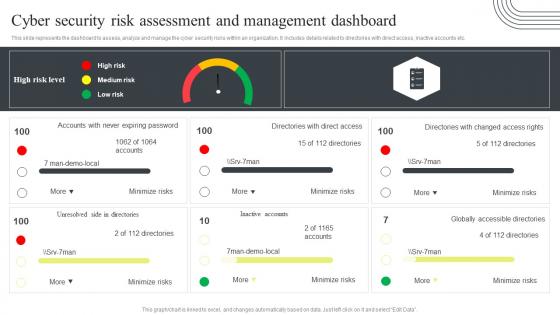 Cyber Security Attacks Response Plan Cyber Security Risk Assessment And Management Dashboard
Cyber Security Attacks Response Plan Cyber Security Risk Assessment And Management DashboardThis slide represents the dashboard to assess, analyze and manage the cyber security risks within an organization. It includes details related to directories with direct access, inactive accounts etc. Deliver an outstanding presentation on the topic using this Cyber Security Attacks Response Plan Cyber Security Risk Assessment And Management Dashboard. Dispense information and present a thorough explanation of Cyber Security, Risk Assessment, Management Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
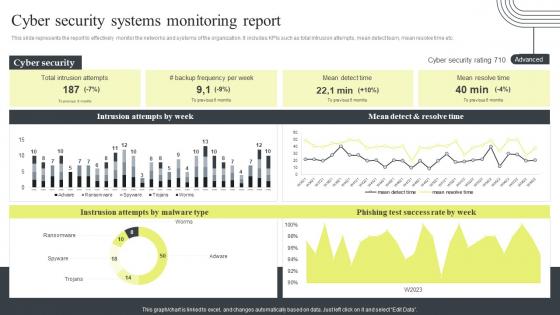 Cyber Security Attacks Response Plan Cyber Security Systems Monitoring Report
Cyber Security Attacks Response Plan Cyber Security Systems Monitoring ReportThis slide represents the report to effectively monitor the networks and systems of the organization. It includes KPIs such as total intrusion attempts, mean detect team, mean resolve time etc. Present the topic in a bit more detail with this Cyber Security Attacks Response Plan Cyber Security Systems Monitoring Report. Use it as a tool for discussion and navigation on Cyber Security Systems, Monitoring Report, Mean Detect And Resolve Time. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Attacks Response Plan Cyber Supply Chain Risk Management Dashboard
Cyber Security Attacks Response Plan Cyber Supply Chain Risk Management DashboardThis slide shows the dashboard representing details related to management of supply chain risks by the incident management team. It includes details related to KPIs such as policy and compliance, resource security hygiene etc. Present the topic in a bit more detail with this Cyber Security Attacks Response Plan Cyber Supply Chain Risk Management Dashboard. Use it as a tool for discussion and navigation on Cyber Supply Chain, Risk Management, Dashboard, Regulatory Compliance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Attacks Response Plan Enterprise Cyber Risk Management Dashboard
Cyber Security Attacks Response Plan Enterprise Cyber Risk Management DashboardThis slide represents the key metrics dashboard representing details related to management of cyber security incidents by an enterprise. It includes key performance indicators such as risk analysis progress, risk rating breakdown etc. Deliver an outstanding presentation on the topic using this Cyber Security Attacks Response Plan Enterprise Cyber Risk Management Dashboard. Dispense information and present a thorough explanation of Enterprise Cyber, Risk Management, Dashboard, Action Plan Breakdown using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
