Powerpoint Templates and Google slides for Implementing Security Awareness
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
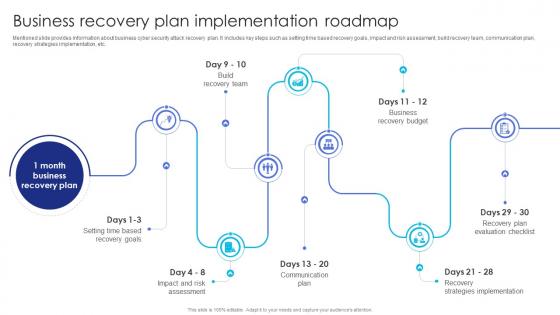 Business Plan Implementation Roadmap Business Recovery Plan To Overcome Cyber Security Threat
Business Plan Implementation Roadmap Business Recovery Plan To Overcome Cyber Security ThreatMentioned slide provides information about business cyber security attack recovery plan. It includes key steps such as setting time based recovery goals, impact and risk assessment, build recovery team, communication plan, recovery strategies implementation, etc. Introducing Business Plan Implementation Roadmap Business Recovery Plan To Overcome Cyber Security Threat to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Assessment, Communication Plan, Recovery Strategies Implementation, using this template. Grab it now to reap its full benefits.
-
 Implementing Smart Security System To Enhance Home Automation
Implementing Smart Security System To Enhance Home AutomationThis slide represents implementation of smart security system that assist people in enhancing their home security and easy assess to home automation system. It includes various features such as access limitation tools, activity detectors, etc. Presenting our set of slides with Implementing Smart Security System To Enhance Home Automation This exhibits information on Six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Access Limitation Tools, Access And Control, Adopt Voice Assistants
-
 Ai Technology Implementation Icon For Robust OT Cyber Security
Ai Technology Implementation Icon For Robust OT Cyber SecurityPresenting our set of slides with Ai Technology Implementation Icon For Robust OT Cyber Security This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on AI Technology Implementation Icon, Robust OT Cyber Security
-
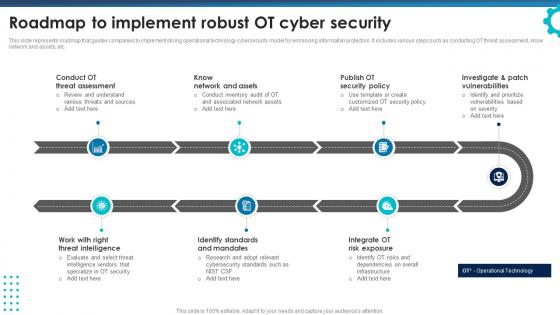 Roadmap To Implement Robust OT Cyber Security
Roadmap To Implement Robust OT Cyber SecurityThis slide represents roadmap that guides companies to implement strong operational technology cybersecurity model for enhancing information protection. It includes various steps such as conducting OT threat assessment, know network and assets, etc. Presenting our set of slides with Roadmap To Implement Robust OT Cyber Security This exhibits information on Seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Conduct OT Threat Assessment, Know Network And Assets, Publish OT Security Policy
-
 Security Considerations Icon For SaaS Implementation
Security Considerations Icon For SaaS ImplementationIntroducing our premium set of slides with Security Considerations Icon For SaaS Implementation Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security Considerations, Saas Implementation So download instantly and tailor it with your information.
-
 Post Implementation Measures To Enhance Ecommerce Security
Post Implementation Measures To Enhance Ecommerce SecurityThis slide shows the three step process of implementing successful ecommerce security to defend against the cyber attacks. The steps are testing, training and continued monitoring Presenting our set of slides with Post Implementation Measures To Enhance Ecommerce Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Implementation, Measures, Continued Monitoring.
-
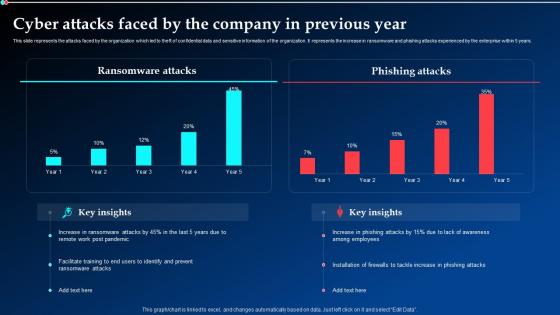 Cyber Attacks Faced By The Company In Previous Year Implementing Cyber Security Ppt Demonstration
Cyber Attacks Faced By The Company In Previous Year Implementing Cyber Security Ppt DemonstrationThis slide represents the attacks faced by the organization which led to theft of confidential data and sensitive information of the organization. It represents the increase in ransomware and phishing attacks experienced by the enterprise within 5 years. Present the topic in a bit more detail with this Cyber Attacks Faced By The Company In Previous Year Implementing Cyber Security Ppt Demonstration. Use it as a tool for discussion and navigation on Ransomware Attacks, Phishing Attacks, Previous Year. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
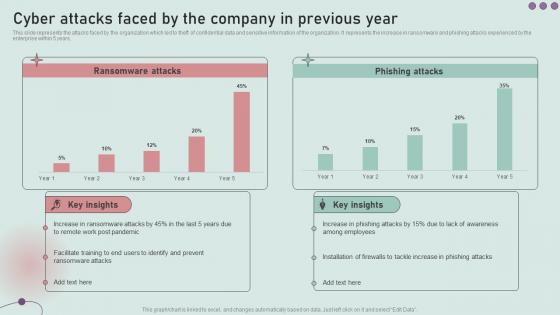 Cyber Attacks Faced By The Company In Previous Year Development And Implementation Of Security
Cyber Attacks Faced By The Company In Previous Year Development And Implementation Of SecurityThis slide represents the attacks faced by the organization which led to theft of confidential data and sensitive information of the organization. It represents the increase in ransomware and phishing attacks experienced by the enterprise within 5 years. Present the topic in a bit more detail with this Cyber Attacks Faced By The Company In Previous Year Development And Implementation Of Security. Use it as a tool for discussion and navigation on Ransomware Attacks, Phishing Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Securing strategy implementation ppt examples slides
Securing strategy implementation ppt examples slidesQuick and simple download without any hassles. Modify text anywhere as per the context. Insert your own company logo, tagline, trademark, brand name etc. Absolutely modifiable PPT infographics- change color and contrast as required. No change in resolution of PPT images after editing. Fully alterable size and orientation of presentation icons.The stages in this process are human resource management, strategy, structure, lateral links, rewards systems.
