Powerpoint Templates and Google slides for Cybersecurity Strategy
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Backup Strategy In Cybersecurity Training Ppt
Backup Strategy In Cybersecurity Training PptPresenting Backup Strategy in Cybersecurity. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Impact Of Supplier Cybersecurity Risk Mitigation Strategy Supplier Risk Management
Impact Of Supplier Cybersecurity Risk Mitigation Strategy Supplier Risk ManagementThis slide showcase impact of supplier cybersecurity risk mitigation strategy. This template includes elements such as decrease in compliance risk cases and data breaches cases, increase in productivity level etc. Present the topic in a bit more detail with this Impact Of Supplier Cybersecurity Risk Mitigation Strategy Supplier Risk Management. Use it as a tool for discussion and navigation on Data Breaches, Service Disruption, Risk Mitigation Strategy. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IoT Password Attack Prevention Strategies Improving IoT Device Cybersecurity IoT SS
IoT Password Attack Prevention Strategies Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to highlight Internet of Things IoT password attack prevention measures. The techniques outlined in slide are limit public information, verifying the source, and no sharing of password. Deliver an outstanding presentation on the topic using this IoT Password Attack Prevention Strategies Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Information, Verify, Password using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
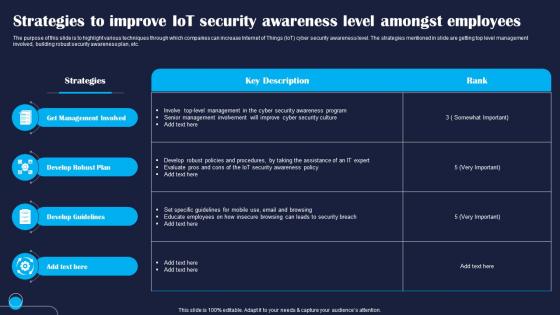 Strategies To Improve IoT Security Improving IoT Device Cybersecurity IoT SS
Strategies To Improve IoT Security Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to highlight various techniques through which companies can increase Internet of Things IoT cyber security awareness level. The strategies mentioned in slide are getting top level management involved, building robust security awareness plan, etc. Present the topic in a bit more detail with this Strategies To Improve IoT Security Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Management, Develop, Guidelines. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
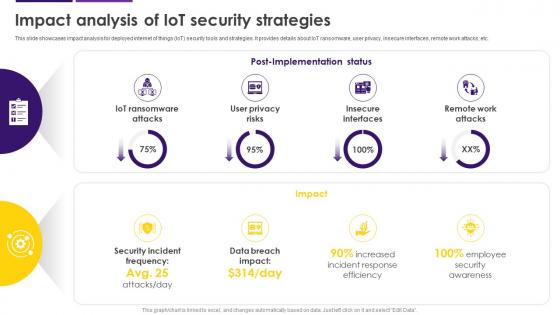 Impact Analysis Of IoT Security Strategies Internet Of Things IoT Security Cybersecurity SS
Impact Analysis Of IoT Security Strategies Internet Of Things IoT Security Cybersecurity SSThis slide showcases impact analysis for deployed internet of things IoT security tools and strategies. It provides details about IoT ransomware, user privacy, insecure interfaces, remote work attacks, etc. Present the topic in a bit more detail with this Impact Analysis Of IoT Security Strategies Internet Of Things IoT Security Cybersecurity SS. Use it as a tool for discussion and navigation on Internet Of Things, Security Tools And Strategies, IoT Ransomware, Remote Work Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Unlocking The Impact Of Technology Steps For Building Business Cybersecurity Strategy
Unlocking The Impact Of Technology Steps For Building Business Cybersecurity StrategyThis slide showcases process for creating cybersecurity strategy. This template focuses on measuring protection against cyberthreats which disrupts employee productivity. It includes information related to assessing maturity, documenting strategy, etc. Introducing Unlocking The Impact Of Technology Steps For Building Business Cybersecurity Strategy to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Understand Cybersecurity Threat, Assess Maturity, Cybersecurity Awareness, Training Initiatives, using this template. Grab it now to reap its full benefits.
-
 Cybersecurity Risks Mitigation Strategy For Compliance Risk Supplier Risk Management
Cybersecurity Risks Mitigation Strategy For Compliance Risk Supplier Risk ManagementThis slide showcases cybersecurity risks mitigation strategy for compliance risk. This template includes strategies such as perform a risk assessment, develop incident response plan, visualize the attack surface etc. Deliver an outstanding presentation on the topic using this Cybersecurity Risks Mitigation Strategy For Compliance Risk Supplier Risk Management. Dispense information and present a thorough explanation of Mitigation Strategies, Strategy Description, Risk using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
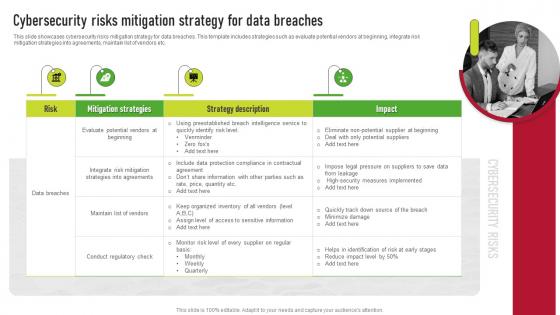 Cybersecurity Risks Mitigation Strategy For Data Breaches Supplier Risk Management
Cybersecurity Risks Mitigation Strategy For Data Breaches Supplier Risk ManagementThis slide showcases cybersecurity risks mitigation strategy for data breaches. This template includes strategies such as evaluate potential vendors at beginning, integrate risk mitigation strategies into agreements, maintain list of vendors etc. Introducing Cybersecurity Risks Mitigation Strategy For Data Breaches Supplier Risk Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Mitigation Strategies, Strategy Description, Risk, using this template. Grab it now to reap its full benefits.
