Powerpoint Templates and Google slides for Data Protection Regulations
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
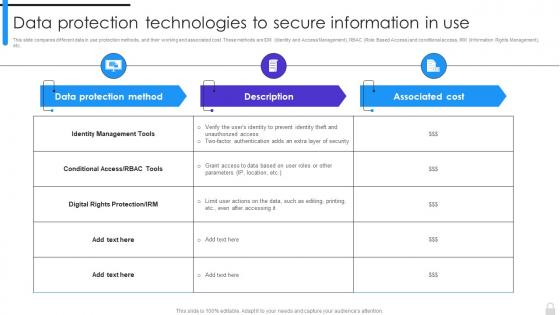 Encryption Implementation Strategies Data Protection Technologies To Secure Information In Use
Encryption Implementation Strategies Data Protection Technologies To Secure Information In UseThis slide compares different data in use protection methods, and their working and associated cost. These methods are IDM Identity and Access Management, RBAC Role Based Access and conditional access, IRM Information Rights Management, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Data Protection Technologies To Secure Information In Use. Use it as a tool for discussion and navigation on Identity Management Tools, Digital Rights Protection, Data Protection Technologies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
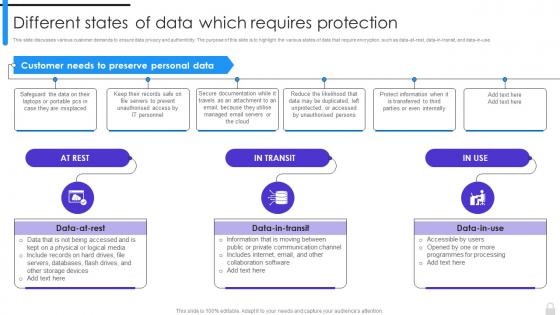 Encryption Implementation Strategies Different States Of Data Which Requires Protection
Encryption Implementation Strategies Different States Of Data Which Requires ProtectionThis slide discusses various customer demands to ensure data privacy and authenticity. The purpose of this slide is to highlight the various states of data that require encryption, such as data-at-rest, data-in-transit, and data-in-use. Introducing Encryption Implementation Strategies Different States Of Data Which Requires Protection to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Customer Demands, Data Privacy And Authenticity, Require Encryption, Collaboration Software, using this template. Grab it now to reap its full benefits.
-
 File Protection And Data Theft Prevention Icon
File Protection And Data Theft Prevention IconPresenting our well structured File Protection And Data Theft Prevention Icon. The topics discussed in this slide are Protection, Data, Prevention. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
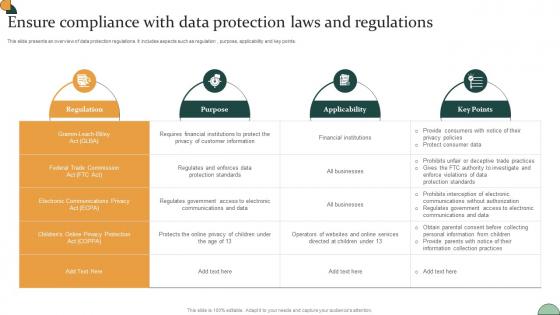 Corporate Compliance Strategy Ensure Compliance With Data Protection Laws Strategy SS V
Corporate Compliance Strategy Ensure Compliance With Data Protection Laws Strategy SS VThis slide presents an overview of data protection regulations. It includes aspects such as regulation , purpose, applicability and key points. Present the topic in a bit more detail with this Corporate Compliance Strategy Ensure Compliance With Data Protection Laws Strategy SS V Use it as a tool for discussion and navigation on Implement RiskAccountability, Conduct Timely RiskAssessments This template is free to edit as deemed fit for your organization. Therefore download it now.
-
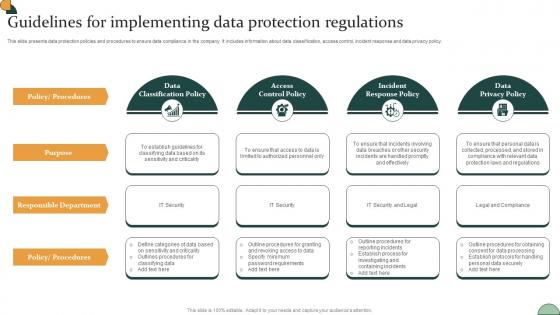 Corporate Compliance Strategy Guidelines For Implementing Data Protection Regulations Strategy SS V
Corporate Compliance Strategy Guidelines For Implementing Data Protection Regulations Strategy SS VThis slide presents data protection policies and procedures to ensure data compliance in the company. It includes information about data classification, access control, incident response and data privacy policy. Introducing Corporate Compliance Strategy Guidelines For Implementing Data Protection Regulations Strategy SS V to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Workplace Safety Compliance, Recordkeeping Compliance, Employment Law Compliance using this template. Grab it now to reap its full benefits.
-
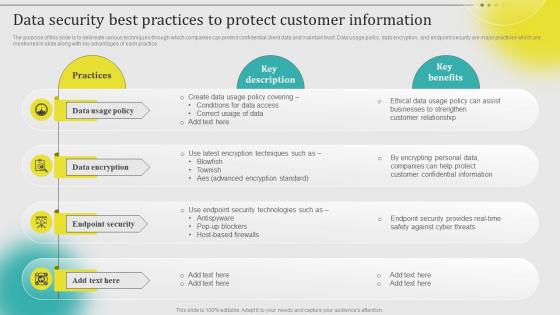 Data Security Best Practices To Protect Customer Information Leveraging Customer Data MKT SS V
Data Security Best Practices To Protect Customer Information Leveraging Customer Data MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Introducing Data Security Best Practices To Protect Customer Information Leveraging Customer Data MKT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Data Usage Policy, Data Encryption, Endpoint Security, using this template. Grab it now to reap its full benefits.
