Powerpoint Templates and Google slides for Cyber Threats
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Icons Slide Implementing Strategies To Mitigate Cyber Security Threats
Icons Slide Implementing Strategies To Mitigate Cyber Security ThreatsIntroducing our well researched set of slides titled Icons Slide Implementing Strategies To Mitigate Cyber Security Threats It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
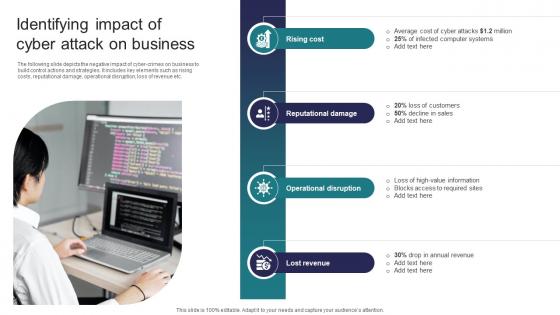 Identifying Impact Of Cyber Attack On Business Implementing Strategies To Mitigate Cyber Security Threats
Identifying Impact Of Cyber Attack On Business Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts the negative impact of cyber crimes on business to build control actions and strategies. It includes key elements such as rising costs, reputational damage, operational disruption, loss of revenue etc. Introducing Identifying Impact Of Cyber Attack On Business Implementing Strategies To Mitigate Cyber Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Rising Cost, Reputational Damage, Operational Disruption using this template. Grab it now to reap its full benefits.
-
 Impact Of Cyber Safety Security Measures Implementing Strategies To Mitigate Cyber Security Threats
Impact Of Cyber Safety Security Measures Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts the projected consequences of implementing cyber security preventive measures. It includes data about number of cyber attracts pre and post adopting latest strategies Present the topic in a bit more detail with this Impact Of Cyber Safety Security Measures Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Cyber Attack Type, Malware, Ransomware This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Impact Of Cyber Security Policies And Practices Implementing Strategies To Mitigate Cyber Security Threats
Impact Of Cyber Security Policies And Practices Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide focuses on drafting cyber security policies to manage data control and breach. It mainly includes elements such as impact of existing cyber safety policies, mitigation actions, Deliver an outstanding presentation on the topic using this Impact Of Cyber Security Policies And Practices Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Inadequate Security Guidelines, Inappropriate Privacy Policies, Insufficient Background Check using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
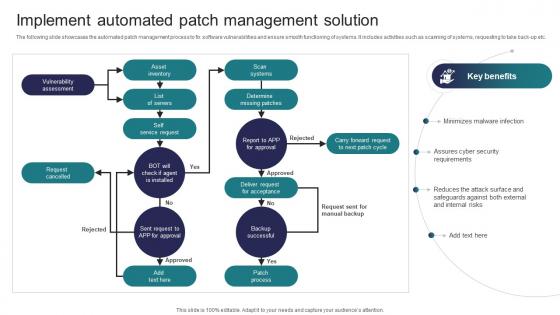 Implement Automated Patch Management Solution Implementing Strategies To Mitigate Cyber Security Threats
Implement Automated Patch Management Solution Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases the automated patch management process to fix software vulnerabilities and ensure smooth functioning of systems. It includes activities such as scanning of systems, requesting to take back up etc. Present the topic in a bit more detail with this Implement Automated Patch Management Solution Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Vulnerability Assessment, Request Cancelled, Asset Inventory This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Implementing Strategies To Mitigate Cyber Security Threats Table Of Content
Implementing Strategies To Mitigate Cyber Security Threats Table Of ContentIncrease audience engagement and knowledge by dispensing information using Implementing Strategies To Mitigate Cyber Security Threats Table Of Content This template helps you present information on one stages. You can also present information on Cyber Security, Cyber Risk using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 KPIs To Evaluate Cyber Security Risk Management Implementing Strategies To Mitigate Cyber Security Threats
KPIs To Evaluate Cyber Security Risk Management Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide highlights some key performance indicators to measure the impact of cyber security risk administration to assess its effectiveness and take improved decisions. It includes elements such as level of preparedness, mean time to detect, success rating etc. Present the topic in a bit more detail with this KPIs To Evaluate Cyber Security Risk Management Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Level Of Preparedness, Mean Time To Detect, Mean Time To Resolve This template is free to edit as deemed fit for your organization. Therefore download it now.
-
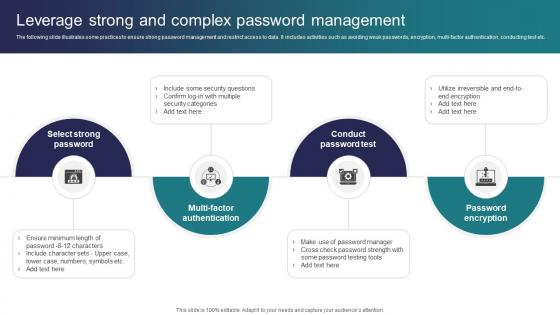 Leverage Strong And Complex Password Management Implementing Strategies To Mitigate Cyber Security Threats
Leverage Strong And Complex Password Management Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide illustrates some practices to ensure strong password management and restrict access to data. It includes activities such as avoiding weak passwords, encryption, multi factor authentication, conducting test etc. Introducing Leverage Strong And Complex Password Management Implementing Strategies To Mitigate Cyber Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Conduct Password Test, Password Encryption, Multi Factor Authentication using this template. Grab it now to reap its full benefits.