-
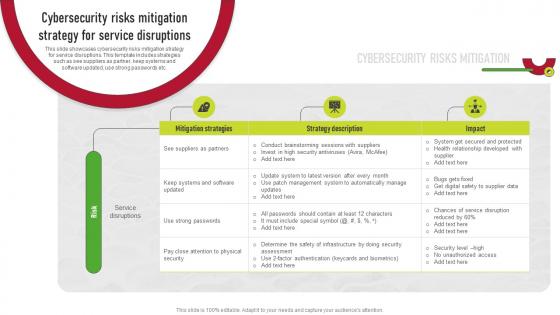 Cybersecurity Risks Mitigation Strategy For Service Disruptions Supplier Risk Management
Cybersecurity Risks Mitigation Strategy For Service Disruptions Supplier Risk ManagementThis slide showcases cybersecurity risks mitigation strategy for service disruptions. This template includes strategies such as see suppliers as partner, keep systems and software updated, use strong passwords etc. Present the topic in a bit more detail with this Cybersecurity Risks Mitigation Strategy For Service Disruptions Supplier Risk Management. Use it as a tool for discussion and navigation on Mitigation Strategies, Strategy Description, Service Disruptions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cybersecurity Strategies in Finance AI Image PowerPoint Presentation PPT ECS
Cybersecurity Strategies in Finance AI Image PowerPoint Presentation PPT ECSIntroducing a Visual PPT on Cybersecurity Strategies in Finance. Our design team have meticulously designed every PowerPoint Slide. Tailor the PPT content effortlessly. Additionally, the PPT Template is compatible with all monitor sizes and as well as Google Slides. Download the PPT, make the needed adjustments, and showcase with conviction.
-
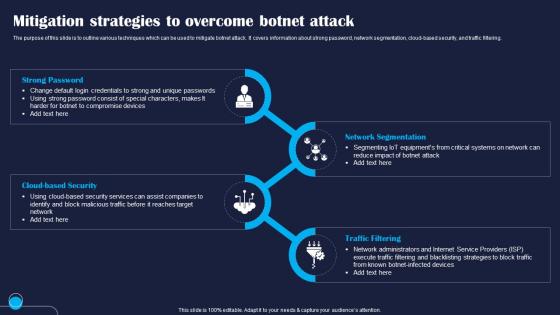 Mitigation Strategies To Overcome Improving IoT Device Cybersecurity IoT SS
Mitigation Strategies To Overcome Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to outline various techniques which can be used to mitigate botnet attack. It covers information about strong password, network segmentation, cloud based security, and traffic filtering. Increase audience engagement and knowledge by dispensing information using Mitigation Strategies To Overcome Improving IoT Device Cybersecurity IoT SS. This template helps you present information on four stages. You can also present information on Strong, Security, Network using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Mitigation Strategies To Overcome IoT Improving IoT Device Cybersecurity IoT SS
Mitigation Strategies To Overcome IoT Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase multiple techniques which can be used to overcome security breach caused by Verkada hack. The strategies mentioned in slide are regular security audit, secure authentication, firmware update, and encryption. Introducing Mitigation Strategies To Overcome IoT Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Continuous, Authentication, Encryption, using this template. Grab it now to reap its full benefits.
-
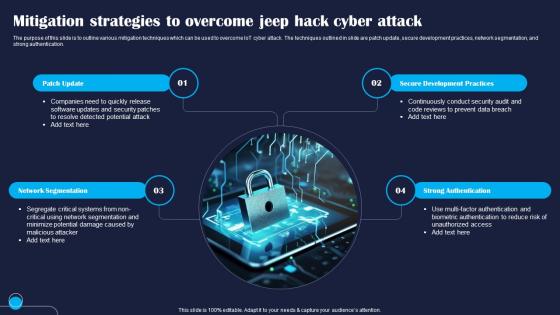 Mitigation Strategies To Overcome Jeep Hack Improving IoT Device Cybersecurity IoT SS
Mitigation Strategies To Overcome Jeep Hack Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to outline various mitigation techniques which can be used to overcome IoT cyber attack. The techniques outlined in slide are patch update, secure development practices, network segmentation, and strong authentication. Increase audience engagement and knowledge by dispensing information using Mitigation Strategies To Overcome Jeep Hack Improving IoT Device Cybersecurity IoT SS. This template helps you present information on four stages. You can also present information on Patch, Segmentation, Authentication using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Mitigation Strategies To Overcome Stuxnet Improving IoT Device Cybersecurity IoT SS
Mitigation Strategies To Overcome Stuxnet Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to highlight different mitigation techniques which can be used by companies to Internet of Things IoT security vulnerability. It covers information about strong access controls, security testing, user training, and robust security response plan. Introducing Mitigation Strategies To Overcome Stuxnet Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Strong, Security, Incident, using this template. Grab it now to reap its full benefits.
-
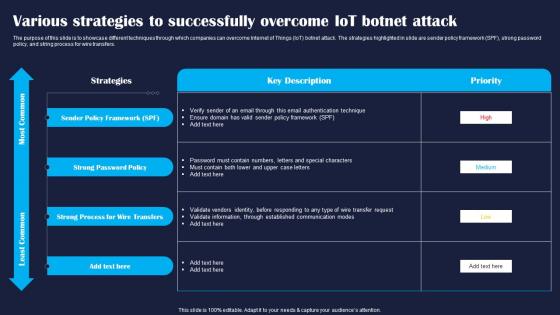 Various Strategies To Successfully Improving IoT Device Cybersecurity IoT SS
Various Strategies To Successfully Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase different techniques through which companies can overcome Internet of Things IoT botnet attack. The strategies highlighted in slide are sender policy framework SPF, strong password policy, and string process for wire transfers. Present the topic in a bit more detail with this Various Strategies To Successfully Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Policy, Strong, Process. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
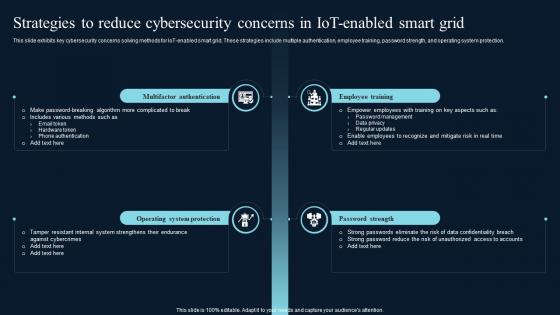 Strategies To Reduce Cybersecurity Concerns Comprehensive Guide On IoT Enabled IoT SS
Strategies To Reduce Cybersecurity Concerns Comprehensive Guide On IoT Enabled IoT SSThis slide exhibits key cybersecurity concerns solving methods for IoT enabled smart grid. These strategies include multiple authentication, employee training, password strength, and operating system protection.Introducing Strategies To Reduce Cybersecurity Concerns Comprehensive Guide On IoT Enabled IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Transmission Line Management, Safety Management, Corrective Maintenance, using this template. Grab it now to reap its full benefits.
