Powerpoint Templates and Google slides for Cyber Protection Deal
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Organization Cyber Protection Proposal Powerpoint Presentation Slides
Organization Cyber Protection Proposal Powerpoint Presentation SlidesPresenting our readily available Organization Cyber Protection Proposal PowerPoint Presentation Slides for your bidding needs. This is a completely adaptable PPT theme that lets you add images, charts, icons, and tables according to your need. The template is available in both 4:3 and 16:9 aspect ratios. It can be downloaded in PDF, JPG, and PNG formats. So download and captivate your audience.
-
 Cyber Protection Analytics Powerpoint Ppt Template Bundles
Cyber Protection Analytics Powerpoint Ppt Template BundlesIf you require a professional template with great design, then this Cyber Protection Analytics Powerpoint Ppt Template Bundles is an ideal fit for you. Deploy it to enthrall your audience and increase your presentation threshold with the right graphics, images, and structure. Portray your ideas and vision using fifteen slides included in this complete deck. This template is suitable for expert discussion meetings presenting your views on the topic. With a variety of slides having the same thematic representation, this template can be regarded as a complete package. It employs some of the best design practices, so everything is well-structured. Not only this, it responds to all your needs and requirements by quickly adapting itself to the changes you make. This PPT slideshow is available for immediate download in PNG, JPG, and PDF formats, further enhancing its usability. Grab it by clicking the download button.
-
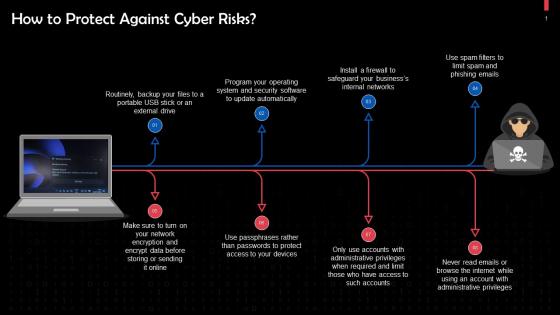
 Protecting Your Organizations From Cyber Risks Training Ppt
Protecting Your Organizations From Cyber Risks Training PptPresenting Protecting Your Organizations from Cyber Risks. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Protection Against Cyber Threats And Attacks Training Ppt
Protection Against Cyber Threats And Attacks Training PptPresenting Protection Against Cyber Threats and Attacks. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Cyber Security Icon Network Protection Threat Server Database Software
Cyber Security Icon Network Protection Threat Server Database SoftwareKeep your audience glued to their seats with professionally designed PPT slides. This deck comprises of total of twelve slides. It has PPT templates with creative visuals and well researched content. Not just this, our PowerPoint professionals have crafted this deck with appropriate diagrams, layouts, icons, graphs, charts and more. This content ready presentation deck is fully editable. Just click the DOWNLOAD button below. Change the colour, text and font size. You can also modify the content as per your need. Get access to this well crafted complete deck presentation and leave your audience stunned.
-
 Cyber safety tips protection against cyberattacks computer system security
Cyber safety tips protection against cyberattacks computer system securityThis slide represents various tips or procedures that can be followed to prevent an organizations cyber security from cyberattacks or cybercriminals. Increase audience engagement and knowledge by dispensing information using Cyber Safety Tips Protection Against Cyberattacks Computer System Security. This template helps you present information on five stages. You can also present information on Cyber Safety Tips Protection Against Cyberattacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
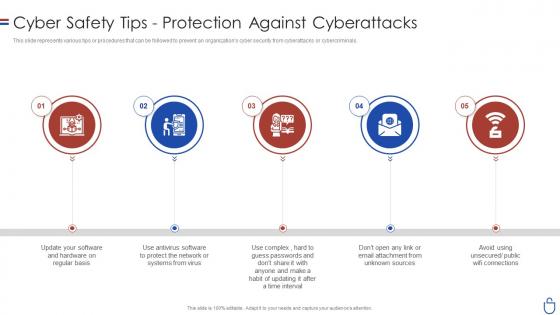 Data security it cyber safety tips protection against cyberattacks
Data security it cyber safety tips protection against cyberattacksThis slide represents various tips or procedures that can be followed to prevent an organizations cyber security from cyberattacks or cybercriminals. Increase audience engagement and knowledge by dispensing information using Data Security IT Cyber Safety Tips Protection Against Cyberattacks. This template helps you present information on five stages. You can also present information on Sources, Public Wifi Connections, Time Interval, Protect Network using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Protect Against Internal Cyber Threats In Powerpoint And Google Slides Cpb
Protect Against Internal Cyber Threats In Powerpoint And Google Slides CpbPresenting our Protect Against Internal Cyber Threats In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Protect Against Internal Cyber Threats This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cyber Security Data Protection Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Cyber Security Data Protection Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured PowerPoint icon is a visual representation of a Cyber Security Action Plan for Data Protection. It illustrates the essential steps needed to ensure the safety of sensitive data and prevent cyber-attacks. Perfect for presentations, reports, and other documents.
