Powerpoint Templates and Google slides for Improved Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Need To Implement IoT Cyber Security Improving IoT Device Cybersecurity IoT SS
Need To Implement IoT Cyber Security Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to exhibit need to implement Internet of Things IoT security in order to avoid cyber attack and minimize losses. The slide covers information about data protection of users, adhering to regulatory standards, limited security of IoT devices, etc. Introducing Need To Implement IoT Cyber Security Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Required, Companies, Potential, using this template. Grab it now to reap its full benefits.
-
 Pricing Plan Of IoT Security Improving IoT Device Cybersecurity IoT SS
Pricing Plan Of IoT Security Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase pricing plan of Internet of Things IoT security awareness package offered by third party. The pricing plan varies according for total number of employees and includes silver, gold, platinum, and diamond. Present the topic in a bit more detail with this Pricing Plan Of IoT Security Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Security, Packages, Plan. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Running IoT Cyber Security Awareness Improving IoT Device Cybersecurity IoT SS
Running IoT Cyber Security Awareness Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to exhibit Internet of Things IoT security awareness campaign for employees. The slide covers information about security campaign goals, security campaign topics to cover, and various activities which will be covered in campaign. Increase audience engagement and knowledge by dispensing information using Running IoT Cyber Security Awareness Improving IoT Device Cybersecurity IoT SS. This template helps you present information on two stages. You can also present information on Security, Protection, Campaign using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
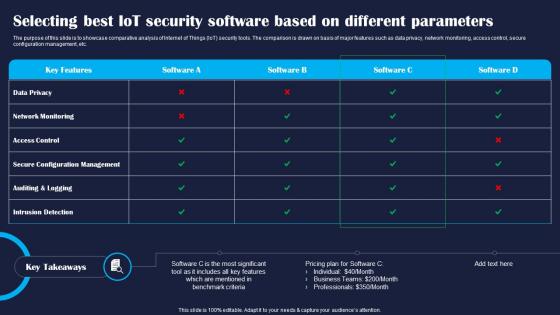 Selecting Best IoT Security Software Based Improving IoT Device Cybersecurity IoT SS
Selecting Best IoT Security Software Based Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase comparative analysis of Internet of Things IoT security tools. The comparison is drawn on basis of major features such as data privacy, network monitoring, access control, secure configuration management, etc. Deliver an outstanding presentation on the topic using this Selecting Best IoT Security Software Based Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Selecting, Software, Parameters using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
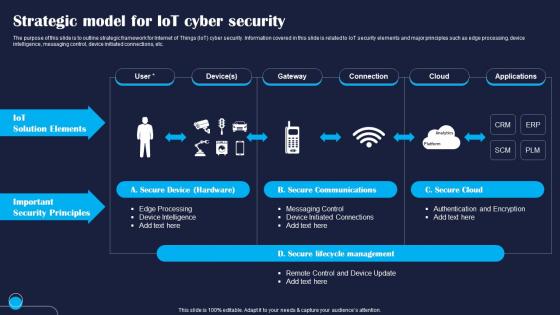 Strategic Model For IoT Cyber Security Improving IoT Device Cybersecurity IoT SS
Strategic Model For IoT Cyber Security Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to outline strategic framework for Internet of Things IoT cyber security. Information covered in this slide is related to IoT security elements and major principles such as edge processing, device intelligence, messaging control, device initiated connections, etc. Deliver an outstanding presentation on the topic using this Strategic Model For IoT Cyber Security Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Elements, Security, Device using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Stuxnet Attack Caused By IoT Security Improving IoT Device Cybersecurity IoT SS
Stuxnet Attack Caused By IoT Security Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to highlight overview of Stuxnet attack caused by Internet of Things IoT security vulnerability. The slide covers information about attack occurred date, its overview, impact of Stuxnet attack, and key takeaways for companies. Introducing Stuxnet Attack Caused By IoT Security Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Efficiency, Reduction, Damage, using this template. Grab it now to reap its full benefits.
-
 Users Of IoT Security Software Tool Improving IoT Device Cybersecurity IoT SS
Users Of IoT Security Software Tool Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase clients of Internet of Things IoT security software. The classification is done on the basis of companies, industrial enterprises, healthcare providers, and financial services companies. Introducing Users Of IoT Security Software Tool Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Providers, Services, Enterprises, using this template. Grab it now to reap its full benefits.
-
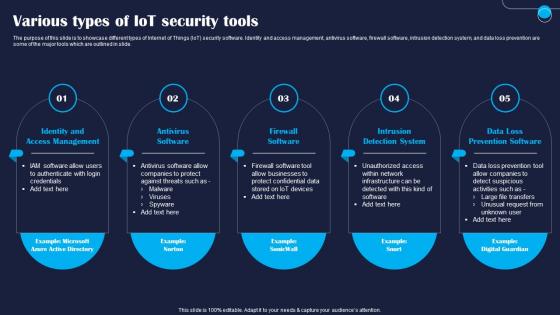 Various Types Of IoT Security Tools Improving IoT Device Cybersecurity IoT SS
Various Types Of IoT Security Tools Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase different types of Internet of Things IoT security software. Identity and access management, antivirus software, firewall software, intrusion detection system, and data loss prevention are some of the major tools which are outlined in slide. Introducing Various Types Of IoT Security Tools Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Management, Software, System, using this template. Grab it now to reap its full benefits.
