Powerpoint Templates and Google slides for Cyber Attack
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
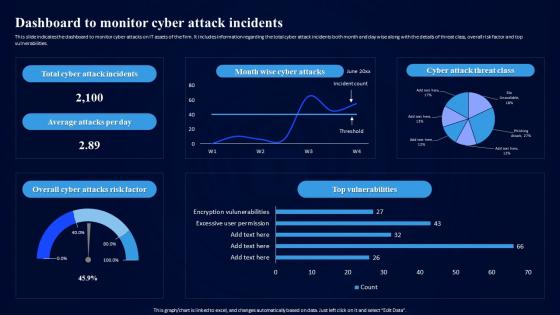 Cybersecurity Risk Assessment Program Dashboard To Monitor Cyber Attack Incidents
Cybersecurity Risk Assessment Program Dashboard To Monitor Cyber Attack IncidentsThis slide indicates the dashboard to monitor cyber attacks on IT assets of the firm. It includes information regarding the total cyber attack incidents both month and day wise along with the details of threat class, overall risk factor and top vulnerabilities. Present the topic in a bit more detail with this Cybersecurity Risk Assessment Program Dashboard To Monitor Cyber Attack Incidents. Use it as a tool for discussion and navigation on Dashboard To Monitor, Cyber Attack Incidents, Vulnerabilities, Dashboard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
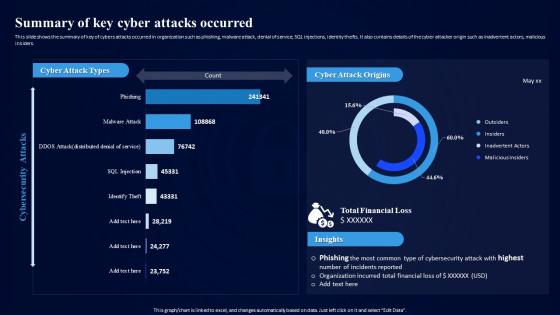 Cybersecurity Risk Assessment Program Summary Of Key Cyber Attacks Occurred
Cybersecurity Risk Assessment Program Summary Of Key Cyber Attacks OccurredThis slide shows the summary of key of cybers attacks occurred in organization such as phishing, malware attack, denial of service, SQL injections, identity thefts. It also contains details of the cyber attacker origin such as inadvertent actors, malicious insiders. Present the topic in a bit more detail with this Cybersecurity Risk Assessment Program Summary Of Key Cyber Attacks Occurred. Use it as a tool for discussion and navigation on Cyber Attacks Occurred, Financial Loss, Cyber Attack Origins. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Strategy To Minimize Cyber Attacks Comprehensive Overview Of Organization IT Assets
Strategy To Minimize Cyber Attacks Comprehensive Overview Of Organization IT AssetsThe purpose this slide is to showcase the comprehensive overview of organization IT assets. The dashboards provide information regarding the IT devices count, distribution in terms of operating system, and location. It also contains details of endpoint by hardware, department and cyber attack visibility. Present the topic in a bit more detail with this Strategy To Minimize Cyber Attacks Comprehensive Overview Of Organization IT Assets. Use it as a tool for discussion and navigation on Operating System Distribution, Assets Distribution By Location, Endpoint By Department, Cyber Attack Visibility. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
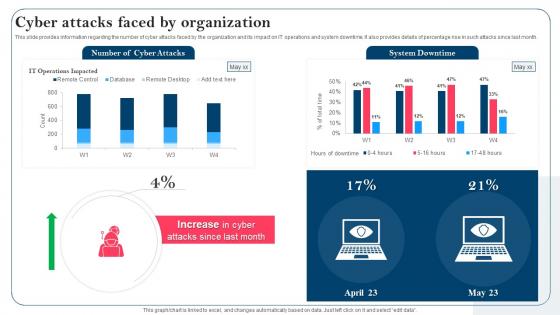 Strategy To Minimize Cyber Attacks Cyber Attacks Faced By Organization
Strategy To Minimize Cyber Attacks Cyber Attacks Faced By OrganizationThis slide provides information regarding the number of cyber attacks faced by the organization and its impact on IT operations and system downtime. It also provides details of percentage rise in such attacks since last month. Deliver an outstanding presentation on the topic using this Strategy To Minimize Cyber Attacks Cyber Attacks Faced By Organization. Dispense information and present a thorough explanation of Cyber Attacks, It Operations, System Downtime using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
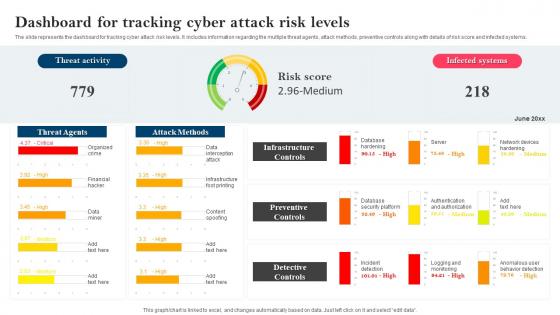 Strategy To Minimize Cyber Attacks Dashboard For Tracking Cyber Attack Risk Levels
Strategy To Minimize Cyber Attacks Dashboard For Tracking Cyber Attack Risk LevelsThe slide represents the dashboard for tracking cyber attack risk levels. It includes information regarding the multiple threat agents, attack methods, preventive controls along with details of risk score and infected systems. Present the topic in a bit more detail with this Strategy To Minimize Cyber Attacks Dashboard For Tracking Cyber Attack Risk Levels. Use it as a tool for discussion and navigation on Dashboard For Tracking, Cyber Attack Risk Levels, Infrastructure Controls, Preventive Controls, Detective Controls. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
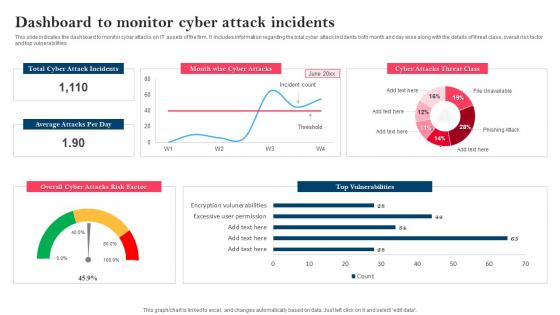 Strategy To Minimize Cyber Attacks Dashboard To Monitor Cyber Attack Incidents
Strategy To Minimize Cyber Attacks Dashboard To Monitor Cyber Attack IncidentsThis slide indicates the dashboard to monitor cyber attacks on IT assets of the firm. It includes information regarding the total cyber attack incidents both month and day wise along with the details of threat class, overall risk factor and top vulnerabilities. Deliver an outstanding presentation on the topic using this Strategy To Minimize Cyber Attacks Dashboard To Monitor Cyber Attack Incidents. Dispense information and present a thorough explanation of Dashboard To Monitor, Cyber Attack Incidents, Top Vulnerabilities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
