Powerpoint Templates and Google slides for Cyber
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
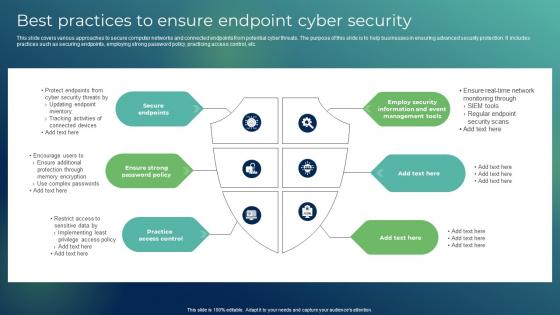 Best Practices To Ensure Endpoint Cyber Security
Best Practices To Ensure Endpoint Cyber SecurityThis slide covers various approaches to secure computer networks and connected endpoints from potential cyber threats. The purpose of this slide is to help businesses in ensuring advanced security protection. It includes practices such as securing endpoints, employing strong password policy, practicing access control, etc. Presenting our well structured Best Practices To Ensure Endpoint Cyber Security The topics discussed in this slide are Secure Endpoints, Ensure Strong Password Policy, Practice Access Control This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
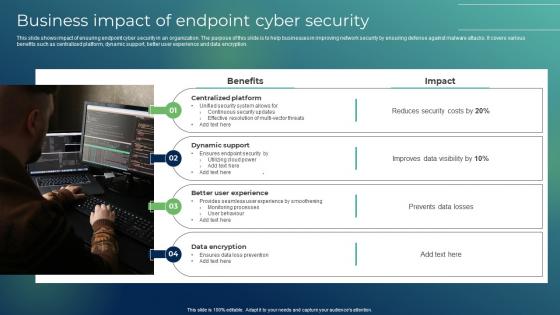 Business Impact Of Endpoint Cyber Security
Business Impact Of Endpoint Cyber SecurityThis slide shows impact of ensuring endpoint cyber security in an organization. The purpose of this slide is to help businesses in improving network security by ensuring defense against malware attacks. It covers various benefits such as centralized platform, dynamic support, better user experience and data encryption. Presenting our set of slides with Business Impact Of Endpoint Cyber Security This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Centralized Platform, Dynamic Support, Better User Experience
-
 Cloud Based Endpoint Cyber Security Icon
Cloud Based Endpoint Cyber Security IconIntroducing our premium set of slides with Cloud Based Endpoint Cyber Security Icon Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cloud Based Endpoint, Cyber Security Icon So download instantly and tailor it with your information.
-
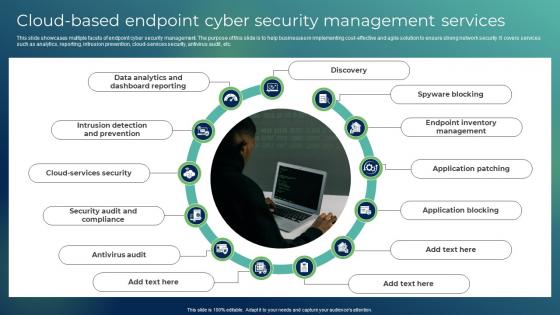 Cloud Based Endpoint Cyber Security Management Services
Cloud Based Endpoint Cyber Security Management ServicesThis slide showcases multiple facets of endpoint cyber security management. The purpose of this slide is to help businesses in implementing cost effective and agile solution to ensure strong network security. It covers services such as analytics, reporting, intrusion prevention, cloud services security, antivirus audit, etc. Presenting our set of slides with Cloud Based Endpoint Cyber Security Management Services This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Discovery, Spyware Blocking, Application Patching
-
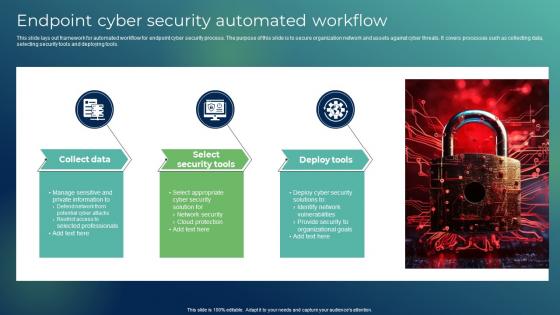 Endpoint Cyber Security Automated Workflow
Endpoint Cyber Security Automated WorkflowThis slide lays out framework for automated workflow for endpoint cyber security process. The purpose of this slide is to secure organization network and assets against cyber threats. It covers processes such as collecting data, selecting security tools and deploying tools. Introducing our premium set of slides with Endpoint Cyber Security Automated Workflow Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Collect Data, Select Security Tools, Deploy Tools So download instantly and tailor it with your information.
-
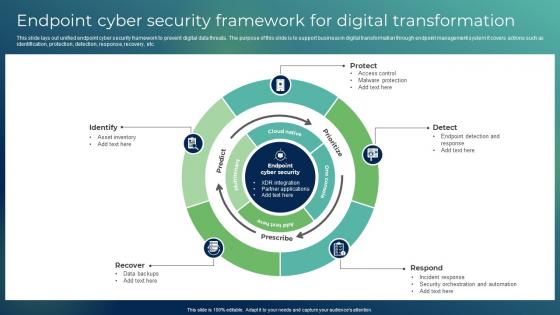 Endpoint Cyber Security Framework For Digital Transformation
Endpoint Cyber Security Framework For Digital TransformationThis slide lays out unified endpoint cyber security framework to prevent digital data threats. The purpose of this slide is to support business in digital transformation through endpoint management system It covers actions such as identification, protection, detection, response, recovery, etc. Presenting our set of slides with Endpoint Cyber Security Framework For Digital Transformation This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify, Protect, Detect
-
 Endpoint Cyber Security Icon For Digital Transformation
Endpoint Cyber Security Icon For Digital TransformationIntroducing our premium set of slides with Endpoint Cyber Security Icon For Digital Transformation Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Endpoint Cyber Security Icon, Digital Transformation So download instantly and tailor it with your information.
