Powerpoint Templates and Google slides for Digital Threat Icon
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Cyber Threats Management To Enable Digital Assets Security Powerpoint Ppt Template Bundles DK MD
Cyber Threats Management To Enable Digital Assets Security Powerpoint Ppt Template Bundles DK MDIf you require a professional template with great design, then this Cyber Threats Management To Enable Digital Assets Security Powerpoint Ppt Template Bundles DK MD is an ideal fit for you. Deploy it to enthrall your audience and increase your presentation threshold with the right graphics, images, and structure. Portray your ideas and vision using twenty one slides included in this complete deck. This template is suitable for expert discussion meetings presenting your views on the topic. With a variety of slides having the same thematic representation, this template can be regarded as a complete package. It employs some of the best design practices, so everything is well-structured. Not only this, it responds to all your needs and requirements by quickly adapting itself to the changes you make. This PPT slideshow is available for immediate download in PNG, JPG, and PDF formats, further enhancing its usability. Grab it by clicking the download button.
-
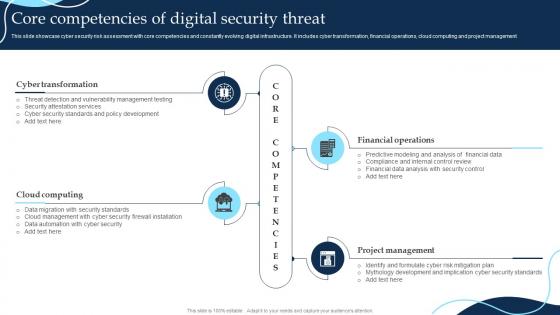 Core Competencies Of Digital Security Threat
Core Competencies Of Digital Security ThreatThis slide showcase cyber security risk assessment with core competencies and constantly evolving digital infrastructure. It includes cyber transformation, financial operations, cloud computing and project management Introducing our premium set of slides with Core Competencies Of Digital Security Threat. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Development, Security, Mythology. So download instantly and tailor it with your information.
-
 Cyber Threat Intelligence Icon To Detect Digital Attacks
Cyber Threat Intelligence Icon To Detect Digital AttacksIntroducing our premium set of slides with Cyber Threat Intelligence Icon To Detect Digital Attacks Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Threat Intelligence Icon, Detect Digital Attacks So download instantly and tailor it with your information.
-
 SWOT Analysis Threats Digital Restaurant Reservation Company Profile CP SS V
SWOT Analysis Threats Digital Restaurant Reservation Company Profile CP SS VMentioned slide provides information about threats faced by company. It includes threats such as competitors, technological disruption, and regulatory changes. Increase audience engagement and knowledge by dispensing information using SWOT Analysis Threats Digital Restaurant Reservation Company Profile CP SS V This template helps you present information on three stages. You can also present information on Technology Disruptions, Competition, Regulatory Changes using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
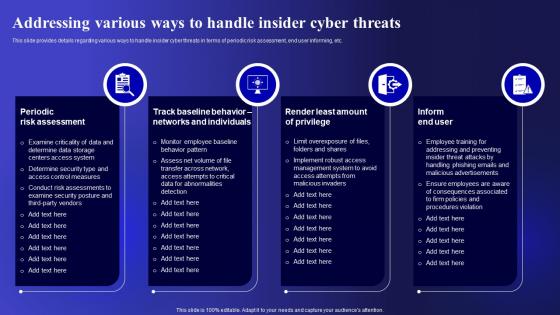 Addressing Various Ways To Handle Cyber Threats Management To Enable Digital Assets Security
