Powerpoint Templates and Google slides for Implementing Security In DevOps
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Implementing Cyber Security Incident Management Powerpoint Presentation Slides
Implementing Cyber Security Incident Management Powerpoint Presentation SlidesDeliver an informational PPT on various topics by using this Implementing Cyber Security Incident Management Powerpoint Presentation Slides. This deck focuses and implements best industry practices, thus providing a birds-eye view of the topic. Encompassed with sixty nine slides, designed using high-quality visuals and graphics, this deck is a complete package to use and download. All the slides offered in this deck are subjective to innumerable alterations, thus making you a pro at delivering and educating. You can modify the color of the graphics, background, or anything else as per your needs and requirements. It suits every business vertical because of its adaptable layout.
-
 Blockchain Implementation Challenges In Education Industry Security Concerns Training Ppt
Blockchain Implementation Challenges In Education Industry Security Concerns Training PptPresenting Challenges Faced While Incorporating Blockchain in Education Industry due to Security Concerns. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. All slides are customizable. You can add or delete the content as per your need. Download this professionally designed business presentation, add your content, and present it with confidence.
-
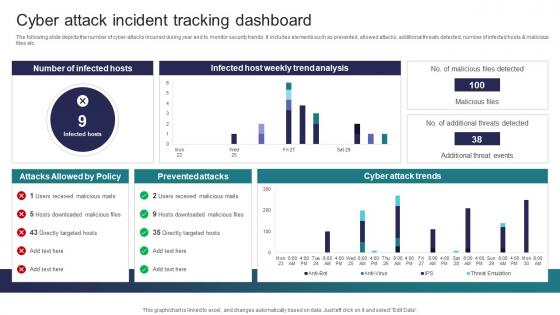 Cyber Attack Incident Tracking Dashboard Implementing Strategies To Mitigate Cyber Security Threats
Cyber Attack Incident Tracking Dashboard Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts the number of cyber attacks incurred during year end to monitor security trends. It includes elements such as prevented, allowed attacks, additional threats detected, number of infected hosts and malicious files etc. Present the topic in a bit more detail with this Cyber Attack Incident Tracking Dashboard Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Prevented Attacks, Cyber Attack Trends This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Strategic Roadmap To Implement DevSecOps Statistics Of Devops Security Risks In Organization
Strategic Roadmap To Implement DevSecOps Statistics Of Devops Security Risks In OrganizationThis slide summarizes DevOps security risks across different organizational departments, such as sales, IT department, finance, marketing, operations, etc. The outlined issues are container security, sever less security issues, cloud deployment risks etc. Deliver an outstanding presentation on the topic using this Strategic Roadmap To Implement DevSecOps Statistics Of Devops Security Risks In Organization. Dispense information and present a thorough explanation of Devops Security Risks Across, Organizational Departments, Finance, Marketing, Operations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
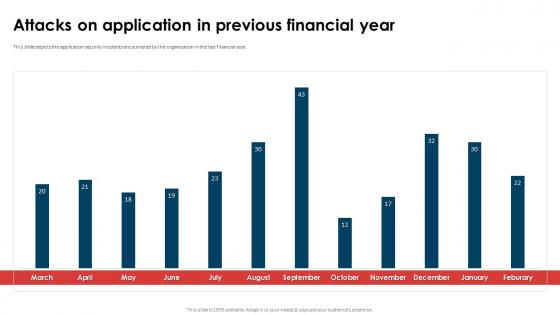 Application Security Implementation Plan Attacks On Application In Previous Financial Year
Application Security Implementation Plan Attacks On Application In Previous Financial YearThis slide depicts the threat scanning dashboard for application security to analyze and monitor vulnerabilities of application. Deliver an outstanding presentation on the topic using this Application Security Implementation Plan Attacks On Application In Previous Financial Year. Dispense information and present a thorough explanation of Attacks On Application, Previous Financial Year, Application Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
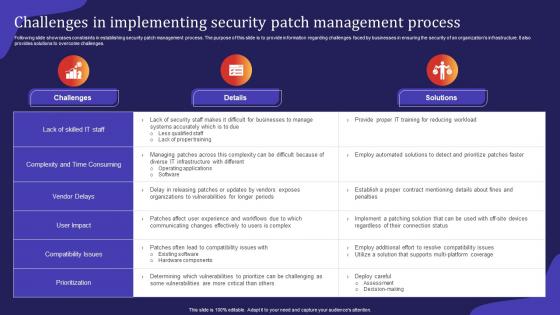 Challenges In Implementing Security Patch Management Process
Challenges In Implementing Security Patch Management ProcessFollowing slide showcases constraints in establishing security patch management process. The purpose of this slide is to provide information regarding challenges faced by businesses in ensuring the security of an organizations infrastructure. It also provides solutions to overcome challenges.Introducing our Challenges In Implementing Security Patch Management Process set of slides. The topics discussed in these slides are Existing Software, Vulnerabilities Prioritize, Compatibility Issues. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
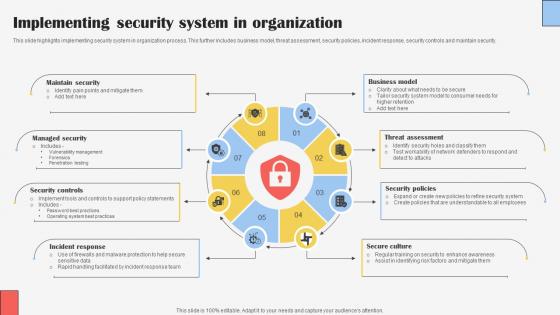 Implementing Security System In Organization
Implementing Security System In OrganizationThis slide highlights implementing security system in organization process. This further includes business model, threat assessment, security policies, incident response, security controls and maintain security. Presenting our set of slides with Implementing Security System In Organization. This exhibits information on eight stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Maintain Security, Managed Security, Security Controls.