-
 Securing strategy implementation powerpoint ideas
Securing strategy implementation powerpoint ideasPresenting securing strategy implementation powerpoint ideas. This is a securing strategy implementation powerpoint ideas. This is a five stage process. The stages in this process are strategy, structure, lateral links, reward systems, human resource management.
-
 Security policy and implementation guidance template ppt design
Security policy and implementation guidance template ppt designPresenting security policy and implementation guidance template ppt design. This is a security policy and implementation guidance template ppt design. This is a six stage process. The stages in this process are client and operation structure, training and presentation, information flow, aggregation control, department size vs operation size, access control and network infrastructure.
-
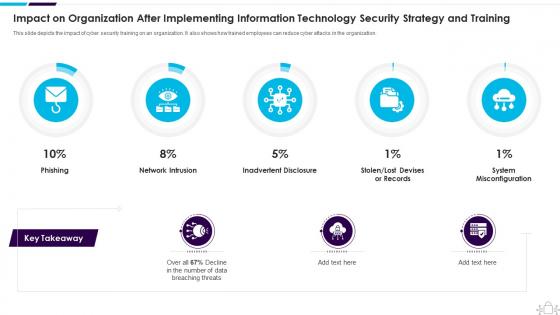 Information Technology Security Impact Organization After Implementing Strategy Training
Information Technology Security Impact Organization After Implementing Strategy TrainingThis slide depicts the impact of cyber security training on an organization. It also shows how trained employees can reduce cyber attacks in the organization. Present the topic in a bit more detail with this Information Technology Security Impact Organization After Implementing Strategy Training. Use it as a tool for discussion and navigation on Organization, Implementing, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
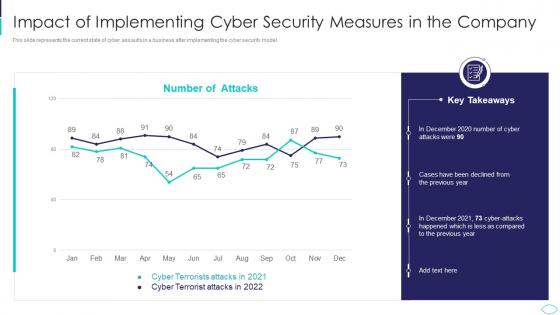 Cyber Terrorism Attacks Impact Of Implementing Cyber Security
Cyber Terrorism Attacks Impact Of Implementing Cyber SecurityThis slide represents the current state of cyber assaults in a business after implementing the cyber security model. Deliver an outstanding presentation on the topic using this Cyber Terrorism Attacks Impact Of Implementing Cyber Security. Dispense information and present a thorough explanation of Impact Of Implementing Cyber Security Measures In The Company using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
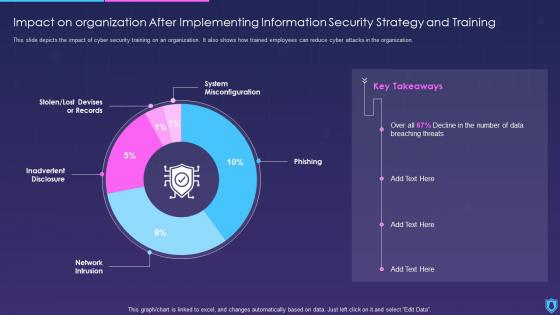 Information Security Impact On Organization After Implementing Information Strategy Training
Information Security Impact On Organization After Implementing Information Strategy TrainingThis slide depicts the impact of cyber security training on an organization. It also shows how trained employees can reduce cyber attacks in the organization. Present the topic in a bit more detail with this Information Security Impact On Organization After Implementing Information Strategy Training. Use it as a tool for discussion and navigation on Implementing, Information, Strategy. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
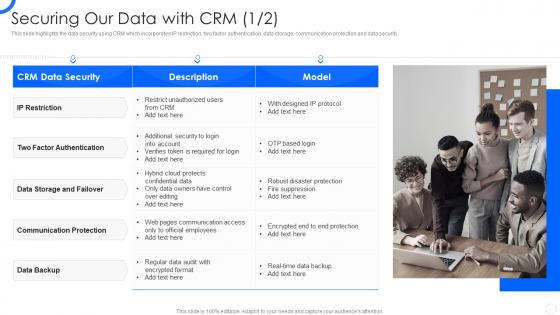
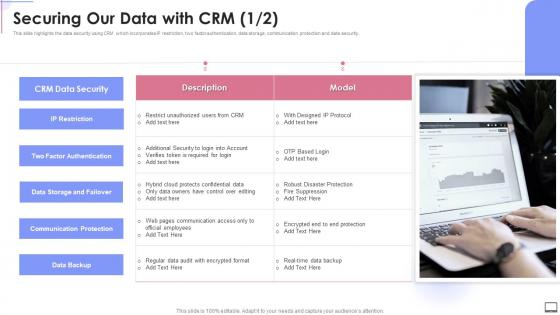 Securing Our Data With Crm Crm Software Implementation Ppt Slides Demonstration
Securing Our Data With Crm Crm Software Implementation Ppt Slides DemonstrationThis slide highlights the data security using CRM which incorporates IP restriction, two factor authentication, data storage, communication protection and data security. Deliver an outstanding presentation on the topic using this Securing Our Data With Crm Crm Software Implementation Ppt Slides Demonstration. Dispense information and present a thorough explanation of Data Storage And Failover, Communication Protection, Data Backup using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Sales CRM Cloud Implementation Securing Our Data With CRM Ppt Slides Image
Sales CRM Cloud Implementation Securing Our Data With CRM Ppt Slides ImageThis slide illustrates the issues that trigger poor relationship with customers which includes no real time support, no innovative product launched, bad after sale service and lack of engagement. Present the topic in a bit more detail with this Sales CRM Cloud Implementation Poor Relationship With Customers Ppt Slides Picture. Use it as a tool for discussion and navigation on Weak Relationship Building, Poor Customer Service, Product Launched. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
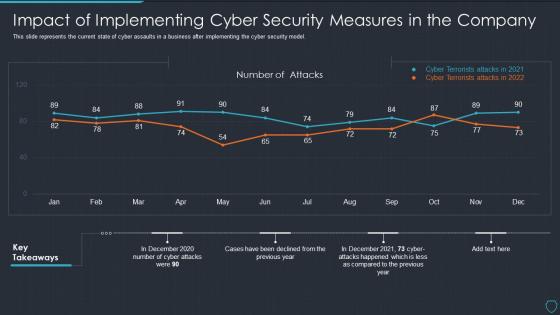 Cyberterrorism it impact of implementing cyber security measures in the company
Cyberterrorism it impact of implementing cyber security measures in the companyThis slide represents the current state of cyber assaults in a business after implementing the cyber security model. Present the topic in a bit more detail with this Cyberterrorism IT Impact Of Implementing Cyber Security Measures In The Company. Use it as a tool for discussion and navigation on Number Attacks, Cyber Terrorists Attacks 2021, Cyber Terrorists Attacks 2022. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
