Powerpoint Templates and Google slides for Breach Of Contract
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Containing The Breach As A Part Of Incident Response Plan Training Ppt
Containing The Breach As A Part Of Incident Response Plan Training PptPresenting Containing the Breach as a Part of Incident Response Plan. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
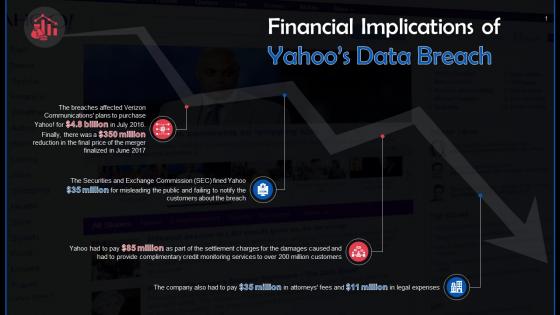 Financial Implications Of Data Breach On Yahoo Training Ppt
Financial Implications Of Data Breach On Yahoo Training PptPresenting Financial Implications of Data Breach on Yahoo. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
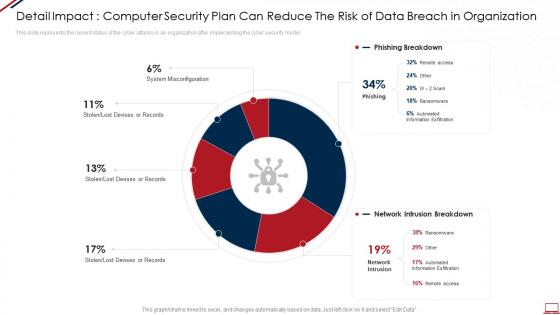 Computer system security detail impact computer security plan can reduce the risk of data breach in organization
Computer system security detail impact computer security plan can reduce the risk of data breach in organizationThis slide represents the current status of the cyber attacks in an organization after implementing the cyber security model. Present the topic in a bit more detail with this Computer System Security Detail Impact Computer Security Plan Can Reduce The Risk Of Data Breach In Organization. Use it as a tool for discussion and navigation on System Misconfiguration, Network Intrusion, Automated Information Exfiltration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Breach Prevention And Mitigation Number Of Data Breaches In Different Sectors
Data Breach Prevention And Mitigation Number Of Data Breaches In Different SectorsThe purpose of this slide is to outline the number of data breach attacks in different sectors from the year 2011 to 2023. The departments covered in this slide are business, medical, educational, government, and financial. Deliver an outstanding presentation on the topic using this Data Breach Prevention And Mitigation Number Of Data Breaches In Different Sectors. Dispense information and present a thorough explanation of Data Breach Attacks, Business, Medical, Educational, Government, Financial using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
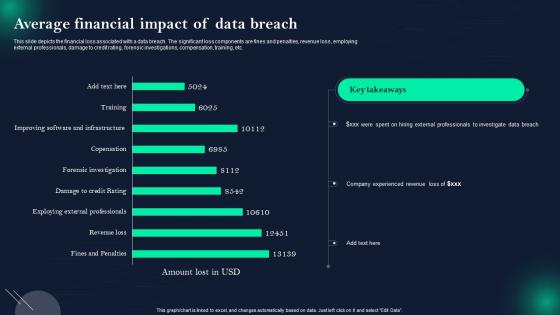 Data Breach Prevention Average Financial Impact Of Data Breach
Data Breach Prevention Average Financial Impact Of Data BreachThis slide depicts the financial loss associated with a data breach. The significant loss components are fines and penalties, revenue loss, employing external professionals, damage to credit rating, forensic investigations, compensation, training, etc. Present the topic in a bit more detail with this Data Breach Prevention Average Financial Impact Of Data Breach. Use it as a tool for discussion and navigation on Financial Loss Associated, Fines And Penalties, External Professionals, Damage To Credit Rating, Forensic Investigations, Compensation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
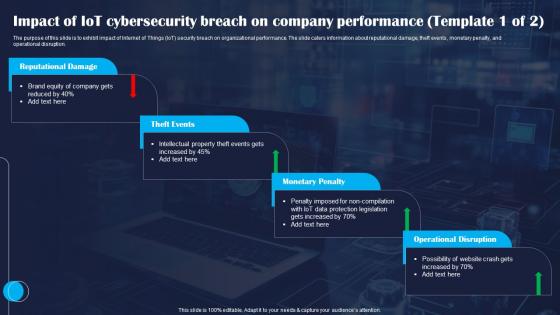 Impact Of IoT Cybersecurity Breach On Improving IoT Device Cybersecurity IoT SS
Impact Of IoT Cybersecurity Breach On Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to exhibit impact of Internet of Things IoT security breach on organizational performance. The slide caters information about reputational damage, theft events, monetary penalty, and operational disruption. Deliver an outstanding presentation on the topic using this Impact Of IoT Cybersecurity Breach On Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Reputational, Events, Penalty using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Table Of Contents Improving IoT Device Cybersecurity To Prevent Data Breaches IoT SS
Table Of Contents Improving IoT Device Cybersecurity To Prevent Data Breaches IoT SSIncrease audience engagement and knowledge by dispensing information using Table Of Contents Improving IoT Device Cybersecurity To Prevent Data Breaches IoT SS. This template helps you present information on six stages. You can also present information on Security, Strategies, Budget using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
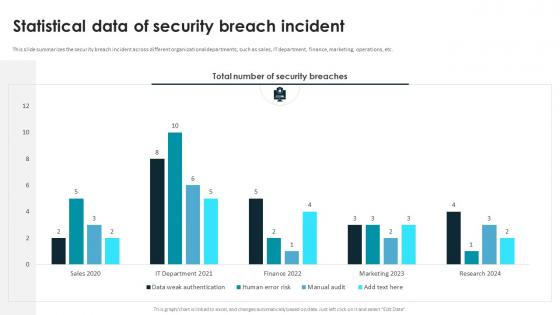 Smart Contracts Implementation Plan Statistical Data Of Security Breach Incident
Smart Contracts Implementation Plan Statistical Data Of Security Breach IncidentThis slide summarizes the security breach incident across different organizational departments, such as sales, IT department, finance, marketing, operations, etc. Present the topic in a bit more detail with this Smart Contracts Implementation Plan Statistical Data Of Security Breach Incident. Use it as a tool for discussion and navigation on Statistical Data, Security Breach Incident, Finance, Marketing, Operations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Breach Response Plan Average Financial Impact Of Data Breach
Data Breach Response Plan Average Financial Impact Of Data BreachThis slide depicts the financial loss associated with a data breach. The significant loss components are fines and penalties, revenue loss, employing external professionals, damage to credit rating, forensic investigations, compensation, training, etc. Deliver an outstanding presentation on the topic using this Data Breach Response Plan Average Financial Impact Of Data Breach. Dispense information and present a thorough explanation of Fines And Penalties, Revenue Loss, Employing External Professionals, Forensic Investigations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
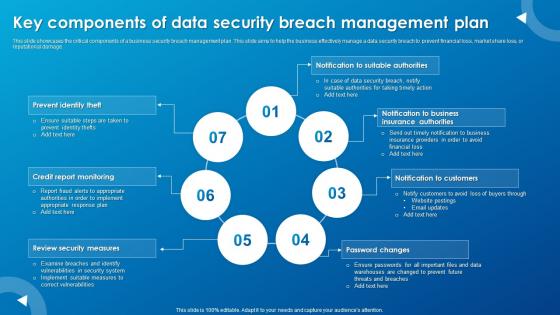 Key Components Of Data Security Breach Management Plan
Key Components Of Data Security Breach Management PlanThis slide showcases the critical components of a business security breach management plan. This slide aims to help the business effectively manage a data security breach to prevent financial loss, market share loss, or reputational damage.Introducing our premium set of slides with Key Components Of Data Security Breach Management Plan. Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Prevent Identity, Credit Report Monitoring, Review Security Measures. So download instantly and tailor it with your information.
