Powerpoint Templates and Google slides for Data security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
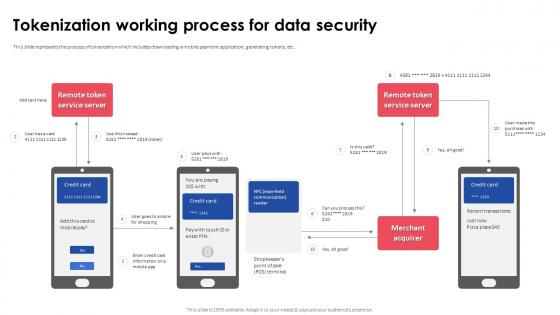 Tokenization Working Process For Data Security Implementing Effective Tokenization
Tokenization Working Process For Data Security Implementing Effective TokenizationThis slide represents the process of tokenization which includes downloading a mobile payment application, generating tokens, etc. Deliver an outstanding presentation on the topic using this Tokenization Working Process For Data Security Implementing Effective Tokenization. Dispense information and present a thorough explanation of Tokenization Working Process, Data Security, Mobile Payment Application, Generating Tokens using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
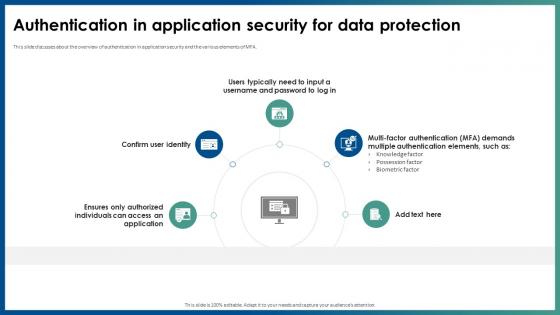 Authentication In Application Security For Data Protection
Authentication In Application Security For Data ProtectionThis slide discusses about the overview of authentication in application security and the various elements of MFA. Increase audience engagement and knowledge by dispensing information using Authentication In Application Security For Data Protection. This template helps you present information on five stages. You can also present information on Knowledge Factor, Possession Factor, Biometric Factor, Data Protection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Authorization In Application Security For Data Privacy
Authorization In Application Security For Data PrivacyThis slide discusses the overview of authorization in application security for authorized access of resource. Increase audience engagement and knowledge by dispensing information using Authorization In Application Security For Data Privacy. This template helps you present information on five stages. You can also present information on Application Security, Data Privacy, Helps Servers Identify Clients using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
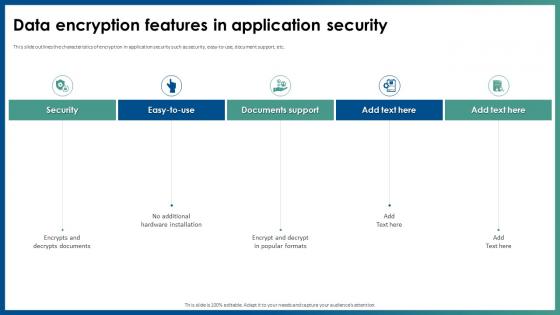 Data Encryption Features In Application Security
Data Encryption Features In Application SecurityThis slide outlines the characteristics of encryption in application security such as security, easy-to-use, document support, etc. Introducing Data Encryption Features In Application Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Implement Strict Input Validation, Employ Bot Detection Mechanisms, Application Security Deployment, using this template. Grab it now to reap its full benefits.