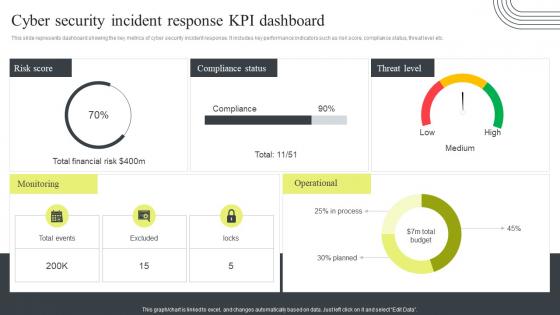 Cyber Security Incident Response Kpi Dashboard Cyber Security Attacks Response Plan
Cyber Security Incident Response Kpi Dashboard Cyber Security Attacks Response PlanThis slide represents dashboard showing the key metrics of cyber security incident response. It includes key performance indicators such as risk score, compliance status, threat level etc. Present the topic in a bit more detail with this Cyber Security Incident Response Kpi Dashboard Cyber Security Attacks Response Plan. Use it as a tool for discussion and navigation on Cyber Security, Incident Response, KPI Dashboard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
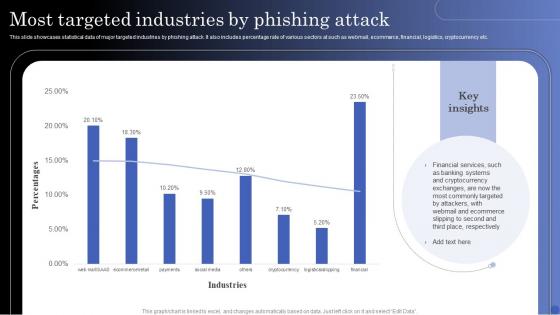 Most Targeted Industries By Phishing Attack
Most Targeted Industries By Phishing AttackThis slide showcases statistical data of major targeted industries by phishing attack. It also includes percentage rate of various sectors at such as webmail, ecommerce, financial, logistics, cryptocurrency etc. Introducing our Most Targeted Industries By Phishing Attack set of slides. The topics discussed in these slides are Cryptocurrency, Banking Systems, Financial Services. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
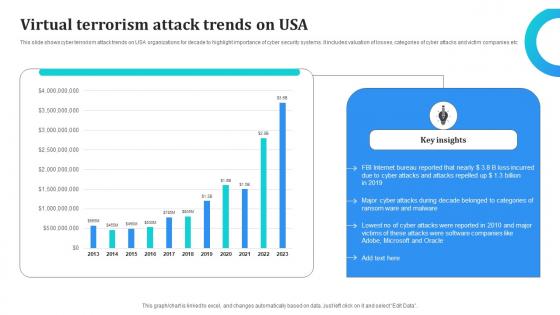 Virtual Terrorism Attack Trends On Usa
Virtual Terrorism Attack Trends On UsaThis slide shows cyber terrorism attack trends on USA organizations for decade to highlight importance of cyber security systems. It includes valuation of losses, categories of cyber attacks and victim companies etc.Presenting our well structured Virtual Terrorism Attack Trends On Usa. The topics discussed in this slide are Internet Bureau, Ransom Malware, Software Companies. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
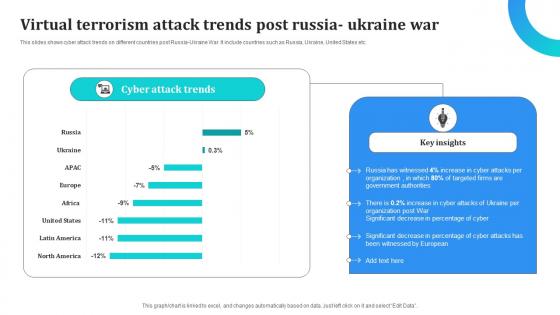 Virtual Terrorism Attack Trends Post Russia Ukraine War
Virtual Terrorism Attack Trends Post Russia Ukraine WarThis slides shows cyber attack trends on different countries post Russia-Ukraine War. It include countries such as Russia, Ukraine, United States etc.Introducing our Virtual Terrorism Attack Trends Post Russia Ukraine War set of slides. The topics discussed in these slides are Government Authorities, Russia Witnessed, Decrease Percentage. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
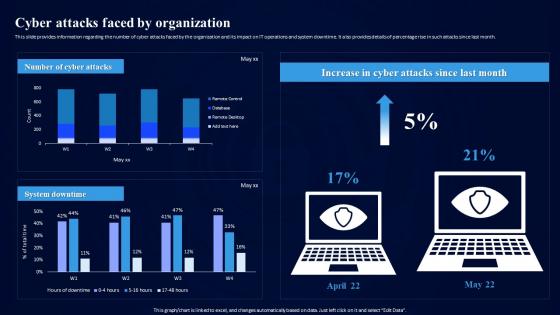 Cybersecurity Risk Assessment Program Cyber Attacks Faced By Organization
