Powerpoint Templates and Google slides for Encryption
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Encryption Implementation Strategies Comparison Between Digital Rights Management Software
Encryption Implementation Strategies Comparison Between Digital Rights Management SoftwareThis slide outlines the available Digital Rights Management DRM software for several industries, such as information technology and services, marketing and advertising, consumer goods, automotive, civil engineering, architecture and planning, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Comparison Between Digital Rights Management Software. Use it as a tool for discussion and navigation on Marketing And Advertising, Architecture And Planning, Information Technology And Services. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
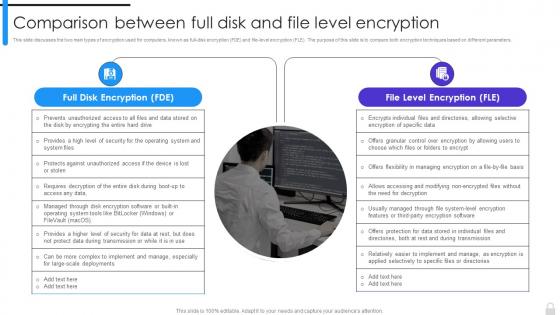 Encryption Implementation Strategies Comparison Between Full Disk And File Level Encryption
Encryption Implementation Strategies Comparison Between Full Disk And File Level EncryptionThis slide discusses the two main types of encryption used for computers, known as full-disk encryption FDE and file-level encryption FLE. The purpose of this slide is to compare both encryption techniques based on different parameters. Increase audience engagement and knowledge by dispensing information using Encryption Implementation Strategies Comparison Between Full Disk And File Level Encryption. This template helps you present information on two stages. You can also present information on Full Disk Encryption, File Level Encryption, Operating System And System Files using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
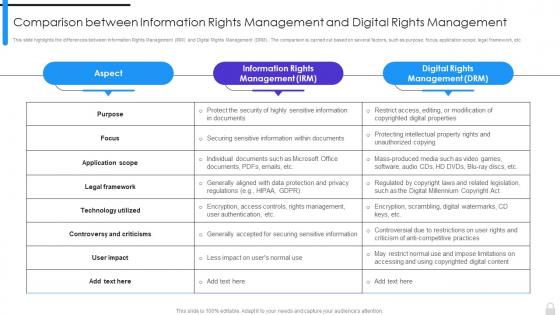 Encryption Implementation Strategies Comparison Between Information Rights Management And Digital
Encryption Implementation Strategies Comparison Between Information Rights Management And DigitalThis slide highlights the differences between Information Rights Management IRM and Digital Rights Management DRM. The comparison is carried out based on several factors, such as purpose, focus, application scope, legal framework, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Comparison Between Information Rights Management And Digital. Dispense information and present a thorough explanation of Information Rights Management, Digital Rights Management, Controversy And Criticisms using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
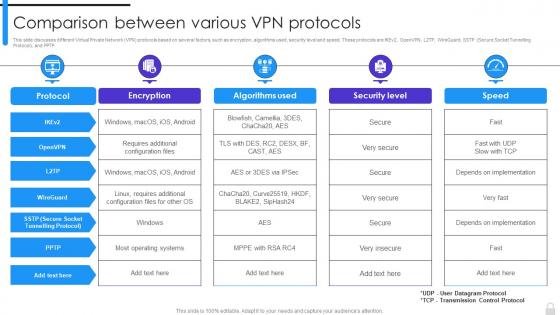 Encryption Implementation Strategies Comparison Between Various VPN Protocols
Encryption Implementation Strategies Comparison Between Various VPN ProtocolsThis slide discusses different Virtual Private Network VPN protocols based on several factors, such as encryption, algorithms used, security level and speed. These protocols are IKEv2, OpenVPN, L2TP, WireGuard, SSTP Secure Socket Tunnelling Protocol, and PPTP. Present the topic in a bit more detail with this Encryption Implementation Strategies Comparison Between Various VPN Protocols. Use it as a tool for discussion and navigation on Virtual Private Network, Algorithms Used, Security Level And Speed, Secure Socket Tunnelling Protocol. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
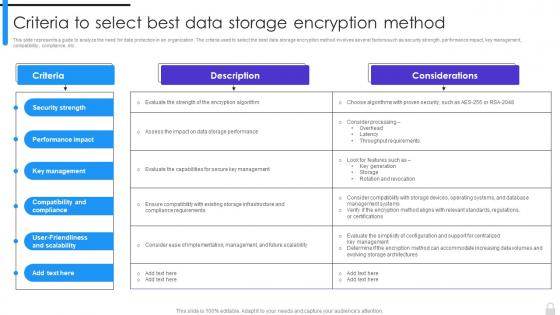 Encryption Implementation Strategies Criteria To Select Best Data Storage Encryption Method
Encryption Implementation Strategies Criteria To Select Best Data Storage Encryption MethodThis slide represents a guide to analyze the need for data protection in an organization. The criteria used to select the best data storage encryption method involves several factors such as security strength, performance impact, key management, compatibility, compliance, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Criteria To Select Best Data Storage Encryption Method. Dispense information and present a thorough explanation of Security Strength, Performance Impact, Key Management, Compatibility And Compliance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