-
 Data Encryption Method In Application Security
Data Encryption Method In Application SecurityThis slide outlines the characteristics of encryption in application security such as security, easy-to-use, document support, etc. Increase audience engagement and knowledge by dispensing information using Data Encryption Method In Application Security. This template helps you present information on five stages. You can also present information on Encodes Plaintext To Ciphertext, Decryption Needs Specific Keys, Create Cryptographic Models using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Introduction Of Application Security For Data Privacy
Introduction Of Application Security For Data PrivacyThis slide discusses the overview of application security which includes its objectives such as protecting data, minimize risk, etc. Increase audience engagement and knowledge by dispensing information using Introduction Of Application Security For Data Privacy. This template helps you present information on four stages. You can also present information on Covers Post Deployment Protection, Protects Data And Code, Application Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Overview Of Virtual Private Network For Data Security
Overview Of Virtual Private Network For Data SecurityThis slide discusses the overview of virtual private network used for secure transfer of data through tunnelling protocols. Increase audience engagement and knowledge by dispensing information using Overview Of Virtual Private Network For Data Security. This template helps you present information on six stages. You can also present information on Public Network, Supporting Multiple Devices, Virtual Private Network, Data Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Security Audit Procedure Icon To Verify Company Data Protection
Security Audit Procedure Icon To Verify Company Data ProtectionPresenting our set of slides with Security Audit Procedure Icon To Verify Company Data Protection. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Audit Procedure, Verify Company, Data Protection.
-
 Smart Contracts Data Security Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Smart Contracts Data Security Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured PowerPoint icon features a blockchain design, representing its use in preventing finance fraud. With its vibrant colours and modern design, this icon is perfect for presentations and materials related to finance and blockchain technology. Use it to showcase the importance of blockchain in preventing fraud in the financial industry.
-
 Smart Contracts Data Security Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Smart Contracts Data Security Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatProtect your financial data with our Monotone PowerPoint icon on Finance Fraud Prevention by Blockchain. This powerful icon visually represents the use of blockchain technology to prevent fraudulent activities in the finance industry. Use it to educate and inform your audience about the importance of implementing blockchain for secure financial transactions
-
 Data Server Security Updates Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Data Server Security Updates Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured PowerPoint icon represents data server preventive maintenance. It features a server with a wrench and gear symbol, indicating the importance of regular maintenance for optimal performance. Use this icon to visually communicate the need for proactive measures to prevent data server issues and ensure smooth operations.
-
 Data Server Security Updates Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Data Server Security Updates Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone powerpoint icon represents Data server preventive maintenance. It features a simple design with a server symbol and a wrench, indicating the importance of regular maintenance to keep data servers running smoothly. Use this icon to visually communicate the need for proactive maintenance in your presentations or documents.
-
 SaaS Security Icon For Protecting Confidential Data
SaaS Security Icon For Protecting Confidential DataPresenting our set of slides with SaaS Security Icon For Protecting Confidential Data. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on SaaS Security, Protecting Confidential Data.
-
 Agenda For Mobile Device Security For Data Protection Cybersecurity SS
Agenda For Mobile Device Security For Data Protection Cybersecurity SSIntroducing Agenda For Mobile Device Security For Data Protection Cybersecurity SS to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Agenda using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Mobile Device Security For Data Protection Cybersecurity SS
Icons Slide For Mobile Device Security For Data Protection Cybersecurity SSIntroducing our well researched set of slides titled Icons Slide For Mobile Device Security For Data Protection Cybersecurity SS It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
 Mobile Device Encryption Plan For Data Security Mobile Device Security Cybersecurity SS
Mobile Device Encryption Plan For Data Security Mobile Device Security Cybersecurity SSThis slide showcases data encryption plan that can help to enhance mobile security. Its key elements are target devices, employees, encryption technique used, software used, authentication method etc. Introducing Mobile Device Encryption Plan For Data Security Mobile Device Security Cybersecurity SS to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Encrypted Communication, Secure Remote Access, Data Privacy using this template. Grab it now to reap its full benefits.
-
 Mobile Device Encryption Policy To Safeguard Data Mobile Device Security Cybersecurity SS
Mobile Device Encryption Policy To Safeguard Data Mobile Device Security Cybersecurity SSThis slide showcases mobile encryption policy that can help in data privacy. Its key components are purpose of policy, scope and encryption policy Increase audience engagement and knowledge by dispensing information using Mobile Device Encryption Policy To Safeguard Data Mobile Device Security Cybersecurity SS This template helps you present information on Three stages. You can also present information on Geographical Region, Detected Globally, Mobile Cyber Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Mobile Device Security For Data Protection Table Of Contents Cybersecurity SS
Mobile Device Security For Data Protection Table Of Contents Cybersecurity SSIntroducing Mobile Device Security For Data Protection Table Of Contents Cybersecurity SS to increase your presentation threshold. Encompassed with One stages, this template is a great option to educate and entice your audience. Dispence information on Target Devices, Target Employees, Encryption Technique Used using this template. Grab it now to reap its full benefits.
