Powerpoint Templates and Google slides for Data Strategy Timeline
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Data Breach Prevention Strategies For Enterprises Data Breach Prevention And Mitigation
Data Breach Prevention Strategies For Enterprises Data Breach Prevention And MitigationThe purpose of this slide is to outline the data breach mitigation strategies for businesses. These include access control, encryption, web security solutions, network security, up-to-date software and hardware, preparation, training employees and users, etc. Present the topic in a bit more detail with this Data Breach Prevention Strategies For Enterprises Data Breach Prevention And Mitigation. Use it as a tool for discussion and navigation on Network Security, Data Loss Prevention, Regularly Perform Patching Activities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Breach Prevention Strategies For Users Data Breach Prevention And Mitigation
Data Breach Prevention Strategies For Users Data Breach Prevention And MitigationThis slide represents the strategies to protect users from data breaches. These include use unique passwords, two-factor authentication, only submit sensitive data on HTTPS websites, software and hardware updates, encrypt hard drives, etc. Deliver an outstanding presentation on the topic using this Data Breach Prevention Strategies For Users Data Breach Prevention And Mitigation. Dispense information and present a thorough explanation of Unusual Email Attachments, Maintain Software And Hardware, Several Online Services using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Icons Slide For Data Breach Prevention And Mitigation Strategies For Businesses
Icons Slide For Data Breach Prevention And Mitigation Strategies For BusinessesPresenting our well crafted Icons Slide For Data Breach Prevention And Mitigation Strategies For Businesses set of slides. The slides include icons that are innovatively designed by our team of experts. The icons are easy to edit so you can conveniently increase or decrease their size without any loss in resolution. Therefore, grab them instantly.
-
 Table Of Contents For Data Breach Prevention And Mitigation Strategies For Businesses
Table Of Contents For Data Breach Prevention And Mitigation Strategies For BusinessesIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Data Breach Prevention And Mitigation Strategies For Businesses. This template helps you present information on ten stages. You can also present information on Data Breach Prevention Tools, Data Breach Response Plan, Prevention And Mitigation, Training And Budget using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
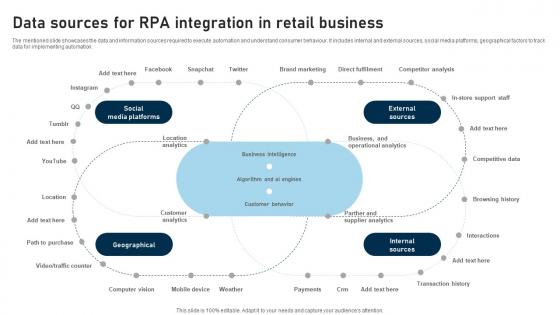 RPA Adoption Strategy Data Sources For RPA Integration In Retail Business
RPA Adoption Strategy Data Sources For RPA Integration In Retail BusinessThis slide showcases the adoption rates of modern technologies among businesses.It incorporates technologies such as AI image, ARVR, big data, blockchain, chatbots, API, IoT, RPA, telematics, wearables, etc. Present the topic in a bit more detail with this RPA Adoption Strategy Data Sources For RPA Integration In Retail Business Use it as a tool for discussion and navigation on Data Sources, Integration In Retail Business This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data AI Artificial Intelligence Sales Solutions To Build Selling Strategy AI SS
Data AI Artificial Intelligence Sales Solutions To Build Selling Strategy AI SSThe slide highlights Data.AI sales solutions for building selling strategies, offering data insights into mobile markets. It helps identify target markets, develop informed sales plans, and analyze trends in app downloads, usage, and revenue for finding top apps. Present the topic in a bit more detail with this Data AI Artificial Intelligence Sales Solutions To Build Selling Strategy AI SS. Use it as a tool for discussion and navigation on Data AI Sales Solutions, Building Selling Strategies, Identify Target Markets, Develop Informed Sales Plans, Analyze Trends In App Downloads. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Agenda For Data Breach Prevention And Mitigation Strategies For Businesses
Agenda For Data Breach Prevention And Mitigation Strategies For BusinessesIntroducing Agenda For Data Breach Prevention And Mitigation Strategies For Businesses to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Data Exploitation Techniques, Data Breach Prevention, Mitigation Strategies For Businesses, using this template. Grab it now to reap its full benefits.
-
 Data Center Consolidation Strategy In Powerpoint And Google Slides Cpb
Data Center Consolidation Strategy In Powerpoint And Google Slides CpbPresenting Data Center Consolidation Strategy In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase Three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Data Center Consolidation Strategy. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
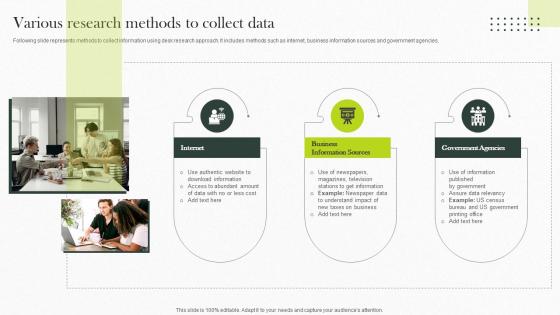 Various Research Methods To Collect Data Implementing Strategies For Business
Various Research Methods To Collect Data Implementing Strategies For BusinessFollowing slide represents methods to collect information using desk research approach. It includes methods such as internet, business information sources and government agencies.Increase audience engagement and knowledge by dispensing information using Various Research Methods To Collect Data Implementing Strategies For Business. This template helps you present information on one stage. You can also present information on Authentic Website, Download Information, Access To Abundant Amount using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
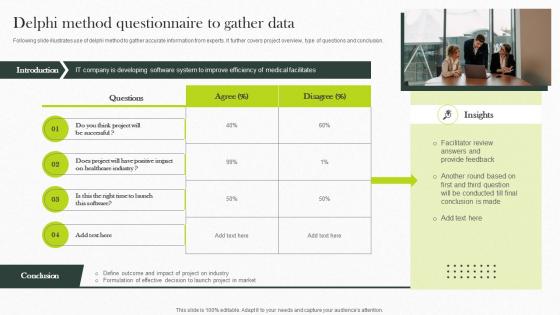 Delphi Method Questionnaire To Gather Data Implementing Strategies For Business
Delphi Method Questionnaire To Gather Data Implementing Strategies For BusinessFollowing slide illustrates use of delphi method to gather accurate information from experts. It further covers project overview, type of questions and conclusion.Increase audience engagement and knowledge by dispensing information using Delphi Method Questionnaire To Gather Data Implementing Strategies For Business. This template helps you present information on four stages. You can also present information on Healthcare Industry, Conclusion Made, Medical Facilitates using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
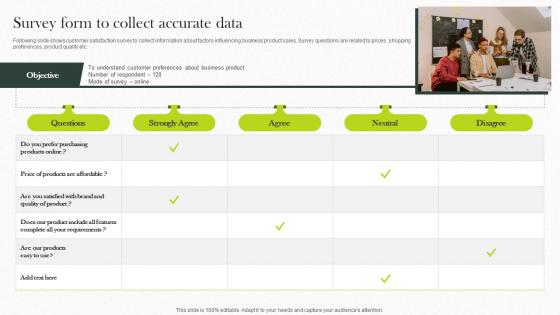 Survey Form To Collect Accurate Data Implementing Strategies For Business
Survey Form To Collect Accurate Data Implementing Strategies For BusinessFollowing slide shows customer satisfaction survey to collect information about factors influencing business product sales. Survey questions are related to prices, shopping preferences, product quality etc.Present the topic in a bit more detail with this Survey Form To Collect Accurate Data Implementing Strategies For Business. Use it as a tool for discussion and navigation on Product Include, Our Products, Strongly Agree . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
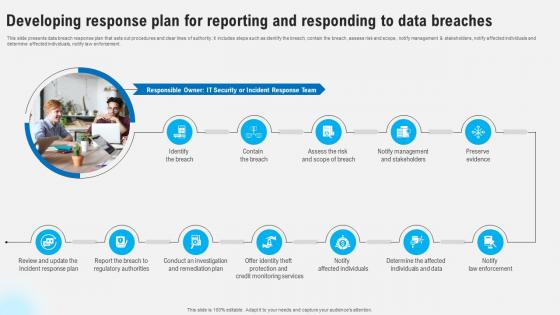 Developing Response Plan For Reporting And Responding To Data Strategies To Comply Strategy SS V
Developing Response Plan For Reporting And Responding To Data Strategies To Comply Strategy SS VThis slide presents data breach response plan that sets out procedures and clear lines of authority. It includes steps such as identify the breach, contain the breach, assess risk and scope , notify management and stakeholders, notify affected individuals and determine affected individuals, notify law enforcement. Introducing Developing Response Plan For Reporting And Responding To Data Strategies To Comply Strategy SS V to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Contain The Breach, Risk And Scope Of Breach, Notify Management And Stakeholders, using this template. Grab it now to reap its full benefits.
