Powerpoint Templates and Google slides for Government Policy
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
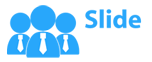
 IT Policy Checklist For Creating Bring Your Own Device Policy
IT Policy Checklist For Creating Bring Your Own Device PolicyThis slide represents the checklist for creating a BYOD policy, including the key considerations such as the list of allowed devices and apps, payment agreement, and so on. Present the topic in a bit more detail with this IT Policy Checklist For Creating Bring Your Own Device Policy. Use it as a tool for discussion and navigation on Key Considerations, Device Policy, Description. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
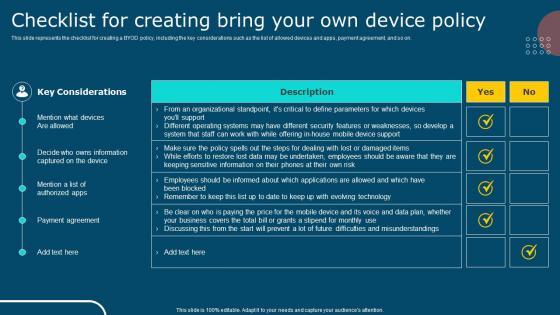
 IT Policy Company Stipend For Bring Your Own Device Policy
IT Policy Company Stipend For Bring Your Own Device PolicyThis slide represents the company stipend for BYOD policy, including the stats for 2022, such as the age of employees using their personal devices, BYOD generated value of each worker per year, and so on. Introducing IT Policy Company Stipend For Bring Your Own Device Policy to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Company Stipend, Byod Stats, Paycheck Stipends, using this template. Grab it now to reap its full benefits.
-
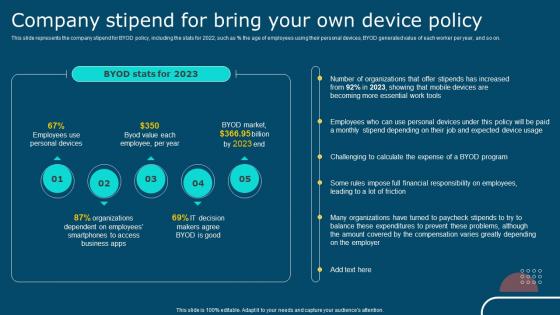
 IT Policy Critical Components Of Information Technology Policy
IT Policy Critical Components Of Information Technology PolicyThis slide depicts the critical components of information technology policy, and it includes integrity, confidentiality, and availability, including how these components work. Introducing IT Policy Critical Components Of Information Technology Policy to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Integrity, Confidentiality, Availability, using this template. Grab it now to reap its full benefits.
-
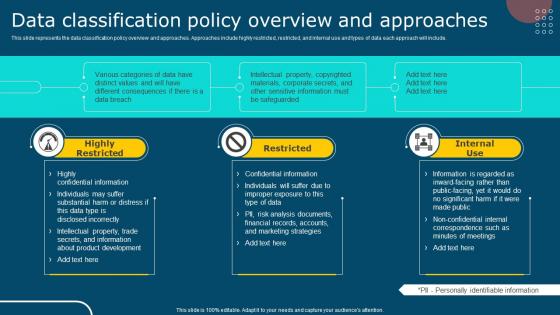 IT Policy Data Classification Policy Overview And Approaches
IT Policy Data Classification Policy Overview And ApproachesThis slide represents the data classification policy overview and approaches. Approaches include highly restricted, restricted, and internal use and types of data each approach will include. Introducing IT Policy Data Classification Policy Overview And Approaches to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Highly Restricted, Restricted, Internal Use, using this template. Grab it now to reap its full benefits.
-
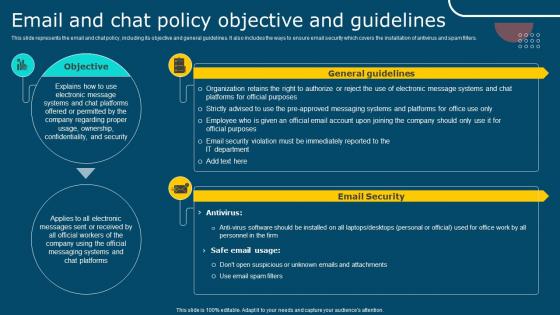 IT Policy Email And Chat Policy Objective And Guidelines Ppt Diagrams
IT Policy Email And Chat Policy Objective And Guidelines Ppt DiagramsThis slide represents the email and chat policy, including its objective and general guidelines. It also includes the ways to ensure email security which covers the installation of antivirus and spam filters. Introducing IT Policy Email And Chat Policy Objective And Guidelines Ppt Diagrams to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Objective, General Guidelines, Email Security, using this template. Grab it now to reap its full benefits.
-
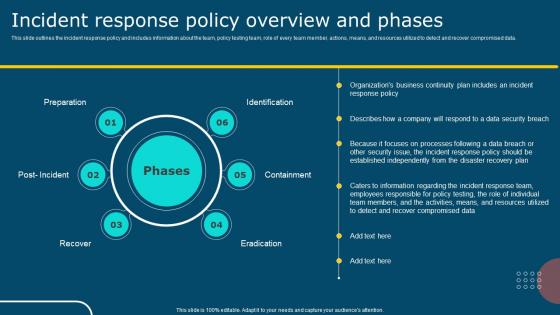 IT Policy Incident Response Policy Overview And Phases
IT Policy Incident Response Policy Overview And PhasesThis slide outlines the incident response policy and includes information about the team, policy testing team, role of every team member, actions, means, and resources utilized to detect and recover compromised data. Introducing IT Policy Incident Response Policy Overview And Phases to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Preparation, Identification, Containment, Post Recover, using this template. Grab it now to reap its full benefits.