-
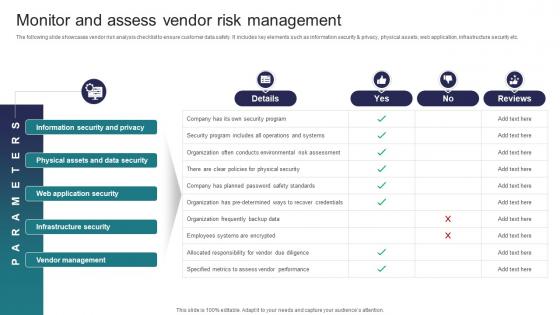 Monitor And Assess Vendor Risk Management Implementing Strategies To Mitigate Cyber Security Threats
Monitor And Assess Vendor Risk Management Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases vendor risk analysis checklist to ensure customer data safety. It includes key elements such as information security and privacy, physical assets, web application, infrastructure security etc. Present the topic in a bit more detail with this Monitor And Assess Vendor Risk Management Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Information Security And Privacy, Physical Assets And Data Security, Web Application Security This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Organize Cyber Security Training For Employees Implementing Strategies To Mitigate Cyber Security Threats
Organize Cyber Security Training For Employees Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts the staff cyber security training plan to educate them regarding technology threats and practices. It mainly includes elements such as topics to be covered, target audience, trainer name, mode, proposed date, timings etc. Deliver an outstanding presentation on the topic using this Organize Cyber Security Training For Employees Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Document Management, Target Audience, Proposed Date using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
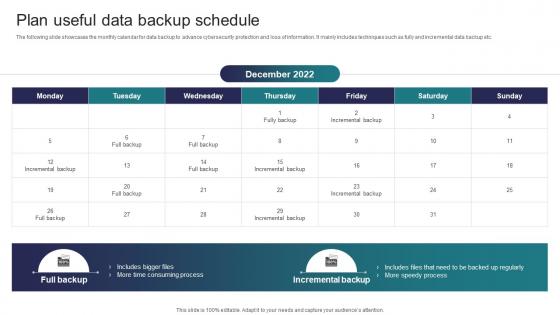 Plan Useful Data Backup Schedule Implementing Strategies To Mitigate Cyber Security Threats
Plan Useful Data Backup Schedule Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases the monthly calendar for data backup to advance cybersecurity protection and loss of information. It mainly includes techniques such as fully and incremental data backup etc. Increase audience engagement and knowledge by dispensing information using Plan Useful Data Backup Schedule Implementing Strategies To Mitigate Cyber Security Threats This template helps you present information on one stages. You can also present information on Time Consuming Process, Speedy Process, Incremental Backup using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Run Penetration Testing To Review Risk Implementing Strategies To Mitigate Cyber Security Threats
Run Penetration Testing To Review Risk Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases various methods to review cyber risks to determine probability and impact of risks. It includes elements such as penetration, red team and risk based testing along with objectives, features, cost, outcomes, duration etc. Present the topic in a bit more detail with this Run Penetration Testing To Review Risk Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Objectives, Features, Duration This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Select Cybersecurity Training Program Courses Implementing Strategies To Mitigate Cyber Security Threats
Select Cybersecurity Training Program Courses Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases the best cybersecurity training courses to educate employees and minimize the possibility of cyber attacks. It includes cloud, disaster recovery, hardware, information security programs, duration, mode and cost Deliver an outstanding presentation on the topic using this Select Cybersecurity Training Program Courses Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Cloud Security, Information Security, Disaster Recovery using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Select Tools To Reduce Cyber Security Failure Implementing Strategies To Mitigate Cyber Security Threats
Select Tools To Reduce Cyber Security Failure Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide highlights some best tools to track and minimize the impact of cyber risks. It includes elements such as tool anme, features, trial period, cost and reviews etc. Present the topic in a bit more detail with this Select Tools To Reduce Cyber Security Failure Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Features, Free Trial, Cost This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Table Of Contents Implementing Strategies To Mitigate Cyber Security Threats
Table Of Contents Implementing Strategies To Mitigate Cyber Security ThreatsIncrease audience engagement and knowledge by dispensing information using Table Of Contents Implementing Strategies To Mitigate Cyber Security Threats This template helps you present information on one stages. You can also present information on Industry Overview, Current Scenario Analysis, Cyber Security Plan using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
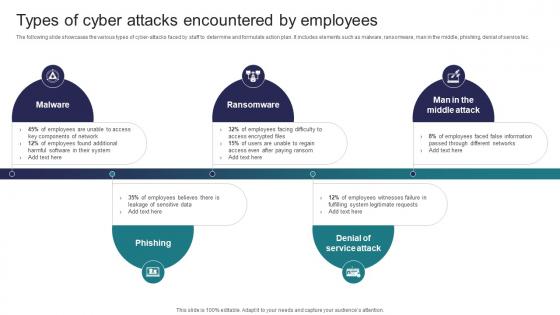 Types Of Cyber Attacks Encountered By Employees Implementing Strategies To Mitigate Cyber Security Threats
Types Of Cyber Attacks Encountered By Employees Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases the various types of cyber attacks faced by staff to determine and formulate action plan. It includes elements such as malware, ransomware, man in the middle, phishing, denial of service tec. Introducing Types Of Cyber Attacks Encountered By Employees Implementing Strategies To Mitigate Cyber Security Threats to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Malware, Ransomware, Phishing using this template. Grab it now to reap its full benefits.
-
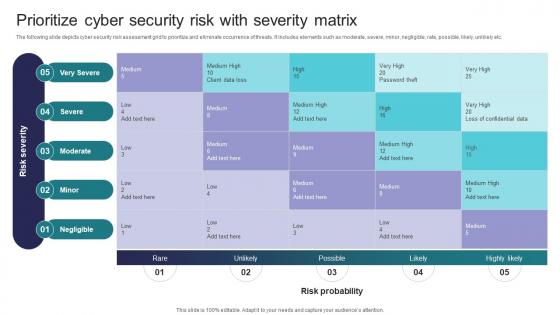 Implementing Strategies To Mitigate Cyber Security Threats Prioritize Cyber Security Risk With Severity Matrix
Implementing Strategies To Mitigate Cyber Security Threats Prioritize Cyber Security Risk With Severity MatrixThe following slide depicts cyber security risk assessment grid to prioritize and eliminate occurrence of threats. It includes elements such as moderate, severe, minor, negligible, rate, possible, likely, unlikely etc. Introducing Implementing Strategies To Mitigate Cyber Security Threats Prioritize Cyber Security Risk With Severity Matrix to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Very Severe, Severe, Moderate using this template. Grab it now to reap its full benefits.