-
 Verkada Hack Caused By IoT Security Improving IoT Device Cybersecurity IoT SS
Verkada Hack Caused By IoT Security Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to exhibit illustration of cyber beach caused by Internet of Things IoT security vulnerability. Information covered in this slide is related to attack launch date, attack description, impact of Verkada cyber attack, and key takeaways for business leaders. Increase audience engagement and knowledge by dispensing information using Verkada Hack Caused By IoT Security Improving IoT Device Cybersecurity IoT SS. This template helps you present information on four stages. You can also present information on Breach, Reputational, Consequences using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
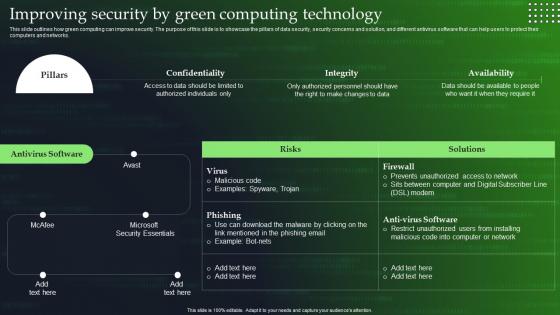 Green Cloud Computing V2 Improving Security By Green Computing Technology
Green Cloud Computing V2 Improving Security By Green Computing TechnologyThis slide outlines how green computing can improve security. The purpose of this slide is to showcase the pillars of data security, security concerns and solution, and different antivirus software that can help users to protect their computers and networks. Present the topic in a bit more detail with this Green Cloud Computing V2 Improving Security By Green Computing Technology. Use it as a tool for discussion and navigation on Green Computing, Data Security, Security Concerns And Solution, Computers And Networks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
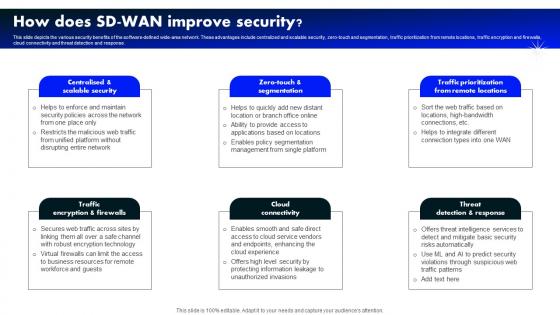 How Does Sd Wan Improve Security Software Defined Wide Area Network
How Does Sd Wan Improve Security Software Defined Wide Area NetworkThis slide depicts the various security benefits of the software-defined wide-area network. These advantages include centralized and scalable security, zero-touch and segmentation, traffic prioritization from remote locations, traffic encryption and firewalls, cloud connectivity and threat detection and response. Introducing How Does Sd Wan Improve Security Software Defined Wide Area Network to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Connectivity, Threat Detection Response, Traffic Prioritization From Remote Locations, using this template. Grab it now to reap its full benefits.
-
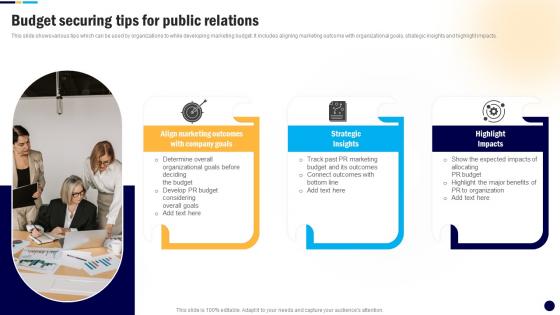 Budget Securing Tips For Public Digital PR Campaign To Improve Brands MKT SS V
Budget Securing Tips For Public Digital PR Campaign To Improve Brands MKT SS VThis slide shows various tips which can be used by organizations to while developing marketing budget. It includes aligning marketing outcome with organizational goals, strategic insights and highlight impacts. Increase audience engagement and knowledge by dispensing information using Budget Securing Tips For Public Digital PR Campaign To Improve Brands MKT SS V. This template helps you present information on three stages. You can also present information on Marketing, Strategic, Impacts using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
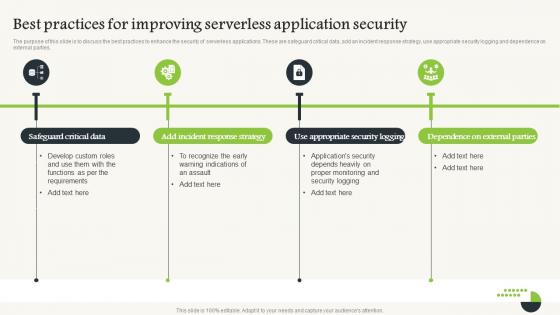 Serverless Computing V2 Best Practices For Improving Serverless Application Security
Serverless Computing V2 Best Practices For Improving Serverless Application SecurityThe purpose of this slide is to discuss the best practices to enhance the security of serverless applications. These are safeguard critical data, add an incident response strategy, use appropriate security logging and dependence on external parties. Introducing Serverless Computing V2 Best Practices For Improving Serverless Application Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Safeguard Critical Data, Incident Response Strategy, Serverless Application Security, Appropriate Security Logging, using this template. Grab it now to reap its full benefits.
-
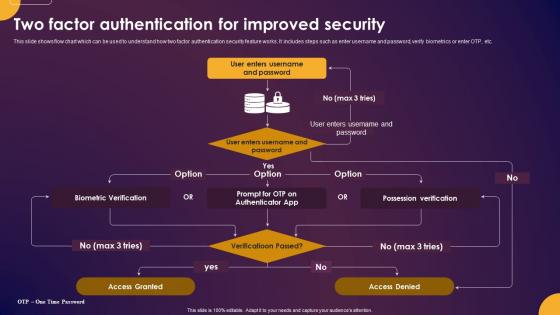 Comprehensive Guide To Understand Two Factor Authentication For Improved Security Fin SS
Comprehensive Guide To Understand Two Factor Authentication For Improved Security Fin SSThis slide shows flow chart which can be used to understand how two factor authentication security feature works. It includes steps such as enter username and password, verify biometrics or enter OTP, etc. Present the topic in a bit more detail with this Comprehensive Guide To Understand Two Factor Authentication For Improved Security Fin SS. Use it as a tool for discussion and navigation on Possession Verification, Biometric Verification, Enter Username And Password. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Website Security Management Action Plan Improved Customer Conversion With Business
Website Security Management Action Plan Improved Customer Conversion With BusinessMentioned slide provides insights into site security management tips which can be implemented by businesses to prevent website hacking. It includes key components such as select secure domain registrar, use safe plugins, anti malware programs, regular backup, SSL certification, etc. Present the topic in a bit more detail with this Website Security Management Action Plan Improved Customer Conversion With Business. Use it as a tool for discussion and navigation on Description, Priority, Manager. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
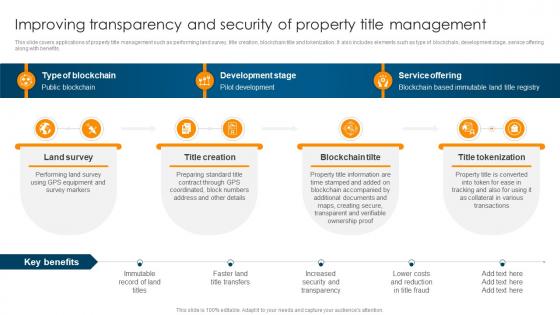 Improving Transparency And Security Of Property Title Ultimate Guide To Understand Role BCT SS
Improving Transparency And Security Of Property Title Ultimate Guide To Understand Role BCT SSThis slide covers applications of property title management such as performing land survey, title creation, blockchain title and tokenization. It also includes elements such as type of blockchain, development stage, service offering along with benefits. Increase audience engagement and knowledge by dispensing information using Improving Transparency And Security Of Property Title Ultimate Guide To Understand Role BCT SS. This template helps you present information on four stages. You can also present information on Land Survey, Title Creation, Blockchain Tilte using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Improve Cyber Security By Big Data In Companies
Improve Cyber Security By Big Data In CompaniesThis slide helps you identify and improve cyber security by integrating big data in companies. Its aim is to prevent attacks and security breaches. This slide consists of prevention of malware attacks, monitor logs, assess risk, integrate big data, etc. Introducing our premium set of slides with Improve Cyber Security By Big Data In Companies. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Attacks, Monitor, Integrate. So download instantly and tailor it with your information.