-
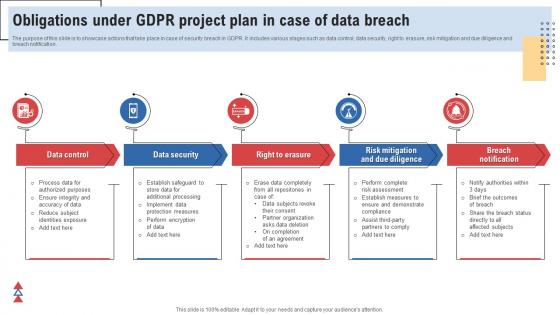 Obligations Under GDPR Project Plan In Case Of Data Breach
Obligations Under GDPR Project Plan In Case Of Data BreachThe purpose of this slide is to showcase actions that take place in case of security breach in GDPR. It includes various stages such as data control, data security, right to erasure, risk mitigation and due diligence and breach notification. Introducing our premium set of slides with Obligations Under GDPR Project Plan In Case Of Data Breach. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Control, Security, Notification. So download instantly and tailor it with your information.
-
 Icon For Investigation Of Data Breach With Digital Forensic
Icon For Investigation Of Data Breach With Digital ForensicIntroducing our Icon For Investigation Of Data Breach With Digital Forensic set of slides. The topics discussed in these slides are Investigation Data, Breach With Digital Forensic. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 K81 Data Breach Prevention And Mitigation Strategies For Businesses For Table Of Contents
K81 Data Breach Prevention And Mitigation Strategies For Businesses For Table Of ContentsIntroducing K81 Data Breach Prevention And Mitigation Strategies For Businesses For Table Of Contents to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Data Breach Prevention, Mitigation Strategies For Businesses, Data Loss Prevention Tools, using this template. Grab it now to reap its full benefits.
-
 Data Breach Prevention Immediate And Long Term Impact Of Data Security Breach
Data Breach Prevention Immediate And Long Term Impact Of Data Security BreachThis slide outlines the immediate and longstanding expenses associated with data breaches. The direct business costs include government fines, public relations costs, attorney fees, cybersecurity investigations, operational disruption, etc. Present the topic in a bit more detail with this Data Breach Prevention Immediate And Long Term Impact Of Data Security Breach. Use it as a tool for discussion and navigation on Customer Breach Notifications, Damaged Brand Reputation, Public Relations Costs, Operational Disruption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Breach Prevention Major Consequences Of Data Breach Cyber Attack
Data Breach Prevention Major Consequences Of Data Breach Cyber AttackThis slide demonstrates the impact of data breach attacks on individuals and organizations. The main consequences of the data breach are financial loss, reputational damage, legal matters, identity theft, and intellectual property loss. Introducing Data Breach Prevention Major Consequences Of Data Breach Cyber Attack to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Intellectual Property Loss, Financial Loss, Reputational Damage, Legal Consequences, using this template. Grab it now to reap its full benefits.
-
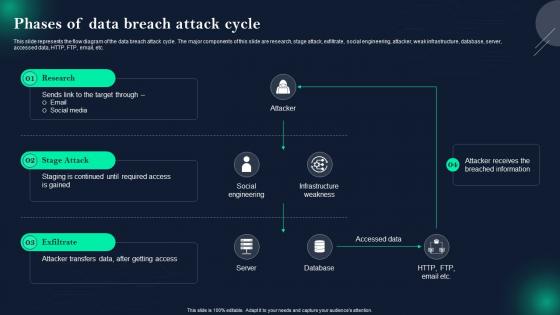 Data Breach Prevention Phases Of Data Breach Attack Cycle
Data Breach Prevention Phases Of Data Breach Attack CycleThis slide represents the flow diagram of the data breach attack cycle. The major components of this slide are research, stage attack, exfiltrate, social engineering, attacker, weak infrastructure, database, server, accessed data, HTTP, FTP, email, etc. Deliver an outstanding presentation on the topic using this Data Breach Prevention Phases Of Data Breach Attack Cycle. Dispense information and present a thorough explanation of Infrastructure Weakness, Accessed Data, Social Engineering, Attacker Transfers Data using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Breach Prevention Types Of Information Leaked In Data Breach
Data Breach Prevention Types Of Information Leaked In Data BreachThis slide outlines the different forms of information loss in a data security breach. The major types of data leaked are financial data, medical or personal health information, Personally Identifiable Information, vulnerable and sensitive data, etc. Introducing Data Breach Prevention Types Of Information Leaked In Data Breach to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Financial Data, Intellectual Property, Vulnerable And Sensitive Information, Personally Identifiable Information, using this template. Grab it now to reap its full benefits.
-
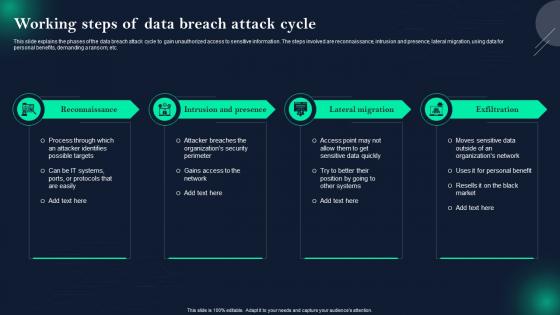 Data Breach Prevention Working Steps Of Data Breach Attack Cycle
Data Breach Prevention Working Steps Of Data Breach Attack CycleThis slide explains the phases of the data breach attack cycle to gain unauthorized access to sensitive information. The steps involved are reconnaissance, intrusion and presence, lateral migration, using data for personal benefits, demanding a ransom, etc. Introducing Data Breach Prevention Working Steps Of Data Breach Attack Cycle to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Reconnaissance, Intrusion And Presence, Lateral Migration, Exfiltration , using this template. Grab it now to reap its full benefits.