-
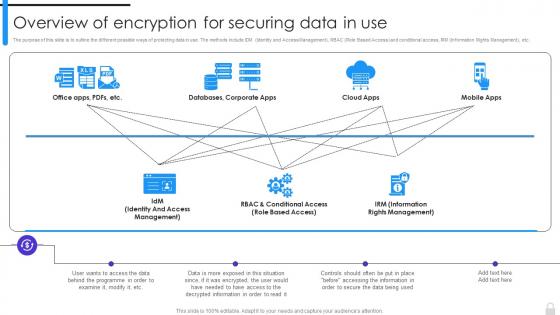 Encryption Implementation Strategies Overview Of Encryption For Securing Data In Use
Encryption Implementation Strategies Overview Of Encryption For Securing Data In UseThe purpose of this slide is to outline the different possible ways of protecting data in use. The methods include IDM Identity and Access Management, RBAC Role Based Access and conditional access, IRM Information Rights Management, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Overview Of Encryption For Securing Data In Use. Dispense information and present a thorough explanation of Information Rights Management, Encryption For Securing Data, Role Based Access using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
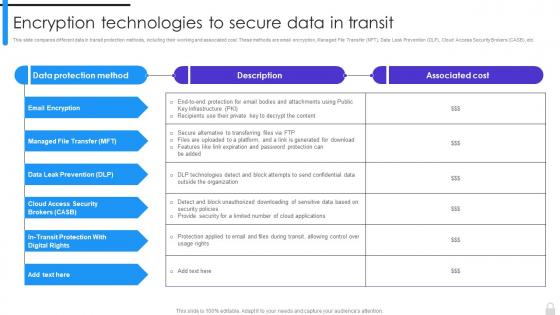 Encryption Technologies To Secure Data In Transit Encryption Implementation Strategies
Encryption Technologies To Secure Data In Transit Encryption Implementation StrategiesThis slide compares different data in transit protection methods, including their working and associated cost. These methods are email encryption, Managed File Transfer MFT, Data Leak Prevention DLP, Cloud Access Security Brokers CASB, etc. Deliver an outstanding presentation on the topic using this Encryption Technologies To Secure Data In Transit Encryption Implementation Strategies. Dispense information and present a thorough explanation of Managed File Transfer, Cloud Access Security Brokers, Email Encryption, Encryption Technologies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
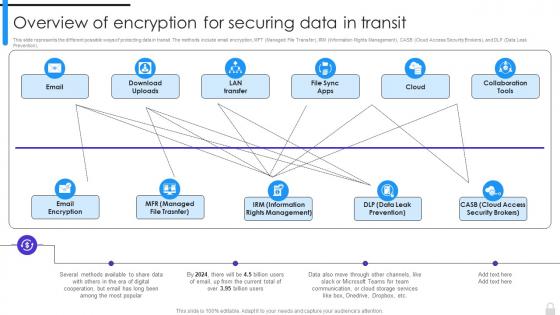 Overview Of Encryption For Securing Data In Transit Encryption Implementation Strategies
Overview Of Encryption For Securing Data In Transit Encryption Implementation StrategiesThis slide represents the different possible ways of protecting data in transit. The methods include email encryption, MFT Managed File Transfer, IRM Information Rights Management, CASB Cloud Access Security Brokers, and DLP Data Leak Prevention. Deliver an outstanding presentation on the topic using this Overview Of Encryption For Securing Data In Transit Encryption Implementation Strategies. Dispense information and present a thorough explanation of Information Rights Management, Data Leak Prevention, Cloud Access Security Brokers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
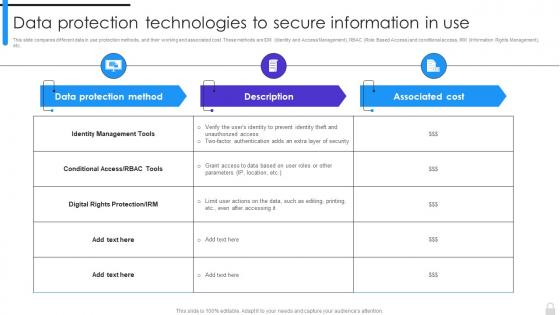 Encryption Implementation Strategies Data Protection Technologies To Secure Information In Use
Encryption Implementation Strategies Data Protection Technologies To Secure Information In UseThis slide compares different data in use protection methods, and their working and associated cost. These methods are IDM Identity and Access Management, RBAC Role Based Access and conditional access, IRM Information Rights Management, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Data Protection Technologies To Secure Information In Use. Use it as a tool for discussion and navigation on Identity Management Tools, Digital Rights Protection, Data Protection Technologies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
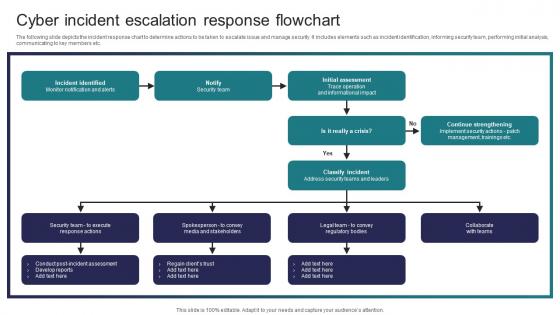 Cyber Incident Escalation Response Flowchart Implementing Strategies To Mitigate Cyber Security Threats
Cyber Incident Escalation Response Flowchart Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts the incident response chart to determine actions to be taken to escalate issue and manage security. It includes elements such as incident identification, informing security team, performing initial analysis, communicating to key members etc. Deliver an outstanding presentation on the topic using this Cyber Incident Escalation Response Flowchart Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Incident Identified, Initial Assessment, Classify Incident using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
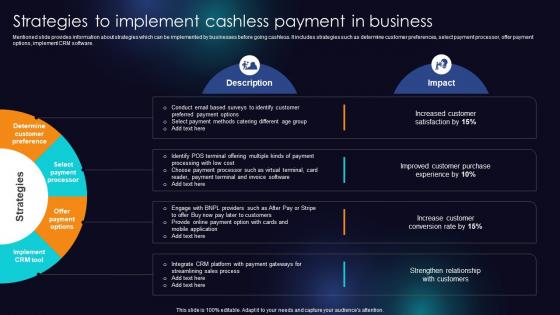 Strategies To Implement Cashless Payment In Business Enhancing Transaction Security With E Payment
Strategies To Implement Cashless Payment In Business Enhancing Transaction Security With E PaymentMentioned slide provides information about strategies which can be implemented by businesses before going cashless. It includes strategies such as determine customer preferences, select payment processor, offer payment options, implement CRM software. Present the topic in a bit more detail with this Strategies To Implement Cashless Payment In Business Enhancing Transaction Security With E Payment Use it as a tool for discussion and navigation on Determine Customer Preference, Select Payment Processor, Implement CRM Tool This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Implement Robust Security Measures Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Implement Robust Security Measures Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured PowerPoint icon features a powerful and secure lock symbol, representing the implementation of robust security measures for big data platforms. It is perfect for presentations and documents related to data security, providing a visual representation of the importance of protecting sensitive information.