-
 Cyber Security Data Protection Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Cyber Security Data Protection Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon depicts a comprehensive action plan for data protection and cyber security. It is a great visual aid to help organizations understand the steps needed to protect their data and ensure cyber security.
-
 Banking Sector Cyber Protection AI Image PowerPoint Presentation PPT ECS
Banking Sector Cyber Protection AI Image PowerPoint Presentation PPT ECSIntroducing a Visual PPT on Banking Sector Cyber Protection. Our Presentation Specialists have taken great care in designing each slide in this PowerPoint. Feel free to tailor the content. The PPT Template fits well with any screen size, and its also compatible with Google Slides. Download the PPT, and present it confidently.
-
 Cyber Protection for Financial Operations AI Image PowerPoint Presentation PPT ECS
Cyber Protection for Financial Operations AI Image PowerPoint Presentation PPT ECSIntroducing a Visual PPT on Cyber Protection for Financial Operations. Our design team have meticulously designed every PowerPoint Slide. Tailor the PPT content effortlessly. Additionally, the PPT Template is compatible with all monitor sizes and as well as Google Slides. Download the PPT, make the needed adjustments, and showcase with conviction.
-
 Advantages Of Utilizing Advanced Threat Protection In Cyber Security
Advantages Of Utilizing Advanced Threat Protection In Cyber SecurityThe following slide highlights the possible benefits of implementing advanced threat protection against sophisticated cyber threats and attacks. Presenting our set of slides with Advantages Of Utilizing Advanced Threat Protection In Cyber Security. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security, Analytics, Protection.
-
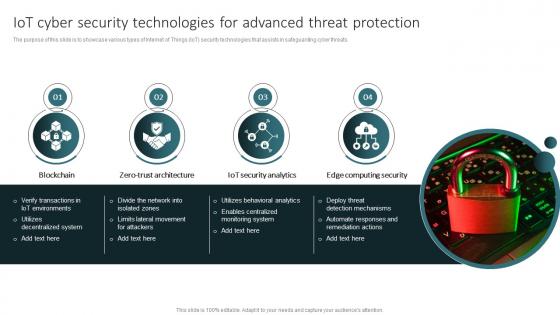 IoT Cyber Security Technologies For Advanced Threat Protection
IoT Cyber Security Technologies For Advanced Threat ProtectionThe purpose of this slide is to showcase various types of Internet of Things IoT security technologies that assists in safeguarding cyber threats. Introducing our premium set of slides with IoT Cyber Security Technologies For Advanced Threat Protection. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Architecture, Security, Computing. So download instantly and tailor it with your information.
-
 Cyber Security Checklist To Protect Saas Applications
Cyber Security Checklist To Protect Saas ApplicationsThis slide represents cybersecurity checklist for SaaS applications to protect data. It aims to assist organizations in identifying potential vulnerabilities as well as examining security standards. It includes various elements such as backing up creation and testing, using real-time security service, etc. Introducing our Cyber Security Checklist To Protect Saas Applications set of slides. The topics discussed in these slides are Determines Data Isolation, Safeguards Against Data Theft This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Saas Cyber Security Icon To Protect Sensitive Data
Saas Cyber Security Icon To Protect Sensitive DataIntroducing our Saas Cyber Security, Icon To Protect Sensitive Data set of slides. The topics discussed in these slides are Saas Cyber Security, Icon To Protect Sensitive Data This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
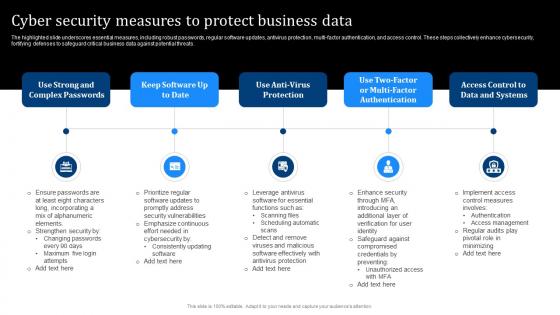 Cyber Security Measures To Protect Business Data
Cyber Security Measures To Protect Business DataThe highlighted slide underscores essential measures, including robust passwords, regular software updates, antivirus protection, multi factor authentication, and access control. These steps collectively enhance cybersecurity, fortifying defenses to safeguard critical business data against potential threats. Presenting our set of slides with Cyber Security Measures To Protect Business Data. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Strong And Complex Passwords, Software Updates, Enhance Security.
-
 Cyber Security Audit Protection Icon
Cyber Security Audit Protection IconIntroducing our premium set of slides with Cyber Security Audit Protection Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Security, Audit Protection Icon. So download instantly and tailor it with your information.