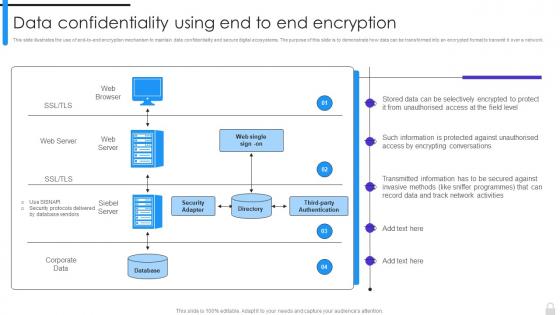 Encryption Implementation Strategies Data Confidentiality Using End To End Encryption
Encryption Implementation Strategies Data Confidentiality Using End To End EncryptionThis slide illustrates the use of end-to-end encryption mechanism to maintain data confidentiality and secure digital ecosystems. The purpose of this slide is to demonstrate how data can be transformed into an encrypted format to transmit it over a network. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Data Confidentiality Using End To End Encryption. Dispense information and present a thorough explanation of Data Confidentiality, Encryption Mechanism, Demonstrate, Digital Ecosystems using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
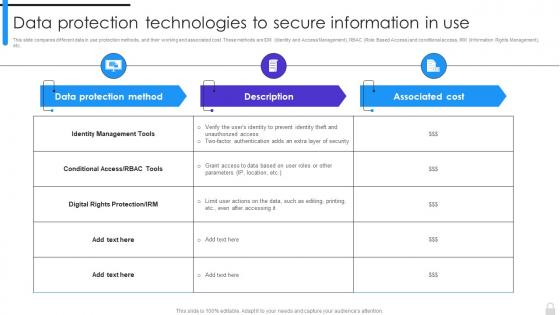 Encryption Implementation Strategies Data Protection Technologies To Secure Information In Use
Encryption Implementation Strategies Data Protection Technologies To Secure Information In UseThis slide compares different data in use protection methods, and their working and associated cost. These methods are IDM Identity and Access Management, RBAC Role Based Access and conditional access, IRM Information Rights Management, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Data Protection Technologies To Secure Information In Use. Use it as a tool for discussion and navigation on Identity Management Tools, Digital Rights Protection, Data Protection Technologies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
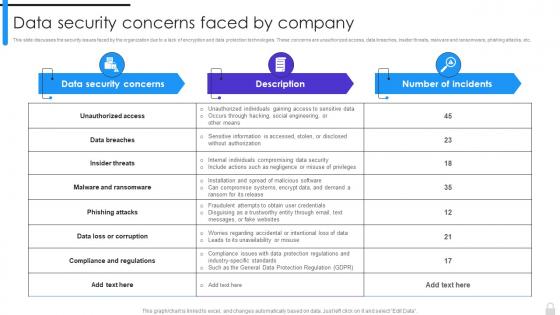 Encryption Implementation Strategies Data Security Concerns Faced By Company
Encryption Implementation Strategies Data Security Concerns Faced By CompanyThis slide discusses the security issues faced by the organization due to a lack of encryption and data protection technologies. These concerns are unauthorized access, data breaches, insider threats, malware and ransomware, phishing attacks, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Data Security Concerns Faced By Company. Dispense information and present a thorough explanation of Data Security Concerns, Phishing Attacks, Data Protection Technologies, Compliance And Regulations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
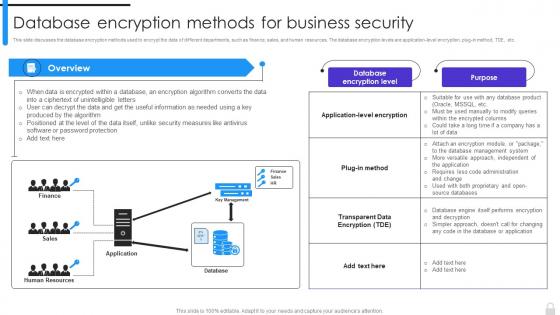 Encryption Implementation Strategies Database Encryption Methods For Business Security
Encryption Implementation Strategies Database Encryption Methods For Business SecurityThis slide discusses the database encryption methods used to encrypt the data of different departments, such as finance, sales, and human resources. The database encryption levels are application-level encryption, plug-in method, TDE, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Database Encryption Methods For Business Security. Use it as a tool for discussion and navigation on Database Encryption Methods, Business Security, Sales And Human Resources. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
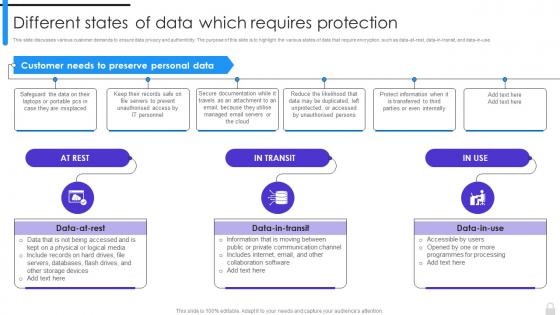 Encryption Implementation Strategies Different States Of Data Which Requires Protection
Encryption Implementation Strategies Different States Of Data Which Requires ProtectionThis slide discusses various customer demands to ensure data privacy and authenticity. The purpose of this slide is to highlight the various states of data that require encryption, such as data-at-rest, data-in-transit, and data-in-use. Introducing Encryption Implementation Strategies Different States Of Data Which Requires Protection to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Customer Demands, Data Privacy And Authenticity, Require Encryption, Collaboration Software, using this template. Grab it now to reap its full benefits.