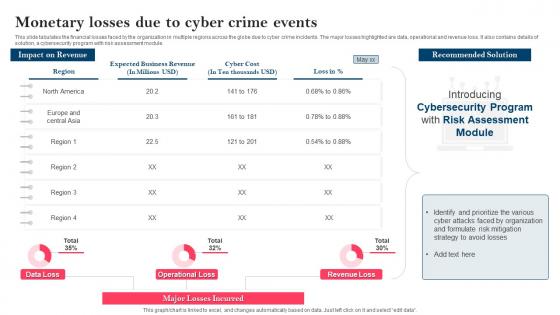 Strategy To Minimize Cyber Attacks Monetary Losses Due To Cyber Crime Events
Strategy To Minimize Cyber Attacks Monetary Losses Due To Cyber Crime EventsThis slide tabulates the financial losses faced by the organization in multiple regions across the globe due to cyber crime incidents. The major losses highlighted are data, operational and revenue loss. It also contains details of solution, a cybersecurity program with risk assessment module. Deliver an outstanding presentation on the topic using this Strategy To Minimize Cyber Attacks Monetary Losses Due To Cyber Crime Events. Dispense information and present a thorough explanation of Monetary Losses, Recommended Solution, Cybersecurity Program, Risk Assessment Module using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
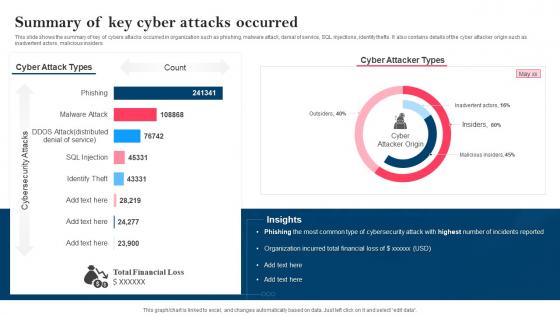 Strategy To Minimize Cyber Attacks Summary Of Key Cyber Attacks Occurred
Strategy To Minimize Cyber Attacks Summary Of Key Cyber Attacks OccurredThis slide shows the summary of key of cybers attacks occurred in organization such as phishing, malware attack, denial of service, SQL injections, identity thefts. It also contains details of the cyber attacker origin such as inadvertent actors, malicious insiders. Present the topic in a bit more detail with this Strategy To Minimize Cyber Attacks Summary Of Key Cyber Attacks Occurred. Use it as a tool for discussion and navigation on Cybers Attacks Occurred, Phishing, Malware Attack, Denial Of Service, SQL Injections, Identity Thefts. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Impact Of Phishing Cyber Scams On Phishing Attacks And Strategies
Impact Of Phishing Cyber Scams On Phishing Attacks And StrategiesThis slide talks about the damage caused by phishing attacks. The purpose of this slide is to explain the impact of phishing scams on organizations. The key points included are information loss, damaged credibility, direct financial loss and productivity loss.Increase audience engagement and knowledge by dispensing information using Impact Of Phishing Cyber Scams On Phishing Attacks And Strategies. This template helps you present information on six stages. You can also present information on Businesses Incur Reputational, Phishing Assault, Maintenance Reconfiguration using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
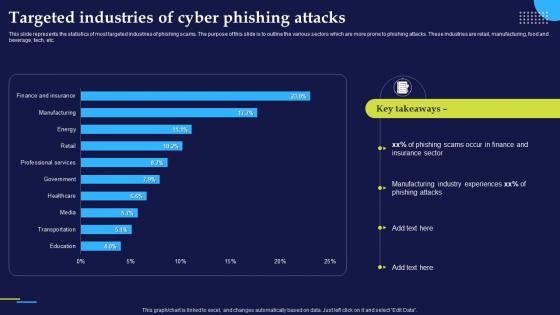 Targeted Industries Of Cyber Phishing Attacks Phishing Attacks And Strategies
Targeted Industries Of Cyber Phishing Attacks Phishing Attacks And StrategiesThis slide represents the statistics of most targeted industries of phishing scams. The purpose of this slide is to outline the various sectors which are more prone to phishing attacks. These industries are retail, manufacturing, food and beverage, tech, etc.Present the topic in a bit more detail with this Targeted Industries Of Cyber Phishing Attacks Phishing Attacks And Strategies. Use it as a tool for discussion and navigation on Phishing Scams, Manufacturing Industry, Phishing Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vishing Cyber Scams In Different Businesses Phishing Attacks And Strategies
Vishing Cyber Scams In Different Businesses Phishing Attacks And StrategiesThis slide demonstrates the various types of vishing scams. The purpose of this slide is to illustrate the ways in which attackers conduct scams in different businesses using vishing technique. These are banking vishing and internal revenue service vishing.Present the topic in a bit more detail with this Vishing Cyber Scams In Different Businesses Phishing Attacks And Strategies. Use it as a tool for discussion and navigation on Internal Revenue, Remote Application, Vishing Example. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber threat icon indicating malware attack
Cyber threat icon indicating malware attackIntroducing our premium set of slides with Cyber Threat Icon Indicating Malware Attack. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Threat Icon Indicating Malware Attack. So download instantly and tailor it with your information.
