Powerpoint Templates and Google slides for Handling Cyber Threats
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Addressing Various Ways To Handle Cyber Threats Management To Enable Digital Assets Security
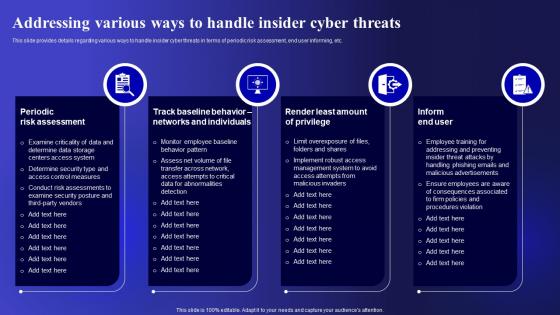
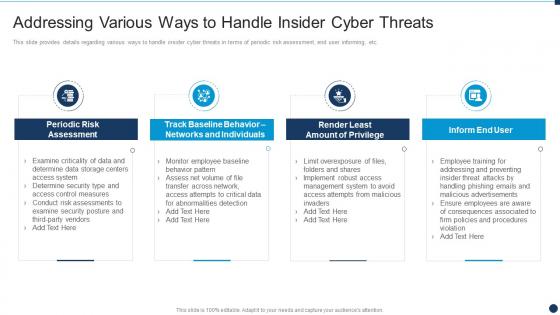
Addressing Various Ways To Handle Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding various ways to handle insider cyber threats in terms of periodic risk assessment, end user informing, etc. Present the topic in a bit more detail with this Addressing Various Ways To Handle Cyber Threats Management To Enable Digital Assets Security. Use it as a tool for discussion and navigation on Periodic Risk Assessment, Individuals, Implement. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Various Ways To Handle Insider Cyber Threats Vulnerability Administration At Workplace
Various Ways To Handle Insider Cyber Threats Vulnerability Administration At WorkplaceThis slide provides details regarding various ways to handle insider cyber threats in terms of periodic risk assessment, end user informing, etc. Present the topic in a bit more detail with this Various Ways To Handle Insider Cyber Threats Vulnerability Administration At Workplace. Use it as a tool for discussion and navigation on Assessment, Individuals, Management This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vulnerability Administration At Workplace Contingency Plan For Cyber Threat Handling
Vulnerability Administration At Workplace Contingency Plan For Cyber Threat HandlingThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations Deliver an outstanding presentation on the topic using this Vulnerability Administration At Workplace Contingency Plan For Cyber Threat Handling. Dispense information and present a thorough explanation of Contingency Plan For Cyber Threat Handling using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Vulnerability Administration At Workplace Various Ways To Handle Insider Cyber Threats Contd
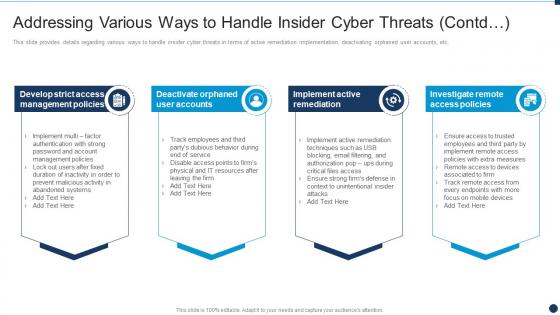
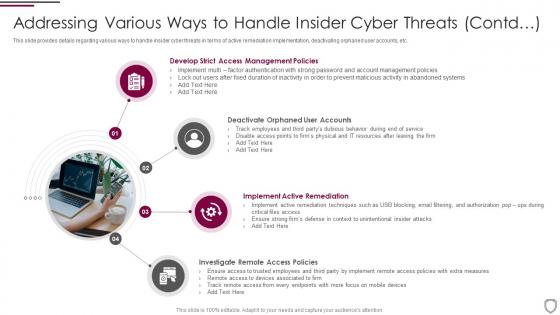
Vulnerability Administration At Workplace Various Ways To Handle Insider Cyber Threats ContdThis slide provides details regarding various ways to handle insider cyber threats in terms of active remediation implementation, deactivating orphaned user accounts, etc. Increase audience engagement and knowledge by dispensing information using Vulnerability Administration At Workplace Various Ways To Handle Insider Cyber Threats Contd. This template helps you present information on four stages. You can also present information on Management Policies, Remediation, Investigate Remote using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Incident Response Playbook Impact Categories For Effectively Handling Cyber Security Incidents
Incident Response Playbook Impact Categories For Effectively Handling Cyber Security IncidentsMentioned slide provides information about the impact categories which can be used for effectively handling various cyber security incidents. Categories covered are function, information and recoverability impact. Increase audience engagement and knowledge by dispensing information using Incident Response Playbook Impact Categories For Effectively Handling Cyber Security Incidents. This template helps you present information on three stages. You can also present information on Functional Impact, Information Impact, Recoverability Impact using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Addressing various ways to handle insider cyber threats corporate security management
Addressing various ways to handle insider cyber threats corporate security managementThis slide provides details regarding various ways to handle insider cyber threats in terms of active remediation implementation, deactivating orphaned user accounts, etc. Introducing Addressing Various Ways To Handle Insider Cyber Threats Corporate Security Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Management Policies, Implement Active Remediation, Investigate Remote Access Policies, Deactivate Orphaned User Accounts, using this template. Grab it now to reap its full benefits.