-
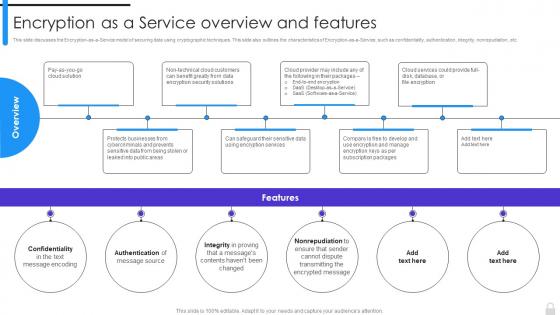 Encryption Implementation Strategies Encryption As A Service Overview And Features
Encryption Implementation Strategies Encryption As A Service Overview And FeaturesThis slide discusses the Encryption-as-a-Service model of securing data using cryptographic techniques. This slide also outlines the characteristics of Encryption-as-a-Service, such as confidentiality, authentication, integrity, nonrepudiation, etc. Increase audience engagement and knowledge by dispensing information using Encryption Implementation Strategies Encryption As A Service Overview And Features. This template helps you present information on six stages. You can also present information on Text Message Encoding, Encryption Services, Subscription Packages, Data Encryption Security Solutions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
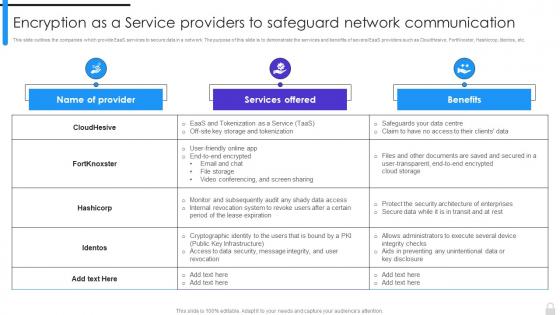 Encryption Implementation Strategies Encryption As A Service Providers To Safeguard Network
Encryption Implementation Strategies Encryption As A Service Providers To Safeguard NetworkThis slide outlines the companies which provide EaaS services to secure data in a network. The purpose of this slide is to demonstrate the services and benefits of several EaaS providers such as CloudHesive, FortKnoxter, Hashicrop, Identos, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Encryption As A Service Providers To Safeguard Network. Dispense information and present a thorough explanation of Encryption As A Service, Safeguard Network Communication, Internal Revocation System using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
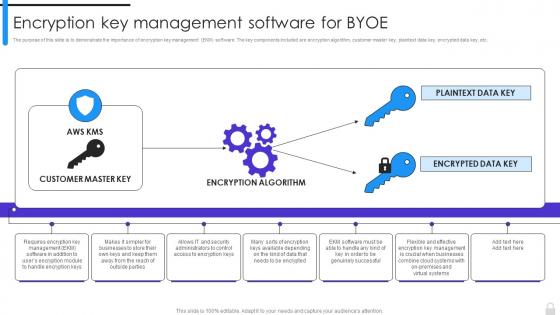 Encryption Implementation Strategies Encryption Key Management Software For Byoe
Encryption Implementation Strategies Encryption Key Management Software For ByoeThe purpose of this slide is to demonstrate the importance of encryption key management EKM software. The key components included are encryption algorithm, customer master key, plaintext data key, encrypted data key, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Encryption Key Management Software For Byoe. Use it as a tool for discussion and navigation on Encryption Algorithm, Customer Master Key, Encrypted Data Key, Key Management Software. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
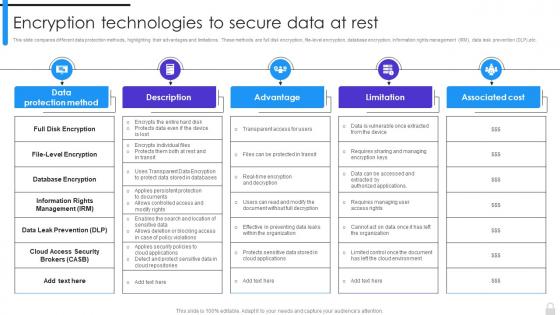 Encryption Implementation Strategies Encryption Technologies To Secure Data At Rest
Encryption Implementation Strategies Encryption Technologies To Secure Data At RestThis slide compares different data protection methods, highlighting their advantages and limitations. These methods are full disk encryption, file-level encryption, database encryption, information rights management IRM, data leak prevention DLP,etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Encryption Technologies To Secure Data At Rest. Dispense information and present a thorough explanation of Information Rights Management, Data Leak Prevention, Full Disk Encryption, Cloud Access Security Brokers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
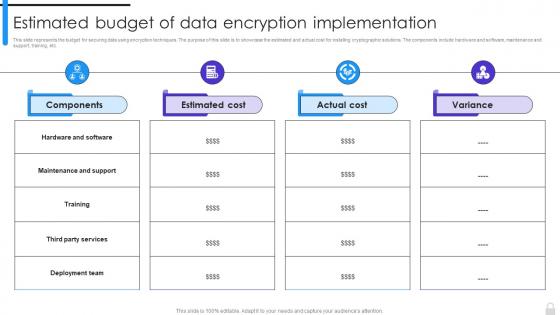 Encryption Implementation Strategies Estimated Budget Of Data Encryption Implementation
Encryption Implementation Strategies Estimated Budget Of Data Encryption ImplementationThis slide represents the budget for securing data using encryption techniques. The purpose of this slide is to showcase the estimated and actual cost for installing cryptographic solutions. The components include hardware and software, maintenance and support, training, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Estimated Budget Of Data Encryption Implementation. Use it as a tool for discussion and navigation on Maintenance And Support, Deployment Team, Data Encryption, Estimated Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Encryption Implementation Strategies For Table Of Contents Ppt Ideas Templates
Encryption Implementation Strategies For Table Of Contents Ppt Ideas TemplatesIntroducing Encryption Implementation Strategies For Table Of Contents Ppt Ideas Templates to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Safeguard Network Communication, Encryption Key Management Software, Applications Of Encryption As A Service, using this template. Grab it now to reap its full benefits.
-
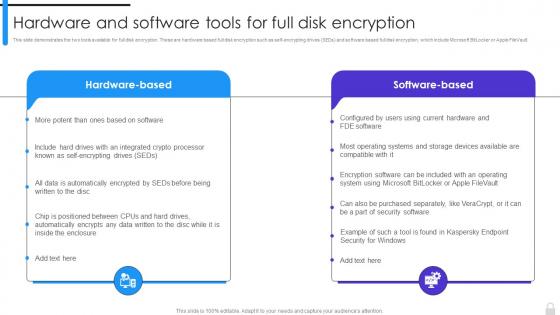 Encryption Implementation Strategies Hardware And Software Tools For Full Disk Encryption
Encryption Implementation Strategies Hardware And Software Tools For Full Disk EncryptionThis slide demonstrates the two tools available for full disk encryption. These are hardware based full disk encryption such as self-encrypting drives SEDs and software based full disk encryption, which include Microsoft BitLocker or Apple FileVault. Increase audience engagement and knowledge by dispensing information using Encryption Implementation Strategies Hardware And Software Tools For Full Disk Encryption. This template helps you present information on two stages. You can also present information on Hardware And Software Tools, Full Disk Encryption, Microsoft Bitlocker, Apple Filevault using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
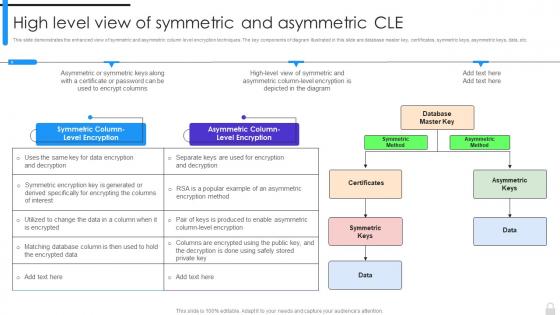 Encryption Implementation Strategies High Level View Of Symmetric And Asymmetric Cle
Encryption Implementation Strategies High Level View Of Symmetric And Asymmetric CleThis slide demonstrates the enhanced view of symmetric and asymmetric column level encryption techniques. The key components of diagram illustrated in this slide are database master key, certificates, symmetric keys, asymmetric keys, data, etc. Introducing Encryption Implementation Strategies High Level View Of Symmetric And Asymmetric Cle to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Symmetric Method, Asymmetric Method, Asymmetric Column Level Encryption, Symmetric Column Level Encryption, using this template. Grab it now to reap its full benefits.