-
 Saas Cyber Security Icon To Improve Operational Efficiency
Saas Cyber Security Icon To Improve Operational EfficiencyPresenting our set of slides with Saas Cyber Security Icon To Improve Operational Efficiency This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Saas Cyber Security, Icon To Improve Operational Efficiency
-
 Zero Trust Architecture ZTA Role Of ZTNA To Improve Business Operations And Security
Zero Trust Architecture ZTA Role Of ZTNA To Improve Business Operations And SecurityThis slide talks about the ways in which ZTNA improves the business operations and security. The purpose of this slide is to showcase the various domains that zero trust network access improves, including increased user experience, remote workforce protection, improve data protection, and network visibility. Introducing Zero Trust Architecture ZTA Role Of ZTNA To Improve Business Operations And Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Traditional Method, ZTNA Approach, Login Capability, using this template. Grab it now to reap its full benefits.
-
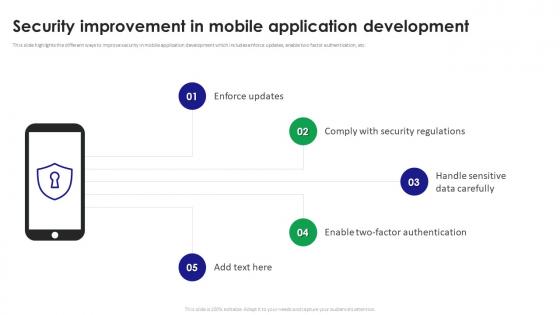 Security Improvement In Mobile Application Development
Security Improvement In Mobile Application DevelopmentThis slide highlights the different ways to improve security in mobile application development which includes enforce updates, enable two factor authentication, etc. Introducing our premium set of slides with name Security Improvement In Mobile Application Development. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security Improvement, Mobile Application Development, Handle Sensitive Data Carefully. So download instantly and tailor it with your information.
-
 Devsecops Best Practices For Secure Continuous Process Improvement In Devsecops
Devsecops Best Practices For Secure Continuous Process Improvement In DevsecopsThis slide discusses the DevSecOps program requirement for continuous improvement. The purpose of this slide is to explain the needs of the DevSecOps program for achieving efficiency, these include strategic goals, architecture operation, and program evaluation. Introducing Devsecops Best Practices For Secure Continuous Process Improvement In Devsecops to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Strategic Goals, Architecture And Operations, Program Evaluation, Devops Environment, using this template. Grab it now to reap its full benefits.
-
 Banking Solutions For Improving Customer Checklist To Ensure Secure Mobile Banking Fin SS V
Banking Solutions For Improving Customer Checklist To Ensure Secure Mobile Banking Fin SS VThis slide shows checklist which can be used to adopt various security measure while using mobile banking. It includes tasks such as change passwords frequently, monitor transactions, avoid using public networks. Deliver an outstanding presentation on the topic using this Banking Solutions For Improving Customer Checklist To Ensure Secure Mobile Banking Fin SS V. Dispense information and present a thorough explanation of Mobile Banking, Change Passwords Frequently, Monitor Transactions, Avoid Using Public Networks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Banking Solutions For Improving Customer Mobile Banking Application Security Testing Tools Fin SS V
Banking Solutions For Improving Customer Mobile Banking Application Security Testing Tools Fin SS VThis slide shows various tools which can be used to evaluate or analyze the security level of mobile banking apps. It includes features and ratings of applications. It also contains various tools such as ImmuniWeb MobileSuite, CodifiedSecurity, QARK, etc. Present the topic in a bit more detail with this Banking Solutions For Improving Customer Mobile Banking Application Security Testing Tools Fin SS V. Use it as a tool for discussion and navigation on Mobile Banking Application, Security Testing Tools, Mobile Banking Apps, Real Time Bot Protection. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
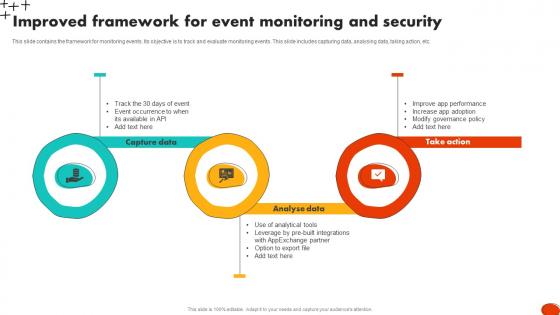 Improved Framework For Event Monitoring And Security
Improved Framework For Event Monitoring And SecurityThis slide contains the framework for monitoring events. Its objective is to track and evaluate monitoring events. This slide includes capturing data, analysing data, taking action, etc. Introducing Improved Framework For Event Monitoring And Security to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Capture Data, Analyse Data, Take Action, using this template. Grab it now to reap its full benefits.