-
 Cloning In Cyber Security For Data Protection
Cloning In Cyber Security For Data ProtectionThis slide shows benefits of cloning for cyber protection. It aims to prevent cloning security risks to mitigate unauthorized access to technical assets. It covers four cyber security measures such as data protection, integrity, loss prevention and transfers. Presenting our set of slides with name Cloning In Cyber Security For Data Protection. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Protection, Data Integrity, Data Transfers.
-
 Cyber Security Icon Protecting Card Cloning Fraud
Cyber Security Icon Protecting Card Cloning FraudIntroducing our premium set of slides with name Cyber Security Icon Protecting Card Cloning Fraud. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Security, Icon Protecting, Card Cloning Fraud. So download instantly and tailor it with your information.
-
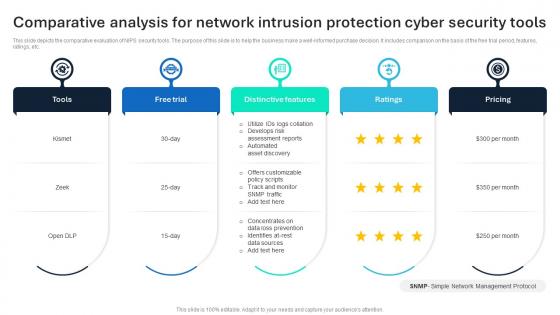 Comparative Analysis For Network Intrusion Protection Cyber Security Tools
Comparative Analysis For Network Intrusion Protection Cyber Security ToolsThis slide depicts the comparative evaluation of NIPS security tools. The purpose of this slide is to help the business make a well informed purchase decision. It includes comparison on the basis of the free trial period, features, ratings, etc. Introducing our premium set of slides with Comparative Analysis For Network Intrusion Protection Cyber Security Tools Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Distinctive Features, Free Trial, Tools So download instantly and tailor it with your information.
-
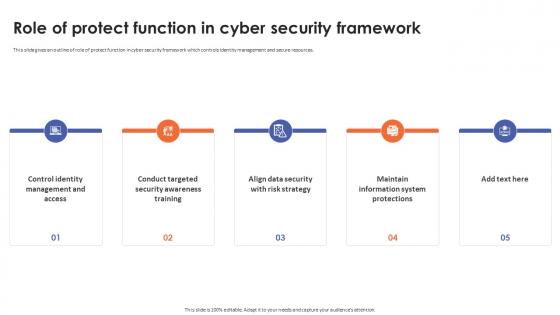 Role Of Protect Function In Cyber Security Framework
Role Of Protect Function In Cyber Security FrameworkThis slide gives an outline of role of protect function in cyber security framework which controls identity management and secure resources. Introducing Role Of Protect Function In Cyber Security Framework to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Security Awareness Training, Data Security With Risk Strategy, Maintain Information System Protections, using this template. Grab it now to reap its full benefits.
-
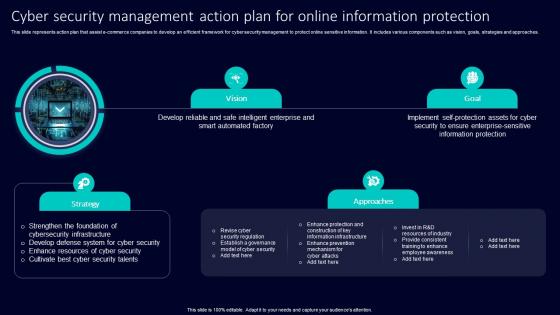 Cyber Security Management Action Plan For Online Information Protection
Cyber Security Management Action Plan For Online Information ProtectionThis slide represents action plan that assist e commerce companies to develop an efficient framework for cyber security management to protect online sensitive information. It includes various components such as vision, goals, strategies and approaches. Presenting our set of slides with Cyber Security Management Action Plan For Online Information Protection. This exhibits information on two stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Strengthen Foundation Cybersecurity Infrastructure, Develop Defense System Cyber Security, Enhance Resources Cyber Security.
-
 Extensive Business Strategy Cyber Strategies For KPMG For Client Data Protection Strategy SS V
Extensive Business Strategy Cyber Strategies For KPMG For Client Data Protection Strategy SS VThis slide covers techniques to secure customers confidential data through several cyber security strategies. The purpose for this template is to provide an overview on important elements of top techniques deployed by the company . It includes strategies such as people, process, data and technology and regulatory. Introducing Extensive Business Strategy Cyber Strategies For KPMG For Client Data Protection Strategy SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on People, Process, Regulatory, using this template. Grab it now to reap its full benefits.