-
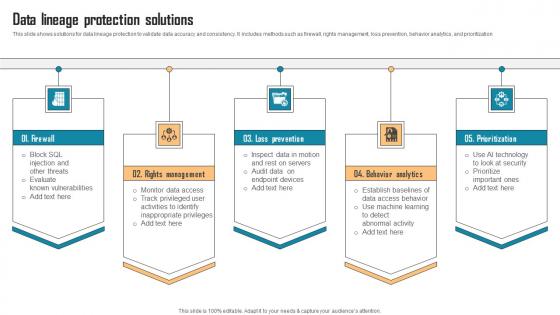 Data Lineage Protection Solutions
Data Lineage Protection SolutionsThis slide shows solutions for data lineage protection to validate data accuracy and consistency. It includes methods such as firewall, rights management, loss prevention, behavior analytics, and prioritization. Introducing our premium set of slides with Data Lineage Protection Solutions. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Firewall, Loss Prevention, Behavior Analytics. So download instantly and tailor it with your information.
-
 Data Protection Processes Rules In Powerpoint And Google Slides Cpb
Data Protection Processes Rules In Powerpoint And Google Slides CpbPresenting our Data Protection Processes Rules In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Data Protection Processes Rules. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
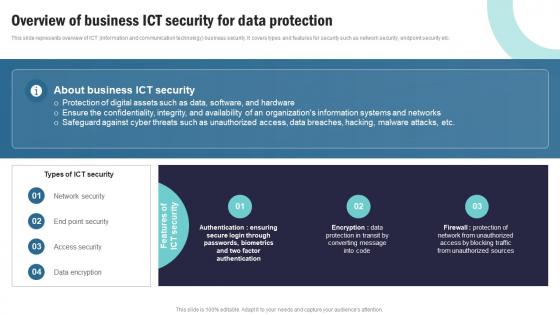 Strategic Plan To Implement Overview Of Business Ict Security For Data Protection Strategy SS V
Strategic Plan To Implement Overview Of Business Ict Security For Data Protection Strategy SS VThis slide represents overview of ICT information and communication technology business security. It covers types and features for security such as network security, endpoint security etc. Introducing Strategic Plan To Implement Overview Of Business Ict Security For Data Protection Strategy SS V to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Incident Management, Request Fulfillment using this template. Grab it now to reap its full benefits.
-
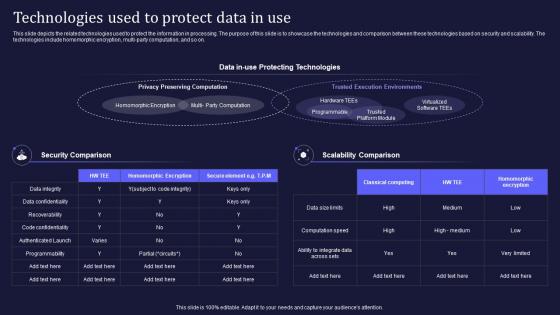 Confidential Computing V2 Technologies Used To Protect Data In Use
Confidential Computing V2 Technologies Used To Protect Data In UseThis slide depicts the related technologies used to protect the information in processing. The purpose of this slide is to showcase the technologies and comparison between these technologies based on security and scalability. The technologies include homomorphic encryption, multi-party computation, and so on. Present the topic in a bit more detail with this Confidential Computing V2 Technologies Used To Protect Data In Use. Use it as a tool for discussion and navigation on Homomorphic Encryption, Trusted Execution Environments, Privacy Preserving Computation, Protecting Technologies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
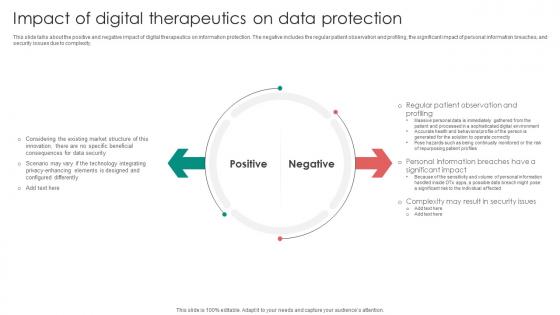 Digital Therapeutics Functions Impact Of Digital Therapeutics On Data Protection
Digital Therapeutics Functions Impact Of Digital Therapeutics On Data ProtectionThis slide talks about the positive and negative impact of digital therapeutics on information protection. The negative includes the regular patient observation and profiling, the significant impact of personal information breaches, and security issues due to complexity. Introducing Digital Therapeutics Functions Impact Of Digital Therapeutics On Data Protection to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Positive, Negative, Data Protection using this template. Grab it now to reap its full benefits.
-
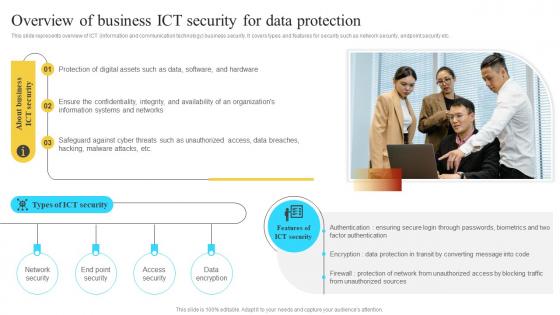 Implementation Of Information Overview Of Business Ict Security For Data Protection Strategy SS V
Implementation Of Information Overview Of Business Ict Security For Data Protection Strategy SS VThis slide represents overview of ICT information and communication technology business security. It covers types and features for security such as network security, endpoint security etc. Introducing Implementation Of Information Overview Of Business Ict Security For Data Protection Strategy SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Protection Of Digital, Safeguard Against Cyber, using this template. Grab it now to reap its full benefits.