-
 Role Of ZTNA To Improve Business Operations And Security Identity Defined Networking
Role Of ZTNA To Improve Business Operations And Security Identity Defined NetworkingThis slide talks about the ways in which ZTNA improves the business operations and security. The purpose of this slide is to showcase the various domains that zero trust network access improves, including increased user experience, remote workforce protection, improve data protection, and network visibility. Present the topic in a bit more detail with this Role Of ZTNA To Improve Business Operations And Security Identity Defined Networking. Use it as a tool for discussion and navigation on Traditional Method, Workforce Protection, Data Protection. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
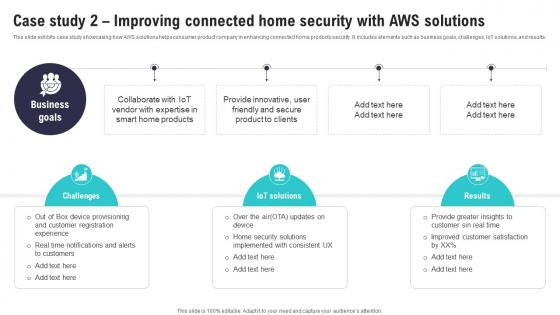 Case Study 2 Improving Connected Home Security IoT Security And Privacy Safeguarding IoT SS
Case Study 2 Improving Connected Home Security IoT Security And Privacy Safeguarding IoT SSThis slide exhibits case study showcasing how AWS solutions helps consumer product company in enhancing connected home products security. It includes elements such as business goals, challenges, IoT solutions, and results. Increase audience engagement and knowledge by dispensing information using Case Study 2 Improving Connected Home Security IoT Security And Privacy Safeguarding IoT SS. This template helps you present information on three stages. You can also present information on Security Solutions, Improved Customer Satisfaction, Provide Innovative using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
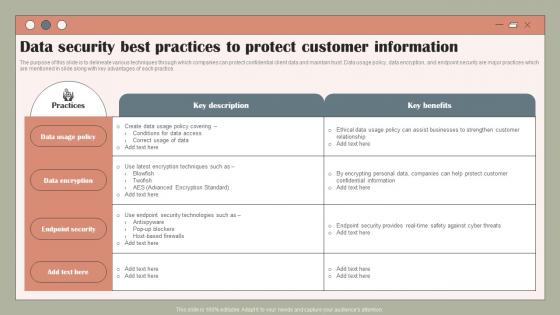 Data Security Best Practices To Protect Using Customer Data To Improve MKT SS V
Data Security Best Practices To Protect Using Customer Data To Improve MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Deliver an outstanding presentation on the topic using this Data Security Best Practices To Protect Using Customer Data To Improve MKT SS V. Dispense information and present a thorough explanation of Policy, Data, Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
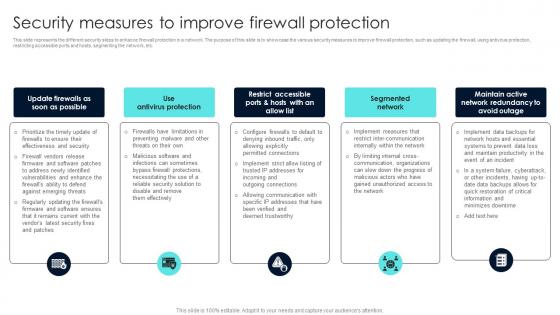 Firewall Network Security Security Measures To Improve Firewall Protection
Firewall Network Security Security Measures To Improve Firewall ProtectionThis slide represents the different security steps to enhance firewall protection in a network. The purpose of this slide is to showcase the various security measures to improve firewall protection, such as updating the firewall, using antivirus protection, restricting accessible ports and hosts, segmenting the network, etc. Introducing Firewall Network Security Security Measures To Improve Firewall Protection to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Screened Host Firewalls, Packet Filtering Router using this template. Grab it now to reap its full benefits.
-
 Agenda For Tokenization For Improved Data Security
Agenda For Tokenization For Improved Data SecurityIntroducing Agenda For Tokenization For Improved Data Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Tokenization Training Program, Budget Allocation And Roadmap, Governance, Security, using this template. Grab it now to reap its full benefits.
-
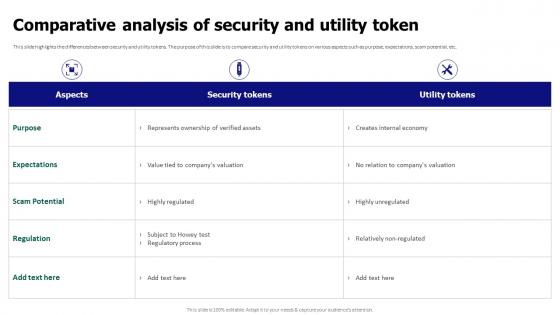 Comparative Analysis Of Security And Utility Token Tokenization For Improved Data Security
Comparative Analysis Of Security And Utility Token Tokenization For Improved Data SecurityThis slide highlights the differences between security and utility tokens. The purpose of this slide is to compare security and utility tokens on various aspects such as purpose, expectations, scam potential, etc. Present the topic in a bit more detail with this Comparative Analysis Of Security And Utility Token Tokenization For Improved Data Security. Use it as a tool for discussion and navigation on Comparative Analysis, Security And Utility Token, Expectations, Scam Potential. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Icons Slide For Tokenization For Improved Data Security
Icons Slide For Tokenization For Improved Data SecurityIntroducing our well researched set of slides titled Icons Slide For Tokenization For Improved Data Security. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
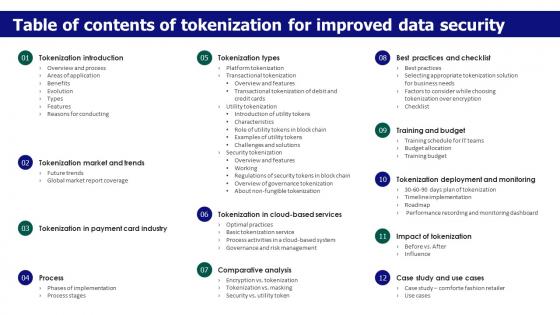 Table Of Contents Of Tokenization For Improved Data Security
Table Of Contents Of Tokenization For Improved Data SecurityIncrease audience engagement and knowledge by dispensing information using Table Of Contents Of Tokenization For Improved Data Security. This template helps you present information on twelve stages. You can also present information on Data Security, Tokenization Market And Trends, Comparative Analysis, Training And Budget using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
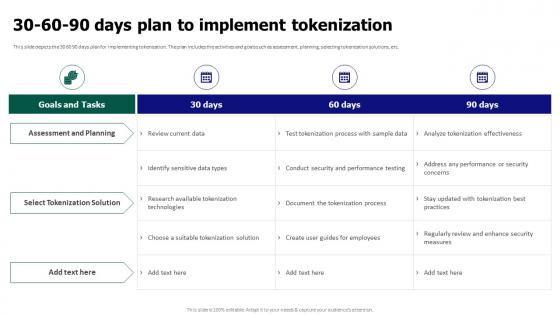 Tokenization For Improved Data Security 30 60 90 Days Plan To Implement Tokenization
Tokenization For Improved Data Security 30 60 90 Days Plan To Implement TokenizationThis slide depicts the 30 60 90 days plan for implementing tokenization. The plan includes the activities and goals such as assessment, planning, selecting tokenization solutions, etc. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security 30 60 90 Days Plan To Implement Tokenization. Dispense information and present a thorough explanation of Assessment And Planning, Select Tokenization Solution, Test Tokenization Process using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
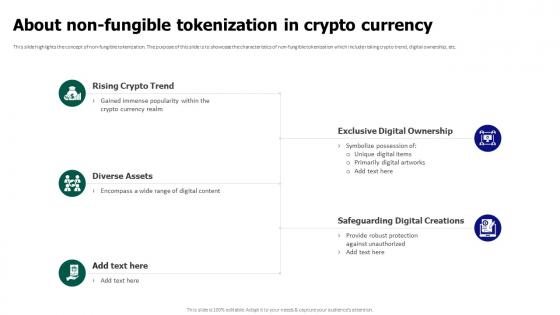 Tokenization For Improved Data Security About Non Fungible Tokenization In Crypto Currency
Tokenization For Improved Data Security About Non Fungible Tokenization In Crypto CurrencyThis slide highlights the concept of non-fungible tokenization. The purpose of this slide is to showcase the characteristics of non-fungible tokenization which include risking crypto trend, digital ownership, etc. Introducing Tokenization For Improved Data Security About Non Fungible Tokenization In Crypto Currency to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Rising Crypto Trend, Exclusive Digital Ownership, Diverse Assets, Safeguarding Digital Creations, using this template. Grab it now to reap its full benefits.
