Powerpoint Templates and Google slides for Cyber Attack
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
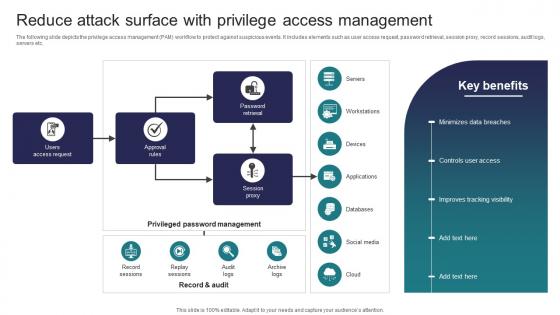 Implementing Strategies To Mitigate Cyber Security Reduce Attack Surface With Privilege Access Management
Implementing Strategies To Mitigate Cyber Security Reduce Attack Surface With Privilege Access ManagementThe following slide depicts the privilege access management PAM workflow to protect against suspicious events. It includes elements such as user access request, password retrieval, session proxy, record sessions, audit logs, servers etc. Present the topic in a bit more detail with this Implementing Strategies To Mitigate Cyber Security Reduce Attack Surface With Privilege Access Management Use it as a tool for discussion and navigation on Access Request, Approval Rules, Session Proxy This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Attack Rate In Powerpoint And Google Slides Cpb
Cyber Security Attack Rate In Powerpoint And Google Slides CpbPresenting Cyber Security Attack Rate In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase six stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cyber Security Attack Rate. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
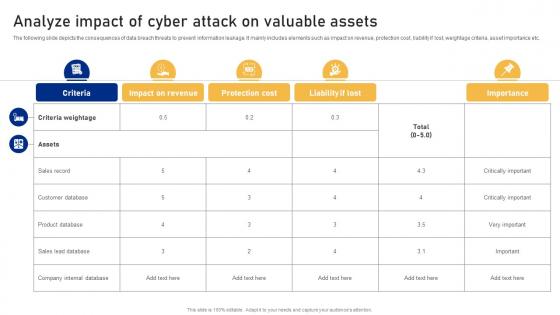 Analyze Impact Of Cyber Attack On Valuable Assets Cyber Risk Assessment
Analyze Impact Of Cyber Attack On Valuable Assets Cyber Risk AssessmentThe following slide depicts the consequences of data breach threats to prevent information leakage. It mainly includes elements such as impact on revenue, protection cost, liability if lost, weightage criteria, asset importance etc. Deliver an outstanding presentation on the topic using this Analyze Impact Of Cyber Attack On Valuable Assets Cyber Risk Assessment Dispense information and present a thorough explanation of Customer Database, Product Database, Sales Lead Database using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
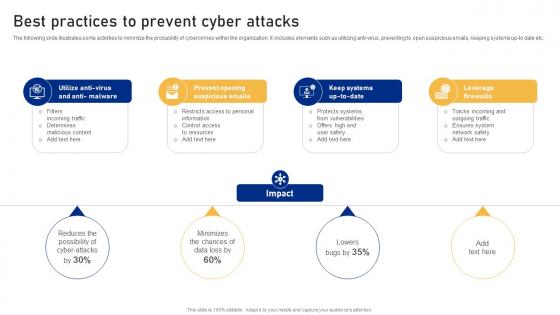 Best Practices To Prevent Cyber Attacks Cyber Risk Assessment
Best Practices To Prevent Cyber Attacks Cyber Risk AssessmentThe following slide illustrates some activities to minimize the probability of cybercrimes within the organization. It includes elements such as utilizing anti-virus, preventing to open suspicious emails, keeping systems up-to date etc. Introducing Best Practices To Prevent Cyber Attacks Cyber Risk Assessment to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Prevent Opening, Suspicious Emails, Leverage Firewalls using this template. Grab it now to reap its full benefits.
-
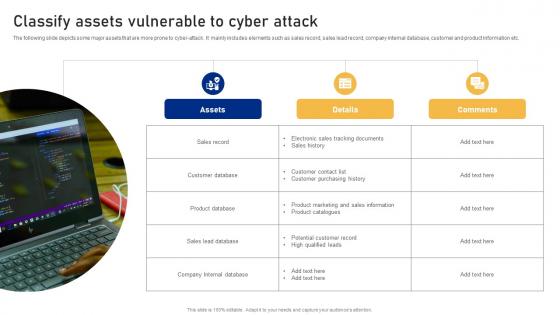 Classify Assets Vulnerable To Cyber Attack Cyber Risk Assessment
Classify Assets Vulnerable To Cyber Attack Cyber Risk AssessmentThe following slide depicts some major assets that are more prone to cyber-attack. It mainly includes elements such as sales record, sales lead record, company internal database, customer and product information etc. Introducing Classify Assets Vulnerable To Cyber Attack Cyber Risk Assessment to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Customer Database, Product Database, Sales Lead Database using this template. Grab it now to reap its full benefits.
-
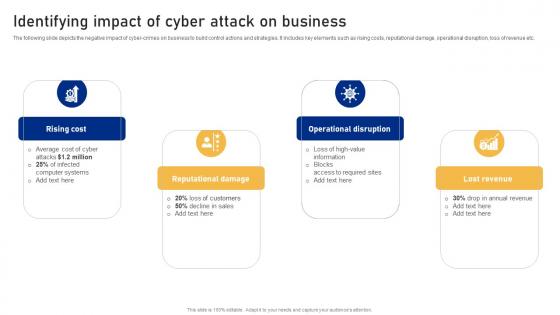 Identifying Impact Of Cyber Attack On Business Cyber Risk Assessment
Identifying Impact Of Cyber Attack On Business Cyber Risk AssessmentThe following slide depicts the negative impact of cyber-crimes on business to build control actions and strategies. It includes key elements such as rising costs, reputational damage, operational disruption, loss of revenue etc. Increase audience engagement and knowledge by dispensing information using Identifying Impact Of Cyber Attack On Business Cyber Risk Assessment This template helps you present information on four stages. You can also present information on Rising Cost, Reputational Damage, Operational Disruption using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
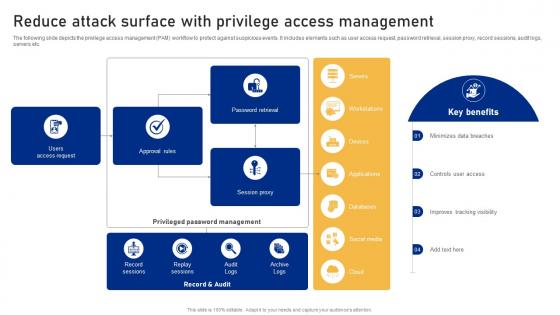 Reduce Attack Surface With Privilege Access Management Cyber Risk Assessment
Reduce Attack Surface With Privilege Access Management Cyber Risk AssessmentThe following slide depicts the privilege access management PAM workflow to protect against suspicious events. It includes elements such as user access request, password retrieval, session proxy, record sessions, audit logs, servers etc. Deliver an outstanding presentation on the topic using this Reduce Attack Surface With Privilege Access Management Cyber Risk Assessment Dispense information and present a thorough explanation of Users Access Request, Record Sessions, Session Proxy using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
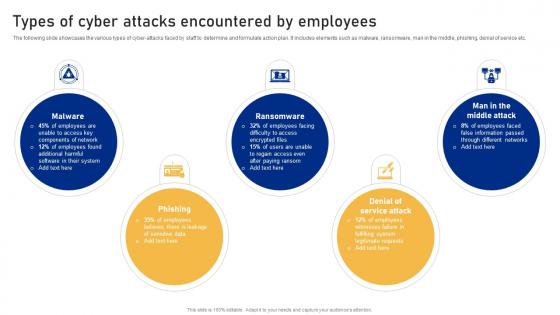 Types Of Cyber Attacks Encountered By Employees Cyber Risk Assessment
Types Of Cyber Attacks Encountered By Employees Cyber Risk AssessmentThe following slide showcases the various types of cyber-attacks faced by staff to determine and formulate action plan. It includes elements such as malware, ransomware, man in the middle, phishing, denial of service etc. Introducing Types Of Cyber Attacks Encountered By Employees Cyber Risk Assessment to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Malware, Phishing, Ransomware, Denial Of Service Attack using this template. Grab it now to reap its full benefits.