-
 Encrypted Google DOCS In Powerpoint And Google Slides Cpb
Encrypted Google DOCS In Powerpoint And Google Slides CpbPresenting our Encrypted Google DOCS In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Encrypted Google DOCS This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Encryption Opposite Types In Powerpoint And Google Slides Cpb
Encryption Opposite Types In Powerpoint And Google Slides CpbPresenting Encryption Opposite Types In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Encryption Opposite Types. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Email Best Practices Privacy Encryption In Powerpoint And Google Slides Cpb
Email Best Practices Privacy Encryption In Powerpoint And Google Slides CpbPresenting our Email Best Practices Privacy Encryption In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Email Best Practices Privacy Encryption This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Security Issues Internet Things Encryption In Powerpoint And Google Slides Cpb
Security Issues Internet Things Encryption In Powerpoint And Google Slides CpbPresenting Security Issues Internet Things Encryption In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Security Issues Internet Things Encryption. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
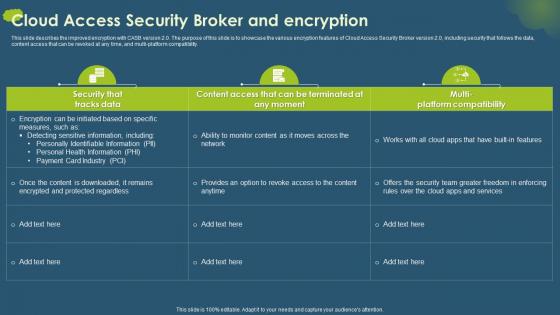 Cloud Access Security Broker CASB V2 And Encryption Ppt Gallery Design Templates
Cloud Access Security Broker CASB V2 And Encryption Ppt Gallery Design TemplatesThis slide describes the improved encryption with CASB version 2.0. The purpose of this slide is to showcase the various encryption features of Cloud Access Security Broker version 2.0, including security that follows the data, content access that can be revoked at any time, and multi-platform compatibility. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 And Encryption Ppt Gallery Design Templates. Dispense information and present a thorough explanation of Detecting Sensitive Information, Personally Identifiable Information, Personal Health Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Encryption Digital Digital Identity Blockchain In Powerpoint And Google Slides Cpb
Encryption Digital Digital Identity Blockchain In Powerpoint And Google Slides CpbPresenting our Encryption Digital Digital Identity Blockchain In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Encryption Digital Digital, Identity Blockchain This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Padlock Heart Encryption Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Padlock Heart Encryption Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis colourful icon features a lock and key design, perfect for adding a touch of security to presentations. Ideal for business, security, or safety-related topics, it will provide a professional and eye-catching look to any project.
-
 Padlock Heart Encryption Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Padlock Heart Encryption Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is perfect for presentations on security, access control, and encryption. It features a simple, black-and-white design of a lock and key, making it an ideal visual aid for any discussion of protection and safety.
-
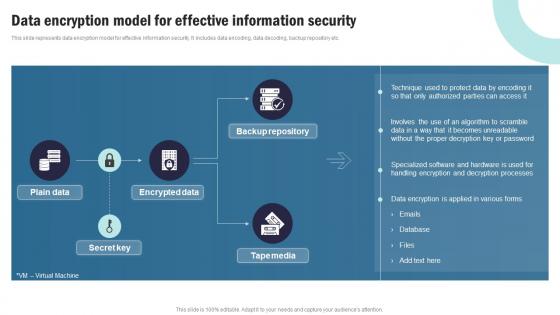 Strategic Plan To Implement Data Encryption Model For Effective Information Security Strategy SS V
Strategic Plan To Implement Data Encryption Model For Effective Information Security Strategy SS VThis slide represents data encryption model for effective information security. It includes data encoding, data decoding, backup repository etc. Present the topic in a bit more detail with this Strategic Plan To Implement Data Encryption Model For Effective Information Security Strategy SS V Use it as a tool for discussion and navigation on Employee Headcount, Average Employee Age, Gender Diversity Ratio This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Encryption Secure Computer Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Data Encryption Secure Computer Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon is a visual representation of secure computer. It is a modern, vibrant and eye catching icon that will help to create an impactful presentation. It is a great way to emphasize the importance of data security and safety.
-
 Data Encryption Secure Computer Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Data Encryption Secure Computer Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is perfect for presentations on secure computer systems. It features a black and white design depicting a computer with a padlock, symbolizing the safety of your data. Use this icon to emphasize the importance of secure computing.
-
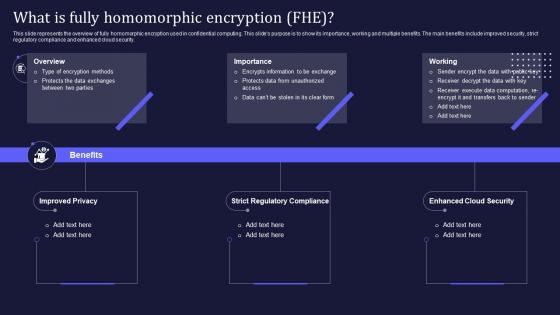 Confidential Computing V2 What Is Fully Homomorphic Encryption FHE
Confidential Computing V2 What Is Fully Homomorphic Encryption FHEThis slide represents the overview of fully homomorphic encryption used in confidential computing. This slides purpose is to show its importance, working and multiple benefits. The main benefits include improved security, strict regulatory compliance and enhanced cloud security. Introducing Confidential Computing V2 What Is Fully Homomorphic Encryption FHE to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Strict Regulatory Compliance, Enhanced Cloud Security, Homomorphic Encryption, using this template. Grab it now to reap its full benefits.