-
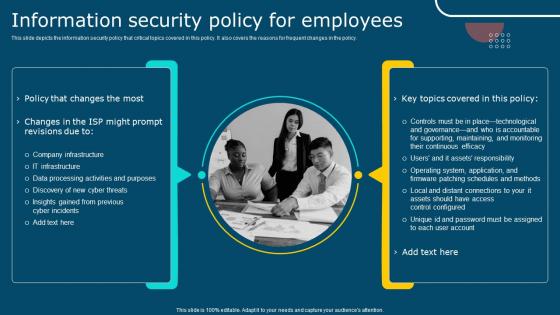 IT Policy Information Security Policy For Employees Ppt Professional
IT Policy Information Security Policy For Employees Ppt ProfessionalThis slide depicts the information security policy that critical topics covered in this policy. It also covers the reasons for frequent changes in the policy. Introducing IT Policy Information Security Policy For Employees Ppt Professional to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Company Infrastructure, Policy That Changes , Key Topics Covered, using this template. Grab it now to reap its full benefits.
-
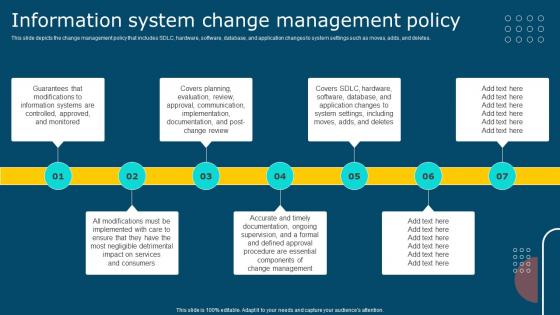 IT Policy Information System Change Management Policy
IT Policy Information System Change Management PolicyThis slide depicts the change management policy that includes SDLC, hardware, software, database, and application changes to system settings such as moves, adds, and deletes. Introducing IT Policy Information System Change Management Policy to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Information System, Management Policy, Approved, Controlled, using this template. Grab it now to reap its full benefits.
-
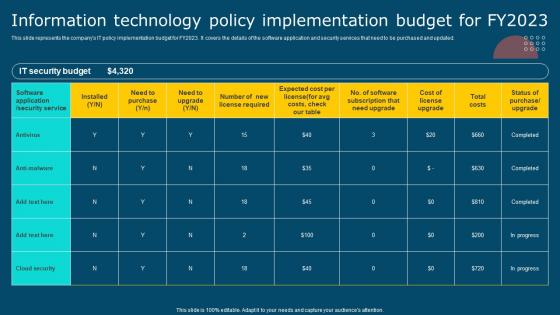 IT Policy Information Technology Policy Implementation Budget For Fy2023
IT Policy Information Technology Policy Implementation Budget For Fy2023This slide represents the companys IT policy implementation budget for FY2023. It covers the details of the software application and security services that need to be purchased and updated. Present the topic in a bit more detail with this IT Policy Information Technology Policy Implementation Budget For Fy2023. Use it as a tool for discussion and navigation on IT Security Budget, Antivirus, Anti Malware. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
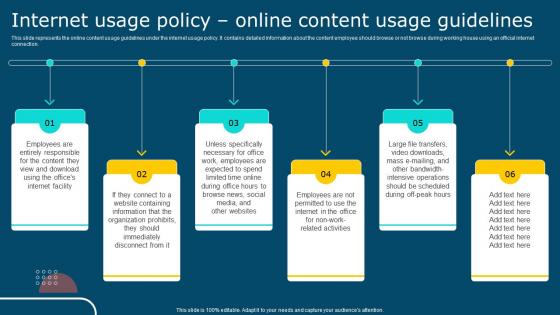 IT Policy Internet Usage Policy Online Content Usage Guidelines
IT Policy Internet Usage Policy Online Content Usage GuidelinesThis slide represents the online content usage guidelines under the internet usage policy. It contains detailed information about the content employee should browse or not browse during working house using an official internet connection. Introducing IT Policy Internet Usage Policy Online Content Usage Guidelines to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Internet Usage Policy, Online Content, Guidelines, using this template. Grab it now to reap its full benefits.
-
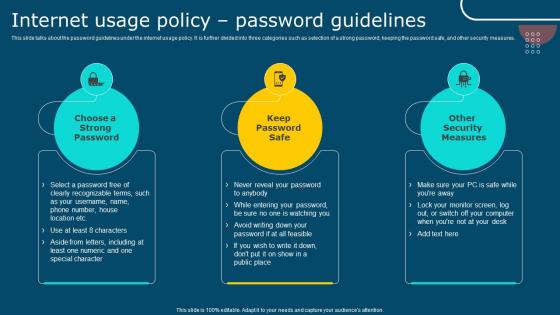 IT Policy Internet Usage Policy Password Guidelines Ppt Diagrams
IT Policy Internet Usage Policy Password Guidelines Ppt DiagramsThis slide talks about the password guidelines under the internet usage policy. It is further divided into three categories such as selection of a strong password, keeping the password safe, and other security measures. Introducing IT Policy Internet Usage Policy Password Guidelines Ppt Diagrams to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Choose A Strong Password, Keep Password Safe, Other Security Measures, using this template. Grab it now to reap its full benefits.