-
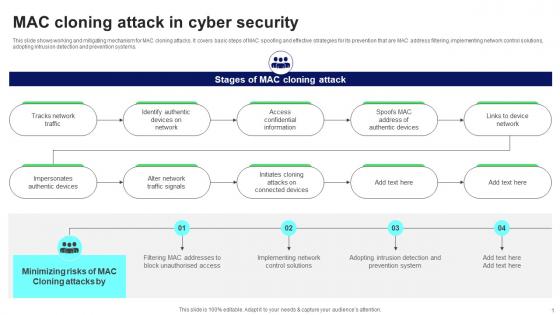 MAC Cloning Attack In Cyber Security
MAC Cloning Attack In Cyber SecurityThis slide shows working and mitigating mechanism for MAC cloning attacks. It covers basic steps of MAC spoofing and effective strategies for its prevention that are MAC address filtering, implementing network control solutions, adopting intrusion detection and prevention systems. Presenting our well structured MAC Cloning Attack In Cyber Security. The topics discussed in this slide are Network Traffic, Traffic Signals, Confidential Information. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
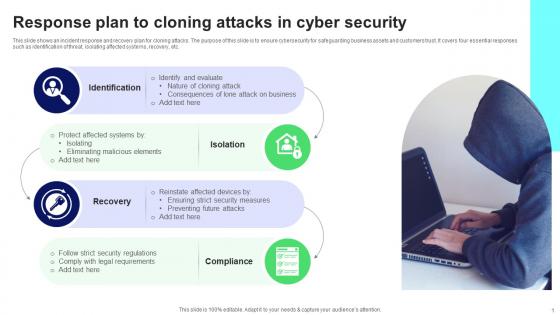 Response Plan To Cloning Attacks In Cyber Security
Response Plan To Cloning Attacks In Cyber SecurityThis slide shows an incident response and recovery plan for cloning attacks. The purpose of this slide is to ensure cybersecurity for safeguarding business assets and customers trust. It covers four essential responses such as identification of threat, isolating affected systems, recovery, etc. Presenting our set of slides with name Response Plan To Cloning Attacks In Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cloning Attack, Malicious Elements, Security Measures.
-
 Types Of Cyber Attacks Faced By Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Types Of Cyber Attacks Faced By Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various types of cyber attacks that significantly damage the organization resources and reputation. Different types of attacks faced are Malware, Phishing, Man in middle attack, SQL injection etc. Increase audience engagement and knowledge by dispensing information using Types Of Cyber Attacks Faced By Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. This template helps you present information on five stages. You can also present information on Phishing, SQL Injection, Organization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Threat Intelligence Icon To Detect Digital Attacks
Cyber Threat Intelligence Icon To Detect Digital AttacksIntroducing our premium set of slides with Cyber Threat Intelligence Icon To Detect Digital Attacks Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Threat Intelligence Icon, Detect Digital Attacks So download instantly and tailor it with your information.
-
 Cyber Security Attack Control Icon
Cyber Security Attack Control IconIntroducing our premium set of slides with Cyber Security Attack Control Icon Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Security Attack Control Icon So download instantly and tailor it with your information.
-
 Web Security Icon To Prevent Cyber Attacks
Web Security Icon To Prevent Cyber AttacksPresenting our set of slides with Web Security Icon To Prevent Cyber Attacks This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Web Security Icon, Prevent Cyber Attacks
-
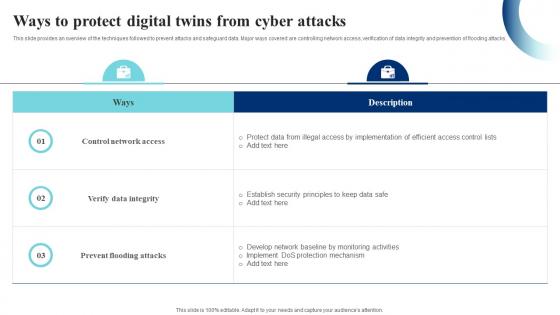 Ways To Protect Digital Twins From Cyber Attacks IoT Digital Twin Technology IOT SS
Ways To Protect Digital Twins From Cyber Attacks IoT Digital Twin Technology IOT SSThis slide provides an overview of the techniques followed to prevent attacks and safeguard data. Major ways covered are controlling network access, verification of data integrity and prevention of flooding attacks. Present the topic in a bit more detail with this Ways To Protect Digital Twins From Cyber Attacks IoT Digital Twin Technology IOT SS. Use it as a tool for discussion and navigation on Control Network Access, Prevent Flooding Attacks, Verify Data Integrity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
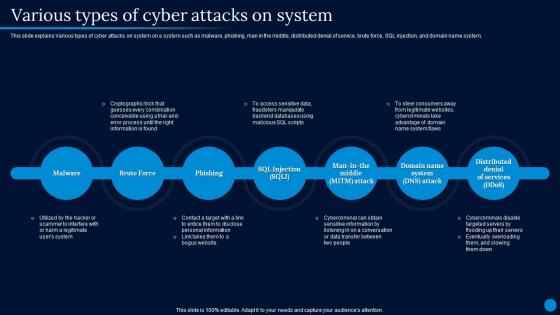 Current Trending Technologies Various Types Of Cyber Attacks On System
Current Trending Technologies Various Types Of Cyber Attacks On SystemThis slide explains Various types of cyber attacks on system on a system such as malware, phishing, man in the middle, distributed denial of service, brute force, SQL injection, and domain name system. Introducing Current Trending Technologies Various Types Of Cyber Attacks On System to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Cyber Attacks On System, Distributed Denial Of Service, Cryptographic Trick, Cybercriminals Disable Targeted Servers, using this template. Grab it now to reap its full benefits.