-
 Cyber Attack Risk In Powerpoint And Google Slides Cpb
Cyber Attack Risk In Powerpoint And Google Slides CpbPresenting our Cyber Attack Risk In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Cyber Attack Risk This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Mitigate Cyber Attacks Ppt Powerpoint Presentation Summary Cpb
Mitigate Cyber Attacks Ppt Powerpoint Presentation Summary CpbPresenting Mitigate Cyber Attacks Ppt Powerpoint Presentation Summary Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Mitigate Cyber Attacks. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Sybil Attack And Cyber Crime Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Sybil Attack And Cyber Crime Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Sybil attack and cyber crime colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Sybil Attack And Cyber Crime Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Sybil Attack And Cyber Crime Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Sybil attack and cyber crime monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 5 Key Practices To Prevent Cyber Phishing Attack
5 Key Practices To Prevent Cyber Phishing AttackMentioned slide showcases best practices which can be implemented to prevent cyber phishing. The practices are recognizing hyperlinks attached in an email, backup system copies, secure robust HTTPs connections, installing a firewall and using anti spam tools. Presenting our set of slides with name 5 Key Practices To Prevent Cyber Phishing Attack. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Recognize Hyperlinks Attached In An Email, Secure HTTP Connections, Backup Copy.
-
 Cyber Phishing Attack Icon To Steal Confidential Data
Cyber Phishing Attack Icon To Steal Confidential DataPresenting our well structured Cyber Phishing Attack Icon To Steal Confidential Data. The topics discussed in this slide are Cyber Phishing Attack Icon To Steal Confidential Data. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
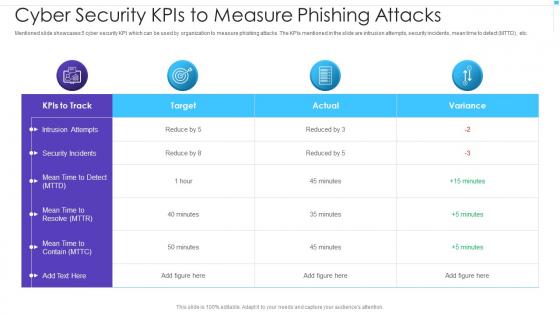 Cyber Security Kpis To Measure Phishing Attacks
Cyber Security Kpis To Measure Phishing AttacksMentioned slide showcases 5 cyber security KPI which can be used by organization to measure phishing attacks. The KPIs mentioned in the slide are intrusion attempts, security incidents, mean time to detect MTTD, etc. Presenting our well structured Cyber Security Kpis To Measure Phishing Attacks. The topics discussed in this slide are Intrusion Attempts, Security Incidents, Mean Time to Resolve. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Icon Of Hacker Launching Cyber Phishing Attack
Icon Of Hacker Launching Cyber Phishing AttackPresenting our set of slides with name Icon Of Hacker Launching Cyber Phishing Attack. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Icon Of Hacker Launching Cyber Phishing Attack.
-
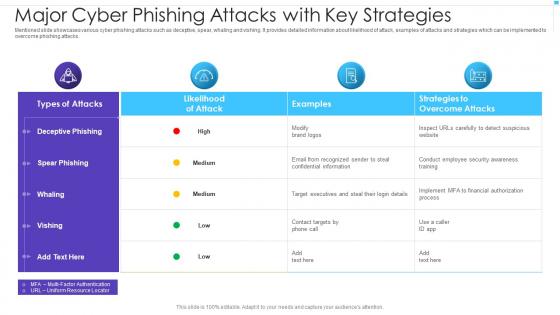 Major Cyber Phishing Attacks With Key Strategies
Major Cyber Phishing Attacks With Key StrategiesMentioned slide showcases various cyber phishing attacks such as deceptive, spear, whaling and vishing. It provides detailed information about likelihood of attack, examples of attacks and strategies which can be implemented to overcome phishing attacks. Introducing our Major Cyber Phishing Attacks With Key Strategies set of slides. The topics discussed in these slides are Spear Phishing, Deceptive Phishing, Whaling. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cost Cyber Attacks Ppt Powerpoint Presentation Model Designs Download Cpb
Cost Cyber Attacks Ppt Powerpoint Presentation Model Designs Download CpbPresenting our Cost Cyber Attacks Ppt Powerpoint Presentation Model Designs Download Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Cost Cyber Attacks This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cyber Security Attacks Statistics Ppt Powerpoint Presentation File Display Cpb
Cyber Security Attacks Statistics Ppt Powerpoint Presentation File Display CpbPresenting our Cyber Security Attacks Statistics Ppt Powerpoint Presentation File Display Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Cyber Security Attacks Statistics This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Increase Cyber Attacks Statistics Ppt Powerpoint Presentation Ideas Elements Cpb
Increase Cyber Attacks Statistics Ppt Powerpoint Presentation Ideas Elements CpbPresenting our Increase Cyber Attacks Statistics Ppt Powerpoint Presentation Ideas Elements Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Increase Cyber Attacks Statistics This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
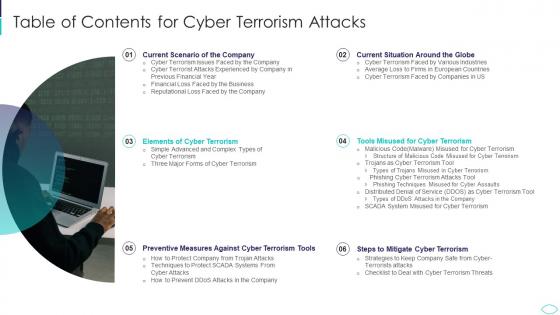 A56 Table Of Contents For Cyber Terrorism Attacks Ppt Slides Guidelines
A56 Table Of Contents For Cyber Terrorism Attacks Ppt Slides GuidelinesIntroducing A56 Table Of Contents For Cyber Terrorism Attacks Ppt Slides Guidelines to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Current Situation, Mitigate, Terrorism Tools, Cyber Terrorism, using this template. Grab it now to reap its full benefits.