-
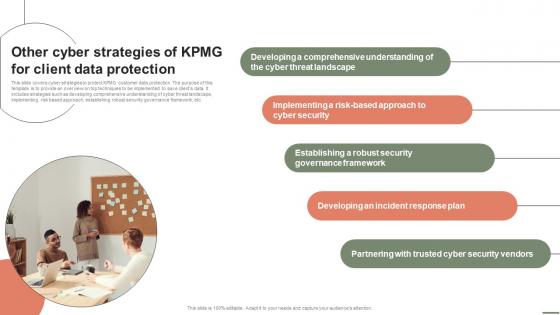 Extensive Business Strategy Other Cyber Strategies Of KPMG For Client Data Protection Strategy SS V
Extensive Business Strategy Other Cyber Strategies Of KPMG For Client Data Protection Strategy SS VThis slide covers cyber strategies to protect KPMG customer data protection. The purpose of this template is to provide an overview on top techniques to be implemented to save clients data. It includes strategies such as developing comprehensive understanding of cyber threat landscape, implementing risk based approach, establishing robust security governance framework, etc. Increase audience engagement and knowledge by dispensing information using Extensive Business Strategy Other Cyber Strategies Of KPMG For Client Data Protection Strategy SS V. This template helps you present information on five stages. You can also present information on Threat Landscape, Cyber Security, Governance Framework using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
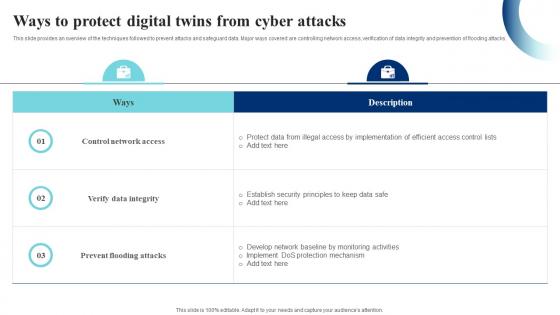 Ways To Protect Digital Twins From Cyber Attacks IoT Digital Twin Technology IOT SS
Ways To Protect Digital Twins From Cyber Attacks IoT Digital Twin Technology IOT SSThis slide provides an overview of the techniques followed to prevent attacks and safeguard data. Major ways covered are controlling network access, verification of data integrity and prevention of flooding attacks. Present the topic in a bit more detail with this Ways To Protect Digital Twins From Cyber Attacks IoT Digital Twin Technology IOT SS. Use it as a tool for discussion and navigation on Control Network Access, Prevent Flooding Attacks, Verify Data Integrity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Icon For Bug Analytics Cyber Protection
Icon For Bug Analytics Cyber ProtectionPresenting our set of slides with Icon For Bug Analytics Cyber Protection. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security, Bug Analytics, Icon.
-
 Icon For Cyber Protection With Threat Analytics
Icon For Cyber Protection With Threat AnalyticsIntroducing our premium set of slides with Icon For Cyber Protection With Threat Analytics. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Security, Threat Analytics, Icon. So download instantly and tailor it with your information.
-
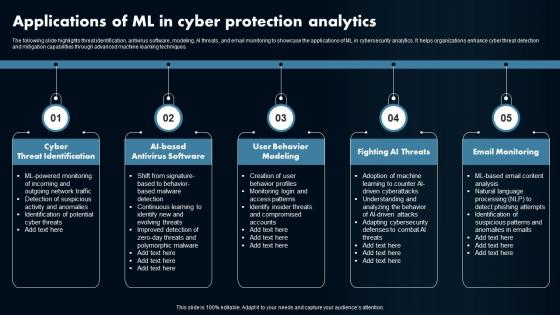 Applications Of ML In Cyber Protection Analytics
Applications Of ML In Cyber Protection AnalyticsThe following slide highlights threat identification, antivirus software, modeling, AI threats, and email monitoring to showcase the applications of ML in cybersecurity analytics. It helps organizations enhance cyber threat detection and mitigation capabilities through advanced machine learning techniques Presenting our set of slides with Applications Of ML In Cyber Protection Analytics. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Threat Identification, Antivirus Software, User Behavior Modeling.
-
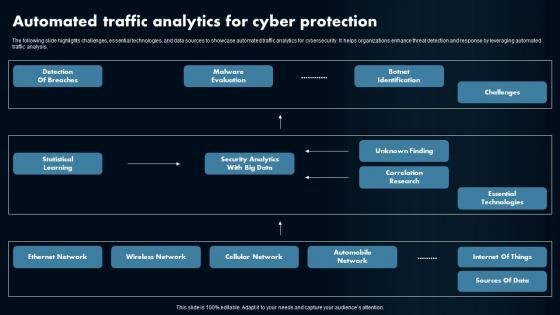 Automated Traffic Analytics For Cyber Protection
Automated Traffic Analytics For Cyber ProtectionThe following slide highlights challenges, essential technologies, and data sources to showcase automated traffic analytics for cybersecurity. It helps organizations enhance threat detection and response by leveraging automated traffic analysis. Introducing our Automated Traffic Analytics For Cyber Protection set of slides. The topics discussed in these slides are Detection Of Breaches, Malware Evaluation, Challenges. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
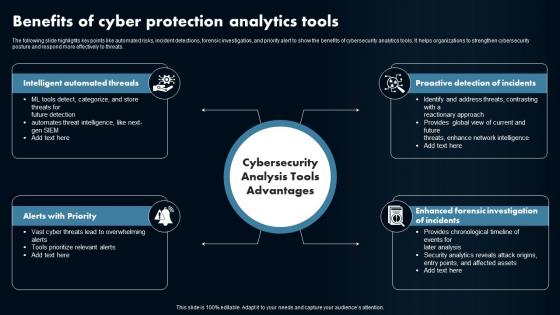 Benefits Of Cyber Protection Analytics Tools
Benefits Of Cyber Protection Analytics ToolsThe following slide highlights key points like automated risks, incident detections, forensic investigation, and priority alert to show the benefits of cybersecurity analytics tools. It helps organizations to strengthen cybersecurity posture and respond more effectively to threats. Introducing our premium set of slides with Benefits Of Cyber Protection Analytics Tools. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Alerts with Priority, Intelligent Automated Threads. So download instantly and tailor it with your information.