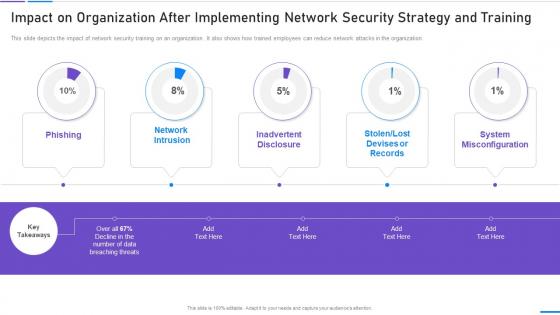 Network Security Impact On Organization After Implementing
Network Security Impact On Organization After ImplementingThis slide depicts the impact of network security training on an organization. It also shows how trained employees can reduce network attacks in the organization. Deliver an outstanding presentation on the topic using this Network Security Impact On Organization After Implementing. Dispense information and present a thorough explanation of Impact On Organization After Implementing Network Security Strategy And Training using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Social Engineering Attack Prevention Techniques Implementing Security Awareness Training
Social Engineering Attack Prevention Techniques Implementing Security Awareness TrainingThe purpose of this slide is to highlight major techniques which can assist the organization in prevention of social engineering attack. It includes techniques such as limit public information, verifying the source and no s haring of password. Present the topic in a bit more detail with this Social Engineering Attack Prevention Techniques Implementing Security Awareness Training. Use it as a tool for discussion and navigation on Limit Public Information, Verify The Source, No Sharing Of Password. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
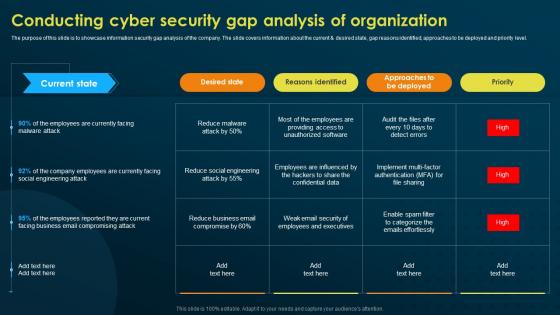 Conducting Cyber Security Gap Analysis Of Organization Implementing Security Awareness Training
Conducting Cyber Security Gap Analysis Of Organization Implementing Security Awareness TrainingThe purpose of this slide is to showcase information security gap analysis of the company. The slide covers information about the current and desired state, gap reasons identified, approaches to be deployed and priority level. Present the topic in a bit more detail with this Conducting Cyber Security Gap Analysis Of Organization Implementing Security Awareness Training. Use it as a tool for discussion and navigation on Desired State, Reasons Identified, Approaches To Be Deployed. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
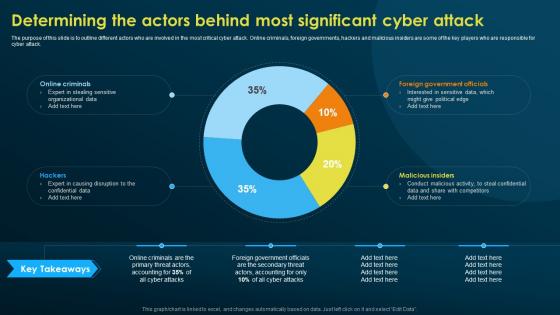 Determining The Actors Behind Most Significant Implementing Security Awareness Training
Determining The Actors Behind Most Significant Implementing Security Awareness TrainingThe purpose of this slide is to outline different actors who are involved in the most critical cyber attack. Online criminals, foreign governments, hackers and malicious insiders are some of the key players who are responsible for cyber attack. Present the topic in a bit more detail with this Determining The Actors Behind Most Significant Implementing Security Awareness Training. Use it as a tool for discussion and navigation on Online Criminals, Foreign Government Officials, Malicious Insiders. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
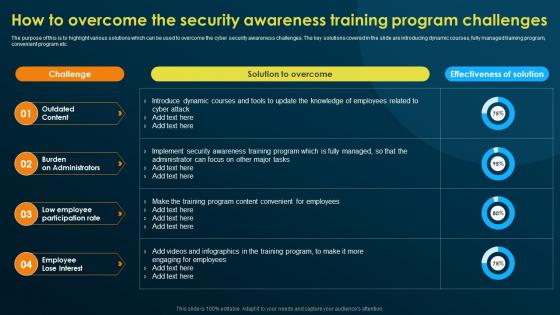 How To Overcome The Security Awareness Training Implementing Security Awareness Training
How To Overcome The Security Awareness Training Implementing Security Awareness TrainingThe purpose of this is to highlight various solutions which can be used to overcome the cyber security awareness challenges. The key solutions covered in the slide are introducing dynamic courses, fully managed training program, convenient program etc. Present the topic in a bit more detail with this How To Overcome The Security Awareness Training Implementing Security Awareness Training. Use it as a tool for discussion and navigation on Outdated Content, Burden On Administrators, Low Employee Participation Rate. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
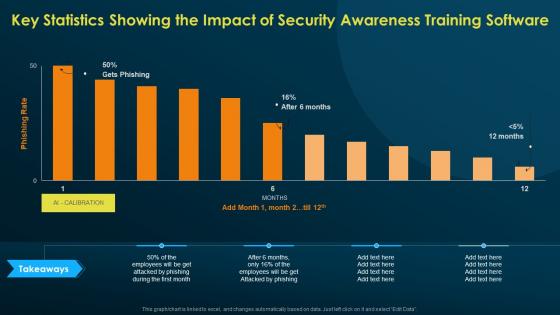 Key Statistics Showing The Impact Of Security Awareness Implementing Security Awareness Training
Key Statistics Showing The Impact Of Security Awareness Implementing Security Awareness TrainingPresent the topic in a bit more detail with this Key Statistics Showing The Impact Of Security Awareness Implementing Security Awareness Training. Use it as a tool for discussion and navigation on Key Statistics, Security Awareness, Training Software. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
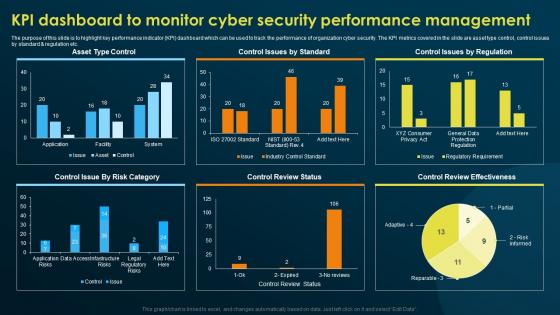 KPI Dashboard To Monitor Cyber Security Performance Implementing Security Awareness Training
KPI Dashboard To Monitor Cyber Security Performance Implementing Security Awareness TrainingThe purpose of this slide is to highlight key performance indicator KPI dashboard which can be used to track the performance of organization cyber security. The KPI metrics covered in the slide are asset type control, control issues by standard and regulation etc. Deliver an outstanding presentation on the topic using this KPI Dashboard To Monitor Cyber Security Performance Implementing Security Awareness Training. Dispense information and present a thorough explanation of Asset Type Control, Control Issues By Standard, Review Effectiveness using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