-
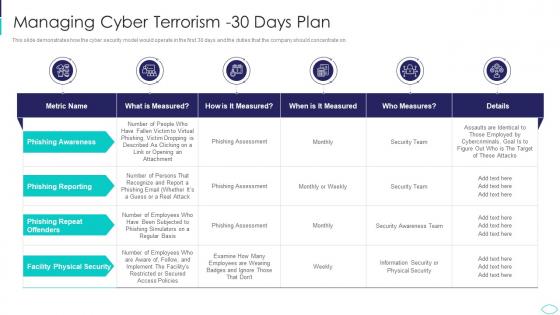 A57 Managing Cyber Terrorism 30 Days Plan Cyber Terrorism Attacks
A57 Managing Cyber Terrorism 30 Days Plan Cyber Terrorism AttacksThis slide demonstrates how the cyber security model would operate in the first 30 days and the duties that the company should concentrate on.Present the topic in a bit more detail with this A57 Managing Cyber Terrorism 30 Days Plan Cyber Terrorism Attacks. Use it as a tool for discussion and navigation on Managing Cyber Terrorism 30 Days Plan. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Agenda For Cyber Terrorism Attacks Ppt Slides Introduction
Agenda For Cyber Terrorism Attacks Ppt Slides IntroductionIncrease audience engagement and knowledge by dispensing information using Agenda For Cyber Terrorism Attacks Ppt Slides Introduction. This template helps you present information on five stages. You can also present information on Situation, Terrorism, Measures, Prevention, Demonstrate using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
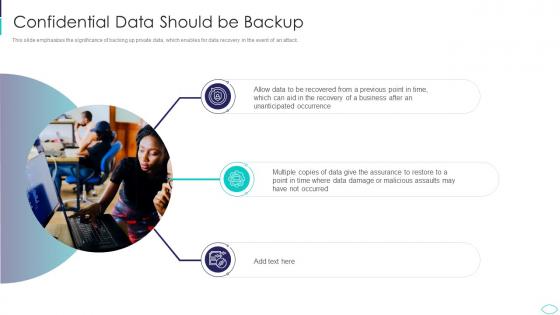 Confidential Data Should Be Backup Cyber Terrorism Attacks
Confidential Data Should Be Backup Cyber Terrorism AttacksThis slide emphasizes the significance of backing up private data, which enables for data recovery in the event of an attack. Introducing Confidential Data Should Be Backup Cyber Terrorism Attacks to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Unanticipated, Occurrence, Recovered, Business, Assurance, using this template. Grab it now to reap its full benefits.
-
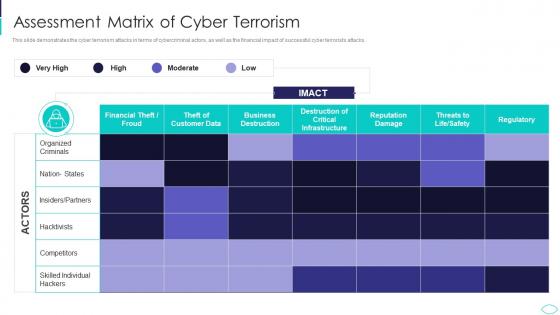 Cyber Terrorism Attacks Assessment Matrix Of Cyber Terrorism
Cyber Terrorism Attacks Assessment Matrix Of Cyber TerrorismThis slide demonstrates the cyber terrorism attacks in terms of cybercriminal actors, as well as the financial impact of successful cyber terrorists attacks. Deliver an outstanding presentation on the topic using this Cyber Terrorism Attacks Assessment Matrix Of Cyber Terrorism. Dispense information and present a thorough explanation of Assessment Matrix Of Cyber Terrorism using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
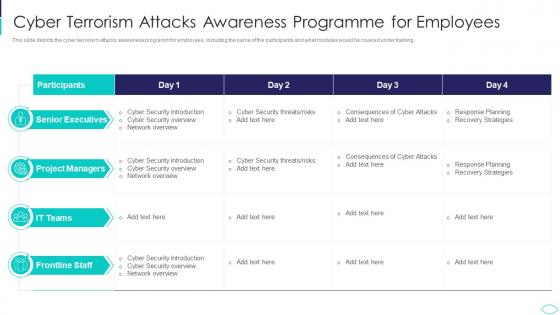 Cyber Terrorism Attacks Awareness Cyber Terrorism Attacks
Cyber Terrorism Attacks Awareness Cyber Terrorism AttacksThis slide depicts the cyber terrorism attacks awareness programm for employees, including the name of the participants and what modules would be covered under training. Present the topic in a bit more detail with this Cyber Terrorism Attacks Awareness Cyber Terrorism Attacks. Use it as a tool for discussion and navigation on Cyber Terrorism Attacks Awareness Programme For Employees. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Terrorism Attacks Checklist To Deal With Cyber Terrorism Threats
Cyber Terrorism Attacks Checklist To Deal With Cyber Terrorism ThreatsThis slide represents the checklist to deal with cyber terrorism attacks threats which involve 24 7 monitoring, employee training, keeping software updated. Increase audience engagement and knowledge by dispensing information using Cyber Terrorism Attacks Checklist To Deal With Cyber Terrorism Threats. This template helps you present information on nine stages. You can also present information on Cyber Security Assessment, Limited Access Privileges, Employee Training, External Cyber Intelligence using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
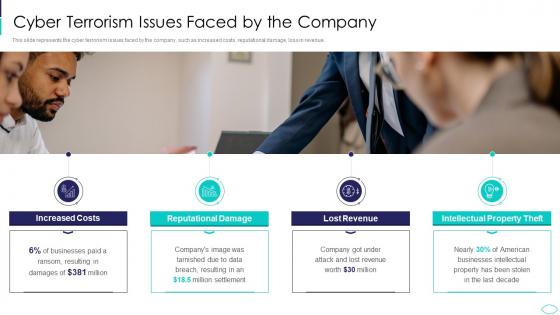 Cyber Terrorism Issues Faced By The Company Cyber Terrorism Attacks
Cyber Terrorism Issues Faced By The Company Cyber Terrorism AttacksThis slide represents the cyber terrorism issues faced by the company, such as increased costs, reputational damage, loss in revenue. Introducing Cyber Terrorism Issues Faced By The Company Cyber Terrorism Attacks to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Increased Costs, Reputational Damage, Lost Revenue, Intellectual Property Theft, using this template. Grab it now to reap its full benefits.
