Powerpoint Templates and Google slides for Improved Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Tokenization For Improved Data Security Overview Of Governance Tokenization In Voting Systems
Tokenization For Improved Data Security Overview Of Governance Tokenization In Voting SystemsThis slide discusses the concept of governance tokenization in data security. The purpose of this slide is to showcase the overview of governance tokenization which include usage, features, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Overview Of Governance Tokenization In Voting Systems. This template helps you present information on eight stages. You can also present information on Lack A Central Authority, Pivotal Decision Making, Widely Used Savings Protocol using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Tokenization For Improved Data Security Overview Of Platform Tokenization In Data Security
Tokenization For Improved Data Security Overview Of Platform Tokenization In Data SecurityThis slide discusses the introduction of first type tokenization in data security. The purpose of this slide is to highlight the overview of platform tokenization and how they gain security, transactional capacity, etc. Introducing Tokenization For Improved Data Security Overview Of Platform Tokenization In Data Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Ethereum Token Exchange, Platform Tokenization, Data Security, Security And Transactional Capacity, using this template. Grab it now to reap its full benefits.
-
 Tokenization For Improved Data Security Overview Of Security Tokenization In Data Security
Tokenization For Improved Data Security Overview Of Security Tokenization In Data SecurityThis slide outlines the introduction of security tokenization in data security. The purpose of this slide is to highlight the overview of security tokenization which include the definition, purpose, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Overview Of Security Tokenization In Data Security. This template helps you present information on eight stages. You can also present information on Security Tokenization, Data Security, Considering Security Tokens, Conventional Financial Securities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
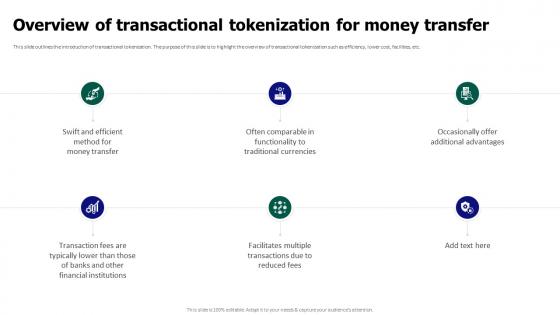 Tokenization For Improved Data Security Overview Of Transactional Tokenization For Money Transfer
Tokenization For Improved Data Security Overview Of Transactional Tokenization For Money TransferThis slide outlines the introduction of transactional tokenization. The purpose of this slide is to highlight the overview of transactional tokenization such as efficiency, lower cost, facilities, etc. Introducing Tokenization For Improved Data Security Overview Of Transactional Tokenization For Money Transfer to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Security Tokenization, Data Security, Considering Security Tokens, Conventional Financial Securities, using this template. Grab it now to reap its full benefits.
-
 Tokenization For Improved Data Security Reasons For Conducting Tokenization In Data Security
Tokenization For Improved Data Security Reasons For Conducting Tokenization In Data SecurityThis slide outlines the rationale for implementing tokenization n data security. The reasons include minimizing risks, build customer trust, advancement in payment methods, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Reasons For Conducting Tokenization In Data Security. This template helps you present information on five stages. You can also present information on Card Accepting Businesses, Regulatory Compliance, Bureaucratic Processes For Businesses using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
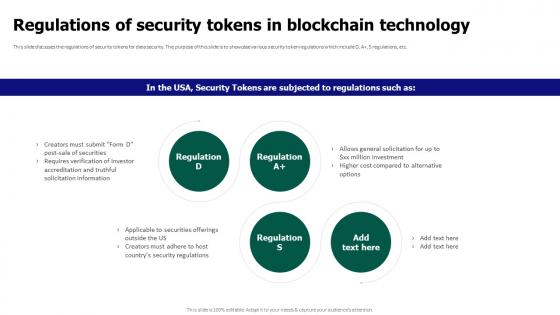 Tokenization For Improved Data Security Regulations Of Security Tokens In Blockchain Technology
Tokenization For Improved Data Security Regulations Of Security Tokens In Blockchain TechnologyThis slide discusses the regulations of security tokens for data security. The purpose of this slide is to showcase various security token regulations which include D, A plus, S regulations, etc. Introducing Tokenization For Improved Data Security Regulations Of Security Tokens In Blockchain Technology to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Regulations Of Security Tokens, Blockchain Technology, Data Security, using this template. Grab it now to reap its full benefits.