-
 Table Of Contents For Mobile Device Security For Data Protection Cybersecurity SS
Table Of Contents For Mobile Device Security For Data Protection Cybersecurity SSIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Mobile Device Security For Data Protection Cybersecurity SS This template helps you present information on Five stages. You can also present information on Financial Companies, Million Phishing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Securing Food Safety In Online Leveraging Data Analytics To Forecast Deliveries
Securing Food Safety In Online Leveraging Data Analytics To Forecast DeliveriesThis slide covers utilizing data analytics tools to forecast demand involves key components such as predictive analytics, customer segmentation and sentiment analysis. Introducing Securing Food Safety In Online Leveraging Data Analytics To Forecast Deliveries to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Predictive Analytics, Customer Segmentation, Sentiment Analysis, using this template. Grab it now to reap its full benefits.
-
 Regtech Icon For Efficient Data Management And Security
Regtech Icon For Efficient Data Management And SecurityIntroducing our premium set of slides with name Regtech Icon For Efficient Data Management And Security. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Regtech Icon, Efficient Data, Management And Security. So download instantly and tailor it with your information.
-
 SIEM Data Cyber Security Icon
SIEM Data Cyber Security IconPresenting our set of slides with name SIEM Data Cyber Security Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on SIEM data cyber security icon.
-
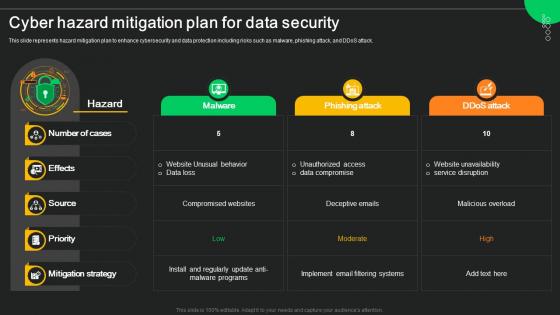 Cyber Hazard Mitigation Plan For Data Security
Cyber Hazard Mitigation Plan For Data SecurityThis slide represents hazard mitigation plan to enhance cybersecurity and data protection including risks such as malware, phishing attack, and DDoS attack. Presenting our well structured Cyber Hazard Mitigation Plan For Data Security. The topics discussed in this slide are Malware, Phishing Attack, Ddos Attack. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
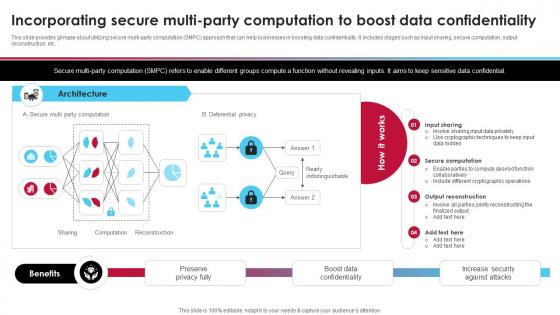 Incorporating Secure Multi-Party Computation To Boost Data Ai Driven Digital Transformation Planning DT SS
Incorporating Secure Multi-Party Computation To Boost Data Ai Driven Digital Transformation Planning DT SSThis slide provides glimpse about utilizing secure multi-party computation SMPC approach that can help businesses in boosting data confidentiality. It includes stages such as input sharing, secure computation, output reconstruction, etc. Present the topic in a bit more detail with this Incorporating Secure Multi-Party Computation To Boost Data Ai Driven Digital Transformation Planning DT SS. Use it as a tool for discussion and navigation on Secure Computation, Output Reconstruction, Input Sharing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Analyzing Cloud Based Service Offerings Best Practices To Improve Data Security
Analyzing Cloud Based Service Offerings Best Practices To Improve Data SecurityThis slide showcases various tips which can be adopted by business to enhance data security of SAAs application. It provides information regarding end to end encryption, application testing, data deletion policy and VPN. Introducing Analyzing Cloud Based Service Offerings Best Practices To Improve Data Security to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on End To End Encryption, Application Testing, Data Deletion Policy, Vpn, using this template. Grab it now to reap its full benefits.