-
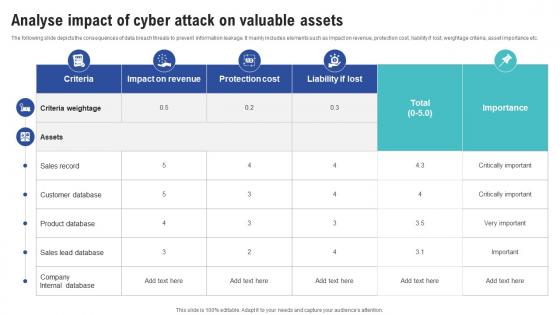 Analyse Impact Of Cyber Attack On Valuable Assets Creating Cyber Security Awareness
Analyse Impact Of Cyber Attack On Valuable Assets Creating Cyber Security AwarenessThe following slide depicts the consequences of data breach threats to prevent information leakage. It mainly includes elements such as impact on revenue, protection cost, liability if lost, weightage criteria, asset importance etc. Deliver an outstanding presentation on the topic using this Analyse Impact Of Cyber Attack On Valuable Assets Creating Cyber Security Awareness Dispense information and present a thorough explanation of Impact On Revenue, Protection Cost using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
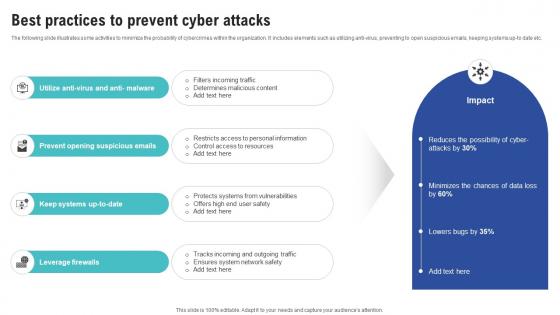 Best Practices To Prevent Cyber Attacks Creating Cyber Security Awareness
Best Practices To Prevent Cyber Attacks Creating Cyber Security AwarenessThe following slide illustrates some activities to minimize the probability of cybercrimes within the organization. It includes elements such as utilizing anti-virus, preventing to open suspicious emails, keeping systems up-to date etc. Introducing Best Practices To Prevent Cyber Attacks Creating Cyber Security Awareness to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Opening Suspicious Emails, Leverage Firewalls using this template. Grab it now to reap its full benefits.
-
 Classify Assets Vulnerable To Cyber Attack Creating Cyber Security Awareness
Classify Assets Vulnerable To Cyber Attack Creating Cyber Security AwarenessThe following slide depicts some major assets that are more prone to cyber-attack. It mainly includes elements such as sales record, sales lead record, company internal database, customer and product information etc. Introducing Classify Assets Vulnerable To Cyber Attack Creating Cyber Security Awareness to increase your presentation threshold. Encompassed with One stages, this template is a great option to educate and entice your audience. Dispence information on Sales Record, Customer Database, Product Database using this template. Grab it now to reap its full benefits.
-
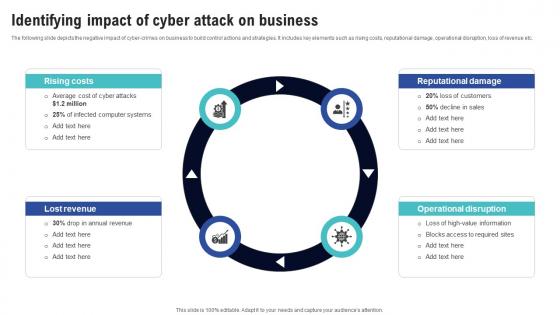 Identifying Impact Of Cyber Attack On Business Creating Cyber Security Awareness
Identifying Impact Of Cyber Attack On Business Creating Cyber Security AwarenessThe following slide depicts the negative impact of cyber-crimes on business to build control actions and strategies. It includes key elements such as rising costs, reputational damage, operational disruption, loss of revenue etc. Increase audience engagement and knowledge by dispensing information using Identifying Impact Of Cyber Attack On Business Creating Cyber Security Awareness This template helps you present information on Four stages. You can also present information on Small Size, Ransomware Attack, Cyber Attacks, Security Precautionary Measures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
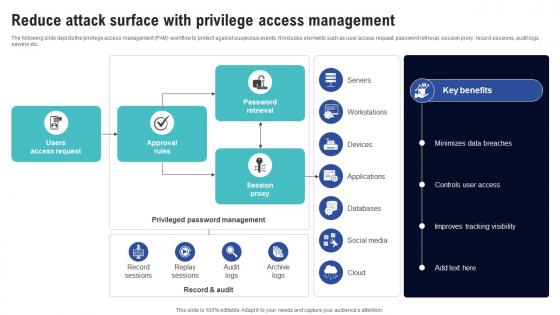 Reduce Attack Surface With Privilege Access Management Creating Cyber Security Awareness
Reduce Attack Surface With Privilege Access Management Creating Cyber Security AwarenessThe following slide depicts the privilege access management PAM workflow to protect against suspicious events. It includes elements such as user access request, password retrieval, session proxy, record sessions, audit logs, servers etc. Deliver an outstanding presentation on the topic using this Reduce Attack Surface With Privilege Access Management Creating Cyber Security Awareness Dispense information and present a thorough explanation of Time Consuming Process, Incremental Backup using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
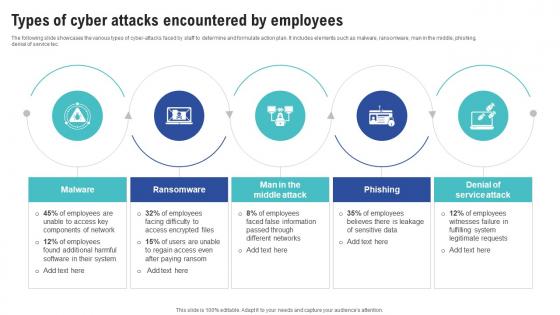 Types Of Cyber Attacks Encountered By Employees Creating Cyber Security Awareness
Types Of Cyber Attacks Encountered By Employees Creating Cyber Security AwarenessThe following slide showcases the various types of cyber-attacks faced by staff to determine and formulate action plan. It includes elements such as malware, ransomware, man in the middle, phishing, denial of service tec. Increase audience engagement and knowledge by dispensing information using Types Of Cyber Attacks Encountered By Employees Creating Cyber Security Awareness This template helps you present information on Five stages. You can also present information on Malware, Ransomware, Middle Attack, Phishing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
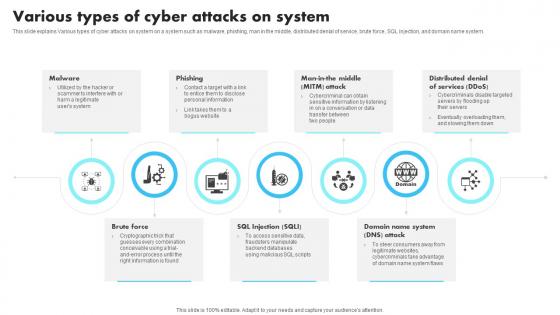 New Technologies Various Types Of Cyber Attacks On System
New Technologies Various Types Of Cyber Attacks On SystemThis slide explains Various types of cyber attacks on system on a system such as malware, phishing, man in the middle, distributed denial of service, brute force, SQL injection, and domain name system. Introducing New Technologies Various Types Of Cyber Attacks On System to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Malware, Phishing, Distributed, using this template. Grab it now to reap its full benefits.