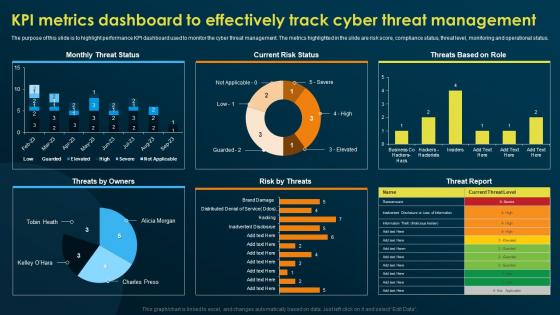 KPI Metrics Dashboard To Effectively Track Cyber Threat Implementing Security Awareness Training
KPI Metrics Dashboard To Effectively Track Cyber Threat Implementing Security Awareness TrainingThe purpose of this slide is to highlight performance KPI dashboard used to monitor the cyber threat management. The metrics highlighted in the slide are risk score, compliance status, threat level, monitoring and operational status. Present the topic in a bit more detail with this KPI Metrics Dashboard To Effectively Track Cyber Threat Implementing Security Awareness Training. Use it as a tool for discussion and navigation on Current Risk Status, Threats By Owners, Risk By Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Measuring The Impact Of Security Awareness Training Implementing Security Awareness Training
Measuring The Impact Of Security Awareness Training Implementing Security Awareness TrainingThe purpose of this slide is to highlight the positive impact of security awareness training. Information covered in this slide is related to malware attack, social engineering attack and business email compromise. Deliver an outstanding presentation on the topic using this Measuring The Impact Of Security Awareness Training Implementing Security Awareness Training. Dispense information and present a thorough explanation of Measuring, Impact Of Security, Awareness Training using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
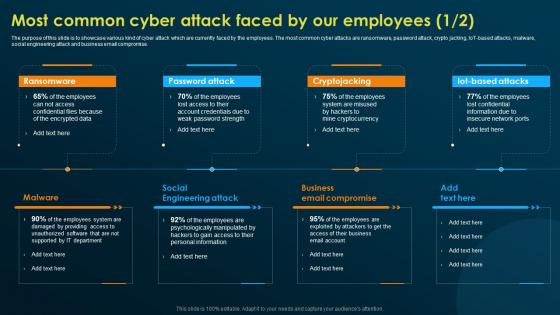 Most Common Cyber Attack Faced By Our Employees Implementing Security Awareness Training
Most Common Cyber Attack Faced By Our Employees Implementing Security Awareness TrainingThe purpose of this slide is to showcase various kind of cyber attack which are currently faced by the employees. The most common cyber attacks are ransomware, password attack, crypto jacking, IoT based attacks, malware, social engineering attack and business email compromise. Introducing Most Common Cyber Attack Faced By Our Employees Implementing Security Awareness Training to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Ransomware, Password Attack, Cryptojacking, Malware, using this template. Grab it now to reap its full benefits.
-
 Operational Outlook Of Security Awareness Training Implementing Security Awareness Training
Operational Outlook Of Security Awareness Training Implementing Security Awareness TrainingThe purpose of this slide is to showcase the general outlook of cyber security awareness training software. The slide covers information about opened simulations, links clicked, reported, attachments opened, data entered etc. Present the topic in a bit more detail with this Operational Outlook Of Security Awareness Training Implementing Security Awareness Training. Use it as a tool for discussion and navigation on Operational Outlook, Security Awareness, Training Software. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Practices To Improve Security Awareness Level Amongst Implementing Security Awareness Training
Practices To Improve Security Awareness Level Amongst Implementing Security Awareness TrainingThe purpose of this slide is to outline different approaches used to enhance the cyber security awareness level. Creating security awareness program, conducting quarterly training session and implementing cyber security drills are some of the major approaches which are highlighted in the slide. Deliver an outstanding presentation on the topic using this Practices To Improve Security Awareness Level Amongst Implementing Security Awareness Training. Dispense information and present a thorough explanation of Create Security, Awareness Program, Cyber Security Training using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security Awareness Training Program Challenges Implementing Security Awareness Training
Security Awareness Training Program Challenges Implementing Security Awareness TrainingThe purpose of this slide is to exhibit biggest cyber security awareness challenges which is faced by the organization. Outdated content, burden on administrators, low employee participation rate and employees losing interest are some of the key challenges which are highlighted in the slide. Introducing Security Awareness Training Program Challenges Implementing Security Awareness Training to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Outdated Content, Burden On Administrators, Employees Lose Interest, using this template. Grab it now to reap its full benefits.