-
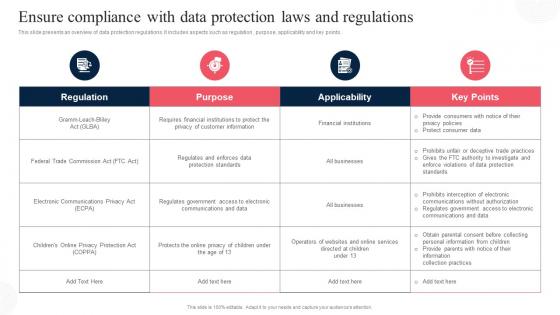 Ensure Compliance With Data Protection Corporate Regulatory Compliance Strategy SS V
Ensure Compliance With Data Protection Corporate Regulatory Compliance Strategy SS VThis slide presents an overview of data protection regulations. It includes aspects such as regulation, purpose, applicability and key points. Present the topic in a bit more detail with this Ensure Compliance With Data Protection Corporate Regulatory Compliance Strategy SS V. Use it as a tool for discussion and navigation on Regulation, Purpose. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
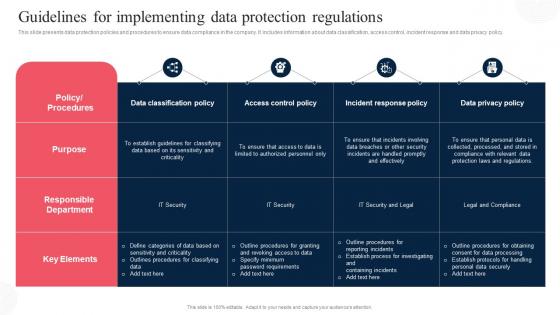 Guidelines For Implementing Data Protection Corporate Regulatory Compliance Strategy SS V
Guidelines For Implementing Data Protection Corporate Regulatory Compliance Strategy SS VThis slide presents data protection policies and procedures to ensure data compliance in the company. It includes information about data classification, access control, incident response and data privacy policy. Present the topic in a bit more detail with this Guidelines For Implementing Data Protection Corporate Regulatory Compliance Strategy SS V. Use it as a tool for discussion and navigation on Data Classification Policy, Access Control Policy. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Ensure Compliance With Data Protection Laws And Regulations Effective Business Risk Strategy SS V
Ensure Compliance With Data Protection Laws And Regulations Effective Business Risk Strategy SS VThis slide represents techniques to effectively engaging employees and stakeholders in the compliance process. It includes strategies such as training programs, communication channels, feedback mechanisms, incentives and recognition and compliance committees. Increase audience engagement and knowledge by dispensing information using Ensure Compliance With Data Protection Laws And Regulations Effective Business Risk Strategy SS V. This template helps you present information on six stages. You can also present information on Training Programs, Communication Channels using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
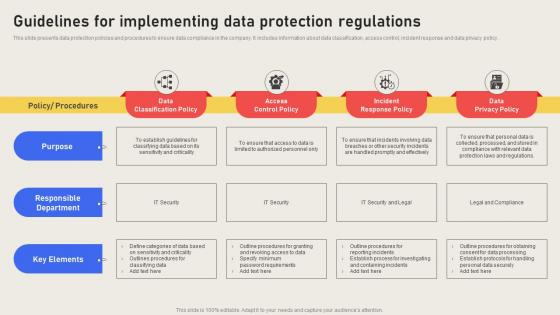 Guidelines For Implementing Data Protection Regulations Effective Business Risk Strategy SS V
Guidelines For Implementing Data Protection Regulations Effective Business Risk Strategy SS VThis slide presents data protection policies and procedures to ensure data compliance in the company. It includes information about data classification, access control, incident response and data privacy policy. Increase audience engagement and knowledge by dispensing information using Guidelines For Implementing Data Protection Regulations Effective Business Risk Strategy SS V. This template helps you present information on four stages. You can also present information on Purpose, Data Classification Policy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data Protection Impact Assessment Under Gdpr Transforming Healthcare BCT SS
Data Protection Impact Assessment Under Gdpr Transforming Healthcare BCT SSThis slide showcases data protection impact assessment checklist used by healthcare providers or companies to investigate potential vulnerabilities and improve data privacy and compliance status. It include various requirements that are evaluated on the basis of their current stage. Present the topic in a bit more detail with this Data Protection Impact Assessment Under Gdpr Transforming Healthcare BCT SS. Use it as a tool for discussion and navigation on Describe The Processing, Identify And Assess Risks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
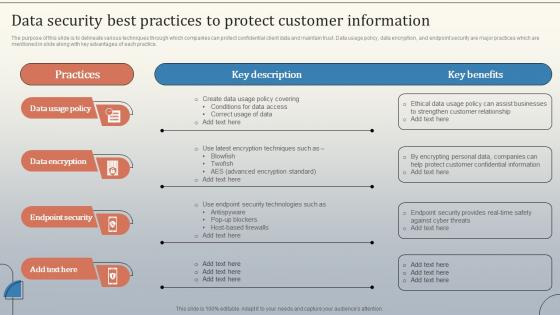 Data Security Best Practices To Protect Customer Database Marketing Strategies MKT SS V
Data Security Best Practices To Protect Customer Database Marketing Strategies MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Introducing Data Security Best Practices To Protect Customer Database Marketing Strategies MKT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Data Usage Policy, Data Encryption, using this template. Grab it now to reap its full benefits.
-
 Saas Cyber Security Icon To Protect Sensitive Data
Saas Cyber Security Icon To Protect Sensitive DataIntroducing our Saas Cyber Security, Icon To Protect Sensitive Data set of slides. The topics discussed in these slides are Saas Cyber Security, Icon To Protect Sensitive Data This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
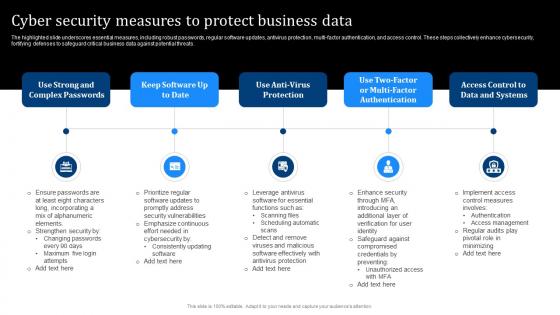 Cyber Security Measures To Protect Business Data
Cyber Security Measures To Protect Business DataThe highlighted slide underscores essential measures, including robust passwords, regular software updates, antivirus protection, multi factor authentication, and access control. These steps collectively enhance cybersecurity, fortifying defenses to safeguard critical business data against potential threats. Presenting our set of slides with Cyber Security Measures To Protect Business Data. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Strong And Complex Passwords, Software Updates, Enhance Security.