-
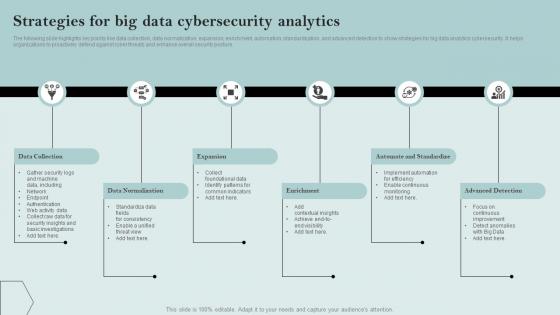 Strategies For Big Data Cybersecurity Analytics
Strategies For Big Data Cybersecurity AnalyticsThe following slide highlights key points like data collection, data normalization, expansion, enrichment, automation, standardization, and advanced detection to show strategies for big data analytics cybersecurity. It helps organizations to proactively defend against cyber threats and enhance overall security posture. Presenting our set of slides with Strategies For Big Data Cybersecurity Analytics. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Collection, Expansion, Enrichment.
-
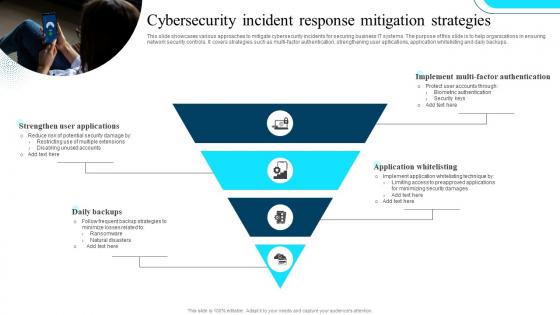 Cybersecurity Incident Response Mitigation Strategies
Cybersecurity Incident Response Mitigation StrategiesThis slide showcases various approaches to mitigate cybersecurity incidents for securing business IT systems. The purpose of this slide is to help organizations in ensuring network security controls. It covers strategies such as multi-factor authentication, strengthening user apllications, application whitelisting and daily backups. Presenting our set of slides with Cybersecurity Incident Response Mitigation Strategies This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Strengthen User Applications, Daily Backups, Application Whitelisting.
-
 Maritime Cybersecurity Strategies For Risk Management
Maritime Cybersecurity Strategies For Risk ManagementThis slide showcases strategies for maritime cybersecurity. The main purpose of this template is to analyze vulnerable assets. This includes maritime assets, risk mitigation strategy, regulatory compliance, etc. Introducing our premium set of slides with Maritime Cybersecurity Strategies For Risk Management. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Maritime Assets, Risk Mitigation Strategy, Regulatory Compliance. So download instantly and tailor it with your information.
-
 Process To Develop Cybersecurity Strategy For Data Protection
Process To Develop Cybersecurity Strategy For Data ProtectionIntroducing our premium set of slides with Process To Develop Cybersecurity Strategy For Data Protection. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Threat Landscape, Cybersecurity Maturity, Cybersecurity Program Improvement. So download instantly and tailor it with your information.
-
 Select Cybersecurity Training Program Courses Implementing Strategies To Mitigate Cyber Security Threats
Select Cybersecurity Training Program Courses Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases the best cybersecurity training courses to educate employees and minimize the possibility of cyber attacks. It includes cloud, disaster recovery, hardware, information security programs, duration, mode and cost Deliver an outstanding presentation on the topic using this Select Cybersecurity Training Program Courses Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Cloud Security, Information Security, Disaster Recovery using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Strategies To Implement Cybersecurity In Education
Strategies To Implement Cybersecurity In EducationThis slide showcases the strategies to implement cybersecurity in education. The purpose of this slide is to help the business manage and ensure cybersecurity is correctly established in an educational institute. It includes strategies such as conducting audits, immediate response to cyber attacks, etc. Introducing our premium set of slides with Strategies To Implement Cybersecurity In Education. Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Rules And Regulations, Technical Control Methods, Cyber Attacks. So download instantly and tailor it with your information.
-
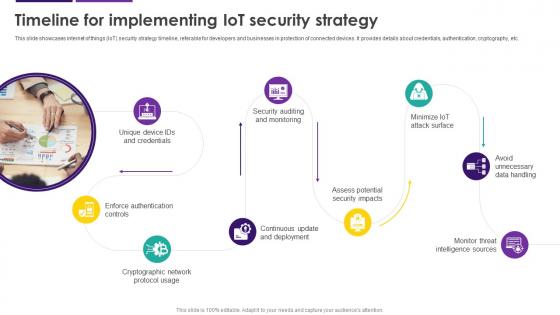 Timeline For Implementing IoT Security Strategy Internet Of Things IoT Security Cybersecurity SS
Timeline For Implementing IoT Security Strategy Internet Of Things IoT Security Cybersecurity SSThis slide showcases internet of things IoT security strategy timeline, referable for developers and businesses in protection of connected devices. It provides details about credentials, authentication, cryptography, etc. Introducing Timeline For Implementing IoT Security Strategy Internet Of Things IoT Security Cybersecurity SS to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Avoid Unnecessary Data Handling, Cryptographic Network Protocol Usage, Enforce Authentication Controls, using this template. Grab it now to reap its full benefits.
-
 Cybersecurity And Risk Management Overview Digital Transformation Strategies To Integrate DT SS
Cybersecurity And Risk Management Overview Digital Transformation Strategies To Integrate DT SSThis slide provides glimpse about summary of cybersecurity and risk management that can help businesses to handle any such incidents. It includes key considerations such as risk assessment, threat intelligence, etc. Increase audience engagement and knowledge by dispensing information using Cybersecurity And Risk Management Overview Digital Transformation Strategies To Integrate DT SS. This template helps you present information on seven stages. You can also present information on Overview, Digital Transformation, Key Considerations using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Use Case Cybersecurity And Risk Management Digital Transformation Strategies To Integrate DT SS
Use Case Cybersecurity And Risk Management Digital Transformation Strategies To Integrate DT SSThis slide provides glimpse about business case that help businesses take various cybersecurity measures and mitigate risks. It includes introduction, challenges, initiatives, etc. Introducing Use Case Cybersecurity And Risk Management Digital Transformation Strategies To Integrate DT SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Data Protection, Industry Standards, Global Technology, using this template. Grab it now to reap its full benefits.