-
 Implement Robust Security Measures Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Implement Robust Security Measures Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis monotone PowerPoint icon represents the implementation of robust security measures for big data platforms. It is designed to convey the importance of protecting sensitive data in a professional and efficient manner. With its clean and simple design, it is perfect for use in presentations, reports, and other materials related to big data security.
-
 Budget For Implementing Security Testing In Organization
Budget For Implementing Security Testing In OrganizationThis slide represents the budget for implementing security testing components such as security assessment tools, training and workshops, security testing software, etc. Present the topic in a bit more detail with this Budget For Implementing Security Testing In Organization. Use it as a tool for discussion and navigation on Security Assessment Tools, Training And Workshops, Security Testing Software. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Checklist For Implementing Security Testing In Organization
Checklist For Implementing Security Testing In OrganizationThe purpose of this slide is to highlight the key approaches for implementing security testing such as identifying and prioritizing assets, choosing appropriate testing tools, etc. Present the topic in a bit more detail with this Checklist For Implementing Security Testing In Organization. Use it as a tool for discussion and navigation on Identify And Prioritize Assets, Choose Appropriate Testing Tools, Conduct Threat Modelling. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
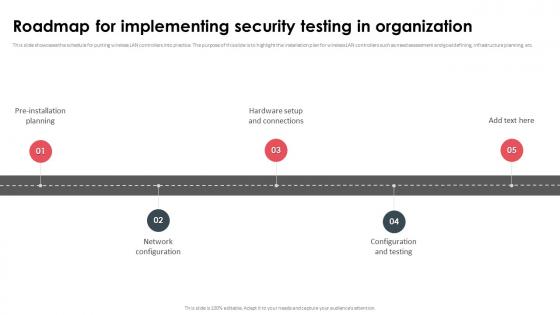 Roadmap For Implementing Security Testing In Organization
Roadmap For Implementing Security Testing In OrganizationThis slide showcases the schedule for putting wireless LAN controllers into practice. The purpose of this slide is to highlight the installation plan for wireless LAN controllers such as need assessment and goal defining, infrastructure planning, etc. Introducing Roadmap For Implementing Security Testing In Organization to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Security Testing, Infrastructure Planning, Installation Plan For Wireless, using this template. Grab it now to reap its full benefits.
-
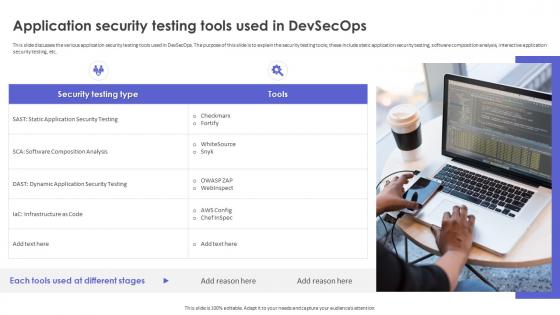 Strategic Roadmap To Implement DevSecOps Application Security Testing Tools Used In DevSecOps
Strategic Roadmap To Implement DevSecOps Application Security Testing Tools Used In DevSecOpsThis slide discusses the various application security testing tools used in DevSecOps. The purpose of this slide is to explain the security testing tools these include static application security testing, software composition analysis, interactive application security testing, etc. Increase audience engagement and knowledge by dispensing information using Strategic Roadmap To Implement DevSecOps Application Security Testing Tools Used In DevSecOps. This template helps you present information on one stages. You can also present information on Application Security Testing, Software Composition Analysis, Interactive Application Security Testing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
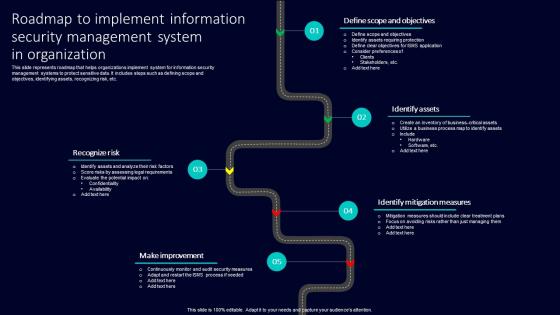 Roadmap To Implement Information Security Management System In Organization
Roadmap To Implement Information Security Management System In OrganizationThis slide represents roadmap that helps organizations implement system for information security management systems to protect sensitive data. It includes steps such as defining scope and objectives, identifying assets, recognizing risk, etc. Introducing our premium set of slides with Roadmap To Implement Information Security Management System In Organization. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Recognize Risk, Make Improvement, Identify Mitigation Measures. So download instantly and tailor it with your information.