-
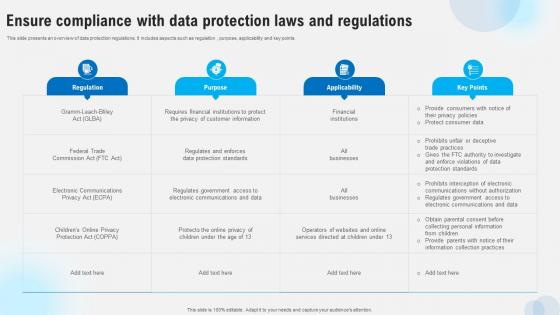 Ensure Compliance With Data Protection Laws And Regulations Strategies To Comply Strategy SS V
Ensure Compliance With Data Protection Laws And Regulations Strategies To Comply Strategy SS VThis slide presents an overview of data protection regulations. It includes aspects such as regulation , purpose, applicability and key points. Present the topic in a bit more detail with this Ensure Compliance With Data Protection Laws And Regulations Strategies To Comply Strategy SS V. Use it as a tool for discussion and navigation on Regulation, Purpose, Applicability. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
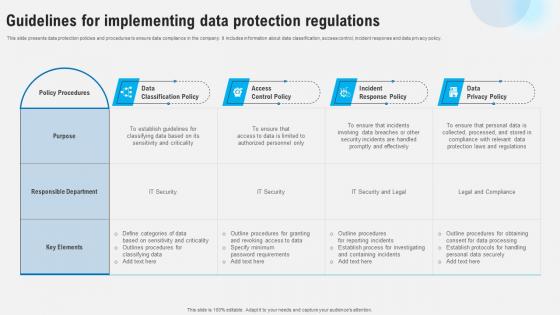 Guidelines For Implementing Data Protection Regulations Strategies To Comply Strategy SS V
Guidelines For Implementing Data Protection Regulations Strategies To Comply Strategy SS VThis slide presents data protection policies and procedures to ensure data compliance in the company. It includes information about data classification, access control, incident response and data privacy policy. Present the topic in a bit more detail with this Guidelines For Implementing Data Protection Regulations Strategies To Comply Strategy SS V. Use it as a tool for discussion and navigation on Data Classification Policy, Access Control Policy, Incident Response Policy. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
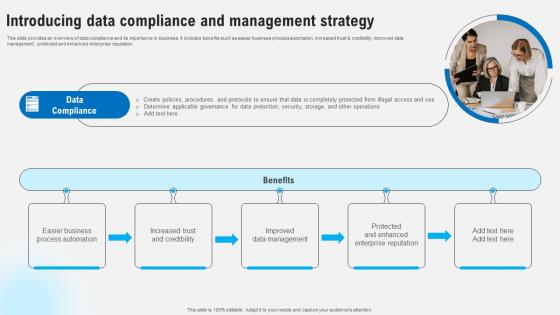 Introducing Data Compliance And Management Strategy Strategies To Comply Strategy SS V
Introducing Data Compliance And Management Strategy Strategies To Comply Strategy SS VThis slide provides an overview of data compliance and its importance in business. It includes benefits such as easier business process automation, increased trust and credibility, improved data management, protected and enhanced enterprise reputation. Increase audience engagement and knowledge by dispensing information using Introducing Data Compliance And Management Strategy Strategies To Comply Strategy SS V. This template helps you present information on one stage. You can also present information on Easier Business Process Automation, Increased Trust And Credibility, Improved Data Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
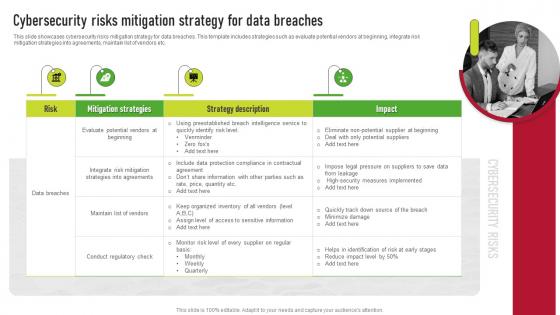 Cybersecurity Risks Mitigation Strategy For Data Breaches Supplier Risk Management
Cybersecurity Risks Mitigation Strategy For Data Breaches Supplier Risk ManagementThis slide showcases cybersecurity risks mitigation strategy for data breaches. This template includes strategies such as evaluate potential vendors at beginning, integrate risk mitigation strategies into agreements, maintain list of vendors etc. Introducing Cybersecurity Risks Mitigation Strategy For Data Breaches Supplier Risk Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Mitigation Strategies, Strategy Description, Risk, using this template. Grab it now to reap its full benefits.
-
 Ensure Compliance With Data Protection Laws Developing Shareholder Trust With Efficient Strategy SS V
Ensure Compliance With Data Protection Laws Developing Shareholder Trust With Efficient Strategy SS VThis slide presents an overview of data protection regulations. It includes aspects such as regulation , purpose, applicability and key points. Introducing Ensure Compliance With Data Protection Laws Developing Shareholder Trust With Efficient Strategy SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Regulation, Purpose, Applicability, using this template. Grab it now to reap its full benefits.