-
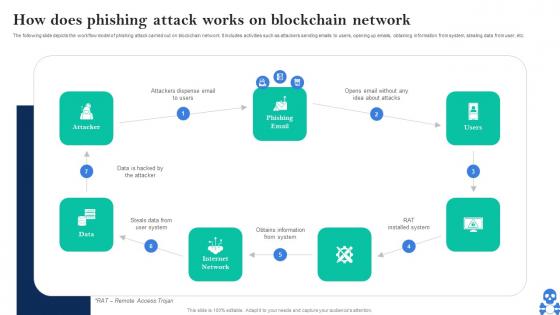 Cyber Threats In Blockchain How Does Phishing Attack Works On Blockchain Network BCT SS V
Cyber Threats In Blockchain How Does Phishing Attack Works On Blockchain Network BCT SS VThe following slide depicts the workflow model of phishing attack carried out on blockchain network. It includes activities such as attackers sending emails to users, opening up emails, obtaining information from system, stealing data from user, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain How Does Phishing Attack Works On Blockchain Network BCT SS V This template helps you present information on Seven stages. You can also present information on Steals Data From User System, Obtains Information From System using this PPT design. This layout is completely editable so personaize it now
-
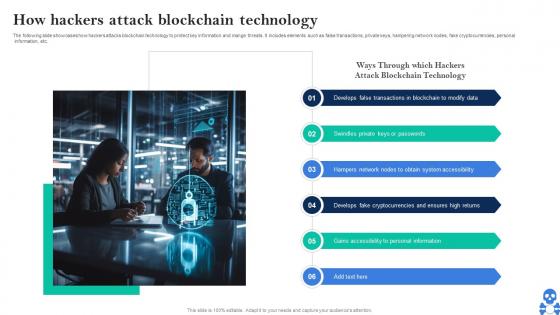 Cyber Threats In Blockchain How Hackers Attack Blockchain Technology BCT SS V
Cyber Threats In Blockchain How Hackers Attack Blockchain Technology BCT SS VThe following slide showcases how hackers attacks blockchain technology to protect key information and mange threats. It includes elements such as false transactions, private keys, hampering network nodes, fake cryptocurrencies, personal information, etc. Introducing Cyber Threats In Blockchain How Hackers Attack Blockchain Technology BCT SS V to increase your presentation threshold. Encompassed with Six stages, this template is a great option to educate and entice your audience. Dispence information on Blockchain To Modify Data, Keys Or Passwords, Obtain System Accessibility using this template. Grab it now to reap its full benefits.
-
 Cyber Threats In Blockchain Impact Of 51 Percent Attack On Bitcoin And Blockchain Transactions BCT SS V
Cyber Threats In Blockchain Impact Of 51 Percent Attack On Bitcoin And Blockchain Transactions BCT SS VThe following slide depicts the key effect of 51percent attack on bitcoin and blockchain technology to plan actions and minimize its impact. It includes element such as delayed transactions, network disruption, low miner rewards, market volatility, reputation, credibility, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Impact Of 51 Percent Attack On Bitcoin And Blockchain Transactions BCT SS V This template helps you present information on Five stages. You can also present information on Delayed Transactions, Network Disruption, Low Miner Rewards using this PPT design. This layout is completely editable so personaize it now
-
 Cyber Threats In Blockchain Impact Of Ddos Attack On Targeted Servers BCT SS V
Cyber Threats In Blockchain Impact Of Ddos Attack On Targeted Servers BCT SS VThe following slide depicts the adverse impact of denial of service DDoS attack to determine malicious attempt to hamper targeted server. It includes elements such as software crashes, node failure, network congestion, bloated ledger, etc. Introducing Cyber Threats In Blockchain Impact Of Ddos Attack On Targeted Servers BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Software Crashes, Node Failures, Network Congestion using this template. Grab it now to reap its full benefits.
-
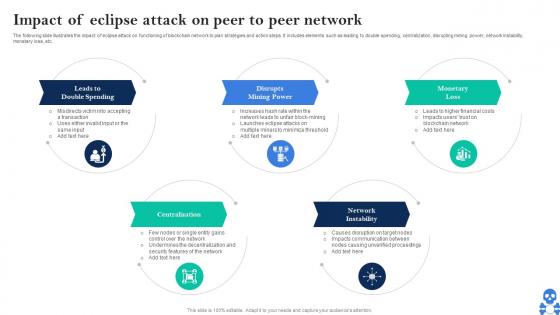 Cyber Threats In Blockchain Impact Of Eclipse Attack On Peer To Peer Network BCT SS V
Cyber Threats In Blockchain Impact Of Eclipse Attack On Peer To Peer Network BCT SS VThe following slide illustrates the impact of eclipse attack on functioning of blockchain network to plan strategies and action steps. It includes elements such as leading to double spending, centralization, disrupting mining power, network instability, monetary loss, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Impact Of Eclipse Attack On Peer To Peer Network BCT SS V This template helps you present information on Five stages. You can also present information on Leads To Double Spending, Disrupts, Mining Power using this PPT design. This layout is completely editable so personaize it now
-
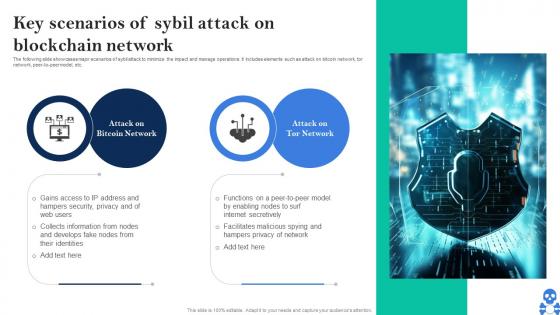 Cyber Threats In Blockchain Key Scenarios Of Sybil Attack On Blockchain Network BCT SS V
Cyber Threats In Blockchain Key Scenarios Of Sybil Attack On Blockchain Network BCT SS VThe following slide showcases major scenarios of sybil attack to minimize the impact and manage operations. It includes elements such as attack on bitcoin network, tor network, peer-to-peer model, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Key Scenarios Of Sybil Attack On Blockchain Network BCT SS V Dispense information and present a thorough explanation of Bitcoin Network, Attack On Tor Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
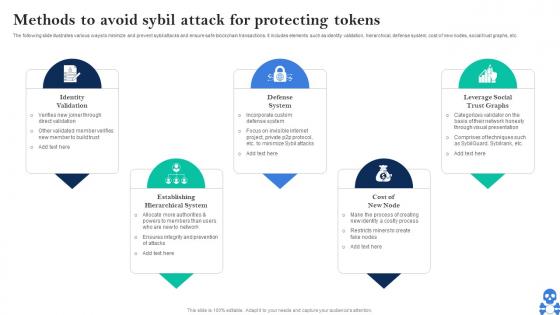 Cyber Threats In Blockchain Methods To Avoid Sybil Attack For Protecting Tokens BCT SS V
Cyber Threats In Blockchain Methods To Avoid Sybil Attack For Protecting Tokens BCT SS VThe following slide illustrates various ways to minimize and prevent sybil attacks and ensure safe blockchain transactions. It includes elements such as identity validation, hierarchical, defense system, cost of new nodes, social trust graphs, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Methods To Avoid Sybil Attack For Protecting Tokens BCT SS V This template helps you present information on Five stages. You can also present information on Identity Validation, Defense System, Cost Of New Node using this PPT design. This layout is completely editable so personaize it now
-
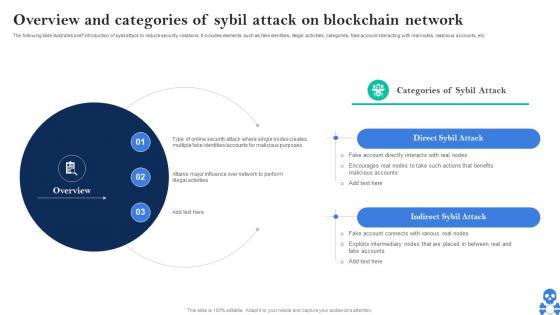 Cyber Threats In Blockchain Overview And Categories Of Sybil Attack On Blockchain Network BCT SS V
Cyber Threats In Blockchain Overview And Categories Of Sybil Attack On Blockchain Network BCT SS VThe following slide illustrates brief introduction of sybil attack to reduce security violations. It includes elements such as fake identities, illegal activities, categories, fake account interacting with real nodes, malicious accounts, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Overview And Categories Of Sybil Attack On Blockchain Network BCT SS V This template helps you present information on Two stages. You can also present information on Direct Sybil Attack, Indirect Sybil Attack using this PPT design. This layout is completely editable so personaize it now
-
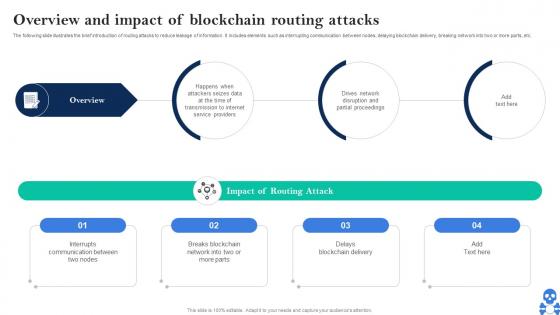 Cyber Threats In Blockchain Overview And Impact Of Blockchain Routing Attacks BCT SS V
Cyber Threats In Blockchain Overview And Impact Of Blockchain Routing Attacks BCT SS VThe following slide illustrates the brief introduction of routing attacks to reduce leakage of information. It includes elements such as interrupting communication between nodes, delaying blockchain delivery, breaking network into two or more parts, etc. Introducing Cyber Threats In Blockchain Overview And Impact Of Blockchain Routing Attacks BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Service Providers, Partial Proceedings, Routing Attack using this template. Grab it now to reap its full benefits.