Addressing Various Ways To Handle Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding various ways to handle insider cyber threats in terms of periodic risk assessment, end user informing, etc. Present the topic in a bit more detail with this Addressing Various Ways To Handle Cyber Threats Management To Enable Digital Assets Security. Use it as a tool for discussion and navigation on Periodic Risk Assessment, Individuals, Implement. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
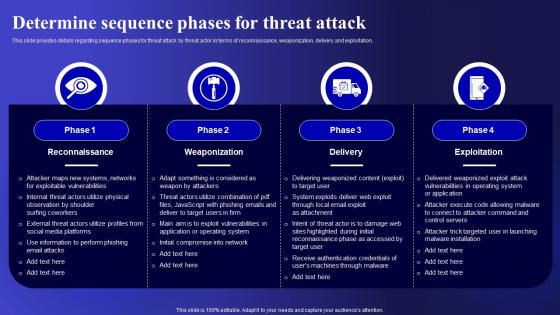 Determine Sequence Phases For Cyber Threats Management To Enable Digital Assets Security
Determine Sequence Phases For Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding sequence phases for threat attack by threat actor in terms of reconnaissance, weaponization, delivery and exploitation. Deliver an outstanding presentation on the topic using this Determine Sequence Phases For Cyber Threats Management To Enable Digital Assets Security. Dispense information and present a thorough explanation of Reconnaissance, Weaponization, Exploitation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Digital Risk Management Dashboard For Tracking Threats And Attacks
Digital Risk Management Dashboard For Tracking Threats And AttacksThe purpose of this slide is to represent dashboard to monitor risks and cyber threats for efficient risk management. It includes various types of key performance indicators such as types of risks, severities, sources and risk meter. Introducing our Digital Risk Management Dashboard For Tracking Threats And Attacks set of slides. The topics discussed in these slides are Severities, Types Of Risk This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
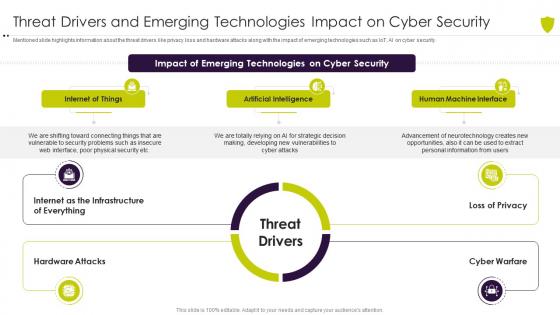 Threat drivers and emerging managing cyber risk in a digital age
Threat drivers and emerging managing cyber risk in a digital ageMentioned slide highlights information about the threat drivers like privacy loss and hardware attacks along with the impact of emerging technologies such as IoT, AI on cyber security. Introducing Threat Drivers And Emerging Managing Cyber Risk In A Digital Age to increase your presentation threshold. Encompassed with threee stages, this template is a great option to educate and entice your audience. Dispence information on Internet Of Things, Artificial Intelligence, Human Machine Interface, using this template. Grab it now to reap its full benefits.
-
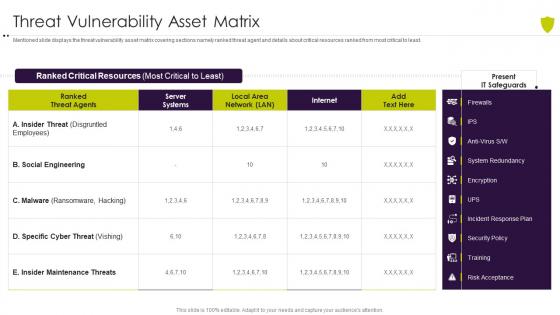 Threat vulnerability asset matrix managing cyber risk in a digital age
Threat vulnerability asset matrix managing cyber risk in a digital ageMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least. Present the topic in a bit more detail with this Threat Vulnerability Asset Matrix Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Threat Vulnerability Asset Matrix. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Digital Transformation In A Banking Financial Analysis Threats Related To The Banking Company
Digital Transformation In A Banking Financial Analysis Threats Related To The Banking CompanyThis slides shows the various threats related to the banking company which includes legal and political framework, high competition, etc. Introducing Digital Transformation In A Banking Financial Analysis Threats Related To The Banking Company to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Political Framework, High Competition, Developing Economies, using this template. Grab it now to reap its full benefits.