-
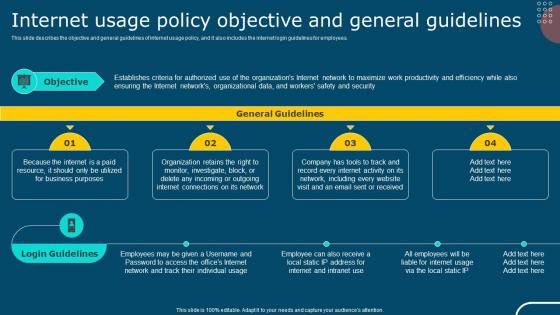 IT Policy Internet Usage Policy Objective And General Guidelines
IT Policy Internet Usage Policy Objective And General GuidelinesThis slide describes the objective and general guidelines of internet usage policy, and it also includes the internet login guidelines for employees. Introducing IT Policy Internet Usage Policy Objective And General Guidelines to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on General Guidelines, Login Guidelines, Objective, using this template. Grab it now to reap its full benefits.
-
 IT Policy Introduction To Information Technology Policy
IT Policy Introduction To Information Technology PolicyThis slide represents the introduction to information technology policy, and it also describes the components of IT policy, such as investments, business applications, architecture, and infrastructure. Introducing IT Policy Introduction To Information Technology Policy to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Introduction, Information, Technology Policy, using this template. Grab it now to reap its full benefits.
-
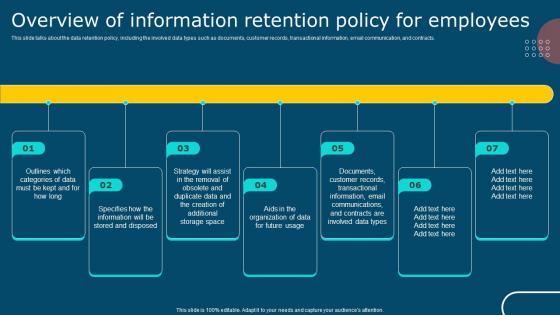 IT Policy Overview Of Information Retention Policy For Employees
IT Policy Overview Of Information Retention Policy For EmployeesThis slide talks about the data retention policy, including the involved data types such as documents, customer records, transactional information, email communication, and contracts. Introducing IT Policy Overview Of Information Retention Policy For Employees to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Documents, Customer Records, Information Retention, Email Communications, using this template. Grab it now to reap its full benefits.
-
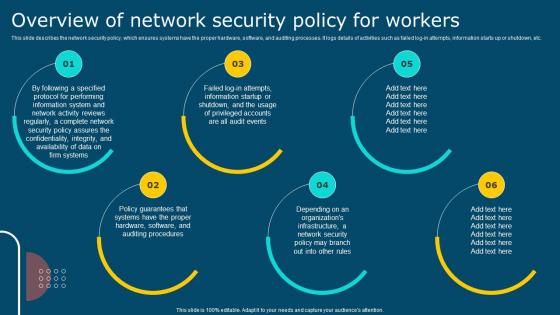 IT Policy Overview Of Network Security Policy For Workers Ppt Diagrams
IT Policy Overview Of Network Security Policy For Workers Ppt DiagramsThis slide describes the network security policy, which ensures systems have the proper hardware, software, and auditing processes. It logs details of activities such as failed log-in attempts, information starts up or shutdown, etc. Introducing IT Policy Overview Of Network Security Policy For Workers Ppt Diagrams to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Network Security, Reviews Regularly, Confidentiality, Integrity, using this template. Grab it now to reap its full benefits.
-
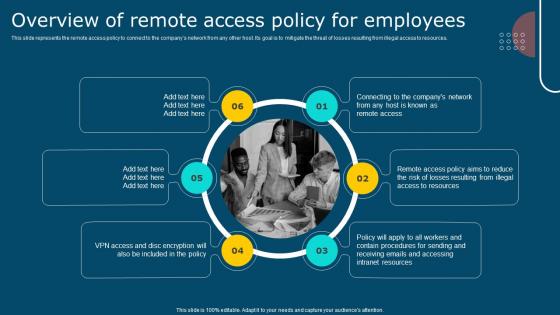 IT Policy Overview Of Remote Access Policy For Employees Ppt Diagrams
IT Policy Overview Of Remote Access Policy For Employees Ppt DiagramsThis slide represents the remote access policy to connect to the company network from any other host. Its goal is to mitigate the threat of losses resulting from illegal access to resources. Introducing IT Policy Overview Of Remote Access Policy For Employees Ppt Diagrams to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Remote Access, Policy For Employees, VPN Access, using this template. Grab it now to reap its full benefits.
-
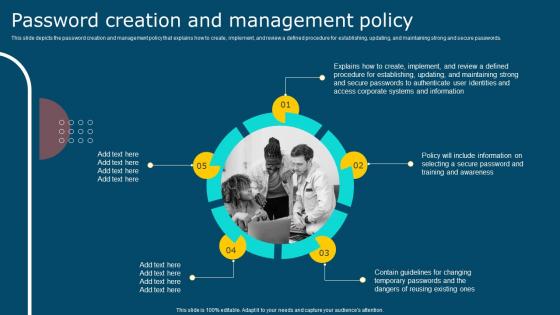 IT Policy Password Creation And Management Policy
IT Policy Password Creation And Management PolicyThis slide depicts the password creation and management policy that explains how to create, implement, and review a defined procedure for establishing, updating, and maintaining strong and secure passwords. Introducing IT Policy Password Creation And Management Policy to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Password Creation, Management Policy, Updating, using this template. Grab it now to reap its full benefits.
