Powerpoint Templates and Google slides for How Security Concerns Affect Firm In Present Times
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 How to present cyber security to senior management complete deck
How to present cyber security to senior management complete deckThis complete deck can be used to present to your team. It has PPT slides on various topics highlighting all the core areas of your business needs. This complete deck focuses on How To Present Cyber Security To Senior Management Complete Deck and has professionally designed templates with suitable visuals and appropriate content. This deck consists of total of fifty five slides. All the slides are completely customizable for your convenience. You can change the colour, text and font size of these templates. You can add or delete the content if needed. Get access to this professionally designed complete presentation by clicking the download button below.
-
 How Amazon Is Securing Competitive Edge Across Globe Powerpoint Ppt Template Bundles Strategy MD
How Amazon Is Securing Competitive Edge Across Globe Powerpoint Ppt Template Bundles Strategy MDIntroduce your topic and host expert discussion sessions with this How Amazon Is Securing Competitive Edge Across Globe Powerpoint Ppt Template Bundles Strategy MD. This template is designed using high-quality visuals, images, graphics, etc, that can be used to showcase your expertise. Different topics can be tackled using the seventeen slides included in this template. You can present each topic on a different slide to help your audience interpret the information more effectively. Apart from this, this PPT slideshow is available in two screen sizes, standard and widescreen making its delivery more impactful. This will not only help in presenting a birds-eye view of the topic but also keep your audience engaged. Since this PPT slideshow utilizes well-researched content, it induces strategic thinking and helps you convey your message in the best possible manner. The biggest feature of this design is that it comes with a host of editable features like color, font, background, etc. So, grab it now to deliver a unique presentation every time.
-
 How Should You Approach Cloud Security Training Ppt
How Should You Approach Cloud Security Training PptPresenting How should you approach Cloud Security. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
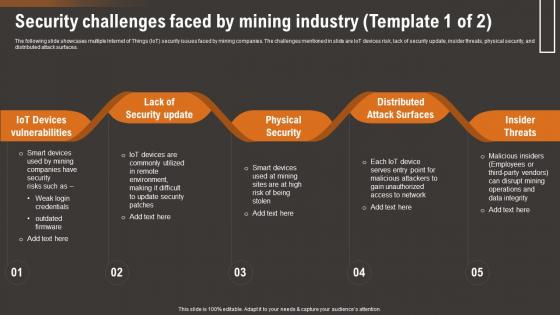 Security Challenges Faced By Mining Industry How IoT Technology Is Transforming IoT SS
Security Challenges Faced By Mining Industry How IoT Technology Is Transforming IoT SSThe following slide showcases multiple Internet of Things IoT security issues faced by mining companies. The challenges mentioned in slide are IoT devices risk, lack of security update, insider threats, physical security, and distributed attack surfaces. Present the topic in a bit more detail with this Security Challenges Faced By Mining Industry How IoT Technology Is Transforming IoT SS. Use it as a tool for discussion and navigation on Iot Devices Vulnerabilities, Lack Security Update, Physical Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
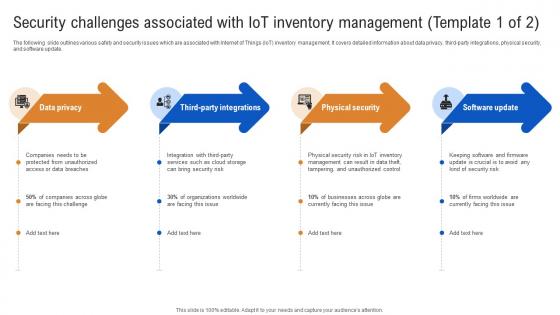 Security Challenges Associated With IoT Inventory How IoT In Inventory Management Streamlining IoT SS
Security Challenges Associated With IoT Inventory How IoT In Inventory Management Streamlining IoT SSThe following slide outlines various safety and security issues which are associated with Internet of Things IoT inventory management. It covers detailed information about data privacy, third-party integrations, physical security, and software update. Introducing Security Challenges Associated With IoT Inventory How IoT In Inventory Management Streamlining IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Data Privacy, Physical Security, Software Update, using this template. Grab it now to reap its full benefits.
-
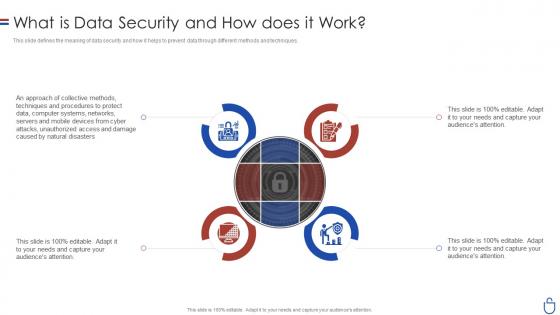 Data security it what is data security and how does it work
Data security it what is data security and how does it workThis slide defines the meaning of data security and how it helps to prevent data through different methods and techniques. Introducing Data Security IT What Is Data Security And How Does IT Work to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Collective Methods, Protect Data, Computer Systems, Networks, Servers And Mobile Devices, using this template. Grab it now to reap its full benefits.
-
 Computer system security how is automation used in computer security
Computer system security how is automation used in computer securityThis slide depicts the cyber protection of an organization through artificial intelligence and how it can be helpful in threat detection, threat response, and human augmentation. Introducing Computer System Security How Is Automation Used In Computer Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Threat Detection, Threat Response, Human Augmentation, using this template. Grab it now to reap its full benefits.
-
 Computer system security what is computer security and how does it work
Computer system security what is computer security and how does it workThis slide defines the meaning of cyber security and how it helps to prevent data through different methods and techniques. Introducing Computer System Security What Is Computer Security And How Does It Work to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Techniques, Collective, Networks, Computer Systems, using this template. Grab it now to reap its full benefits.
-
 Data security it how is automation used in data security
Data security it how is automation used in data securityThis slide depicts the cyber protection of an organization through artificial intelligence and how it can be helpful in threat detection, threat response, and human augmentation. Present the topic in a bit more detail with this Data Security IT How Is Automation Used In Data Security. Use it as a tool for discussion and navigation on Threat Detection, Threat Response, Human Augmentation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
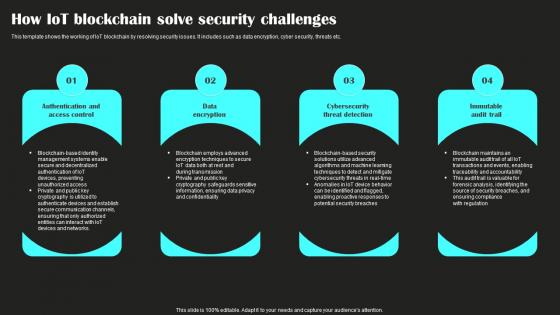 How Iot Blockchain Solve Security Challenges
How Iot Blockchain Solve Security ChallengesThis template shows the working of IoT blockchain by resolving security issues. It includes such as data encryption, cyber security, threats etc. Presenting our set of slides with How Iot Blockchain Solve Security Challenges. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Authentication Access Control, Data Encryption.