-
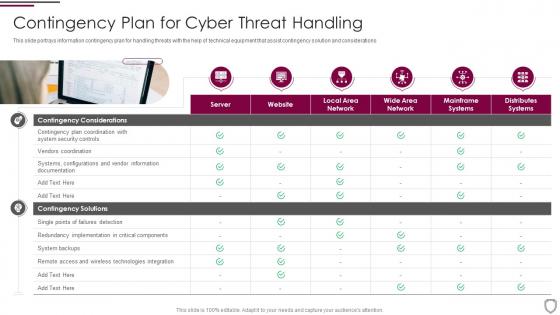 Contingency plan for cyber threat handling corporate security management
Contingency plan for cyber threat handling corporate security managementThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Increase audience engagement and knowledge by dispensing information using Contingency Plan For Cyber Threat Handling Corporate Security Management. This template helps you present information on one stages. You can also present information on Contingency Considerations, Contingency Solutions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
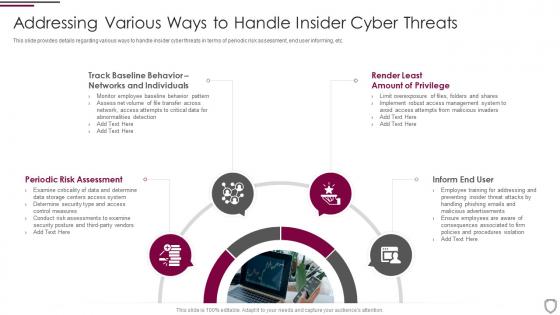 Corporate security management addressing various ways to handle insider cyber threats
Corporate security management addressing various ways to handle insider cyber threatsThis slide provides details regarding various ways to handle insider cyber threats in terms of periodic risk assessment, end user informing, etc. Introducing Corporate Security Management Addressing Various Ways To Handle Insider Cyber Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Periodic Risk Assessment, Inform End User, Render Least, Networks And Individuals, using this template. Grab it now to reap its full benefits.
-
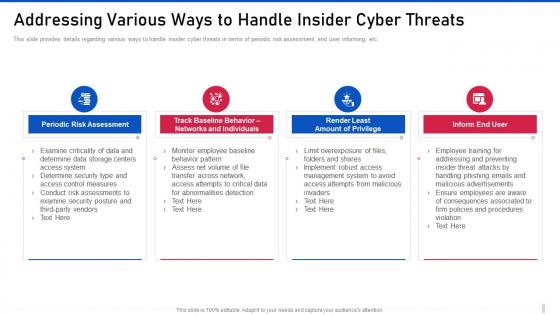 Addressing various ways to handle insider cyber threat management for organization critical
Addressing various ways to handle insider cyber threat management for organization criticalThis slide provides details regarding various ways to handle insider cyber threats in terms of periodic risk assessment, end user informing, etc. Introducing Addressing Various Ways To Handle Insider Cyber Threat Management For Organization Critical to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Periodic Risk Assessment, Networks And Individuals, Amount Of Privilege, using this template. Grab it now to reap its full benefits.