-
 Vulnerability Administration At Workplace Different Kinds Of Insider Digital Threats
Vulnerability Administration At Workplace Different Kinds Of Insider Digital ThreatsThis slide provides details regarding various kinds of insider digital threats such as malicious insider, negligent insider, third party insider, etc. Deliver an outstanding presentation on the topic using this Vulnerability Administration At Workplace Different Kinds Of Insider Digital Threats. Dispense information and present a thorough explanation of Malicious Insider, Compromised, Third Party Insiderusing the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
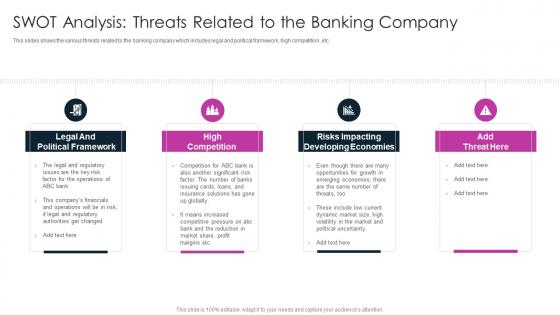 SWOT Analysis Threats Related To The Banking Company Digitalization In Retail Banking Company
SWOT Analysis Threats Related To The Banking Company Digitalization In Retail Banking CompanyThis slides shows the various threats related to the banking company which includes legal and political framework, high competition, etc.Increase audience engagement and knowledge by dispensing information using SWOT Analysis Threats Related To The Banking Company Digitalization In Retail Banking Company This template helps you present information on four stages. You can also present information on Legal And Political Framework, High Competition, Risks Impacting Developing Economies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
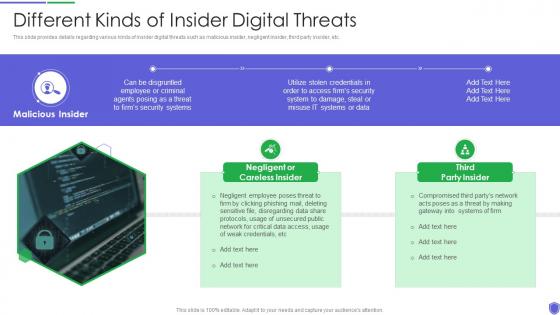 Different kinds of insider digital managing critical threat vulnerabilities and security threats
Different kinds of insider digital managing critical threat vulnerabilities and security threatsThis slide provides details regarding various kinds of insider digital threats such as malicious insider, negligent insider, third party insider, etc. Introducing Different Kinds Of Insider Digital Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Third Party Insider, Malicious Insider, using this template. Grab it now to reap its full benefits.
-
 Different kinds of insider digital threats corporate security management
Different kinds of insider digital threats corporate security managementThis slide provides details regarding various kinds of insider digital threats such as malicious insider, negligent insider, third party insider, etc. Introducing Different Kinds Of Insider Digital Threats Corporate Security Management to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Malicious Insider, Negligent Or Careless Insider, Third Party Insider, using this template. Grab it now to reap its full benefits.
-
 Threat management for organization critical different kinds of insider digital threats
Threat management for organization critical different kinds of insider digital threatsThis slide provides details regarding various kinds of insider digital threats such as malicious insider, negligent insider, third party insider, etc. Introducing Threat Management For Organization Critical Different Kinds Of Insider Digital Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Malicious Insider, Negligent Or Careless Insider, Compromised Third, using this template. Grab it now to reap its full benefits.
-
 Cyber security risk management different kinds of insider digital threats
Cyber security risk management different kinds of insider digital threatsThis slide provides details regarding various kinds of insider digital threats such as malicious insider, negligent insider, third party insider, etc. Introducing Cyber Security Risk Management Different Kinds Of Insider Digital Threats to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Malicious Insider, Negligent Or Careless Insider, Third Party Insider, using this template. Grab it now to reap its full benefits.