Cybersecurity Risk Assessment Program Cyber Attacks Faced By OrganizationThis slide provides information regarding the number of cyber attacks faced by the organization and its impact on IT operations and system downtime. It also provides details of percentage rise in such attacks since last month. Present the topic in a bit more detail with this Cybersecurity Risk Assessment Program Cyber Attacks Faced By Organization. Use it as a tool for discussion and navigation on Cyber Attacks, IT Operations, System Downtime. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cybersecurity Risk Assessment Program Dashboard For Tracking Cyber Attack Risk Levels
Cybersecurity Risk Assessment Program Dashboard For Tracking Cyber Attack Risk LevelsThe slide represents the dashboard for tracking cyber attack risk levels. It includes information regarding the multiple threat agents, attack methods, preventive controls along with details of risk score and infected systems. Deliver an outstanding presentation on the topic using this Cybersecurity Risk Assessment Program Dashboard For Tracking Cyber Attack Risk Levels. Dispense information and present a thorough explanation of Infrastructure Controls, Preventive Controls, Detective Controls using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
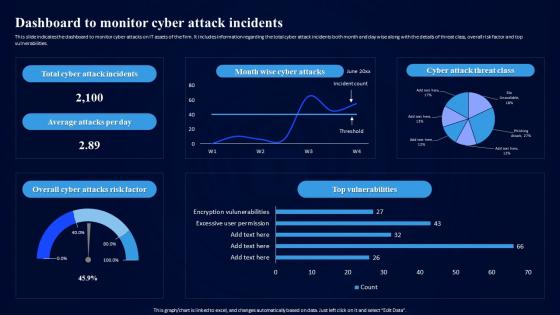 Cybersecurity Risk Assessment Program Dashboard To Monitor Cyber Attack Incidents
Cybersecurity Risk Assessment Program Dashboard To Monitor Cyber Attack IncidentsThis slide indicates the dashboard to monitor cyber attacks on IT assets of the firm. It includes information regarding the total cyber attack incidents both month and day wise along with the details of threat class, overall risk factor and top vulnerabilities. Present the topic in a bit more detail with this Cybersecurity Risk Assessment Program Dashboard To Monitor Cyber Attack Incidents. Use it as a tool for discussion and navigation on Dashboard To Monitor, Cyber Attack Incidents, Vulnerabilities, Dashboard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
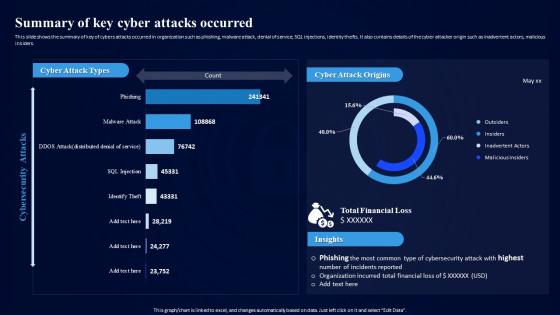 Cybersecurity Risk Assessment Program Summary Of Key Cyber Attacks Occurred
Cybersecurity Risk Assessment Program Summary Of Key Cyber Attacks OccurredThis slide shows the summary of key of cybers attacks occurred in organization such as phishing, malware attack, denial of service, SQL injections, identity thefts. It also contains details of the cyber attacker origin such as inadvertent actors, malicious insiders. Present the topic in a bit more detail with this Cybersecurity Risk Assessment Program Summary Of Key Cyber Attacks Occurred. Use it as a tool for discussion and navigation on Cyber Attacks Occurred, Financial Loss, Cyber Attack Origins. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Strategy To Minimize Cyber Attacks Comprehensive Overview Of Organization IT Assets