-
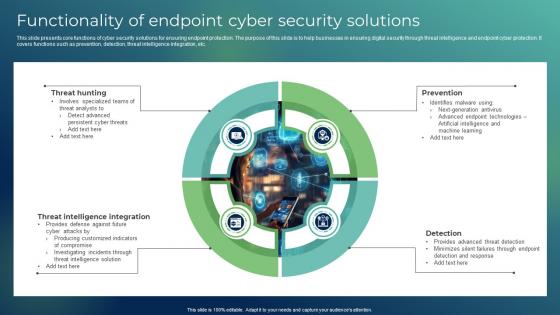 Functionality Of Endpoint Cyber Security Solutions
Functionality Of Endpoint Cyber Security SolutionsThis slide presents core functions of cyber security solutions for ensuring endpoint protection. The purpose of this slide is to help businesses in ensuring digital security through threat intelligence and endpoint cyber protection. It covers functions such as prevention, detection, threat intelligence integration, etc. Presenting our well structured Functionality Of Endpoint Cyber Security Solutions The topics discussed in this slide are Threat Hunting, Threat Intelligence Integration, Prevention This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
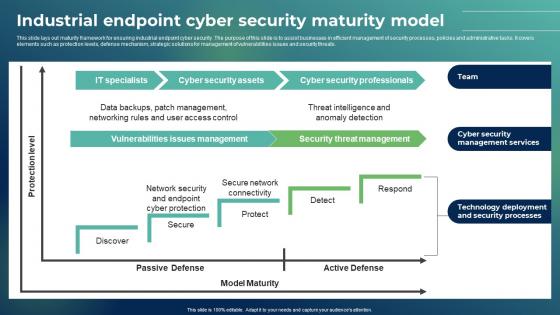 Industrial Endpoint Cyber Security Maturity Model
Industrial Endpoint Cyber Security Maturity ModelThis slide lays out maturity framework for ensuring industrial endpoint cyber security. The purpose of this slide is to assist businesses in efficient management of security processes, policies and administrative tasks. It covers elements such as protection levels, defense mechanism, strategic solutions for management of vulnerabilities issues and security threats. Introducing our Industrial Endpoint Cyber Security Maturity Model set of slides. The topics discussed in these slides are Specialists, Cyber Security Assets, Cyber Security Professionals This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
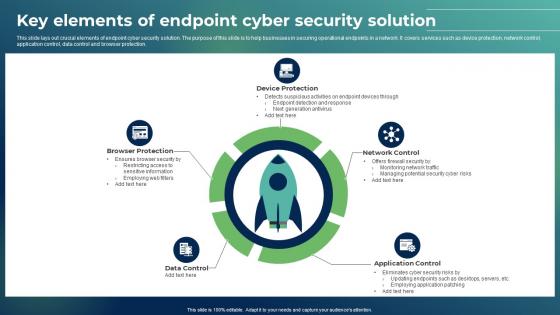 Key Elements Of Endpoint Cyber Security Solution
Key Elements Of Endpoint Cyber Security SolutionThis slide lays out crucial elements of endpoint cyber security solution. The purpose of this slide is to help businesses in securing operational endpoints in a network. It covers services such as device protection, network control, application control, data control and browser protection. Presenting our set of slides with Key Elements Of Endpoint Cyber Security Solution This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Browser Protection, Device Protection, Network Control
-
 Software Patching Icon For Ensuring Endpoint Cyber Security
Software Patching Icon For Ensuring Endpoint Cyber SecurityIntroducing our premium set of slides with Software Patching Icon For Ensuring Endpoint Cyber Security Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Software Patching Icon, Ensuring Endpoint Cyber Security So download instantly and tailor it with your information.
-
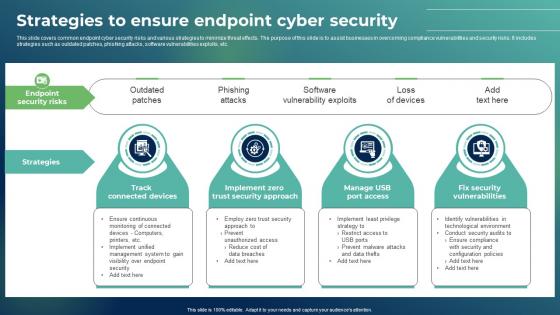 Strategies To Ensure Endpoint Cyber Security
Strategies To Ensure Endpoint Cyber SecurityThis slide covers common endpoint cyber security risks and various strategies to minimize threat effects. The purpose of this slide is to assist businesses in overcoming compliance vulnerabilities and security risks. It includes strategies such as outdated patches, phishing attacks, software vulnerabilities exploits, etc. Presenting our set of slides with Strategies To Ensure Endpoint Cyber Security This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Track Connected Devices, Strategies, Manage USB Port Access
-
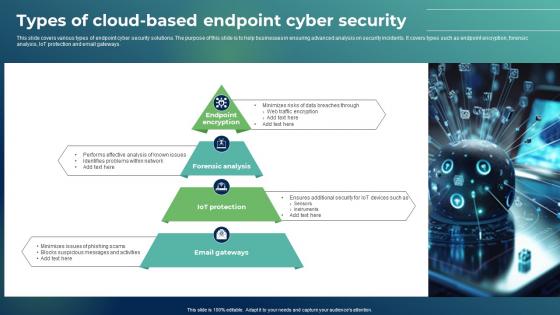 Types Of Cloud Based Endpoint Cyber Security
Types Of Cloud Based Endpoint Cyber SecurityThis slide covers various types of endpoint cyber security solutions. The purpose of this slide is to help businesses in ensuring advanced analysis on security incidents. It covers types such as endpoint encryption, forensic analysis, IoT protection and email gateways. Presenting our well structured Types Of Cloud Based Endpoint Cyber Security The topics discussed in this slide are Forensic Analysis, Iot Protection, Email Gateways This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
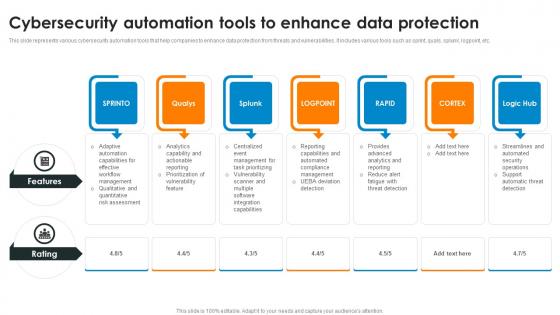 Cybersecurity Automation Tools To Enhance Data Protection
Cybersecurity Automation Tools To Enhance Data ProtectionThis slide represents various cybersecurity automation tools that help companies to enhance data protection from threats and vulnerabilities. It includes various tools such as sprint, quals, splunk, logpoint, etc. Introducing our premium set of slides with Cybersecurity Automation Tools To Enhance Data Protection Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Features, Cybersecurity Automation, Data Protection So download instantly and tailor it with your information.