-
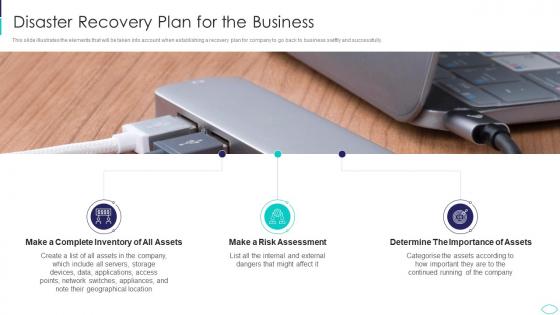 Disaster Recovery Plan For The Business Cyber Terrorism Attacks
Disaster Recovery Plan For The Business Cyber Terrorism AttacksThis slide illustrates the elements that will be taken into account when establishing a recovery plan for company to go back to business swiftly and successfully. Increase audience engagement and knowledge by dispensing information using Disaster Recovery Plan For The Business Cyber Terrorism Attacks. This template helps you present information on three stages. You can also present information on Inventory, Assets, Assessment, Importance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Employee Access Control Protocols Cyber Terrorism Attacks
Employee Access Control Protocols Cyber Terrorism AttacksThis slide highlights how it is critical to limit employee rights and access in order to keep data safe and prevent it from being deleted or manipulated. Introducing Employee Access Control Protocols Cyber Terrorism Attacks to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Physical Assets, Access Control, Sensitive Data, Restricts Access, using this template. Grab it now to reap its full benefits.
-
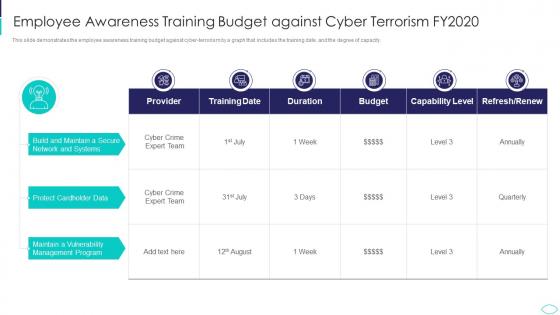 Employee Awareness Training Budget Cyber Terrorism Attacks
Employee Awareness Training Budget Cyber Terrorism AttacksThis slide demonstrates the employee awareness training budget against cyber terrorism by a graph that includes the training date, and the degree of capacity. Deliver an outstanding presentation on the topic using this Employee Awareness Training Budget Cyber Terrorism Attacks. Dispense information and present a thorough explanation of Employee Awareness Training Budget Against Cyber Terrorism Fy2020 using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Financial Loss Faced By The Business Cyber Terrorism Attacks
Financial Loss Faced By The Business Cyber Terrorism AttacksThis slide depicts the average financial loss faced by the business when projects of different scales are attacked. Increase audience engagement and knowledge by dispensing information using Financial Loss Faced By The Business Cyber Terrorism Attacks. This template helps you present information on one stages. You can also present information on Financial Loss Faced By The Business using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 How To Prevent Ddos Attacks In The Company Cyber Terrorism Attacks
How To Prevent Ddos Attacks In The Company Cyber Terrorism AttacksThis slide represents the ways to prevent DDoS attacks in the company, which include network monitoring, updating security elements, etc. Introducing How To Prevent Ddos Attacks In The Company Cyber Terrorism Attacks to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Service, Bandwidth, Capacity, Network Monitoring, Mitigation Technologies, using this template. Grab it now to reap its full benefits.
-
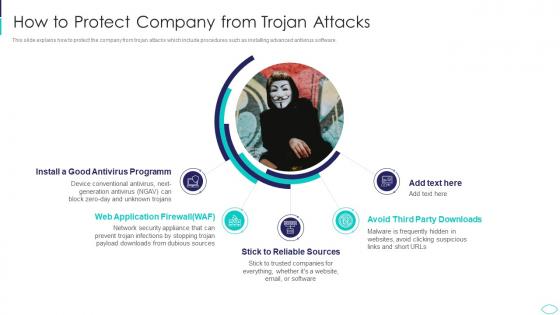 How To Protect Company From Trojan Attacks Cyber Terrorism Attacks
How To Protect Company From Trojan Attacks Cyber Terrorism AttacksThis slide explains how to protect the company from trojan attacks which include procedures such as installing advanced antivirus software. Increase audience engagement and knowledge by dispensing information using How To Protect Company From Trojan Attacks Cyber Terrorism Attacks. This template helps you present information on five stages. You can also present information on Antivirus Programm, Application Firewall, Reliable Sources, Avoid Third Party Downloads using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons Slide For Cyber Terrorism Attacks Ppt Slides Background Designs
Icons Slide For Cyber Terrorism Attacks Ppt Slides Background DesignsPresenting our well crafted Icons Slide For Cyber Terrorism Attacks Ppt Slides Background Designs set of slides. The slides include icons that are innovatively designed by our team of experts. The icons are easy to edit so you can conveniently increase or decrease their size without any loss in resolution. Therefore, grab them instantly.