-
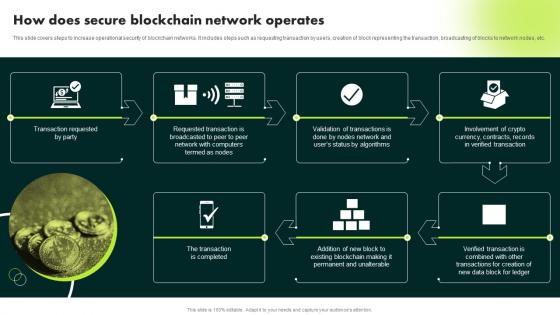 How Does Secure Blockchain Network Operates Ultimate Guide To Blockchain BCT SS
How Does Secure Blockchain Network Operates Ultimate Guide To Blockchain BCT SSThis slide covers steps to increase operational security of blockchain networks. It includes steps such as requesting transaction by users, creation of block representing the transaction, broadcasting of blocks to network nodes, etc. Introducing How Does Secure Blockchain Network Operates Ultimate Guide To Blockchain BCT SS to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Transaction Requested, Verified Transaction, Network Operates, using this template. Grab it now to reap its full benefits.
-
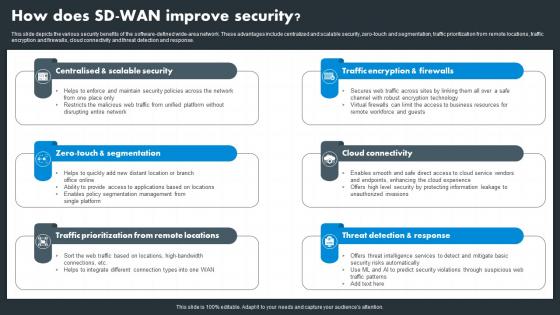
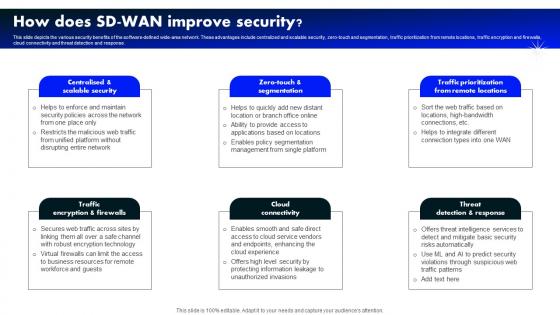
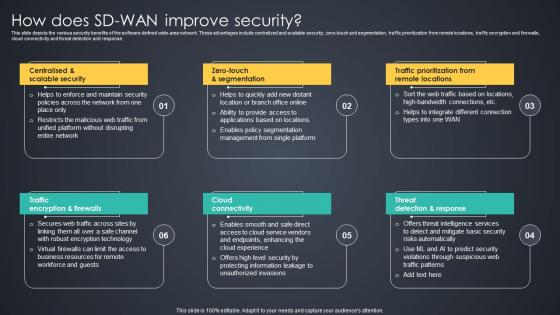 How Does SD WAN Improve Security Managed Wan Services
How Does SD WAN Improve Security Managed Wan ServicesThis slide depicts the various security benefits of the software defined wide area network. These advantages include centralized and scalable security, zero touch and segmentation, traffic prioritization from remote locations, traffic encryption and firewalls, cloud connectivity and threat detection and response.Increase audience engagement and knowledge by dispensing information using How Does SD WAN Improve Security Managed Wan Services. This template helps you present information on six stages. You can also present information on Traffic Prioritization, Business Resources, Encryption Technology using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
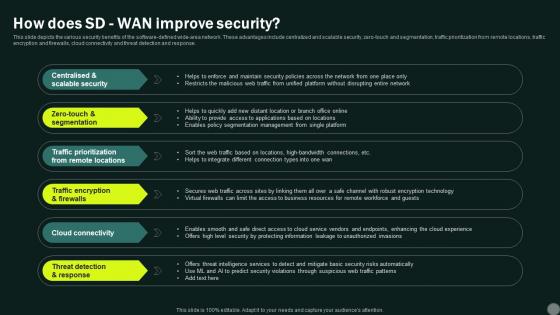 Intelligent Wan How Does Sd Wan Improve Security
Intelligent Wan How Does Sd Wan Improve SecurityThis slide depicts the various security benefits of the software-defined wide-area network. These advantages include centralized and scalable security, zero-touch and segmentation, traffic prioritization from remote locations, traffic encryption and firewalls, cloud connectivity and threat detection and response. Increase audience engagement and knowledge by dispensing information using Intelligent Wan How Does Sd Wan Improve Security. This template helps you present information on six stages. You can also present information on Centralised Scalable Security, Traffic Prioritization From Remote Locations, Traffic Encryption Firewalls using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
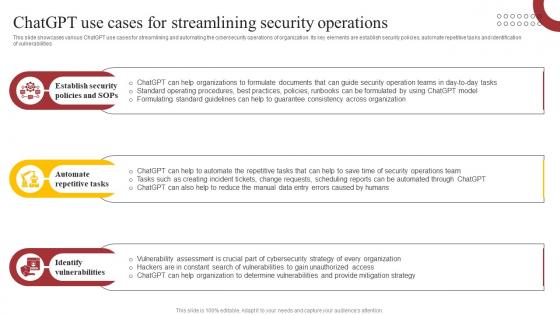 ChatGPT Use Cases For Streamlining Security How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SS
ChatGPT Use Cases For Streamlining Security How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SSThis slide showcases various ChatGPT use cases for streamlining and automating the cybersecurity operations of organization. Its key elements are establish security policies, automate repetitive tasks and identification of vulnerabilities Increase audience engagement and knowledge by dispensing information using ChatGPT Use Cases For Streamlining Security How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SS. This template helps you present information on three stages. You can also present information on Security, Policies, Repetitive using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
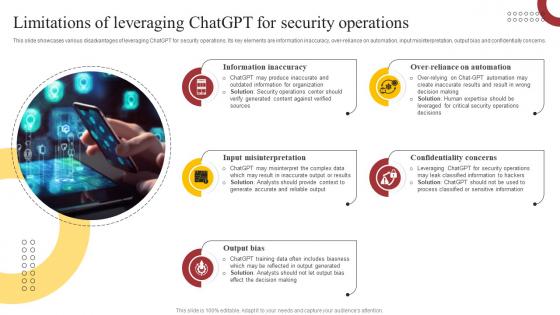 Limitations Of Leveraging ChatGPT For Security How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SS
Limitations Of Leveraging ChatGPT For Security How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SSThis slide showcases various disadvantages of leveraging ChatGPT for security operations. Its key elements are information inaccuracy, over reliance on automation, input misinterpretation, output bias and confidentially concerns. Introducing Limitations Of Leveraging ChatGPT For Security How ChatGPT Is Revolutionizing Cybersecurity ChatGPT SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Information, Automation, Concerns, using this template. Grab it now to reap its full benefits.