-
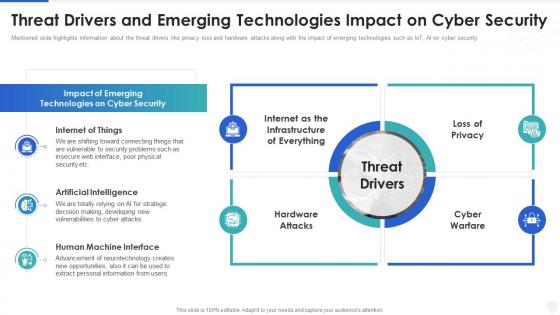 Cybersecurity and digital business risk management threat drivers and emerging technologies
Cybersecurity and digital business risk management threat drivers and emerging technologiesMentioned slide highlights information about the threat drivers like privacy loss and hardware attacks along with the impact of emerging technologies such as IoT, AI on cyber security. Deliver an outstanding presentation on the topic using this Cybersecurity And Digital Business Risk Management Threat Drivers And Emerging Technologies. Dispense information and present a thorough explanation of Internet Of Things, Artificial Intelligence, Human Machine Interface using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
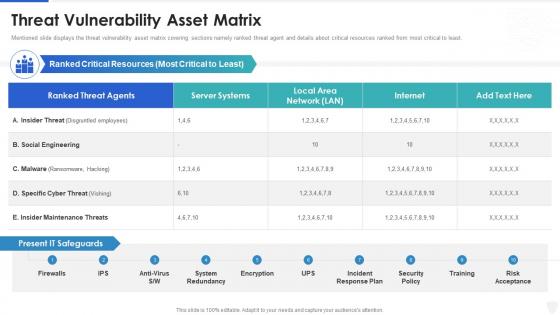 Cybersecurity and digital business risk management threat vulnerability asset matrix
Cybersecurity and digital business risk management threat vulnerability asset matrixMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least. Deliver an outstanding presentation on the topic using this Cybersecurity And Digital Business Risk Management Threat Vulnerability Asset Matrix. Dispense information and present a thorough explanation of Threat Vulnerability Asset Matrix using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
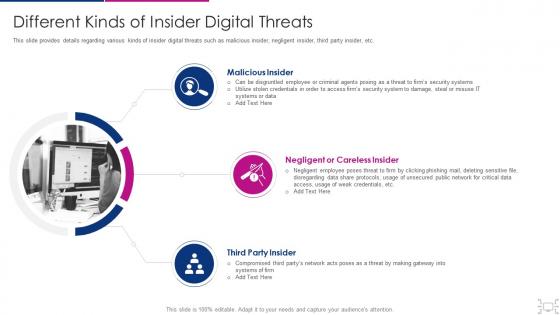 Cyber threat management workplace different kinds of insider digital threats
Cyber threat management workplace different kinds of insider digital threatsThis slide provides details regarding various kinds of insider digital threats such as malicious insider, negligent insider, third party insider, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threat Management Workplace Different Kinds Of Insider Digital Threats. This template helps you present information on three stages. You can also present information on Malicious Insider, Negligent Or Careless Insider, Third Party Insider using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Checklist For Digital Safety Threat And Risk Assessment
Checklist For Digital Safety Threat And Risk AssessmentThis slide represents digital safety threat and assessment checklist which ensure risk management in cost effective manner. It provides information regarding conducting assessment, perform threat analysis, risk mitigation and process completion. Introducing our Checklist For Digital Safety Threat And Risk Assessment set of slides. The topics discussed in these slides are Conduct Assessment, Perform Threat Analysis, Result And Completion. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
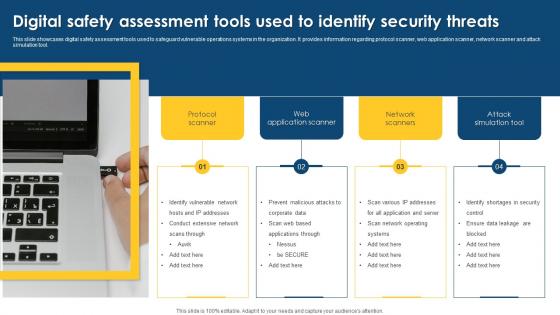 Digital Safety Assessment Tools Used To Identify Security Threats
Digital Safety Assessment Tools Used To Identify Security ThreatsThis slide showcases digital safety assessment tools used to safeguard vulnerable operations systems in the organization. It provides information regarding protocol scanner, web application scanner, network scanner and attack simulation tool. Presenting our well structured Digital Safety Assessment Tools Used To Identify Security Threats. The topics discussed in this slide are Assessment, Application, Identify Vulnerable. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
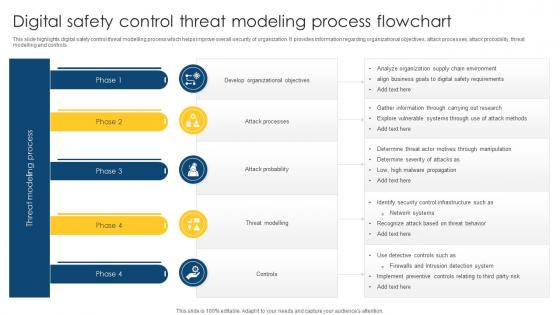 Digital Safety Control Threat Modeling Process Flowchart