-
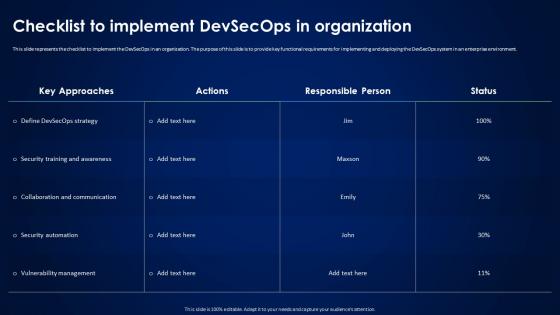 Devsecops Best Practices For Secure Checklist To Implement Devsecops In Organization
Devsecops Best Practices For Secure Checklist To Implement Devsecops In OrganizationThis slide represents the checklist to implement the DevSecOps in an organization. The purpose of this slide is to provide key functional requirements for implementing and deploying the DevSecOps system in an enterprise environment. Present the topic in a bit more detail with this Devsecops Best Practices For Secure Checklist To Implement Devsecops In Organization. Use it as a tool for discussion and navigation on Security Training And Awareness, Collaboration And Communication, Security Automation, Vulnerability Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
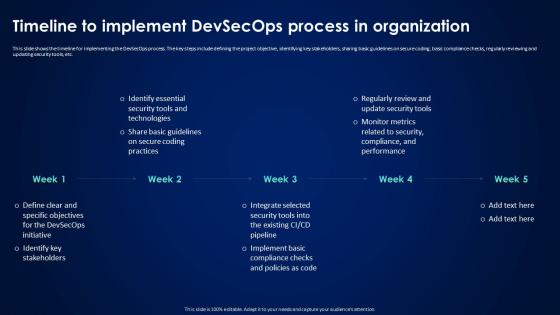 Devsecops Best Practices For Secure Timeline To Implement Devsecops Process In Organization
Devsecops Best Practices For Secure Timeline To Implement Devsecops Process In OrganizationThis slide shows the timeline for implementing the DevSecOps process. The key steps include defining the project objective, identifying key stakeholders, sharing basic guidelines on secure coding, basic compliance checks, regularly reviewing and updating security tools, etc. Increase audience engagement and knowledge by dispensing information using Devsecops Best Practices For Secure Timeline To Implement Devsecops Process In Organization. This template helps you present information on five stages. You can also present information on Timeline To Implement Devsecops, Regularly Reviewing, Updating Security Tools, Sharing Basic Guidelines using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
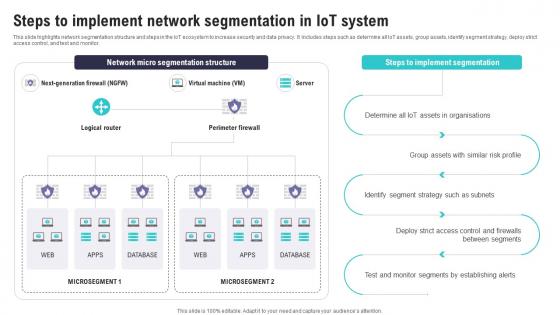 Steps To Implement Network Segmentation In IoT System IoT Security And Privacy Safeguarding IoT SS
Steps To Implement Network Segmentation In IoT System IoT Security And Privacy Safeguarding IoT SSThis slide highlights network segmentation structure and steps in the IoT ecosystem to increase security and data privacy. It includes steps such as determine all IoT assets, group assets, identify segment strategy, deploy strict access control, and test and monitor. Deliver an outstanding presentation on the topic using this Steps To Implement Network Segmentation In IoT System IoT Security And Privacy Safeguarding IoT SS. Dispense information and present a thorough explanation of Assets Organisations, Between Segments, Monitor Segments using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Tokenization For Improved Data Security Before Vs After Implementing Tokenization In Data Security
Tokenization For Improved Data Security Before Vs After Implementing Tokenization In Data SecurityThis slide showcases the comparative analysis of the before versus after tokenization. The purpose of this slide is to showcase the different performance metrics and how tokenization has improved these metrics. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Before Vs After Implementing Tokenization In Data Security. Dispense information and present a thorough explanation of Compliance With Regulations, Reduced Insider Threats, Exposure Of Sensitive Data using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
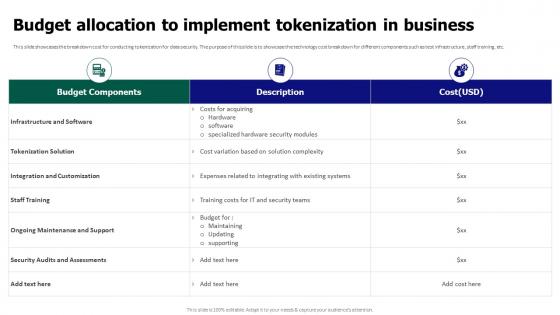 Tokenization For Improved Data Security Budget Allocation To Implement Tokenization In Business
Tokenization For Improved Data Security Budget Allocation To Implement Tokenization In BusinessThis slide showcases the breakdown cost for conducting tokenization for data security. The purpose of this slide is to showcase the technology cost breakdown for different components such as test infrastructure, staff training, etc. Present the topic in a bit more detail with this Tokenization For Improved Data Security Budget Allocation To Implement Tokenization In Business. Use it as a tool for discussion and navigation on Tokenization Solution, Integration And Customization, Infrastructure And Software. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
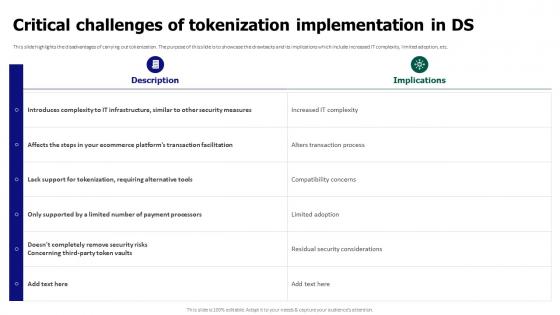 Tokenization For Improved Data Security Critical Challenges Of Tokenization Implementation In Ds
Tokenization For Improved Data Security Critical Challenges Of Tokenization Implementation In DsThis slide highlights the disadvantages of carrying out tokenization. The purpose of this slide is to showcase the drawbacks and its implications which include increased IT complexity, limited adoption, etc. Present the topic in a bit more detail with this Tokenization For Improved Data Security Critical Challenges Of Tokenization Implementation In Ds. Use it as a tool for discussion and navigation on Critical Challenges, Tokenization Implementation, Alters Transaction Process, Compatibility Concerns. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