-
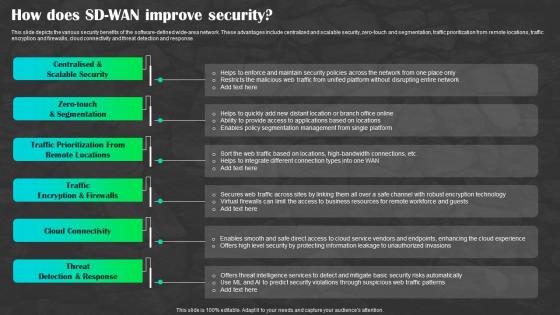 Sd Wan As A Service Sd Wan How Does Sd Wan Improve Security Ppt Formats
Sd Wan As A Service Sd Wan How Does Sd Wan Improve Security Ppt FormatsThis slide depicts the various security benefits of the software-defined wide-area network. These advantages include centralized and scalable security, zero-touch and segmentation, traffic prioritization from remote locations, traffic encryption and firewalls, cloud connectivity and threat detection and response. Introducing Sd Wan As A Service Sd Wan How Does Sd Wan Improve Security Ppt Formats to increase your presentation threshold. Encompassed with Six stages, this template is a great option to educate and entice your audience. Dispence information on Remote Locations, Encryption And Firewalls, Cloud Connectivity, using this template. Grab it now to reap its full benefits.
-
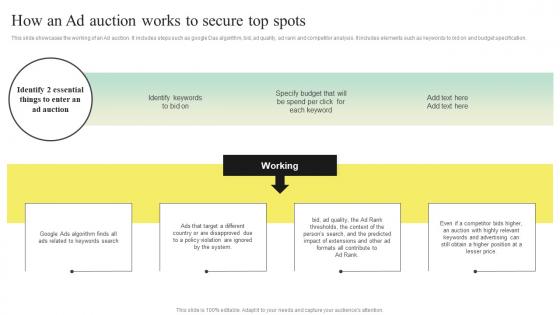 Search Engine Marketing Strategy To Enhance How An Ad Auction Works To Secure Top Spots MKT SS V
Search Engine Marketing Strategy To Enhance How An Ad Auction Works To Secure Top Spots MKT SS VThis slide showcases the working of an Ad auction. It includes steps such as google Das algorithm, bid, ad quality, ad rank and competitor analysis. It includes elements such as keywords to bid on and budget specification. Introducing Search Engine Marketing Strategy To Enhance How An Ad Auction Works To Secure Top Spots MKT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Algorithm, Violation Are Ignored, Extensions, using this template. Grab it now to reap its full benefits.
-
 Hybrid Wan How Does Sd Wan Improve Security
Hybrid Wan How Does Sd Wan Improve SecurityThis slide depicts the various security benefits of the software defined wide area network. These advantages include centralized and scalable security, zero touch and segmentation, traffic prioritization from remote locations, traffic encryption and firewalls, cloud connectivity and threat detection and response. Introducing Hybrid Wan How Does Sd Wan Improve Security to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Connectivity, Threat Detection Response, using this template. Grab it now to reap its full benefits.
-
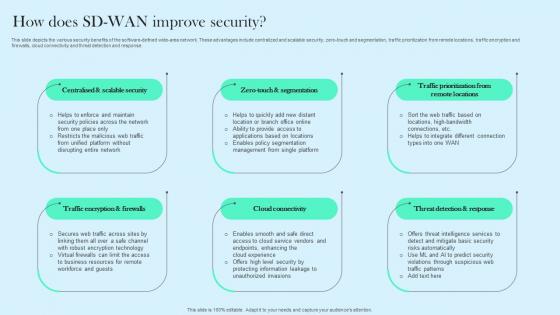 How Does SD WAN Improve Security Cloud WAN Ppt Infographics
How Does SD WAN Improve Security Cloud WAN Ppt InfographicsThis slide depicts the various security benefits of the software defined wide area network. These advantages include centralized and scalable security, zero touch and segmentation, traffic prioritization from remote locations, traffic encryption and firewalls, cloud connectivity and threat detection and response. Introducing How Does SD WAN Improve Security Cloud WAN Ppt Infographics to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Security, Segmentation, Locations, using this template. Grab it now to reap its full benefits.
-
 How Does Sd Wan Improve Security Software Defined Wide Area Network
How Does Sd Wan Improve Security Software Defined Wide Area NetworkThis slide depicts the various security benefits of the software-defined wide-area network. These advantages include centralized and scalable security, zero-touch and segmentation, traffic prioritization from remote locations, traffic encryption and firewalls, cloud connectivity and threat detection and response. Introducing How Does Sd Wan Improve Security Software Defined Wide Area Network to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Connectivity, Threat Detection Response, Traffic Prioritization From Remote Locations, using this template. Grab it now to reap its full benefits.
-
 Steps To Conduct Micro Segmentation And Security Stack How Digital Transformation DT SS
Steps To Conduct Micro Segmentation And Security Stack How Digital Transformation DT SSThis slide presents a strategy to conduct network micro-segmentation and rationalization of security stack. It includes steps such as identify and classify assets and data, implement network segmentation, apply security controls at segment boundaries, regularly review and update security stack. Increase audience engagement and knowledge by dispensing information using Steps To Conduct Micro Segmentation And Security Stack How Digital Transformation DT SS. This template helps you present information on four stages. You can also present information on Identify And Classify, Network Segmentation, Segment Boundaries using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
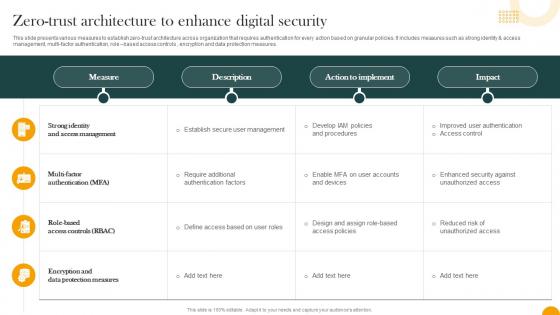 Zero Trust Architecture To Enhance Digital Security How Digital Transformation DT SS
Zero Trust Architecture To Enhance Digital Security How Digital Transformation DT SSThis slide presents various measures to establish zero-trust architecture across organization that requires authentication for every action based on granular policies. It includes measures such as strong identity and access management, multi-factor authentication, role based access controls , encryption and data protection measures. Deliver an outstanding presentation on the topic using this Zero Trust Architecture To Enhance Digital Security How Digital Transformation DT SS. Dispense information and present a thorough explanation of Protection Measures, Access Management, Role Based Access Controls using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
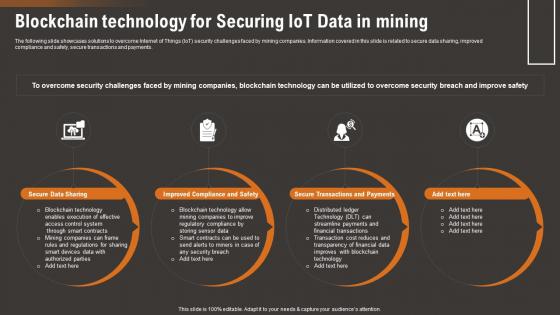 Blockchain Technology For Securing IoT Data How IoT Technology Is Transforming IoT SS
Blockchain Technology For Securing IoT Data How IoT Technology Is Transforming IoT SSThe following slide showcases solutions to overcome Internet of Things IoT security challenges faced by mining companies. Information covered in this slide is related to secure data sharing, improved compliance and safety, secure transactions and payments.Introducing Blockchain Technology For Securing IoT Data How IoT Technology Is Transforming IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Secure Data Sharing, Blockchain Technology, Enables Execution, using this template. Grab it now to reap its full benefits.