-
 Table Of Contents For Data Breach Prevention And Mitigation Strategies For Businesses
Table Of Contents For Data Breach Prevention And Mitigation Strategies For BusinessesIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Data Breach Prevention And Mitigation Strategies For Businesses. This template helps you present information on ten stages. You can also present information on Data Breach Prevention Tools, Data Breach Response Plan, Prevention And Mitigation, Training And Budget using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
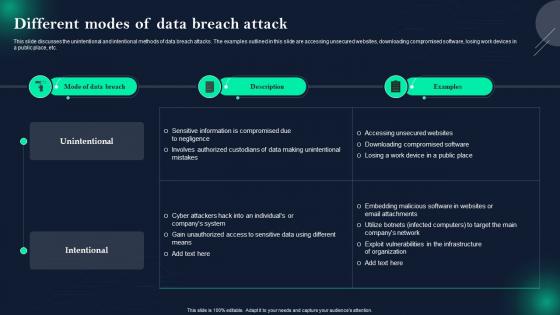 Data Breach Prevention And Mitigation Different Modes Of Data Breach Attack
Data Breach Prevention And Mitigation Different Modes Of Data Breach AttackThis slide discusses the unintentional and intentional methods of data breach attacks. The examples outlined in this slide are accessing unsecured websites, downloading compromised software, losing work devices in a public place, etc. Deliver an outstanding presentation on the topic using this Data Breach Prevention And Mitigation Different Modes Of Data Breach Attack. Dispense information and present a thorough explanation of Unintentional And Intentional Methods, Data Breach Attacks, Unsecured Websites, Downloading Compromised Software, Losing Work Devices using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Breach Prevention And Mitigation Major Types Of Data Security Breaches
Data Breach Prevention And Mitigation Major Types Of Data Security BreachesThis slide discusses the significant categories of information loss. The purpose of this slide is to describe several types of data security breaches. These include human error, device loss, cyberattacks, internal breaches, etc. Deliver an outstanding presentation on the topic using this Data Breach Prevention And Mitigation Major Types Of Data Security Breaches. Dispense information and present a thorough explanation of Social Engineering Attacks, IT Team Misconfiguring Servers, Disgruntled Employees, Gain Unauthorized Access using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Breach Prevention And Mitigation Overview Of Various Targets Of Data Breach
Data Breach Prevention And Mitigation Overview Of Various Targets Of Data BreachThis slide represents information about several data breach targets and types of data compromised. These targets are organizations and businesses, government agencies, healthcare providers, financial institutions, individuals, websites, online platforms, etc. Present the topic in a bit more detail with this Data Breach Prevention And Mitigation Overview Of Various Targets Of Data Breach. Use it as a tool for discussion and navigation on Organizations And Businesses, Healthcare Providers, Educational Institutions, Websites And Online Platforms. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Improving IoT Device Cybersecurity To Prevent Data Breaches Table Of Contents IoT SS
Improving IoT Device Cybersecurity To Prevent Data Breaches Table Of Contents IoT SSIntroducing Improving IoT Device Cybersecurity To Prevent Data Breaches Table Of Contents IoT SS to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on General, Strategies, Security, using this template. Grab it now to reap its full benefits.
-
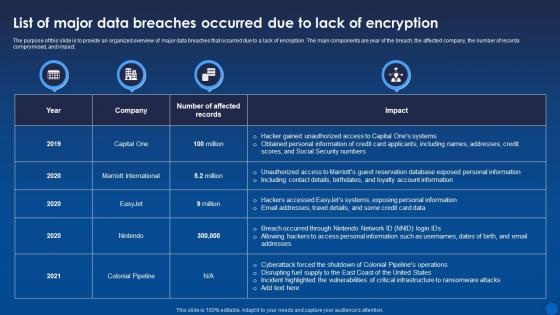 List Of Major Data Breaches Occurred Due To Lack Of Encryption Encryption For Data Privacy In Digital Age It
List Of Major Data Breaches Occurred Due To Lack Of Encryption Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to provide an organized overview of major data breaches that occurred due to a lack of encryption. The main components are year of the breach, the affected company, the number of records compromised, and impact. Present the topic in a bit more detail with this List Of Major Data Breaches Occurred Due To Lack Of Encryption Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Compromised, Encryption, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
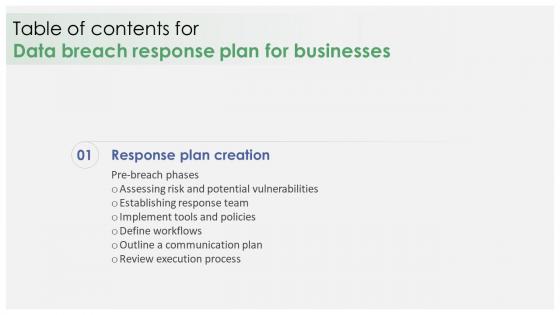 Data Breach Response Plan For Businesses For Table Of Contents
Data Breach Response Plan For Businesses For Table Of ContentsPresent the topic in a bit more detail with this Data Breach Response Plan For Businesses For Table Of Contents. Use it as a tool for discussion and navigation on Establishing Response Team, Implement Tools And Policies, Define Workflows, Outline A Communication Plan. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Breach Response Plan Possible Causes Of Data Breach Attack
Data Breach Response Plan Possible Causes Of Data Breach AttackThis slide highlights the reasons behind the success of data breach attack. These include phishing attacks, unpatched software, malware, insider threats, third-party vulnerabilities, SQL Structured Query Language injections, unsecured APIs, etc. Deliver an outstanding presentation on the topic using this Data Breach Response Plan Possible Causes Of Data Breach Attack. Dispense information and present a thorough explanation of Phishing Attacks, Unpatched Software, Third Party Vulnerabilities, Structured Query Language using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
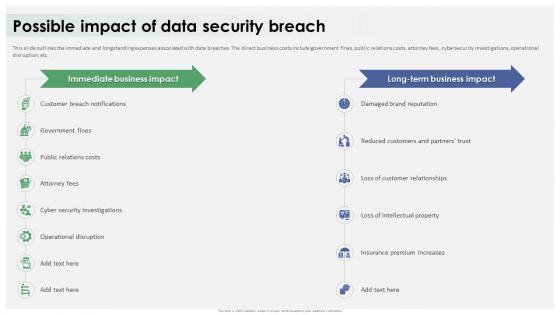 Data Breach Response Plan Possible Impact Of Data Security Breach