-
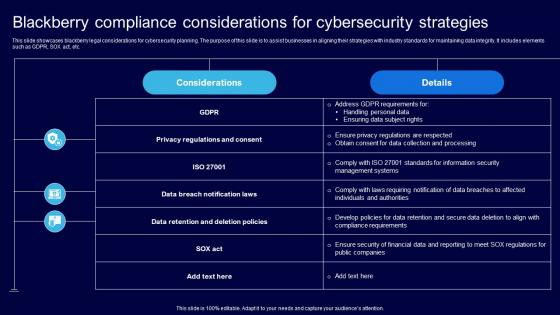 Blackberry Compliance Considerations For Cybersecurity Strategies
Blackberry Compliance Considerations For Cybersecurity StrategiesThis slide showcases blackberry legal considerations for cybersecurity planning. The purpose of this slide is to assist businesses in aligning their strategies with industry standards for maintaining data integrity. It includes elements such as GDPR, SOX act, etc. Introducing our Blackberry Compliance Considerations For Cybersecurity Strategies set of slides. The topics discussed in these slides are Considerations, Strategies, Cybersecurity. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
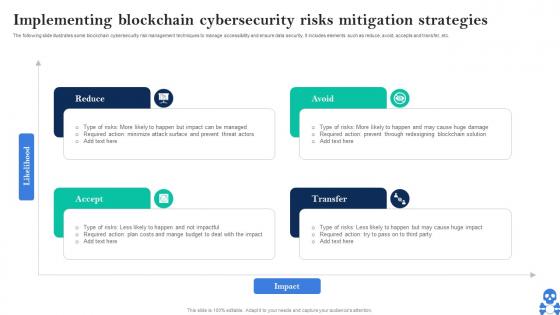
 Implementing Blockchain Cybersecurity Risks Mitigation Strategies Guide For Blockchain BCT SS V
Implementing Blockchain Cybersecurity Risks Mitigation Strategies Guide For Blockchain BCT SS VThe following slide illustrates some blockchain cybersecurity risk management techniques to manage accessibility and ensure data security. It includes elements such as reduce, avoid, accepts and transfer, etc. Increase audience engagement and knowledge by dispensing information using Implementing Blockchain Cybersecurity Risks Mitigation Strategies Guide For Blockchain BCT SS V This template helps you present information on four stages. You can also present information on Reduce, Avoid, Transfer, Accept using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
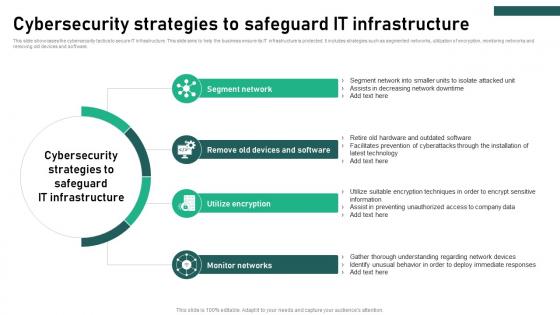 Cybersecurity Strategies To Safeguard It Infrastructure
Cybersecurity Strategies To Safeguard It InfrastructureThis slide showcases the cybersecurity tactics to secure IT infrastructure. This slide aims to help the business ensure its IT infrastructure is protected. It includes strategies such as segmented networks, utilization of encryption, monitoring networks and removing old devices and software. Introducing our premium set of slides with Cybersecurity Strategies To Safeguard It Infrastructure Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Segment Network, Utilize Encryption, Monitor Networks So download instantly and tailor it with your information.
-
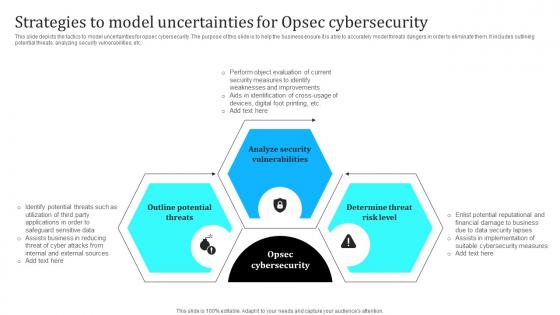 Strategies To Model Uncertainties For Opsec Cybersecurity
Strategies To Model Uncertainties For Opsec CybersecurityThis slide depicts the tactics to model uncertainties for opsec cybersecurity. The purpose of this slide is to help the business ensure it is able to accurately model threats dangers in order to eliminate them. It includes outlining potential threats, analyzing security vulnerabilities, etc. Introducing our premium set of slides with Strategies To Model Uncertainties For Opsec Cybersecurity. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Potential Threats, Analyze Security, Risk Level. So download instantly and tailor it with your information.
-
 Cyber Threats In Blockchain Implementing Blockchain Cybersecurity Risks Mitigation Strategies BCT SS V
Cyber Threats In Blockchain Implementing Blockchain Cybersecurity Risks Mitigation Strategies BCT SS VThe following slide illustrates some blockchain cybersecurity risk management techniques to manage accessibility and ensure data security. It includes elements such as reduce, avoid, accepts and transfer, etc. Introducing Cyber Threats In Blockchain Implementing Blockchain Cybersecurity Risks Mitigation Strategies BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Reduce, Avoid, Transfer, Accept using this template. Grab it now to reap its full benefits.
-
 Strategies And Recommendations For Cybersecurity Industry Global Cybersecurity Industry Outlook
Strategies And Recommendations For Cybersecurity Industry Global Cybersecurity Industry OutlookThe purpose of the slide is to provide valuable recommendations and effective strategies for cybersecurity industry players to succeed in a dynamic and competitive market. It covers strategies such as. Increase audience engagement and knowledge by dispensing information using Strategies And Recommendations For Cybersecurity Industry Global Cybersecurity Industry Outlook. This template helps you present information on five stages. You can also present information on Innovation And Research, Tailored Solutions, Education And Awareness using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Key Strategies For Cybersecurity Risk Management
Key Strategies For Cybersecurity Risk ManagementFollowing slide highlights various risk management strategies to boost cyber security and sensitive data protection. It further covers capability assessments, program design, strategy, risk management, compliance, etc. Introducing our premium set of slides with Key Strategies For Cybersecurity Risk Management. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Third Party Risk Management, Capability Assessments, Risk Management. So download instantly and tailor it with your information.
-
 Implementation Latest Technologies Strategy 3 Establish Cybersecurity In The Banking
Implementation Latest Technologies Strategy 3 Establish Cybersecurity In The BankingThe slide explains the establish cybersecurity strategy of the company. It provides key points such as what to do in the strategy, major reason behind the strategy and key steps required for the strategy. Introducing Implementation Latest Technologies Strategy 3 Establish Cybersecurity In The Banking to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Driven Protection, Technology, Measures, Customers, Research And Development, using this template. Grab it now to reap its full benefits.