-
 Consequences Of Security Challenge On Mining How IoT Technology Is Transforming IoT SS
Consequences Of Security Challenge On Mining How IoT Technology Is Transforming IoT SSThe following slide showcases impact of Internet of Things IoT security challenges on mining companies. The slide covers information about unsafe working conditions, lost data, higher downtime, data leak, cost associated with security incident, loss of productivity, etc.Increase audience engagement and knowledge by dispensing information using Consequences Of Security Challenge On Mining How IoT Technology Is Transforming IoT SS. This template helps you present information on five stages. You can also present information on Compromised Smart, Working Conditions, Higher Downtime using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
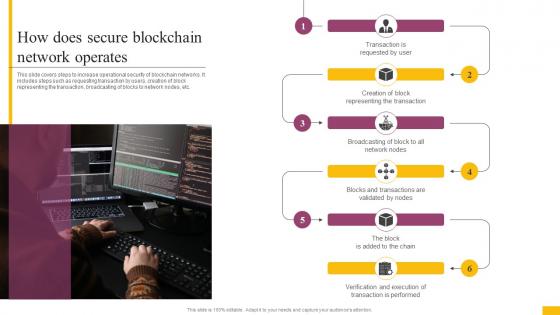 How Does Secure Blockchain Network Operates Complete Guide To Understand BCT SS
How Does Secure Blockchain Network Operates Complete Guide To Understand BCT SSThis slide covers steps to increase operational security of blockchain networks. It includes steps such as requesting transaction by users, creation of block representing the transaction, broadcasting of blocks to network nodes, etc. Introducing How Does Secure Blockchain Network Operates Complete Guide To Understand BCT SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Representing The Transaction, Network Nodes, Transaction Is Performed using this template. Grab it now to reap its full benefits.
-
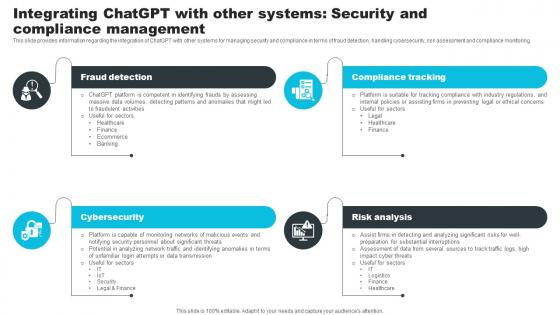 Integrating ChatGPT With Other Systems Security How ChatGPT Actually Work ChatGPT SS V
Integrating ChatGPT With Other Systems Security How ChatGPT Actually Work ChatGPT SS VThis slide provides information regarding the integration of ChatGPT with other systems for managing security and compliance in terms of fraud detection, handling cybersecurity, risk assessment and compliance monitoring. Increase audience engagement and knowledge by dispensing information using Integrating ChatGPT With Other Systems Security How ChatGPT Actually Work ChatGPT SS V. This template helps you present information on four stages. You can also present information on Fraud Detection, Compliance Tracking, Risk Analysis using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
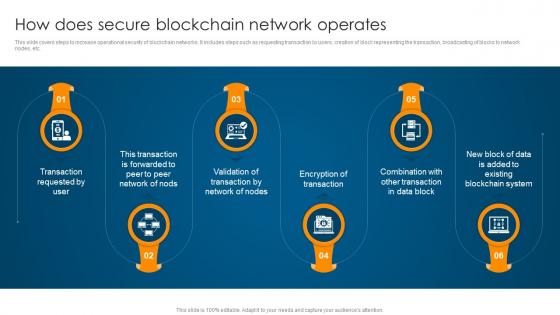 How Does Secure Blockchain Network Operates Ultimate Guide To Understand Role BCT SS
How Does Secure Blockchain Network Operates Ultimate Guide To Understand Role BCT SSThis slide covers steps to increase operational security of blockchain networks. It includes steps such as requesting transaction by users, creation of block representing the transaction, broadcasting of blocks to network nodes, etc. Introducing How Does Secure Blockchain Network Operates Ultimate Guide To Understand Role BCT SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Transaction Requested, Network Of Nodes, Encryption Of Transaction, using this template. Grab it now to reap its full benefits.
-
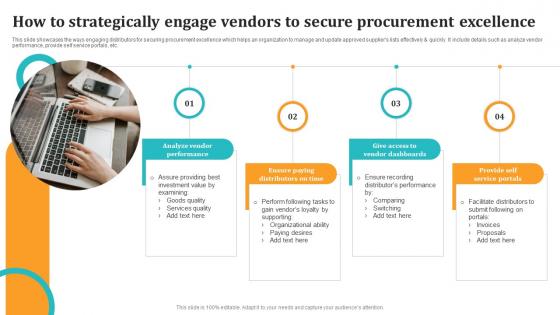 How To Strategically Engage Vendors To Secure Procurement Excellence
How To Strategically Engage Vendors To Secure Procurement ExcellenceThis slide showcases the ways engaging distributors for securing procurement excellence which helps an organization to manage and update approved suppliers lists effectively and quickly. It include details such as analyze vendor performance, provide self service portals, etc. Presenting our set of slides with How To Strategically Engage Vendors To Secure Procurement Excellence. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Analyze Vendor Performance, Service Portals, Vendor Dashboards.
-
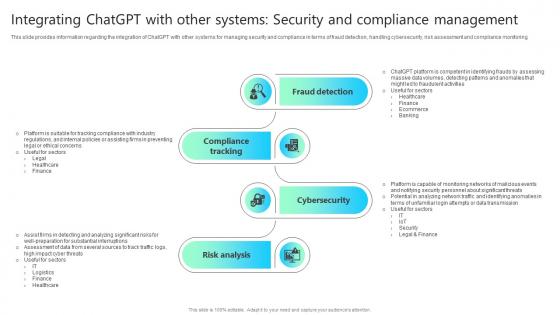 Integrating Chatgpt With Other Systems Security And Compliance Chatgpt Impact How ChatGPT SS V
Integrating Chatgpt With Other Systems Security And Compliance Chatgpt Impact How ChatGPT SS VThis slide provides information regarding the integration of ChatGPT with other systems for managing security and compliance in terms of fraud detection, handling cybersecurity, risk assessment and compliance monitoring. Increase audience engagement and knowledge by dispensing information using Integrating Chatgpt With Other Systems Security And Compliance Chatgpt Impact How ChatGPT SS V This template helps you present information on Four stages. You can also present information on Consumer Assistance, Sales Support, Customization, Consumer Feedback Assessment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
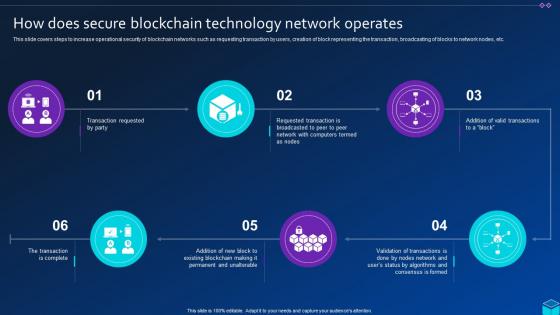 How Does Secure Blockchain Technology Comprehensive Approach To Privacy BCT SS
How Does Secure Blockchain Technology Comprehensive Approach To Privacy BCT SSThis slide covers steps to increase operational security of blockchain networks such as requesting transaction by users, creation of block representing the transaction, broadcasting of blocks to network nodes, etc. Introducing How Does Secure Blockchain Technology Comprehensive Approach To Privacy BCT SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Secure Blockchain Technology, Network Operates, using this template. Grab it now to reap its full benefits.