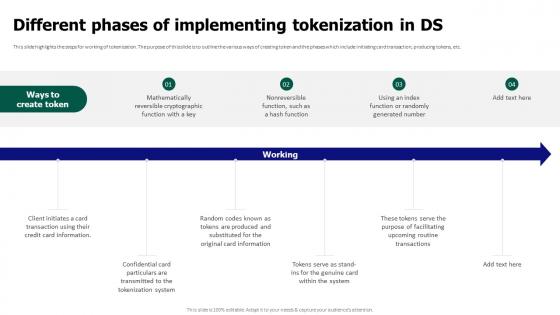 Tokenization For Improved Data Security Different Phases Of Implementing Tokenization In Ds
Tokenization For Improved Data Security Different Phases Of Implementing Tokenization In DsThis slide highlights the steps for working of tokenization. The purpose of this slide is to outline the various ways of creating token and the phases which include initiating card transaction, producing tokens, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Different Phases Of Implementing Tokenization In Ds. This template helps you present information on six stages. You can also present information on Mathematically Reversible, Cryptographic Function, Producing Tokens using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
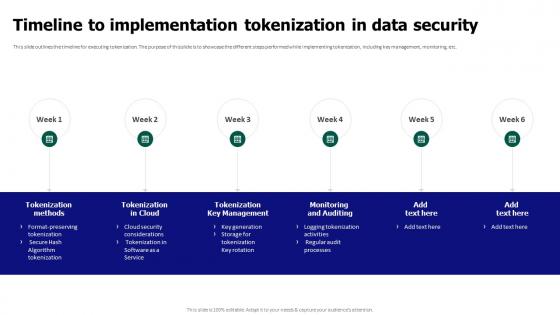 Tokenization For Improved Data Security Timeline To Implementation Tokenization In Data Security
Tokenization For Improved Data Security Timeline To Implementation Tokenization In Data SecurityThis slide outlines the timeline for executing tokenization. The purpose of this slide is to showcase the different steps performed while implementing tokenization, including key management, monitoring, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Timeline To Implementation Tokenization In Data Security. This template helps you present information on six stages. You can also present information on Tokenization Key Management, Monitoring And Auditing, Tokenization Methods, Data Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Application Security Implementation Plan Implementing Effective Security Testing In Organization
Application Security Implementation Plan Implementing Effective Security Testing In OrganizationThis slide showcases the deployment process of security testing parallel to Software Development Testing Lifecycle SDLC stages. Increase audience engagement and knowledge by dispensing information using Application Security Implementation Plan Implementing Effective Security Testing In Organization. This template helps you present information on seven stages. You can also present information on System Testing, Implementation System Testing, Integration Testing, Requirement using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
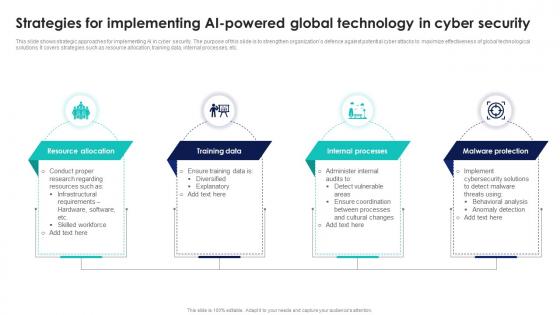 Strategies For Implementing AI Powered Global Technology In Cyber Security
Strategies For Implementing AI Powered Global Technology In Cyber SecurityThis slide shows strategic approaches for implementing AI in cyber security. The purpose of this slide is to strengthen organizations defence against potential cyber attacks to maximize effectiveness of global technological solutions. It covers strategies such as resource allocation, training data, internal processes, etc. Presenting our set of slides with Strategies For Implementing AI Powered Global Technology In Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Resource Allocation, Training Data, Internal Processes.
-
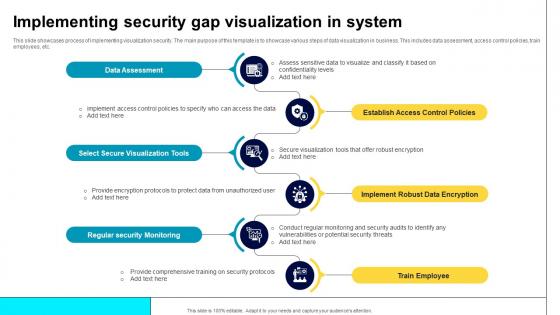 Implementing Security Gap Visualization In System
Implementing Security Gap Visualization In SystemThis slide showcases process of implementing visualization security. The main purpose of this template is to showcase various steps of data visualization in business. This includes data assessment, access control policies, train employees, etc. Presenting our set of slides with name Implementing Security Gap Visualization In System. This exhibits information on Six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Assessment, Select Secure Visualization Tools, Establish Access Control Policies, Regular Security Monitoring.
-
 Implement ATP Cyber Security Strategies In Organisation
Implement ATP Cyber Security Strategies In OrganisationThis slide depicts the strategies for cyber security ATP. Its objective is to help formulate advanced strategies for threat protection. This slide includes broad test repository, benign software behaviour, analysis of data, etc. Presenting our set of slides with name Implement ATP Cyber Security Strategies In Organisation. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Broad Test Repository, Benign Software Behaviour, Analysis Of Data.