Data Breach Response Plan Possible Impact Of Data Security BreachThis slide outlines the immediate and longstanding expenses associated with data breaches. The direct business costs include government fines, public relations costs, attorney fees, cybersecurity investigations, operational disruption, etc. Present the topic in a bit more detail with this Data Breach Response Plan Possible Impact Of Data Security Breach. Use it as a tool for discussion and navigation on Customer Breach Notifications, Loss Of Customer Relationships, Operational Disruption, Damaged Brand Reputation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
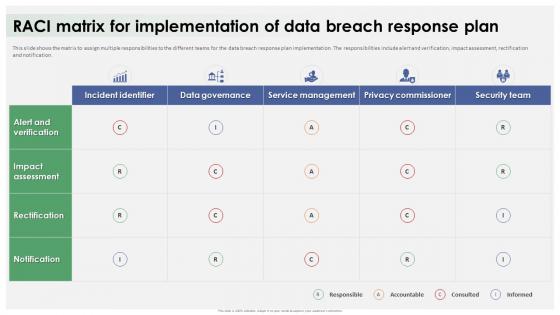 Data Breach Response Plan Raci Matrix For Implementation Of Data Breach Response Plan
Data Breach Response Plan Raci Matrix For Implementation Of Data Breach Response PlanThis slide shows the matrix to assign multiple responsibilities to the different teams for the data breach response plan implementation. The responsibilities include alert and verification, impact assessment, rectification and notification. Deliver an outstanding presentation on the topic using this Data Breach Response Plan Raci Matrix For Implementation Of Data Breach Response Plan. Dispense information and present a thorough explanation of Assign Multiple Responsibilities, Data Breach Response Plan, Rectification And Notification using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
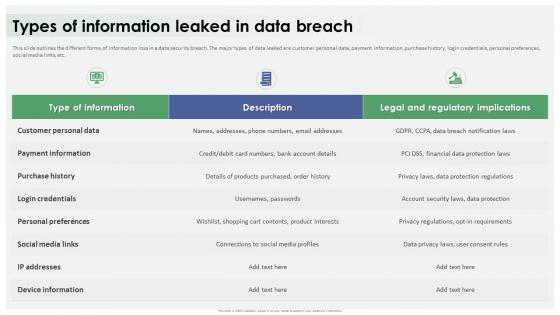 Data Breach Response Plan Types Of Information Leaked In Data Breach
Data Breach Response Plan Types Of Information Leaked In Data BreachThis slide outlines the different forms of information loss in a data security breach. The major types of data leaked are customer personal data, payment information, purchase history, login credentials, personal preferences, social media links, etc. Deliver an outstanding presentation on the topic using this Data Breach Response Plan Types Of Information Leaked In Data Breach. Dispense information and present a thorough explanation of Customer Personal Data, Payment Information, Personal Preferences, Social Media Links using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
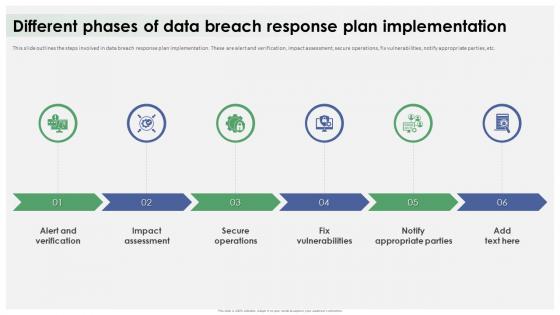 Different Phases Of Data Breach Response Plan Implementation
Different Phases Of Data Breach Response Plan ImplementationThis slide outlines the steps involved in data breach response plan implementation. These are alert and verification, impact assessment, secure operations, fix vulnerabilities, notify appropriate parties, etc. Introducing Different Phases Of Data Breach Response Plan Implementation to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Alert And Verification, Impact Assessment, Secure Operations, Fix Vulnerabilities, using this template. Grab it now to reap its full benefits.
-
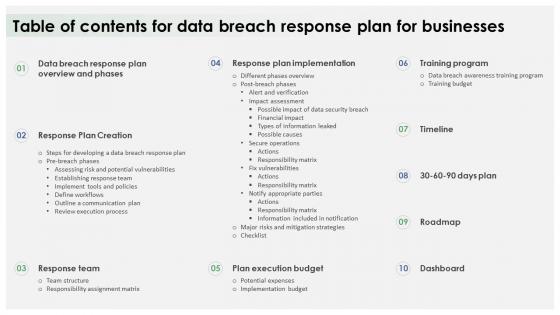 Table Of Contents For Data Breach Response Plan For Businesses
Table Of Contents For Data Breach Response Plan For BusinessesIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Data Breach Response Plan For Businesses. This template helps you present information on ten stages. You can also present information on Response Plan Creation, Response Team, Plan Execution Budget, Training Program, Response Plan Implementation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
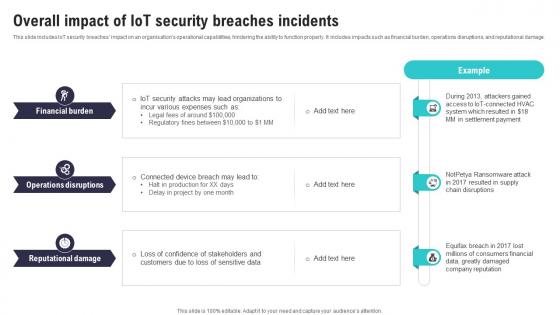 Overall Impact Of IoT Security Breaches Incidents IoT Security And Privacy Safeguarding IoT SS
Overall Impact Of IoT Security Breaches Incidents IoT Security And Privacy Safeguarding IoT SSThis slide includes IoT security breaches impact on an organisations operational capabilities, hindering the ability to function properly. It includes impacts such as financial burden, operations disruptions, and reputational damage. Deliver an outstanding presentation on the topic using this Overall Impact Of IoT Security Breaches Incidents IoT Security And Privacy Safeguarding IoT SS. Dispense information and present a thorough explanation of Operations Disruptions, Reputational Damage, Financial Burden using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
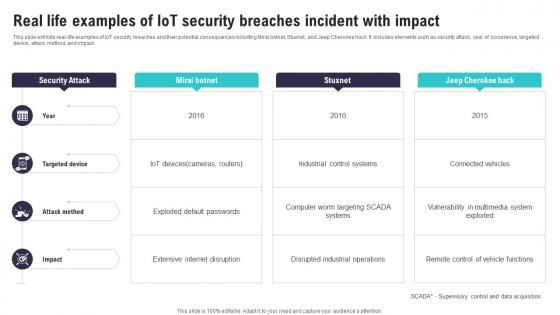 Real Life Examples Of IoT Security Breaches Incident IoT Security And Privacy Safeguarding IoT SS
Real Life Examples Of IoT Security Breaches Incident IoT Security And Privacy Safeguarding IoT SSThis slide exhibits real life examples of IoT security breaches and their potential consequences including Mirai botnet, Stuxnet, and Jeep Cherokee hack. It includes elements such as security attack, year of occurrence, targeted device, attack method, and impact. Deliver an outstanding presentation on the topic using this Real Life Examples Of IoT Security Breaches Incident IoT Security And Privacy Safeguarding IoT SS. Dispense information and present a thorough explanation of Exploited Default, Extensive Internet, Disrupted Industrial Operations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
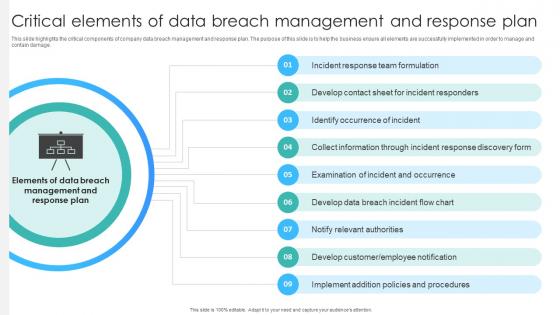 Critical Elements Of Data Breach Management And Response Plan
Critical Elements Of Data Breach Management And Response PlanThis slide highlights the critical components of company data breach management and response plan. The purpose of this slide is to help the business ensure all elements are successfully implemented in order to manage and contain damage. Presenting our set of slides with Critical Elements Of Data Breach Management And Response Plan. This exhibits information on nine stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Incident Response Team Formulation, Identify Occurrence Of Incident, Notify Relevant Authorities .