-
 IT Policy Roadmap To Develop An Information Technology Policy
IT Policy Roadmap To Develop An Information Technology PolicyThis slide represents the roadmap to developing an information technology policy, and it includes all the steps to be performed while developing an IT policy. Introducing IT Policy Roadmap To Develop An Information Technology Policy to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Roadmap, Develop An Information, Technology Policy, using this template. Grab it now to reap its full benefits.
-
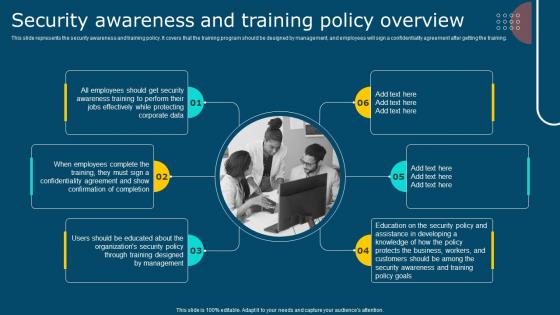 IT Policy Security Awareness And Training Policy Overview Ppt Diagrams
IT Policy Security Awareness And Training Policy Overview Ppt DiagramsThis slide represents the security awareness and training policy. It covers that the training program should be designed by management, and employees will sign a confidentiality agreement after getting the training. Introducing IT Policy Security Awareness And Training Policy Overview Ppt Diagrams to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Security Awareness, Training Policy, Training, using this template. Grab it now to reap its full benefits.
-
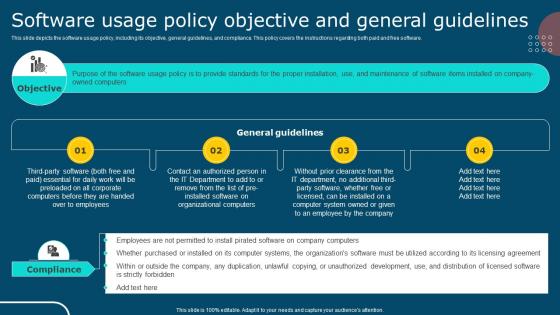 IT Policy Software Usage Policy Objective And General Guidelines
IT Policy Software Usage Policy Objective And General GuidelinesThis slide depicts the software usage policy, including its objective, general guidelines, and compliance. This policy covers the instructions regarding both paid and free software. Introducing IT Policy Software Usage Policy Objective And General Guidelines to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on General Guidelines, Compliance, Objective, using this template. Grab it now to reap its full benefits.
-
 IT Policy Termination Of Employment And Violation Of Byod Policy
IT Policy Termination Of Employment And Violation Of Byod PolicyThis slide talks about the termination of employment and violation of BYOD policy. Both include the actions to be performed if any employee leaves or violates the BYOD policy. Introducing IT Policy Termination Of Employment And Violation Of Byod Policy to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Termination, Violation, Corporate Policies, using this template. Grab it now to reap its full benefits.
-
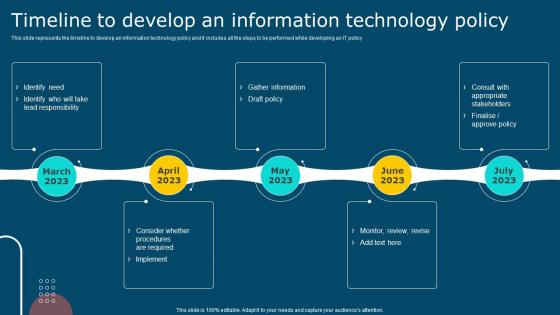 IT Policy Timeline To Develop An Information Technology Policy
IT Policy Timeline To Develop An Information Technology PolicyThis slide represents the timeline to develop an information technology policy and it includes all the steps to be performed while developing an IT policy. Introducing IT Policy Timeline To Develop An Information Technology Policy to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Timeline, Develop An Information, Technology Policy, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Policy Acceptable Use Of Equipment Policy Overview
Cyber Security Policy Acceptable Use Of Equipment Policy OverviewThis slide outlines the acceptable use policy, and it includes how official computers should be used, risks associated with improper usage, and appropriate behavior while handling sensitive information. Introducing Cyber Security Policy Acceptable Use Of Equipment Policy Overview to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Overview, Consumers, Information, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Policy Bring Your Own Device Byod Policy Objective And Scope
Cyber Security Policy Bring Your Own Device Byod Policy Objective And ScopeThis slide represents the bring your own device policy, including its objective and scope. It also includes the types of devices used in BYOD policy, which comprises cellphones, smartphones, tablets, laptops, and PCs. Present the topic in a bit more detail with this Cyber Security Policy Bring Your Own Device Byod Policy Objective And Scope. Use it as a tool for discussion and navigation on Technological, Compatibility, Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
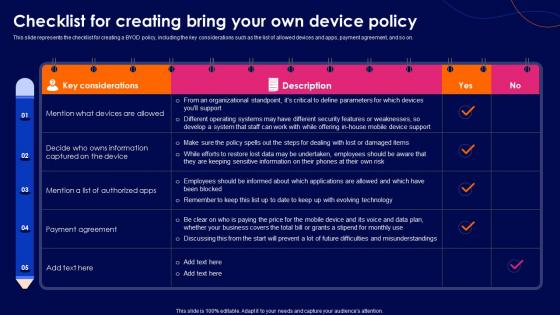 Cyber Security Policy Checklist For Creating Bring Your Own Device Policy