-
 Analyze And Rank Impact Of Cyber Threat Cyber Risk Assessment
Analyze And Rank Impact Of Cyber Threat Cyber Risk AssessmentThe following slide highlights the prioritization of cyber security threats to minimize possibility of likelihood and severity. It mainly includes elements such as vulnerability, threat, source, likelihood, impact and ranking etc. Present the topic in a bit more detail with this Analyze And Rank Impact Of Cyber Threat Cyber Risk Assessment Use it as a tool for discussion and navigation on Framework, Appropriate Structure, Internet Access This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Determine Cyber Security Risks And Threats Cyber Risk Assessment
Determine Cyber Security Risks And Threats Cyber Risk AssessmentThe following slide highlights cyber security risks and threats identified within the company to analyze and protect from potential loss. It includes elements such as objectives, issue identifier, malware, phishing, ransomware, weak credentials, data breach etc. Increase audience engagement and knowledge by dispensing information using Determine Cyber Security Risks And Threats Cyber Risk Assessment This template helps you present information on three stages. You can also present information on Malware, Phishing, Ransomware, Weak Credentials using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
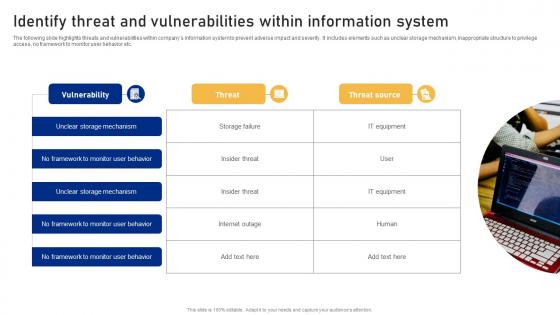 Identify Threat And Vulnerabilities Within Information System Cyber Risk Assessment
Identify Threat And Vulnerabilities Within Information System Cyber Risk AssessmentThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Introducing Identify Threat And Vulnerabilities Within Information System Cyber Risk Assessment to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on No Framework, Monitor User Behavior, Vulnerability using this template. Grab it now to reap its full benefits.
-
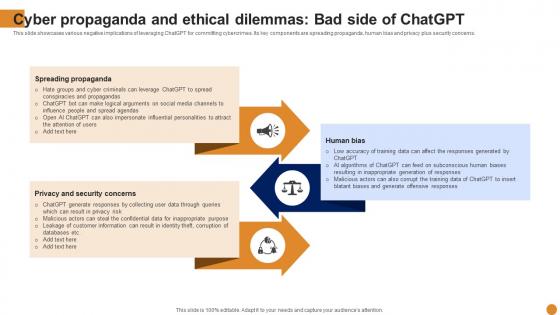 Cyber Propaganda And Ethical Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Cyber Propaganda And Ethical Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various negative implications of leveraging ChatGPT for committing cybercrimes. Its key components are spreading propaganda, human bias and privacy plus security concerns. Introducing Cyber Propaganda And Ethical Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Spreading Propaganda, Privacy And Security Concerns, Propaganda, using this template. Grab it now to reap its full benefits.
-
 Types Of Cyber Attacks Faced By Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Types Of Cyber Attacks Faced By Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various types of cyber attacks that significantly damage the organization resources and reputation. Different types of attacks faced are Malware, Phishing, Man in middle attack, SQL injection etc. Increase audience engagement and knowledge by dispensing information using Types Of Cyber Attacks Faced By Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. This template helps you present information on five stages. You can also present information on Phishing, SQL Injection, Organization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Impact Of Cyber Security Threats On Organisational Policy
Impact Of Cyber Security Threats On Organisational PolicyThis slide covers the negative impacts of prevalent cybersecurity threats. This template aims to highlight two key negative impacts of threats, including DNS Attacks, SQL Injection, Malware, Phishing, and Ransomware. Presenting our set of slides with Impact Of Cyber Security Threats On Organisational Policy This exhibits information on Six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Malware, DNS Attack, SQL Injection
-
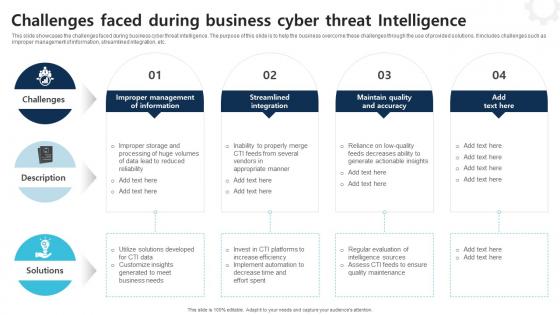 Challenges Faced During Business Cyber Threat Intelligence
Challenges Faced During Business Cyber Threat IntelligenceThis slide showcases the challenges faced during business cyber threat intelligence. The purpose of this slide is to help the business overcome these challenges through the use of provided solutions. It includes challenges such as improper management of information, streamlined integration, etc. Introducing our premium set of slides with Challenges Faced During Business Cyber Threat Intelligence Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Description, Challenges, Solutions So download instantly and tailor it with your information.
-
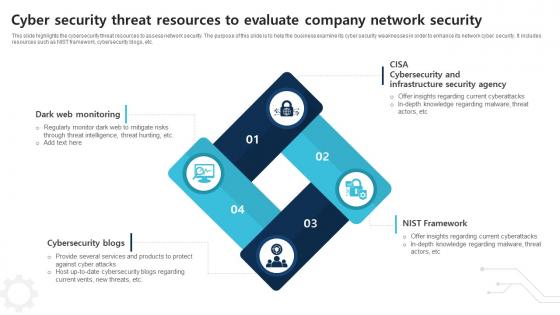 Cyber Security Threat Resources To Evaluate Company Network Security
Cyber Security Threat Resources To Evaluate Company Network SecurityThis slide highlights the cybersecurity threat resources to assess network security. The purpose of this slide is to help the business examine its cyber security weaknesses in order to enhance its network cyber security. It includes resources such as NIST framework, cybersecurity blogs, etc. Introducing our premium set of slides with Cyber Security Threat Resources To Evaluate Company Network Security Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Dark Web Monitoring, Cybersecurity Blogs, Nist Framework So download instantly and tailor it with your information.