-
 Table Of Contents Implementing Security Awareness Training To Prevent Cyber Attacks
Table Of Contents Implementing Security Awareness Training To Prevent Cyber AttacksPresent the topic in a bit more detail with this Table Of Contents Implementing Security Awareness Training To Prevent Cyber Attacks. Use it as a tool for discussion and navigation on Security Awareness, Current Assessment, Organization. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
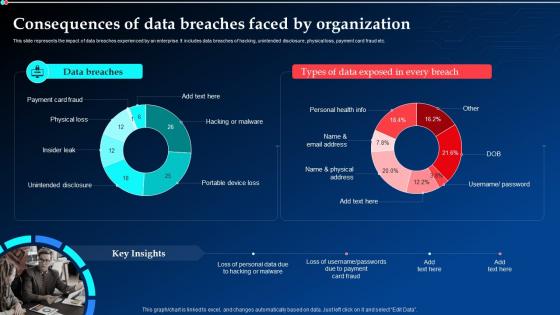 Consequences Of Data Breaches Faced By Organization Implementing Cyber Security Ppt Diagrams
Consequences Of Data Breaches Faced By Organization Implementing Cyber Security Ppt DiagramsThis slide represents the impact of data breaches experienced by an enterprise. It includes data breaches of hacking, unintended disclosure, physical loss, payment card fraud etc. Deliver an outstanding presentation on the topic using this Consequences Of Data Breaches Faced By Organization Implementing Cyber Security Ppt Diagrams. Dispense information and present a thorough explanation of Data Breaches, Consequences, Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Enterprise Cyber Risk Management Dashboard Implementing Cyber Security Ppt Demonstration
Enterprise Cyber Risk Management Dashboard Implementing Cyber Security Ppt DemonstrationThis slide represents the key metrics dashboard representing details related to management of cyber security incidents by an enterprise. It includes key performance indicators such as risk analysis progress, risk rating breakdown etc. Deliver an outstanding presentation on the topic using this Enterprise Cyber Risk Management Dashboard Implementing Cyber Security Ppt Demonstration. Dispense information and present a thorough explanation of Enterprise Cyber, Risk Management, Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Financial Implementing Cyber Security Incident Management Ppt Topics
Financial Implementing Cyber Security Incident Management Ppt TopicsPresent the topic in a bit more detail with this Financial Implementing Cyber Security Incident Management Ppt Topics. Use it as a tool for discussion and navigation on Minimum, Medium, Maximum. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 SecOps Effective Implementation Impact On Security Breaches Ppt Elements
SecOps Effective Implementation Impact On Security Breaches Ppt ElementsThis slide outlines the successful implementation impact of SecOps on organizational security breaches. The purpose of this slide is to highlight the number of reduced security breaches inside a company after implementing SecOps. Security breaches include phishing, network intrusion, and so on. Present the topic in a bit more detail with this SecOps Effective Implementation Impact On Security Breaches Ppt Elements. Use it as a tool for discussion and navigation on Security Breaches, Implementing Secops System. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
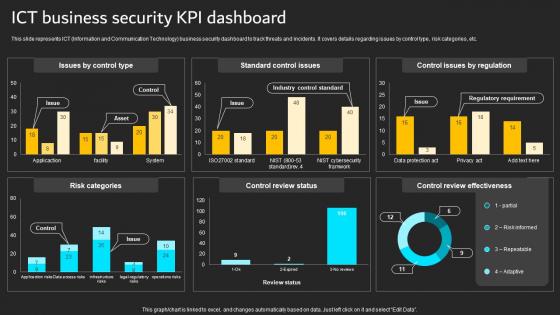 ICT Business Security KPI Dashboard Implementation Of ICT Strategic Plan Strategy SS
ICT Business Security KPI Dashboard Implementation Of ICT Strategic Plan Strategy SSThis slide represents ICT Information and Communication Technology business security dashboard to track threats and incidents. It covers details regarding issues by control type, risk categories, etc.Present the topic in a bit more detail with this ICT Business Security KPI Dashboard Implementation Of ICT Strategic Plan Strategy SS. Use it as a tool for discussion and navigation on Risk Categories, Control Review, Control Review Effectiveness. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
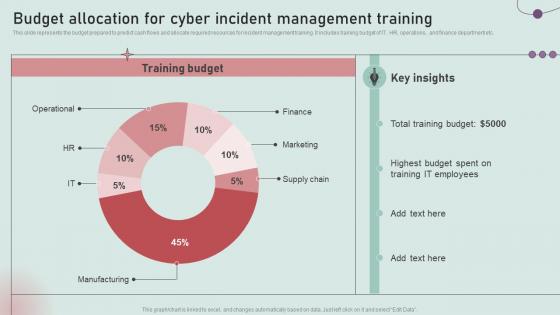 Budget Allocation For Cyber Incident Management Training Development And Implementation Of Security
Budget Allocation For Cyber Incident Management Training Development And Implementation Of SecurityThis slide represents the budget prepared to predict cash flows and allocate required resources for incident management training. It includes training budget of IT, HR, operations, and finance department etc. Deliver an outstanding presentation on the topic using this Budget Allocation For Cyber Incident Management Training Development And Implementation Of Security. Dispense information and present a thorough explanation of Total Training Budget, It Employees, Highest Budget using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
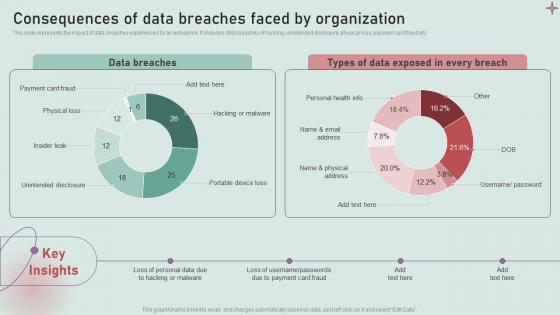 Consequences Of Data Breaches Faced By Organization Development And Implementation Of Security
Consequences Of Data Breaches Faced By Organization Development And Implementation Of SecurityThis slide represents the impact of data breaches experienced by an enterprise. It includes data breaches of hacking, unintended disclosure, physical loss, payment card fraud etc. Deliver an outstanding presentation on the topic using this Consequences Of Data Breaches Faced By Organization Development And Implementation Of Security. Dispense information and present a thorough explanation of Payment Card Fraud, Physical Loss, Insider Leak using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