Cyber Security Policy Checklist For Creating Bring Your Own Device PolicyThis slide represents the checklist for creating a BYOD policy, including the key considerations such as the list of allowed devices and apps, payment agreement, and so on. Deliver an outstanding presentation on the topic using this Cyber Security Policy Checklist For Creating Bring Your Own Device Policy. Dispense information and present a thorough explanation of Considerations, Agreement, Represents using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Policy Checklist For Writing An Effective It Policy
Cyber Security Policy Checklist For Writing An Effective It PolicyThis slide describes the checklist for an effective information technology policy, and it includes all the best practices that should be considered while writing an IT policy. Present the topic in a bit more detail with this Cyber Security Policy Checklist For Writing An Effective It Policy. Use it as a tool for discussion and navigation on Assessment, Essential, Weaknesses. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
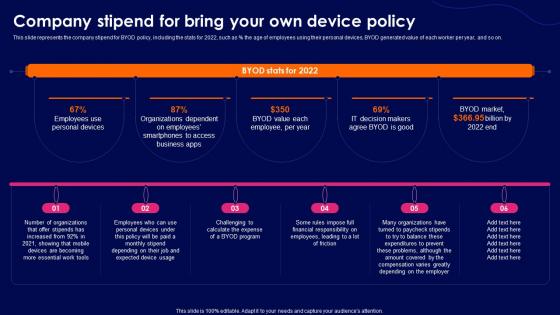 Cyber Security Policy Company Stipend For Bring Your Own Device Policy
Cyber Security Policy Company Stipend For Bring Your Own Device PolicyThis slide represents the company stipend for BYOD policy, including the stats for 2022, such as percent the age of employees using their personal devices, BYOD generated value of each worker per year, and so on. Present the topic in a bit more detail with this Cyber Security Policy Company Stipend For Bring Your Own Device Policy. Use it as a tool for discussion and navigation on Expenditures, Compensation, Organizations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
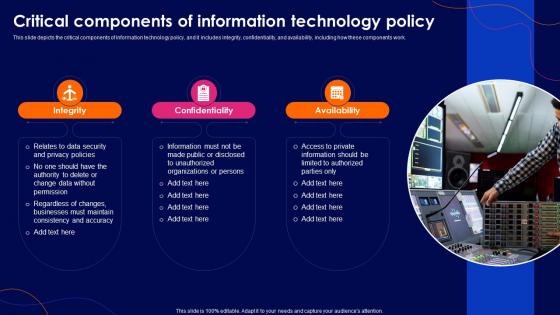 Cyber Security Policy Critical Components Of Information Technology Policy
Cyber Security Policy Critical Components Of Information Technology PolicyThis slide depicts the critical components of information technology policy, and it includes integrity, confidentiality, and availability, including how these components work. Deliver an outstanding presentation on the topic using this Cyber Security Policy Critical Components Of Information Technology Policy. Dispense information and present a thorough explanation of Information, Technology, Components using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Policy Data Classification Policy Overview And Approaches
Cyber Security Policy Data Classification Policy Overview And ApproachesThis slide represents the data classification policy overview and approaches. Approaches include highly restricted, restricted, and internal use and types of data each approach will include. Deliver an outstanding presentation on the topic using this Cyber Security Policy Data Classification Policy Overview And Approaches. Dispense information and present a thorough explanation of Highly Restricted, Approaches, Overview using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Policy Email And Chat Policy Objective And Guidelines
Cyber Security Policy Email And Chat Policy Objective And GuidelinesThis slide represents the email and chat policy, including its objective and general guidelines. It also includes the ways to ensure email security which covers the installation of antivirus and spam filters. Present the topic in a bit more detail with this Cyber Security Policy Email And Chat Policy Objective And Guidelines. Use it as a tool for discussion and navigation on Ownership, Confidentiality, Installation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
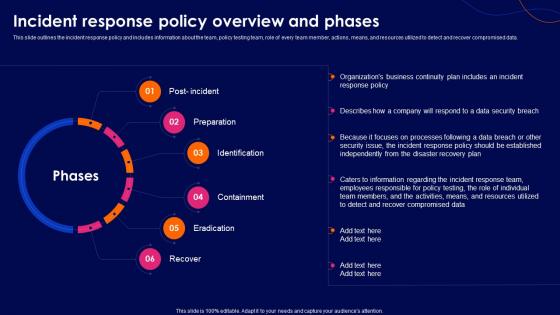 Cyber Security Policy Incident Response Policy Overview And Phases
Cyber Security Policy Incident Response Policy Overview And PhasesThis slide outlines the incident response policy and includes information about the team, policy testing team, role of every team member, actions, means, and resources utilized to detect and recover compromised data. Introducing Cyber Security Policy Incident Response Policy Overview And Phases to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Preparation, Identification, Containment, using this template. Grab it now to reap its full benefits.