-
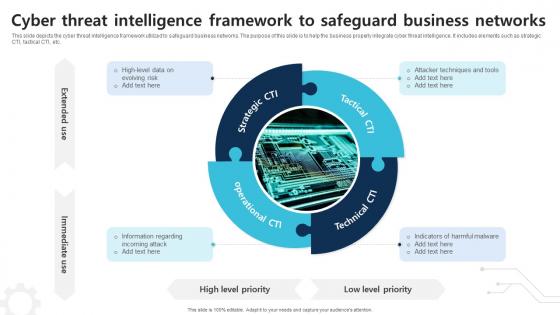 Cyber Threat Intelligence Framework To Safeguard Business Networks
Cyber Threat Intelligence Framework To Safeguard Business NetworksThis slide depicts the cyber threat intelligence framework utilized to safeguard business networks. The purpose of this slide is to help the business properly integrate cyber threat intelligence. It includes elements such as strategic CTI, tactical CTI, etc. Presenting our set of slides with Cyber Threat Intelligence Framework To Safeguard Business Networks This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Operational CTI, Strategic CTI
-
 Cyber Threat Intelligence Icon To Detect Digital Attacks
Cyber Threat Intelligence Icon To Detect Digital AttacksIntroducing our premium set of slides with Cyber Threat Intelligence Icon To Detect Digital Attacks Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Threat Intelligence Icon, Detect Digital Attacks So download instantly and tailor it with your information.
-
 Cyber Threat Intelligence Icon To Enhance Cybersecurity
Cyber Threat Intelligence Icon To Enhance CybersecurityPresenting our set of slides with Cyber Threat Intelligence Icon To Enhance Cybersecurity This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Threat Intelligence Icon, Enhance Cybersecurity
-
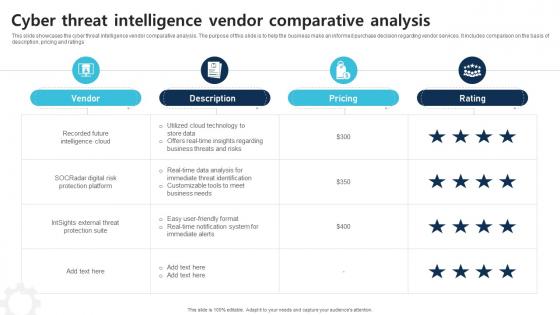 Cyber Threat Intelligence Vendor Comparative Analysis
Cyber Threat Intelligence Vendor Comparative AnalysisThis slide showcases the cyber threat intelligence vendor comparative analysis. The purpose of this slide is to help the business make an informed purchase decision regarding vendor services. It includes comparison on the basis of description, pricing and ratings Introducing our Cyber Threat Intelligence Vendor Comparative Analysis set of slides. The topics discussed in these slides are Vendor, Description, Pricing This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
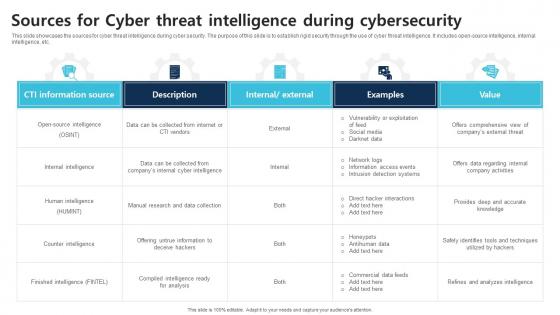 Sources For Cyber Threat Intelligence During Cybersecurity
Sources For Cyber Threat Intelligence During CybersecurityThis slide showcases the sources for cyber threat intelligence during cyber security. The purpose of this slide is to establish rigid security through the use of cyber threat intelligence. It includes open source intelligence, internal intelligence, etc. Presenting our well structured Sources For Cyber Threat Intelligence During Cybersecurity The topics discussed in this slide are CTI Information Source, Description, Examples This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Steps For Cyber Threat Intelligence Lifecycles
Steps For Cyber Threat Intelligence LifecyclesThis slide depicts the steps for cyber threat intelligence lifecycles. The purpose of this slide is to help the business successfully implement cyber threat intelligence practices. It includes steps such as requirements, collection, processing, etc. Introducing our premium set of slides with Steps For Cyber Threat Intelligence Lifecycles Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Requirements, Collection, Processing So download instantly and tailor it with your information.
-
 Types Of Cyber Threat Intelligence To Safeguard Business
Types Of Cyber Threat Intelligence To Safeguard BusinessThis slide depicts the steps for cyber threat intelligence lifecycles. The purpose of this slide is to help the business successfully implement cyber threat intelligence practices. It includes steps such as requirements, collection, processing, etc. Presenting our set of slides with Types Of Cyber Threat Intelligence To Safeguard Business This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Strategic Intelligence, Tactical Intelligence, Operational Intelligence
-
 Use Cases Of Cyber Threat Intelligence Framework To Establish Cybersecurity
Use Cases Of Cyber Threat Intelligence Framework To Establish CybersecurityThis slide depicts the use cases of cyber threat intelligence framework to establish cybersecurity. The purpose of this slide is to help the business appropriately utilize cyber threat intelligence framework in order to enhance its network security. It includes cyber risk management, security operations center, etc. Introducing our premium set of slides with Use Cases Of Cyber Threat Intelligence Framework To Establish Cybersecurity Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Risk Management, Vulnerability Management, Security Operations Center So download instantly and tailor it with your information.