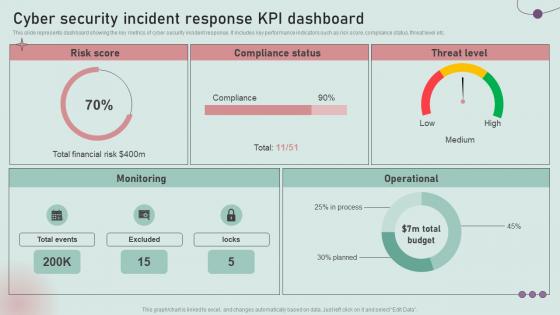 Cyber Security Incident Response KPI Dashboard Development And Implementation Of Security Incident
Cyber Security Incident Response KPI Dashboard Development And Implementation Of Security IncidentThis slide represents dashboard showing the key metrics of cyber security incident response. It includes key performance indicators such as risk score, compliance status, threat level etc. Deliver an outstanding presentation on the topic using this Cyber Security Incident Response KPI Dashboard Development And Implementation Of Security Incident. Dispense information and present a thorough explanation of Total Financial Risk, Compliance, Monitoring using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
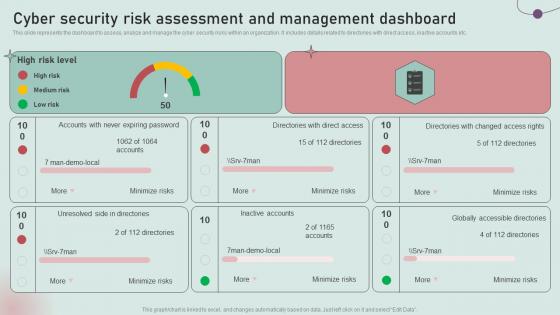 Cyber Security Risk Assessment And Management Dashboard Development And Implementation Of Security
Cyber Security Risk Assessment And Management Dashboard Development And Implementation Of SecurityThis slide represents the dashboard to assess, analyze and manage the cyber security risks within an organization. It includes details related to directories with direct access, inactive accounts etc. Deliver an outstanding presentation on the topic using this Cyber Security Risk Assessment And Management Dashboard Development And Implementation Of Security. Dispense information and present a thorough explanation of Medium Risk, Unresolved Side, Inactive Accounts using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
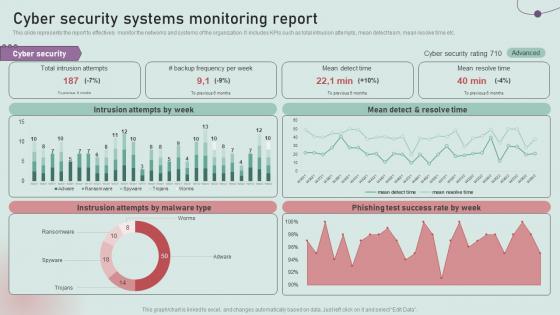 Cyber Security Systems Monitoring Report Development And Implementation Of Security Incident Management
Cyber Security Systems Monitoring Report Development And Implementation Of Security Incident ManagementThis slide represents the report to effectively monitor the networks and systems of the organization. It includes KPIs such as total intrusion attempts, mean detect team, mean resolve time etc. Deliver an outstanding presentation on the topic using this Cyber Security Systems Monitoring Report Development And Implementation Of Security Incident Management. Dispense information and present a thorough explanation of Intrusion Attempts, Mean Detect, Resolve Time using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Supply Chain Risk Management Dashboard Development And Implementation Of Security Incident
Cyber Supply Chain Risk Management Dashboard Development And Implementation Of Security IncidentThis slide shows the dashboard representing details related to management of supply chain risks by the incident management team. It includes details related to KPIs such as policy and compliance, resource security hygiene etc. Deliver an outstanding presentation on the topic using this Cyber Supply Chain Risk Management Dashboard Development And Implementation Of Security Incident. Dispense information and present a thorough explanation of Regulatory Compliance, Subscription Coverage, Resource Health using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
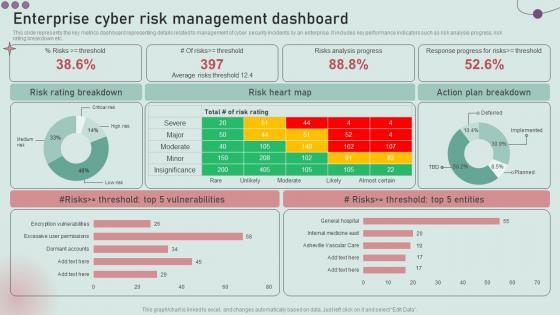 Enterprise Cyber Risk Management Dashboard Development And Implementation Of Security Incident
Enterprise Cyber Risk Management Dashboard Development And Implementation Of Security IncidentThis slide represents the key metrics dashboard representing details related to management of cyber security incidents by an enterprise. It includes key performance indicators such as risk analysis progress, risk rating breakdown etc. Present the topic in a bit more detail with this Enterprise Cyber Risk Management Dashboard Development And Implementation Of Security Incident. Use it as a tool for discussion and navigation on Risk Rating Breakdown, Risk Heart Map, Action Plan Breakdown. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Facilities Offered By Implementation Of Security Centre Building Business Analytics Architecture
Facilities Offered By Implementation Of Security Centre Building Business Analytics ArchitectureThis slide portrays information regarding the various facilities that are offered by successful implementation of security center in the organization in terms if malware detection, phishing detection, investigations by HR, risk mitigation, etc. Introducing Facilities Offered By Implementation Of Security Centre Building Business Analytics Architecture to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Malware Detection And Investigation, Phishing Detection And Prevention, Investigations By HR, Risk Mitigation Of Left Employees, using this template. Grab it now to reap its full benefits.
-
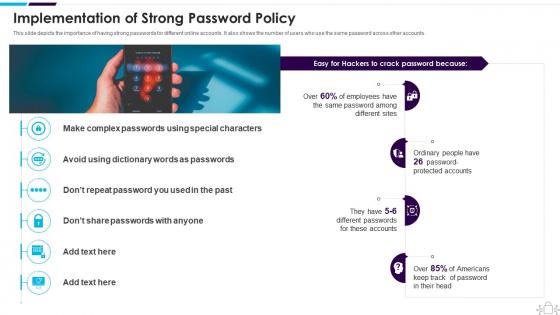 Implementation Of Strong Password Policy Information Technology Security
Implementation Of Strong Password Policy Information Technology SecurityThis slide depicts the importance of having strong passwords for different online accounts. It also shows the number of users who use the same password across other accounts. Introducing Implementation Of Strong Password Policy Information Technology Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Americans, Implementation, Passwords, using this template. Grab it now to reap its full benefits.