-
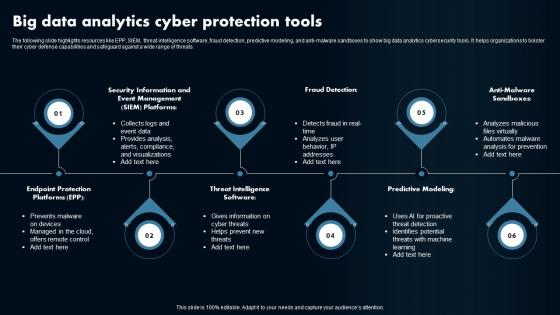 Big Data Analytics Cyber Protection Tools
Big Data Analytics Cyber Protection ToolsThe following slide highlights resources like EPP, SIEM, threat intelligence software, fraud detection, predictive modeling, and anti-malware sandboxes to show big data analytics cybersecurity tools. It helps organizations to bolster their cyber defense capabilities and safeguard against a wide range of threats. Presenting our set of slides with Big Data Analytics Cyber Protection Tools. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Fraud Detection, Predictive Modeling, Anti-Malware Sandboxes.
-
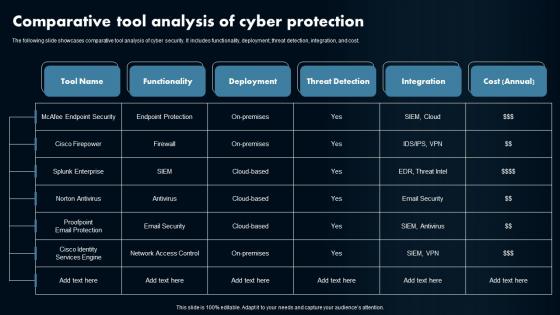 Comparative Tool Analysis Of Cyber Protection
Comparative Tool Analysis Of Cyber ProtectionThe following slide showcases comparative tool analysis of cyber security. It includes functionality, deployment, threat detection, integration, and cost Introducing our Comparative Tool Analysis Of Cyber Protection set of slides. The topics discussed in these slides are Tool Name, Functionality, Deployment. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Protection Analytics Best Practices
Cyber Protection Analytics Best PracticesThe following slide highlights firewall protection, security software, strong password enforcement, two-factor authentication, and regular data backup to emphasize cybersecurity analytics best practices. It helps organizations fortify defenses and safeguard sensitive information from cyber threats. Introducing our premium set of slides with Cyber Protection Analytics Best Practices. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Firewall Protection, Security Software, Factor Authentication . So download instantly and tailor it with your information.