-
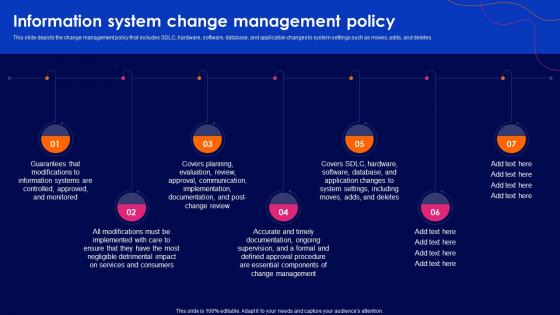 Cyber Security Policy Information System Change Management Policy
Cyber Security Policy Information System Change Management PolicyThis slide depicts the change management policy that includes SDLC, hardware, software, database, and application changes to system settings such as moves, adds, and deletes. Increase audience engagement and knowledge by dispensing information using Cyber Security Policy Information System Change Management Policy. This template helps you present information on seven stages. You can also present information on Information, Management, Documentation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
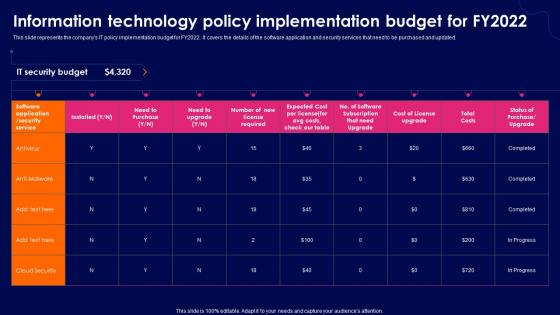 Cyber Security Policy Information Technology Policy Implementation Budget For Fy2022
Cyber Security Policy Information Technology Policy Implementation Budget For Fy2022This slide represents the companys IT policy implementation budget for FY2022. It covers the details of the software application and security services that need to be purchased and updated. Present the topic in a bit more detail with this Cyber Security Policy Information Technology Policy Implementation Budget For Fy2022. Use it as a tool for discussion and navigation on Information, Technology, Implementation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
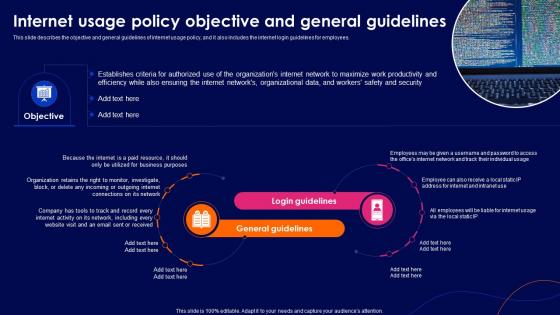 Cyber Security Policy Internet Usage Policy Objective And General Guidelines
Cyber Security Policy Internet Usage Policy Objective And General GuidelinesThis slide describes the objective and general guidelines of internet usage policy, and it also includes the internet login guidelines for employees. Deliver an outstanding presentation on the topic using this Cyber Security Policy Internet Usage Policy Objective And General Guidelines. Dispense information and present a thorough explanation of Organizational, Productivity, Business using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Policy Introduction To Information Technology Policy
Cyber Security Policy Introduction To Information Technology PolicyThis slide represents the introduction to information technology policy, and it also describes the components of IT policy, such as investments, business applications, architecture, and infrastructure. Increase audience engagement and knowledge by dispensing information using Cyber Security Policy Introduction To Information Technology Policy. This template helps you present information on seven stages. You can also present information on Introduction, Information, Technology using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Policy Overview Of Information Retention Policy For Employees
Cyber Security Policy Overview Of Information Retention Policy For EmployeesThis slide talks about the data retention policy, including the involved data types such as documents, customer records, transactional information, email communication, and contracts. Introducing Cyber Security Policy Overview Of Information Retention Policy For Employees to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Overview, Information, Communications, using this template. Grab it now to reap its full benefits.
-
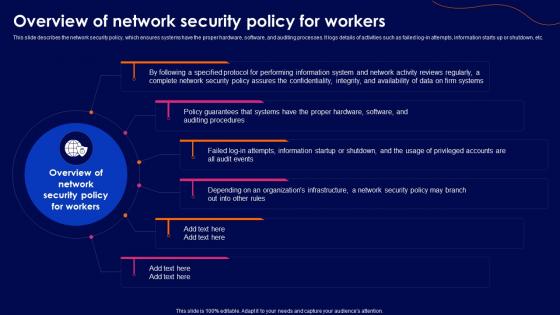 Cyber Security Policy Overview Of Network Security Policy For Workers
Cyber Security Policy Overview Of Network Security Policy For WorkersThis slide describes the network security policy, which ensures systems have the proper hardware, software, and auditing processes. It logs details of activities such as failed log-in attempts, information starts up or shutdown, etc. Increase audience engagement and knowledge by dispensing information using Cyber Security Policy Overview Of Network Security Policy For Workers. This template helps you present information on six stages. You can also present information on Overview, Information, Confidentiality using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Policy Overview Of Remote Access Policy For Employees
Cyber Security Policy Overview Of Remote Access Policy For EmployeesThis slide represents the remote access policy to connect to the companys network from any other host. Its goal is to mitigate the threat of losses resulting from illegal access to resources. Introducing Cyber Security Policy Overview Of Remote Access Policy For Employees to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Overview, Resources, Procedures, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Policy Password Creation And Management Policy
Cyber Security Policy Password Creation And Management PolicyThis slide depicts the password creation and management policy that explains how to create, implement, and review a defined procedure for establishing, updating, and maintaining strong and secure passwords. Increase audience engagement and knowledge by dispensing information using Cyber Security Policy Password Creation And Management Policy. This template helps you present information on five stages. You can also present information on Management, Information, Authenticate using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