-
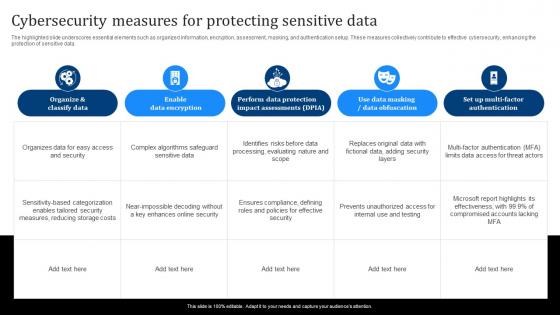 Cybersecurity Measures For Protecting Sensitive Data
Cybersecurity Measures For Protecting Sensitive DataThe highlighted slide underscores essential elements such as organized information, encryption, assessment, masking, and authentication setup. These measures collectively contribute to effective cybersecurity, enhancing the protection of sensitive data. Introducing our Cybersecurity Measures For Protecting Sensitive Data set of slides. The topics discussed in these slides are Enable Data Encryption, Data Obfuscation, Organize And Classify Data. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cybersecurity Tools To Enhance Data Protection
Cybersecurity Tools To Enhance Data ProtectionThe highlighted slide details essential aspects such as tools, descriptions, use cases, platforms, and licenses, presenting cybersecurity tools designed to enhance data protection. This information aids in selecting and implementing the right tools to bolster the security infrastructure and safeguard sensitive data effectively. Presenting our well structured Cybersecurity Tools To Enhance Data Protection. The topics discussed in this slide are Intrusion Detection And Prevention, Penetration Testing, Ethical Hacking. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Process To Develop Cybersecurity Strategy For Data Protection
Process To Develop Cybersecurity Strategy For Data ProtectionIntroducing our premium set of slides with Process To Develop Cybersecurity Strategy For Data Protection. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Threat Landscape, Cybersecurity Maturity, Cybersecurity Program Improvement. So download instantly and tailor it with your information.
-
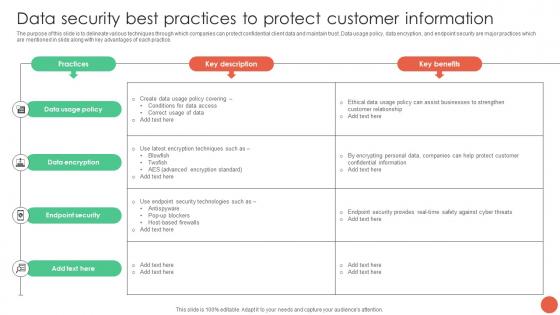 Data Security Best Practices To Protect Customer Information Database Marketing Techniques MKT SS V
Data Security Best Practices To Protect Customer Information Database Marketing Techniques MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Deliver an outstanding presentation on the topic using this Data Security Best Practices To Protect Customer Information Database Marketing Techniques MKT SS V. Dispense information and present a thorough explanation of Data Usage Policy, Data Encryption, Endpoint Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
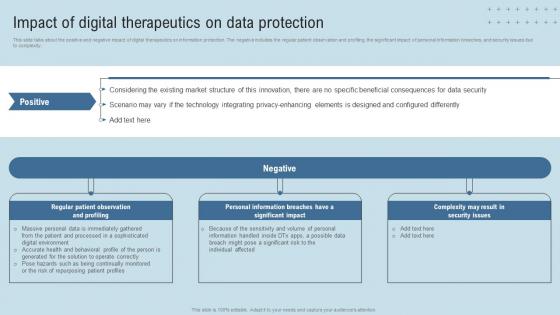 DTx Enablers Impact Of Digital Therapeutics On Data Protection
DTx Enablers Impact Of Digital Therapeutics On Data ProtectionThis slide talks about the positive and negative impact of digital therapeutics on information protection. The negative includes the regular patient observation and profiling, the significant impact of personal information breaches, and security issues due to complexity. Present the topic in a bit more detail with this DTx Enablers Impact Of Digital Therapeutics On Data Protection. Use it as a tool for discussion and navigation on Market Structure, Technology, Data Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
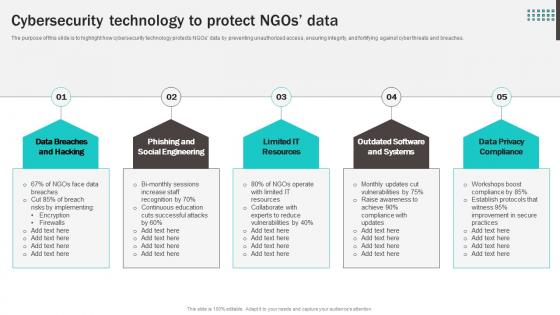 Cybersecurity Technology To Protect NGOs Data
Cybersecurity Technology To Protect NGOs DataThe purpose of this slide is to highlight how cybersecurity technology protects NGOs data by preventing unauthorized access, ensuring integrity, and fortifying against cyber threats and breaches. Introducing our premium set of slides with Cybersecurity Technology To Protect NGOs Data. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Breaches And Hacking, Phishing And Social Engineering, Outdated Software And Systems, Data Privacy Compliance. So download instantly and tailor it with your information.
-
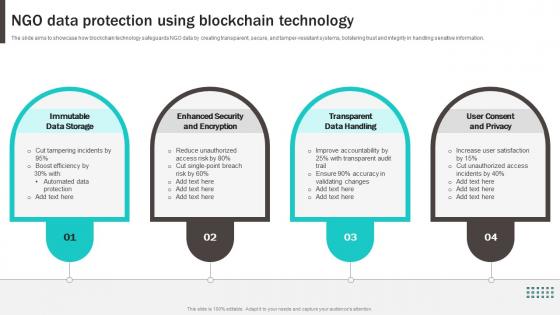 NGO Data Protection Using Blockchain Technology
NGO Data Protection Using Blockchain TechnologyThe slide aims to showcase how blockchain technology safeguards NGO data by creating transparent, secure, and tamper-resistant systems, bolstering trust and integrity in handling sensitive information. Presenting our set of slides with NGO Data Protection Using Blockchain Technology. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Immutable Data Storage, Enhanced Security And Encryption, Transparent Data Handling, User Consent And Privacy.
-
 Cloning In Cyber Security For Data Protection
Cloning In Cyber Security For Data ProtectionThis slide shows benefits of cloning for cyber protection. It aims to prevent cloning security risks to mitigate unauthorized access to technical assets. It covers four cyber security measures such as data protection, integrity, loss prevention and transfers. Presenting our set of slides with name Cloning In Cyber Security For Data Protection. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Protection, Data Integrity, Data Transfers.
-
 Data Security Management Icon To Protect Organizational Information
Data Security Management Icon To Protect Organizational InformationIntroducing our premium set of slides with Data Security Management Icon To Protect Organizational Information. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Security Management, Icon, Protect Organizational Information. So download instantly and tailor it with your information.