-
 4 Threats To Cybersecurity In Automobile Industry
4 Threats To Cybersecurity In Automobile IndustryThis slide highlights cyber safety concerns in automotive sector. The purpose of this slide is to provide businesses with the required knowledge regarding various malware attacks in vehicles. It includes elements such as software, unauthorized access, etc. Presenting our set of slides with 4 Threats To Cybersecurity In Automobile Industry This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Unauthorized Access, Supply Chain, Software
-
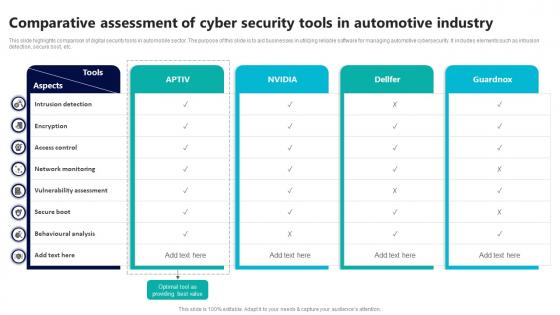 Comparative Assessment Of Cyber Security Tools In Automotive Industry
Comparative Assessment Of Cyber Security Tools In Automotive IndustryThis slide highlights comparison of digital security tools in automobile sector. The purpose of this slide is to aid businesses in utilizing reliable software for managing automotive cybersecurity. It includes elements such as intrusion detection, secure boot, etc. Introducing our Comparative Assessment Of Cyber Security Tools In Automotive Industry set of slides. The topics discussed in these slides are Intrusion Detection, Access Control, Network Monitoring This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
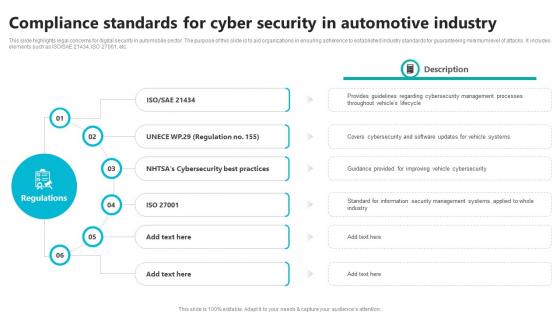 Compliance Standards For Cyber Security In Automotive Industry
Compliance Standards For Cyber Security In Automotive IndustryThis slide highlights legal concerns for digital security in automobile sector. The purpose of this slide is to aid organizations in ensuring adherence to established industry standards for guaranteeing minimum level of attacks. It includes elements such as ISO SAE 21434, ISO 27001, etc. Presenting our set of slides with Compliance Standards For Cyber Security In Automotive Industry This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cybersecurity Best Practices, Management Processes.
-
 Core Responsibilities Of Cybersecurity Engineer In Automotive Sector
Core Responsibilities Of Cybersecurity Engineer In Automotive SectorThis slide highlights cyber security obligations of technicians in?retail sector. The purpose of this slide is to help businesses in managing security protocols by implementing preventive measures for maintaining integrity of systems. It includes elements such as threat analysis, awareness training, etc. Introducing our premium set of slides with Core Responsibilities Of Cybersecurity Engineer In Automotive Sector Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Vehicle Security Assessment, Threat Analysis, Awareness Training So download instantly and tailor it with your information.
-
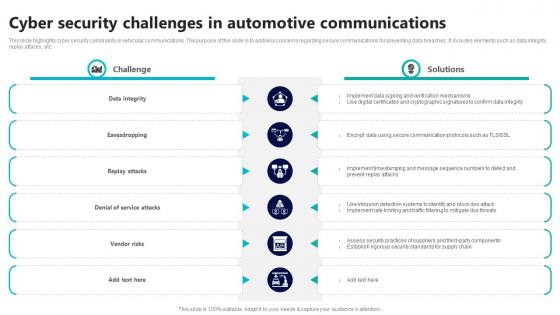 Cyber Security Challenges In Automotive Communications
Cyber Security Challenges In Automotive CommunicationsThis slide highlights cyber security constraints in vehicular communications. The purpose of this slide is to address concerns regarding secure communications for preventing data breaches. It includes elements such as data integrity, replay attacks, etc. Presenting our set of slides with Cyber Security Challenges In Automotive Communications This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Integrity, Eavesdropping, Replay Attacks
-
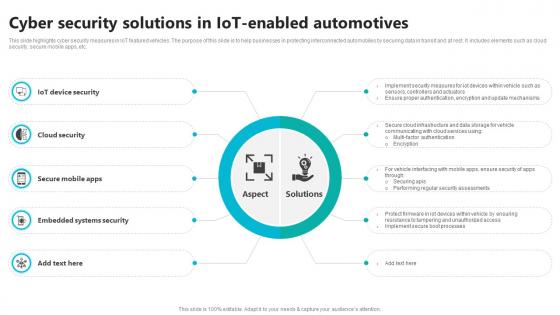 Cyber Security Solutions In IOT Enabled Automotives
Cyber Security Solutions In IOT Enabled AutomotivesThis slide highlights cyber security measures in IoT featured vehicles. The purpose of this slide is to help businesses in protecting interconnected automobiles by securing data in transit and at rest. It includes elements such as cloud security, secure mobile apps, etc. Introducing our premium set of slides with Cyber Security Solutions In IOT Enabled Automotives Ellicudate the ten stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Device Security, Cloud Security, Embedded Systems Security So download instantly and tailor it with your information.