-
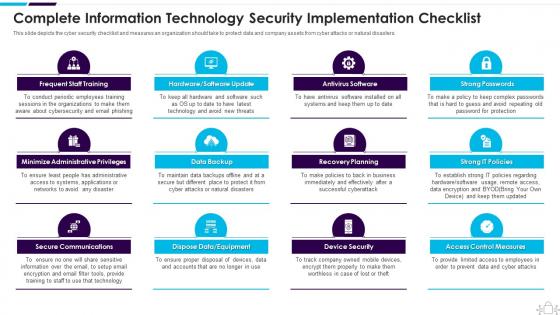 Information Technology Security Complete Information Security Implementation Checklist
Information Technology Security Complete Information Security Implementation ChecklistThis slide depicts the cyber security checklist and measures an organization should take to protect data and company assets from cyber attacks or natural disasters. Introducing Information Technology Security Complete Information Security Implementation Checklist to increase your presentation threshold. Encompassed with twelve stages, this template is a great option to educate and entice your audience. Dispence information on Frequent Staff Training, Administrative Privileges, Data Backup, using this template. Grab it now to reap its full benefits.
-
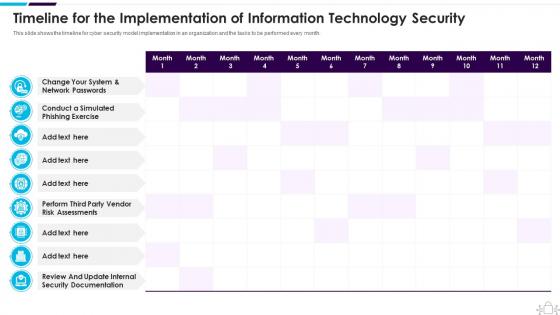 Timeline For The Implementation Of Information Technology Security
Timeline For The Implementation Of Information Technology SecurityThis slide shows the timeline for cyber security model implementation in an organization and the tasks to be performed every month. Deliver an outstanding presentation on the topic using this Timeline For The Implementation Of Information Technology Security. Dispense information and present a thorough explanation of Implementation, Information, Technology using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
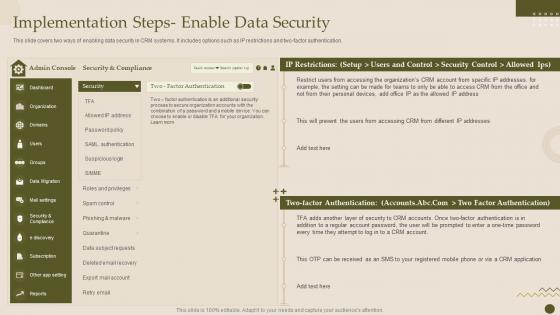 Implementation Steps Enable Data Security Crm Software Deployment Guide
Implementation Steps Enable Data Security Crm Software Deployment GuideThis slide covers two ways of enabling data security in CRM systems. It includes options such as IP restrictions and two-factor authentication. Present the topic in a bit more detail with this Implementation Steps Enable Data Security Crm Software Deployment Guide. Use it as a tool for discussion and navigation on Implementation, Authentication, Restrictions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Implementation Steps Enable Data Security Crm Platform Implementation Plan
Implementation Steps Enable Data Security Crm Platform Implementation PlanThis slide covers two ways of enabling data security in CRM systems. It includes options such as IP restrictions and two-factor authentication. Deliver an outstanding presentation on the topic using this Implementation Steps Enable Data Security Crm Platform Implementation Plan. Dispense information and present a thorough explanation of Authentication, Implementation, Security Control using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Customer Relationship Management System Implementation Steps Enable Data Security
Customer Relationship Management System Implementation Steps Enable Data SecurityThis slide covers two ways of enabling data security in CRM systems. It includes options such as IP restrictions and two-factor authentication. Deliver an outstanding presentation on the topic using this Customer Relationship Management System Implementation Steps Enable Data Security. Dispense information and present a thorough explanation of Implementation, Authentication, Restrictions using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
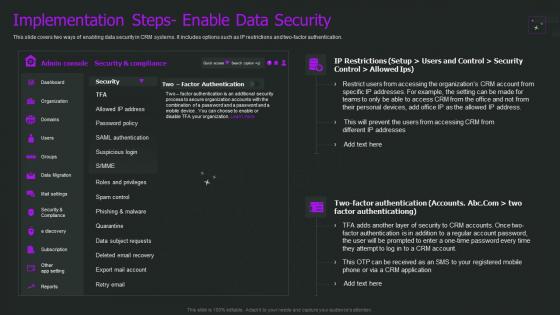 Crm Implementation Process Implementation Steps Enable Data Security
Crm Implementation Process Implementation Steps Enable Data SecurityThis slide covers two ways of enabling data security in CRM systems. It includes options such as IP restrictions and two-factor authentication. Present the topic in a bit more detail with this Crm Implementation Process Implementation Steps Enable Data Security. Use it as a tool for discussion and navigation on Implementation, Authentication, Restrictions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Roadmap To Implement Cyber Security Cyber Terrorism Attacks
Roadmap To Implement Cyber Security Cyber Terrorism AttacksThis slide depicts the roadmap to implement strategies to mitigate cyber terrorism such as training employees about cyber terrorism, creating personal accounts. Introducing Roadmap To Implement Cyber Security Cyber Terrorism Attacks to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Personal Accounts, Awareness Training, Software Updated, using this template. Grab it now to reap its full benefits.
-
 30 60 90 Days Plan To Implement Cloud Security In Business
30 60 90 Days Plan To Implement Cloud Security In BusinessThis slide defines the 30,60 and 90-days plan to implement cloud security in the organization and what tasks would be performed on each 30 days interval. Introducing 30 60 90 Days Plan To Implement Cloud Security In Business to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispense information on Data Access, Operations Performed, Cloud Services, using this template. Grab it now to reap its full benefits.