-
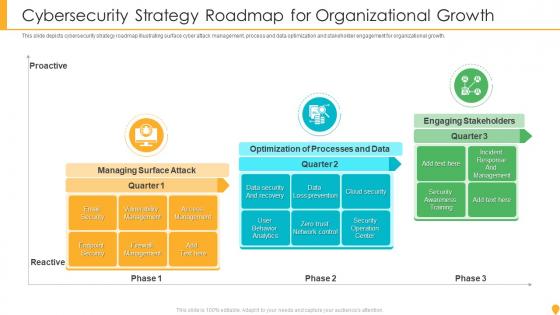 Cybersecurity Strategy Roadmap For Organizational Growth
Cybersecurity Strategy Roadmap For Organizational GrowthThis slide depicts cybersecurity strategy roadmap illustrating surface cyber attack management, process and data optimization and stakeholder engagement for organizational growth. Presenting our set of slides with name Cybersecurity Strategy Roadmap For Organizational Growth. This exhibits information on three stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Managing Surface Attack, Optimization Processes Data, Engaging Stakeholders.
-
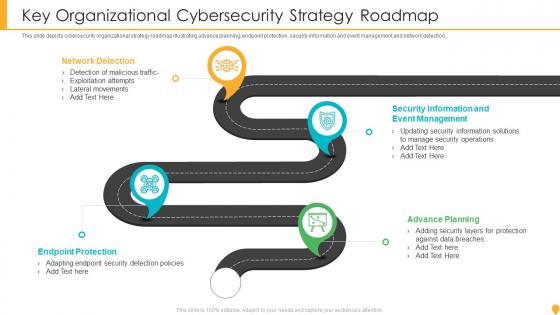 Key Organizational Cybersecurity Strategy Roadmap
Key Organizational Cybersecurity Strategy RoadmapThis slide depicts cybersecurity organizational strategy roadmap illustrating advance planning, endpoint protection, security information and event management and network detection. Presenting our set of slides with name Key Organizational Cybersecurity Strategy Roadmap. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Network Detection, Endpoint Protection, Advance Planning, Security Information.
-
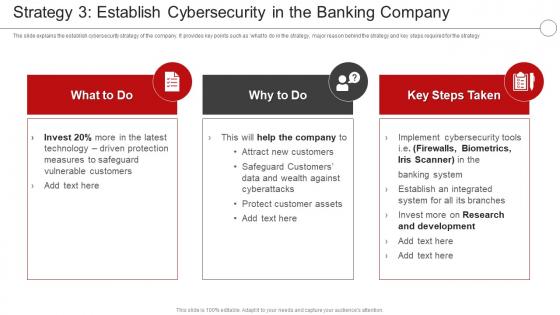 Strategy 3 Establish Cybersecurity Digital Transformation In A Banking Financial Services Company
Strategy 3 Establish Cybersecurity Digital Transformation In A Banking Financial Services CompanyThe slide explains the establish cybersecurity strategy of the company. It provides key points such as what to do in the strategy, major reason behind the strategy and key steps required for the strategy Present the topic in a bit more detail with this Strategy 3 Establish Cybersecurity Digital Transformation In A Banking Financial Services Company. Use it as a tool for discussion and navigation on Strategy, Cybersecurity, Development. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
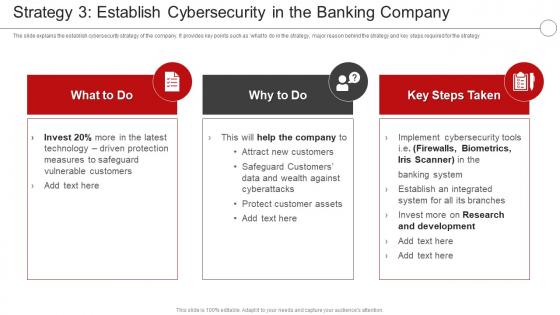 Digital Transformation In A Banking Financial Services Company Strategy 3 Establish Cybersecurity
Digital Transformation In A Banking Financial Services Company Strategy 3 Establish CybersecurityThe slide explains the establish cybersecurity strategy of the company. It provides key points such as what to do in the strategy, major reason behind the strategy and key steps required for the strategy Present the topic in a bit more detail with this Digital Transformation In A Banking Financial Services Company Strategy 3 Establish Cybersecurity. Use it as a tool for discussion and navigation on Strategy, Cybersecurity, Development. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
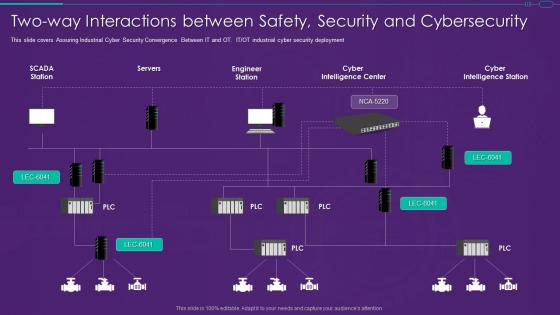 It Ot Convergence Strategy Two Way Interactions Between Safety Security And Cybersecurity
It Ot Convergence Strategy Two Way Interactions Between Safety Security And CybersecurityThis slide covers Assuring Industrial Cyber Security Convergence Between IT and OT. IT or OT industrial cyber security deployment Present the topic in a bit more detail with this It Ot Convergence Strategy Two Way Interactions Between Safety Security And Cybersecurity. Use it as a tool for discussion and navigation on Interactions, Security, Cybersecurity This template is free to edit as deemed fit for your organization. Therefore download it now.