-
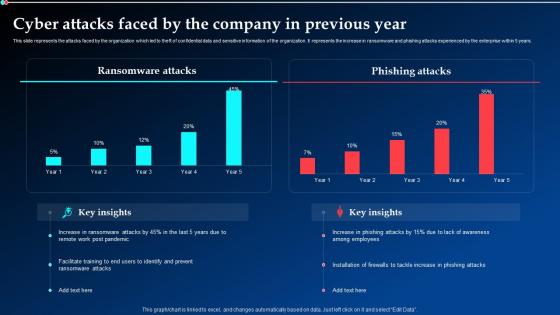 Cyber Attacks Faced By The Company In Previous Year Implementing Cyber Security Ppt Demonstration
Cyber Attacks Faced By The Company In Previous Year Implementing Cyber Security Ppt DemonstrationThis slide represents the attacks faced by the organization which led to theft of confidential data and sensitive information of the organization. It represents the increase in ransomware and phishing attacks experienced by the enterprise within 5 years. Present the topic in a bit more detail with this Cyber Attacks Faced By The Company In Previous Year Implementing Cyber Security Ppt Demonstration. Use it as a tool for discussion and navigation on Ransomware Attacks, Phishing Attacks, Previous Year. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
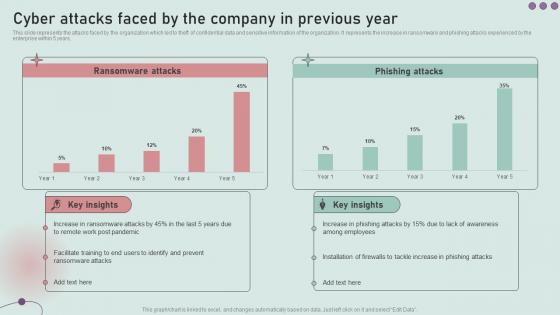 Cyber Attacks Faced By The Company In Previous Year Development And Implementation Of Security
Cyber Attacks Faced By The Company In Previous Year Development And Implementation Of SecurityThis slide represents the attacks faced by the organization which led to theft of confidential data and sensitive information of the organization. It represents the increase in ransomware and phishing attacks experienced by the enterprise within 5 years. Present the topic in a bit more detail with this Cyber Attacks Faced By The Company In Previous Year Development And Implementation Of Security. Use it as a tool for discussion and navigation on Ransomware Attacks, Phishing Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
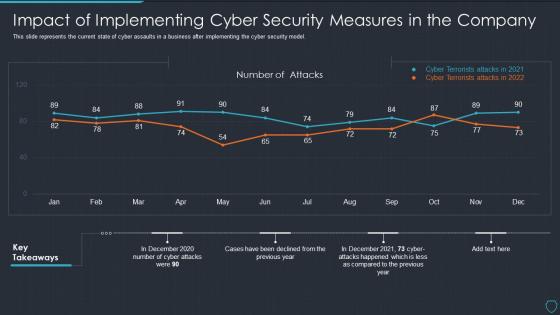 Cyberterrorism it impact of implementing cyber security measures in the company
Cyberterrorism it impact of implementing cyber security measures in the companyThis slide represents the current state of cyber assaults in a business after implementing the cyber security model. Present the topic in a bit more detail with this Cyberterrorism IT Impact Of Implementing Cyber Security Measures In The Company. Use it as a tool for discussion and navigation on Number Attacks, Cyber Terrorists Attacks 2021, Cyber Terrorists Attacks 2022. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Financial Implementing Cyber Security Incident Management Ppt Topics
Financial Implementing Cyber Security Incident Management Ppt TopicsPresent the topic in a bit more detail with this Financial Implementing Cyber Security Incident Management Ppt Topics. Use it as a tool for discussion and navigation on Minimum, Medium, Maximum. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 30 60 90 Days Plan To Implement Cloud Security In Business
30 60 90 Days Plan To Implement Cloud Security In BusinessThis slide defines the 30,60 and 90-days plan to implement cloud security in the organization and what tasks would be performed on each 30 days interval. Introducing 30 60 90 Days Plan To Implement Cloud Security In Business to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispense information on Data Access, Operations Performed, Cloud Services, using this template. Grab it now to reap its full benefits.
-
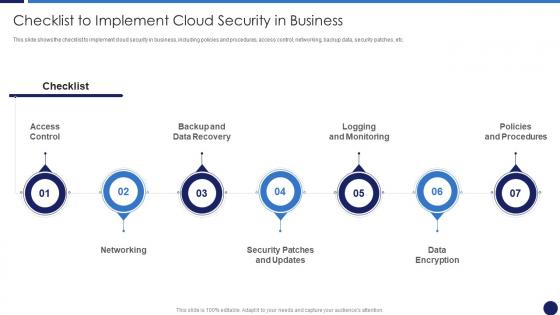 Checklist To Implement Cloud Security In Business Cloud Data Protection
Checklist To Implement Cloud Security In Business Cloud Data ProtectionThis slide shows the checklist to implement cloud security in business, including policies and procedures, access control, networking, backup data, security patches, etc. Introducing Checklist To Implement Cloud Security In Business Cloud Data Protection to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispense information on Logging And Monitoring, Networking, Data Encryption, using this template. Grab it now to reap its full benefits.
-
 Timeline For Cyber Security Implementation In Company
Timeline For Cyber Security Implementation In CompanyIntroducing our premium set of slides with name Timeline For Cyber Security Implementation In Company. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Timeline For Cyber Security, Implementation In Company. So download instantly and tailor it with your information.
-
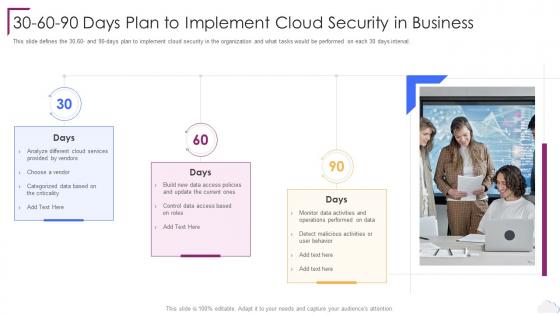 Cloud Computing Security 30 60 90 Days Plan To Implement Cloud Security In Business
Cloud Computing Security 30 60 90 Days Plan To Implement Cloud Security In BusinessThis slide defines the 30,60 and 90 days plan to implement cloud security in the organization and what tasks would be performed on each 30 days interval. Increase audience engagement and knowledge by dispensing information using Cloud Computing Security 30 60 90 Days Plan To Implement Cloud Security In Business. This template helps you present information on three stages. You can also present information on Monitor Data Activities, User Behavior, Cloud Services using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
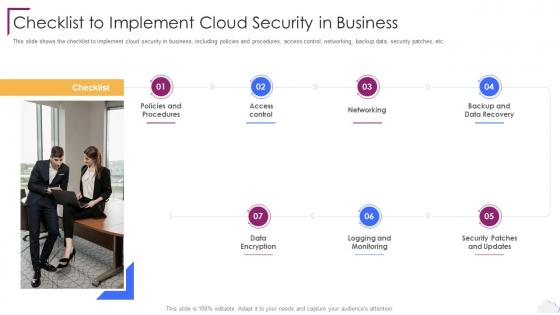 Cloud Computing Security Checklist To Implement Cloud Security In Business
Cloud Computing Security Checklist To Implement Cloud Security In BusinessThis slide shows the checklist to implement cloud security in business, including policies and procedures, access control, networking, backup data, security patches, etc. Introducing Cloud Computing Security Checklist To Implement Cloud Security In Business to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Logging And Monitoring, Data Encryption, Backup And Data Recovery, Policies And Procedures, Networking, using this template. Grab it now to reap its full benefits.