Digital Safety Control Threat Modeling Process FlowchartThis slide highlights digital safety control threat modelling process which helps improve overall security of organization. It provides information regarding organizational objectives, attack processes, attack probability, threat modelling and controls. Introducing our Digital Safety Control Threat Modeling Process Flowchart set of slides. The topics discussed in these slides are Process, Flowchart, Attack Probability. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Digital Safety Threat And Risk Assessment Matrix
Digital Safety Threat And Risk Assessment MatrixThis slide showcases digital safety risk assessment matrix which helps analyze impact of threat on business processes. It provides information regarding hacking, data breaches, information misuse, malicious attacks and system failure. Introducing our Digital Safety Threat And Risk Assessment Matrix set of slides. The topics discussed in these slides are Information Misuse, Malicious Attacks, Assessment Matrix. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Major Types Of E Banking Security Threats Digital Banking System To Optimize Financial
Major Types Of E Banking Security Threats Digital Banking System To Optimize FinancialThis slide represents types of e banking security threats. It includes brute force, phishing, pharming, cross site scripting and trojan horse. Present the topic in a bit more detail with this Major Types Of E Banking Security Threats Digital Banking System To Optimize Financial. Use it as a tool for discussion and navigation on Phishing, Pharming, Security Threats, Software For Protection . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
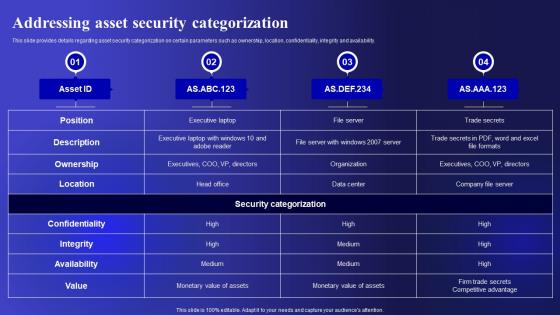 Addressing Asset Security Categorization Cyber Threats Management To Enable Digital Assets Security
Addressing Asset Security Categorization Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding asset security categorization on certain parameters such as ownership, location, confidentiality, integrity and availability. Present the topic in a bit more detail with this Addressing Asset Security Categorization Cyber Threats Management To Enable Digital Assets Security. Use it as a tool for discussion and navigation on Categorization, Confidentiality, Availability. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Addressing Cyber Threats In Various Cyber Threats Management To Enable Digital Assets Security
Addressing Cyber Threats In Various Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding insider threats identified in various industries such as healthcare, manufacturing, government, energy, etc. Deliver an outstanding presentation on the topic using this Addressing Cyber Threats In Various Cyber Threats Management To Enable Digital Assets Security. Dispense information and present a thorough explanation of Manufacturing, Government, Healthcare using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Addressing Indicators Associated Cyber Threats Management To Enable Digital Assets Security
Addressing Indicators Associated Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding indicators associated to insider threats in terms of traits, demeanor and goals, etc. Present the topic in a bit more detail with this Addressing Indicators Associated Cyber Threats Management To Enable Digital Assets Security. Use it as a tool for discussion and navigation on Unauthorized, Business, Authentication. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
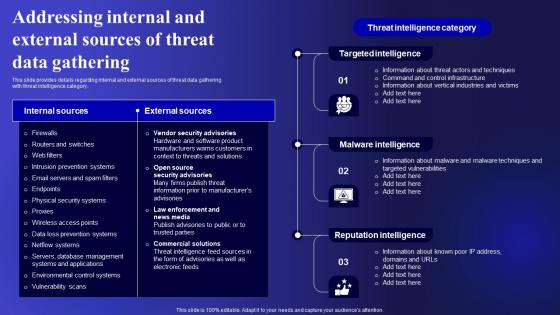 Addressing Internal And External Sources Cyber Threats Management To Enable Digital Assets Security