-
 Corporate Email Encryption In Powerpoint And Google Slides Cpb
Corporate Email Encryption In Powerpoint And Google Slides CpbPresenting Corporate Email Encryption In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Corporate Email Encryption. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
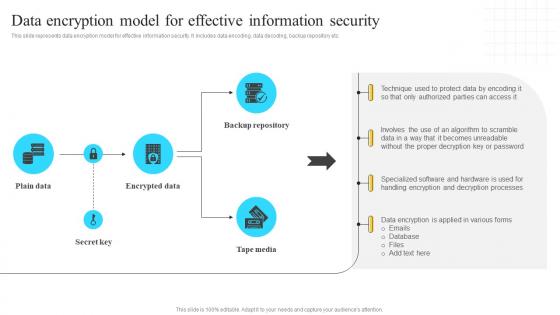 Implementation Of Information Data Encryption Model For Effective Information Security Strategy SS V
Implementation Of Information Data Encryption Model For Effective Information Security Strategy SS VThis slide represents data encryption model for effective information security. It includes data encoding, data decoding, backup repository etc. Present the topic in a bit more detail with this Implementation Of Information Data Encryption Model For Effective Information Security Strategy SS V. Use it as a tool for discussion and navigation on Backup Repository, Encrypted Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Computing System Technology What Is Fully Homomorphic Encryption Fhe
Confidential Computing System Technology What Is Fully Homomorphic Encryption FheThis slide represents the overview of fully homomorphic encryption used in confidential computing. This slides purpose is to show its importance, working and multiple benefits. The main benefits include improved security, strict regulatory compliance and enhanced cloud security. Deliver an outstanding presentation on the topic using this Confidential Computing System Technology What Is Fully Homomorphic Encryption Fhe. Dispense information and present a thorough explanation of Improved Privacy, Strict Regulatory Compliance, Enhanced Cloud Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
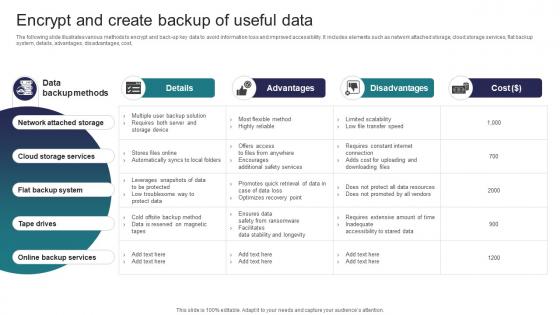 Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security Threats
Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide illustrates various methods to encrypt and back up key data to avoid information loss and improved accessibility. It includes elements such as network attached storage, cloud storage services, flat backup system, details, advantages, disadvantages, cost, Deliver an outstanding presentation on the topic using this Encrypt And Create Backup Of Useful Data Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Network Attached Storage, Cloud Storage Services, Flat Backup System using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 About Us For Our Encryption Services Company Encryption Framework Upgradation Proposal
About Us For Our Encryption Services Company Encryption Framework Upgradation ProposalThis slide gives an overview of the encryption service provider company. It includes the total number of clients, employees, successful encryption projects, partnerships and collaborations with industry-leading organizations, and history. Introducing About Us For Our Encryption Services Company Encryption Framework Upgradation Proposal to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Encryption Service, Encryption Projects, Partnerships And Collaborations, Industry Leading Organizations, using this template. Grab it now to reap its full benefits.
-
 Case Study For Encryption Framework Upgradation Proposal
Case Study For Encryption Framework Upgradation ProposalThis slide showcases the case study for encryption framework upgradation in a government organization. It includes the problems experienced by the department, solutions offered by the encryption service provider company, and the outcomes of the upgradation. Increase audience engagement and knowledge by dispensing information using Case Study For Encryption Framework Upgradation Proposal. This template helps you present information on three stages. You can also present information on Encryption Framework, Government Organization, Encryption Service, Fine Tuning Network using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Contact Us For Encryption Framework Upgradation Services
Contact Us For Encryption Framework Upgradation ServicesDeliver an outstanding presentation on the topic using this Contact Us For Encryption Framework Upgradation Services. Dispense information and present a thorough explanation of Contact Us, Encryption Framework, Upgradation Services using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cover Letter For Encryption Framework Upgradation Proposal
Cover Letter For Encryption Framework Upgradation ProposalPresent the topic in a bit more detail with this Cover Letter For Encryption Framework Upgradation Proposal. Use it as a tool for discussion and navigation on Encryption Framework, Upgradation Proposal, Return On Investment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Icons Slide For Encryption Framework Upgradation Proposal