Strategy To Minimize Cyber Attacks Comprehensive Overview Of Organization IT AssetsThe purpose this slide is to showcase the comprehensive overview of organization IT assets. The dashboards provide information regarding the IT devices count, distribution in terms of operating system, and location. It also contains details of endpoint by hardware, department and cyber attack visibility. Present the topic in a bit more detail with this Strategy To Minimize Cyber Attacks Comprehensive Overview Of Organization IT Assets. Use it as a tool for discussion and navigation on Operating System Distribution, Assets Distribution By Location, Endpoint By Department, Cyber Attack Visibility. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
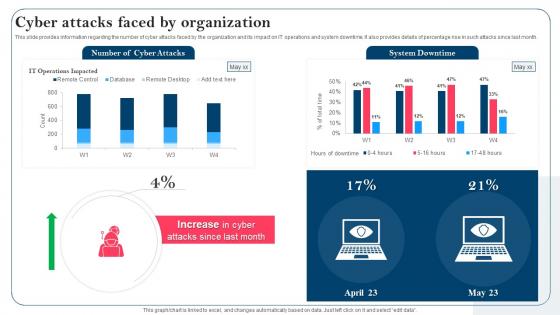 Strategy To Minimize Cyber Attacks Cyber Attacks Faced By Organization
Strategy To Minimize Cyber Attacks Cyber Attacks Faced By OrganizationThis slide provides information regarding the number of cyber attacks faced by the organization and its impact on IT operations and system downtime. It also provides details of percentage rise in such attacks since last month. Deliver an outstanding presentation on the topic using this Strategy To Minimize Cyber Attacks Cyber Attacks Faced By Organization. Dispense information and present a thorough explanation of Cyber Attacks, It Operations, System Downtime using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
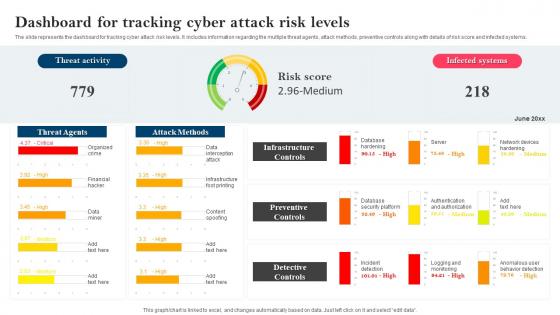 Strategy To Minimize Cyber Attacks Dashboard For Tracking Cyber Attack Risk Levels
Strategy To Minimize Cyber Attacks Dashboard For Tracking Cyber Attack Risk LevelsThe slide represents the dashboard for tracking cyber attack risk levels. It includes information regarding the multiple threat agents, attack methods, preventive controls along with details of risk score and infected systems. Present the topic in a bit more detail with this Strategy To Minimize Cyber Attacks Dashboard For Tracking Cyber Attack Risk Levels. Use it as a tool for discussion and navigation on Dashboard For Tracking, Cyber Attack Risk Levels, Infrastructure Controls, Preventive Controls, Detective Controls. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
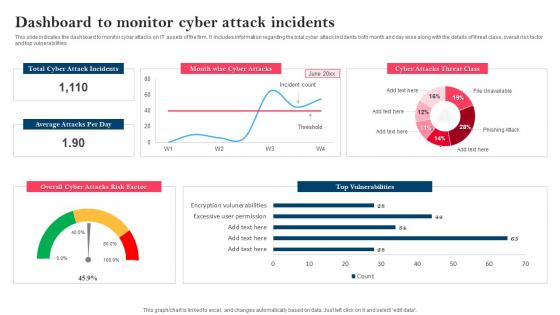 Strategy To Minimize Cyber Attacks Dashboard To Monitor Cyber Attack Incidents