Addressing Internal And External Sources Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding internal and external sources of threat data gathering with threat intelligence category. Deliver an outstanding presentation on the topic using this Addressing Internal And External Sources Cyber Threats Management To Enable Digital Assets Security. Dispense information and present a thorough explanation of Targeted Intelligence, Malware Intelligence, Reputation Intelligence using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
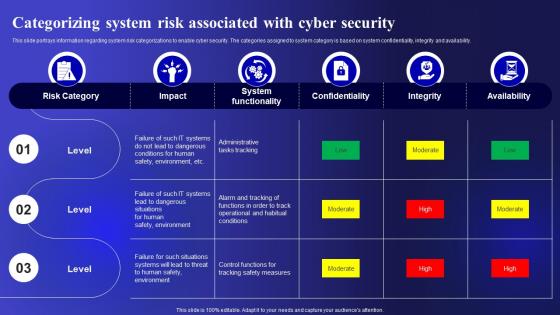 Categorizing System Risk Associated With Cyber Threats Management To Enable Digital Assets Security
Categorizing System Risk Associated With Cyber Threats Management To Enable Digital Assets SecurityThis slide portrays information regarding system risk categorizations to enable cyber security. The categories assigned to system category is based on system confidentiality, integrity and availability. Deliver an outstanding presentation on the topic using this Categorizing System Risk Associated With Cyber Threats Management To Enable Digital Assets Security. Dispense information and present a thorough explanation of Categorizing, Confidentiality, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
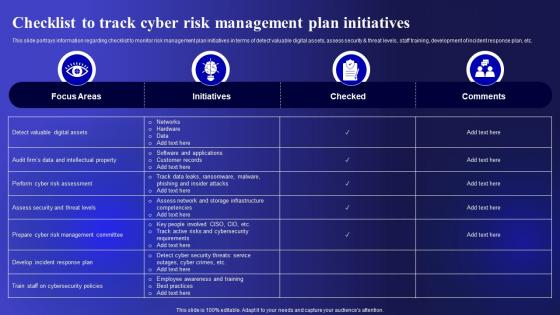 Checklist To Track Cyber Risk Management Cyber Threats Management To Enable Digital Assets Security
Checklist To Track Cyber Risk Management Cyber Threats Management To Enable Digital Assets SecurityThis slide portrays information regarding checklist to monitor risk management plan initiatives in terms of detect valuable digital assets, assess security and threat levels, staff training, development of incident response plan, etc. Present the topic in a bit more detail with this Checklist To Track Cyber Risk Management Cyber Threats Management To Enable Digital Assets Security. Use it as a tool for discussion and navigation on Management, Initiatives, Development. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
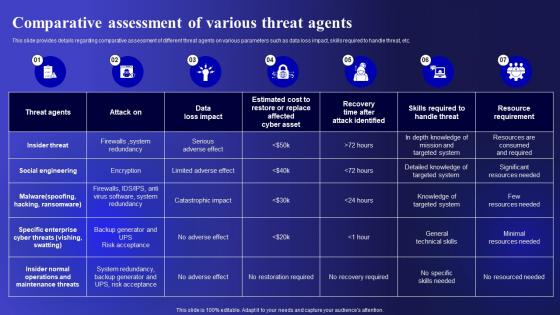 Comparative Assessment Of Various Cyber Threats Management To Enable Digital Assets Security
Comparative Assessment Of Various Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding comparative assessment of different threat agents on various parameters such as data loss impact, skills required to handle threat, etc. Deliver an outstanding presentation on the topic using this Comparative Assessment Of Various Cyber Threats Management To Enable Digital Assets Security. Dispense information and present a thorough explanation of Comparative, Assessment, Parameters using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Contingency Plan For Cyber Threat Cyber Threats Management To Enable Digital Assets Security
Contingency Plan For Cyber Threat Cyber Threats Management To Enable Digital Assets SecurityThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Present the topic in a bit more detail with this Contingency Plan For Cyber Threat Cyber Threats Management To Enable Digital Assets Security. Use it as a tool for discussion and navigation on Contingency Solutions, Contingency Considerations, Information . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
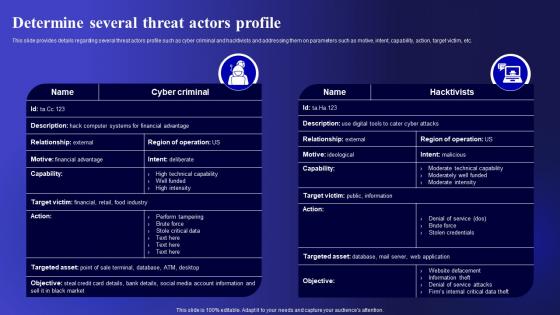 Determine Several Threat Actors Profile Cyber Threats Management To Enable Digital Assets Security