-
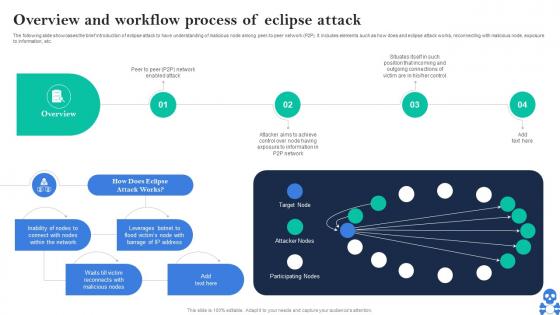 Cyber Threats In Blockchain Overview And Workflow Process Of Eclipse Attack BCT SS V
Cyber Threats In Blockchain Overview And Workflow Process Of Eclipse Attack BCT SS VThe following slide showcases the brief introduction of eclipse attack to have understanding of malicious node among peer-to peer network P2P. It includes elements such as how does and eclipse attack works, reconnecting with malicious node, exposure to information, etc. Introducing Cyber Threats In Blockchain Overview And Workflow Process Of Eclipse Attack BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Target Node, Attacker Nodes, Participating Nodes using this template. Grab it now to reap its full benefits.
-
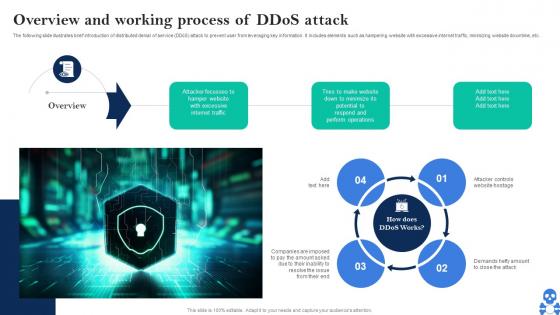 Cyber Threats In Blockchain Overview And Working Process Of Ddos Attack BCT SS V
Cyber Threats In Blockchain Overview And Working Process Of Ddos Attack BCT SS VThe following slide illustrates brief introduction of distributed denial of service DDoS attack to prevent user from leveraging key information. It includes elements such as hampering website with excessive internet traffic, minimizing website downtime, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Overview And Working Process Of Ddos Attack BCT SS V This template helps you present information on Three stages. You can also present information on Internet Traffic, Perform Operations, Website Hostage using this PPT design. This layout is completely editable so personaize it now
-
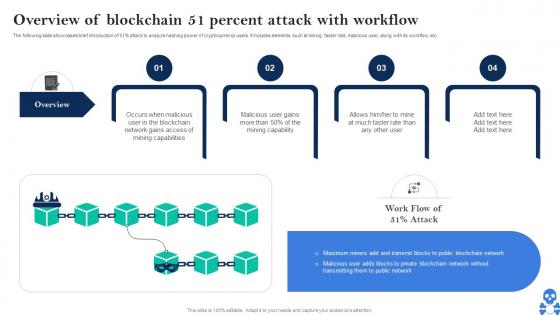 Cyber Threats In Blockchain Overview Of Blockchain 51 Percent Attack With Workflow BCT SS V
Cyber Threats In Blockchain Overview Of Blockchain 51 Percent Attack With Workflow BCT SS VThe following slide showcases brief introduction of 51percent attack to analyze hashing power of cryptocurrency users. It includes elements such at mining faster rate, malicious user, along with its workflow, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Overview Of Blockchain 51 Percent Attack With Workflow BCT SS V This template helps you present information on Four stages. You can also present information on Mining Capability, Mining Capabilities, Much Faster Rate using this PPT design. This layout is completely editable so personaize it now
-
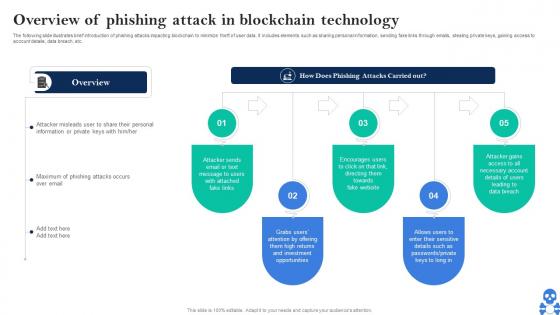 Cyber Threats In Blockchain Overview Of Phishing Attack In Blockchain Technology BCT SS V
Cyber Threats In Blockchain Overview Of Phishing Attack In Blockchain Technology BCT SS VThe following slide illustrates brief introduction of phishing attacks impacting blockchain to minimize theft of user data. It includes elements such as sharing personal information, sending fake links through emails, stealing private keys, gaining access to account details, data breach, etc. Introducing Cyber Threats In Blockchain Overview Of Phishing Attack In Blockchain Technology BCT SS V to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Opportunities, Fake Website, Data Breach using this template. Grab it now to reap its full benefits.
-
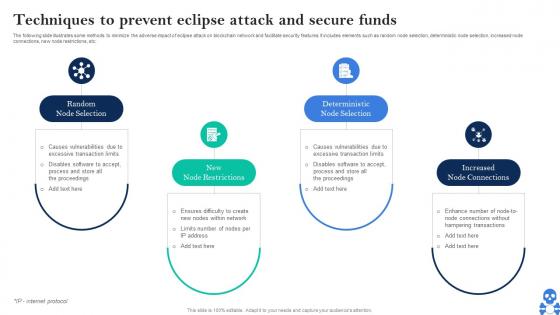 Cyber Threats In Blockchain Techniques To Prevent Eclipse Attack And Secure Funds BCT SS V
Cyber Threats In Blockchain Techniques To Prevent Eclipse Attack And Secure Funds BCT SS VThe following slide illustrates some methods to minimize the adverse impact of eclipse attack on blockchain network and facilitate security features. It includes elements such as random node selection, deterministic node selection, increased node connections, new node restrictions, etc. Introducing Cyber Threats In Blockchain Techniques To Prevent Eclipse Attack And Secure Funds BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Mining Capability, Mining Capabilities, Much Faster Rate using this template. Grab it now to reap its full benefits.