-
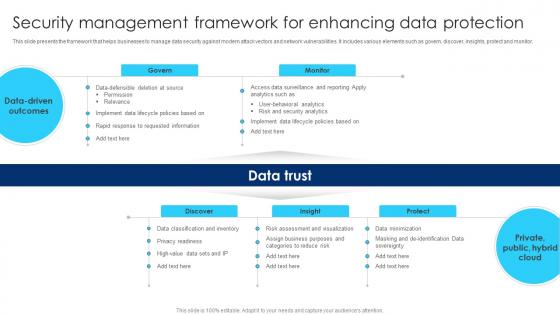 Security Management Framework For Enhancing Data Protection
Security Management Framework For Enhancing Data ProtectionThis slide presents the framework that helps businesses to manage data security against modern attack vectors and network vulnerabilities. It includes various elements such as govern, discover, insights, protect and monitor. Presenting our well structured Security Management Framework For Enhancing Data Protection. The topics discussed in this slide are Privacy Readiness, Risk And Security Analytics, Data Driven Outcomes. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 End To End Encryption Icon For User Data Protection
End To End Encryption Icon For User Data ProtectionIncrease audience engagement and knowledge by dispensing information using End To End Encryption Icon For User Data Protection This template helps you present information on Three stages. You can also present information on End To End Encryption, Icon For User Data Protection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data Protection Compliance Standards Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Data Protection Compliance Standards Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured PowerPoint icon features a graphic representation of cyber security analysis for prioritizing security updates. Perfect for presentations and reports related to cyber security, this icon highlights the importance of analyzing and prioritizing security updates to ensure maximum protection against potential threats.
-
 Data Protection Compliance Standards Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Data Protection Compliance Standards Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint icon is perfect for presentations on cyber security analysis and prioritizing security updates. The sleek and modern design will enhance your slides and effectively convey the importance of staying up-to-date with security measures. Use it to educate and inform your audience on the latest cyber security trends and best practices.
-
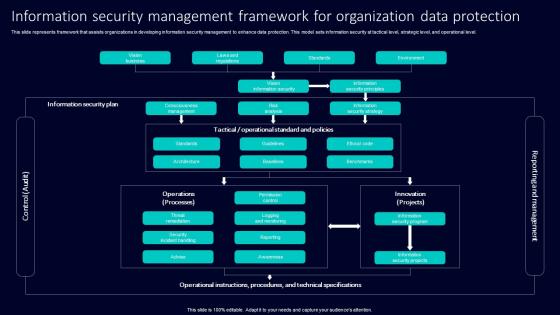 Information Security Management Framework For Organization Data Protection
Information Security Management Framework For Organization Data ProtectionThis slide represents framework that assists organizations in developing information security management to enhance data protection. This model sets information security at tactical level, strategic level, and operational level. Introducing our Information Security Management Framework For Organization Data Protection set of slides. The topics discussed in these slides are Information Security Plan, Consciousness Management, Risk Analysis. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Information Security Management Icon For Data Protection
Information Security Management Icon For Data ProtectionPresenting our set of slides with Information Security Management Icon For Data Protection. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Information Security Management Icon, Data Protection.
-
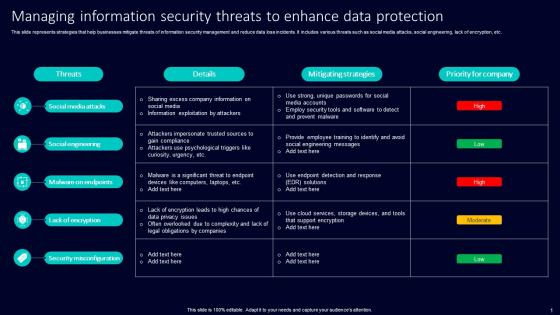 Managing Information Security Threats To Enhance Data Protection
Managing Information Security Threats To Enhance Data ProtectionThis slide represents strategies that help businesses mitigate threats of information security management and reduce data loss incidents. It includes various threats such as social media attacks, social engineering, lack of encryption, etc. Presenting our well structured Managing Information Security Threats To Enhance Data Protection. The topics discussed in this slide are Social Media Attacks, Social Engineering, Malware On Endpoints. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
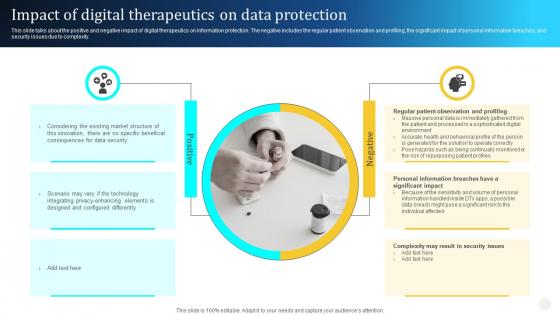 Digital Therapeutics Types Impact Of Digital Therapeutics On Data Protection Ppt Professional
Digital Therapeutics Types Impact Of Digital Therapeutics On Data Protection Ppt ProfessionalThis slide talks about the positive and negative impact of digital therapeutics on information protection. The negative includes the regular patient observation and profiling, the significant impact of personal information breaches, and security issues due to complexity. Introducing Digital Therapeutics Types Impact Of Digital Therapeutics On Data Protection Ppt Professional to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Positive, Negative, Regular Patient Observation, using this template. Grab it now to reap its full benefits.
-
 Extensive Business Strategy Cyber Strategies For KPMG For Client Data Protection Strategy SS V
Extensive Business Strategy Cyber Strategies For KPMG For Client Data Protection Strategy SS VThis slide covers techniques to secure customers confidential data through several cyber security strategies. The purpose for this template is to provide an overview on important elements of top techniques deployed by the company . It includes strategies such as people, process, data and technology and regulatory. Introducing Extensive Business Strategy Cyber Strategies For KPMG For Client Data Protection Strategy SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on People, Process, Regulatory, using this template. Grab it now to reap its full benefits.