-
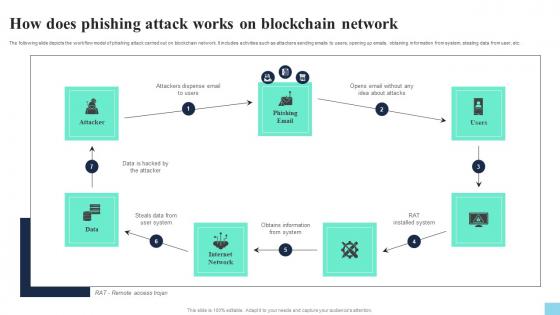 How Does Phishing Attack Works On Blockchain Network Hands On Blockchain Security Risk BCT SS V
How Does Phishing Attack Works On Blockchain Network Hands On Blockchain Security Risk BCT SS VThe following slide depicts the workflow model of phishing attack carried out on blockchain network. It includes activities such as attackers sending emails to users, opening up emails, obtaining information from system, stealing data from user, etc. Present the topic in a bit more detail with this How Does Phishing Attack Works On Blockchain Network Hands On Blockchain Security Risk BCT SS V. Use it as a tool for discussion and navigation on Attacker, Phishing Email, Internet Network. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
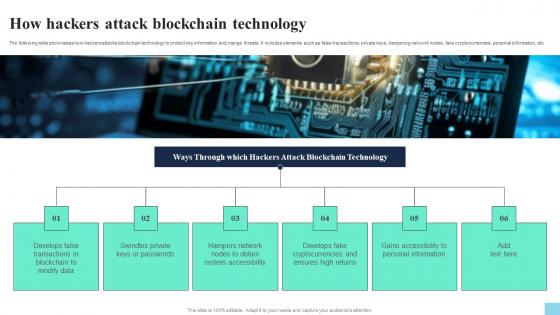 How Hackers Attack Blockchain Technology Hands On Blockchain Security Risk BCT SS V
How Hackers Attack Blockchain Technology Hands On Blockchain Security Risk BCT SS VThe following slide showcases how hackers attacks blockchain technology to protect key information and mange threats. It includes elements such as false transactions, private keys, hampering network nodes, fake cryptocurrencies, personal information, etc. Introducing How Hackers Attack Blockchain Technology Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Modify Data, Swindles Private, System Accessibility, using this template. Grab it now to reap its full benefits.
-
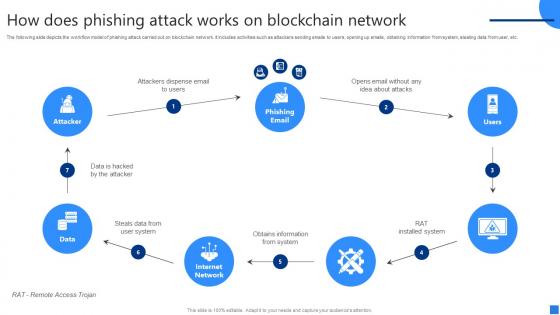 How Does Phishing Attack Works Securing Blockchain Transactions A Beginners Guide BCT SS V
How Does Phishing Attack Works Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide depicts the workflow model of phishing attack carried out on blockchain network. It includes activities such as attackers sending emails to users, opening up emails, obtaining information from system, stealing data from user, etc. Increase audience engagement and knowledge by dispensing information using How Does Phishing Attack Works Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on six stages. You can also present information on Attackers Dispense Email, Steals Data, Obtains Information From System using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
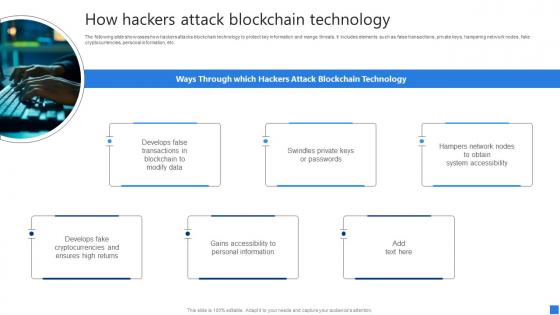 How Hackers Attack Blockchain Securing Blockchain Transactions A Beginners Guide BCT SS V
How Hackers Attack Blockchain Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide showcases how hackers attacks blockchain technology to protect key information and mange threats. It includes elements such as false transactions, private keys, hampering network nodes, fake cryptocurrencies, personal information, etc. Introducing How Hackers Attack Blockchain Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Develops False, Swindles Private, Hampers Network Nodes, using this template. Grab it now to reap its full benefits.
-
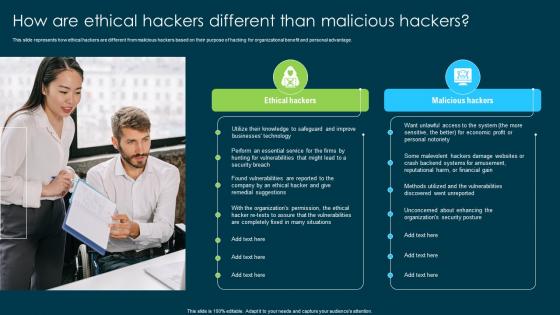 Ethical Hacking And Network Security How Are Ethical Hackers Different Than Malicious Hackers
Ethical Hacking And Network Security How Are Ethical Hackers Different Than Malicious HackersThis slide represents how ethical hackers are different from malicious hackers based on their purpose of hacking for organizational benefit and personal advantage. Increase audience engagement and knowledge by dispensing information using Ethical Hacking And Network Security How Are Ethical Hackers Different Than Malicious Hackers. This template helps you present information on two stages. You can also present information on Ethical Hackers, Malicious Hackers, Organizational Benefit, Organizations Security Posture using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
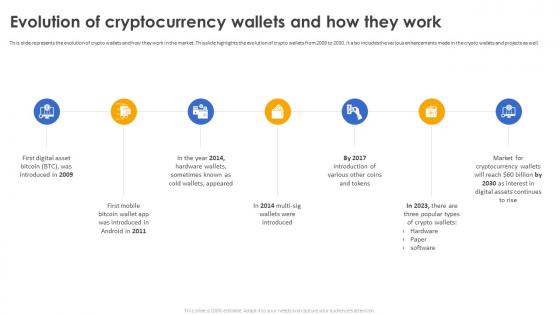 Secure Your Digital Assets Evolution Of Cryptocurrency Wallets And How They Work
Secure Your Digital Assets Evolution Of Cryptocurrency Wallets And How They WorkThis slide represents the evolution of crypto wallets and how they work in the market. This slide highlights the evolution of crypto wallets from 2009 to 2030. It also includes the various enhancements made in the crypto wallets and projects as well. Increase audience engagement and knowledge by dispensing information using Secure Your Digital Assets Evolution Of Cryptocurrency Wallets And How They Work. This template helps you present information on seven stages. You can also present information on Evolution Of Cryptocurrency Wallets, Crypto Wallets, Market For Cryptocurrency Wallets using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
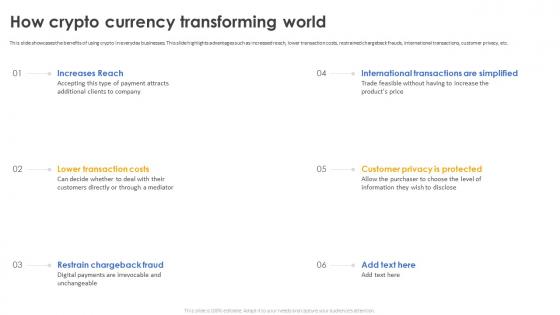 Secure Your Digital Assets How Crypto Currency Transforming World