-
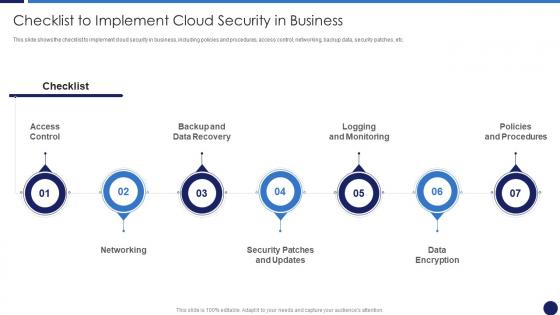 Checklist To Implement Cloud Security In Business Cloud Data Protection
Checklist To Implement Cloud Security In Business Cloud Data ProtectionThis slide shows the checklist to implement cloud security in business, including policies and procedures, access control, networking, backup data, security patches, etc. Introducing Checklist To Implement Cloud Security In Business Cloud Data Protection to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispense information on Logging And Monitoring, Networking, Data Encryption, using this template. Grab it now to reap its full benefits.
-
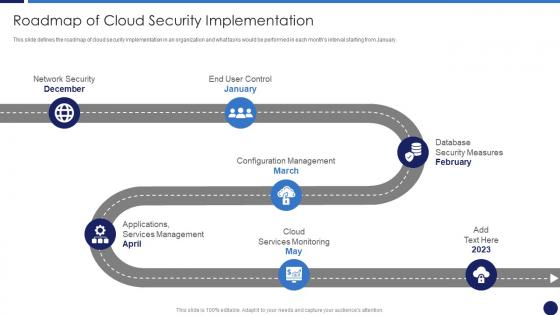 Roadmap Of Cloud Security Implementation Cloud Data Protection
Roadmap Of Cloud Security Implementation Cloud Data ProtectionThis slide defines the roadmap of cloud security implementation in an organization and what tasks would be performed in each months interval starting from January. Introducing Roadmap Of Cloud Security Implementation Cloud Data Protection to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispense information on Cloud Services Monitoring, Services Management, Database Security Measures, Network Security, using this template. Grab it now to reap its full benefits.
-
 Implementing Mobile Device Security Effective Mobile Device Management Ppt Formats
Implementing Mobile Device Security Effective Mobile Device Management Ppt FormatsThis slide portrays information regarding optimization of current mobile device security framework. The IT department will require to fulfill crucial activities in specific timeframe. Present the topic in a bit more detail with this Implementing Mobile Device Security Effective Mobile Device Management Ppt Formats. Use it as a tool for discussion and navigation on Implement Enterprise Security Program, Implement Control Environment, Implement Security Processes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
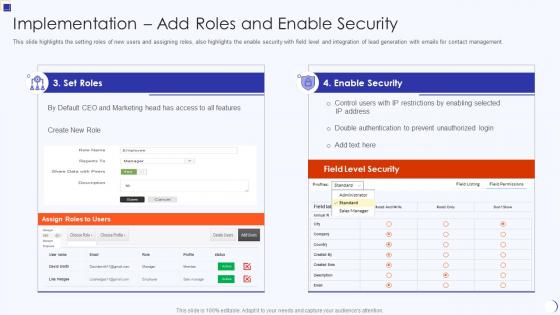 Implementation Add Roles And Enable Security Planning And Implementation Crm Software
Implementation Add Roles And Enable Security Planning And Implementation Crm SoftwareThis slide highlights the setting roles of new users and assigning roles, also highlights the enable security with field level and integration of lead generation with emails for contact management. Present the topic in a bit more detail with this Implementation Add Roles And Enable Security Planning And Implementation Crm Software. Use it as a tool for discussion and navigation on Implementation Add Roles And Enable Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Planning And Implementation Of Crm Software Securing Our Data With Crm
Planning And Implementation Of Crm Software Securing Our Data With CrmThis slide highlights the CRM data security model which includes the user based, profile based, group based, record sharing and login based security. Deliver an outstanding presentation on the topic using this Planning And Implementation Of Crm Software Securing Our Data With Crm. Dispense information and present a thorough explanation of User Role Based Security, Profile Based Security, Record Sharing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
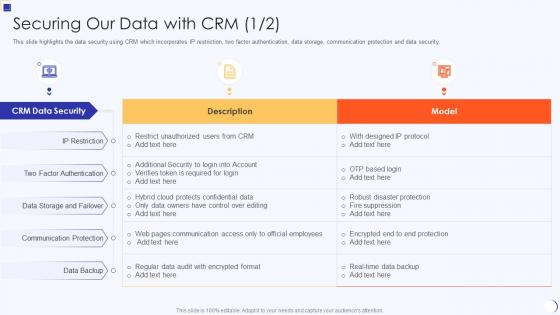 Securing Our Data With Crm Planning And Implementation Of Crm Software
Securing Our Data With Crm Planning And Implementation Of Crm SoftwareThis slide highlights the data security using CRM which incorporates IP restriction, two factor authentication, data storage, communication protection and data security. Present the topic in a bit more detail with this Securing Our Data With Crm Planning And Implementation Of Crm Software. Use it as a tool for discussion and navigation on Securing Our Data With CRM. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
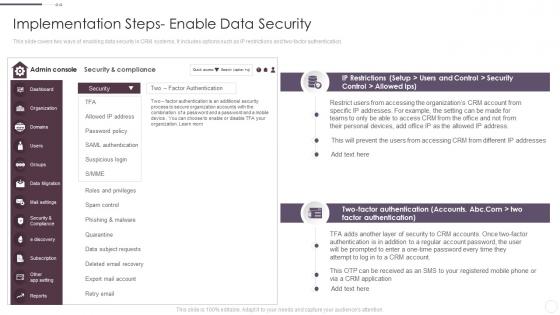 Implementation Steps Enable Data Security Crm System Implementation Guide For Businesses
Implementation Steps Enable Data Security Crm System Implementation Guide For BusinessesThis slide covers two ways of enabling data security in CRM systems. It includes options such as IP restrictions and two-factor authentication. Present the topic in a bit more detail with this Implementation Steps Enable Data Security Crm System Implementation Guide For Businesses. Use it as a tool for discussion and navigation on Implementation, Compliance, Authentication. This template is free to edit as deemed fit for your organization. Therefore download it now.