-
 IT Modernization Strategy Icon For Data Security
IT Modernization Strategy Icon For Data SecurityIntroducing our premium set of slides with IT Modernization Strategy Icon For Data Security Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Modernization Strategy, Data Security So download instantly and tailor it with your information.
-
 Saas Best Practices Icon To Optimize Data Migration Security
Saas Best Practices Icon To Optimize Data Migration SecurityIntroducing our Saas Best Practices Icon To Optimize Data Migration Security set of slides. The topics discussed in these slides are Optimize Data, Migration Security, Best Practices. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Mobile Security Icon To Safeguard Sensitive Data
Mobile Security Icon To Safeguard Sensitive DataPresenting our set of slides with name Mobile Security Icon To Safeguard Sensitive Data. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Mobile Security Icon, Safeguard Sensitive Data.
-
 Cloud Virtualization Icon Showcasing Data Security
Cloud Virtualization Icon Showcasing Data SecurityPresenting our set of slides with name Cloud Virtualization Icon Showcasing Data Security This exhibits information on Threestages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cloud Virtualization Icon, Showcasing Data Security
-
 Fingerprint Biometric Technology Icon For Securing Data
Fingerprint Biometric Technology Icon For Securing DataIntroducing our Fingerprint Biometric Technology Icon For Securing Data set of slides. The topics discussed in these slides are Fingerprint Biometric Technology, Icon For Securing Data This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Data Center Facility Security Plan
Data Center Facility Security PlanThe purpose of this slide is to ensure comprehensive protection against unauthorized access, physical threats, and data breaches including security aspects such as data center layout, environmental controls, etc. Introducing our premium set of slides with name Data Center Facility Security Plan. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Environmental Controls, Data Center Layout, Network Security, Vendor And Contractor Access. So download instantly and tailor it with your information.
-
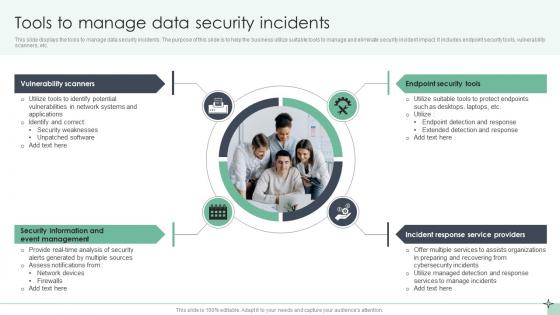 Tools To Manage Data Security Incidents
Tools To Manage Data Security IncidentsThis slide displays the tools to manage data security incidents. The purpose of this slide is to help the business utilize suitable tools to manage and eliminate security incident impact. It includes endpoint security tools, vulnerability scanners, etc. Presenting our set of slides with Tools To Manage Data Security Incidents. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Vulnerability Scanners, Endpoint Security Tools, Incident Response.