-
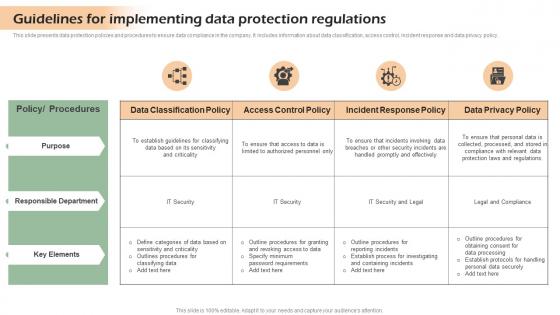 Guidelines For Implementing Data Developing Shareholder Trust With Efficient Strategy SS V
Guidelines For Implementing Data Developing Shareholder Trust With Efficient Strategy SS VThis slide presents data protection policies and procedures to ensure data compliance in the company. It includes information about data classification, access control, incident response and data privacy policy. Deliver an outstanding presentation on the topic using this Guidelines For Implementing Data Developing Shareholder Trust With Efficient Strategy SS V. Dispense information and present a thorough explanation of Responsible, Department, Elements using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
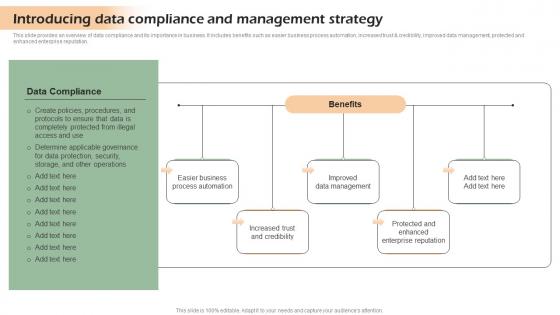 Introducing Data Compliance And Developing Shareholder Trust With Efficient Strategy SS V
Introducing Data Compliance And Developing Shareholder Trust With Efficient Strategy SS VThis slide provides an overview of data compliance and its importance in business. It includes benefits such as easier business process automation, increased trust and credibility, improved data management, protected and enhanced enterprise reputation. Increase audience engagement and knowledge by dispensing information using Introducing Data Compliance And Developing Shareholder Trust With Efficient Strategy SS V. This template helps you present information on five stages. You can also present information on Automation, Credibility, Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
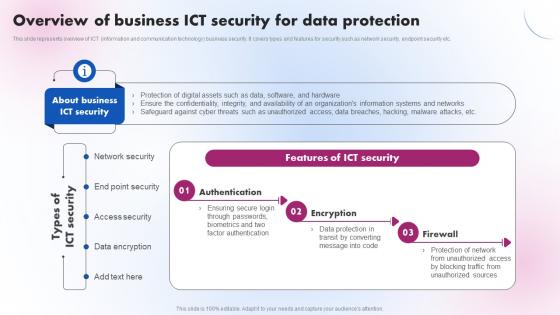 Overview Of Business ICT Security For Data Elivering ICT Services For Enhanced Business Strategy SS V
Overview Of Business ICT Security For Data Elivering ICT Services For Enhanced Business Strategy SS VThis slide represents overview of ICT information and communication technology business security. It covers types and features for security such as network security, endpoint security etc. Increase audience engagement and knowledge by dispensing information using Overview Of Business ICT Security For Data Elivering ICT Services For Enhanced Business Strategy SS V. This template helps you present information on three stages. You can also present information on Authentication, Encryption, Firewall using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
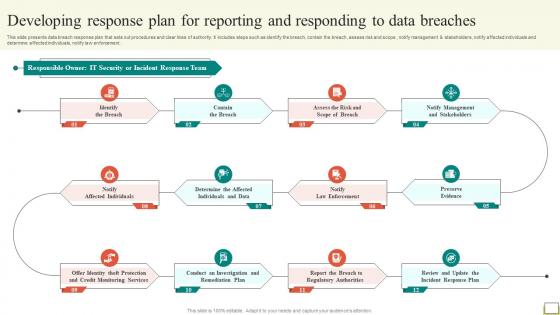 Employee And Workplace Developing Response Plan For Reporting And Responding To Data Strategy SS V
Employee And Workplace Developing Response Plan For Reporting And Responding To Data Strategy SS VThis slide presents data breach response plan that sets out procedures and clear lines of authority. It includes steps such as identify the breach, contain the breach, assess risk and scope , notify management and stakeholders, notify affected individuals and determine affected individuals, notify law enforcement. Increase audience engagement and knowledge by dispensing information using Employee And Workplace Developing Response Plan For Reporting And Responding To Data Strategy SS V This template helps you present information on One stages. You can also present information on Maintaining Product Quality, Certain Standard, Company Activity using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
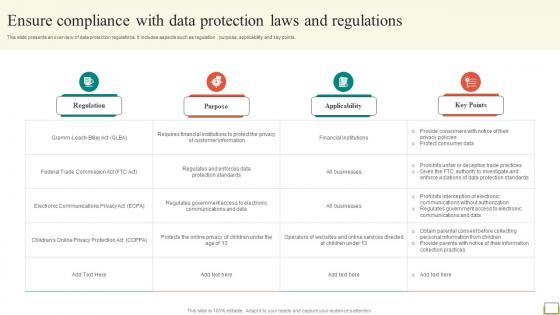 Employee And Workplace Ensure Compliance With Data Protection Laws And Regulations Strategy SS V
Employee And Workplace Ensure Compliance With Data Protection Laws And Regulations Strategy SS VThis slide presents an overview of data protection regulations. It includes aspects such as regulation , purpose, applicability and key points. Deliver an outstanding presentation on the topic using this Employee And Workplace Ensure Compliance With Data Protection Laws And Regulations Strategy SS V Dispense information and present a thorough explanation of Regulatory Requirement, Training Objectives, Training Method using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
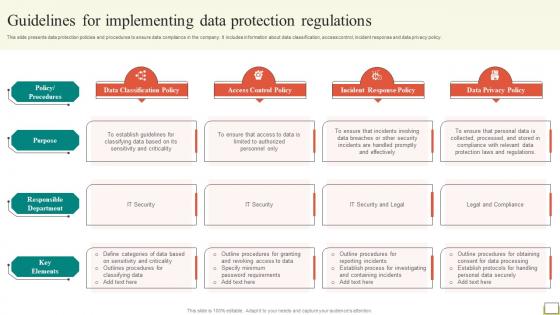 Employee And Workplace Guidelines For Implementing Data Protection Regulations Strategy SS V
Employee And Workplace Guidelines For Implementing Data Protection Regulations Strategy SS VThis slide presents data protection policies and procedures to ensure data compliance in the company. It includes information about data classification, access control, incident response and data privacy policy.Increase audience engagement and knowledge by dispensing information using Employee And Workplace Guidelines For Implementing Data Protection Regulations Strategy SS V This template helps you present information on Four stages. You can also present information on Internal Review, External Audit, Compliance Surveys using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Employee And Workplace Introducing Data Compliance And Management Strategy Strategy SS V
Employee And Workplace Introducing Data Compliance And Management Strategy Strategy SS VThis slide provides an overview of data compliance and its importance in business. It includes benefits such as easier business process automation, increased trust and credibility, improved data management, protected and enhanced enterprise reputation. Increase audience engagement and knowledge by dispensing information using Employee And Workplace Introducing Data Compliance And Management Strategy Strategy SS V This template helps you present information on Four stages. You can also present information on Benefits Organizations, Regulatory Compliance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
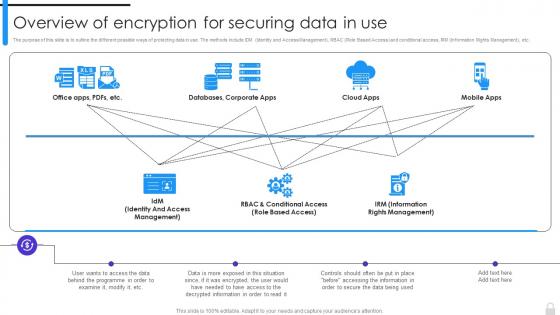 Encryption Implementation Strategies Overview Of Encryption For Securing Data In Use
Encryption Implementation Strategies Overview Of Encryption For Securing Data In UseThe purpose of this slide is to outline the different possible ways of protecting data in use. The methods include IDM Identity and Access Management, RBAC Role Based Access and conditional access, IRM Information Rights Management, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Overview Of Encryption For Securing Data In Use. Dispense information and present a thorough explanation of Information Rights Management, Encryption For Securing Data, Role Based Access using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
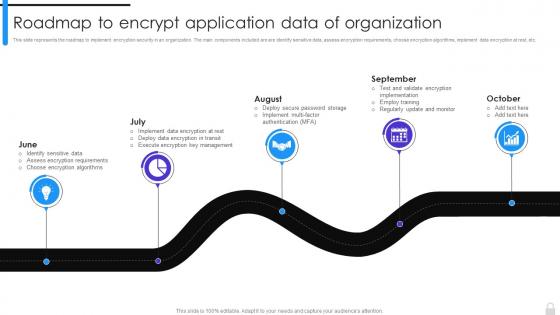 Encryption Implementation Strategies Roadmap To Encrypt Application Data Of Organization
Encryption Implementation Strategies Roadmap To Encrypt Application Data Of OrganizationThis slide represents the roadmap to implement encryption security in an organization. The main components included are are identify sensitive data, assess encryption requirements, choose encryption algorithms, implement data encryption at rest, etc. Introducing Encryption Implementation Strategies Roadmap To Encrypt Application Data Of Organization to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Encryption Security, Identify Sensitive Data, Assess Encryption Requirements, Encryption Algorithms, Implement Data Encryption, using this template. Grab it now to reap its full benefits.