Determine Several Threat Actors Profile Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding several threat actors profile such as cyber criminal and hacktivists and addressing them on parameters such as motive, intent, capability, action, target victim, etc. Present the topic in a bit more detail with this Determine Several Threat Actors Profile Cyber Threats Management To Enable Digital Assets Security. Use it as a tool for discussion and navigation on Parameters, Capability, Determine . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Determine Threat Scenario Analysis Cyber Threats Management To Enable Digital Assets Security
Determine Threat Scenario Analysis Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding threat scenario assessment by understanding various phases of threat actor attack on victim. Deliver an outstanding presentation on the topic using this Determine Threat Scenario Analysis Cyber Threats Management To Enable Digital Assets Security. Dispense information and present a thorough explanation of Reconnaissance, Weaponization, Installation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Different Kinds Of Insider Digital Threats Cyber Threats Management To Enable Digital Assets Security
Different Kinds Of Insider Digital Threats Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding various kinds of insider digital threats such as malicious insider, negligent insider, third party insider, etc. Present the topic in a bit more detail with this Different Kinds Of Insider Digital Threats Cyber Threats Management To Enable Digital Assets Security. Use it as a tool for discussion and navigation on Malicious Insider, Negligent Or Careless Insider, Third Party Insider . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Ensuring Collaboration Among Various Cyber Threats Management To Enable Digital Assets Security
Ensuring Collaboration Among Various Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding ensuring collaboration among various functional areas in order to minimize insider cyber threats. Introducing Ensuring Collaboration Among Various Cyber Threats Management To Enable Digital Assets Security to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Finance, Corporate Security, Business Division, using this template. Grab it now to reap its full benefits.
-
 Key Activities Checklist Associated To Insider Cyber Threats Management To Enable Digital Assets Security
Key Activities Checklist Associated To Insider Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding checklist associated to insider threat program in terms of plan and collect, review and analyze and strategic framework development. Increase audience engagement and knowledge by dispensing information using Key Activities Checklist Associated To Insider Cyber Threats Management To Enable Digital Assets Security. This template helps you present information on three stages. You can also present information on Plan And Collect, Review And Analyze, Strategic Framework using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
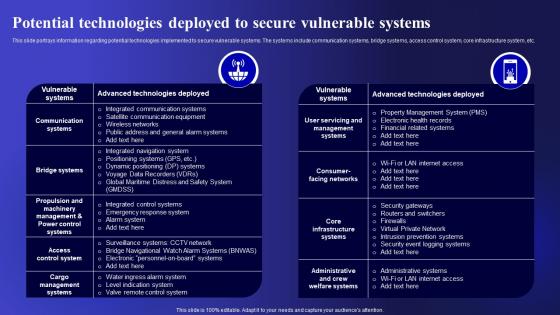 Potential Technologies Deployed To Secure Cyber Threats Management To Enable Digital Assets Security
Potential Technologies Deployed To Secure Cyber Threats Management To Enable Digital Assets SecurityThis slide portrays information regarding potential technologies implemented to secure vulnerable systems. The systems include communication systems, bridge systems, access control system, core infrastructure system, etc. Deliver an outstanding presentation on the topic using this Potential Technologies Deployed To Secure Cyber Threats Management To Enable Digital Assets Security. Dispense information and present a thorough explanation of Potential, Technologies, Communication using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Table Of Contents Cyber Threats Management To Enable Digital Assets Security