-
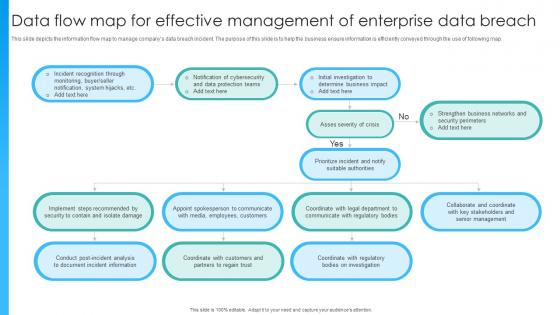 Data Flow Map For Effective Management Of Enterprise Data Breach
Data Flow Map For Effective Management Of Enterprise Data BreachThis slide depicts the information flow map to manage companys data breach incident. The purpose of this slide is to help the business ensure information is efficiently conveyed through the use of following map. Presenting our set of slides with Data Flow Map For Effective Management Of Enterprise Data Breach. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Determine Business Impact, Notification Of Cybersecurity, Incident Recognition Through.
-
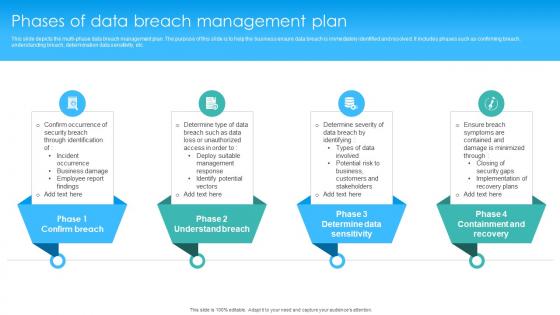 Phases Of Data Breach Management Plan
Phases Of Data Breach Management PlanThis slide depicts the multi phase data breach management plan. The purpose of this slide is to help the business ensure data breach is immediately identified and resolved. It includes phases such as confirming breach, understanding breach, determination data sensitivity, etc. Introducing our premium set of slides with Phases Of Data Breach Management Plan. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Determine Severity Of Data, Deploy Suitable Management, Identify Potential Vectors . So download instantly and tailor it with your information.
-
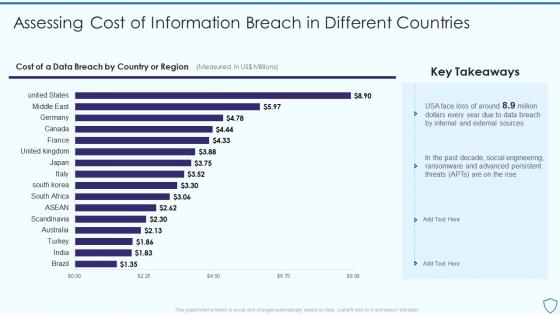 Assessing Cost Of Information Breach In Risk Assessment And Management Plan For Information Security
Assessing Cost Of Information Breach In Risk Assessment And Management Plan For Information SecurityPresent the topic in a bit more detail with this Assessing Cost Of Information Breach In Risk Assessment And Management Plan For Information Security. Use it as a tool for discussion and navigation on Information, Sources, Engineering. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
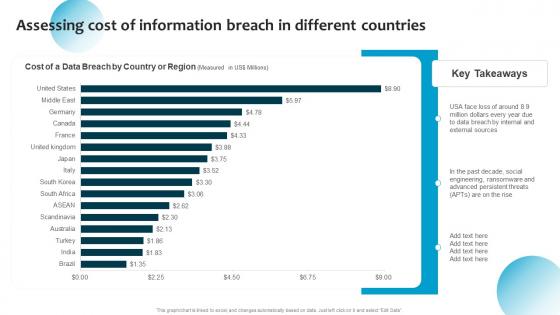 Assessing Cost Of Information Breach In Different Information System Security And Risk Administration Plan
Assessing Cost Of Information Breach In Different Information System Security And Risk Administration PlanPresent the topic in a bit more detail with this Assessing Cost Of Information Breach In Different Information System Security And Risk Administration Plan. Use it as a tool for discussion and navigation on Past Decade, Social Engineering, Advanced Persistent Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
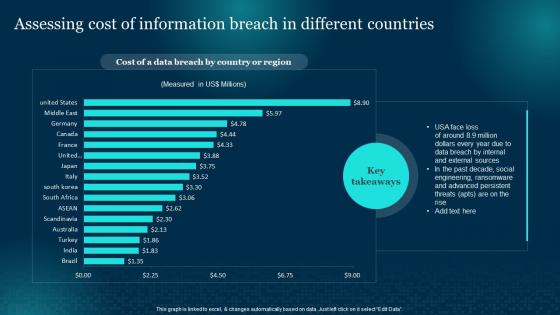 Assessing Cost Of Information Breach In Cybersecurity Risk Analysis And Management Plan
Assessing Cost Of Information Breach In Cybersecurity Risk Analysis And Management PlanPresent the topic in a bit more detail with this Assessing Cost Of Information Breach In Cybersecurity Risk Analysis And Management Plan. Use it as a tool for discussion and navigation on Information, Ransomware, Sources. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
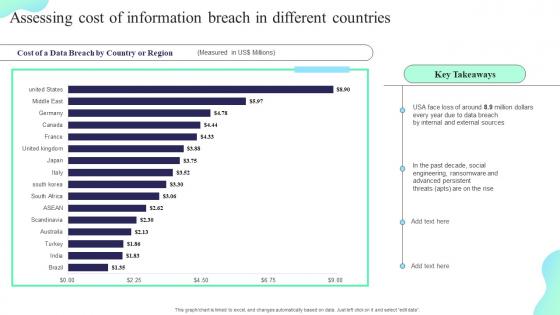 Assessing Cost Of Information Breach In Different Countries Formulating Cybersecurity Plan
Assessing Cost Of Information Breach In Different Countries Formulating Cybersecurity PlanPresent the topic in a bit more detail with this Assessing Cost Of Information Breach In Different Countries Formulating Cybersecurity Plan. Use it as a tool for discussion and navigation on Assessing, Information Breach, Different Countries. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
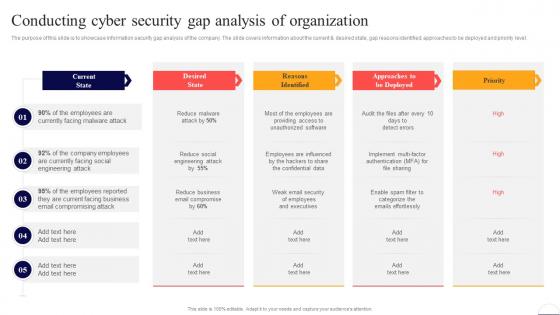 Conducting Cyber Security Gap Analysis Of Organization Preventing Data Breaches Through Cyber Security
Conducting Cyber Security Gap Analysis Of Organization Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase information security gap analysis of the company. The slide covers information about the current and desired state, gap reasons identified, approaches to be deployed and priority level. Deliver an outstanding presentation on the topic using this Conducting Cyber Security Gap Analysis Of Organization Preventing Data Breaches Through Cyber Security. Dispense information and present a thorough explanation of Current State, Email, Business using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