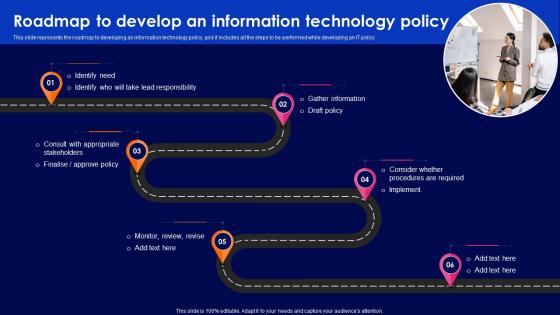 Cyber Security Policy Roadmap To Develop An Information Technology Policy
Cyber Security Policy Roadmap To Develop An Information Technology PolicyThis slide represents the roadmap to developing an information technology policy, and it includes all the steps to be performed while developing an IT policy. Introducing Cyber Security Policy Roadmap To Develop An Information Technology Policy to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Roadmap, Information, Technology, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Policy Security Awareness And Training Policy Overview
Cyber Security Policy Security Awareness And Training Policy OverviewThis slide represents the security awareness and training policy. It covers that the training program should be designed by management, and employees will sign a confidentiality agreement after getting the training. Increase audience engagement and knowledge by dispensing information using Cyber Security Policy Security Awareness And Training Policy Overview. This template helps you present information on six stages. You can also present information on Awareness, Overview, Business using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Policy Software Usage Policy Objective And General Guidelines
Cyber Security Policy Software Usage Policy Objective And General GuidelinesThis slide depicts the software usage policy, including its objective, general guidelines, and compliance. This policy covers the instructions regarding both paid and free software. Deliver an outstanding presentation on the topic using this Cyber Security Policy Software Usage Policy Objective And General Guidelines. Dispense information and present a thorough explanation of Software, Organizational Computers, Corporate using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Policy Termination Of Employment And Violation Of Byod Policy
Cyber Security Policy Termination Of Employment And Violation Of Byod PolicyThis slide talks about the termination of employment and violation of BYOD policy. Both include the actions to be performed if any employee leaves or violates the BYOD policy. Introducing Cyber Security Policy Termination Of Employment And Violation Of Byod Policy to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Employment, Termination, Business, using this template. Grab it now to reap its full benefits.
-
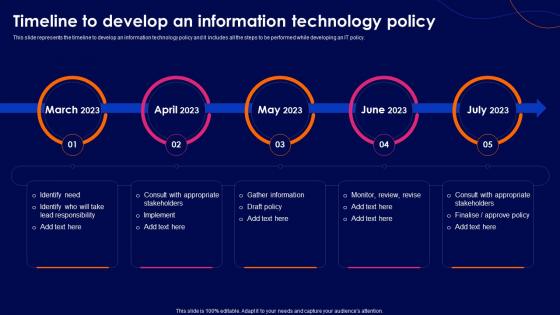 Cyber Security Policy Timeline To Develop An Information Technology Policy
Cyber Security Policy Timeline To Develop An Information Technology PolicyThis slide represents the timeline to develop an information technology policy and it includes all the steps to be performed while developing an IT policy. Introducing Cyber Security Policy Timeline To Develop An Information Technology Policy to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Timeline, Information, Technology, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Policy Vendor Management Policy Overview And Considerations
Cyber Security Policy Vendor Management Policy Overview And ConsiderationsThis slide represents the vendor management policy, and it also includes points to be considered when choosing a vendor. This policy is about the vendor with whom organizations share their critical information. Present the topic in a bit more detail with this Cyber Security Policy Vendor Management Policy Overview And Considerations. Use it as a tool for discussion and navigation on Management, Considerations, Overview. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 F982 Cyber Security Policy Information Security Policy For Employees
F982 Cyber Security Policy Information Security Policy For EmployeesThis slide depicts the information security policy that critical topics covered in this policy. It also covers the reasons for frequent changes in the policy. Present the topic in a bit more detail with this F982 Cyber Security Policy Information Security Policy For Employees. Use it as a tool for discussion and navigation on Information, Infrastructure, Responsibility. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 F983 Cyber Security Policy Internet Usage Policy Online Content Usage Guidelines
F983 Cyber Security Policy Internet Usage Policy Online Content Usage GuidelinesThis slide represents the online content usage guidelines under the internet usage policy. It contains detailed information about the content employee should browse or not browse during working house using an official internet connection. Introducing F983 Cyber Security Policy Internet Usage Policy Online Content Usage Guidelines to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Organization, Intensive, Information, using this template. Grab it now to reap its full benefits.