-
 Checklist To Implement Cloud Security In Business Cloud Information Security
Checklist To Implement Cloud Security In Business Cloud Information SecurityThis slide shows the checklist to implement cloud security in business, including policies and procedures, access control, networking, backup data, security patches, etc.Introducing Checklist To Implement Cloud Security In Business Cloud Information Security to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Impact Analysis, Recovery Strategies, Plan Development using this template. Grab it now to reap its full benefits.
-
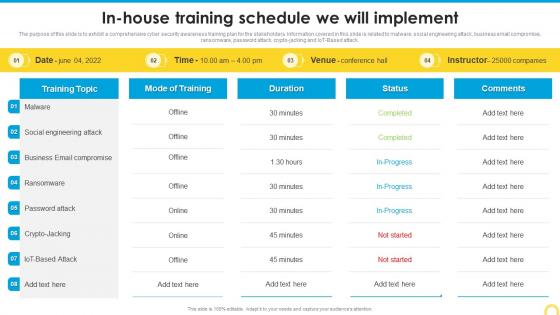 In House Training Schedule We Will Implement Building A Security Awareness Program
In House Training Schedule We Will Implement Building A Security Awareness ProgramThe purpose of this slide is to exhibit a comprehensive cyber security awareness training plan for the stakeholders. Information covered in this slide is related to malware, social engineering attack, business email compromise, ransomware, password attack, crypto jacking and IoT Based attack. Deliver an outstanding presentation on the topic using this In House Training Schedule We Will Implement Building A Security Awareness Program. Dispense information and present a thorough explanation of Social Engineering Attack, Business Email Compromise, Ransomware using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
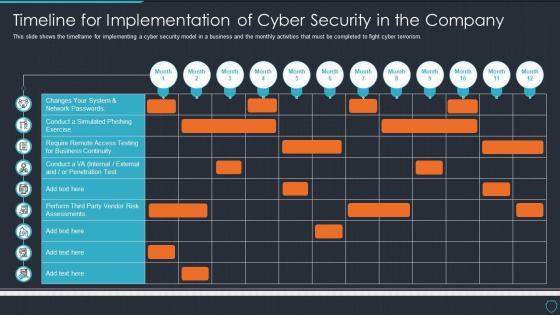 Cyberterrorism it timeline for implementation of cyber security in the company
Cyberterrorism it timeline for implementation of cyber security in the companyThis slide shows the timeframe for implementing a cyber security model in a business and the monthly activities that must be completed to fight cyber terrorism. Present the topic in a bit more detail with this Cyberterrorism IT Timeline For Implementation Of Cyber Security In The Company. Use it as a tool for discussion and navigation on Changes System, Network Passwords, Penetration Test. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
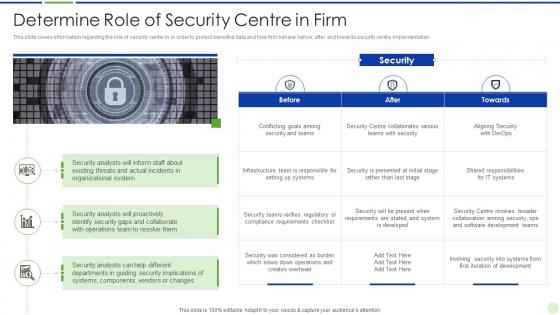 Implementing advanced analytics system at workplace determine role of security centre in firm
Implementing advanced analytics system at workplace determine role of security centre in firmThis slide covers information regarding the role of security center in in order to protect sensitive data and how firm behave before, after and towards security centre implementation. Present the topic in a bit more detail with this Implementing Advanced Analytics System At Workplace Determine Role Of Security Centre In Firm. Use it as a tool for discussion and navigation on Determine Role Of Security Centre In Firm. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
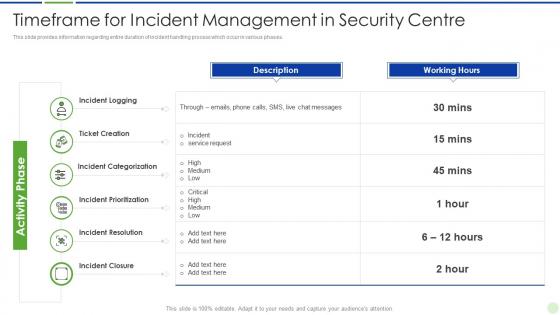 Implementing advanced analytics system at workplace timeframe for incident management in security centre
Implementing advanced analytics system at workplace timeframe for incident management in security centreThis slide provides information regarding entire duration of incident handling process which occur in various phases. Present the topic in a bit more detail with this Implementing Advanced Analytics System At Workplace Timeframe For Incident Management In Security Centre. Use it as a tool for discussion and navigation on Timeframe, Management, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 In House Training Schedule We Will Implement Implementing Security Awareness Training
In House Training Schedule We Will Implement Implementing Security Awareness TrainingThe purpose of this slide is to exhibit a comprehensive cyber security awareness training plan for the stakeholders. Information covered in this slide is related to malware, social engineering attack, business email compromise, ransomware, password attack, crypto-jacking and IoT Based attack. Deliver an outstanding presentation on the topic using this In House Training Schedule We Will Implement Implementing Security Awareness Training. Dispense information and present a thorough explanation of Training Topic, Mode Of Training, Social Engineering Attack using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Awareness Trends In 2023 Implementing Security Awareness Training
Cyber Security Awareness Trends In 2023 Implementing Security Awareness TrainingThe purpose of this slide is to showcase security awareness trends which the organization has to look out for in 2023. Increase malware and ransomware attack, more employees will be targeted by mobile malware attack and advancement of phishing attack are some of the major trends mentioned in the slide. Introducing Cyber Security Awareness Trends In 2023 Implementing Security Awareness Training to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Ransomware Attack, Malware Attack, Phishing Attack, using this template. Grab it now to reap its full benefits.