-
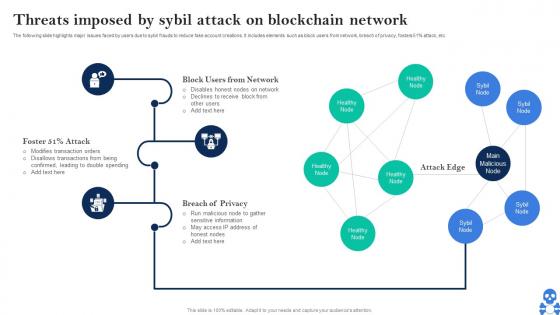 Cyber Threats In Blockchain Threats Imposed By Sybil Attack On Blockchain Network BCT SS V
Cyber Threats In Blockchain Threats Imposed By Sybil Attack On Blockchain Network BCT SS VThe following slide highlights major issues faced by users due to sybil frauds to reduce fake account creations. It includes elements such as block users from network, breach of privacy, fosters 51percent attack, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Threats Imposed By Sybil Attack On Blockchain Network BCT SS V Dispense information and present a thorough explanation of Block Users From Network, Breach Of Privacy, Attack Edge using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
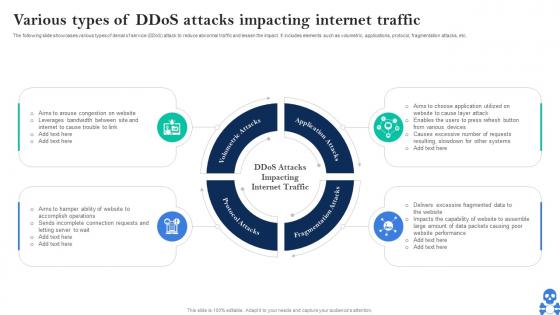 Cyber Threats In Blockchain Various Types Of Ddos Attacks Impacting Internet Traffic BCT SS V
Cyber Threats In Blockchain Various Types Of Ddos Attacks Impacting Internet Traffic BCT SS VThe following slide showcases various types of denial of service DDoS attack to reduce abnormal traffic and lessen the impact. It includes elements such as volumetric, applications, protocol, fragmentation attacks, etc. Introducing Cyber Threats In Blockchain Various Types Of Ddos Attacks Impacting Internet Traffic BCT SS V to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Volumetric Attacks, Application Attacks, Fragmentation Attacks using this template. Grab it now to reap its full benefits.
-
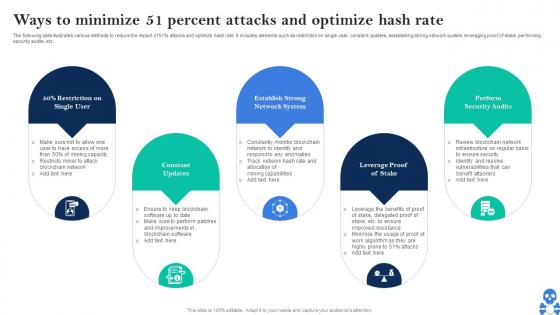 Cyber Threats In Blockchain Ways To Minimize 51 Percent Attacks And Optimize Hash Rate BCT SS V
Cyber Threats In Blockchain Ways To Minimize 51 Percent Attacks And Optimize Hash Rate BCT SS VThe following slide illustrates various methods to reduce the impact of 51percent attacks and optimize hash rate. It includes elements such as restriction on single user, constant updates, establishing strong network system, leveraging proof of stake, performing security audits, etc. Introducing Cyber Threats In Blockchain Ways To Minimize 51 Percent Attacks And Optimize Hash Rate BCT SS V to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Constant Updates, Network System, Perform Security Audits using this template. Grab it now to reap its full benefits.
-
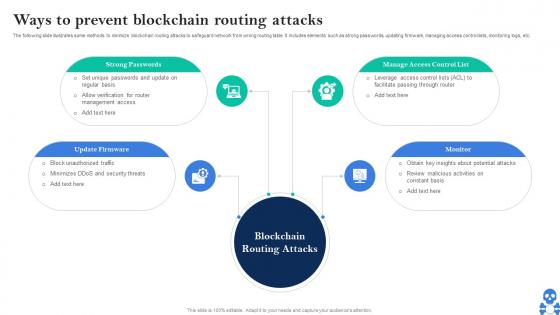 Cyber Threats In Blockchain Ways To Prevent Blockchain Routing Attacks BCT SS V
Cyber Threats In Blockchain Ways To Prevent Blockchain Routing Attacks BCT SS VThe following slide illustrates some methods to minimize blockchain routing attacks to safeguard network from wrong routing table. It includes elements such as strong passwords, updating firmware, managing access control lists, monitoring logs, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Ways To Prevent Blockchain Routing Attacks BCT SS V This template helps you present information on Four stages. You can also present information on Blockchain Routing Attacks, Strong Passwords, Manage Access Control List using this PPT design. This layout is completely editable so personaize it now
-
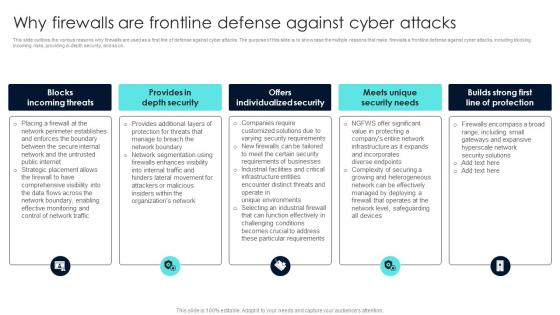 Firewall Network Security Why Firewalls Are Frontline Defense Against Cyber Attacks
Firewall Network Security Why Firewalls Are Frontline Defense Against Cyber AttacksThis slide outlines the various reasons why firewalls are used as a first line of defense against cyber attacks. The purpose of this slide is to showcase the multiple reasons that make firewalls a frontline defense against cyber attacks, including blocking incoming risks, providing in-depth security, and so on. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Why Firewalls Are Frontline Defense Against Cyber Attacks This template helps you present information on Five stages. You can also present information on Blocks Incoming Threats, Provides In Depth Security, Offers Individualized Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
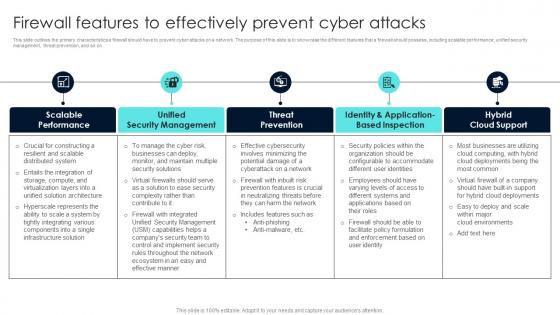 Firewall Network Security Firewall Features To Effectively Prevent Cyber Attacks
Firewall Network Security Firewall Features To Effectively Prevent Cyber AttacksThis slide outlines the primary characteristics a firewall should have to prevent cyber attacks on a network. The purpose of this slide is to showcase the different features that a firewall should possess, including scalable performance, unified security management, threat prevention, and so on. Introducing Firewall Network Security Firewall Features To Effectively Prevent Cyber Attacks to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on URL Categories By Traffic, Traffic Source IP, Traffic Desintation IP using this template. Grab it now to reap its full benefits.