Table Of Contents Cyber Threats Management To Enable Digital Assets SecurityPresent the topic in a bit more detail with this Table Of Contents Cyber Threats Management To Enable Digital Assets Security. Use it as a tool for discussion and navigation on Categorizing, Associated, Determine Sequence. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
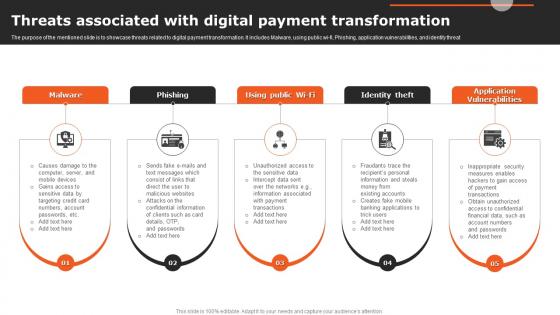 Threats Associated With Digital Payment Transformation
Threats Associated With Digital Payment TransformationThe purpose of the mentioned slide is to showcase threats related to digital payment transformation. It includes Malware, using public wi fi, Phishing, application vulnerabilities, and identity threat Introducing our premium set of slides with Threats Associated With Digital Payment Transformation Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Malware, Phishing, Identity Theft So download instantly and tailor it with your information.
-
 Digital Risk And Threat Identifying Icon
Digital Risk And Threat Identifying IconIntroducing our premium set of slides with Digital Risk And Threat Identifying Icon Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Digital Risk And Threat Identifying So download instantly and tailor it with your information.
-
 Digital threat management ppt powerpoint presentation deck cpb
Digital threat management ppt powerpoint presentation deck cpbPresenting this set of slides with name Digital Threat Management Ppt Powerpoint Presentation Deck Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Digital Threat Management to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Six building blocks of digital transformation threats ppt powerpoint slides
Six building blocks of digital transformation threats ppt powerpoint slidesPresenting this set of slides with name Six Building Blocks Of Digital Transformation Threats Ppt Powerpoint Slides. This is a six stage process. The stages in this process are Mindset, Leaders, Business, Excellence, Strategy, Opportunities, Threats, Develop, Digital Business, Capabilities. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Digital threat hunting ppt powerpoint presentation portfolio slide download cpb
Digital threat hunting ppt powerpoint presentation portfolio slide download cpbPresenting this set of slides with name Digital Threat Hunting Ppt Powerpoint Presentation Portfolio Slide Download Cpb. This is an editable Powerpoint six stages graphic that deals with topics like Digital Threat Hunting to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
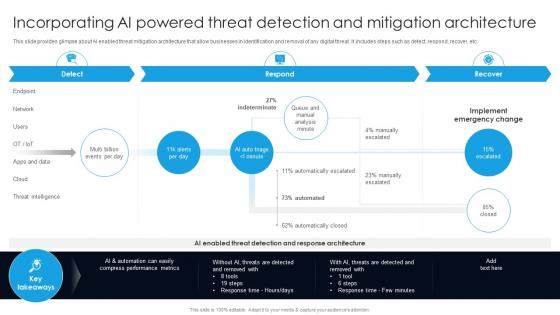 Incorporating Ai Powered Threat Detection And Mitigation Digital Transformation With AI DT SS
Incorporating Ai Powered Threat Detection And Mitigation Digital Transformation With AI DT SSThis slide provides glimpse about AI enabled threat mitigation architecture that allow businesses in identification and removal of any digital threat. It includes steps such as detect, respond, recover, etc. Present the topic in a bit more detail with this Incorporating Ai Powered Threat Detection And Mitigation Digital Transformation With AI DT SS Use it as a tool for discussion and navigation on Key Takeaways, Threat Detection, Mitigation Architecture This template is free to edit as deemed fit for your organization. Therefore download it now.