-
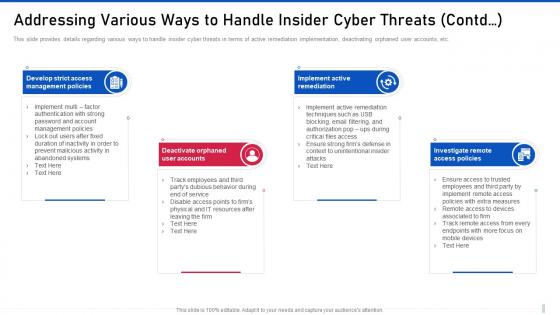 Threat management for organization critical addressing various ways to handle insider cyber threats contd
Threat management for organization critical addressing various ways to handle insider cyber threats contdThis slide provides details regarding various ways to handle insider cyber threats in terms of active remediation implementation, deactivating orphaned user accounts, etc. Introducing Threat Management For Organization Critical Addressing Various Ways To Handle Insider Cyber Threats Contd to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Management Policies, Deactivate Orphaned, Implement Active, using this template. Grab it now to reap its full benefits.
-
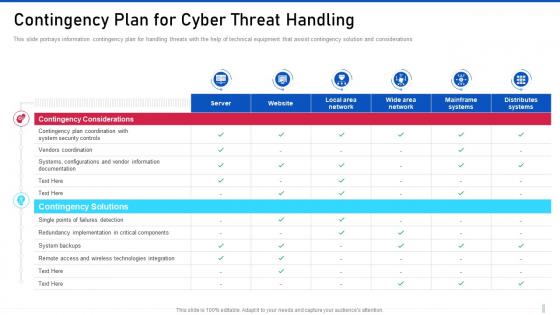 Threat management for organization critical contingency plan for cyber threat handling
Threat management for organization critical contingency plan for cyber threat handlingThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations Present the topic in a bit more detail with this Threat Management For Organization Critical Contingency Plan For Cyber Threat Handling. Use it as a tool for discussion and navigation on Contingency Considerations, Contingency Solutions, Remote Access. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
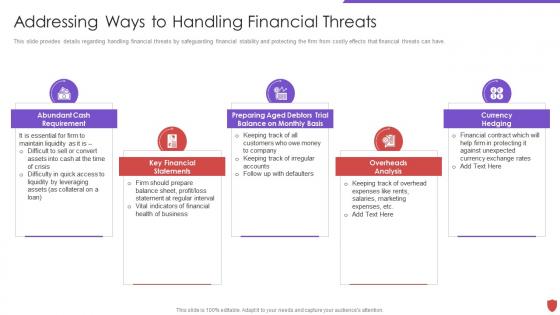 Addressing ways to handling financial threats cyber security risk management
Addressing ways to handling financial threats cyber security risk managementThis slide provides details regarding handling financial threats by safeguarding financial stability and protecting the firm from costly effects that financial threats can have. Introducing Addressing Ways To Handling Financial Threats Cyber Security Risk Management to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Abundant Cash Requirement, Key Financial Statements, Preparing Aged Debtors Trial Balance, using this template. Grab it now to reap its full benefits.
-
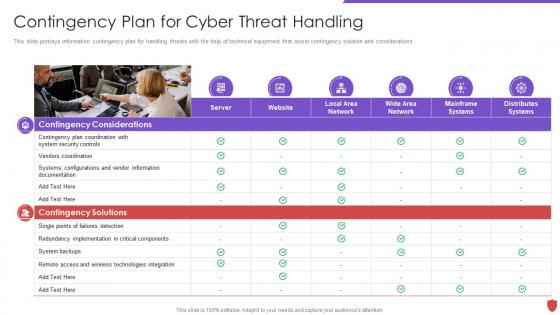 Cyber security risk management contingency plan for cyber threat handling
Cyber security risk management contingency plan for cyber threat handlingThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Introducing Cyber Security Risk Management Contingency Plan For Cyber Threat Handling to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Contingency Solutions, Contingency Considerations, System Backups, Vendors Coordination, using this template. Grab it now to reap its full benefits.