-
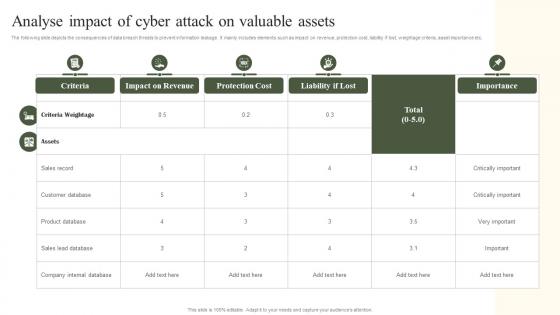 Analyse Impact Of Cyber Attack On Valuable Assets Implementing Cyber Risk Management Process
Analyse Impact Of Cyber Attack On Valuable Assets Implementing Cyber Risk Management ProcessThe following slide depicts the consequences of data breach threats to prevent information leakage. It mainly includes elements such as impact on revenue, protection cost, liability if lost, weightage criteria, asset importance etc. Present the topic in a bit more detail with this Analyse Impact Of Cyber Attack On Valuable Assets Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Criteria, Impact On Revenue, Protection Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
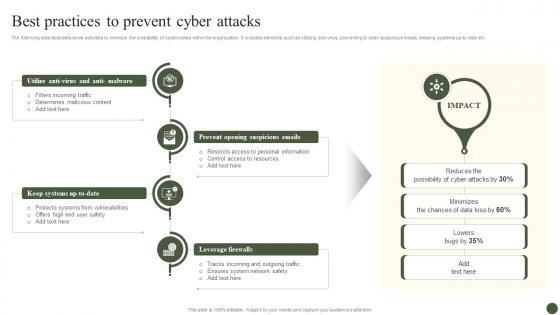 Best Practices To Prevent Cyber Attacks Implementing Cyber Risk Management Process
Best Practices To Prevent Cyber Attacks Implementing Cyber Risk Management ProcessThe following slide illustrates some activities to minimize the probability of cybercrimes within the organization. It includes elements such as utilizing anti-virus, preventing to open suspicious emails, keeping systems up-to date etc. Introducing Best Practices To Prevent Cyber Attacks Implementing Cyber Risk Management Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Utilize Anti Virus, Prevent Opening Suspicious, Leverage Firewalls, using this template. Grab it now to reap its full benefits.
-
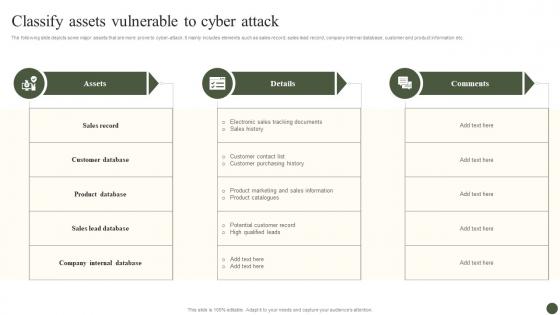 Classify Assets Vulnerable To Cyber Attack Implementing Cyber Risk Management Process
Classify Assets Vulnerable To Cyber Attack Implementing Cyber Risk Management ProcessThe following slide depicts some major assets that are more prone to cyber-attack. It mainly includes elements such as sales record, sales lead record, company internal database, customer and product information etc. Present the topic in a bit more detail with this Classify Assets Vulnerable To Cyber Attack Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Assets, Details, Comments. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
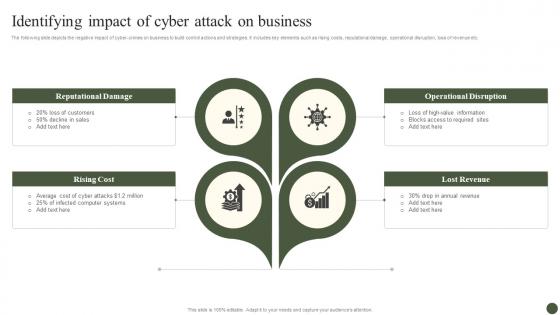 Identifying Impact Of Cyber Attack On Business Implementing Cyber Risk Management Process
Identifying Impact Of Cyber Attack On Business Implementing Cyber Risk Management ProcessThe following slide depicts the negative impact of cyber-crimes on business to build control actions and strategies. It includes key elements such as rising costs, reputational damage, operational disruption, loss of revenue etc. Increase audience engagement and knowledge by dispensing information using Identifying Impact Of Cyber Attack On Business Implementing Cyber Risk Management Process. This template helps you present information on four stages. You can also present information on Reputational Damage, Rising Cost, Operational Disruption using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
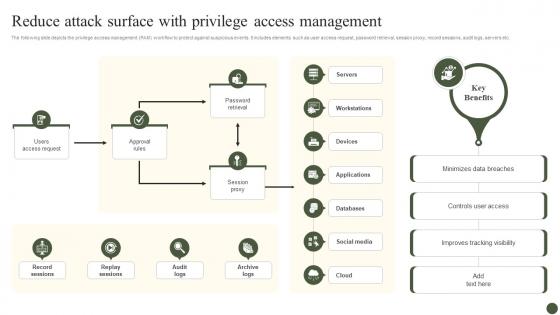 Reduce Attack Surface With Privilege Access Management Implementing Cyber Risk Management Process
Reduce Attack Surface With Privilege Access Management Implementing Cyber Risk Management ProcessThe following slide depicts the privilege access management PAM workflow to protect against suspicious events. It includes elements such as user access request, password retrieval, session proxy, record sessions, audit logs, servers etc. Deliver an outstanding presentation on the topic using this Reduce Attack Surface With Privilege Access Management Implementing Cyber Risk Management Process. Dispense information and present a thorough explanation of Users Access Request, Approval Rules, Session Proxy using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Types Of Cyber Attacks Encountered By Employees Implementing Cyber Risk Management Process
Types Of Cyber Attacks Encountered By Employees Implementing Cyber Risk Management ProcessThe following slide showcases the various types of cyber-attacks faced by staff to determine and formulate action plan. It includes elements such as malware, ransomware, man in the middle, phishing, denial of service etc. Introducing Types Of Cyber Attacks Encountered By Employees Implementing Cyber Risk Management Process to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Malware, Ransomware, Phishing, using this template. Grab it now to reap its full benefits.
-
 SAP Security Measures To Prevent Cyber Attacks
SAP Security Measures To Prevent Cyber AttacksPresenting our set of slides with SAP Security Measures To Prevent Cyber Attacks. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on SAP Security, Measures To Prevent, Cyber Attacks.