Strategy To Minimize Cyber Attacks Dashboard To Monitor Cyber Attack IncidentsThis slide indicates the dashboard to monitor cyber attacks on IT assets of the firm. It includes information regarding the total cyber attack incidents both month and day wise along with the details of threat class, overall risk factor and top vulnerabilities. Deliver an outstanding presentation on the topic using this Strategy To Minimize Cyber Attacks Dashboard To Monitor Cyber Attack Incidents. Dispense information and present a thorough explanation of Dashboard To Monitor, Cyber Attack Incidents, Top Vulnerabilities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
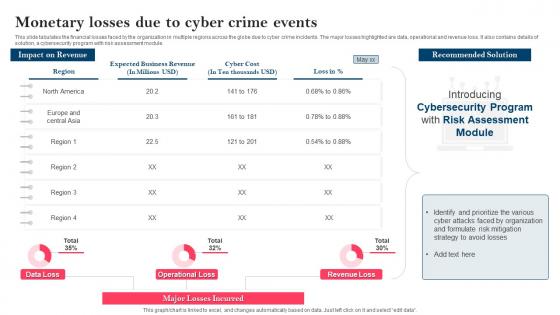 Strategy To Minimize Cyber Attacks Monetary Losses Due To Cyber Crime Events
Strategy To Minimize Cyber Attacks Monetary Losses Due To Cyber Crime EventsThis slide tabulates the financial losses faced by the organization in multiple regions across the globe due to cyber crime incidents. The major losses highlighted are data, operational and revenue loss. It also contains details of solution, a cybersecurity program with risk assessment module. Deliver an outstanding presentation on the topic using this Strategy To Minimize Cyber Attacks Monetary Losses Due To Cyber Crime Events. Dispense information and present a thorough explanation of Monetary Losses, Recommended Solution, Cybersecurity Program, Risk Assessment Module using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
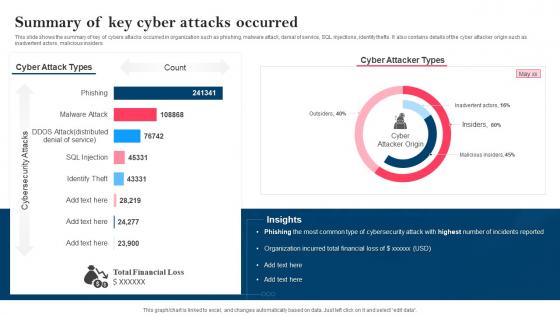 Strategy To Minimize Cyber Attacks Summary Of Key Cyber Attacks Occurred
Strategy To Minimize Cyber Attacks Summary Of Key Cyber Attacks OccurredThis slide shows the summary of key of cybers attacks occurred in organization such as phishing, malware attack, denial of service, SQL injections, identity thefts. It also contains details of the cyber attacker origin such as inadvertent actors, malicious insiders. Present the topic in a bit more detail with this Strategy To Minimize Cyber Attacks Summary Of Key Cyber Attacks Occurred. Use it as a tool for discussion and navigation on Cybers Attacks Occurred, Phishing, Malware Attack, Denial Of Service, SQL Injections, Identity Thefts. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Ultimate Guide For Blockchain Various Types Of Crypto Phishing Attacks BCT SS
Ultimate Guide For Blockchain Various Types Of Crypto Phishing Attacks BCT SSIntroducing Ultimate Guide For Blockchain Various Types Of Crypto Phishing Attacks BCT SS to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Spear Phishing, Whaling Phishing using this template. Grab it now to reap its full benefits.