-
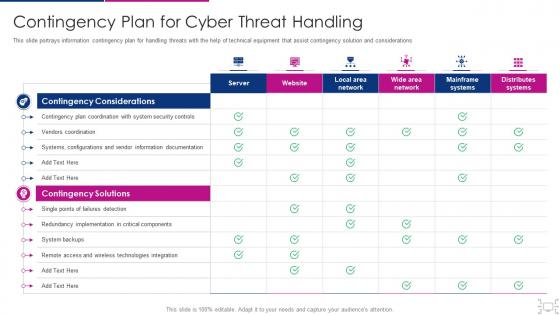 Cyber threat management workplace contingency plan cyber threat handling
Cyber threat management workplace contingency plan cyber threat handlingThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Deliver an outstanding presentation on the topic using this Cyber Threat Management Workplace Contingency Plan Cyber Threat Handling. Dispense information and present a thorough explanation of Contingency Solutions, Contingency Considerations, System Backups, Vendors Coordination using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
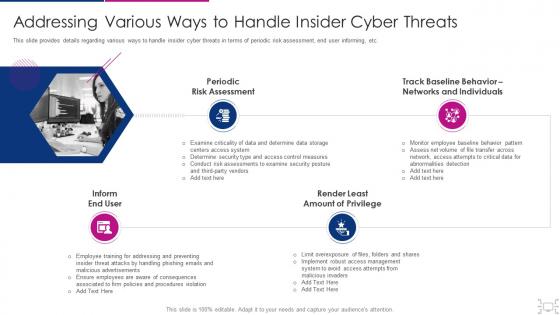 Cyber threat management workplace addressing various ways handle insider
Cyber threat management workplace addressing various ways handle insiderThis slide provides details regarding various ways to handle insider cyber threats in terms of periodic risk assessment, end user informing, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threat Management Workplace Addressing Various Ways Handle Insider. This template helps you present information on four stages. You can also present information on Periodic Risk Assessment, Inform End User, Render Least Amount Privilege, Track Baseline Behavior, Networks And Individuals using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
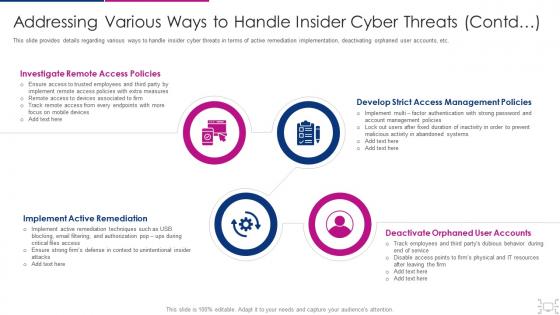 Cyber threat management workplace addressing various ways to handle insider
Cyber threat management workplace addressing various ways to handle insiderThis slide provides details regarding various ways to handle insider cyber threats in terms of active remediation implementation, deactivating orphaned user accounts, etc. Introducing Cyber Threat Management Workplace Addressing Various Ways To Handle Insider to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Investigate Remote Access Policies, Develop Strict Access Management Policies, Deactivate Orphaned User Accounts, Implement Active Remediation , using this template. Grab it now to reap its full benefits.
-
 Cyber threat management workplace addressing ways to handling financial
Cyber threat management workplace addressing ways to handling financialThis slide provides details regarding handling financial threats by safeguarding financial stability and protecting the firm from costly effects that financial threats can have. Increase audience engagement and knowledge by dispensing information using Cyber Threat Management Workplace Addressing Ways To Handling Financial. This template helps you present information on five stages. You can also present information on Abundant Cash Requirement, Key Financial Statements, Preparing Aged Debtors Trial Balance, Monthly Basis, Overheads Analysis Currency Hedging using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
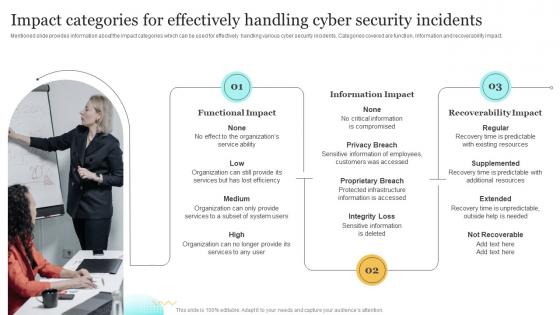 Impact Categories For Effectively Handling Cyber Upgrading Cybersecurity With Incident Response Playbook
Impact Categories For Effectively Handling Cyber Upgrading Cybersecurity With Incident Response PlaybookMentioned slide provides information about the impact categories which can be used for effectively handling various cyber security incidents. Categories covered are function, information and recoverability impact. Present the topic in a bit more detail with this Impact Categories For Effectively Handling Cyber Upgrading Cybersecurity With Incident Response Playbook. Use it as a tool for discussion and navigation on Functional Impact, Information Impact, Recoverability Impact. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