-
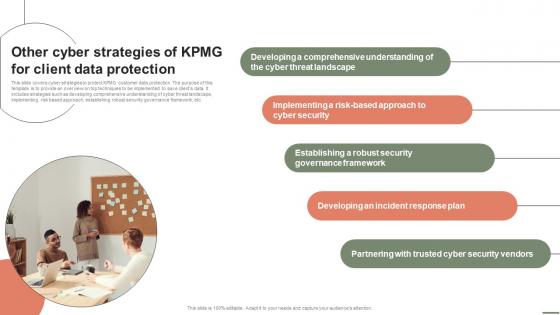 Extensive Business Strategy Other Cyber Strategies Of KPMG For Client Data Protection Strategy SS V
Extensive Business Strategy Other Cyber Strategies Of KPMG For Client Data Protection Strategy SS VThis slide covers cyber strategies to protect KPMG customer data protection. The purpose of this template is to provide an overview on top techniques to be implemented to save clients data. It includes strategies such as developing comprehensive understanding of cyber threat landscape, implementing risk based approach, establishing robust security governance framework, etc. Increase audience engagement and knowledge by dispensing information using Extensive Business Strategy Other Cyber Strategies Of KPMG For Client Data Protection Strategy SS V. This template helps you present information on five stages. You can also present information on Threat Landscape, Cyber Security, Governance Framework using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
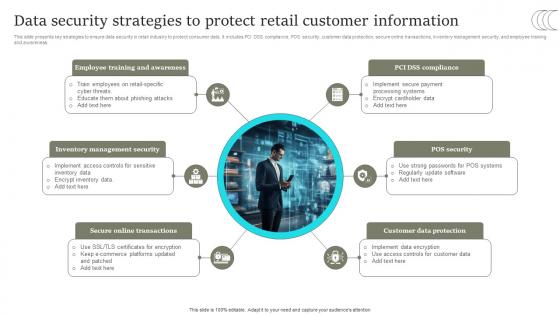 Data Security Strategies To Protect Retail Customer Comprehensive Retail Transformation DT SS
Data Security Strategies To Protect Retail Customer Comprehensive Retail Transformation DT SSThis slide presents key strategies to ensure data security in retail industry to protect consumer data. It includes PCI DSS compliance, POS security, customer data protection, secure online transactions, inventory management security, and employee training and awareness. Present the topic in a bit more detail with this Data Security Strategies To Protect Retail Customer Comprehensive Retail Transformation DT SS. Use it as a tool for discussion and navigation on Online Transactions, Customer Data Protection, POS Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
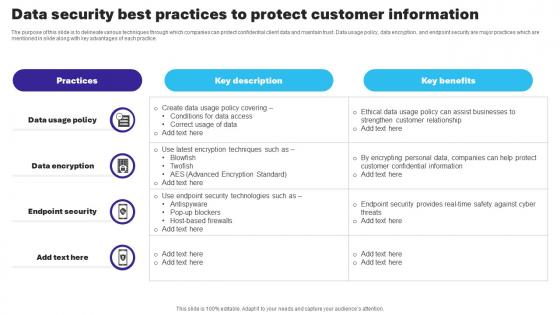 Essential Guide To Database Marketing Data Security Best Practices To Protect Customer Information MKT SS V
Essential Guide To Database Marketing Data Security Best Practices To Protect Customer Information MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Deliver an outstanding presentation on the topic using this Essential Guide To Database Marketing Data Security Best Practices To Protect Customer Information MKT SS V Dispense information and present a thorough explanation of Data Usage Policy, Data Encryption, Endpoint Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
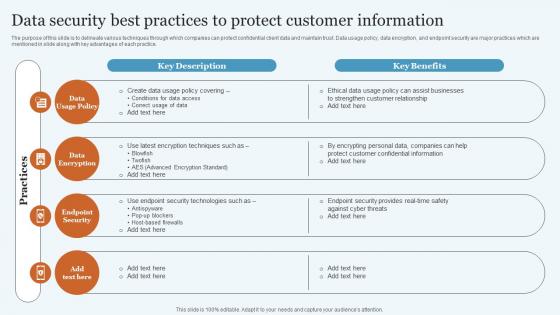 Data Security Best Practices To Protect Database Marketing Practices To Increase MKT SS V
Data Security Best Practices To Protect Database Marketing Practices To Increase MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Increase audience engagement and knowledge by dispensing information using Data Security Best Practices To Protect Database Marketing Practices To Increase MKT SS V. This template helps you present information on four stages. You can also present information on Policy, Encryption, Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
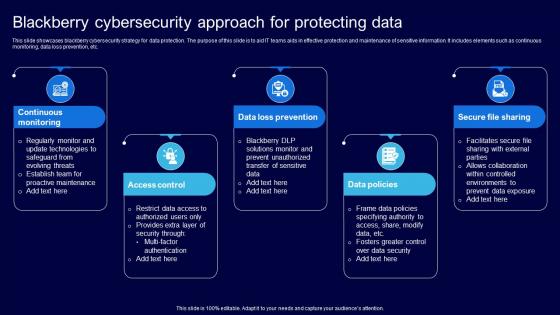 Blackberry Cybersecurity Approach For Protecting Data
Blackberry Cybersecurity Approach For Protecting DataThis slide showcases blackberry cybersecurity strategy for data protection. The purpose of this slide is to aid IT teams aids in effective protection and maintenance of sensitive information. It includes elements such as continuous monitoring, data loss prevention, etc. Presenting our set of slides with Blackberry Cybersecurity Approach For Protecting Data. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Monitoring, Access, Prevention.
-
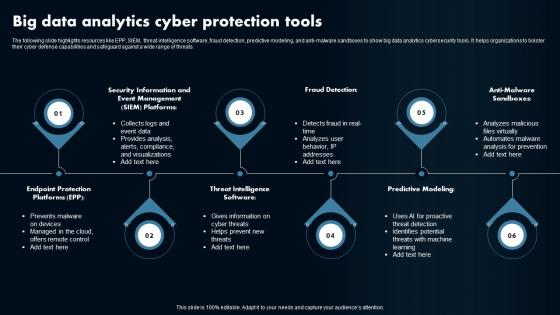 Big Data Analytics Cyber Protection Tools
Big Data Analytics Cyber Protection ToolsThe following slide highlights resources like EPP, SIEM, threat intelligence software, fraud detection, predictive modeling, and anti-malware sandboxes to show big data analytics cybersecurity tools. It helps organizations to bolster their cyber defense capabilities and safeguard against a wide range of threats. Presenting our set of slides with Big Data Analytics Cyber Protection Tools. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Fraud Detection, Predictive Modeling, Anti-Malware Sandboxes.