-
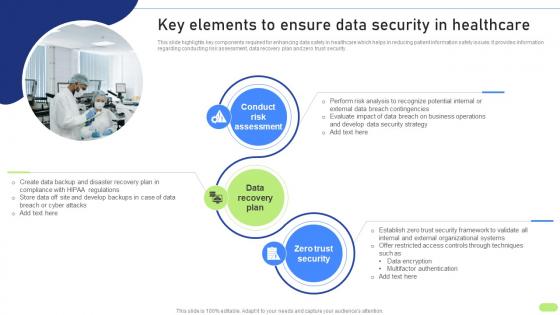 Key Elements To Ensure Data Security Definitive Guide To Implement Data Analytics SS
Key Elements To Ensure Data Security Definitive Guide To Implement Data Analytics SSThis slide highlights key components required for enhancing data safety in healthcare which helps in reducing patient information safety issues. It provides information regarding conducting risk assessment, data recovery plan and zero trust security. Introducing Key Elements To Ensure Data Security Definitive Guide To Implement Data Analytics SS to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Conduct Risk Assessment, Data Recovery Plan, Zero Trust Security, using this template. Grab it now to reap its full benefits.
-
 Implement Robust Security Measures Icon For Big Data Platforms
Implement Robust Security Measures Icon For Big Data PlatformsIntroducing our Implement Robust Security Measures Icon For Big Data Platforms set of slides. The topics discussed in these slides are Implement Robust Security Measures, Icon For Big Data Platforms. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Project Data Security And Privacy Checklist Matrix
Project Data Security And Privacy Checklist MatrixThe purpose of this slide is to introduce project data security and privacy checklist matrix, which systematically ensures and enhances data and privacy protection measures throughout the project lifecycle. Introducing our Project Data Security And Privacy Checklist Matrix set of slides. The topics discussed in these slides are Data Encryption, Access Controls, Security Audits, User Authentication. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
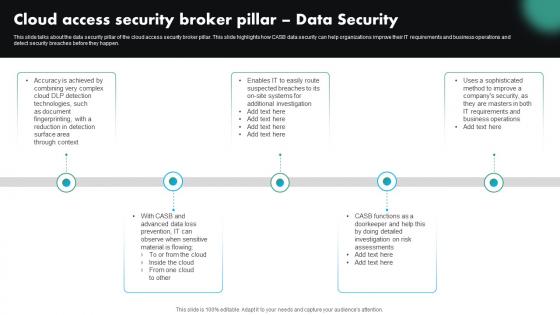 Cloud Access Security Broker Pillar Data Security CASB Cloud Security
Cloud Access Security Broker Pillar Data Security CASB Cloud SecurityThis slide talks about the data security pillar of the cloud access security broker pillar. This slide highlights how CASB data security can help organizations improve their IT requirements and business operations and detect security breaches before they happen. Introducing Cloud Access Security Broker Pillar Data Security CASB Cloud Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Access Security Broker, Business Operations, Risk Assessments, using this template. Grab it now to reap its full benefits.
-
 Comparison Between CASB And Data Loss Prevention DLP CASB Cloud Security
Comparison Between CASB And Data Loss Prevention DLP CASB Cloud SecurityThis slide describes the difference between cloud access security broker and data loss prevention. This slide highlights the main comparisons between CASB and DLP systems based on their purpose, focus area, use cases, key features, implementation and relationship. Present the topic in a bit more detail with this Comparison Between CASB And Data Loss Prevention DLP CASB Cloud Security. Use it as a tool for discussion and navigation on Cloud Access Security Broker, Data Loss Prevention, Focus Area, Implementation And Relationship. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Big Data Security Technology To Enhance Systems Efficiency
Big Data Security Technology To Enhance Systems EfficiencyThis slide represents big data security technology which enhances security of non relational databases and boosts endpoint security. It includes big data security technology to enhance systems efficiency such as encryption, user access control etc. Presenting our set of slides with name Big Data Security Technology To Enhance Systems Efficiency. This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Centralized Key Management, Physical Security, User Access Control, Encryption.