-
 Impact Of E Security System Implementation In Organizations
Impact Of E Security System Implementation In OrganizationsThis slide mentions the impact of implementing e-security systems in organizations. The effects include Asset Protection, Security Updates, Conflict Resolution and Automation and Analytics. Presenting our set of slides with name Impact Of E Security System Implementation In Organizations. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Implementation, Organizations, Automation.
-
 Our Mission Implementing Cyber Security Incident Management Ppt Sample
Our Mission Implementing Cyber Security Incident Management Ppt SampleIntroducing Our Mission Implementing Cyber Security Incident Management Ppt Sample to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Vision, Mission, Goal, using this template. Grab it now to reap its full benefits.
-
 Puzzle Implementing Cyber Security Incident Management Ppt Topics
Puzzle Implementing Cyber Security Incident Management Ppt TopicsIncrease audience engagement and knowledge by dispensing information using Puzzle Implementing Cyber Security Incident Management Ppt Topics. This template helps you present information on four stages. You can also present information on Puzzle using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Swot Implementing Cyber Security Incident Management Ppt Brochure
Swot Implementing Cyber Security Incident Management Ppt BrochureIntroducing Swot Implementing Cyber Security Incident Management Ppt Brochure to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Strengths, Weaknesses, Opportunities, Threats, using this template. Grab it now to reap its full benefits.
-
 Table Of Contents For Implementing Cyber Security Incident Management Ppt Clipart
Table Of Contents For Implementing Cyber Security Incident Management Ppt ClipartPresent the topic in a bit more detail with this Table Of Contents For Implementing Cyber Security Incident Management Ppt Clipart. Use it as a tool for discussion and navigation on Response Management, Cyber Security Incident, Dashboards. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Thanks For Watching Implementing Cyber Security Incident Management Ppt Inspiration
Thanks For Watching Implementing Cyber Security Incident Management Ppt InspirationIntroducing Thanks For Watching Implementing Cyber Security Incident Management Ppt Inspiration to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Address, Contact Number, Email Address, using this template. Grab it now to reap its full benefits.
-
 Timeline Implementing Cyber Security Incident Management Ppt Designs
Timeline Implementing Cyber Security Incident Management Ppt DesignsIncrease audience engagement and knowledge by dispensing information using Timeline Implementing Cyber Security Incident Management Ppt Designs. This template helps you present information on four stages. You can also present information on Timeline using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
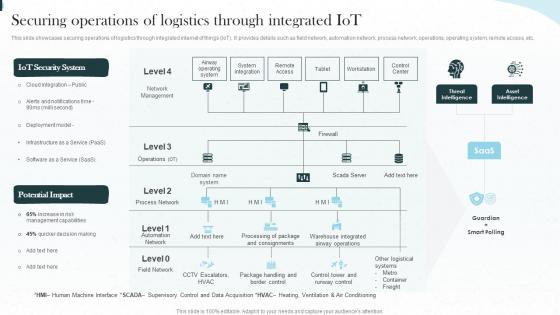 Implementing Iot Architecture In Shipping Business Securing Operations Of Logistics Through Integrated Iot
Implementing Iot Architecture In Shipping Business Securing Operations Of Logistics Through Integrated IotThis slide showcases securing operations of logistics through integrated internet of things IoT. It provides details such as field network, automation network, process network, operations, operating system, remote access, etc. Present the topic in a bit more detail with this Implementing Iot Architecture In Shipping Business Securing Operations Of Logistics Through Integrated Iot. Use it as a tool for discussion and navigation on Operations, Integrated, Workstation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Iot Security Lock For Safe Fleet Management Implementing Iot Architecture In Shipping Business
Iot Security Lock For Safe Fleet Management Implementing Iot Architecture In Shipping BusinessThe following slide illustrates internet of things IoT security lock for safe fleet management. It provides information about unlocking methods, Bluetooth, QR code, power saving, alarm notifications, large memory, etc. Deliver an outstanding presentation on the topic using this Iot Security Lock For Safe Fleet Management Implementing Iot Architecture In Shipping Business. Dispense information and present a thorough explanation of Management, Potential Impact, Key Applications using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
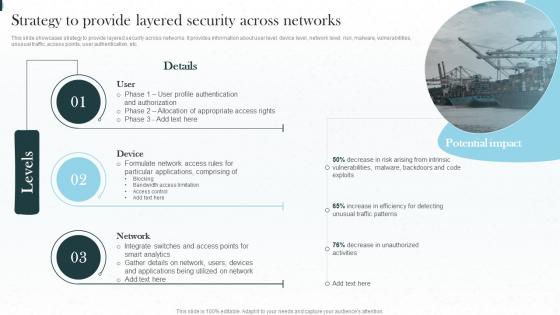 Strategy To Provide Layered Security Across Networks Implementing Iot Architecture In Shipping Business
Strategy To Provide Layered Security Across Networks Implementing Iot Architecture In Shipping BusinessThis slide showcases strategy to provide layered security across networks. It provides information about user level, device level, network level, risk, malware, vulnerabilities, unusual traffic, access points, user authentication, etc. Present the topic in a bit more detail with this Strategy To Provide Layered Security Across Networks Implementing Iot Architecture In Shipping Business. Use it as a tool for discussion and navigation on Strategy, Authentication, Appropriate Access. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Timeline For Security Implementation Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Timeline For Security Implementation Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Timeline for security implementation colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Timeline For Security Implementation Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Timeline For Security Implementation Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Timeline for security implementation monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.