-
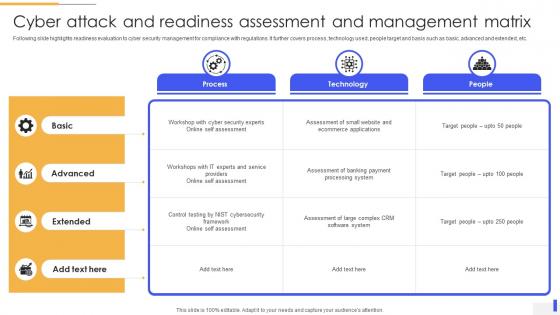 Cyber Attack And Readiness Assessment And Management Matrix
Cyber Attack And Readiness Assessment And Management MatrixFollowing slide highlights readiness evaluation to cyber security management for compliance with regulations. It further covers process, technology used, people target and basis such as basic, advanced and extended, etc. Introducing our Cyber Attack And Readiness Assessment And Management Matrix set of slides. The topics discussed in these slides are Process, Technology, People. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Common Cyber Attacks On Smart Contracts Ppt Slides Graphics Download
Common Cyber Attacks On Smart Contracts Ppt Slides Graphics DownloadThe purpose of this slide is to highlight the cyber attacks on smart contracts these include reentrancy attacks, transaction order dependence, force-feeding, etc. Deliver an outstanding presentation on the topic using this Common Cyber Attacks On Smart Contracts Ppt Slides Graphics Download. Dispense information and present a thorough explanation of Reentrancy Attacks, Force Feeding Attacks, Transaction Order Dependence, Denial Of Service using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
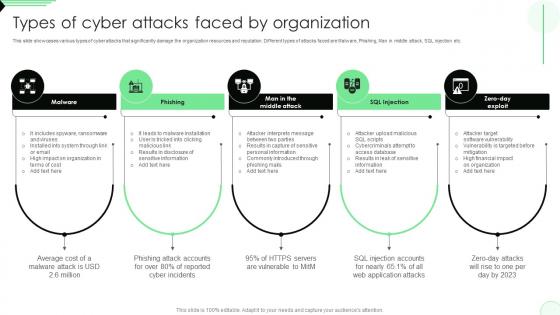 Types Of Cyber Attacks Faced By Organization Opportunities And Risks Of ChatGPT AI SS V
Types Of Cyber Attacks Faced By Organization Opportunities And Risks Of ChatGPT AI SS VThis slide showcases various types of cyber attacks that significantly damage the organization resources and reputation. Different types of attacks faced are Malware, Phishing, Man in middle attack, SQL injection etc. Introducing Types Of Cyber Attacks Faced By Organization Opportunities And Risks Of ChatGPT AI SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Phishing, Malware, SQL Injection, using this template. Grab it now to reap its full benefits.
-
 Types Of Cyber Attacks Faced By Organization Impact Of Generative AI SS V
Types Of Cyber Attacks Faced By Organization Impact Of Generative AI SS VThis slide showcases various types of cyber attacks that significantly damage the organization resources and reputation. Different types of attacks faced are Malware, Phishing, Man in middle attack, SQL injection etc. Introducing Types Of Cyber Attacks Faced By Organization Impact Of Generative AI SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Malware, Phishing, Injection, using this template. Grab it now to reap its full benefits.
-
 Reducing Attack Surface By Cyber Security Mesh Icon
Reducing Attack Surface By Cyber Security Mesh IconIntroducing our premium set of slides with Reducing Attack Surface By Cyber Security Mesh Icon Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Reducing Attack Surface, Cyber Security Mesh Icon. So download instantly and tailor it with your information.
-
 Security Incident Icon To Prevent Cyber Attacks
Security Incident Icon To Prevent Cyber AttacksPresenting our set of slides with Security Incident Icon To Prevent Cyber Attacks. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Incident, Prevent Cyber Attacks.
-
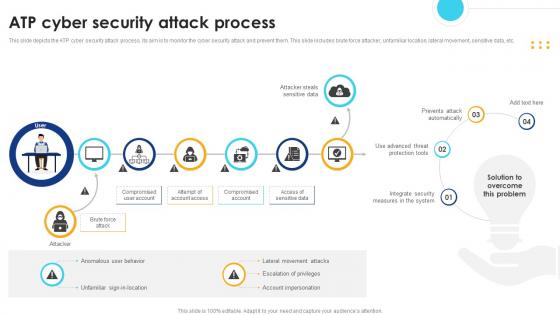 ATP Cyber Security Attack Process
ATP Cyber Security Attack ProcessThis slide depicts the ATP cyber security attack process. Its aim is to monitor the cyber security attack and prevent them. This slide includes brute force attacker, unfamiliar location, lateral movement, sensitive data, etc. Presenting our set of slides with name ATP Cyber Security Attack Process. This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Integrate Security, Measures In The System, Prevents Attack Automatically, Access Of Sensitive Data.
-
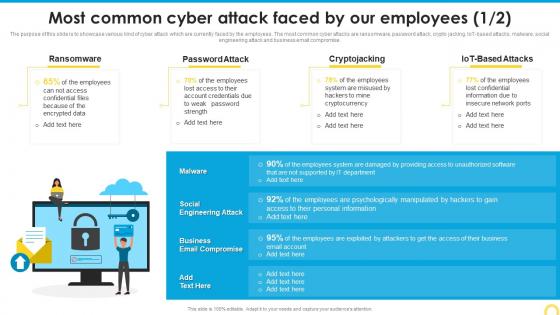 Most Common Cyber Attack Building A Security Awareness Program
Most Common Cyber Attack Building A Security Awareness ProgramThe purpose of this slide is to showcase various kind of cyber attack which are currently faced by the employees. The most common cyber attacks are ransomware, password attack, crypto jacking, IoT based attacks, malware, social engineering attack and business email compromise. Present the topic in a bit more detail with this Most Common Cyber Attack Building A Security Awareness Program. Use it as a tool for discussion and navigation on Ransomware, Password Attack, Cryptojacking. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
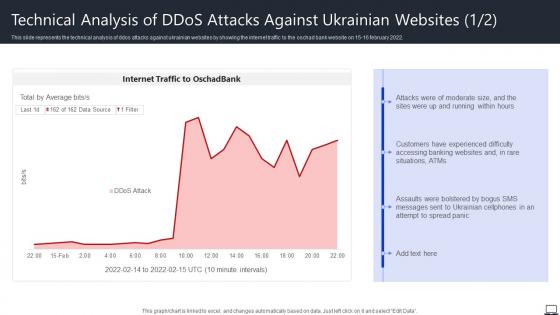 Technical Analysis Of DDOS Attacks Against Ukrainian Websites String Of Cyber Attacks Against
Technical Analysis Of DDOS Attacks Against Ukrainian Websites String Of Cyber Attacks AgainstThis slide represents the technical analysis of ddos attacks against ukrainian websites by showing the internet traffic to the oschad bank website on 15 16 february 2022. Deliver an outstanding presentation on the topic using this Technical Analysis Of DDOS Attacks Against Ukrainian Websites String Of Cyber Attacks Against. Dispense information and present a thorough explanation of Customers, Accessing Banking, Websites using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
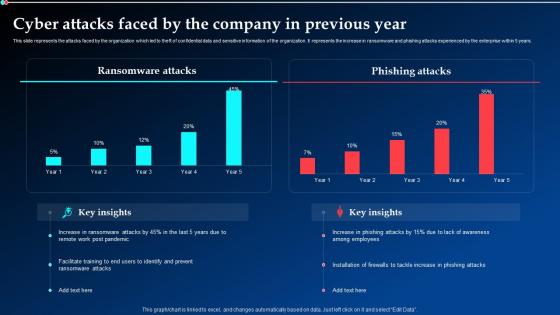 Cyber Attacks Faced By The Company In Previous Year Implementing Cyber Security Ppt Demonstration
Cyber Attacks Faced By The Company In Previous Year Implementing Cyber Security Ppt DemonstrationThis slide represents the attacks faced by the organization which led to theft of confidential data and sensitive information of the organization. It represents the increase in ransomware and phishing attacks experienced by the enterprise within 5 years. Present the topic in a bit more detail with this Cyber Attacks Faced By The Company In Previous Year Implementing Cyber Security Ppt Demonstration. Use it as a tool for discussion and navigation on Ransomware Attacks, Phishing Attacks, Previous Year. This template is free to edit as deemed fit for your organization. Therefore download it now.