-
 Data Encryption And Authentication In Automotive Cyber Security
Data Encryption And Authentication In Automotive Cyber SecurityThis slide highlights data privacy and encryption in automotive cybersecurity. The purpose of this slide is to aid organizations in implementing measures for securing sensitive data from possible manipulation. It includes various measures for authentication and data encryption. Presenting our set of slides with Data Encryption And Authentication In Automotive Cyber Security This exhibits information on two stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Authentication, Data Encryption, Authenticity Of Software
-
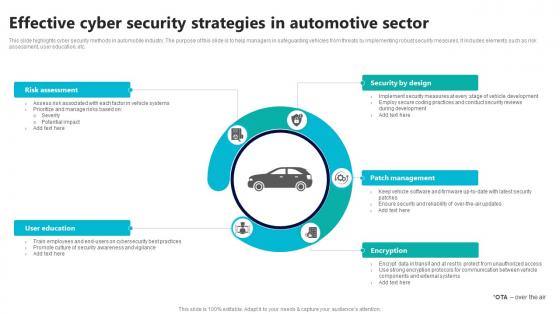 Effective Cyber Security Strategies In Automotive Sector
Effective Cyber Security Strategies In Automotive SectorThis slide highlights cyber security methods in automobile industry. The purpose of this slide is to help managers in safeguarding vehicles from threats by implementing robust security measures. It includes elements such as risk assessment, user education, etc. Introducing our premium set of slides with Effective Cyber Security Strategies In Automotive Sector Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Risk Assessment, Security By Design, Patch Management So download instantly and tailor it with your information.
-
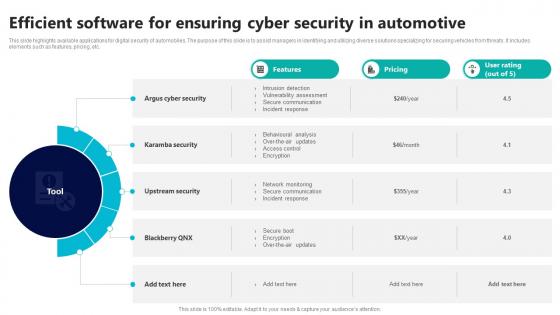 Efficient Software For Ensuring Cyber Security In Automotive
Efficient Software For Ensuring Cyber Security In AutomotiveThis slide highlights available applications for digital security of automobiles. The purpose of this slide is to assist managers in identifying and utilizing diverse solutions specializing for securing vehicles from threats. It includes elements such as features, pricing, etc. Presenting our set of slides with Efficient Software For Ensuring Cyber Security In Automotive This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Argus Cyber Security, Karamba Security, Upstream Security
-
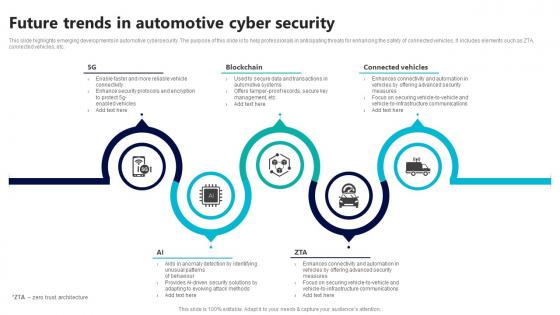 Future Trends In Automotive Cyber Security
Future Trends In Automotive Cyber SecurityThis slide highlights emerging developments in automotive cybersecurity. The purpose of this slide is to help professionals in anticipating threats for enhancing the safety of connected vehicles. It includes elements such as ZTA, connected vehicles, etc. Introducing our premium set of slides with Future Trends In Automotive Cyber Security Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Blockchain, Connected Vehicles, Cyber Security So download instantly and tailor it with your information.
-
 Icon For Incident Response In Automotive Cyber Security
Icon For Incident Response In Automotive Cyber SecurityPresenting our set of slides with Icon For Incident Response In Automotive Cyber Security This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Icon For Incident, Response In Automotive, Cyber Security
-
 Icon For Role Of 5g Technology In Automotive Cyber Security
Icon For Role Of 5g Technology In Automotive Cyber SecurityIntroducing our premium set of slides with Icon For Role Of 5g Technology In Automotive Cyber Security Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Icon For Role, 5G Technology In Automotive, Cyber Security So download instantly and tailor it with your information.
-
 Icon For Utilization Of Blockchain In Automotive Cyber Security
Icon For Utilization Of Blockchain In Automotive Cyber SecurityPresenting our set of slides with Icon For Utilization Of Blockchain In Automotive Cyber Security This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Icon For Utilization, Blockchain In Automotive, Cyber Security
-
 Impact Analysis Of Cyber Security Threats In Automotive Industry
Impact Analysis Of Cyber Security Threats In Automotive IndustryThis slide highlights influence assessment cyber security risks in automobile industry. The purpose of this slide is to aid businesses in evaluating potential consequences of digital factors. It includes elements such as data privacy, supply chain disruption, etc. Introducing our premium set of slides with Impact Analysis Of Cyber Security Threats In Automotive Industry Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Privacy, Intellectual Property, Supply Chain Disruption So download instantly and tailor it with your information.
-
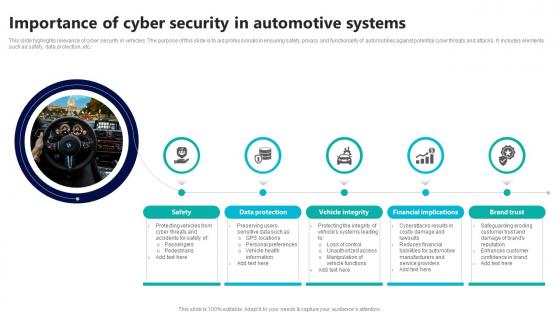 Importance Of Cyber Security In Automotive Systems
Importance Of Cyber Security In Automotive SystemsThis slide highlights relevance of cyber security in vehicles. The purpose of this slide is to aid professionals in ensuring safety, privacy and functionality of automobiles against potential cyber threats and attacks. It includes elements such as safety, data protection, etc. Presenting our set of slides with Importance Of Cyber Security In Automotive Systems This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Protection, Vehicle Integrity, Financial Implications.