Secure Your Digital Assets How Crypto Currency Transforming WorldThis slide showcases the benefits of using crypto in everyday businesses. This slide highlights advantages such as increased reach, lower transaction costs, restrained chargeback frauds, international transactions, customer privacy, etc. Increase audience engagement and knowledge by dispensing information using Secure Your Digital Assets How Crypto Currency Transforming World. This template helps you present information on six stages. You can also present information on Restrain Chargeback Fraud, Currency Transforming World, Customer Privacy Is Protected using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
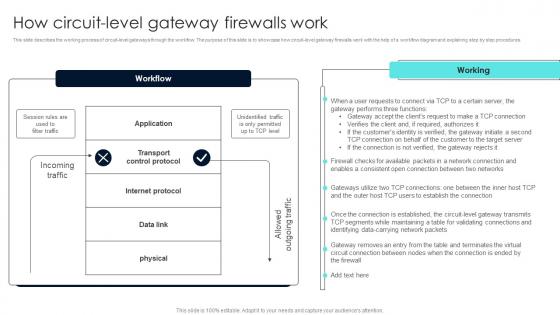 Firewall Network Security How Circuit Level Gateway Firewalls Work
Firewall Network Security How Circuit Level Gateway Firewalls WorkThis slide describes the working process of circuit-level gateways through the workflow. The purpose of this slide is to showcase how circuit-level gateway firewalls work with the help of a workflow diagram and explaining step by step procedures. Present the topic in a bit more detail with this Firewall Network Security How Circuit Level Gateway Firewalls Work Use it as a tool for discussion and navigation on Data Traffic, Web Application, Web Server This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Firewall Network Security How Does A Hardware Firewall Works
Firewall Network Security How Does A Hardware Firewall WorksThis slide provides an overview of the working of hardware firewalls. The purpose of this slide is to showcase the various steps a hardware firewall takes to protect a network and devices from malicious activities. The components of a network containing hardware firewall include LAN, hardware firewall, and internet. Deliver an outstanding presentation on the topic using this Firewall Network Security How Does A Hardware Firewall Works Dispense information and present a thorough explanation of Security From Insider Attacks, Intrusion Detection, Service Exposure And Port Scanning using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
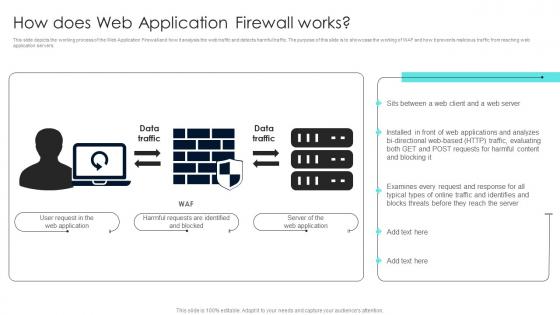 Firewall Network Security How Does Web Application Firewall Works
Firewall Network Security How Does Web Application Firewall WorksThis slide depicts the working process of the Web Application Firewall and how it analysis the web traffic and detects harmful traffic. The purpose of this slide is to showcase the working of WAF and how it prevents malicious traffic from reaching web application servers. Present the topic in a bit more detail with this Firewall Network Security How Does Web Application Firewall Works Use it as a tool for discussion and navigation on Importance, Functions This template is free to edit as deemed fit for your organization. Therefore download it now.
-
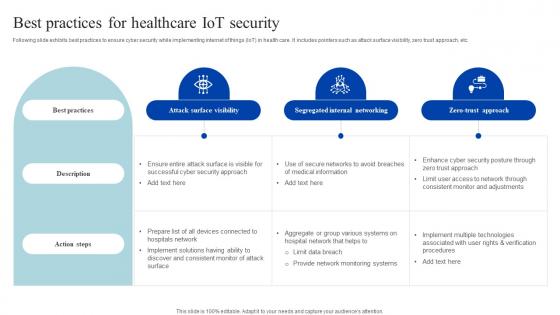 Best Practices For Healthcare Iot Security How Iomt Is Transforming Medical Industry IoT SS V
Best Practices For Healthcare Iot Security How Iomt Is Transforming Medical Industry IoT SS VFollowing slide exhibits best practices to ensure cyber security while implementing internet of things IoT in health care. It includes pointers such as attack surface visibility, zero trust approach, etc. Present the topic in a bit more detail with this Best Practices For Healthcare Iot Security How Iomt Is Transforming Medical Industry IoT SS V. Use it as a tool for discussion and navigation on Attack Surface Visibility, Segregated Internal Networking, Zero Trust Approach. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
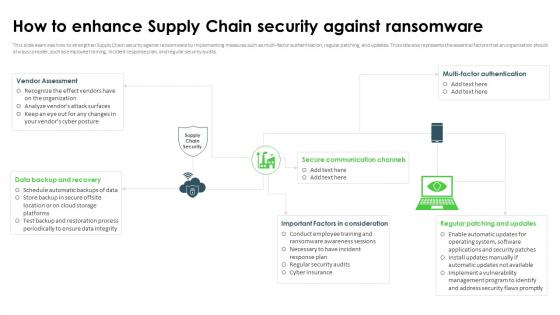 Ransomware In Digital Age How To Enhance Supply Chain Security Against Ransomware
Ransomware In Digital Age How To Enhance Supply Chain Security Against RansomwareThis slide examines how to strengthen Supply Chain security against ransomware by implementing measures such as multi-factor authentication, regular patching, and updates. This slide also represents the essential factors that an organization should always consider, such as employee training, incident response plan, and regular security audits. Deliver an outstanding presentation on the topic using this Ransomware In Digital Age How To Enhance Supply Chain Security Against Ransomware. Dispense information and present a thorough explanation of Secure Communication Channels, Important Factors In Consideration, Regular Patching And Updates, Data Backup And Recovery using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
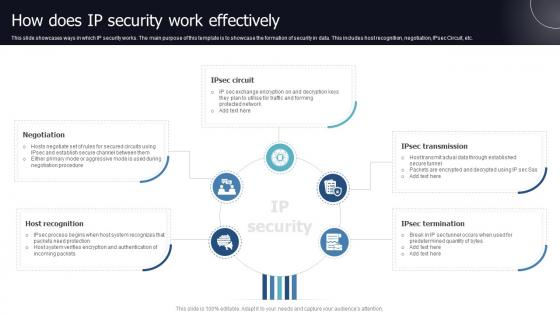 How Does IP Security Work Effectively
How Does IP Security Work EffectivelyThis slide showcases ways in which IP security works. The main purpose of this template is to showcase the formation of security in data. This includes host recognition, negotiation, IPsec Circuit, etc. Introducing our premium set of slides with name How Does IP Security Work Effectively. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Host Recognition, Negotiation, Security Work Effectively. So download instantly and tailor it with your information.