-
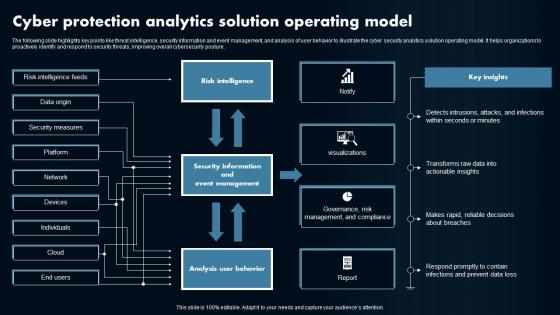 Cyber Protection Analytics Solution Operating Model
Cyber Protection Analytics Solution Operating ModelThe following slide highlights key points like threat intelligence, security information and event management, and analysis of user behavior to illustrate the cyber security analytics solution operating model. It helps organizations to proactively identify and respond to security threats, improving overall cybersecurity posture Presenting our well structured Cyber Protection Analytics Solution Operating Model. The topics discussed in this slide are Risk Intelligence, Key Insights, Analysis User Behavior. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
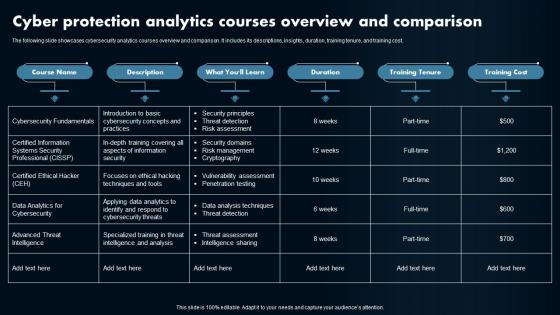 Cyber Protection Analytics Courses Overview And Comparison
Cyber Protection Analytics Courses Overview And ComparisonThe following slide showcases cybersecurity analytics courses overview and comparison. It includes its descriptions, insights, duration, training tenure, and training cost Introducing our Cyber Protection Analytics Courses Overview And Comparison set of slides. The topics discussed in these slides are Course Name, Description, Duration. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
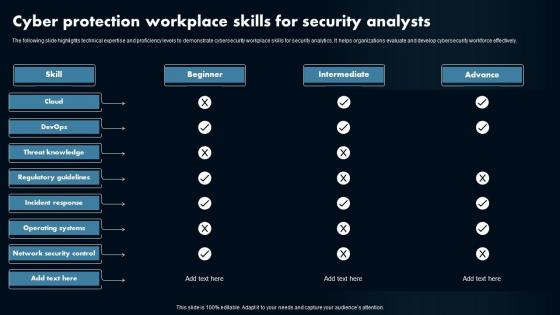 Cyber Protection Workplace Skills For Security Analysts
Cyber Protection Workplace Skills For Security AnalystsThe following slide highlights technical expertise and proficiency levels to demonstrate cybersecurity workplace skills for security analytics. It helps organizations evaluate and develop cybersecurity workforce effectively Presenting our well structured Cyber Protection Workplace Skills For Security Analysts. The topics discussed in this slide are Beginner, Intermediate, Advance. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
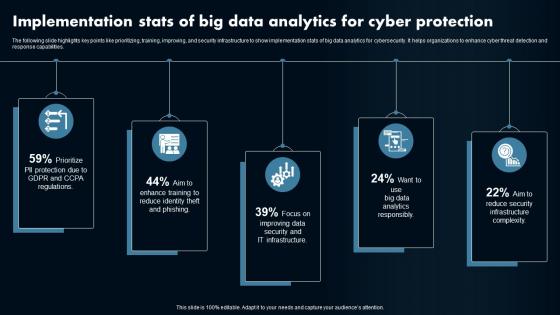 Implementation Stats Of Big Data Analytics For Cyber Protection
Implementation Stats Of Big Data Analytics For Cyber ProtectionThe following slide highlights key points like prioritizing, training, improving, and security infrastructure to show implementation stats of big data analytics for cybersecurity. It helps organizations to enhance cyber threat detection and response capabilities. Presenting our set of slides with Implementation Stats Of Big Data Analytics For Cyber Protection. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Implementation, Data Analytics, Cybersecurity.
-
 Strategies For Big Data Cyber Protection Analytics
Strategies For Big Data Cyber Protection AnalyticsThe following slide highlights key points like data collection, data normalization, expansion, enrichment, automation, standardization, and advanced detection to show strategies for big data analytics cybersecurity. It helps organizations to proactively defend against cyber threats and enhance overall security posture. Introducing our premium set of slides with Strategies For Big Data Cyber Protection Analytics. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Collection, Data Normalization, Expansion. So download instantly and tailor it with your information.
-
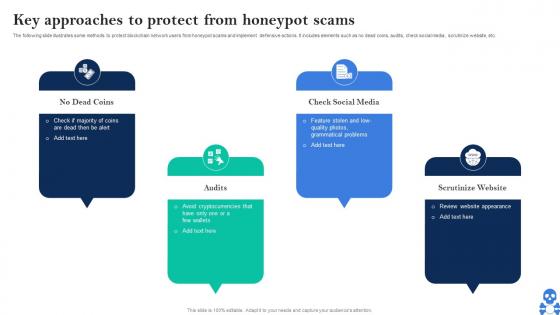 Cyber Threats In Blockchain Key Approaches To Protect From Honeypot Scams BCT SS V
Cyber Threats In Blockchain Key Approaches To Protect From Honeypot Scams BCT SS VThe following slide illustrates some methods to protect blockchain network users from honeypot scams and implement defensive actions. It includes elements such as no dead coins, audits, check social media, scrutinize website, etc. Introducing Cyber Threats In Blockchain Key Approaches To Protect From Honeypot Scams BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on No Dead Coins, Check Social Media, Scrutinize Website using this template. Grab it now to reap its full benefits.