-
 Risk Assessment And Mitigation In Automotive Cybersecurity
Risk Assessment And Mitigation In Automotive CybersecurityThis slide highlights risk evaluation and minimization strategies in automotive cybersecurity. The purpose of this slide is to aid businesses in identifying vulnerabilities associated with cybersecurity of systems. It includes elements such as malware, human factors, etc. Introducing our Risk Assessment And Mitigation In Automotive Cybersecurity set of slides. The topics discussed in these slides are Unauthorized Access, Supply Chain Security, Incident Response This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
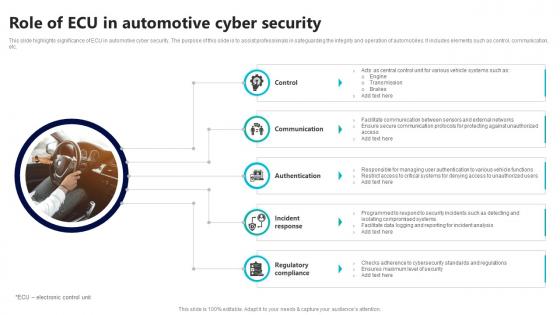 Role Of Ecu In Automotive Cyber Security
Role Of Ecu In Automotive Cyber SecurityThis slide highlights significance of ECU in automotive cyber security. The purpose of this slide is to assist professionals in safeguarding the integrity and operation of automobiles. It includes elements such as control, communication, etc. Presenting our set of slides with Role Of Ecu In Automotive Cyber Security This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Communication, Authentication, Incident Response
-
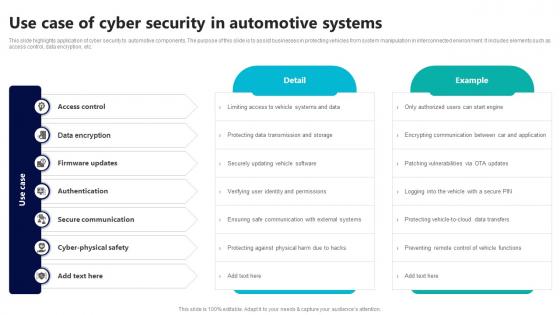 Use Case Of Cyber Security In Automotive Systems
Use Case Of Cyber Security In Automotive SystemsThis slide highlights application of cyber security to automotive components. The purpose of this slide is to assist businesses in protecting vehicles from system manipulation in interconnected environment. It includes elements such as access control, data encryption, etc. Introducing our premium set of slides with Use Case Of Cyber Security In Automotive Systems Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Access Control, Data Encryption, Firmware Updates So download instantly and tailor it with your information.
-
 Cyber Security Crisis Monitoring Solutions
Cyber Security Crisis Monitoring SolutionsThe purpose of this slide is to help cybersecurity professionals in monitoring potential threats and implementing proactive solutions such as detecting security incidents, assessing account activity, monitoring network traffic, etc. Presenting our set of slides with Cyber Security Crisis Monitoring Solutions This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Detect Security Incidents, Cyber Risk Management, Assess Account Activity
-
 Addressing Emerging Challenges Icon Of Cybersecurity
Addressing Emerging Challenges Icon Of CybersecurityPresenting our set of slides with Addressing Emerging Challenges Icon Of Cybersecurity This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Addressing Emerging Challenges Icon, Cybersecurity
-
 Cybersecurity Challenge Icon For Ensuring Business Continuity
Cybersecurity Challenge Icon For Ensuring Business ContinuityIntroducing our premium set of slides with Cybersecurity Challenge Icon For Ensuring Business Continuity Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cybersecurity Challenge Icon, Ensuring Business Continuity So download instantly and tailor it with your information.
-
 Cybersecurity Challenges Faced By Financial Services Department
Cybersecurity Challenges Faced By Financial Services DepartmentThis slide covers cybersecurity challenges for protecting assets, maintaining trust, and ensuring financial system stability. It includes issues such as skill shortages, legacy systems, and supply chain risks. Introducing our Cybersecurity Challenges Faced By Financial Services Department set of slides. The topics discussed in these slides are Skill Shortages, Legacy Systems, Supply Chain Risks This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
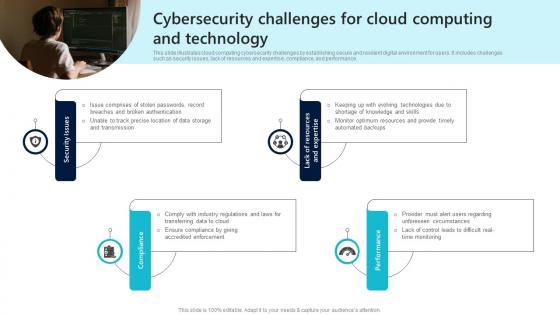 Cybersecurity Challenges For Cloud Computing And Technology
Cybersecurity Challenges For Cloud Computing And TechnologyThis slide illustrates cloud computing cybersecurity challenges by establishing secure and resilient digital environment for users. It includes challenges such as security issues, lack of resources and expertise, compliance, and performance. Presenting our well structured Cybersecurity Challenges For Cloud Computing And Technology The topics discussed in this slide are Security Issues, Compliance, Performance This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
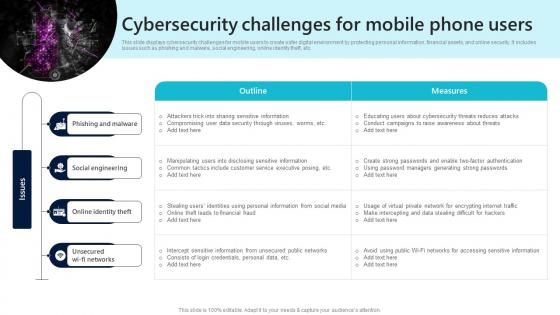 Cybersecurity Challenges For Mobile Phone Users