-
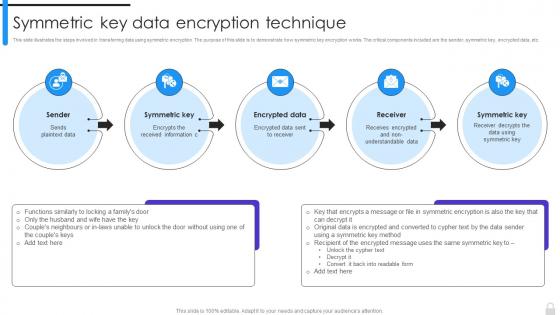 Encryption Implementation Strategies Symmetric Key Data Encryption Technique
Encryption Implementation Strategies Symmetric Key Data Encryption TechniqueThis slide illustrates the steps involved in transferring data using symmetric encryption. The purpose of this slide is to demonstrate how symmetric key encryption works. The critical components included are the sender, symmetric key, encrypted data, etc. Increase audience engagement and knowledge by dispensing information using Encryption Implementation Strategies Symmetric Key Data Encryption Technique. This template helps you present information on five stages. You can also present information on Encrypted Data, Symmetric Key, Data Encryption Technique, Non Understandable Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
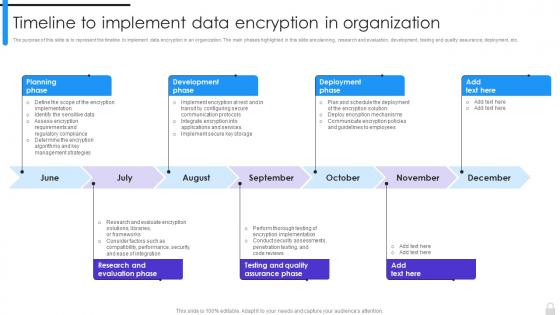 Encryption Implementation Strategies Timeline To Implement Data Encryption In Organization
Encryption Implementation Strategies Timeline To Implement Data Encryption In OrganizationThe purpose of this slide is to represent the timeline to implement data encryption in an organization. The main phases highlighted in this slide are planning, research and evaluation, development, testing and quality assurance, deployment, etc. Introducing Encryption Implementation Strategies Timeline To Implement Data Encryption In Organization to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Development Phase, Testing And Quality Assurance Phase, Research And Evaluation Phase, Planning Phase, using this template. Grab it now to reap its full benefits.
-
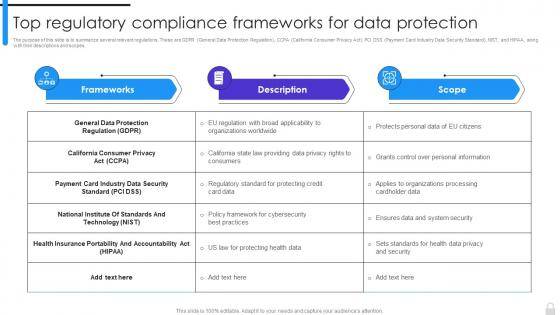 Encryption Implementation Strategies Top Regulatory Compliance Frameworks For Data Protection
Encryption Implementation Strategies Top Regulatory Compliance Frameworks For Data ProtectionThe purpose of this slide is to summarize several relevant regulations. These are GDPR General Data Protection Regulation, CCPA California Consumer Privacy Act, PCI DSS Payment Card Industry Data Security Standard, NIST, and HIPAA, along with their descriptions and scopes. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Top Regulatory Compliance Frameworks For Data Protection. Dispense information and present a thorough explanation of General Data Protection Regulation, California Consumer Privacy Act, Health Insurance Portability And Accountability Act using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
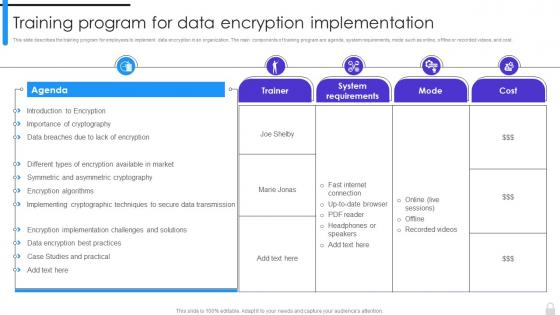 Encryption Implementation Strategies Training Program For Data Encryption Implementation
Encryption Implementation Strategies Training Program For Data Encryption ImplementationThis slide describes the training program for employees to implement data encryption in an organization. The main components of training program are agenda, system requirements, mode such as online, offline or recorded videos, and cost. Present the topic in a bit more detail with this Encryption Implementation Strategies Training Program For Data Encryption Implementation. Use it as a tool for discussion and navigation on Symmetric And Asymmetric Cryptography, Data Encryption Best Practices, Case Studies And Practical, Implementing Cryptographic Techniques. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
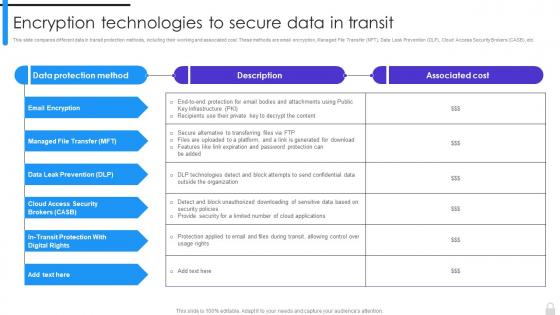 Encryption Technologies To Secure Data In Transit Encryption Implementation Strategies
Encryption Technologies To Secure Data In Transit Encryption Implementation StrategiesThis slide compares different data in transit protection methods, including their working and associated cost. These methods are email encryption, Managed File Transfer MFT, Data Leak Prevention DLP, Cloud Access Security Brokers CASB, etc. Deliver an outstanding presentation on the topic using this Encryption Technologies To Secure Data In Transit Encryption Implementation Strategies. Dispense information and present a thorough explanation of Managed File Transfer, Cloud Access Security Brokers, Email Encryption, Encryption Technologies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
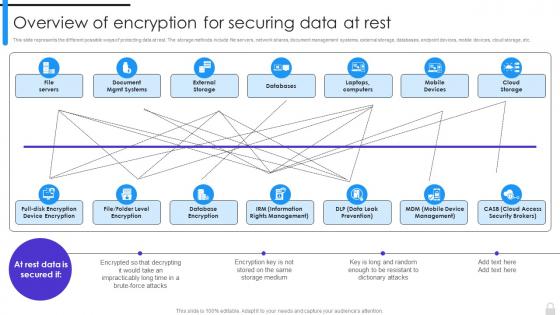 Overview Of Encryption For Securing Data At Rest Encryption Implementation Strategies
Overview Of Encryption For Securing Data At Rest Encryption Implementation StrategiesThis slide represents the different possible ways of protecting data at rest. The storage methods include file servers, network shares, document management systems, external storage, databases, endpoint devices, mobile devices, cloud storage, etc. Present the topic in a bit more detail with this Overview Of Encryption For Securing Data At Rest Encryption Implementation Strategies. Use it as a tool for discussion and navigation on Database Encryption, Information Rights Management, Data Leak Prevention, Mobile Device Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