-
 Implementing Least Privilege Administrative Model Cyber Terrorism Attacks
Implementing Least Privilege Administrative Model Cyber Terrorism AttacksThis slide depicts that administration and employees should have limited access to the information and confidential data. Introducing Implementing Least Privilege Administrative Model Cyber Terrorism Attacks to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Privileges, Control, Risk Levels, Prevent, using this template. Grab it now to reap its full benefits.
-
 Malicious Codemalware Misused For Cyber Terrorism Cyber Terrorism Attacks
Malicious Codemalware Misused For Cyber Terrorism Cyber Terrorism AttacksThis slide depicts the malicious code or malware misused for cyber terrorism attacks to hijack or access information from computers. Increase audience engagement and knowledge by dispensing information using Malicious Codemalware Misused For Cyber Terrorism Cyber Terrorism Attacks. This template helps you present information on five stages. You can also present information on Malicious Code Malware Misused For Cyber Terrorism using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
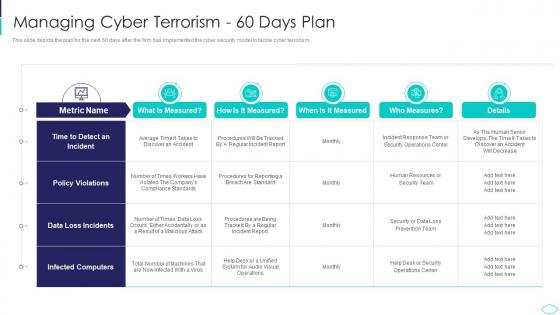 Managing Cyber Terrorism 60 Days Plan Cyber Terrorism Attacks
Managing Cyber Terrorism 60 Days Plan Cyber Terrorism AttacksThis slide depicts the plan for the next 60 days after the firm has implemented the cyber security model to tackle cyber terrorism. Deliver an outstanding presentation on the topic using this Managing Cyber Terrorism 60 Days Plan Cyber Terrorism Attacks. Dispense information and present a thorough explanation of Managing Cyber Terrorism 60 Days Plan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
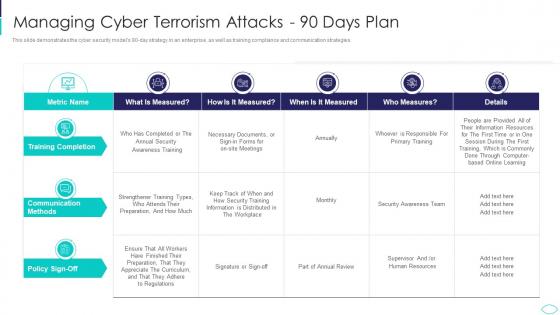 Managing Cyber Terrorism Attacks 90 Days Plan Cyber Terrorism Attacks
Managing Cyber Terrorism Attacks 90 Days Plan Cyber Terrorism AttacksThis slide demonstrates the cyber security models 90 day strategy in an enterprise, as well as training compliance and communication strategies. Deliver an outstanding presentation on the topic using this Managing Cyber Terrorism Attacks 90 Days Plan Cyber Terrorism Attacks. Dispense information and present a thorough explanation of Managing Cyber Terrorism Attacks 90 Days Plan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
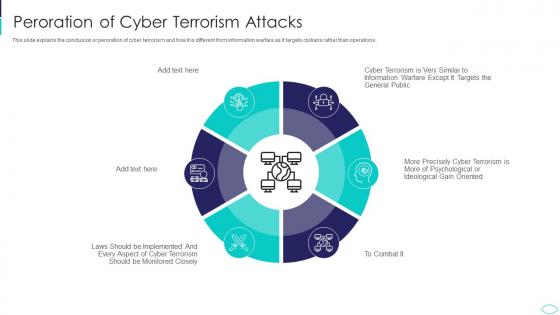 Peroration Of Cyber Terrorism Attacks Cyber Terrorism Attacks
Peroration Of Cyber Terrorism Attacks Cyber Terrorism AttacksThis slide explains the conclusion or peroration of cyber terrorism and how it is different from information warfare as it targets civilians rather than operations. Introducing Peroration Of Cyber Terrorism Attacks Cyber Terrorism Attacks to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Peroration Of Cyber Terrorism Attacks, using this template. Grab it now to reap its full benefits.
-
 Phishing Cyber Terrorism Tool Cyber Terrorism Attacks
Phishing Cyber Terrorism Tool Cyber Terrorism AttacksThis slide describes phishing in which an attacker tricks a victim to open an email, provide card credentials or any sensitive information. Increase audience engagement and knowledge by dispensing information using Phishing Cyber Terrorism Tool Cyber Terrorism Attacks. This template helps you present information on five stages. You can also present information on Obtain, Sensitive, Information, Trustworthy, Convinces using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
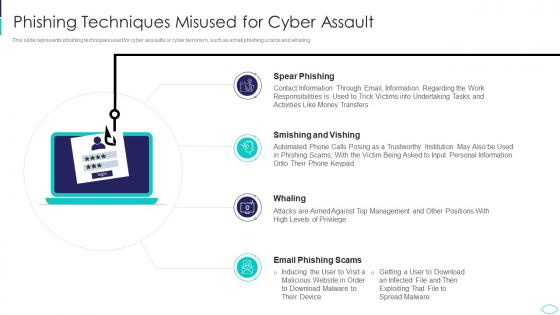 Phishing Techniques Misused For Cyber Assault Cyber Terrorism Attacks
Phishing Techniques Misused For Cyber Assault Cyber Terrorism AttacksThis slide represents phishing techniques used for cyber assaults or cyber terrorism, such as email phishing scams and whaling. Introducing Phishing Techniques Misused For Cyber Assault Cyber Terrorism Attacks to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Phishing Techniques Misused For Cyber Assault, using this template. Grab it now to reap its full benefits.