Cybersecurity Challenges For Mobile Phone UsersThis slide displays cybersecurity challenges for mobile users to create safer digital environment by protecting personal information, financial assets, and online security. It includes issues such as phishing and malware, social engineering, online identity theft, etc. Introducing our Cybersecurity Challenges For Mobile Phone Users set of slides. The topics discussed in these slides are Phishing And Malware, Social Engineering, Online Identity Theft This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
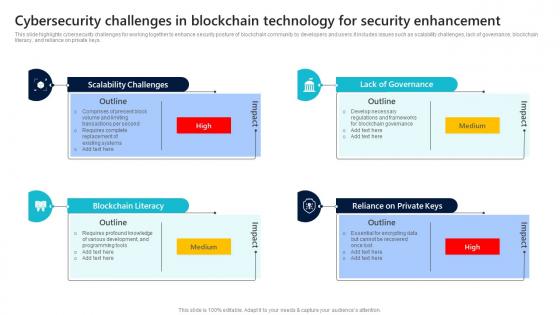 Cybersecurity Challenges In Blockchain Technology For Security Enhancement
Cybersecurity Challenges In Blockchain Technology For Security EnhancementThis slide highlights cybersecurity challenges for working together to enhance security posture of blockchain community by developers and users.It includes issues such as scalability challenges, lack of governance, blockchain literacy, and reliance on private keys. Presenting our set of slides with Cybersecurity Challenges In Blockchain Technology For Security Enhancement This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Scalability Challenges, Blockchain Literacy, Lack Of Governance
-
 Cybersecurity Challenges In Supply Chain Management
Cybersecurity Challenges In Supply Chain ManagementThis slide displays cybersecurity challenges in supply chain ecosystem for ensuring security, resilience, and trustworthiness of critical processes. It includes issues such as untrained staff, cloud cost management, and unsecured camera systems. Presenting our well structured Cybersecurity Challenges In Supply Chain Management The topics discussed in this slide are Challenges, Solutions, Impact This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
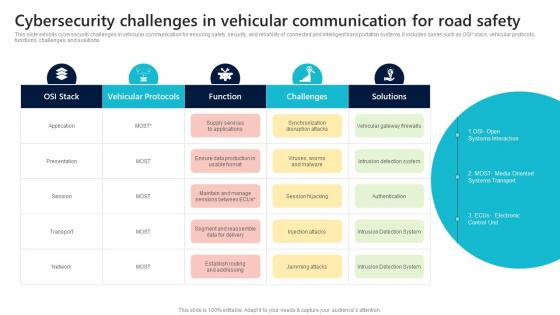 Cybersecurity Challenges In Vehicular Communication For Road Safety
Cybersecurity Challenges In Vehicular Communication For Road SafetyThis slide exhibits cybersecurity challenges in vehicular communication for ensuring safety, security, and reliability of connected and intelligent transportation systems. It includes bases such as OSI stack, vehicular protocols, functions, challenges, and solutions. Introducing our Cybersecurity Challenges In Vehicular Communication For Road Safety set of slides. The topics discussed in these slides are Systems Interaction, Systems Transport, Electronic Control Unit This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
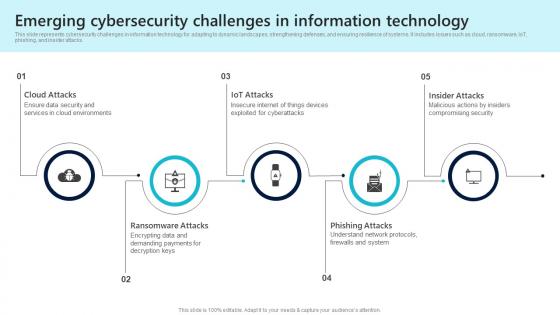 Emerging Cybersecurity Challenges In Information Technology
Emerging Cybersecurity Challenges In Information TechnologyThis slide represents cybersecurity challenges in information technology for adapting to dynamic landscapes, strengthening defenses, and ensuring resilience of systems. It includes issues such as cloud, ransomware, IoT, phishing, and insider attacks. Introducing our premium set of slides with Emerging Cybersecurity Challenges In Information Technology Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cloud Attacks, Iot Attacks, Insider Attacks So download instantly and tailor it with your information.
-
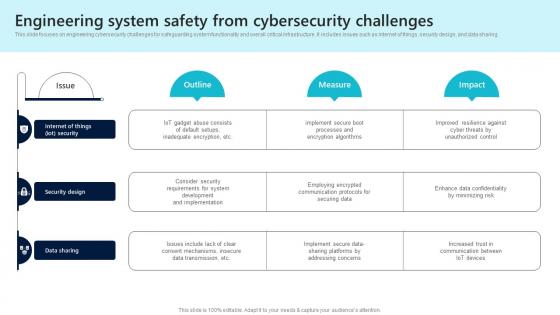 Engineering System Safety From Cybersecurity Challenges
Engineering System Safety From Cybersecurity ChallengesThis slide focuses on engineering cybersecurity challenges for safeguarding system functionality and overall critical infrastructure. It includes issues such as internet of things, security design, and data sharing. Presenting our well structured Engineering System Safety From Cybersecurity Challenges The topics discussed in this slide are Security Design, Data Sharing, Security This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 IoT Cybersecurity Challenges For Securing Sensitive Information
IoT Cybersecurity Challenges For Securing Sensitive InformationThis slide exhibits cybersecurity challenges for creating secure and resilient IoT ecosystem delivering benefits of efficiency, automation, and connectivity. It includes challenges such as software and firmware vulnerabilities, insecure communications, etc. Introducing our premium set of slides with IoT Cybersecurity Challenges For Securing Sensitive Information Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Software Firmware Vulnerabilities, Insecure Communications, Data Leaks Iot Systems So download instantly and tailor it with your information.