-
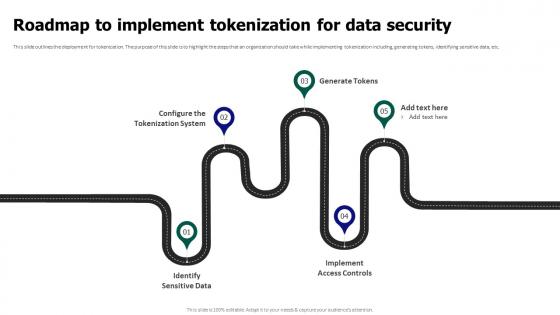 Tokenization For Improved Data Security Roadmap To Implement Tokenization For Data Security
Tokenization For Improved Data Security Roadmap To Implement Tokenization For Data SecurityThis slide outlines the deployment for tokenization. The purpose of this slide is to highlight the steps that an organization should take while implementing tokenization including, generating tokens, identifying sensitive data, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Roadmap To Implement Tokenization For Data Security. This template helps you present information on five stages. You can also present information on Identify Sensitive Data, Implement Access Controls, Configure The Tokenization System, Data Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
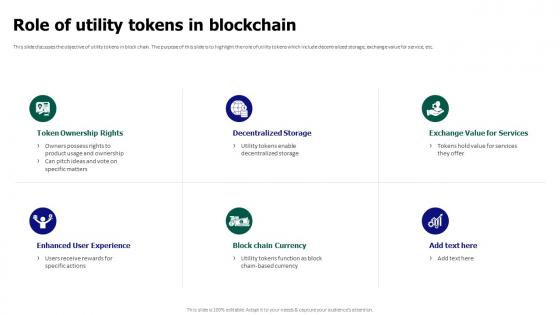 Tokenization For Improved Data Security Role Of Utility Tokens In Blockchain
Tokenization For Improved Data Security Role Of Utility Tokens In BlockchainThis slide discusses the objective of utility tokens in block chain. The purpose of this slide is to highlight the role of utility tokens which include decentralized storage, exchange value for service, etc. Introducing Tokenization For Improved Data Security Role Of Utility Tokens In Blockchain to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Decentralized Storage, Block Chain Currency, Enhanced User Experience, Token Ownership Rights, using this template. Grab it now to reap its full benefits.