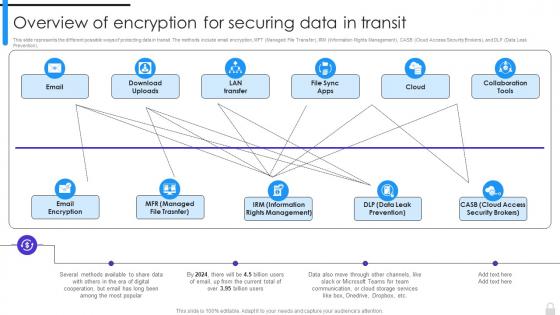 Overview Of Encryption For Securing Data In Transit Encryption Implementation Strategies
Overview Of Encryption For Securing Data In Transit Encryption Implementation StrategiesThis slide represents the different possible ways of protecting data in transit. The methods include email encryption, MFT Managed File Transfer, IRM Information Rights Management, CASB Cloud Access Security Brokers, and DLP Data Leak Prevention. Deliver an outstanding presentation on the topic using this Overview Of Encryption For Securing Data In Transit Encryption Implementation Strategies. Dispense information and present a thorough explanation of Information Rights Management, Data Leak Prevention, Cloud Access Security Brokers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
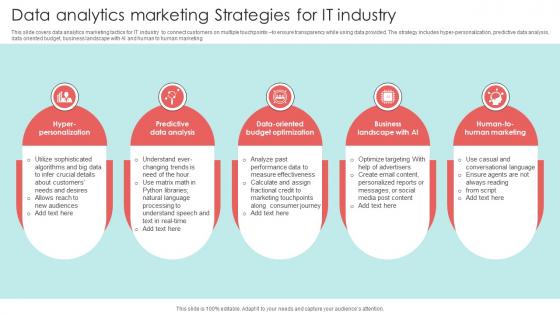 Data Analytics Marketing Strategies For IT Industry
Data Analytics Marketing Strategies For IT IndustryThis slide covers data analytics marketing tactics for IT industry to connect customers on multiple touchpoints to ensure transparency while using data provided. The strategy includes hyper-personalization, predictive data analysis, data oriented budget, business landscape with AI and human to human marketing Presenting our set of slides with Data Analytics Marketing Strategies For IT Industry. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Personalization, Analysis, Budget.
-
 Data Analytics Strategy Icon For IT Industry
Data Analytics Strategy Icon For IT IndustryPresenting our set of slides with Data Analytics Strategy Icon For IT Industry. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Analytics, Industry, Strategy.
-
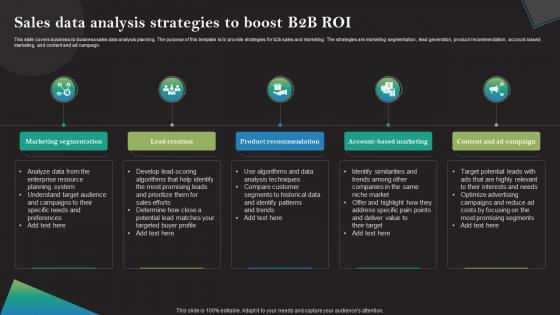 Sales Data Analysis Strategies To Boost B2b Roi
Sales Data Analysis Strategies To Boost B2b RoiThis slide covers business-to-business sales data analysis planning. The purpose of this template is to provide strategies for b2b sales and marketing. The strategies are marketing segmentation, lead generation, product recommendation, account-based marketing, and content and ad campaign. Introducing our premium set of slides with Sales Data Analysis Icon For Strategic Decision Making. Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Marketing Segmentation, Lead Creation, Product Recommendation. So download instantly and tailor it with your information.
-
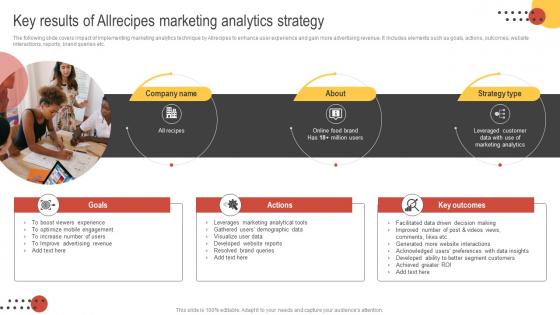 Big Data Marketing Key Results Of Allrecipes Marketing Analytics Strategy MKT SS V
Big Data Marketing Key Results Of Allrecipes Marketing Analytics Strategy MKT SS VThe following slide covers impact of implementing marketing analytics technique by Allrecipes to enhance user experience and gain more advertising revenue. It includes elements such as goals, actions, outcomes, website interactions, reports, brand queries etc. Increase audience engagement and knowledge by dispensing information using Big Data Marketing Key Results Of Allrecipes Marketing Analytics Strategy MKT SS V This template helps you present information on Three stages. You can also present information on Goals, Actions, Strategy Type using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Big Data Marketing Netflix Successful Marketing Analytics Strategy MKT SS V
Big Data Marketing Netflix Successful Marketing Analytics Strategy MKT SS VThe following slide illustrates Netflixs marketing analytics use case to retain customers and deliver better products and services. It includes elements such as goals, actions, outcomes, personalized recommendations, retention rate, strategy type etc. Increase audience engagement and knowledge by dispensing information using Big Data Marketing Netflix Successful Marketing Analytics Strategy MKT SS V This template helps you present information on Three stages. You can also present information on Goals, Actions, Strategy Type using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Exit Strategy Data Processing Investor Funding Elevator Pitch Deck
Exit Strategy Data Processing Investor Funding Elevator Pitch DeckThis slide represents major exit strategy of company. It includes options such as mergers and acquisitions and IPO Initial Public Offer. Introducing Exit Strategy Data Processing Investor Funding Elevator Pitch Deck to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Mergers, Acquisition, Investors, using this template. Grab it now to reap its full benefits.
-
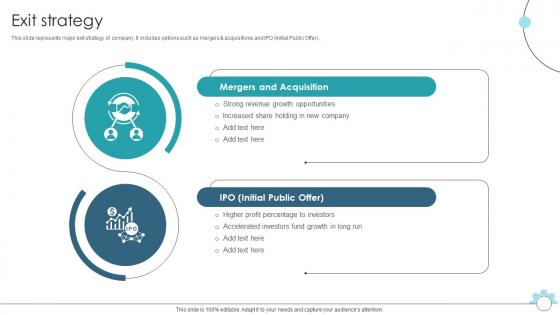 Exit Strategy Data Pipeline Automation Platform Fund Elevator Presentation
Exit Strategy Data Pipeline Automation Platform Fund Elevator PresentationThis slide represents major exit strategy of company. It includes options such as mergers and acquisitions and IPO Initial Public Offer. Introducing Exit Strategy Data Pipeline Automation Platform Fund Elevator Presentation to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Mergers And Acquisition, Initial Public Offer, using this template. Grab it now to reap its full benefits.