-
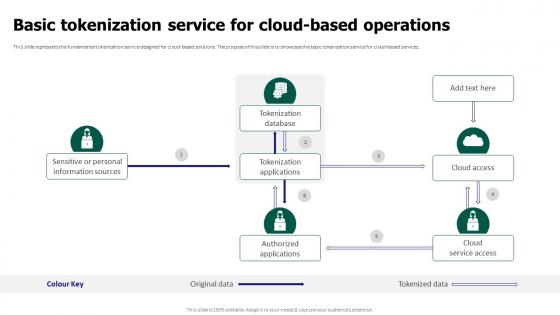 Tokenization For Improved Data Security Basic Tokenization Service For Cloud Based Operations
Tokenization For Improved Data Security Basic Tokenization Service For Cloud Based OperationsThis slide represents the fundamental tokenization service designed for cloud-based solutions. The purpose of this slide is to showcase the basic tokenization service for cloud-based services. Present the topic in a bit more detail with this Tokenization For Improved Data Security Basic Tokenization Service For Cloud Based Operations. Use it as a tool for discussion and navigation on Sensitive Or Personal Information Sources, Tokenization Database, Tokenization Applications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Tokenization For Improved Data Security Before Vs After Implementing Tokenization In Data Security
Tokenization For Improved Data Security Before Vs After Implementing Tokenization In Data SecurityThis slide showcases the comparative analysis of the before versus after tokenization. The purpose of this slide is to showcase the different performance metrics and how tokenization has improved these metrics. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Before Vs After Implementing Tokenization In Data Security. Dispense information and present a thorough explanation of Compliance With Regulations, Reduced Insider Threats, Exposure Of Sensitive Data using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
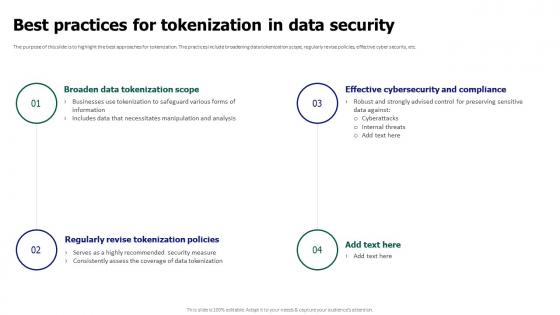 Tokenization For Improved Data Security Best Practices For Tokenization In Data Security
Tokenization For Improved Data Security Best Practices For Tokenization In Data SecurityThe purpose of this slide is to highlight the best approaches for tokenization. The practices include broadening data tokenization scope, regularly revise policies, effective cyber security, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Best Practices For Tokenization In Data Security. This template helps you present information on four stages. You can also present information on Effective Cybersecurity And Compliance, Broaden Data Tokenization Scope, Regularly Revise Tokenization Policies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
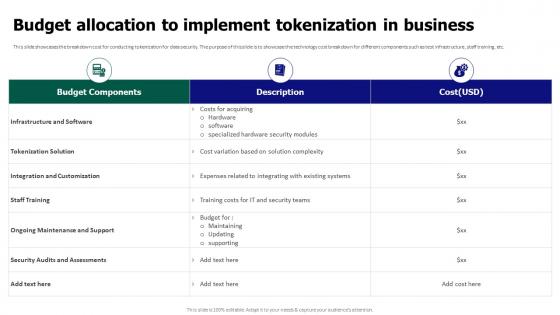 Tokenization For Improved Data Security Budget Allocation To Implement Tokenization In Business
Tokenization For Improved Data Security Budget Allocation To Implement Tokenization In BusinessThis slide showcases the breakdown cost for conducting tokenization for data security. The purpose of this slide is to showcase the technology cost breakdown for different components such as test infrastructure, staff training, etc. Present the topic in a bit more detail with this Tokenization For Improved Data Security Budget Allocation To Implement Tokenization In Business. Use it as a tool for discussion and navigation on Tokenization Solution, Integration And Customization, Infrastructure And Software. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
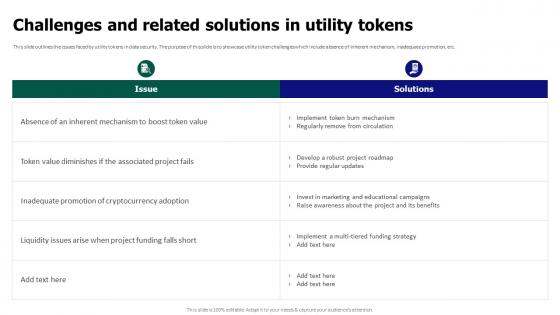 Tokenization For Improved Data Security Challenges And Related Solutions In Utility Tokens
Tokenization For Improved Data Security Challenges And Related Solutions In Utility TokensThis slide outlines the issues faced by utility tokens in data security. The purpose of this slide is to showcase utility token challenges which include absence of inherent mechanism, inadequate promotion, etc. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Challenges And Related Solutions In Utility Tokens. Dispense information and present a thorough explanation of Regularly Remove From Circulation, Inadequate Promotion, Cryptocurrency Adoption using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
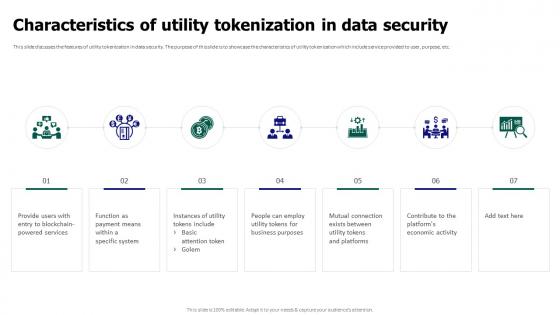 Tokenization For Improved Data Security Characteristics Of Utility Tokenization In Data Security
Tokenization For Improved Data Security Characteristics Of Utility Tokenization In Data SecurityThis slide discusses the features of utility tokenization in data security. The purpose of this slide is to showcase the characteristics of utility tokenization which include service provided to user, purpose, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Characteristics Of Utility Tokenization In Data Security. This template helps you present information on seven stages. You can also present information on Utility Tokenization, Data Security, Platforms Economic Activity, Blockchain Powered Services using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