-
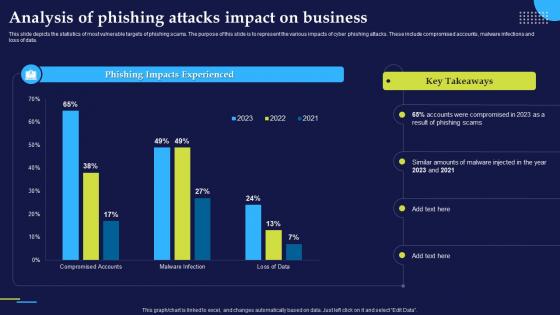 Analysis Of Phishing Attacks Impact On Business Phishing Attacks And Strategies
Analysis Of Phishing Attacks Impact On Business Phishing Attacks And StrategiesThis slide depicts the statistics of most vulnerable targets of phishing scams. The purpose of this slide is to represent the various impacts of cyber phishing attacks. These include compromised accounts, malware infections and loss of data.Present the topic in a bit more detail with this Analysis Of Phishing Attacks Impact On Business Phishing Attacks And Strategies. Use it as a tool for discussion and navigation on Phishing Impacts Experienced, Amounts Malware, Phishing Scams. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Impact Of Phishing Cyber Scams On Phishing Attacks And Strategies
Impact Of Phishing Cyber Scams On Phishing Attacks And StrategiesThis slide talks about the damage caused by phishing attacks. The purpose of this slide is to explain the impact of phishing scams on organizations. The key points included are information loss, damaged credibility, direct financial loss and productivity loss.Increase audience engagement and knowledge by dispensing information using Impact Of Phishing Cyber Scams On Phishing Attacks And Strategies. This template helps you present information on six stages. You can also present information on Businesses Incur Reputational, Phishing Assault, Maintenance Reconfiguration using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Table Of Contents Phishing Attacks And Strategies To Mitigate Them
Table Of Contents Phishing Attacks And Strategies To Mitigate ThemDeliver an outstanding presentation on the topic using this Table Of Contents Phishing Attacks And Strategies To Mitigate Them. Dispense information and present a thorough explanation of Phishing Attacks Overview, Types Phishing, Attacks Prevention using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
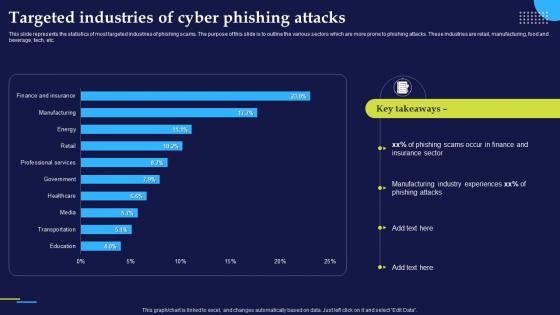 Targeted Industries Of Cyber Phishing Attacks Phishing Attacks And Strategies
Targeted Industries Of Cyber Phishing Attacks Phishing Attacks And StrategiesThis slide represents the statistics of most targeted industries of phishing scams. The purpose of this slide is to outline the various sectors which are more prone to phishing attacks. These industries are retail, manufacturing, food and beverage, tech, etc.Present the topic in a bit more detail with this Targeted Industries Of Cyber Phishing Attacks Phishing Attacks And Strategies. Use it as a tool for discussion and navigation on Phishing Scams, Manufacturing Industry, Phishing Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vishing Cyber Scams In Different Businesses Phishing Attacks And Strategies
Vishing Cyber Scams In Different Businesses Phishing Attacks And StrategiesThis slide demonstrates the various types of vishing scams. The purpose of this slide is to illustrate the ways in which attackers conduct scams in different businesses using vishing technique. These are banking vishing and internal revenue service vishing.Present the topic in a bit more detail with this Vishing Cyber Scams In Different Businesses Phishing Attacks And Strategies. Use it as a tool for discussion and navigation on Internal Revenue, Remote Application, Vishing Example. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Malware Attack Awareness Training Program In Organization
Malware Attack Awareness Training Program In OrganizationFollowing slides shows the various campaign plan organize in organization regarding cyber awareness to reduce the threat. It includes various campaign.Introducing our Malware Attack Awareness Training Program In Organization set of slides. The topics discussed in these slides are Highly Employee, Security Awareness, Least Affected. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