-
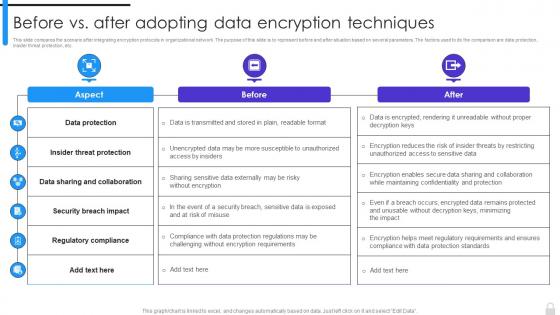 Encryption Implementation Strategies Before Vs After Adopting Data Encryption Techniques
Encryption Implementation Strategies Before Vs After Adopting Data Encryption TechniquesThis slide compares the scenario after integrating encryption protocols in organizational network. The purpose of this slide is to represent before and after situation based on several parameters. The factors used to do the comparison are data protection, insider threat protection, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Before Vs After Adopting Data Encryption Techniques. Use it as a tool for discussion and navigation on Data Protection, Security Breach Impact, Regulatory Compliance, Data Sharing And Collaboration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
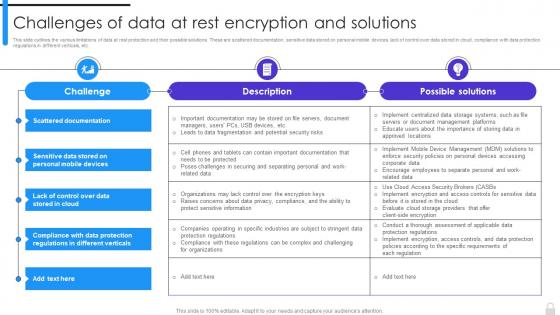 Encryption Implementation Strategies Challenges Of Data At Rest Encryption And Solutions
Encryption Implementation Strategies Challenges Of Data At Rest Encryption And SolutionsThis slide outlines the various limitations of data at rest protection and their possible solutions. These are scattered documentation, sensitive data stored on personal mobile devices, lack of control over data stored in cloud, compliance with data protection regulations in different verticals, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Challenges Of Data At Rest Encryption And Solutions. Use it as a tool for discussion and navigation on Data At Rest Protection, Scattered Documentation, Sensitive Data Stored, Personal Mobile Devices, Data Protection Regulations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
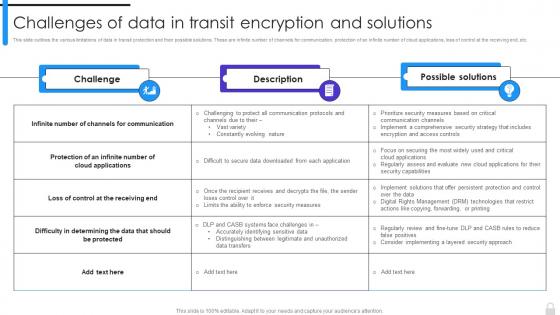 Encryption Implementation Strategies Challenges Of Data In Transit Encryption And Solutions
Encryption Implementation Strategies Challenges Of Data In Transit Encryption And SolutionsThis slide outlines the various limitations of data in transit protection and their possible solutions. These are infinite number of channels for communication, protection of an infinite number of cloud applications, loss of control at the receiving end, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Challenges Of Data In Transit Encryption And Solutions. Dispense information and present a thorough explanation of Data In Transit, Encryption And Solutions, Cloud Applications, Channels For Communication using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
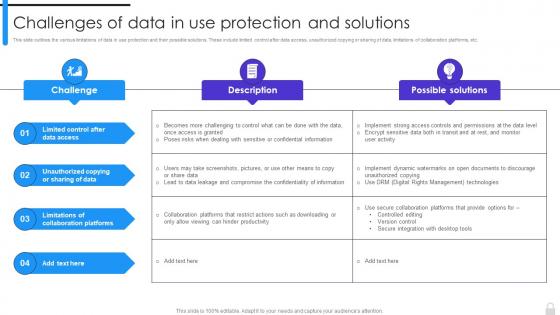 Encryption Implementation Strategies Challenges Of Data In Use Protection And Solutions
Encryption Implementation Strategies Challenges Of Data In Use Protection And SolutionsThis slide outlines the various limitations of data in use protection and their possible solutions. These include limited control after data access, unauthorized copying or sharing of data, limitations of collaboration platforms, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Challenges Of Data In Use Protection And Solutions. Use it as a tool for discussion and navigation on Limitations Of Collaboration Platforms, Unauthorized Copying Or Sharing Of Data, Limited Control After Data Access. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
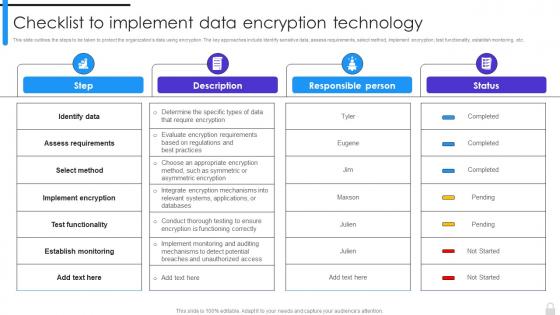 Encryption Implementation Strategies Checklist To Implement Data Encryption Technology
Encryption Implementation Strategies Checklist To Implement Data Encryption TechnologyThis slide outlines the steps to be taken to protect the organizations data using encryption. The key approaches include identify sensitive data, assess requirements, select method, implement encryption, test functionality, establish monitoring, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Checklist To Implement Data Encryption Technology. Dispense information and present a thorough explanation of Assess Requirements, Implement Encryption, Establish Monitoring, Test Functionality using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
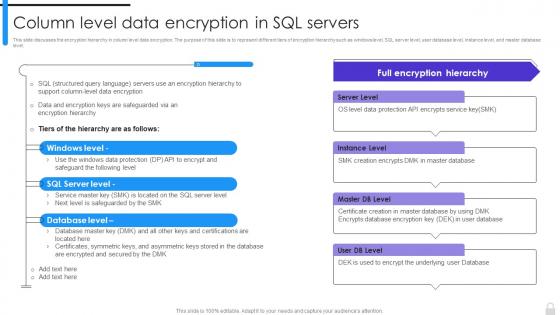 Encryption Implementation Strategies Column Level Data Encryption In SQL Servers
Encryption Implementation Strategies Column Level Data Encryption In SQL ServersThis slide discusses the encryption hierarchy in column level data encryption. The purpose of this slide is to represent different tiers of encryption hierarchy such as windows level, SQL server level, user database level, instance level, and master database level. Present the topic in a bit more detail with this Encryption Implementation Strategies Column Level Data Encryption In SQL Servers. Use it as a tool for discussion and navigation on Encrypts Service Key, Master Database, Encrypts Database Encryption Key. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
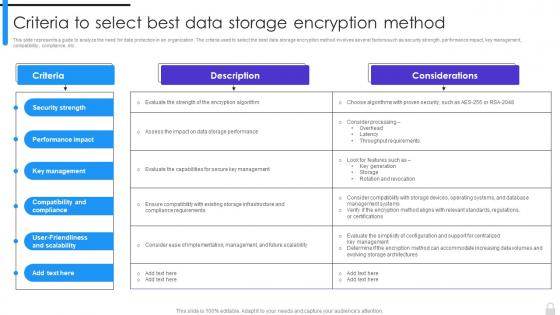 Encryption Implementation Strategies Criteria To Select Best Data Storage Encryption Method
Encryption Implementation Strategies Criteria To Select Best Data Storage Encryption MethodThis slide represents a guide to analyze the need for data protection in an organization. The criteria used to select the best data storage encryption method involves several factors such as security strength, performance impact, key management, compatibility, compliance, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Criteria To Select Best Data Storage Encryption Method. Dispense information and present a thorough explanation of Security Strength, Performance Impact, Key Management, Compatibility And Compliance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