-
 Cyber Security Online Threat Control Icon
Cyber Security Online Threat Control IconPresenting our set of slides with Cyber Security Online Threat Control Icon This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Online Threat Control Icon
-
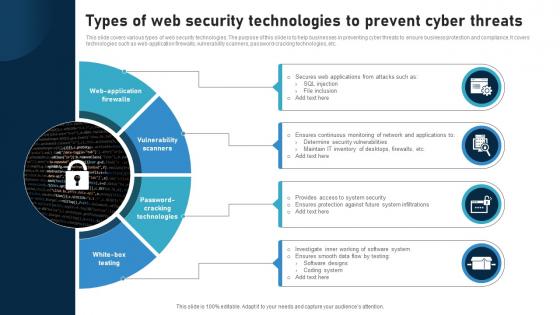 Types Of Web Security Technologies To Prevent Cyber Threats
Types Of Web Security Technologies To Prevent Cyber ThreatsThis slide covers various types of web security technologies. The purpose of this slide is to help businesses in preventing cyber threats to ensure business protection and compliance. It covers technologies such as web application firewalls, vulnerability scanners, password cracking technologies, etc. Presenting our set of slides with Types Of Web Security Technologies To Prevent Cyber Threats This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Web Application Firewalls, Vulnerability Scanners, Password Cracking Technologies
-
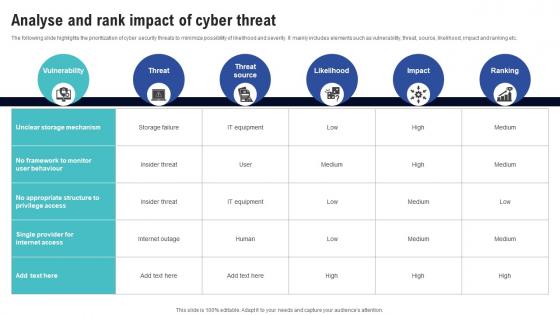 Analyse And Rank Impact Of Cyber Threat Creating Cyber Security Awareness
Analyse And Rank Impact Of Cyber Threat Creating Cyber Security AwarenessThe following slide highlights the prioritization of cyber security threats to minimize possibility of likelihood and severity. It mainly includes elements such as vulnerability, threat, source, likelihood, impact and ranking etc. Present the topic in a bit more detail with this Analyse And Rank Impact Of Cyber Threat Creating Cyber Security Awareness Use it as a tool for discussion and navigation on Likelihood, Impact, Ranking This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Determine Cyber Security Risks And Threats Creating Cyber Security Awareness
Determine Cyber Security Risks And Threats Creating Cyber Security AwarenessThe following slide highlights cyber security risks and threats identified within the company to analyze and protect from potential loss. It includes elements such as objectives, issue identifier, malware, phishing, ransomware, weak credentials, data breach etc. Present the topic in a bit more detail with this Determine Cyber Security Risks And Threats Creating Cyber Security Awareness Use it as a tool for discussion and navigation on Human Errors, Factor Authentication This template is free to edit as deemed fit for your organization. Therefore download it now.
-
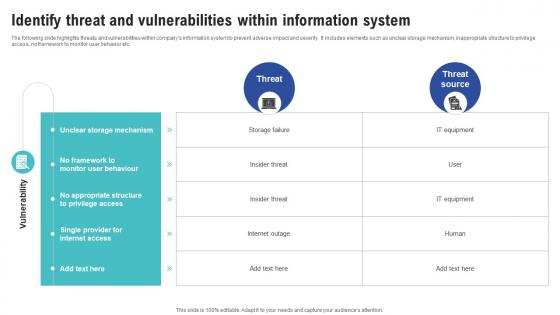 Identify Threat And Vulnerabilities Within Information System Creating Cyber Security Awareness
Identify Threat And Vulnerabilities Within Information System Creating Cyber Security AwarenessThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Deliver an outstanding presentation on the topic using this Identify Threat And Vulnerabilities Within Information System Creating Cyber Security Awareness Dispense information and present a thorough explanation of Unclear Storage Mechanism, Monitor User Behaviour, No Appropriate Structure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Icon For Threat Identification
Cyber Security Icon For Threat IdentificationIntroducing our premium set of slides with Cyber Security Icon For Threat Identification. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Security Icon, Threat Identification. So download instantly and tailor it with your information.
-
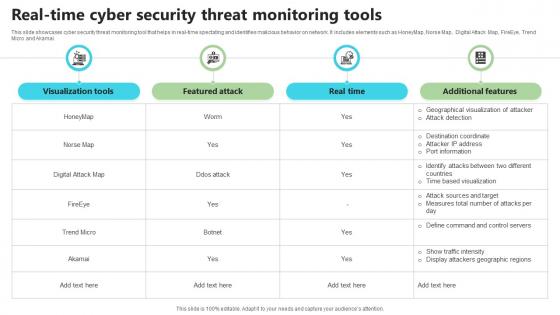 Real Time Cyber Security Threat Monitoring Tools
Real Time Cyber Security Threat Monitoring ToolsThis slide showcases cyber security threat monitoring tool that helps in real-time spectating and identifies malicious behavior on network. It includes elements such as HoneyMap, Norse Map, Digital Attack Map, FireEye, Trend Micro and Akamai. Presenting our well structured Real Time Cyber Security Threat Monitoring Tools. The topics discussed in this slide are Visualization Tools, Real Time, Additional Features. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Icon For Cyber Protection With Threat Analytics
Icon For Cyber Protection With Threat AnalyticsIntroducing our premium set of slides with Icon For Cyber Protection With Threat Analytics. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Security, Threat Analytics, Icon. So download instantly and tailor it with your information.
-
 Agenda For Cyber Threats In Blockchain World Best Practices BCT SS V
Agenda For Cyber Threats In Blockchain World Best Practices BCT SS VIntroducing Agenda For Cyber Threats In Blockchain World Best Practices BCT SS V to increase your presentation threshold. Encompassed with Six stages, this template is a great option to educate and entice your audience. Dispence information on Agenda using this template. Grab it now to reap its full benefits.