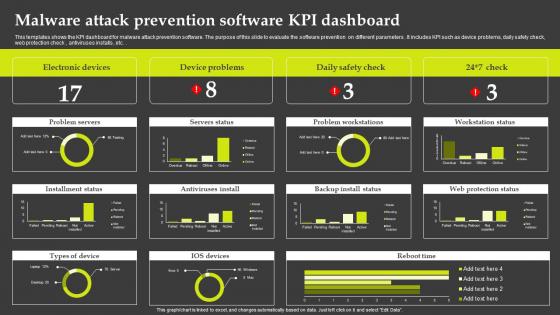 Malware Attack Prevention Software KPI Dashboard
Malware Attack Prevention Software KPI DashboardThis templates shows the KPI dashboard for malware attack prevention software. The purpose of this slide to evaluate the software prevention on different parameters . It includes KPI such as device problems, daily safety check, web protection check , antiviruses installs , etc.Introducing our Malware Attack Prevention Software KPI Dashboard set of slides. The topics discussed in these slides are Electronic Devices, Device Problems, Problem Workstations. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
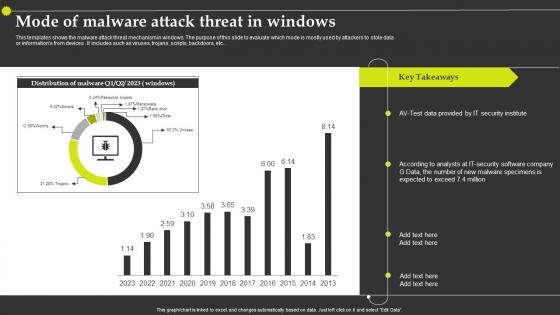 Mode Of Malware Attack Threat In Windows
Mode Of Malware Attack Threat In WindowsThis templates shows the malware attack threat mechanism in windows. The purpose of this slide to evaluate which mode is mostly used by attackers to stole data or informations from devices . It includes such as viruses, trojans, scripts, backdoors, etc.Introducing our Mode Of Malware Attack Threat In Windows set of slides. The topics discussed in these slides are Security Institute, Malware Specimens, Security Software Company. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
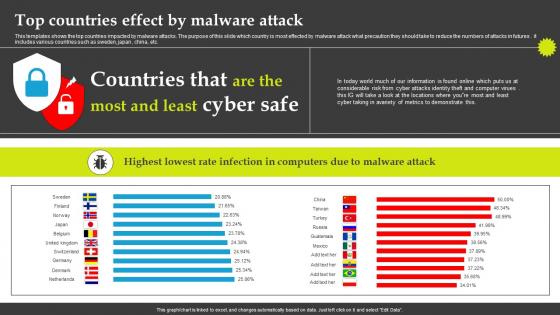 Top Countries Effect By Malware Attack
Top Countries Effect By Malware AttackThis templates shows the top countries impacted by malware attacks. The purpose of this slide which country is most effected by malware attack what precaution they should take to reduce the numbers of attacks in futures . it includes various countries such as sweden, japan , china, etc. Introducing our Top Countries Effect By Malware Attack set of slides. The topics discussed in these slides are Information Found, Metrics Demonstrate, Infection Computers. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
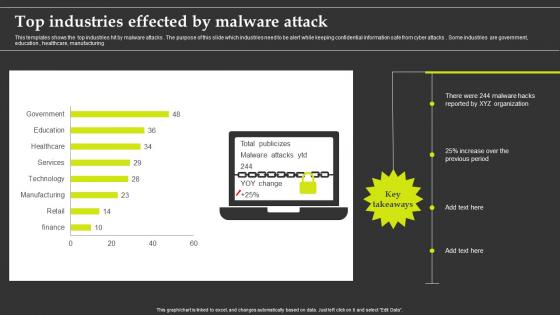 Top Industries Effected By Malware Attack
Top Industries Effected By Malware AttackThis templates shows the top industries hit by malware attacks . The purpose of this slide which industries need to be alert while keeping confidential information safe from cyber attacks . Some industries are government, education , healthcare, manufacturing.Presenting our well structured Top Industries Effected By Malware Attack. The topics discussed in this slide are Top Industries Effected, Malware Attack. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
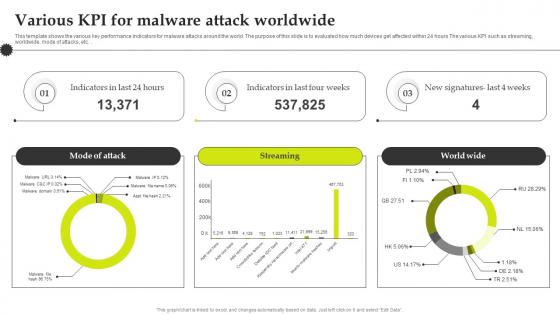 Various Kpi For Malware Attack Worldwide
Various Kpi For Malware Attack WorldwideThis template shows the various key performance indicators for malware attacks around the world. The purpose of this slide is to evaluated how much devices get affected within 24 hours The various KPI such as streaming, worldwide, mode of attacks, etc.Introducing our Various Kpi For Malware Attack Worldwide set of slides. The topics discussed in these slides are Various KPI For Malware, Attack Worldwide . This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Digital Risk Management Dashboard For Tracking Threats And Attacks
Digital Risk Management Dashboard For Tracking Threats And AttacksThe purpose of this slide is to represent dashboard to monitor risks and cyber threats for efficient risk management. It includes various types of key performance indicators such as types of risks, severities, sources and risk meter. Introducing our Digital Risk Management Dashboard For Tracking Threats And Attacks set of slides. The topics discussed in these slides are Severities, Types Of Risk This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Hooded hacker attacking security systems