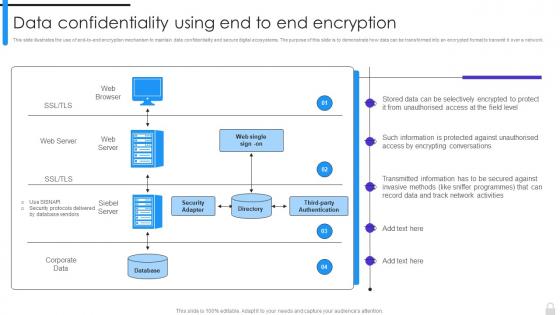 Encryption Implementation Strategies Data Confidentiality Using End To End Encryption
Encryption Implementation Strategies Data Confidentiality Using End To End EncryptionThis slide illustrates the use of end-to-end encryption mechanism to maintain data confidentiality and secure digital ecosystems. The purpose of this slide is to demonstrate how data can be transformed into an encrypted format to transmit it over a network. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Data Confidentiality Using End To End Encryption. Dispense information and present a thorough explanation of Data Confidentiality, Encryption Mechanism, Demonstrate, Digital Ecosystems using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
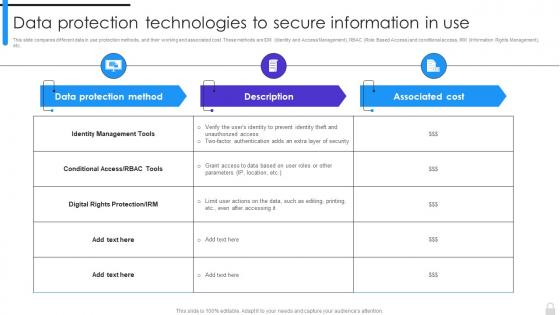 Encryption Implementation Strategies Data Protection Technologies To Secure Information In Use
Encryption Implementation Strategies Data Protection Technologies To Secure Information In UseThis slide compares different data in use protection methods, and their working and associated cost. These methods are IDM Identity and Access Management, RBAC Role Based Access and conditional access, IRM Information Rights Management, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Data Protection Technologies To Secure Information In Use. Use it as a tool for discussion and navigation on Identity Management Tools, Digital Rights Protection, Data Protection Technologies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
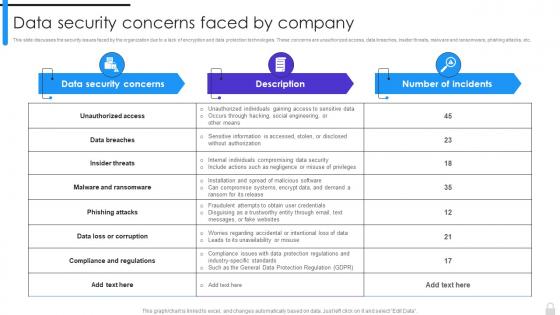 Encryption Implementation Strategies Data Security Concerns Faced By Company
Encryption Implementation Strategies Data Security Concerns Faced By CompanyThis slide discusses the security issues faced by the organization due to a lack of encryption and data protection technologies. These concerns are unauthorized access, data breaches, insider threats, malware and ransomware, phishing attacks, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Data Security Concerns Faced By Company. Dispense information and present a thorough explanation of Data Security Concerns, Phishing Attacks, Data Protection Technologies, Compliance And Regulations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
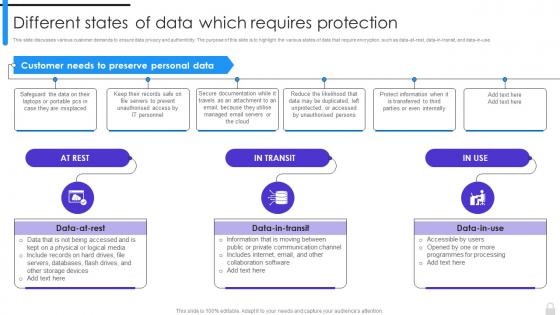 Encryption Implementation Strategies Different States Of Data Which Requires Protection
Encryption Implementation Strategies Different States Of Data Which Requires ProtectionThis slide discusses various customer demands to ensure data privacy and authenticity. The purpose of this slide is to highlight the various states of data that require encryption, such as data-at-rest, data-in-transit, and data-in-use. Introducing Encryption Implementation Strategies Different States Of Data Which Requires Protection to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Customer Demands, Data Privacy And Authenticity, Require Encryption, Collaboration Software, using this template. Grab it now to reap its full benefits.
-
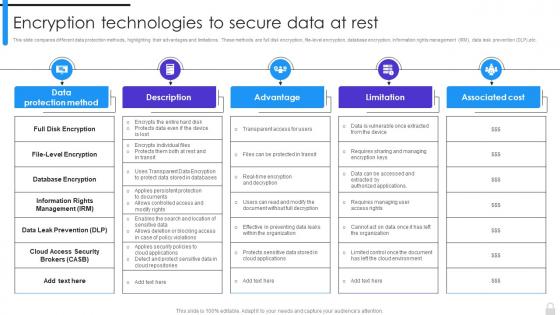 Encryption Implementation Strategies Encryption Technologies To Secure Data At Rest
Encryption Implementation Strategies Encryption Technologies To Secure Data At RestThis slide compares different data protection methods, highlighting their advantages and limitations. These methods are full disk encryption, file-level encryption, database encryption, information rights management IRM, data leak prevention DLP,etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Encryption Technologies To Secure Data At Rest. Dispense information and present a thorough explanation of Information Rights Management, Data Leak Prevention, Full Disk Encryption, Cloud Access Security Brokers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
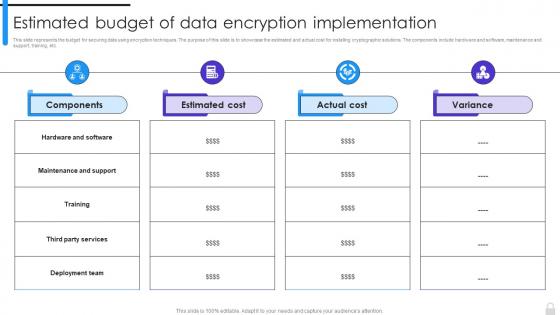 Encryption Implementation Strategies Estimated Budget Of Data Encryption Implementation
Encryption Implementation Strategies Estimated Budget Of Data Encryption ImplementationThis slide represents the budget for securing data using encryption techniques. The purpose of this slide is to showcase the estimated and actual cost for installing cryptographic solutions. The components include hardware and software, maintenance and support, training, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Estimated Budget Of Data Encryption Implementation. Use it as a tool for discussion and navigation on Maintenance And Support, Deployment Team, Data Encryption, Estimated Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
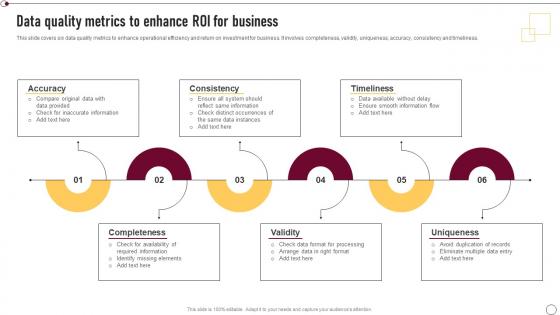 Supplier Quality Management Data Quality Metrics To Enhance Roi For Business Strategy SS V
Supplier Quality Management Data Quality Metrics To Enhance Roi For Business Strategy SS VThis slide covers six data quality metrics to enhance operational efficiency and return on investment for business. It involves completeness, validity, uniqueness, accuracy, consistency and timeliness. Introducing Supplier Quality Management Data Quality Metrics To Enhance Roi For Business Strategy SS V to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Accuracy, Consistency, Timeliness, Completeness, Uniqueness, using this template. Grab it now to reap its full benefits.