-
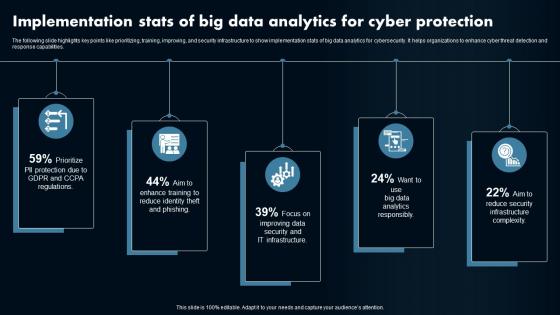 Implementation Stats Of Big Data Analytics For Cyber Protection
Implementation Stats Of Big Data Analytics For Cyber ProtectionThe following slide highlights key points like prioritizing, training, improving, and security infrastructure to show implementation stats of big data analytics for cybersecurity. It helps organizations to enhance cyber threat detection and response capabilities. Presenting our set of slides with Implementation Stats Of Big Data Analytics For Cyber Protection. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Implementation, Data Analytics, Cybersecurity.
-
 Strategies For Big Data Cyber Protection Analytics
Strategies For Big Data Cyber Protection AnalyticsThe following slide highlights key points like data collection, data normalization, expansion, enrichment, automation, standardization, and advanced detection to show strategies for big data analytics cybersecurity. It helps organizations to proactively defend against cyber threats and enhance overall security posture. Introducing our premium set of slides with Strategies For Big Data Cyber Protection Analytics. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Collection, Data Normalization, Expansion. So download instantly and tailor it with your information.
-
 Encryption Data Protection Devices Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Encryption Data Protection Devices Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon is a great visual aid for representing folder password protection. It is a modern and vibrant design that will add a professional touch to any presentation. The icon is easy to use and can be used to quickly and effectively communicate the importance of password security.
-
 Encryption Data Protection Devices Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Encryption Data Protection Devices Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone Powerpoint Icon on Folder Password is a simple yet effective way to protect your confidential data. It is easy to use and provides a secure encryption for your files. It is an ideal solution for those who want to keep their documents safe and secure.
-
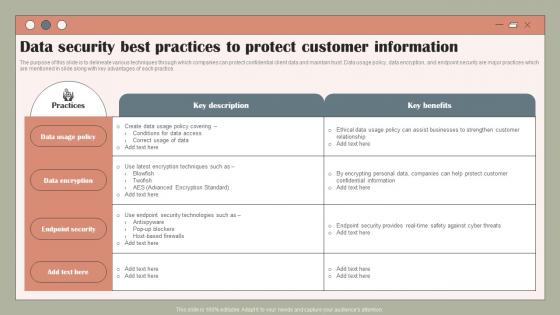 Data Security Best Practices To Protect Using Customer Data To Improve MKT SS V
Data Security Best Practices To Protect Using Customer Data To Improve MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Deliver an outstanding presentation on the topic using this Data Security Best Practices To Protect Using Customer Data To Improve MKT SS V. Dispense information and present a thorough explanation of Policy, Data, Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Security Strategies To Protect Retail Customer Digital Transformation Of Retail DT SS
Data Security Strategies To Protect Retail Customer Digital Transformation Of Retail DT SSThis slide presents key strategies to ensure data security in retail industry to protect consumer data. It includes PCI DSS compliance, POS security, customer data protection, secure online transactions, inventory management security, and employee training and awareness. Increase audience engagement and knowledge by dispensing information using Data Security Strategies To Protect Retail Customer Digital Transformation Of Retail DT SS This template helps you present information on six stages. You can also present information on Customer Data Protection, Online Transactions, Management Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Implement General Data Protection Regulation Digital Transformation Of Retail DT SS
Implement General Data Protection Regulation Digital Transformation Of Retail DT SSThis slide presents actions to establish a safe-custodian image in retail industry. It includes integrating general data protection and regulation with steps understand GDPR, data audit, consent and legal basis, privacy notices and policies, data security and breach notification and ongoing compliance. Introducing Implement General Data Protection Regulation Digital Transformation Of Retail DT SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Ongoing Compliance, Data Security, Consent And Legal Basis using this template. Grab it now to reap its full benefits.
-
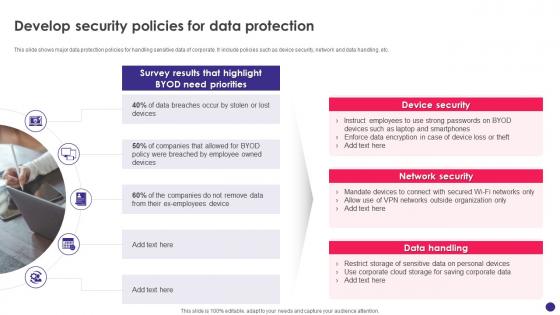 Implementing Byod Policy To Enhance Develop Security Policies For Data Protection
Implementing Byod Policy To Enhance Develop Security Policies For Data ProtectionThis slide shows major data protection policies for handling sensitive data of corporate. It include policies such as device security, network and data handling, etc. Introducing Implementing Byod Policy To Enhance Develop Security Policies For Data Protection to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Network Security, Data Handling, Device Security, Data Protection, using this template. Grab it now to reap its full benefits.