-
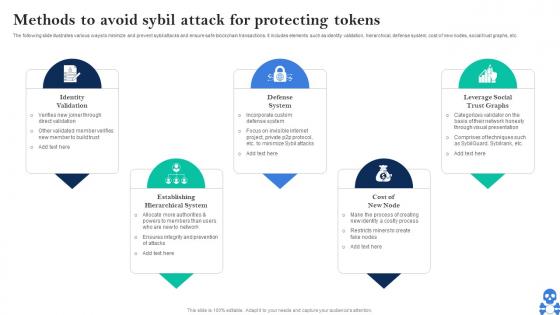 Cyber Threats In Blockchain Methods To Avoid Sybil Attack For Protecting Tokens BCT SS V
Cyber Threats In Blockchain Methods To Avoid Sybil Attack For Protecting Tokens BCT SS VThe following slide illustrates various ways to minimize and prevent sybil attacks and ensure safe blockchain transactions. It includes elements such as identity validation, hierarchical, defense system, cost of new nodes, social trust graphs, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Methods To Avoid Sybil Attack For Protecting Tokens BCT SS V This template helps you present information on Five stages. You can also present information on Identity Validation, Defense System, Cost Of New Node using this PPT design. This layout is completely editable so personaize it now
-
 Network Encryption Protection Icon For Cyber Security Management
Network Encryption Protection Icon For Cyber Security ManagementPresenting our set of slides with Network Encryption Protection Icon For Cyber Security Management. This exhibits information on two stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Network Encryption Protection Icon, Cyber Security Management.
-
 Triage Cyber Security For System Protection Icon
Triage Cyber Security For System Protection IconPresenting our set of slides with name Triage Cyber Security For System Protection Icon This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Triage Cyber Security, System Protection Icon
-
 Firewall Security Icon Protecting From Cyber Threats
Firewall Security Icon Protecting From Cyber ThreatsIntroducing our Firewall Security Icon Protecting From Cyber Threats set of slides. The topics discussed in these slides are Firewall Security, Protecting. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Csirt Cyber Security Icon For Protecting Data
Csirt Cyber Security Icon For Protecting DataIntroducing our premium set of slides with Csirt Cyber Security Icon For Protecting Data. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Csirt Cyber Security, Protecting Data. So download instantly and tailor it with your information.
-
 SIEM Cyber Security Protection Icon
SIEM Cyber Security Protection IconIntroducing our premium set of slides with name SIEM Cyber Security Protection Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like SIEM Cyber, Security Protection, Icon. So download instantly and tailor it with your information.
-
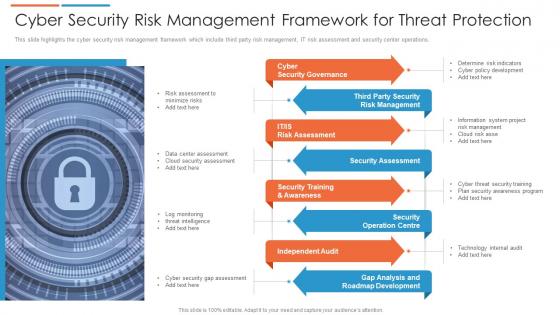 Cyber security risk management framework for threat protection
Cyber security risk management framework for threat protectionThis slide highlights the cyber security risk management framework which include third party risk management, IT risk assessment and security center operations. Presenting our set of slides with Cyber Security Risk Management Framework For Threat Protection. This exhibits information on eight stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Governance, Security Assessment, Independent Audit.
-
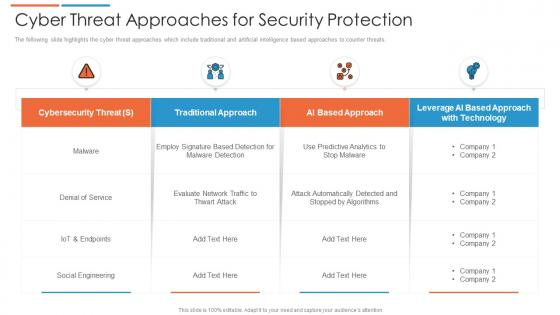 Cyber threat approaches for security protection
Cyber threat approaches for security protectionThe following slide highlights the cyber threat approaches which include traditional and artificial intelligence based approaches to counter threats. Presenting our well structured Cyber Threat Approaches For Security Protection. The topics discussed in this slide are Cybersecurity Threat, Social Engineering, Traditional Approach. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
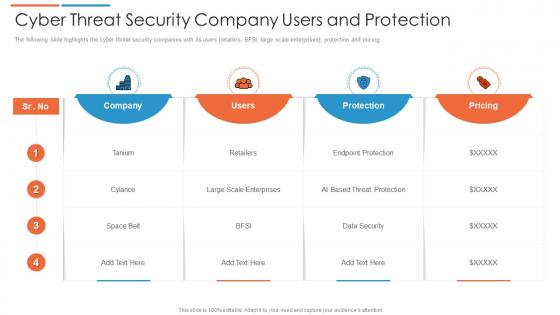 Cyber threat security company users and protection
Cyber threat security company users and protectionThe following slide highlights the cyber threat security companies with its users retailers, BFSI, large scale enterprises, protection and pricing. Introducing our Cyber Threat Security Company Users And Protection set of slides. The topics discussed in these slides are Pricing, Company, Users. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
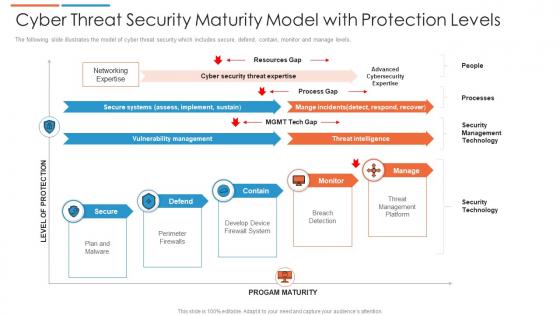 Cyber threat security maturity model with protection levels
Cyber threat security maturity model with protection levelsThe following slide illustrates the model of cyber threat security which includes secure, defend, contain, monitor and manage levels. Presenting our well structured Cyber Threat Security Maturity Model With Protection Levels. The topics discussed in this slide are Security Management Technology, Threat Management Platform, Threat Intelligence. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cyber threat strategies for security protection
Cyber threat strategies for security protectionThis slide highlights the cyber threat strategies that include risk assessment, phishing program, software protocols and end point protection. Presenting our set of slides with Cyber Threat Strategies For Security Protection. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Phishing Program, Software Protocols, End Point Protection.