Icons Slide For Encryption Framework Upgradation ProposalIntroducing our well researched set of slides titled Icons Slide For Encryption Framework Upgradation Proposal. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
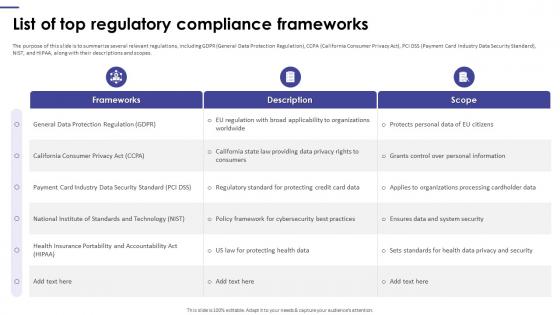 List Of Top Regulatory Compliance Frameworks Encryption Framework Upgradation Proposal
List Of Top Regulatory Compliance Frameworks Encryption Framework Upgradation ProposalThe purpose of this slide is to summarize several relevant regulations, including GDPR General Data Protection Regulation, CCPA California Consumer Privacy Act, PCI DSS Payment Card Industry Data Security Standard, NIST, and HIPAA, along with their descriptions and scopes. Deliver an outstanding presentation on the topic using this List Of Top Regulatory Compliance Frameworks Encryption Framework Upgradation Proposal. Dispense information and present a thorough explanation of General Data Protection Regulation, California Consumer Privacy Act, Industry Data Security Standard, Ensures Data And System Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
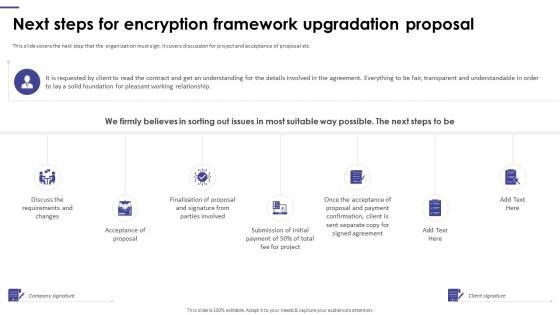 Next Steps For Encryption Framework Upgradation Proposal
Next Steps For Encryption Framework Upgradation ProposalThis slide covers the next step that the organization must sign. It covers discussion for project and acceptance of proposal etc. Increase audience engagement and knowledge by dispensing information using Next Steps For Encryption Framework Upgradation Proposal. This template helps you present information on seven stages. You can also present information on Project And Acceptance Of Proposal, Encryption Framework, Upgradation Proposal using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
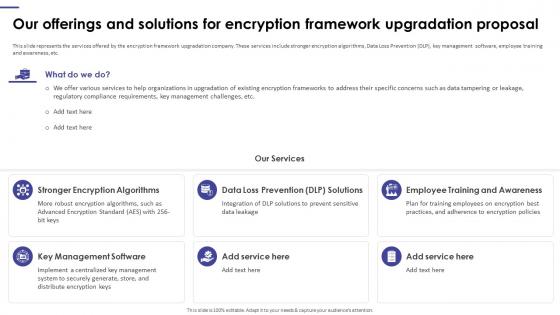 Our Offerings And Solutions For Encryption Framework Upgradation Proposal
Our Offerings And Solutions For Encryption Framework Upgradation ProposalThis slide represents the services offered by the encryption framework upgradation company. These services include stronger encryption algorithms, Data Loss Prevention DLP, key management software, employee training and awareness, etc. Introducing Our Offerings And Solutions For Encryption Framework Upgradation Proposal to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Stronger Encryption Algorithms, Employee Training And Awareness, Key Management Software, Encryption Framework Upgradation Proposal, using this template. Grab it now to reap its full benefits.
-
 Our Proposed Automated Encryption Decryption System For Upgradation Proposal
Our Proposed Automated Encryption Decryption System For Upgradation ProposalThis slide represents the proposed Automated Encryption or Decryption System AEDS for encryption framework upgradation proposal. The main phases include key generation stage, divide data into random size of blocks, and implementation stage. Deliver an outstanding presentation on the topic using this Our Proposed Automated Encryption Decryption System For Upgradation Proposal. Dispense information and present a thorough explanation of Automated Encryption, Decryption System, Upgradation Proposal, Encryption Framework using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
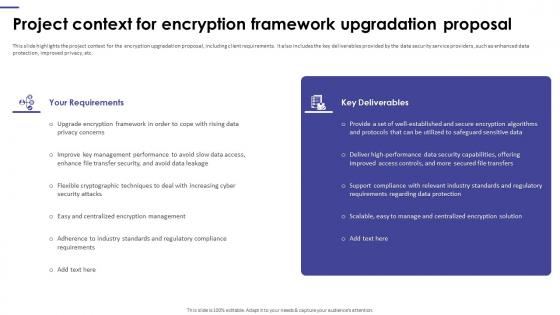 Project Context For Encryption Framework Upgradation Proposal
Project Context For Encryption Framework Upgradation ProposalThis slide highlights the project context for the encryption upgradation proposal, including client requirements. It also includes the key deliverables provided by the data security service providers, such as enhanced data protection, improved privacy, etc. Deliver an outstanding presentation on the topic using this Project Context For Encryption Framework Upgradation Proposal. Dispense information and present a thorough explanation of Centralized Encryption Management, Regulatory Compliance Requirements, Management Performance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
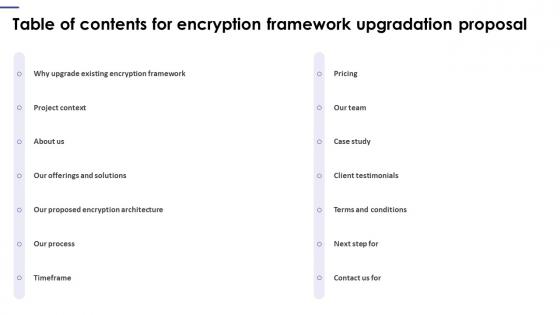 Table Of Contents For Encryption Framework Upgradation Proposal
Table Of Contents For Encryption Framework Upgradation ProposalIntroducing Table Of Contents For Encryption Framework Upgradation Proposal to increase your presentation threshold. Encompassed with fourteen stages, this template is a great option to educate and entice your audience. Dispence information on Client Testimonials, Existing Encryption Framework, Terms And Conditions, Our Team, using this template. Grab it now to reap its full benefits.