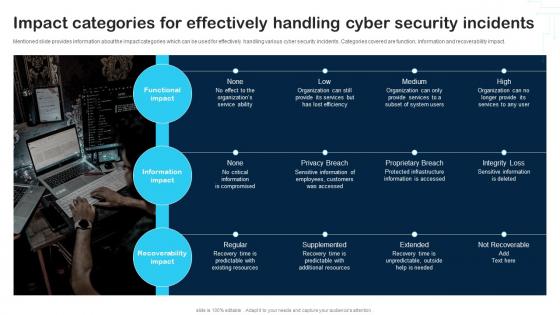 Impact Categories For Effectively Handling Cyber Security Incidents Cybersecurity Incident And Vulnerability
Impact Categories For Effectively Handling Cyber Security Incidents Cybersecurity Incident And VulnerabilityMentioned slide provides information about the impact categories which can be used for effectively handling various cyber security incidents. Categories covered are function, information and recoverability impact. Increase audience engagement and knowledge by dispensing information using Impact Categories For Effectively Handling Cyber Security Incidents Cybersecurity Incident And Vulnerability. This template helps you present information on three stages. You can also present information on Functional Impact, Information Impact, Recoverability Impact using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
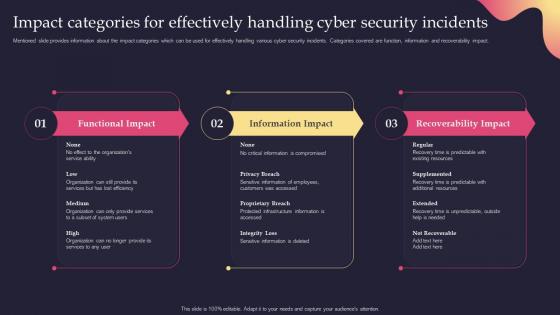 Security Incident Response Playbook Impact Categories For Effectively Handling Cyber Security Incidents
Security Incident Response Playbook Impact Categories For Effectively Handling Cyber Security IncidentsMentioned slide provides information about the impact categories which can be used for effectively handling various cyber security incidents. Categories covered are function, information and recoverability impact. Present the topic in a bit more detail with this Security Incident Response Playbook Impact Categories For Effectively Handling Cyber Security Incidents. Use it as a tool for discussion and navigation on Categories, Effectively, Information Impact. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Incident Handling Checklist Ppt Powerpoint Presentation Model Introduction
Cyber Security Incident Handling Checklist Ppt Powerpoint Presentation Model IntroductionThis slide represents the checklist to ensure activities to effectively handle and manage cyber security incidents. It includes details related to detection and analysis, containment, eradication and recovery and post incident activity. Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Handling Checklist Ppt Powerpoint Presentation Model Introduction. This template helps you present information on one stage. You can also present information on Detection And Analysis, Containment, Eradication And Recovery using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
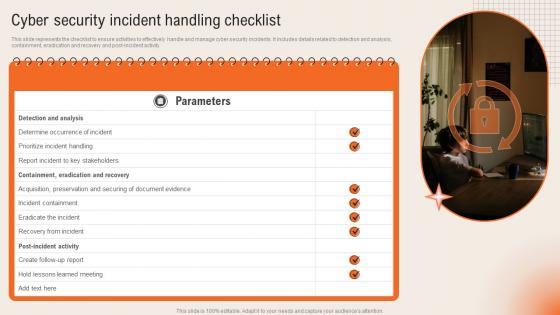 Cyber Security Incident Handling Checklist Deploying Computer Security Incident Management
Cyber Security Incident Handling Checklist Deploying Computer Security Incident ManagementThis slide represents the checklist to ensure activities to effectively handle and manage cyber security incidents. It includes details related to detection and analysis, containment, eradication and recovery and post incident activity.Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Handling Checklist Deploying Computer Security Incident Management. This template helps you present information on one stage. You can also present information on Containment Eradication, Acquisition Preservation, Incident Containment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