-
 Reputational Loss Faced By The Company Cyber Terrorism Attacks
Reputational Loss Faced By The Company Cyber Terrorism AttacksThis slide demonstrates the reputational loss of the company due to cyber terrorism, which leads to the customers leaving and a decline in sales. Increase audience engagement and knowledge by dispensing information using Reputational Loss Faced By The Company Cyber Terrorism Attacks. This template helps you present information on five stages. You can also present information on Margin Reduces, Cyber Assaults, Influence, Suppliers, Stakeholders using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Roadmap To Implement Cyber Security Cyber Terrorism Attacks
Roadmap To Implement Cyber Security Cyber Terrorism AttacksThis slide depicts the roadmap to implement strategies to mitigate cyber terrorism such as training employees about cyber terrorism, creating personal accounts. Introducing Roadmap To Implement Cyber Security Cyber Terrorism Attacks to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Personal Accounts, Awareness Training, Software Updated, using this template. Grab it now to reap its full benefits.
-
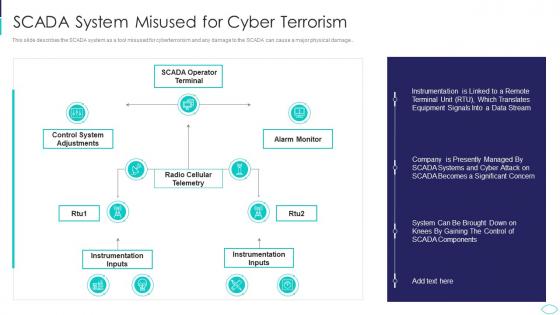 SCADA System Misused For Cyber Terrorism Cyber Terrorism Attacks
SCADA System Misused For Cyber Terrorism Cyber Terrorism AttacksThis slide describes the SCADA system as a tool misused for cyberterrorism and any damage to the SCADA can cause a major physical damage.. Present the topic in a bit more detail with this SCADA System Misused For Cyber Terrorism Cyber Terrorism Attacks. Use it as a tool for discussion and navigation on Scada System Misused For Cyber Terrorism. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
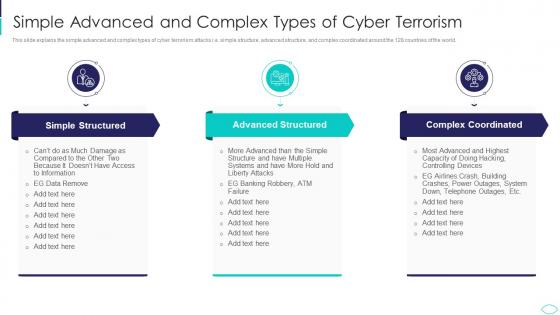 Simple Advanced And Complex Types Cyber Terrorism Attacks
Simple Advanced And Complex Types Cyber Terrorism AttacksThis slide explains the simple advanced and complex types of cyber terrorism attacks i.e. simple structure, advanced structure, and complex coordinated around the 128 countries of the world. Increase audience engagement and knowledge by dispensing information using Simple Advanced And Complex Types Cyber Terrorism Attacks. This template helps you present information on three stages. You can also present information on Simple Structured, Advanced Structured, Complex Coordinated using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
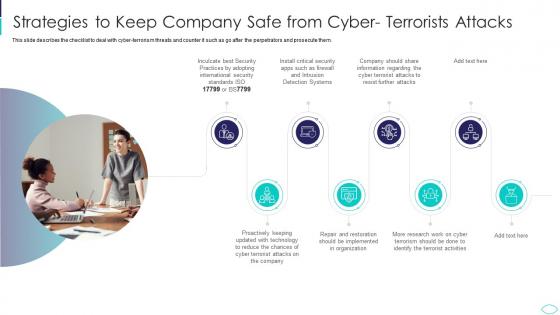 Strategies To Keep Company Safe From Cyber Terrorism Attacks
Strategies To Keep Company Safe From Cyber Terrorism AttacksThis slide describes the checklist to deal with cyber terrorism threats and counter it such as go after the perpetrators and prosecute them. Introducing Strategies To Keep Company Safe From Cyber Terrorism Attacks to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Technology, Reduce, Implemented, Restoration, Organization, using this template. Grab it now to reap its full benefits.
-
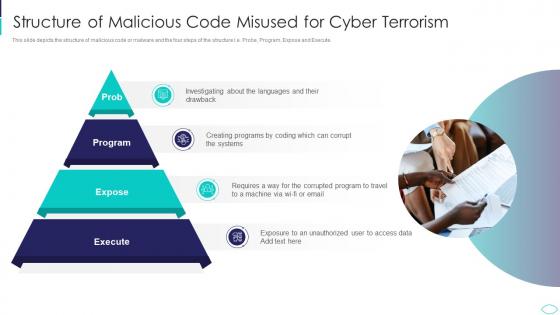 Structure Of Malicious Code Misused Cyber Terrorism Attacks
Structure Of Malicious Code Misused Cyber Terrorism AttacksThis slide depicts the structure of malicious code or malware and the four steps of the structure i.e. Probe, Program, Expose and Execute.Increase audience engagement and knowledge by dispensing information using Structure Of Malicious Code Misused Cyber Terrorism Attacks. This template helps you present information on four stages. You can also present information on Structure Of Malicious Code Misused For Cyber Terrorism using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Table Of Contents For Cyber Terrorism Attacks Mitigate
Table Of Contents For Cyber Terrorism Attacks MitigateIntroducing Table Of Contents For Cyber Terrorism Attacks Mitigate to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Assessment Matrix, Security Budget, Security Measures, using this template. Grab it now to reap its full benefits.