-
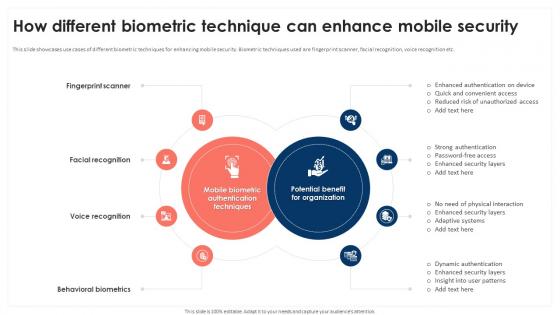 How Different Biometric Technique Can Enhance Mobile Device Security Cybersecurity SS
How Different Biometric Technique Can Enhance Mobile Device Security Cybersecurity SSThis slide showcases use cases of different biometric techniques for enhancing mobile security. Biometric techniques used are fingerprint scanner, facial recognition, voice recognition etc. Introducing How Different Biometric Technique Can Enhance Mobile Device Security Cybersecurity SS to increase your presentation threshold. Encompassed with Two stages, this template is a great option to educate and entice your audience. Dispence information on Company Financial Loss, Operational Disruption using this template. Grab it now to reap its full benefits.
-
 How Mobile Vpn Help In Organization Security Mobile Device Security Cybersecurity SS
How Mobile Vpn Help In Organization Security Mobile Device Security Cybersecurity SSThis slides showcases various use cases of VPN in enhancing mobile security. Its key components are encrypted communication, secure remote access, data privacy etc. Increase audience engagement and knowledge by dispensing information using How Mobile Vpn Help In Organization Security Mobile Device Security Cybersecurity SS This template helps you present information on Three stages. You can also present information on Company Data Loss, Data Breaches, Unauthorized Access using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
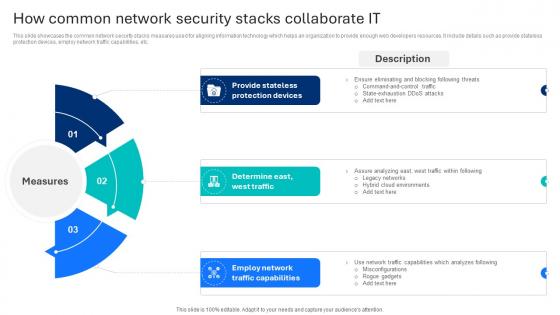 How Common Network Security Stacks Collaborate It
How Common Network Security Stacks Collaborate ItThis slide showcases the common network security stacks measures used for aligning information technology which helps an organization to provide enough web developers resources. It include details such as provide stateless protection devices, employ network traffic capabilities, etc. Introducing our premium set of slides with name How Common Network Security Stacks Collaborate It Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Provide Stateless, Protection Devices, Traffic Capabilities. So download instantly and tailor it with your information.
-
 How Does Secure Blockchain Network Operates Ultimate Handbook For Blockchain BCT SS V
How Does Secure Blockchain Network Operates Ultimate Handbook For Blockchain BCT SS VThis slide covers steps to increase operational security of blockchain networks. It includes steps such as requesting transaction by users, creation of block representing the transaction, broadcasting of blocks to network nodes, etc. Deliver an outstanding presentation on the topic using this How Does Secure Blockchain Network Operates Ultimate Handbook For Blockchain BCT SS V Dispense information and present a thorough explanation of Transaction Requested, Transaction Is Completed, Blockchain using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Computing Security How To Manage Security In Cloud Cont Ppt Professional
Cloud Computing Security How To Manage Security In Cloud Cont Ppt ProfessionalThis slide defines the process of data security management in the cloud system that includes firewalls, access controls, data masking, and data recovery. Increase audience engagement and knowledge by dispensing information using Cloud Computing Security How To Manage Security In Cloud Cont Ppt Professional. This template helps you present information on four stages. You can also present information on Firewalls, Access Controls, Data Masking, Data Recovery using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 How Achieve ISO 27001 Certification Dashboard For Information Security Risk Management
How Achieve ISO 27001 Certification Dashboard For Information Security Risk ManagementThis slide displays dashboard for information security risk management. It includes KPIs such as risk analysis progress, percentage risk, response progress for risks and number of risks encountered. Present the topic in a bit more detail with this How Achieve ISO 27001 Certification Dashboard For Information Security Risk Management. Use it as a tool for discussion and navigation on Dashboard For Information Security Risk Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
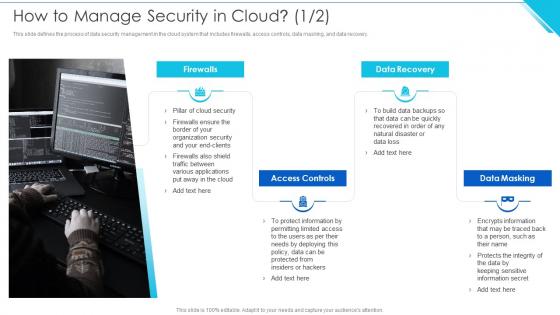 How To Manage Security In Cloud Information Security
How To Manage Security In Cloud Information SecurityThis slide defines the process of data security management in the cloud system that includes firewalls, access controls, data masking, and data recovery.Introducing How To Manage Security In Cloud Information Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Categorization Services, Redundancy, Attacks Or Ransomware using this template. Grab it now to reap its full benefits.