-
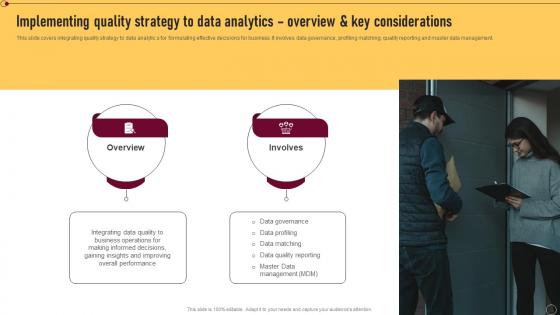 Supplier Quality Management Implementing Quality Strategy To Data Analytics Overview Strategy SS V
Supplier Quality Management Implementing Quality Strategy To Data Analytics Overview Strategy SS VThis slide covers integrating quality strategy to data analytic s for formulating effective decisions for business. It involves data governance, profiling matching, quality reporting and master data management. Introducing Supplier Quality Management Implementing Quality Strategy To Data Analytics Overview Strategy SS V to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Data Governance, Data Profiling, Data Matching, Data Quality Reporting, using this template. Grab it now to reap its full benefits.
-
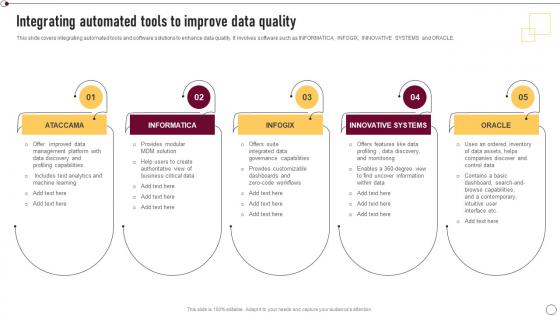 Supplier Quality Management Integrating Automated Tools To Improve Data Quality Strategy SS V
Supplier Quality Management Integrating Automated Tools To Improve Data Quality Strategy SS VThis Slide Covers Integrating Automated Tools And Software Solutions To Enhance Data Quality. It Involves Software Such As Informatica, Infogix, Innovative Systems And Oracle. Increase audience engagement and knowledge by dispensing information using Supplier Quality Management Integrating Automated Tools To Improve Data Quality Strategy SS V. This template helps you present information on five stages. You can also present information on Integrating Automated Tools, Data Quality, Innovative Systems, Zero Code Workflows using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
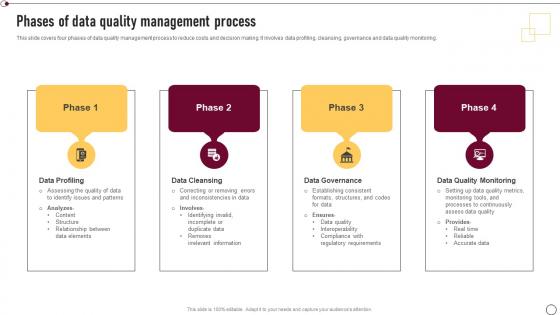 Supplier Quality Management Phases Of Data Quality Management Process Strategy SS V
Supplier Quality Management Phases Of Data Quality Management Process Strategy SS VThis slide covers four phases of data quality management process to reduce costs and decision making. It involves data profiling, cleansing, governance and data quality monitoring. Introducing Supplier Quality Management Phases Of Data Quality Management Process Strategy SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Data Profiling, Data Cleansing, Data Governance, Data Quality Monitoring, using this template. Grab it now to reap its full benefits.
-
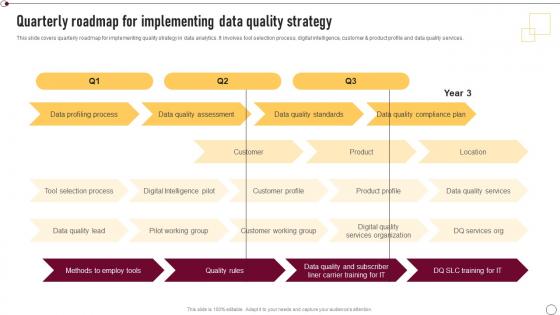 Supplier Quality Management Quarterly Roadmap For Implementing Data Quality Strategy SS V
Supplier Quality Management Quarterly Roadmap For Implementing Data Quality Strategy SS VThis slide covers quarterly roadmap for implementing quality strategy in data analytics. It involves tool selection process, digital intelligence, customer and product profile and data quality services. Deliver an outstanding presentation on the topic using this Supplier Quality Management Quarterly Roadmap For Implementing Data Quality Strategy SS V. Dispense information and present a thorough explanation of Digital Intelligence Pilot, Customer Working Group, Data Quality Services, Tool Selection Process using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
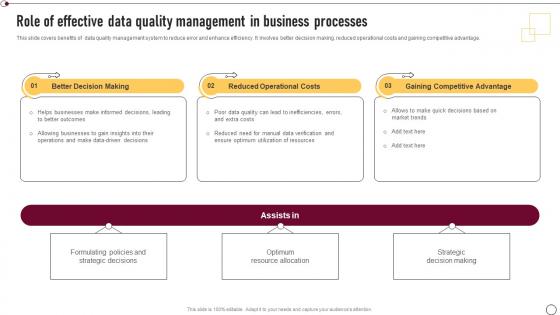 Supplier Quality Management Role Of Effective Data Quality Management In Business Strategy SS V
Supplier Quality Management Role Of Effective Data Quality Management In Business Strategy SS VThis slide covers benefits of data quality management system to reduce error and enhance efficiency. It involves better decision making, reduced operational costs and gaining competitive advantage. Increase audience engagement and knowledge by dispensing information using Supplier Quality Management Role Of Effective Data Quality Management In Business Strategy SS V. This template helps you present information on three stages. You can also present information on Better Decision Making, Reduced Operational Costs, Gaining Competitive Advantage, Optimum Resource Allocation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Supplier Quality Management Selection Of Most Suitable Data Quality Management Strategy SS V
Supplier Quality Management Selection Of Most Suitable Data Quality Management Strategy SS VThis slide covers cost comparison of data quality management tools for selecting most suitable one. It involves key features such as recruitment, performance tracking, centralized employee data management and employee onboarding. Present the topic in a bit more detail with this Supplier Quality Management Selection Of Most Suitable Data Quality Management Strategy SS V. Use it as a tool for discussion and navigation on Cost Comparison, Data Quality Management Tools, Recruitment, Performance Tracking. This template is free to edit as deemed fit for your organization. Therefore download it now.