-
 Major Cybersecurity Challenges In Digital Banking
Major Cybersecurity Challenges In Digital BankingThis slide displays cybersecurity challenges in banking sector for protecting financial systems integrity by upholding stability of overall economy. It includes issues such as inadequate budgets, weak access management, increased ransomware, and mobile devices and apps. Presenting our set of slides with Major Cybersecurity Challenges In Digital Banking This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Inadequate Budgets, Weak Access Management, Increased Ransomware
-
 Mitigating Damage Icon By Minimizing Cybersecurity Challenges
Mitigating Damage Icon By Minimizing Cybersecurity ChallengesIntroducing our Mitigating Damage Icon By Minimizing Cybersecurity Challenges set of slides. The topics discussed in these slides are Mitigating Damage Icon, Minimizing Cybersecurity Challenges This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Navigating Cybersecurity Challenges On Maritime Attacks
Navigating Cybersecurity Challenges On Maritime AttacksThis slide represents maritime cybersecurity challenges for protecting human lives, securing assets, and maintaining overall stability of industry. It includes bases such as date, victim, location, incident type, and malware. Presenting our well structured Navigating Cybersecurity Challenges On Maritime Attacks The topics discussed in this slide are Victim, Location, Incident Type This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Overcoming Challenges Faced In Healthcare Cybersecurity
Overcoming Challenges Faced In Healthcare CybersecurityThis slide showcases healthcare cybersecurity challenges to create secure and trustworthy environment prioritizing patient privacy and safety. It includes issues such as patient privacy protection, vulnerable legacy system, IT challenges and security breaches. Introducing our Overcoming Challenges Faced In Healthcare Cybersecurity set of slides. The topics discussed in these slides are Challenges, Outline, Solutions This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Overcoming Cybersecurity Challenges In Artificial Intelligence
Overcoming Cybersecurity Challenges In Artificial IntelligenceThis slide displays cybersecurity challenges in artificial intelligence to ensure secure development, deployment, and utilization of technologies. It includes bases such as company, challenges, and AI powered cybersecurity measures. Presenting our well structured Overcoming Cybersecurity Challenges In Artificial Intelligence The topics discussed in this slide are Ai Powered, Cybersecurity Measures, Challenges, Company This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Common Cyber Attacks On Smart Contracts Ppt Slides Graphics Download
Common Cyber Attacks On Smart Contracts Ppt Slides Graphics DownloadThe purpose of this slide is to highlight the cyber attacks on smart contracts these include reentrancy attacks, transaction order dependence, force-feeding, etc. Deliver an outstanding presentation on the topic using this Common Cyber Attacks On Smart Contracts Ppt Slides Graphics Download. Dispense information and present a thorough explanation of Reentrancy Attacks, Force Feeding Attacks, Transaction Order Dependence, Denial Of Service using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Emergency Plan Icon For Risk Mitigation And Preparedness
Cyber Emergency Plan Icon For Risk Mitigation And PreparednessIntroducing our premium set of slides with Cyber Emergency Plan Icon For Risk Mitigation And Preparedness. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Emergency Plan, Risk Mitigation. So download instantly and tailor it with your information.
-
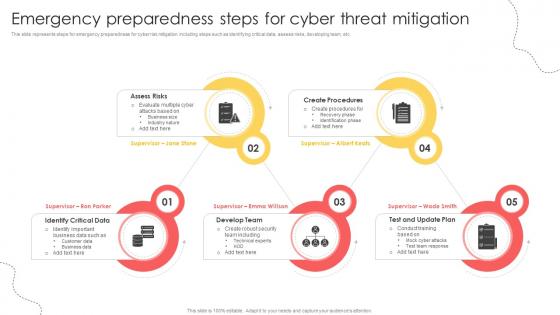 Emergency Preparedness Steps For Cyber Threat Mitigation
Emergency Preparedness Steps For Cyber Threat MitigationThis slide represents steps for emergency preparedness for cyber risk mitigation including steps such as identifying critical data, assess risks, developing team, etc. Introducing our premium set of slides with Emergency Preparedness Steps For Cyber Threat Mitigation. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Assess Risks, Create Procedures, Develop Team. So download instantly and tailor it with your information.
-
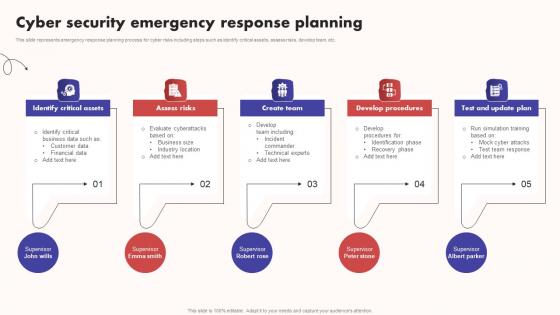 Cyber Security Emergency Response Planning
Cyber Security Emergency Response PlanningThis slide represents emergency response planning process for cyber risks including steps such as identify critical assets, assess risks, develop team, etc. Introducing our premium set of slides with Cyber Security Emergency Response Planning. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identify Critical Assets, Assess Risks, Develop Procedures. So download instantly and tailor it with your information.
-
 Comparison Of Cybersecurity Apps For Threat Detection
Comparison Of Cybersecurity Apps For Threat DetectionThis slide represents comparison table for cybersecurity applications for online risk mitigation including Wireshark, Metasploit, and Entersoft apps. Introducing our premium set of slides with Comparison Of Cybersecurity Apps For Threat Detection. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Network Protocol Analysis, Security Assessment, Infrastructure Security Analysis. So download instantly and tailor it with your information.
-
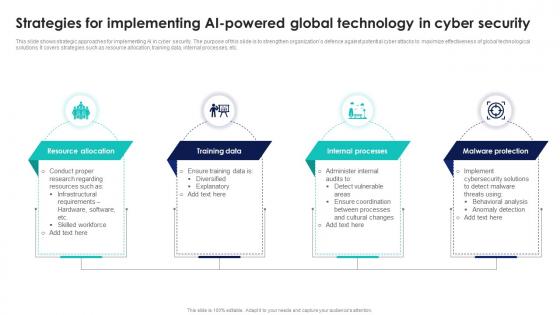 Strategies For Implementing AI Powered Global Technology In Cyber Security
Strategies For Implementing AI Powered Global Technology In Cyber SecurityThis slide shows strategic approaches for implementing AI in cyber security. The purpose of this slide is to strengthen organizations defence against potential cyber attacks to maximize effectiveness of global technological solutions. It covers strategies such as resource allocation, training data, internal processes, etc. Presenting our set of slides with Strategies For Implementing AI Powered Global Technology In Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Resource Allocation, Training Data, Internal Processes.