-
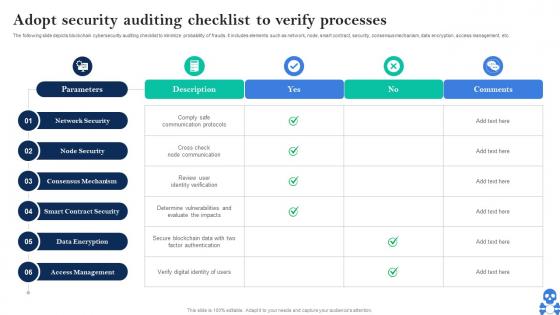 Cyber Threats In Blockchain Adopt Security Auditing Checklist To Verify Processes BCT SS V
Cyber Threats In Blockchain Adopt Security Auditing Checklist To Verify Processes BCT SS VThe following slide depicts blockchain cybersecurity auditing checklist to minimize probability of frauds. It includes elements such as network, node, smart contract, security, consensus mechanism, data encryption, access management, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Adopt Security Auditing Checklist To Verify Processes BCT SS V Dispense information and present a thorough explanation of Consensus Mechanism, Smart Contract Security, Data Encryption using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
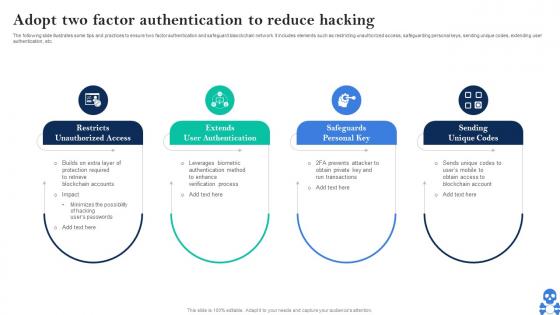 Cyber Threats In Blockchain Adopt Two Factor Authentication To Reduce Hacking BCT SS V
Cyber Threats In Blockchain Adopt Two Factor Authentication To Reduce Hacking BCT SS VThe following slide illustrates some tips and practices to ensure two factor authentication and safeguard blaockchain network. It includes elements such as restricting unauthorized access, safeguarding personal keys, sending unique codes, extending user authentication, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Adopt Two Factor Authentication To Reduce Hacking BCT SS V This template helps you present information on Four stages. You can also present information on Restricts, Unauthorized Access, Extends User Authentication, Safeguards Personal Key using this PPT design. This layout is completely editable so personaize it now
-
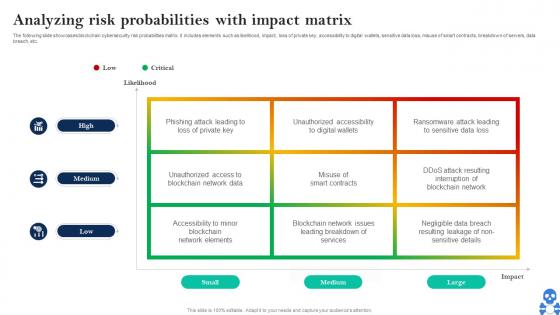 Cyber Threats In Blockchain Analyzing Risk Probabilities With Impact Matrix BCT SS V
Cyber Threats In Blockchain Analyzing Risk Probabilities With Impact Matrix BCT SS VThe following slide showcases blockchain cybersecurity risk probabilities matrix. it includes elements such as likelihood, impact, loss of private key, accessibility to digital wallets, sensitive data loss, misuse of smart contracts, breakdown of servers, data breach, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Analyzing Risk Probabilities With Impact Matrix BCT SS V Dispense information and present a thorough explanation of Private Key, Digital Wallets, Smart Contracts using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Threats In Blockchain Backing Up Data To Enhance Security And Efficiency BCT SS V
Cyber Threats In Blockchain Backing Up Data To Enhance Security And Efficiency BCT SS VThe following slide illustrates some methods to regularly backing up data to prevent primary data failures. It includes elements such as regularly backing up, offsite, automated backup and constantly monitoring, etc. Introducing Cyber Threats In Blockchain Backing Up Data To Enhance Security And Efficiency BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Regularly Backup, Automated Backup, Track Backup using this template. Grab it now to reap its full benefits.
-
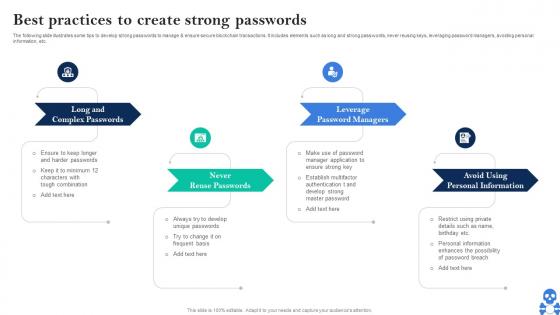 Cyber Threats In Blockchain Best Practices To Create Strong Passwords BCT SS V
Cyber Threats In Blockchain Best Practices To Create Strong Passwords BCT SS VThe following slide illustrates some tips to develop strong passwords to manage and ensure secure blockchain transactions. It includes elements such as long and strong passwords, never reusing keys, leveraging password managers, avoiding personal information, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Best Practices To Create Strong Passwords BCT SS V This template helps you present information on Four stages. You can also present information on Long And Complex Passwords, Never Reuse Passwords, Leverage Password Managers using this PPT design. This layout is completely editable so personaize it now
-
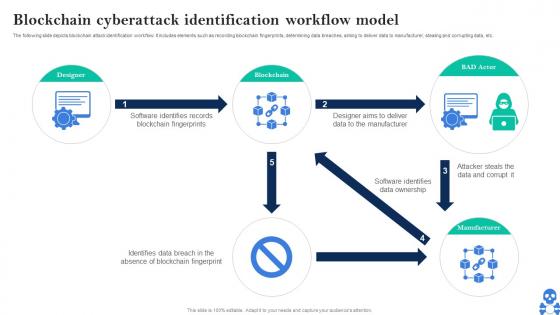 Cyber Threats In Blockchain Blockchain Cyberattack Identification Workflow Model BCT SS V
Cyber Threats In Blockchain Blockchain Cyberattack Identification Workflow Model BCT SS VThe following slide depicts blockchain attack identification workflow. It includes elements such as recording blockchain fingerprints, determining data breaches, aiming to deliver data to manufacturer, stealing and corrupting data, etc. Present the topic in a bit more detail with this Cyber Threats In Blockchain Blockchain Cyberattack Identification Workflow Model BCT SS V Use it as a tool for discussion and navigation on Designer, Blockchain, BAD Actor This template is free to edit as deemed fit for your organization. Therefore download it now.