-
 Techniques To Protect SCADA Systems From Cyber Terrorism Attacks
Techniques To Protect SCADA Systems From Cyber Terrorism AttacksThis slide depicts the techniques to protect SCADA from cyber attacks which include security training of employees, strict firewalls. Increase audience engagement and knowledge by dispensing information using Techniques To Protect SCADA Systems From Cyber Terrorism Attacks. This template helps you present information on six stages. You can also present information on Security Training, Access Controls, Strict Firewalls, Security Procedures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Three Major Forms Of Cyber Terrorism Attacks Ppt Slides Designs Download
Three Major Forms Of Cyber Terrorism Attacks Ppt Slides Designs DownloadThis slide describes the three major forms of cyber terrorism attacks such as privacy violation, networks damage, and disruptions, and distribution denial of service attack. Introducing Three Major Forms Of Cyber Terrorism Attacks Ppt Slides Designs Download to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Privacy Violation, Damage Disruptions, Distributed Denial, using this template. Grab it now to reap its full benefits.
-
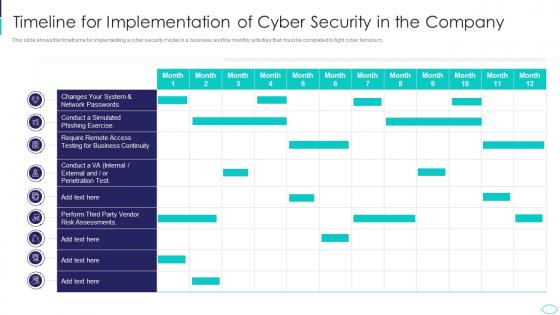 Timeline For Implementation Cyber Terrorism Attacks
Timeline For Implementation Cyber Terrorism AttacksThis slide shows the timeframe for implementing a cyber security model in a business and the monthly activities that must be completed to fight cyber terrorism. Deliver an outstanding presentation on the topic using this Timeline For Implementation Cyber Terrorism Attacks. Dispense information and present a thorough explanation of Timeline For Implementation Of Cyber Security In The Company using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
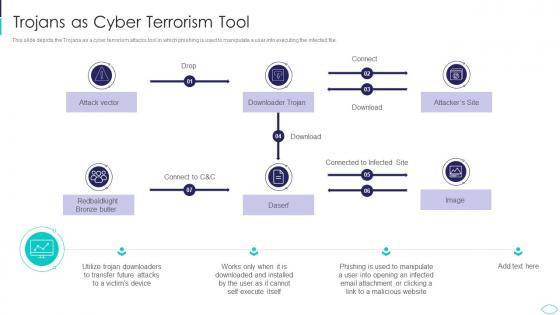 Trojans As Cyber Terrorism Tool Cyber Terrorism Attacks
Trojans As Cyber Terrorism Tool Cyber Terrorism AttacksThis slide depicts the Trojans as a cyber terrorism attacks tool in which phishing is used to manipulate a user into executing the infected file. Present the topic in a bit more detail with this Trojans As Cyber Terrorism Tool Cyber Terrorism Attacks. Use it as a tool for discussion and navigation on Trojans As Cyber Terrorism Tool. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
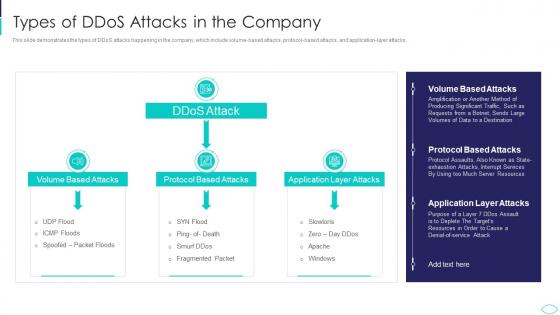 Types Of Ddos Attacks In The Company Cyber Terrorism Attacks
Types Of Ddos Attacks In The Company Cyber Terrorism AttacksThis slide demonstrates the types of DDoS attacks happening in the company, which include volume based attacks, protocol based attacks, and application layer attacks. Deliver an outstanding presentation on the topic using this Types Of Ddos Attacks In The Company Cyber Terrorism Attacks. Dispense information and present a thorough explanation of Application Layer Attacks, Protocol Based Attacks, Volume Based Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
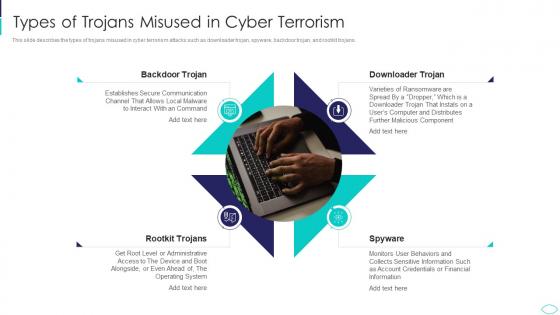 Types Of Trojans Misused In Cyber Terrorism Cyber Terrorism Attacks
Types Of Trojans Misused In Cyber Terrorism Cyber Terrorism AttacksThis slide describes the types of trojans misused in cyber terrorism attacks such as downloader trojan, spyware, backdoor trojan, and rootkit trojans. Increase audience engagement and knowledge by dispensing information using Types Of Trojans Misused In Cyber Terrorism Cyber Terrorism Attacks. This template helps you present information on four stages. You can also present information on Types Of Trojans Misused In Cyber Terrorism using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
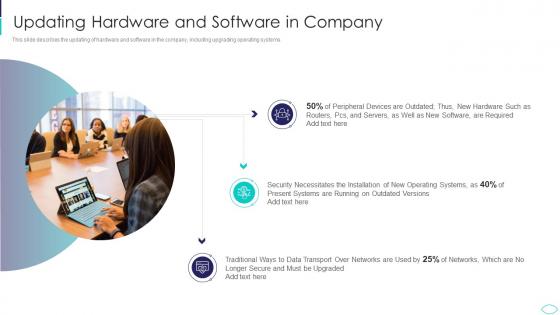 Updating Hardware And Software In Company Cyber Terrorism Attacks
Updating Hardware And Software In Company Cyber Terrorism AttacksThis slide describes the updating of hardware and software in the company, including upgrading operating systems. Introducing Updating Hardware And Software In Company Cyber Terrorism Attacks to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Required, Necessitates, Installation, Transport, using this template. Grab it now to reap its full benefits.