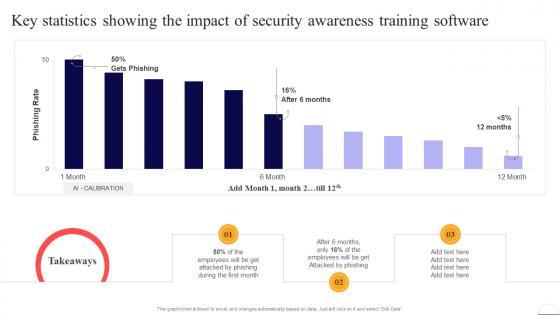 Key Statistics Showing The Impact Of Security Awarenesspreventing Data Breaches Through Cyber Security
Key Statistics Showing The Impact Of Security Awarenesspreventing Data Breaches Through Cyber SecurityPresent the topic in a bit more detail with this Key Statistics Showing The Impact Of Security Awarenesspreventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Employees, Security, Software. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
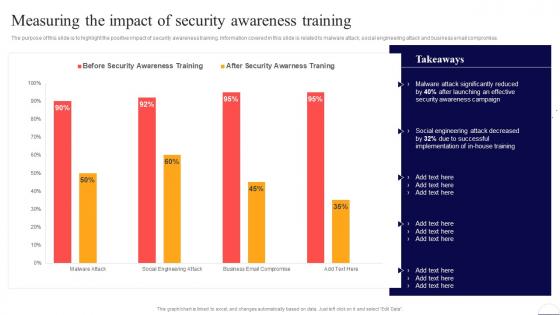 Measuring The Impact Of Security Awareness Training Preventing Data Breaches Through Cyber Security
Measuring The Impact Of Security Awareness Training Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to highlight the positive impact of security awareness training. Information covered in this slide is related to malware attack, social engineering attack and business email compromise. Present the topic in a bit more detail with this Measuring The Impact Of Security Awareness Training Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Security Awareness, Social Engineering. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
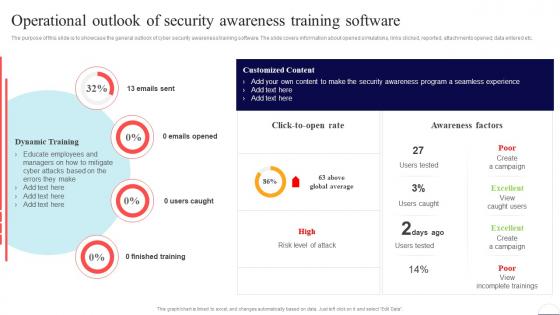 Operational Outlook Of Security Awareness Training Software Preventing Data Breaches Through Cyber Security
Operational Outlook Of Security Awareness Training Software Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase the general outlook of cyber security awareness training software. The slide covers information about opened simulations, links clicked, reported, attachments opened, data entered etc. Present the topic in a bit more detail with this Operational Outlook Of Security Awareness Training Software Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Finished Training, Awareness Factors, Training Software. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
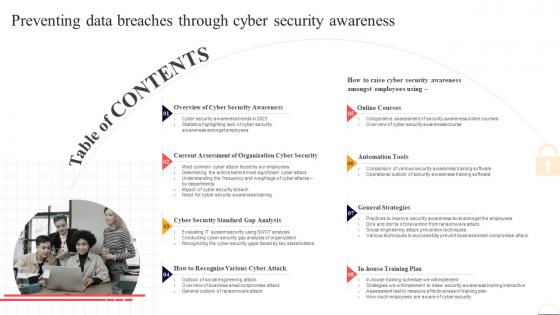 Table Of Contents For Preventing Data Breaches Through Cyber Security Awareness
Table Of Contents For Preventing Data Breaches Through Cyber Security AwarenessDeliver an outstanding presentation on the topic using this Table Of Contents For Preventing Data Breaches Through Cyber Security Awareness. Dispense information and present a thorough explanation of Cyber Security Awareness, Online Courses, Automation Tools using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
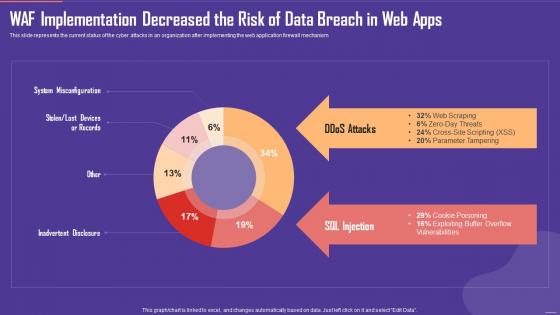 Application Firewall WAF Implementation Decreased the Risk of Data Breach in Web Apps
Application Firewall WAF Implementation Decreased the Risk of Data Breach in Web AppsThis slide represents the current status of the cyber attacks in an organization after implementing the web application firewall mechanism. Present the topic in a bit more detail with this Application Firewall WAF Implementation Decreased the Risk of Data Breach in Web Apps. Use it as a tool for discussion and navigation on SQL Injection, Ddos Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
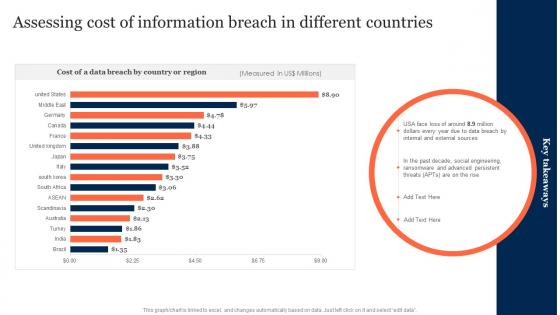 Assessing Cost Of Information Breach In Different Countries Information Security Risk Management
Assessing Cost Of Information Breach In Different Countries Information Security Risk ManagementDeliver an outstanding presentation on the topic using this Assessing Cost Of Information Breach In Different Countries Information Security Risk Management. Dispense information and present a thorough explanation of Assessing, Information Breach, Different Countries using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
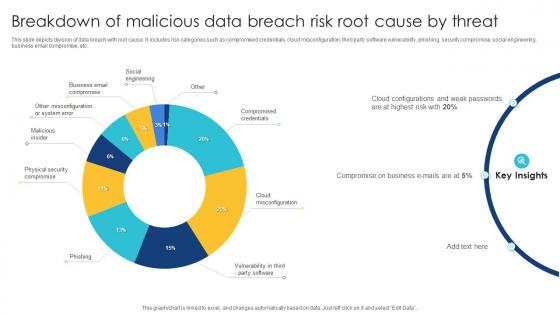 Breakdown Of Malicious Data Breach Risk Root Cause By Threat
Breakdown Of Malicious Data Breach Risk Root Cause By ThreatThis slide depicts division of data breach with root cause. It includes risk categories such as compromised credentials, cloud misconfiguration, third party software vulnerability, phishing, security compromise, social engineering, business email compromise, etc. Introducing our Breakdown Of Malicious Data Breach Risk Root Cause By Threat set of slides. The topics discussed in these slides are Social Engineering, Business Email Compromise, Malicious Insider. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