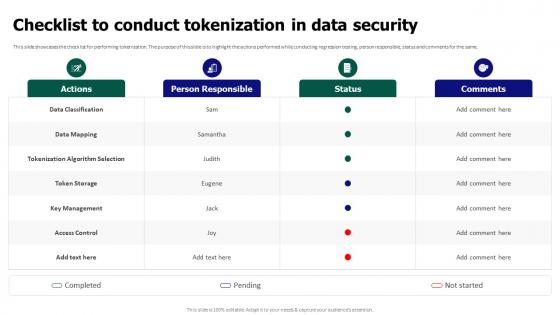 Tokenization For Improved Data Security Checklist To Conduct Tokenization In Data Security
Tokenization For Improved Data Security Checklist To Conduct Tokenization In Data SecurityThis slide showcases the checklist for performing tokenization. The purpose of this slide is to highlight the actions performed while conducting regression testing, person responsible, status and comments for the same. Present the topic in a bit more detail with this Tokenization For Improved Data Security Checklist To Conduct Tokenization In Data Security. Use it as a tool for discussion and navigation on Data Classification, Tokenization Algorithm Selection, Key Management, Access Control. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
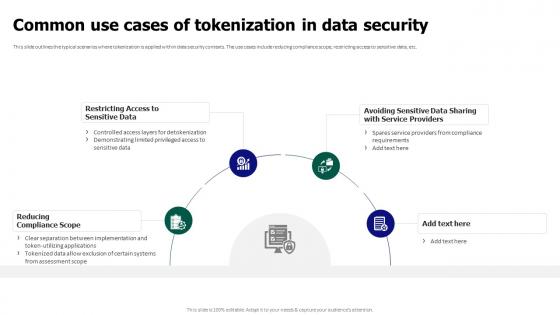 Tokenization For Improved Data Security Common Use Cases Of Tokenization In Data Security
Tokenization For Improved Data Security Common Use Cases Of Tokenization In Data SecurityThis slide outlines the typical scenarios where tokenization is applied within data security contexts. The use cases include reducing compliance scope, restricting access to sensitive data, etc. Introducing Tokenization For Improved Data Security Common Use Cases Of Tokenization In Data Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Restricting Access To Sensitive Data, Reducing Compliance Scope, Tokenization In Data Security, using this template. Grab it now to reap its full benefits.
-
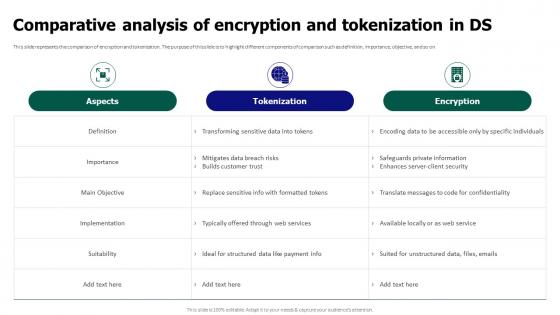 Tokenization For Improved Data Security Comparative Analysis Of Encryption And Tokenization In Ds
Tokenization For Improved Data Security Comparative Analysis Of Encryption And Tokenization In DsThis slide represents the comparison of encryption and tokenization. The purpose of this slide is to highlight different components of comparison such as definition, importance, objective, and so on. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Comparative Analysis Of Encryption And Tokenization In Ds. Dispense information and present a thorough explanation of Comparative Analysis, Encryption And Tokenization, Safeguards Private Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
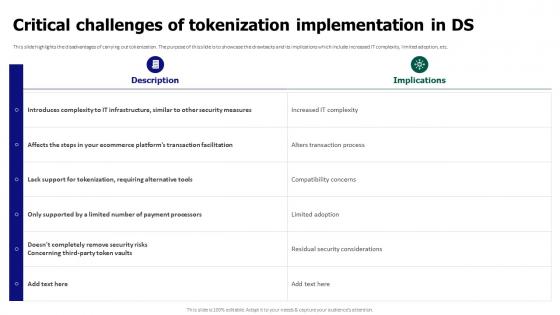 Tokenization For Improved Data Security Critical Challenges Of Tokenization Implementation In Ds
Tokenization For Improved Data Security Critical Challenges Of Tokenization Implementation In DsThis slide highlights the disadvantages of carrying out tokenization. The purpose of this slide is to showcase the drawbacks and its implications which include increased IT complexity, limited adoption, etc. Present the topic in a bit more detail with this Tokenization For Improved Data Security Critical Challenges Of Tokenization Implementation In Ds. Use it as a tool for discussion and navigation on Critical Challenges, Tokenization Implementation, Alters Transaction Process, Compatibility Concerns. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
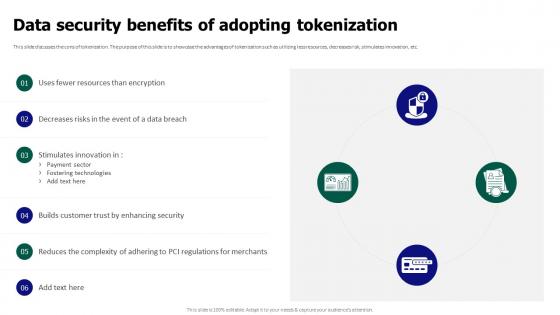 Tokenization For Improved Data Security Data Security Benefits Of Adopting Tokenization
Tokenization For Improved Data Security Data Security Benefits Of Adopting TokenizationThis slide discusses the cons of tokenization. The purpose of this slide is to showcase the advantages of tokenization such as utilizing less resources, decreases risk, stimulates innovation, etc. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Data Security Benefits Of Adopting Tokenization. Dispense information and present a thorough explanation of Builds Customer Trust, Data Security Benefits, Adopting Tokenization, Fostering Technologies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
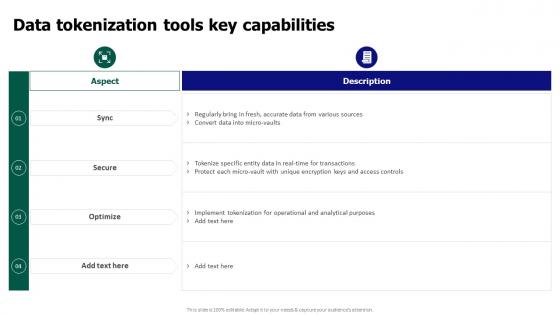 Tokenization For Improved Data Security Data Tokenization Tools Key Capabilities