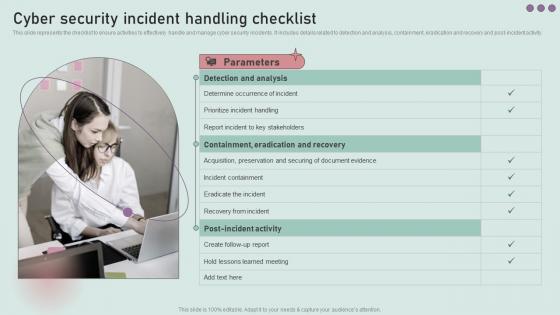 Cyber Security Incident Handling Checklist Development And Implementation Of Security
Cyber Security Incident Handling Checklist Development And Implementation Of SecurityThis slide represents the checklist to ensure activities to effectively handle and manage cyber security incidents. It includes details related to detection and analysis, containment, eradication and recovery and post incident activity. Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Handling Checklist Development And Implementation Of Security. This template helps you present information on three stages. You can also present information on Detection And Analysis, Prioritize Incident Handling, Incident Containment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
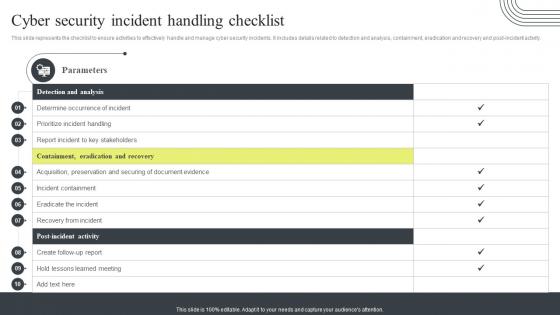 Cyber Security Incident Handling Checklist Cyber Security Attacks Response Plan
Cyber Security Incident Handling Checklist Cyber Security Attacks Response PlanThis slide represents the checklist to ensure activities to effectively handle and manage cyber security incidents. It includes details related to detection and analysis, containment, eradication and recovery and post incident activity. Present the topic in a bit more detail with this Cyber Security Incident Handling Checklist Cyber Security Attacks Response Plan. Use it as a tool for discussion and navigation on Containment, Eradication And Recovery, Detection And Analysis, Handling Checklist Acquisition. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Incident Handling Checklist Incident Response Strategies Deployment
Cyber Security Incident Handling Checklist Incident Response Strategies DeploymentThis slide represents the checklist to ensure activities to effectively handle and manage cyber security incidents. It includes details related to detection and analysis, containment, eradication and recovery and post incident activity. Introducing Cyber Security Incident Handling Checklist Incident Response Strategies Deployment to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Parameters, Analysis, Containment, using this template. Grab it now to reap its full benefits.
-
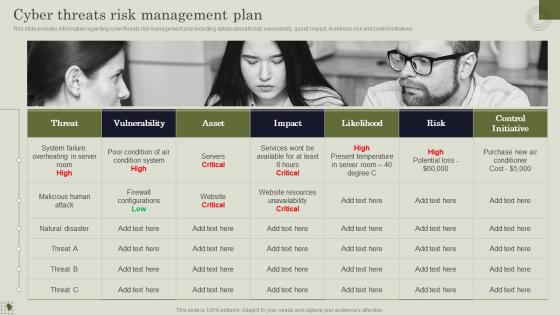 Cyber Threats Risk Management Plan Handling Pivotal Assets Associated With Firm
Cyber Threats Risk Management Plan Handling Pivotal Assets Associated With FirmThis slide provides information regarding cyber threats risk management plan including details about threat, vulnerability, asset, impact, likelihood, risk and control initiatives. Present the topic in a bit more detail with this Cyber Threats Risk Management Plan Handling Pivotal Assets Associated With Firm. Use it as a tool for discussion and navigation on Management, Vulnerability, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Various Cyber Threats Existing At Workplace Handling Pivotal Assets Associated With Firm
Various Cyber Threats Existing At Workplace Handling Pivotal Assets Associated With FirmThis slide provides information regarding various types of cyberthreats existing at workspace in terms of malware, ransomware, etc. The sources of cyber threats include criminal groups, hackers, etc. Introducing Various Cyber Threats Existing At Workplace Handling Pivotal Assets Associated With Firm to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Ransomware, Phishing, Spear Phishing , using this template. Grab it now to reap its full benefits.