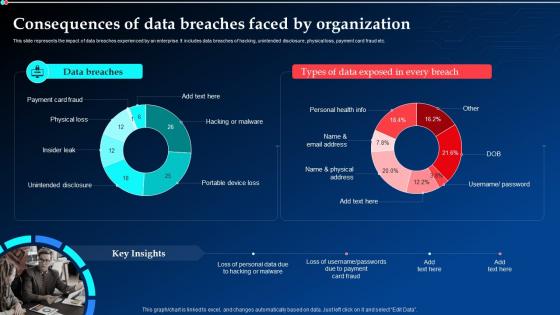 Consequences Of Data Breaches Faced By Organization Implementing Cyber Security Ppt Diagrams
Consequences Of Data Breaches Faced By Organization Implementing Cyber Security Ppt DiagramsThis slide represents the impact of data breaches experienced by an enterprise. It includes data breaches of hacking, unintended disclosure, physical loss, payment card fraud etc. Deliver an outstanding presentation on the topic using this Consequences Of Data Breaches Faced By Organization Implementing Cyber Security Ppt Diagrams. Dispense information and present a thorough explanation of Data Breaches, Consequences, Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
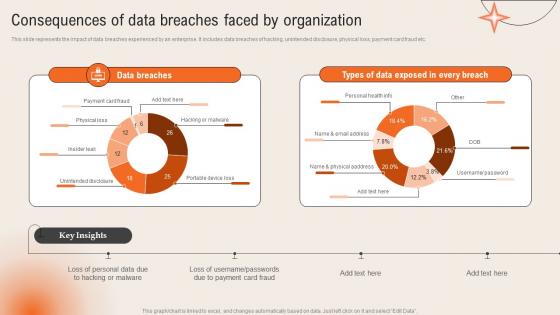 Consequences Of Data Breaches Faced By Organization Deploying Computer Security Incident Management
Consequences Of Data Breaches Faced By Organization Deploying Computer Security Incident ManagementThis slide represents the impact of data breaches experienced by an enterprise. It includes data breaches of hacking, unintended disclosure, physical loss, payment card fraud etc.Present the topic in a bit more detail with this Consequences Of Data Breaches Faced By Organization Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Unintended Disclosure, Portable Device, Hacking Malware. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
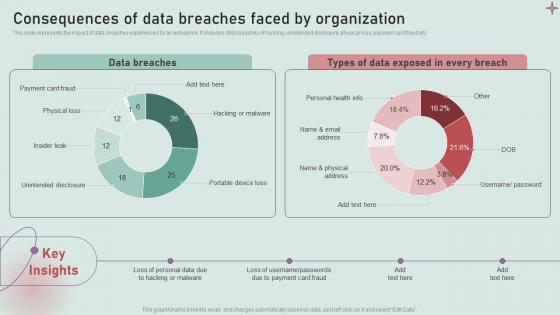 Consequences Of Data Breaches Faced By Organization Development And Implementation Of Security
Consequences Of Data Breaches Faced By Organization Development And Implementation Of SecurityThis slide represents the impact of data breaches experienced by an enterprise. It includes data breaches of hacking, unintended disclosure, physical loss, payment card fraud etc. Deliver an outstanding presentation on the topic using this Consequences Of Data Breaches Faced By Organization Development And Implementation Of Security. Dispense information and present a thorough explanation of Payment Card Fraud, Physical Loss, Insider Leak using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
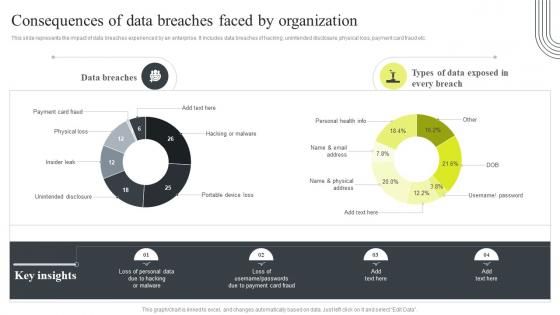 Cyber Security Attacks Response Plan Consequences Of Data Breaches Faced By Organization
Cyber Security Attacks Response Plan Consequences Of Data Breaches Faced By OrganizationThis slide represents the impact of data breaches experienced by an enterprise. It includes data breaches of hacking, unintended disclosure, physical loss, payment card fraud etc. Present the topic in a bit more detail with this Cyber Security Attacks Response Plan Consequences Of Data Breaches Faced By Organization. Use it as a tool for discussion and navigation on Consequences, Data Breaches, Unintended Disclosure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
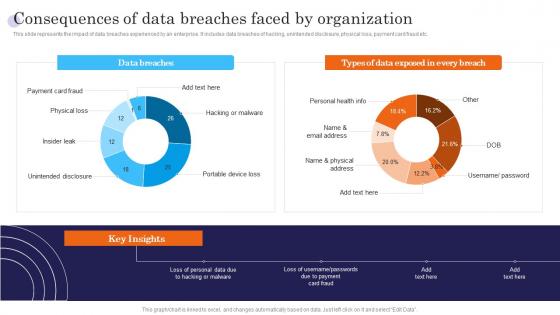 Consequences Of Data Breaches Faced By Organization Incident Response Strategies Deployment
Consequences Of Data Breaches Faced By Organization Incident Response Strategies DeploymentThis slide represents the impact of data breaches experienced by an enterprise. It includes data breaches of hacking, unintended disclosure, physical loss, payment card fraud etc. Present the topic in a bit more detail with this Consequences Of Data Breaches Faced By Organization Incident Response Strategies Deployment. Use it as a tool for discussion and navigation on Data, Consequences, Portable. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Kpi for number of major control breaches percentage of key controls ppt slide
Kpi for number of major control breaches percentage of key controls ppt slidePresenting kpi for number of major control breaches percentage of key controls ppt slide. This presentation slide shows two Key Performance Indicators or KPIs in a Dashboard style design. The first KPI that can be shown is Number of Major Internal Control Breaches. The second KPI is percentage of Key Controls. These KPI Powerpoint graphics are all data driven,and the shape automatically adjusts according to your data. Just right click on the KPI graphic,enter the right value and the shape will adjust automatically. Make a visual impact with our KPI slides.