-
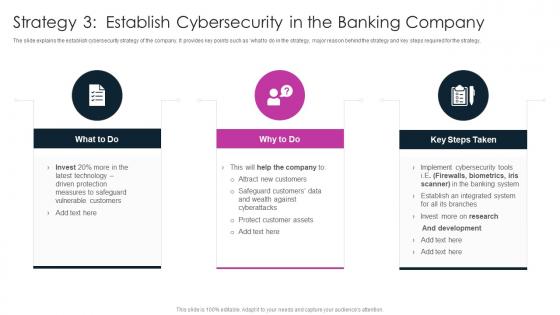 Strategy 3 Establish Cybersecurity In The Banking Digitalization In Retail Banking Company
Strategy 3 Establish Cybersecurity In The Banking Digitalization In Retail Banking CompanyThe slide explains the establish cybersecurity strategy of the company. It provides key points such as what to do in the strategy, major reason behind the strategy and key steps required for the strategy.Increase audience engagement and knowledge by dispensing information using Strategy 3 Establish Cybersecurity In The Banking Digitalization In Retail Banking Company This template helps you present information on three stages. You can also present information on Safeguard Customers, Protect Customer Assets, Establish An Integrated using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 It Professional Upskilling For Cybersecurity It Strategy For Digitalization In Business
It Professional Upskilling For Cybersecurity It Strategy For Digitalization In BusinessThis slide displays the upskilling for cybersecurity which covers chief information security officer, cloud security architect, etc. Present the topic in a bit more detail with this It Professional Upskilling For Cybersecurity It Strategy For Digitalization In Business. Use it as a tool for discussion and navigation on Information, Management, Architect. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cost estimation for strategy minimize cybersecurity threats in healthcare company
Cost estimation for strategy minimize cybersecurity threats in healthcare companyThe slide shows the estimation of major cost involved in the next four years 2021 to 2025 for implementing the strategies. The strategies are implementing Data Encryption, Increase Employee Awareness, Restricting Access to Physical Devices etc. Present the topic in a bit more detail with this Cost Estimation For Strategy Minimize Cybersecurity Threats In Healthcare Company. Use it as a tool for discussion and navigation on Data Encryption, Market Research, Software Installation, Employee Awareness. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
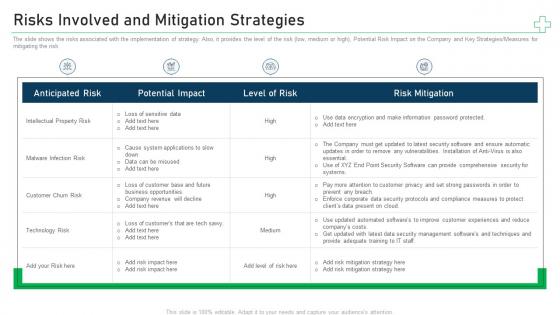 Risks involved and mitigation strategies minimize cybersecurity threats in healthcare company
Risks involved and mitigation strategies minimize cybersecurity threats in healthcare companyThe slide shows the risks associated with the implementation of strategy. Also, it provides the level of the risk low, medium or high, Potential Risk Impact on the Company and Key Strategies Measures for mitigating the risk. Present the topic in a bit more detail with this Risks Involved And Mitigation Strategies Minimize Cybersecurity Threats In Healthcare Company. Use it as a tool for discussion and navigation on Intellectual Property Risk, Malware Infection Risk, Customer Churn Risk. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
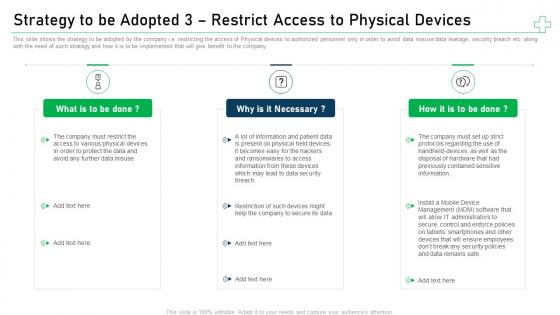 Strategy to be adopted 3 restrict access to minimize cybersecurity threats in healthcare company
Strategy to be adopted 3 restrict access to minimize cybersecurity threats in healthcare companyThis slide shows the strategy to be adopted by the company i.e. restricting the access of Physical devices to authorized personnel only in order to avoid data misuse data leakage, security breach etc. along with the need of such strategy and how it is to be implemented that will give benefit to the company. Introducing Strategy To Be Adopted 3 Restrict Access To Minimize Cybersecurity Threats In Healthcare Company to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Data Security, Hardware, Mobile Device Management, Security Policies, using this template. Grab it now to reap its full benefits.
-
 Approaches To Overcome Cybersecurity Risk Faced Effective Risk Management Strategies
Approaches To Overcome Cybersecurity Risk Faced Effective Risk Management StrategiesThe following slide exhibits various approaches which can be used to prevent cybersecurity risk faced by the real estate enterprise. The key approaches highlighted in the slide are updating the security system, installing anti-phishing add ons, using a customized web application firewall etc. Present the topic in a bit more detail with this Approaches To Overcome Cybersecurity Risk Faced Effective Risk Management Strategies. Use it as a tool for discussion and navigation on Ransomware, Phishing, Business Email Compromise. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cybersecurity Defense Strategy In Powerpoint And Google Slides Cpb
Cybersecurity Defense Strategy In Powerpoint And Google Slides CpbPresenting our Cybersecurity Defense Strategy In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Cybersecurity Defense Strategy. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
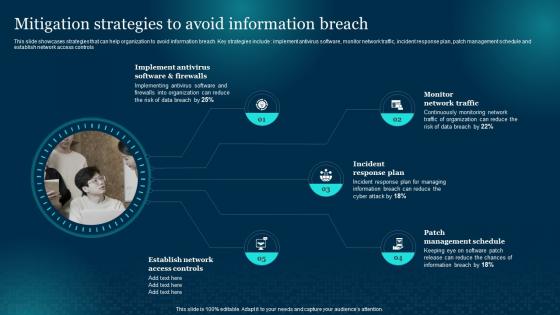 F857 Mitigation Strategies To Avoid Information Breach Cybersecurity Risk Analysis And Management Plan
F857 Mitigation Strategies To Avoid Information Breach Cybersecurity Risk Analysis And Management PlanThis slide showcases strategies that can help organization to avoid information breach. Key strategies include implement antivirus software, monitor network traffic, incident response plan, patch management schedule and establish network access controls Increase audience engagement and knowledge by dispensing information using F857 Mitigation Strategies To Avoid Information Breach Cybersecurity Risk Analysis And Management Plan. This template helps you present information on five stages. You can also present information on Mitigation, Strategies, Information Breach using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Mitigation Strategies To Tackle Information Security Cybersecurity Risk Analysis And Management Plan
Mitigation Strategies To Tackle Information Security Cybersecurity Risk Analysis And Management PlanThis slide showcases mitigation strategies that can help organization to tackle the cybersecurity attacks. It can help organization to minimize the financial loss and main reputation of business Introducing Mitigation Strategies To Tackle Information Security Cybersecurity Risk Analysis And Management Plan to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Mitigation, Strategies, Information, using this template. Grab it now to reap its full benefits.