-
 Checklist For Holistic Data Security And Privacy In Big Data Technology
Checklist For Holistic Data Security And Privacy In Big Data TechnologyThis slide represents checklist for data security and privacy in big data technology which assists to prevent unauthorized access and provides safeguard against cyber threat. It includes key steps such as secure and monitor, find and classify, etc. Introducing our Checklist For Holistic Data Security And Privacy In Big Data Technology set of slides. The topics discussed in these slides are Find And Classify, Secure And Monitor, Harden, Protect And Remain Vigilant. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
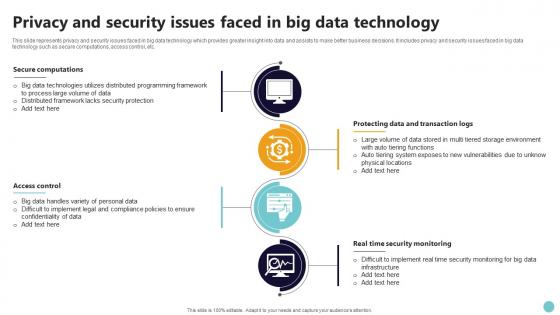 Privacy And Security Issues Faced In Big Data Technology
Privacy And Security Issues Faced In Big Data TechnologyThis slide represents privacy and security issues faced in big data technology which provides greater insight into data and assists to make better business decisions. It includes privacy and security issues faced in big data technology such as secure computations, access control, etc. Presenting our set of slides with name Privacy And Security Issues Faced In Big Data Technology. This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Secure Computations, Access Control, Protecting Data And Transaction Logs, Real Time Security Monitoring.
-
 Different Encryption Methods To Secure Business Data
Different Encryption Methods To Secure Business DataThis slide represents various types of encryption method which assists businesses to protect data and maintain regulatory compliances. It includes different encryption methods to secure business data such as advance encryption standards, rivest shamir adleman, etc. Introducing our premium set of slides with name Different Encryption Methods To Secure Business Data. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Format Preserving Encryption, Blowfish, Advance Encryption Standards. So download instantly and tailor it with your information.
-
 Emerging Encryption Trends For Enhancing Data Security
Emerging Encryption Trends For Enhancing Data SecurityThis slide represents latest trends in encryption which assists to scramble data into a secret code which can be unlocked with unique digital key. It includes latest trends in encryption such as homomorphic encryption, quantum encryption, etc. Presenting our set of slides with name Emerging Encryption Trends For Enhancing Data Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Quantum Cryptography, Homomorphic Encryption, Moving Target Defense.
-
 Network Virtualization Icon To Enhance Data Security
Network Virtualization Icon To Enhance Data SecurityIntroducing our Network Virtualization Icon To Enhance Data Security set of slides. The topics discussed in these slides are Network Virtualization, Data Security. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Technology Project Goals Icon To Strength Data Security
Technology Project Goals Icon To Strength Data SecurityPresenting our set of slides with Technology Project Goals Icon To Strength Data Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Technology, Goals, Strength.
-
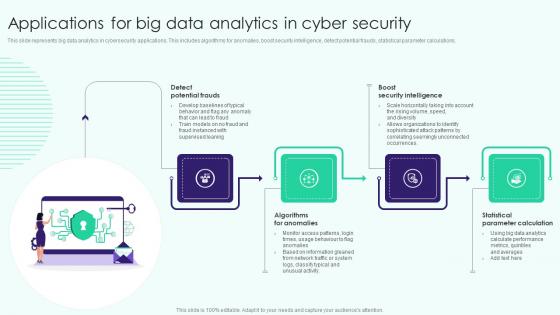 Applications For Big Data Analytics In Cyber Security
Applications For Big Data Analytics In Cyber SecurityThis slide represents big data analytics in cybersecurity applications. This includes algorithms for anomalies, boost security intelligence, detect potential frauds, statistical parameter calculations. Presenting our set of slides with name Applications For Big Data Analytics In Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Detect Potential Frauds, Algorithms For Anomalies, Statistical Parameter Calculation .