-
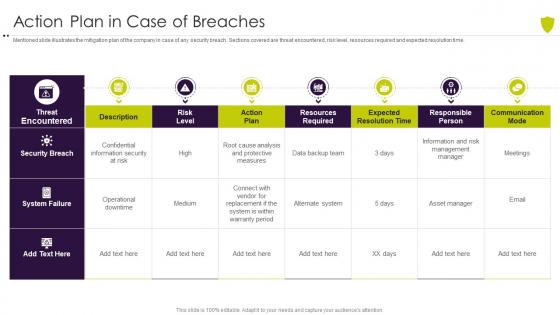 Action plan in case of breaches managing cyber risk in a digital age
Action plan in case of breaches managing cyber risk in a digital ageMentioned slide illustrates the mitigation plan of the company in case of any security breach. Sections covered are threat encountered, risk level, resources required and expected resolution time. Present the topic in a bit more detail with this Action Plan In Case Of Breaches Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Action Plan In Case Of Breaches. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
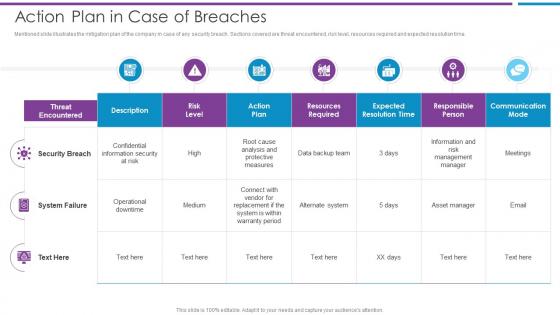 Action Plan In Case Of Breaches Risk Based Methodology To Cyber
Action Plan In Case Of Breaches Risk Based Methodology To CyberMentioned slide illustrates the mitigation plan of the company in case of any security breach. Sections covered are threat encountered, risk level, resources required and expected resolution time.Present the topic in a bit more detail with this Action Plan In Case Of Breaches Risk Based Methodology To Cyber Use it as a tool for discussion and navigation on Security Breach, Confidential Information, Resources Required This template is free to edit as deemed fit for your organization. Therefore download it now.
-
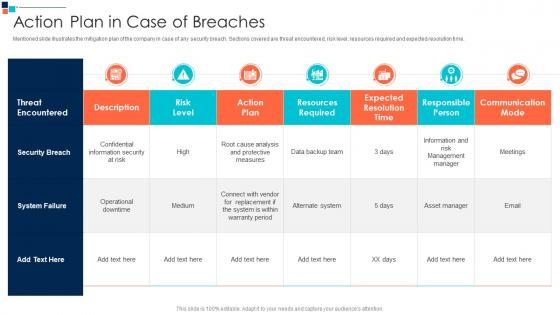 Action Plan In Case Of Breaches Introducing A Risk Based Approach To Cyber Security
Action Plan In Case Of Breaches Introducing A Risk Based Approach To Cyber SecurityMentioned slide illustrates the mitigation plan of the company in case of any security breach. Sections covered are threat encountered, risk level, resources required and expected resolution time.Present the topic in a bit more detail with this Action Plan In Case Of Breaches Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on Expected Resolution Time, Responsible Person, Communication Mode This template is free to edit as deemed fit for your organization. Therefore download it now.
-
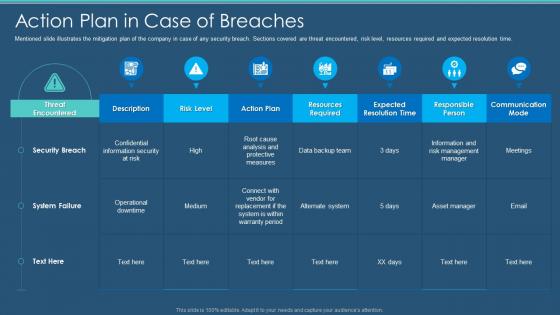 Information Security Program Cybersecurity Action Plan In Case Of Breaches
Information Security Program Cybersecurity Action Plan In Case Of BreachesMentioned slide illustrates the mitigation plan of the company in case of any security breach. Sections covered are threat encountered, risk level, resources required and expected resolution time. Deliver an outstanding presentation on the topic using this Information Security Program Cybersecurity Action Plan In Case Of Breaches. Dispense information and present a thorough explanation of Action Plan In Case Of Breaches using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
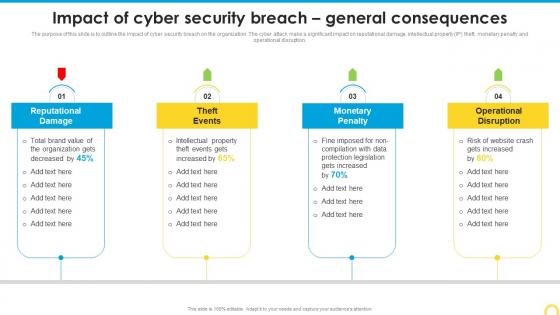 Impact Of Cyber Security Breach Building A Security Awareness Program
Impact Of Cyber Security Breach Building A Security Awareness ProgramThe purpose of this slide is to outline the impact of cyber security breach on the organization. The cyber attack make a significant impact on reputational damage, intellectual property IP theft, monetary penalty and operational disruption. Introducing Impact Of Cyber Security Breach Building A Security Awareness Program to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Reputational Damage, Monetary Penalty, Operational Disruption, using this template. Grab it now to reap its full benefits.
-
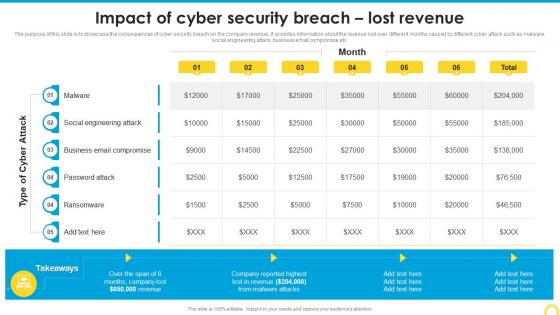 Impact Of Cyber Security Breach Lost Revenue Building A Security Awareness Program
Impact Of Cyber Security Breach Lost Revenue Building A Security Awareness ProgramThe purpose of this slide is to showcase the consequences of cyber security breach on the company revenue. It provides information about the revenue lost over different months caused by different cyber attack such as malware, social engineering attack, business email compromise etc. Present the topic in a bit more detail with this Impact Of Cyber Security Breach Lost Revenue Building A Security Awareness Program. Use it as a tool for discussion and navigation on Social Engineering Attack, Business Email Compromise, Ransomware. This template is free to edit as deemed fit for your organization. Therefore download it now.