-
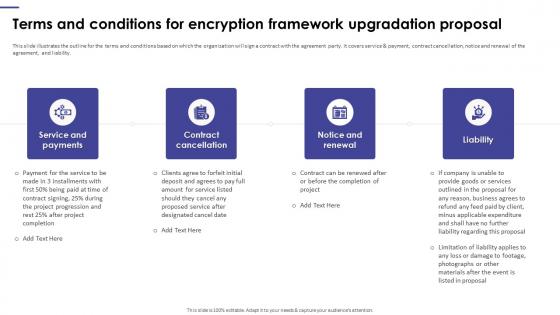 Terms And Conditions For Encryption Framework Upgradation Proposal
Terms And Conditions For Encryption Framework Upgradation ProposalThis slide illustrates the outline for the terms and conditions based on which the organization will sign a contract with the agreement party. It covers service and payment, contract cancellation, notice and renewal of the agreement, and liability. Increase audience engagement and knowledge by dispensing information using Terms And Conditions For Encryption Framework Upgradation Proposal. This template helps you present information on four stages. You can also present information on Service And Payments, Contract Cancellation, Notice And Renewal, Encryption Framework using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
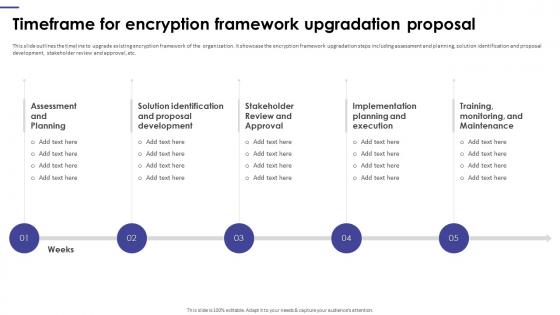 Timeframe For Encryption Framework Upgradation Proposal
Timeframe For Encryption Framework Upgradation ProposalThis slide outlines the timeline to upgrade existing encryption framework of the organization. It showcase the encryption framework upgradation steps including assessment and planning, solution identification and proposal development, stakeholder review and approval, etc. Introducing Timeframe For Encryption Framework Upgradation Proposal to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Timeframe For Encryption, Framework Upgradation Proposal, Proposal Development, using this template. Grab it now to reap its full benefits.
-
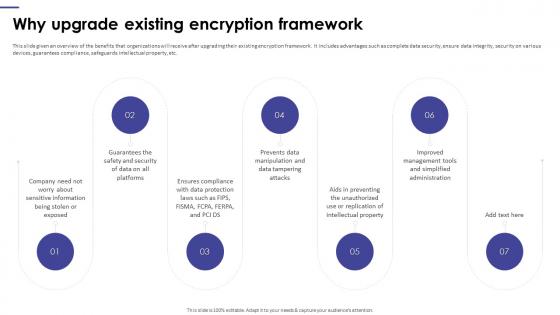 Why Upgrade Existing Encryption Framework Upgradation Proposal
Why Upgrade Existing Encryption Framework Upgradation ProposalIncrease audience engagement and knowledge by dispensing information using Why Upgrade Existing Encryption Framework Upgradation Proposal. This template helps you present information on seven stages. You can also present information on Prevents Data Manipulation, Existing Encryption Framework, Data Protection Laws using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
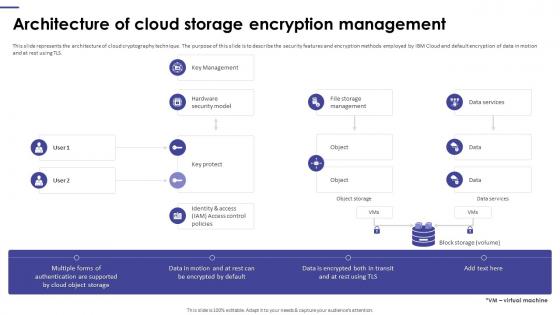 Encryption Framework Upgradation Proposal Architecture Of Cloud Storage Encryption Management
Encryption Framework Upgradation Proposal Architecture Of Cloud Storage Encryption ManagementPresent the topic in a bit more detail with this Encryption Framework Upgradation Proposal Architecture Of Cloud Storage Encryption Management. Use it as a tool for discussion and navigation on Architecture Of Cloud Storage, Encryption Management, Cloud Cryptography Technique. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
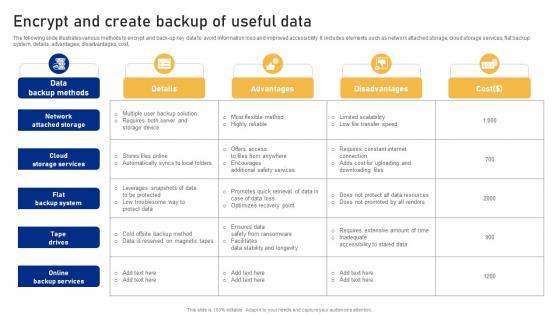 Encrypt And Create Backup Of Useful Data Cyber Risk Assessment
Encrypt And Create Backup Of Useful Data Cyber Risk AssessmentThe following slide illustrates various methods to encrypt and back-up key data to avoid information loss and improved accessibility. It includes elements such as network attached storage, cloud storage services, flat backup system, details, advantages, disadvantages, cost, Deliver an outstanding presentation on the topic using this Encrypt And Create Backup Of Useful Data Cyber Risk Assessment Dispense information and present a thorough explanation of Network Attached, Backup System, Backup Services using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 About Bring Your Own Encryption Overview And Benefits Encryption For Data Privacy In Digital Age It
About Bring Your Own Encryption Overview And Benefits Encryption For Data Privacy In Digital Age ItThis slide discusses about widely used encryption method known as Bring Your Own Encryption BYOE. The purpose of this slide is to elaborate the meaning of BYOE. This slide also outlines the benefits of Bring Your Own Keys BYOK method. Present the topic in a bit more detail with this About Bring Your Own Encryption Overview And Benefits Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Overview, Encryption, Technique. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 About Cloud Encryption Tools And Services Encryption For Data Privacy In Digital Age It
About Cloud Encryption Tools And Services Encryption For Data Privacy In Digital Age ItThis slide talks about the cloud encryption methodologies. The purpose of this slide is to outline the encryption tools used in cloud cryptography. It also describes services provided by popular cloud encryption tools such as data encryption, key management, etc. Deliver an outstanding presentation on the topic using this About Cloud Encryption Tools And Services Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Encryption, Services, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
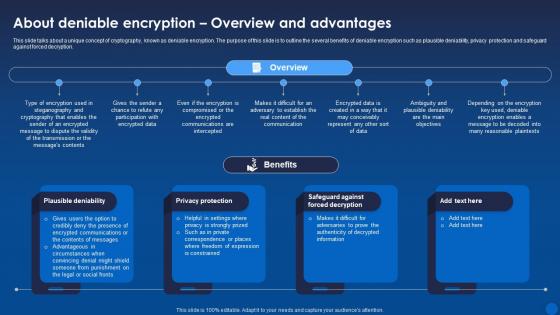 About Deniable Encryption Overview And Advantages Encryption For Data Privacy In Digital Age It
About Deniable Encryption Overview And Advantages Encryption For Data Privacy In Digital Age ItThis slide talks about a unique concept of cryptography, known as deniable encryption. The purpose of this slide is to outline the several benefits of deniable encryption such as plausible deniability, privacy protection and safeguard against forced decryption. Present the topic in a bit more detail with this About Deniable Encryption Overview And Advantages Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Encryption, Overview, Decryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