-
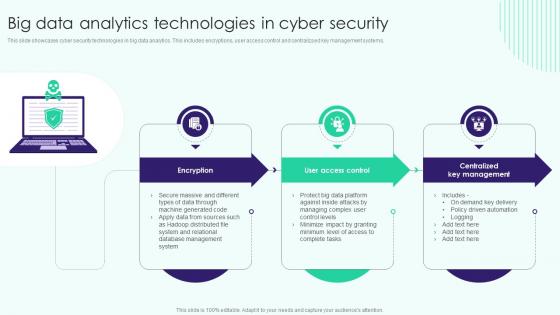 Big Data Analytics Technologies In Cyber Security
Big Data Analytics Technologies In Cyber SecurityThis slide showcases cyber security technologies in big data analytics. This includes encryptions, user access control and centralizsed key management systems. Presenting our set of slides with name Big Data Analytics Technologies In Cyber Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Big Data Analytics, Centralized Key Management, Technologies In Cyber Security.
-
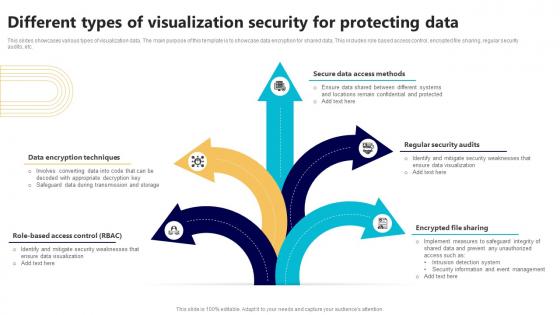 Different Types Of Visualization Security For Protecting Data
Different Types Of Visualization Security For Protecting DataThis slides showcases various types of visualization data. The main purpose of this template is to showcase data encryption for shared data. This includes role based access control, encrypted file sharing, regular security audits, etc. Introducing our premium set of slides with Different Types Of Visualization Security For Protecting Data. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Access Methods, Regular Security Audits, Encrypted File Sharing. So download instantly and tailor it with your information.
-
 Role Of Visualization Security For Understanding Complex Data
Role Of Visualization Security For Understanding Complex DataThis slides showcase ways of simplifying data through visualization security. The main purpose of this template is to showcase ways in which data can be protected and gain insights from customers. This includes simplifying complex data, identification trends, real time monitoring, etc. Presenting our set of slides with Role Of Visualization Security For Understanding Complex Data. This exhibits information on seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Simplifying Complex, Identification Trends, Driving Innovation.
-
 Visualization Security Icon For Data Protection
Visualization Security Icon For Data ProtectionPresenting our set of slides with Visualization Security Icon For Data Protection. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Visualization Security, Data Protection.
-
 Icon For Wireless Internet Security To Secure Data
Icon For Wireless Internet Security To Secure DataPresenting our well structured Icon For Wireless Internet Security To Secure Data. The topics discussed in this slide are Wireless Internet, Security, Secure Data. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
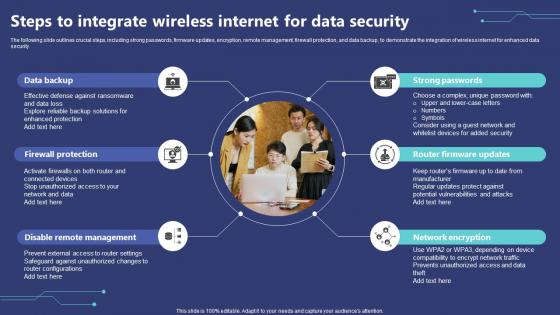 Steps To Integrate Wireless Internet For Data Security
Steps To Integrate Wireless Internet For Data SecurityThe following slide outlines crucial steps, including strong passwords, firmware updates, encryption, remote management, firewall protection, and data backup, to demonstrate the integration of wireless internet for enhanced data security. Presenting our set of slides with Steps To Integrate Wireless Internet For Data Security. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Backup, Firewall Protection, Disable Remote Management.
-
 Types Of Wireless Internet Security For Data Protection
Types Of Wireless Internet Security For Data ProtectionThe following slide highlights key points such as WEP, WPA, WPA2, and WPA3 protocols to show types of wireless internet security for privacy protection. It helps in understanding and comparing different safety procedures for effective data protection. Introducing our premium set of slides with Types Of Wireless Internet Security For Data Protection. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Protection, Wireless Internet. So download instantly and tailor it with your information.