Hooded hacker attacking security systemsPresenting this set of slides with name Hooded Hacker Attacking Security Systems. The topics discussed in these slides are Hacker, Network, Computer. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Cyber threat icon indicating malware attack
Cyber threat icon indicating malware attackIntroducing our premium set of slides with Cyber Threat Icon Indicating Malware Attack. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Threat Icon Indicating Malware Attack. So download instantly and tailor it with your information.
-
 Bitcoin Finney Attack Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Bitcoin Finney Attack Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Bitcoin finney attack colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Bitcoin Finney Attack Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Bitcoin Finney Attack Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Bitcoin finney attack monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Currency Finney Attack Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Currency Finney Attack Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Currency finney attack colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Currency Finney Attack Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Currency Finney Attack Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Currency finney attack monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Digital Wallet User Attack Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Digital Wallet User Attack Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Digital wallet user attack colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Digital Wallet User Attack Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Digital Wallet User Attack Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Digital wallet user attack monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Finney Attack On People Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Finney Attack On People Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Finney attack on people colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Finney Attack On People Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Finney Attack On People Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Finney attack on people monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 User Wallet Attack Risk Colored Icon In Powerpoint Pptx Png And Editable Eps Format
User Wallet Attack Risk Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable User wallet attack risk colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 User Wallet Attack Risk Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
User Wallet Attack Risk Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable User wallet attack risk monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 User Wallet Id Attack Colored Icon In Powerpoint Pptx Png And Editable Eps Format
User Wallet Id Attack Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable User wallet id attack colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 User Wallet Id Attack Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
User Wallet Id Attack Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable User wallet id attack monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Zero Day Attack With Broken Shield Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Zero Day Attack With Broken Shield Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Zero day attack with broken shield colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Zero Day Attack With Broken Shield Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Zero Day Attack With Broken Shield Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Zero day attack with broken shield monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.