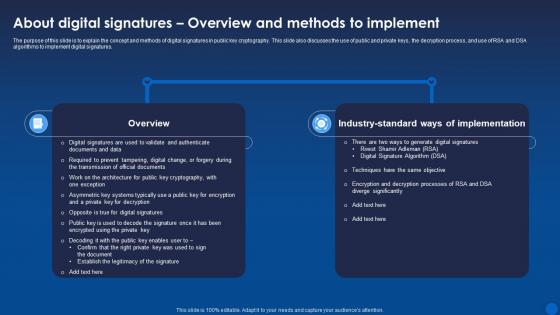 About Digital Signatures Overview And Methods Encryption For Data Privacy In Digital Age It
About Digital Signatures Overview And Methods Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to explain the concept and methods of digital signatures in public key cryptography. This slide also discusses the use of public and private keys, the decryption process, and use of RSA and DSA algorithms to implement digital signatures. Deliver an outstanding presentation on the topic using this About Digital Signatures Overview And Methods Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Implementation, Overview, Significantly using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
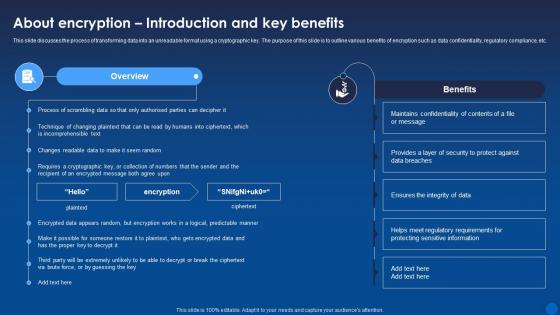 About Encryption Introduction And Key Benefits Encryption For Data Privacy In Digital Age It
About Encryption Introduction And Key Benefits Encryption For Data Privacy In Digital Age ItThis slide discusses the process of transforming data into an unreadable format using a cryptographic key. The purpose of this slide is to outline various benefits of encryption such as data confidentiality, regulatory compliance, etc. Present the topic in a bit more detail with this About Encryption Introduction And Key Benefits Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Introduction, Sensitive, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
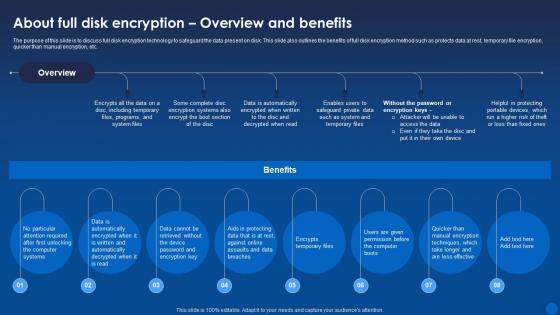 About Full Disk Encryption Overview And Benefits Encryption For Data Privacy In Digital Age It
About Full Disk Encryption Overview And Benefits Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to discuss full disk encryption technology to safeguard the data present on disk. This slide also outlines the benefits of full disk encryption method such as protects data at rest, temporary file encryption, quicker than manual encryption, etc. Deliver an outstanding presentation on the topic using this About Full Disk Encryption Overview And Benefits Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Encryption, Overview, Automatically using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 About Homomorphic Encryption Overview And Types Encryption For Data Privacy In Digital Age It
About Homomorphic Encryption Overview And Types Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to explain the concept of homomorphic encryption. The benefits of this technique are privacy preservation, data security, secure outsourcing, trust in untrusted environments, enhanced data exchange, etc. Present the topic in a bit more detail with this About Homomorphic Encryption Overview And Types Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Homomorphic, Encryption, Overview. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 About Internet Protocol Security Overview And Uses Encryption For Data Privacy In Digital Age It
About Internet Protocol Security Overview And Uses Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to explain the role and functionality of IPsec Internet Protocol Security in securing connections between devices. This slide also outlines the uses of IPsec such as protecting data during transmission over open networks, use in building VPNs, etc. Deliver an outstanding presentation on the topic using this About Internet Protocol Security Overview And Uses Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Overview, Protocol Security, Destination using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
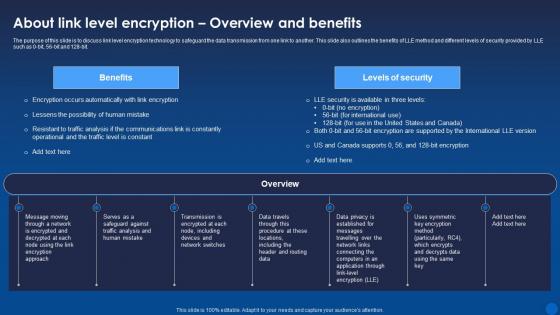 About Link Level Encryption Overview And Benefits Encryption For Data Privacy In Digital Age It
About Link Level Encryption Overview And Benefits Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to discuss link level encryption technology to safeguard the data transmission from one link to another. This slide also outlines the benefits of LLE method and different levels of security provided by LLE such as 0-bit, 56-bit and 128-bit. Present the topic in a bit more detail with this About Link Level Encryption Overview And Benefits Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Encryption, Overview, Application. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 About Quantum Cryptography Overview And Properties Encryption For Data Privacy In Digital Age It
About Quantum Cryptography Overview And Properties Encryption For Data Privacy In Digital Age ItThis slide discusses the emerging cryptographic technology known as quantum encryption. The purpose of this slide is to discuss the meaning of quantum cryptography. This slide also outlines the properties such as Quantum-safe cryptography and Quantum key distribution. Deliver an outstanding presentation on the topic using this About Quantum Cryptography Overview And Properties Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Quantum, Cryptography, Properties using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.