-
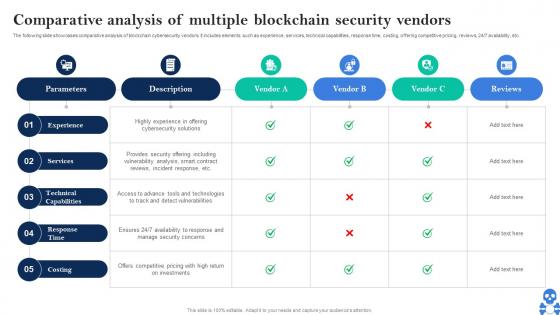 Cyber Threats In Blockchain Comparative Analysis Of Multiple Blockchain Security Vendors BCT SS V
Cyber Threats In Blockchain Comparative Analysis Of Multiple Blockchain Security Vendors BCT SS VThe following slide showcases comparative analysis of blockchain cybersecurity vendors. It includes elements such as experience, services, technical capabilities, response time, costing, offering competitive pricing, reviews, 247 availability, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Comparative Analysis Of Multiple Blockchain Security Vendors BCT SS V Dispense information and present a thorough explanation of Experience, Services, Technical Capabilities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
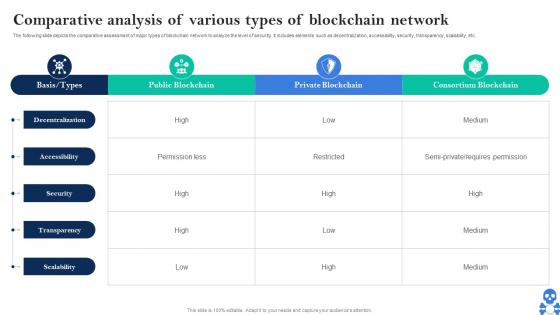 Cyber Threats In Blockchain Comparative Analysis Of Various Types Of Blockchain Network BCT SS V
Cyber Threats In Blockchain Comparative Analysis Of Various Types Of Blockchain Network BCT SS VThe following slide depicts the comparative assessment of major types of blockchain network to analyze the level of security. It includes elements such as decentralization, accessibility, security, transparency, scalability, etc. Present the topic in a bit more detail with this Cyber Threats In Blockchain Comparative Analysis Of Various Types Of Blockchain Network BCT SS V Use it as a tool for discussion and navigation on Public Blockchain, Private Blockchain, Consortium Blockchain This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Threats In Blockchain Conducting Blockchain Cybersecurity Training For Users BCT SS V
Cyber Threats In Blockchain Conducting Blockchain Cybersecurity Training For Users BCT SS VThe following slide showcases blockchain cybersecurity training plan to reduce insider threats. It includes elements such as introduction, blockchain security risks, smart contracts development, network security, data encryption, incidence response management, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Conducting Blockchain Cybersecurity Training For Users BCT SS V Dispense information and present a thorough explanation of Introduction To Blockchain, Blockchain Security Risks, Smart Contracts Development using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
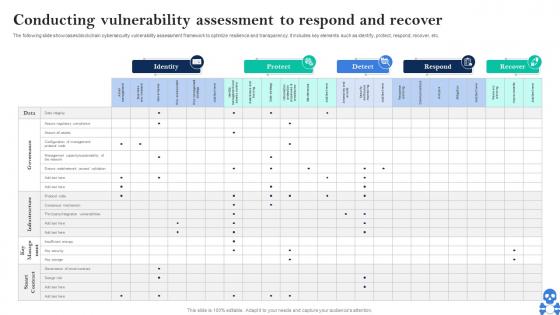 Cyber Threats In Blockchain Conducting Vulnerability Assessment To Respond And Recover BCT SS V
Cyber Threats In Blockchain Conducting Vulnerability Assessment To Respond And Recover BCT SS VThe following slide showcases blockchain cybersecurity vulnerability assessment framework to optimize resilience and transparency. It includes key elements such as identify, protect, respond, recover, etc. Present the topic in a bit more detail with this Cyber Threats In Blockchain Conducting Vulnerability Assessment To Respond And Recover BCT SS V Use it as a tool for discussion and navigation on Identity, Protect, Detect This template is free to edit as deemed fit for your organization. Therefore download it now.
-
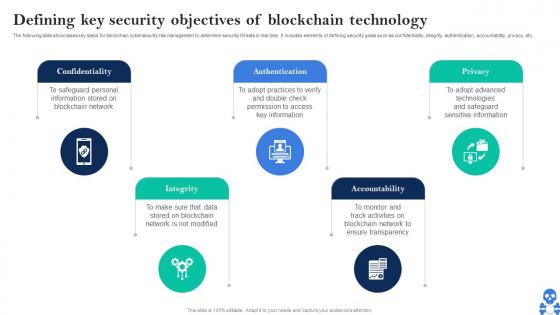 Cyber Threats In Blockchain Defining Key Security Objectives Of Blockchain Technology BCT SS V
Cyber Threats In Blockchain Defining Key Security Objectives Of Blockchain Technology BCT SS VThe following slide showcases key steps for blockchain cybersecurity risk management to determine security threats in real time. It includes elements of defining security goals such as confidentiality, integrity, authentication, accountability, privacy, etc. Introducing Cyber Threats In Blockchain Defining Key Security Objectives Of Blockchain Technology BCT SS V to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Confidentiality, Integrity, Authentication using this template. Grab it now to reap its full benefits.
-
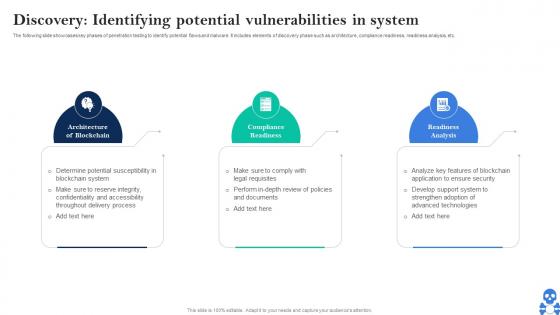 Cyber Threats In Blockchain Discovery Identifying Potential Vulnerabilities In System BCT SS V
Cyber Threats In Blockchain Discovery Identifying Potential Vulnerabilities In System BCT SS VThe following slide showcases key phases of penetration testing to identify potential flaws and malware. It includes elements of discovery phase such as architecture, compliance readiness, readiness analysis, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Discovery Identifying Potential Vulnerabilities In System BCT SS V This template helps you present information on Three stages. You can also present information on Architecture Of Blockchain, Compliance Readiness, Readiness Analysis using this PPT design. This layout is completely editable so personaize it now
-
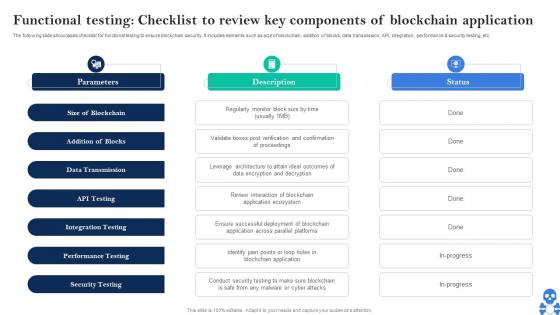 Cyber Threats In Blockchain Functional Testing Checklist To Review Key Components Of Blockchain BCT SS V
Cyber Threats In Blockchain Functional Testing Checklist To Review Key Components Of Blockchain BCT SS VThe following slide showcases checklist for functional testing to ensure blockchain security. It includes elements such as size of blockchain, addition of blocks, data transmission, API, integration, performance and security testing, etc. Introducing Cyber Threats In Blockchain Functional Testing Checklist To Review Key Components Of Blockchain BCT SS V to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Size Of Blockchain, Addition Of Blocks, Data Transmission using this template. Grab it now to reap its full benefits.