-
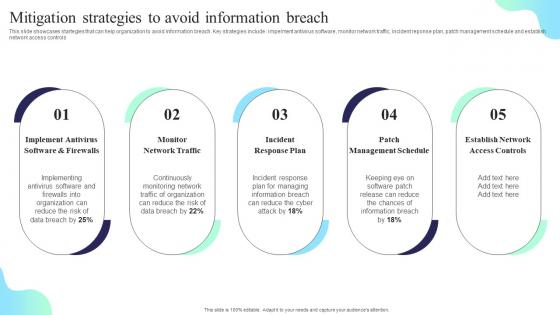 Mitigation Strategies To Avoid Information Breach Formulating Cybersecurity Plan
Mitigation Strategies To Avoid Information Breach Formulating Cybersecurity PlanThis slide showcases startegies that can help organization to avoid information breach. Key strategies include impelment antivirus software, monitor network traffic, incident reponse plan, patch management schedule and establish network access controls. Introducing Mitigation Strategies To Avoid Information Breach Formulating Cybersecurity Plan to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Implement Antivirus, Monitor Network Traffic, Incident Response Plan, using this template. Grab it now to reap its full benefits.
-
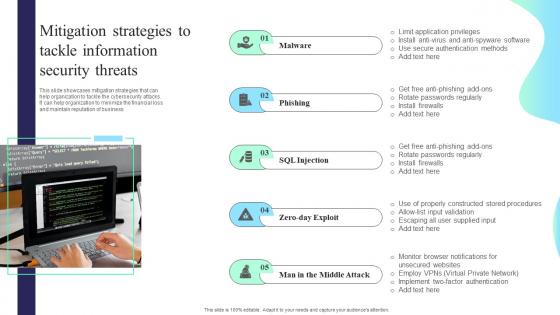 Mitigation Strategies To Tackle Information Security Threats Formulating Cybersecurity Plan
Mitigation Strategies To Tackle Information Security Threats Formulating Cybersecurity PlanThis slide showcases mitigation strategies that can help organization to tackle the cybersecurity attacks. It can help organization to minimize the financial loss and maintain reputation of business. Increase audience engagement and knowledge by dispensing information using Mitigation Strategies To Tackle Information Security Threats Formulating Cybersecurity Plan. This template helps you present information on five stages. You can also present information on Malware, Phishing, Mitigation Strategies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
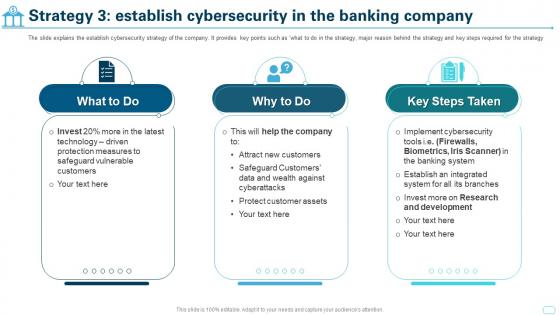 Cultural Shift Toward A Technology Strategy 3 Establish Cybersecurity In The Banking Company
Cultural Shift Toward A Technology Strategy 3 Establish Cybersecurity In The Banking CompanyThe slide explains the establish cybersecurity strategy of the company. It provides key points such as what to do in the strategy, major reason behind the strategy and key steps required for the strategy. Increase audience engagement and knowledge by dispensing information using Cultural Shift Toward A Technology Strategy 3 Establish Cybersecurity In The Banking Company. This template helps you present information on three stages. You can also present information on Safeguard Vulnerable Customers, Protect Customer Assets, Research And Development, Cybersecurity Tools using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
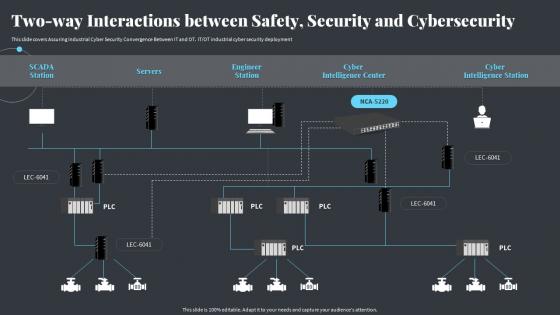 Two Way Interactions Between Safety Security And Cybersecurity Strategies Ot And It Modern Pi System
Two Way Interactions Between Safety Security And Cybersecurity Strategies Ot And It Modern Pi SystemThis slide covers Assuring Industrial Cyber Security Convergence Between IT and OT. IT or OT industrial cyber security deployment Deliver an outstanding presentation on the topic using this Two Way Interactions Between Safety Security And Cybersecurity Strategies Ot And It Modern Pi System. Dispense information and present a thorough explanation of Cybersecurity, Interactions, Intelligence Station using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
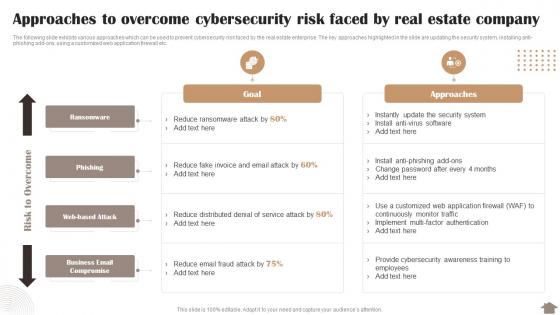 Risk Reduction Strategies Stakeholders Approaches To Overcome Cybersecurity Risk Faced By Real Estate Company
Risk Reduction Strategies Stakeholders Approaches To Overcome Cybersecurity Risk Faced By Real Estate CompanyThe following slide exhibits various approaches which can be used to prevent cybersecurity risk faced by the real estate enterprise. The key approaches highlighted in the slide are updating the security system, installing anti-phishing add-ons, using a customized web application firewall etc. Deliver an outstanding presentation on the topic using this Risk Reduction Strategies Stakeholders Approaches To Overcome Cybersecurity Risk Faced By Real Estate Company. Dispense information and present a thorough explanation of Approaches, Cybersecurity, Ransomware using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
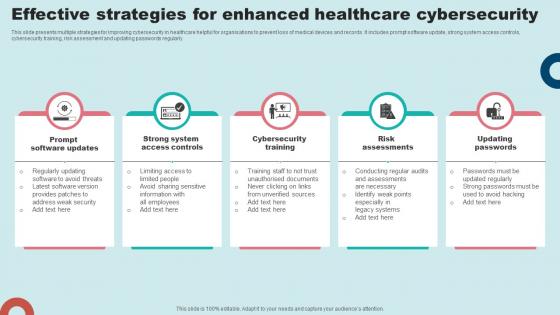 Effective Strategies For Enhanced Healthcare Cybersecurity
Effective Strategies For Enhanced Healthcare CybersecurityThis slide presents multiple strategies for improving cybersecurity in healthcare helpful for organisations to prevent loss of medical devices and records. It includes prompt software update, strong system access controls, cybersecurity training, risk assessment and updating passwords regularly. Presenting our set of slides with Effective Strategies For Enhanced Healthcare Cybersecurity This exhibits information on fivestages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Prompt Software Updates, Cybersecurity Training, Risk Assessments.