-
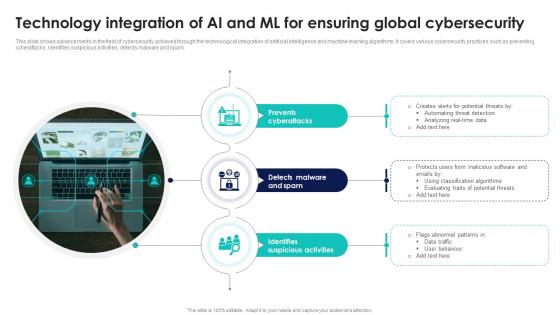 Technology Integration Of AI And ML For Ensuring Global Cybersecurity
Technology Integration Of AI And ML For Ensuring Global CybersecurityThis slide shows advancements in the field of cybersecurity achieved through the technological integration of artificial intelligence and machine learning algorithms. It covers various cybersecurity practices such as preventing cyberattacks, identifies suspicious activities, detects malware and spam. Presenting our set of slides with Technology Integration Of AI And ML For Ensuring Global Cybersecurity. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Prevents Cyberattacks, Detects Malware, Identifies Suspicious Activities.
-
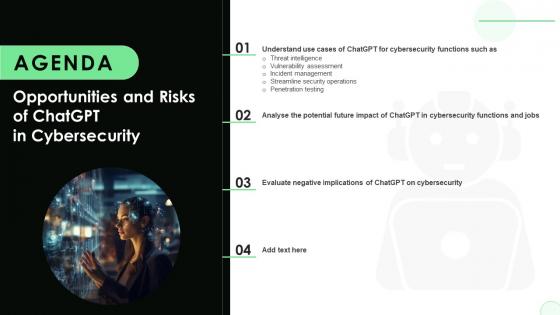 Agenda Opportunities And Risks Of ChatGPT In Cybersecurity AI SS V
Agenda Opportunities And Risks Of ChatGPT In Cybersecurity AI SS VIntroducing Agenda Opportunities And Risks Of ChatGPT In Cybersecurity AI SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on ChatGPT On Cybersecurity, Cybersecurity Functions And Jobs, Potential Future Impact Of ChatGPT, using this template. Grab it now to reap its full benefits.
-
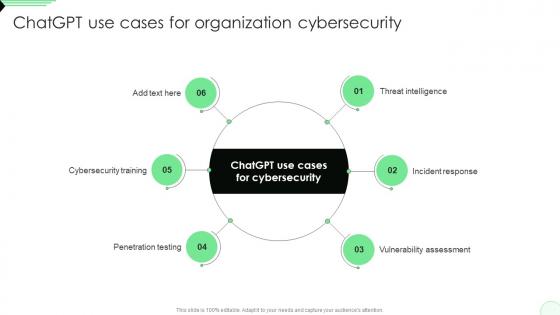 ChatGPT Use Cases For Organization Cybersecurity Opportunities And Risks Of ChatGPT AI SS V
ChatGPT Use Cases For Organization Cybersecurity Opportunities And Risks Of ChatGPT AI SS VIntroducing ChatGPT Use Cases For Organization Cybersecurity Opportunities And Risks Of ChatGPT AI SS V to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Cybersecurity Training, Penetration Testing, Vulnerability Assessment, Incident Response, using this template. Grab it now to reap its full benefits.
-
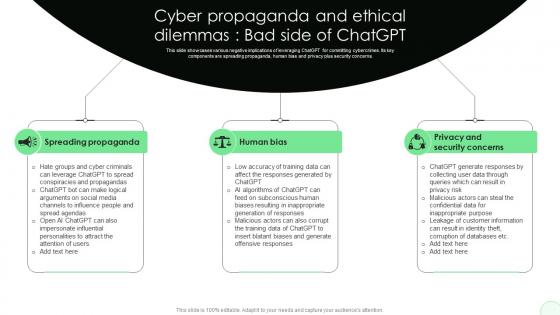 Cyber Propaganda And Ethical Dilemmas Opportunities And Risks Of ChatGPT AI SS V
Cyber Propaganda And Ethical Dilemmas Opportunities And Risks Of ChatGPT AI SS VThis slide showcases various negative implications of leveraging ChatGPT for committing cybercrimes. Its key components are spreading propaganda, human bias and privacy plus security concerns. Introducing Cyber Propaganda And Ethical Dilemmas Opportunities And Risks Of ChatGPT AI SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Spreading Propaganda, Human Bias, Privacy And Security Concerns, using this template. Grab it now to reap its full benefits.
-
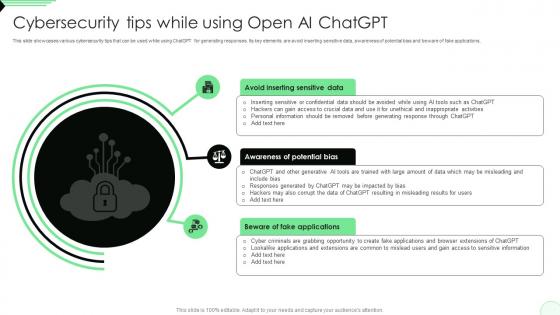 Cybersecurity Tips While Using Open AI ChatGPT Opportunities And Risks Of ChatGPT AI SS V
Cybersecurity Tips While Using Open AI ChatGPT Opportunities And Risks Of ChatGPT AI SS VThis slide showcases various cybersecurity tips that can be used while using ChatGPT for generating responses. Its key elements are avoid inserting sensitive data, awareness of potential bias and beware of fake applications. Increase audience engagement and knowledge by dispensing information using Cybersecurity Tips While Using Open AI ChatGPT Opportunities And Risks Of ChatGPT AI SS V. This template helps you present information on three stages. You can also present information on Avoid Inserting Sensitive Data, Awareness Of Potential Bias, Beware Of Fake Applications using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.