-
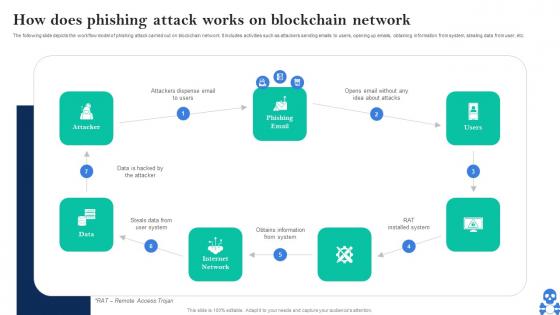 Cyber Threats In Blockchain How Does Phishing Attack Works On Blockchain Network BCT SS V
Cyber Threats In Blockchain How Does Phishing Attack Works On Blockchain Network BCT SS VThe following slide depicts the workflow model of phishing attack carried out on blockchain network. It includes activities such as attackers sending emails to users, opening up emails, obtaining information from system, stealing data from user, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain How Does Phishing Attack Works On Blockchain Network BCT SS V This template helps you present information on Seven stages. You can also present information on Steals Data From User System, Obtains Information From System using this PPT design. This layout is completely editable so personaize it now
-
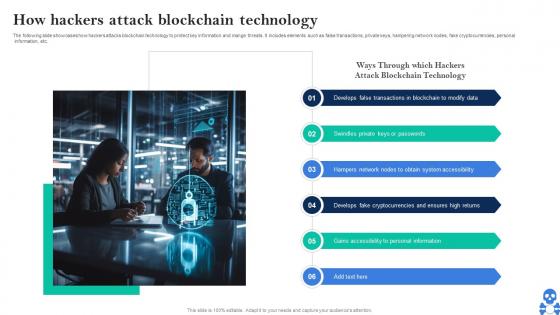 Cyber Threats In Blockchain How Hackers Attack Blockchain Technology BCT SS V
Cyber Threats In Blockchain How Hackers Attack Blockchain Technology BCT SS VThe following slide showcases how hackers attacks blockchain technology to protect key information and mange threats. It includes elements such as false transactions, private keys, hampering network nodes, fake cryptocurrencies, personal information, etc. Introducing Cyber Threats In Blockchain How Hackers Attack Blockchain Technology BCT SS V to increase your presentation threshold. Encompassed with Six stages, this template is a great option to educate and entice your audience. Dispence information on Blockchain To Modify Data, Keys Or Passwords, Obtain System Accessibility using this template. Grab it now to reap its full benefits.
-
 Cyber Threats In Blockchain Impact Of 51 Percent Attack On Bitcoin And Blockchain Transactions BCT SS V
Cyber Threats In Blockchain Impact Of 51 Percent Attack On Bitcoin And Blockchain Transactions BCT SS VThe following slide depicts the key effect of 51percent attack on bitcoin and blockchain technology to plan actions and minimize its impact. It includes element such as delayed transactions, network disruption, low miner rewards, market volatility, reputation, credibility, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Impact Of 51 Percent Attack On Bitcoin And Blockchain Transactions BCT SS V This template helps you present information on Five stages. You can also present information on Delayed Transactions, Network Disruption, Low Miner Rewards using this PPT design. This layout is completely editable so personaize it now
-
 Cyber Threats In Blockchain Impact Of Ddos Attack On Targeted Servers BCT SS V
Cyber Threats In Blockchain Impact Of Ddos Attack On Targeted Servers BCT SS VThe following slide depicts the adverse impact of denial of service DDoS attack to determine malicious attempt to hamper targeted server. It includes elements such as software crashes, node failure, network congestion, bloated ledger, etc. Introducing Cyber Threats In Blockchain Impact Of Ddos Attack On Targeted Servers BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Software Crashes, Node Failures, Network Congestion using this template. Grab it now to reap its full benefits.
-
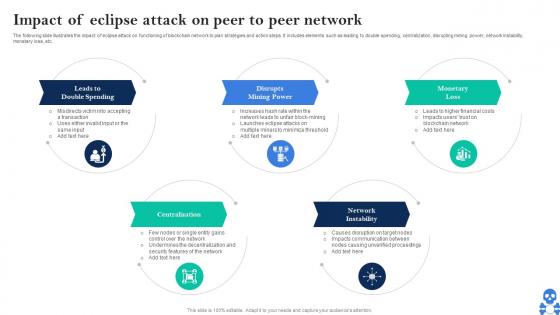 Cyber Threats In Blockchain Impact Of Eclipse Attack On Peer To Peer Network BCT SS V
Cyber Threats In Blockchain Impact Of Eclipse Attack On Peer To Peer Network BCT SS VThe following slide illustrates the impact of eclipse attack on functioning of blockchain network to plan strategies and action steps. It includes elements such as leading to double spending, centralization, disrupting mining power, network instability, monetary loss, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Impact Of Eclipse Attack On Peer To Peer Network BCT SS V This template helps you present information on Five stages. You can also present information on Leads To Double Spending, Disrupts, Mining Power using this PPT design. This layout is completely editable so personaize it now