Tokenization For Improved Data Security Data Tokenization Tools Key CapabilitiesPresent the topic in a bit more detail with this Tokenization For Improved Data Security Data Tokenization Tools Key Capabilities. Use it as a tool for discussion and navigation on Data Tokenization Tools, Key Capabilities, Operational And Analytical Purposes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
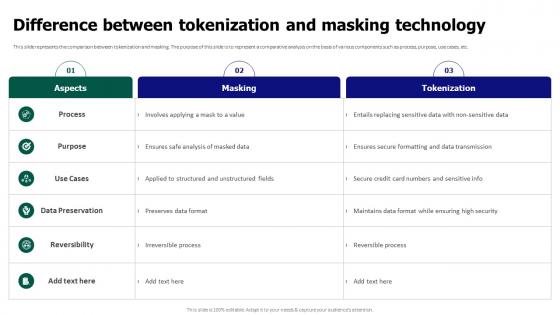 Tokenization For Improved Data Security Difference Between Tokenization And Masking Technology
Tokenization For Improved Data Security Difference Between Tokenization And Masking TechnologyThis slide represents the comparison between tokenization and masking. The purpose of this slide is to represent a comparative analysis on the basis of various components such as process, purpose, use cases, etc. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Difference Between Tokenization And Masking Technology. Dispense information and present a thorough explanation of Data Preservation, Masking Technology, Maintains Data Format using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
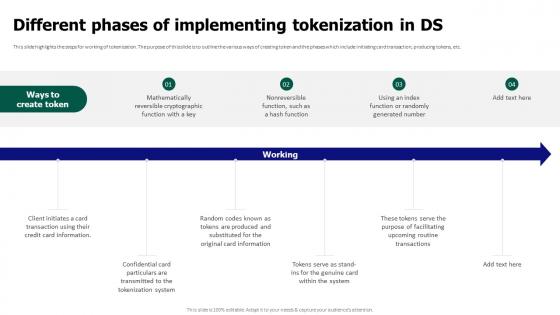 Tokenization For Improved Data Security Different Phases Of Implementing Tokenization In Ds
Tokenization For Improved Data Security Different Phases Of Implementing Tokenization In DsThis slide highlights the steps for working of tokenization. The purpose of this slide is to outline the various ways of creating token and the phases which include initiating card transaction, producing tokens, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Different Phases Of Implementing Tokenization In Ds. This template helps you present information on six stages. You can also present information on Mathematically Reversible, Cryptographic Function, Producing Tokens using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Tokenization For Improved Data Security Evolution Of Tokenization From Ancient Times To Modern Era
Tokenization For Improved Data Security Evolution Of Tokenization From Ancient Times To Modern EraThis slide outlines the history of tokenization. The purpose of this slide is to showcase the years of evolution such as 1970s digital tokenization, data compliance in 2001, etc. Present the topic in a bit more detail with this Tokenization For Improved Data Security Evolution Of Tokenization From Ancient Times To Modern Era. Use it as a tool for discussion and navigation on Evolution Of Tokenization, Tokenization Recently Secured, Payment Card Data Compliance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
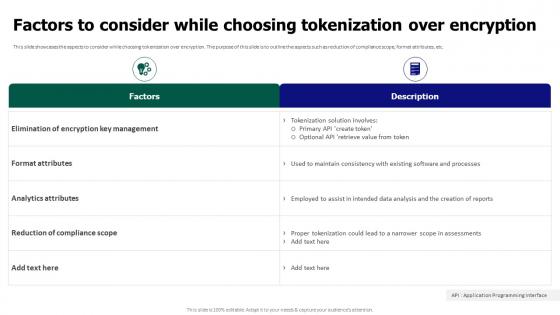 Tokenization For Improved Data Security Factors To Consider While Choosing Tokenization Over Encryption
Tokenization For Improved Data Security Factors To Consider While Choosing Tokenization Over EncryptionThis slide showcases the aspects to consider while choosing tokenization over encryption. The purpose of this slide is to outline the aspects such as reduction of compliance scope, format attributes, etc. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Factors To Consider While Choosing Tokenization Over Encryption. Dispense information and present a thorough explanation of Elimination Of Encryption Key Management, Format Attributes, Reduction Of Compliance Scope using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Tokenization For Improved Data Security For Table Of Contents
Tokenization For Improved Data Security For Table Of ContentsPresent the topic in a bit more detail with this Tokenization For Improved Data Security For Table Of Contents. Use it as a tool for discussion and navigation on Overview And Process, Areas Of Application, Reasons For Conducting. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
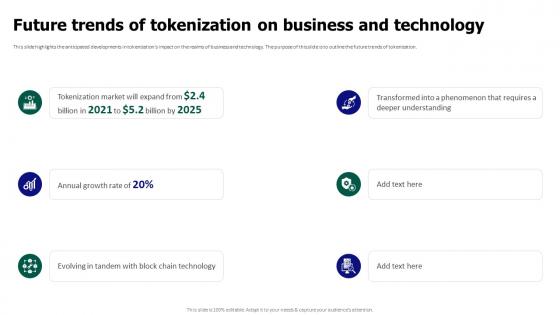 Tokenization For Improved Data Security Future Trends Of Tokenization On Business And Technology
Tokenization For Improved Data Security Future Trends Of Tokenization On Business And TechnologyThis slide highlights the anticipated developments in tokenizations impact on the realms of business and technology. The purpose of this slide is to outline the future trends of tokenization. Introducing Tokenization For Improved Data Security Future Trends Of Tokenization On Business And Technology to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Anticipated Developments, Business And Technology, Future Trends Of Tokenization, using this template. Grab it now to reap its full benefits.