-
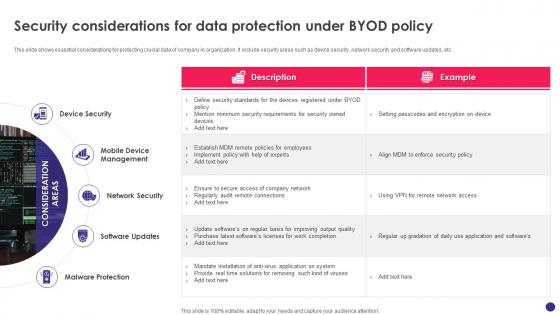 Implementing Byod Policy To Enhance Security Considerations For Data Protection Under Byod Policy
Implementing Byod Policy To Enhance Security Considerations For Data Protection Under Byod PolicyThis slide shows essential considerations for protecting crucial data of company in organization. It include security areas such as device security, network security and software updates, etc. Increase audience engagement and knowledge by dispensing information using Implementing Byod Policy To Enhance Security Considerations For Data Protection Under Byod Policy. This template helps you present information on five stages. You can also present information on Device Security, Mobile Device Management, Network Security, Malware Protection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
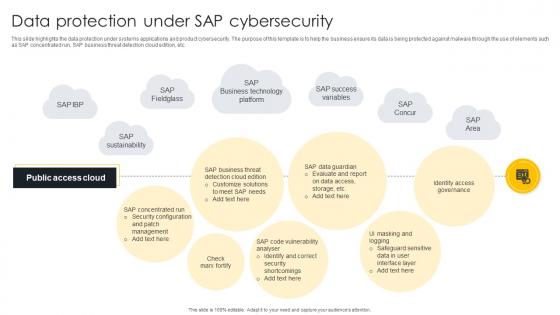 Data Protection Under SAP Cybersecurity
Data Protection Under SAP CybersecurityThis slide highlights the data protection under systems applications and product cybersecurity. The purpose of this template is to help the business ensure its data is being protected against malware through the use of elements such as SAP concentrated run, SAP business threat detection cloud edition, etc. Presenting our well structured Data Protection Under SAP Cybersecurity. The topics discussed in this slide are Identity Access Governance, Identify And Correct Security, Evaluate And Report. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Major Components Of IP Security To Protect Sensitive Data
Major Components Of IP Security To Protect Sensitive DataThis slide showcases key elements of IP security for protecting data. The main purpose of this template is to showcase protection and trustworthiness of data. This includes encapsulating security payload, authentication header, and internet key exchange. Presenting our set of slides with name Major Components Of IP Security To Protect Sensitive Data. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Internet Key Exchange, Authentication Header, Encapsulating Security Payload.
-
 Data Masking Icon To Optimize Patient Data Protection
Data Masking Icon To Optimize Patient Data ProtectionIntroducing our premium set of slides with Data Masking Icon To Optimize Patient Data Protection. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Masking Icon, Optimize Patient Data Protection.So download instantly and tailor it with your information.
-
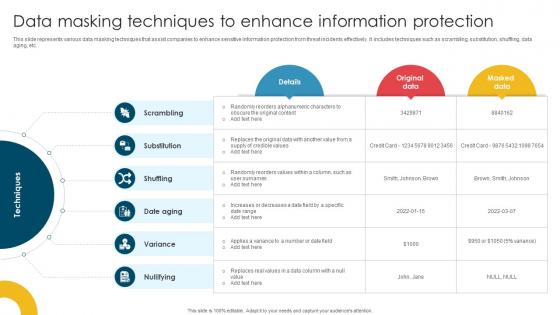 Data Masking Techniques To Enhance Information Protection
Data Masking Techniques To Enhance Information ProtectionThis slide represents various data masking techniques that assist companies to enhance sensitive information protection from threat incidents effectively. It includes techniques such as scrambling, substitution, shuffling, data aging, etc. Presenting our well structured Data Masking Techniques To Enhance Information Protection. The topics discussed in this slide are Date Aging, Substitution, Variance. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
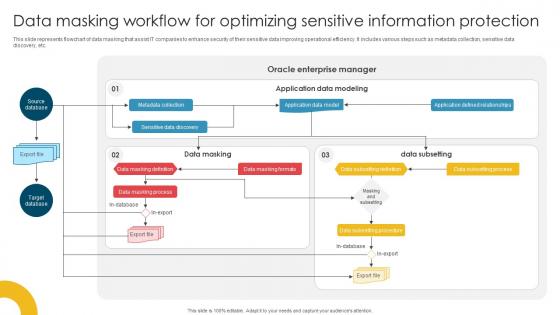 Data Masking Workflow For Optimizing Sensitive Information Protection
Data Masking Workflow For Optimizing Sensitive Information ProtectionThis slide represents flowchart of data masking that assist IT companies to enhance security of their sensitive data improving operational efficiency. It includes various steps such as metadata collection, sensitive data discovery, etc. Introducing our Data Masking Workflow For Optimizing Sensitive Information Protection set of slides. The topics discussed in these slides are Data Masking Definition, Data Masking Process, Data Subsetting Definition.This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
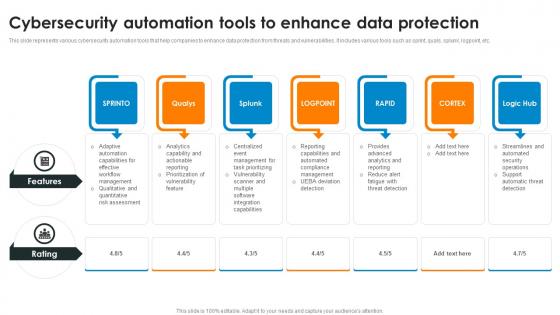 Cybersecurity Automation Tools To Enhance Data Protection
Cybersecurity Automation Tools To Enhance Data ProtectionThis slide represents various cybersecurity automation tools that help companies to enhance data protection from threats and vulnerabilities. It includes various tools such as sprint, quals, splunk, logpoint, etc. Introducing our premium set of slides with Cybersecurity Automation Tools To Enhance Data Protection Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Features, Cybersecurity Automation, Data Protection So download instantly and tailor it with your information.
-
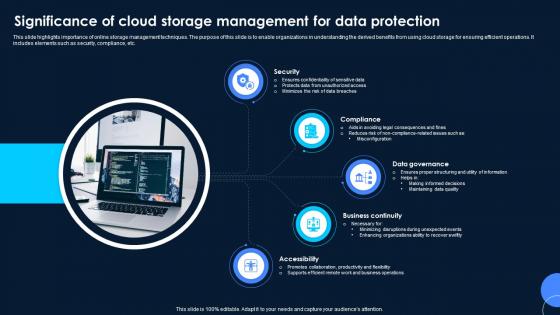 Significance Of Cloud Storage Management For Data Protection
Significance Of Cloud Storage Management For Data ProtectionThis slide highlights importance of online storage management techniques. The purpose of this slide is to enable organizations in understanding the derived benefits from using cloud storage for ensuring efficient operations. It includes elements such as security, compliance, etc. Introducing our premium set of slides with Significance Of Cloud Storage Management For Data Protection. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security, Compliance, Data Governance. So download instantly and tailor it with your information.