-
 F984 Cyber Security Policy Internet Usage Policy Password Guidelines
F984 Cyber Security Policy Internet Usage Policy Password GuidelinesThis slide talks about the password guidelines under the internet usage policy. It is further divided into three categories such as selection of a strong password, keeping the password safe, and other security measures. Deliver an outstanding presentation on the topic using this F984 Cyber Security Policy Internet Usage Policy Password Guidelines. Dispense information and present a thorough explanation of Measures, Recognizable, Location using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
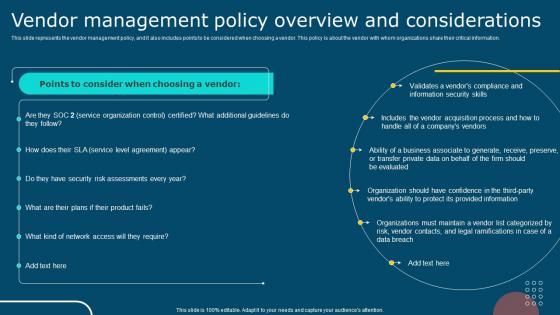 IT Policy Vendor Management Policy Overview And Considerations
IT Policy Vendor Management Policy Overview And ConsiderationsPresent the topic in a bit more detail with this IT Policy Vendor Management Policy Overview And Considerations. Use it as a tool for discussion and navigation on Points To Consider, Management Policy, Product Fails. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
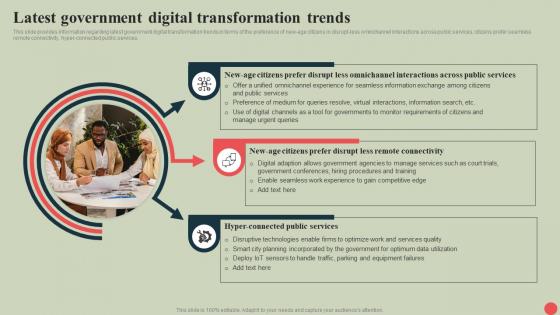 Government Digital Services Latest Government Digital Transformation Trends
Government Digital Services Latest Government Digital Transformation TrendsThis slide provides information regarding latest government digital transformation trends in terms of the preference of new-age citizens in disrupt-less omnichannel interactions across public services, citizens prefer seamless remote connectivity, hyper-connected public services. Increase audience engagement and knowledge by dispensing information using Government Digital Services Latest Government Digital Transformation Trends. This template helps you present information on three stages. You can also present information on Omnichannel Interactions, Remote Connectivity, Hyper Connected Public Services using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Government Digital Services Recommendations For Agencies And Policy Makers To Enable Digital
Government Digital Services Recommendations For Agencies And Policy Makers To Enable DigitalThis slide provides information regarding recommendations crucial for agencies and policymakers to enable digital transformation in terms of the involvement of non-technical government employees in digital service teams, managing legacy IT teams, determining value across digital service teams activities, etc. Introducing Government Digital Services Recommendations For Agencies And Policy Makers To Enable Digital to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Recommendations For Agencies, Recommendations For Policy Makers, IT Stakeholders, using this template. Grab it now to reap its full benefits.
-
 Global economic factors government policy ppt slides
Global economic factors government policy ppt slidesPresenting global economic factors government policy ppt slides. This is a global economic factors government policy ppt slides. This is a four stage process. The stages in this process are forces influencing industry, technological change, government policy, global economic factors.
-
 Csr with environment society governance and action policy
Csr with environment society governance and action policyPresenting this set of slides with name - Csr With Environment Society Governance And Action Policy. This is a three stage process. The stages in this process are Corporate Social Responsibility, Csr, Corporate Sustainability.
-
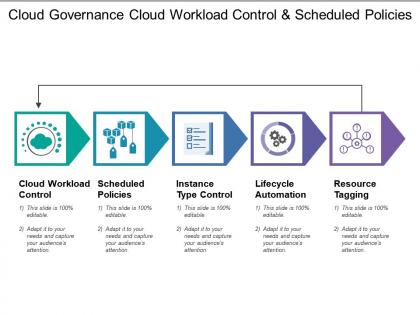 Cloud governance cloud workload control and scheduled policies
Cloud governance cloud workload control and scheduled policiesPresenting this set of slides with name - Cloud Governance Cloud Workload Control And Scheduled Policies. This is a five stage process. The stages in this process are Cloud Governance, Cloud Computing, Cloud Management.
-
 Cloud governance define roles security policies and processes
Cloud governance define roles security policies and processesPresenting this set of slides with name - Cloud Governance Define Roles Security Policies And Processes. This is a five stage process. The stages in this process are Cloud Governance, Cloud Computing, Cloud Management.
-
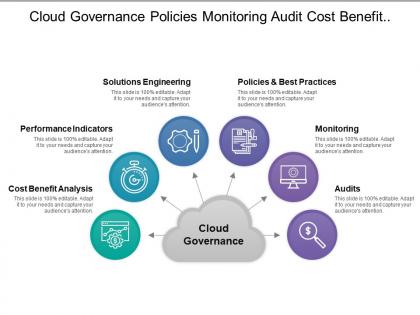 Cloud governance policies monitoring audit cost benefit analysis
Cloud governance policies monitoring audit cost benefit analysisPresenting this set of slides with name - Cloud Governance Policies Monitoring Audit Cost Benefit Analysis. This is a six stage process. The stages in this process are Cloud Governance, Cloud Computing, Cloud Management.
-
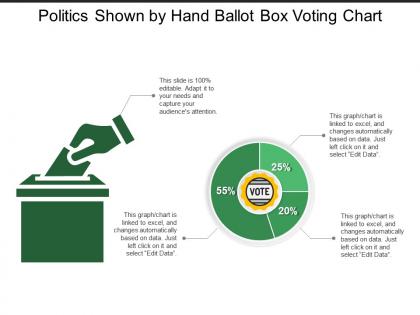 Politics shown by hand ballot box voting chart
Politics shown by hand ballot box voting chartPresenting this set of slides with name - Politics Shown By Hand Ballot Box Voting Chart. This is a two stage process. The stages in this process are Politics, Government, Public Affairs.
-
 Importance industry supplies strategic management framework government policies
Importance industry supplies strategic management framework government policiesPresenting this set of slides with name - Importance Industry Supplies Strategic Management Framework Government Policies. This is an editable five graphic that deals with topics like to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Market segment government politics strategies grow market demand
Market segment government politics strategies grow market demandPresenting this set of slides with name - Market Segment Government Politics Strategies Grow Market Demand. This is an editable four stages graphic that deals with topics like Market Segment, Government Politics, Strategies Grow Market Demand to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Future legislation regulatory process government policies government team change
Future legislation regulatory process government policies government team changePresenting this set of slides with name - Future Legislation Regulatory Process Government Policies Government Team Change. This is an editable two graphic that deals with topics like Future Legislation, Regulatory Process, Government Policies, Government Team Change to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.