-
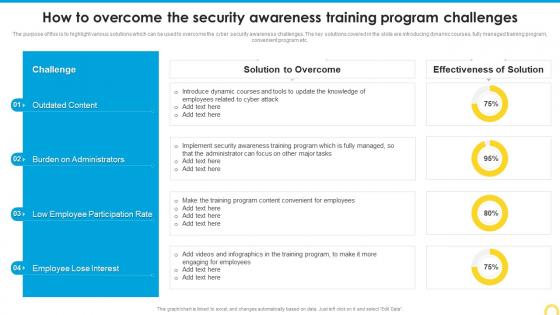 How To Overcome The Security Building A Security Awareness Program
How To Overcome The Security Building A Security Awareness ProgramThe purpose of this is to highlight various solutions which can be used to overcome the cyber security awareness challenges. The key solutions covered in the slide are introducing dynamic courses, fully managed training program, convenient program etc. Deliver an outstanding presentation on the topic using this How To Overcome The Security Building A Security Awareness Program. Dispense information and present a thorough explanation of Outdated Content, Participation Rate, Burden Administrators using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
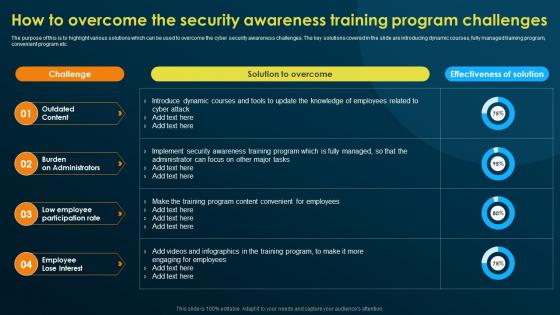 How To Overcome The Security Awareness Training Implementing Security Awareness Training
How To Overcome The Security Awareness Training Implementing Security Awareness TrainingThe purpose of this is to highlight various solutions which can be used to overcome the cyber security awareness challenges. The key solutions covered in the slide are introducing dynamic courses, fully managed training program, convenient program etc. Present the topic in a bit more detail with this How To Overcome The Security Awareness Training Implementing Security Awareness Training. Use it as a tool for discussion and navigation on Outdated Content, Burden On Administrators, Low Employee Participation Rate. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
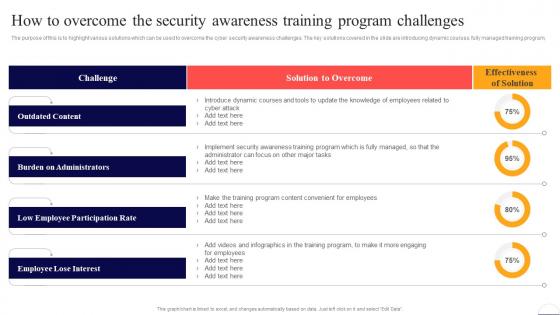 How To Overcome The Security Awareness Training Program Preventing Data Breaches Through Cyber Security
How To Overcome The Security Awareness Training Program Preventing Data Breaches Through Cyber SecurityThe purpose of this is to highlight various solutions which can be used to overcome the cyber security awareness challenges. The key solutions covered in the slide are introducing dynamic courses, fully managed training program. Deliver an outstanding presentation on the topic using this How To Overcome The Security Awareness Training Program Preventing Data Breaches Through Cyber Security. Dispense information and present a thorough explanation of Outdated Content, Burden On Administrators, Low Employee Participation Rate using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
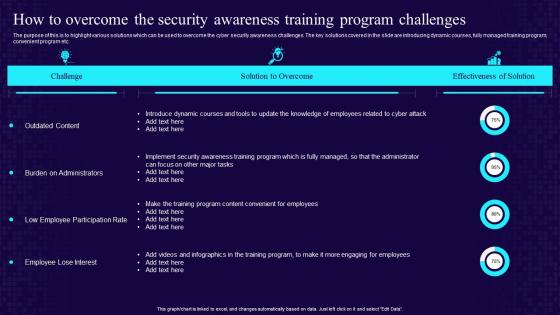 How To Overcome The Security Awareness Training Program Challenges Developing Cyber Security Awareness
How To Overcome The Security Awareness Training Program Challenges Developing Cyber Security AwarenessThe purpose of this is to highlight various solutions which can be used to overcome the cyber security awareness challenges. The key solutions covered in the slide are introducing dynamic courses, fully managed training program, convenient program etc. Deliver an outstanding presentation on the topic using this How To Overcome The Security Awareness Training Program Challenges Developing Cyber Security Awareness. Dispense information and present a thorough explanation of Security Awareness, Training Program, Challenges using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Competitive Analysis Of Major How Amazon Is Securing Competitive Edge Across Globe Strategy SS
Competitive Analysis Of Major How Amazon Is Securing Competitive Edge Across Globe Strategy SSThis slide provides information regarding comparative analysis of potential players existing across marketplace. The points of differentiation include financial parameters, critical success factors such as product variety, customer services, email marketing, etc. Present the topic in a bit more detail with this Competitive Analysis Of Major How Amazon Is Securing Competitive Edge Across Globe Strategy SS. Use it as a tool for discussion and navigation on Ecommerce Market Share, Ecommerce Ecosystem, Dynamics. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
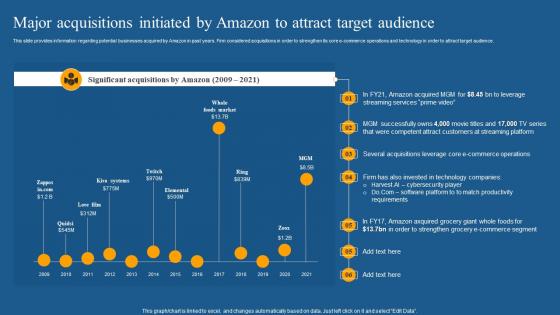 Major Acquisitions Initiated How Amazon Is Securing Competitive Edge Across Globe Strategy SS
Major Acquisitions Initiated How Amazon Is Securing Competitive Edge Across Globe Strategy SSThis slide provides information regarding potential businesses acquired by Amazon in past years. Firm considered acquisitions in order to strengthen its core e commerce operations and technology in order to attract target audience. Present the topic in a bit more detail with this Major Acquisitions Initiated How Amazon Is Securing Competitive Edge Across Globe Strategy SS. Use it as a tool for discussion and navigation on E Commerce Operations, Technology, Cybersecurity Player. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
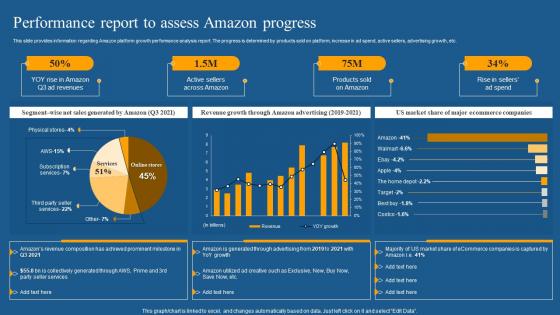 Performance Report To Assess How Amazon Is Securing Competitive Edge Across Globe Strategy SS
Performance Report To Assess How Amazon Is Securing Competitive Edge Across Globe Strategy SSThis slide provides information regarding Amazon platform growth performance analysis report. The progress is determined by products sold on platform, increase in ad spend, active sellers, advertising growth, etc. Deliver an outstanding presentation on the topic using this Performance Report To Assess How Amazon Is Securing Competitive Edge Across Globe Strategy SS. Dispense information and present a thorough explanation of Revenue Growth, Amazon Advertising, Market Share using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Significant Business Research How Amazon Is Securing Competitive Edge Across Globe Strategy SS
Significant Business Research How Amazon Is Securing Competitive Edge Across Globe Strategy SSThis slide provides information regarding potential business and research collaboration initiated by Amazon. The focus of Amazon is to cooperate with credible, knowledgeable, innovative industry partners who share similar vision such as microsoft, ford, etc. Introducing Significant Business Research How Amazon Is Securing Competitive Edge Across Globe Strategy SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Implemented, Security Systems, Capability, using this template. Grab it now to reap its full benefits.
-
 Information Technology Security How Is Automation Used In Information Technology Security
Information Technology Security How Is Automation Used In Information Technology SecurityThis slide depicts the cyber protection of an organization through artificial intelligence and how it can be helpful in threat detection, threat response, and human augmentation. Introducing Information Technology Security How Is Automation Used In Information Technology Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Threat Detection, Threat Response, Human Augmentation, using this template. Grab it now to reap its full benefits.
-
 Information Technology Security What Is Information Technology Security And How Does It Work
Information Technology Security What Is Information Technology Security And How Does It WorkThis slide defines the meaning of cyber security and how it helps to prevent data through different methods and techniques. Introducing Information Technology Security What Is Information Technology Security And How Does It Work to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Information, Technology, Security, using this template. Grab it now to reap its full benefits.