-
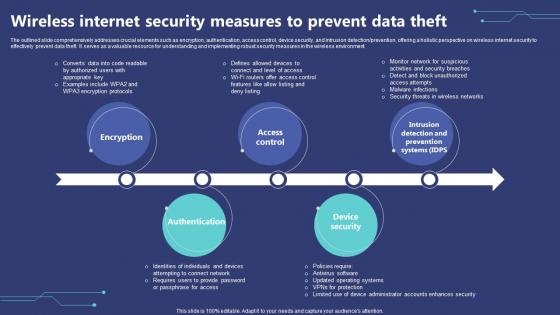 Wireless Internet Security Measures To Prevent Data Theft
Wireless Internet Security Measures To Prevent Data TheftThe outlined slide comprehensively addresses crucial elements such as encryption, authentication, access control, device security, and intrusion detection prevention, offering a holistic perspective on wireless internet security to effectively prevent data theft. It serves as a valuable resource for understanding and implementing robust security measures in the wireless environment. Introducing our premium set of slides with Wireless Internet Security Measures To Prevent Data Theft. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Encryption, Access Control, Intrusion Detection And Prevention Systems. So download instantly and tailor it with your information.
-
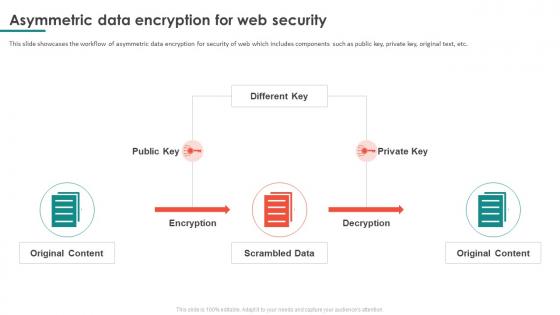 Asymmetric Data Encryption For Web Security
Asymmetric Data Encryption For Web SecurityThis slide showcases the workflow of asymmetric data encryption for security of web which includes components such as public key, private key, original text, etc. Introducing our Asymmetric Data Encryption For Web Security set of slides. The topics discussed in these slides are Asymmetric Data Encryption, Web Security, Private Key, Original Text. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Csirt Cyber Security Icon For Data Safety
Csirt Cyber Security Icon For Data SafetyPresenting our set of slides with Csirt Cyber Security Icon For Data Safety. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Csirt Cyber Security, Data Safety.
-
 Csirt Cyber Security Icon For Protecting Data
Csirt Cyber Security Icon For Protecting DataIntroducing our premium set of slides with Csirt Cyber Security Icon For Protecting Data. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Csirt Cyber Security, Protecting Data. So download instantly and tailor it with your information.
-
 Data Protection Server Security Technology Icon
Data Protection Server Security Technology IconPresenting our set of slides with Data Protection Server Security Technology Icon. This exhibits information on threestages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Protection, Server Security Technology.
-
 Enhance Server Security Through Data Protection Storage Icon
Enhance Server Security Through Data Protection Storage IconPresenting our set of slides with Enhance Server Security Through Data Protection Storage Icon. This exhibits information on fourstages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Server Security, Data Protection Storage.
-
 Virtual Private Cloud Icon Representing Data Security
Virtual Private Cloud Icon Representing Data SecurityPresenting our set of slides with Virtual Private Cloud Icon Representing Data Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Security, Representing, Cloud Icon.
-
 Management Of Redundant Data Understanding Security Risk Related With Dark Data
Management Of Redundant Data Understanding Security Risk Related With Dark DataThis slide focuses on the security risks associated with dark data. Some of the risks associated with dark data include vulnerability to hacking, negative impact on the business, and an increased workload for IT teams, etc. Introducing Management Of Redundant Data Understanding Security Risk Related With Dark Data to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Increased Workload For IT Teams, Negative Impact On Business, Vulnerability To Hacking, using this template. Grab it now to reap its full benefits.