-
 Marketing Initiatives For Tech Segments Cybersecurity Develop Business Aligned IT Strategy
Marketing Initiatives For Tech Segments Cybersecurity Develop Business Aligned IT StrategyThis slide provides information regarding marketing initiatives for a technology firm across the cybersecurity segment. The slide includes goal and marketing initiatives such as prepare brand identity, etc. Increase audience engagement and knowledge by dispensing information using Marketing Initiatives For Tech Segments Cybersecurity Develop Business Aligned IT Strategy. This template helps you present information on three stages. You can also present information on Marketing Initiatives, Prepare Brand Identity, Formulate Thought Leadership using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
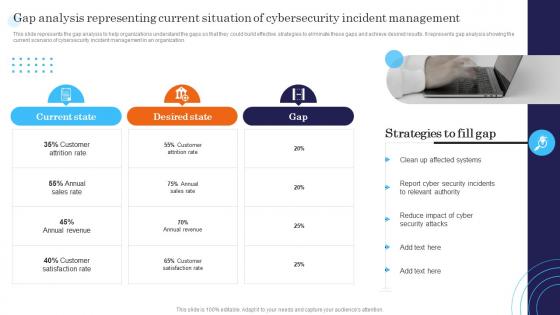 Incident Response Strategies Deployment Gap Analysis Representing Current Situation Of Cybersecurity
Incident Response Strategies Deployment Gap Analysis Representing Current Situation Of CybersecurityThis slide represents the gap analysis to help organizations understand the gaps so that they could build effective strategies to eliminate these gaps and achieve desired results. It represents gap analysis showing the current scenario of cybersecurity incident management in an organization. Introducing Incident Response Strategies Deployment Gap Analysis Representing Current Situation Of Cybersecurity to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Current, Desired, Gap, using this template. Grab it now to reap its full benefits.
-
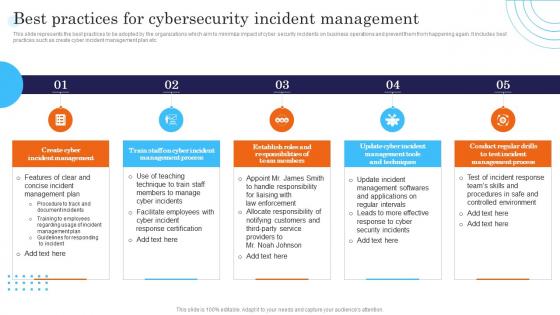 Best Practices For Cybersecurity Incident Management Incident Response Strategies Deployment
Best Practices For Cybersecurity Incident Management Incident Response Strategies DeploymentThis slide represents the best practices to be adopted by the organizations which aim to minimize impact of cyber security incidents on business operations and prevent them from happening again. It includes best practices such as create cyber incident management plan etc. Increase audience engagement and knowledge by dispensing information using Best Practices For Cybersecurity Incident Management Incident Response Strategies Deployment. This template helps you present information on five stages. You can also present information on Cybersecurity, Incident, Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Five Phases Of Cybersecurity Incident Management Incident Response Strategies Deployment
Five Phases Of Cybersecurity Incident Management Incident Response Strategies DeploymentThis slide represents the stages of the process which aims towards minimizing the impact of cyber security incidents on operational functions. It includes cyber security incident management stages such as plan and prepare, detect and report etc. Increase audience engagement and knowledge by dispensing information using Five Phases Of Cybersecurity Incident Management Incident Response Strategies Deployment. This template helps you present information on five stages. You can also present information on Plan, Respond, Report using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
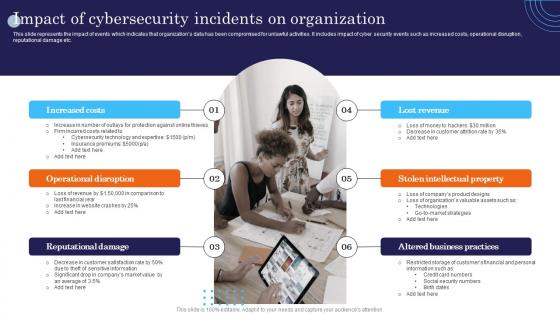 Impact Of Cybersecurity Incidents On Organization Incident Response Strategies Deployment
Impact Of Cybersecurity Incidents On Organization Incident Response Strategies DeploymentThis slide represents the impact of events which indicates that organizations data has been compromised for unlawful activities. It includes impact of cyber security events such as increased costs, operational disruption, reputational damage etc. Increase audience engagement and knowledge by dispensing information using Impact Of Cybersecurity Incidents On Organization Incident Response Strategies Deployment. This template helps you present information on six stages. You can also present information on Operational, Reputational, Revenue using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Effective Cybersecurity Risk Mitigation Strategies
Effective Cybersecurity Risk Mitigation StrategiesThe following slide illustrates key risk mitigation strategies for cybersecurity to limit impact of potential threats. This covers five strategies risk assessment, data encryption, firewalls, employee training and incident response plan.Presenting our set of slides with Effective Cybersecurity Risk Mitigation Strategies. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Conduct Risk Assessment, Encryption Software, Incident Response.
-
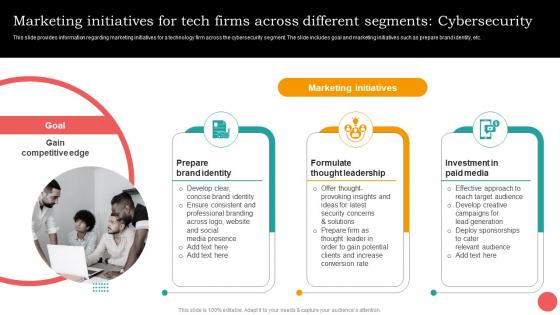 Marketing Initiatives Different Segments Cybersecurity Cios Guide For It Strategy Strategy SS V
Marketing Initiatives Different Segments Cybersecurity Cios Guide For It Strategy Strategy SS VThis slide provides information regarding marketing initiatives for a technology firm across the cybersecurity segment. The slide includes goal and marketing initiatives such as prepare brand identity, etc. Deliver an outstanding presentation on the topic using this Marketing Initiatives Different Segments Cybersecurity Cios Guide For It Strategy Strategy SS V. Dispense information and present a thorough explanation of Prepare Brand Identity, Formulate Thought Leadership, Investment In Paid Media using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.