-
 Tokenization For Improved Data Security Governance And Risk Management In Cloud Based Systems
Tokenization For Improved Data Security Governance And Risk Management In Cloud Based SystemsThis slide discusses the management and risk mitigation in cloud-based systems. The purpose of this slide is to showcase the elements on which tokenization depend, importance of governance and objectives of categorization. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Governance And Risk Management In Cloud Based Systems. Dispense information and present a thorough explanation of Governance And Risk Management, Cloud Based Systems, During Categorization Organization Must using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Tokenization For Improved Data Security Impact Of Tokenization On Different Industries
Tokenization For Improved Data Security Impact Of Tokenization On Different IndustriesThis slide showcases the after tokenization impact on data security. It highlights the various factors that have improved the overall security by reducing time of release, rapid defect detection, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Impact Of Tokenization On Different Industries. This template helps you present information on six stages. You can also present information on Tokenization, Data Security, Rapid Defect Detection, Ensuring Trust And Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Tokenization For Improved Data Security Introduction Of Utility Token In Data Security
Tokenization For Improved Data Security Introduction Of Utility Token In Data SecurityThis slide showcases the overview of utility tokens in data security. The purpose of this slide is to discuss the introduction of utility tokens required for data security and preventing thefts. Introducing Tokenization For Improved Data Security Introduction Of Utility Token In Data Security to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Data Security, Utility Tokens, Preventing Thefts, Unique To Each Platform, using this template. Grab it now to reap its full benefits.
-
 Tokenization For Improved Data Security Key Applications And Use Cases Of Tokenization
Tokenization For Improved Data Security Key Applications And Use Cases Of TokenizationThis slide discusses various application fields of tokenization. The purpose of this slide is to highlight the areas of application which include mobile wallet services, online retail platforms, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Key Applications And Use Cases Of Tokenization. This template helps you present information on three stages. You can also present information on Mobile Wallet Services, Online Retail Platforms, Businesses Storing Customer, Card Data Securely using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
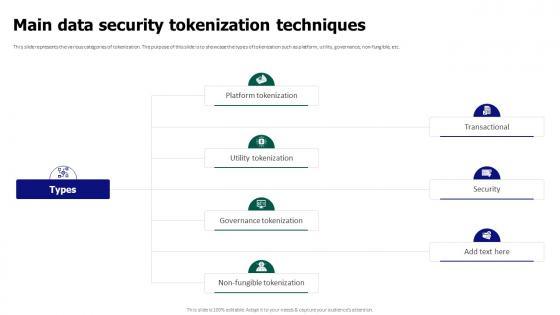 Tokenization For Improved Data Security Main Data Security Tokenization Techniques
Tokenization For Improved Data Security Main Data Security Tokenization TechniquesThis slide represents the various categories of tokenization. The purpose of this slide is to showcase the types of tokenization such as platform, utility, governance, non-fungible, etc. Introducing Tokenization For Improved Data Security Main Data Security Tokenization Techniques to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Transactional, Governance Tokenization, Utility Tokenization, Platform Tokenization, using this template. Grab it now to reap its full benefits.
-
 Tokenization For Improved Data Security Optimal Practices For Incorporating Tokenization Into Cloud
Tokenization For Improved Data Security Optimal Practices For Incorporating Tokenization Into CloudThis slide discusses the utilization of tokenization in the context of cloud-based services. The purpose of this slide is to discuss the overview of implementing tokenization for cloud based services. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Optimal Practices For Incorporating Tokenization Into Cloud. This template helps you present information on six stages. You can also present information on Incorporating Tokenization, Cloud Based Services, Protect Sensitive Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Tokenization For Improved Data Security Overview And Benefits Of Encryption For Data Security
Tokenization For Improved Data Security Overview And Benefits Of Encryption For Data SecurityThis slide outlines the introduction and cons of encryption. The purpose of this slide is to highlight the overview and advantages of encryption which include broad application, provides protection, security, etc. Present the topic in a bit more detail with this Tokenization For Improved Data Security Overview And Benefits Of Encryption For Data Security. Use it as a tool for discussion and navigation on Employing Mathematical Algorithms, Transform Sensitive Data, Unstructured Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
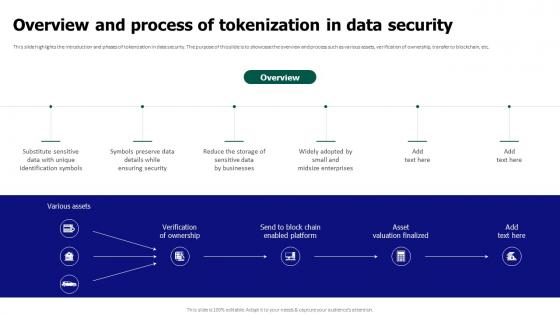 Tokenization For Improved Data Security Overview And Process Of Tokenization In Data Security
Tokenization For Improved Data Security Overview And Process Of Tokenization In Data SecurityThis slide highlights the introduction and phases of tokenization in data security. The purpose of this slide is to showcase the overview and process such as various assets, verification of ownership, transfer to blockchain, etc. Introducing Tokenization For Improved Data Security Overview And Process Of Tokenization In Data Security to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Tokenization In Data Security, While Ensuring Security, Small And Midsize Enterprises, using this template. Grab it now to reap its full benefits.