-
 Cyber Protection Team Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Cyber Protection Team Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Cyber protection team colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Cyber Protection Team Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Cyber Protection Team Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Cyber protection team monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
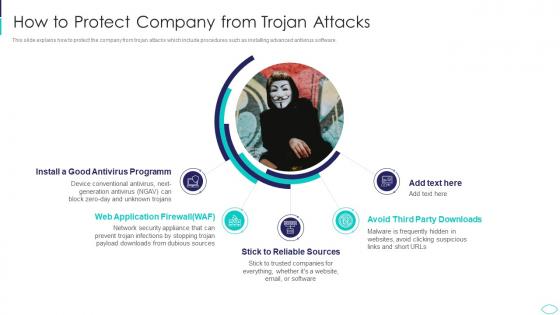 How To Protect Company From Trojan Attacks Cyber Terrorism Attacks
How To Protect Company From Trojan Attacks Cyber Terrorism AttacksThis slide explains how to protect the company from trojan attacks which include procedures such as installing advanced antivirus software. Increase audience engagement and knowledge by dispensing information using How To Protect Company From Trojan Attacks Cyber Terrorism Attacks. This template helps you present information on five stages. You can also present information on Antivirus Programm, Application Firewall, Reliable Sources, Avoid Third Party Downloads using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Techniques To Protect SCADA Systems From Cyber Terrorism Attacks
Techniques To Protect SCADA Systems From Cyber Terrorism AttacksThis slide depicts the techniques to protect SCADA from cyber attacks which include security training of employees, strict firewalls. Increase audience engagement and knowledge by dispensing information using Techniques To Protect SCADA Systems From Cyber Terrorism Attacks. This template helps you present information on six stages. You can also present information on Security Training, Access Controls, Strict Firewalls, Security Procedures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Business Cyber Security Protection Icon
Business Cyber Security Protection IconIntroducing our Business Cyber Security Protection Icon set of slides. The topics discussed in these slides are Business Cyber Security, Protection Icon. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Security With Virus Protection Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Cyber Security With Virus Protection Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Cyber security with virus protection colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Cyber Security With Virus Protection Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Cyber Security With Virus Protection Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Cyber security with virus protection monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 3 Step Cyber Security Plan For Data Protection
3 Step Cyber Security Plan For Data ProtectionThis slide signifies the three stage cyber security program to improve data protection. It covers information about steps like prevention, response and remediation. Presenting our set of slides with 3 Step Cyber Security Plan For Data Protection. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Prevention, Response, Remediation.
-
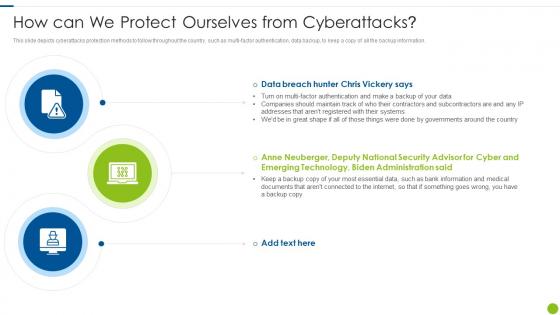 Cyber Attacks On Ukraine How Can We Protect Ourselves From Cyberattacks
Cyber Attacks On Ukraine How Can We Protect Ourselves From CyberattacksThis slide depicts cyberattacks protection methods to follow throughout the country, such as multi factor authentication, data backup, to keep a copy of all the backup information. Introducing Cyber Attacks On Ukraine How Can We Protect Ourselves From Cyberattacks to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on How Can We Protect Ourselves From Cyberattacks, using this template. Grab it now to reap its full benefits.