-
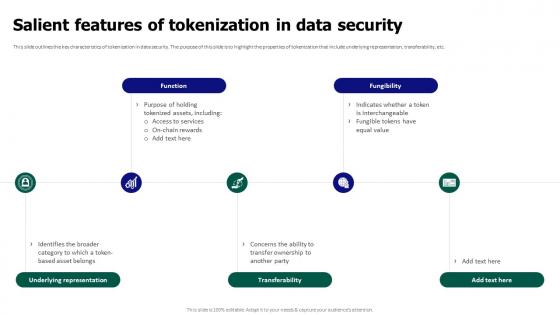 Tokenization For Improved Data Security Salient Features Of Tokenization In Data Security
Tokenization For Improved Data Security Salient Features Of Tokenization In Data SecurityThis slide outlines the key characteristics of tokenization in data security. The purpose of this slide is to highlight the properties of tokenization that include underlying representation, transferability, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Salient Features Of Tokenization In Data Security. This template helps you present information on five stages. You can also present information on Underlying Representation, Transferability, Fungibility, Data Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
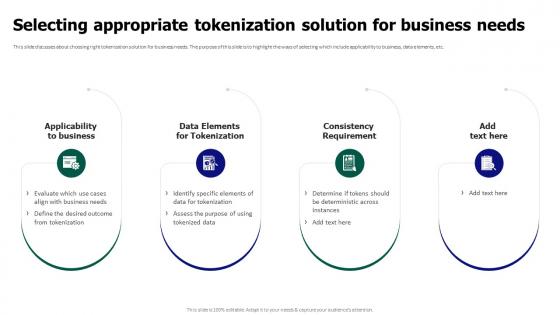 Tokenization For Improved Data Security Selecting Appropriate Tokenization Solution For Business Needs
Tokenization For Improved Data Security Selecting Appropriate Tokenization Solution For Business NeedsThis slide discusses about choosing right tokenization solution for business needs. The purpose of this slide is to highlight the ways of selecting which include applicability to business, data elements, etc. Introducing Tokenization For Improved Data Security Selecting Appropriate Tokenization Solution For Business Needs to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Consistency Requirement, Data Elements For Tokenization, Applicability To Business, using this template. Grab it now to reap its full benefits.
-
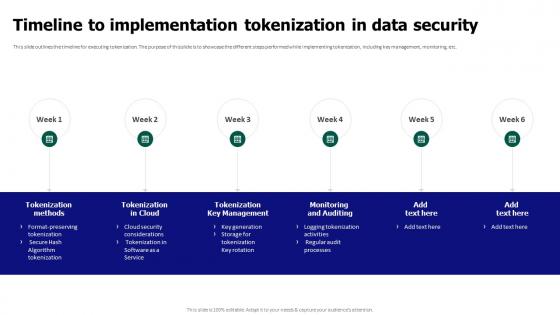 Tokenization For Improved Data Security Timeline To Implementation Tokenization In Data Security
Tokenization For Improved Data Security Timeline To Implementation Tokenization In Data SecurityThis slide outlines the timeline for executing tokenization. The purpose of this slide is to showcase the different steps performed while implementing tokenization, including key management, monitoring, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Timeline To Implementation Tokenization In Data Security. This template helps you present information on six stages. You can also present information on Tokenization Key Management, Monitoring And Auditing, Tokenization Methods, Data Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
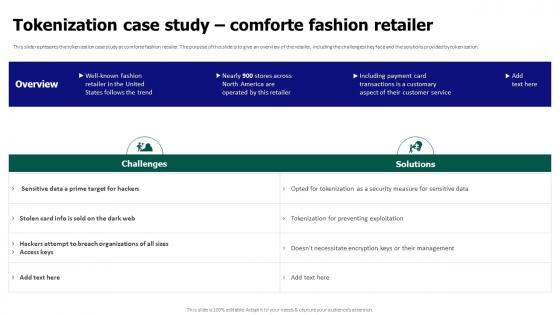 Tokenization For Improved Data Security Tokenization Case Study Comforte Fashion Retailer
Tokenization For Improved Data Security Tokenization Case Study Comforte Fashion RetailerThis slide represents the tokenization case study at comforte fashion retailer. The purpose of this slide is to give an overview of the retailer, including the challenges they face and the solutions provided by tokenization. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Tokenization Case Study Comforte Fashion Retailer. Dispense information and present a thorough explanation of Tokenization Case Study, Comforte Fashion Retailer, Customer Service, Sensitive Data using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Tokenization For Improved Data Security Tokenization In Payment Card Industry For Data Security
Tokenization For Improved Data Security Tokenization In Payment Card Industry For Data SecurityThis slide outlines the introduction of tokenization in payment card industry. The purpose of this slide is to showcase the process of tokenization in payment card industry to secure non sharable details of client. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Tokenization In Payment Card Industry For Data Security. Dispense information and present a thorough explanation of Tokenization In Payment Card, Data Security, Converts Credit Card, Point Of Sale Terminals using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
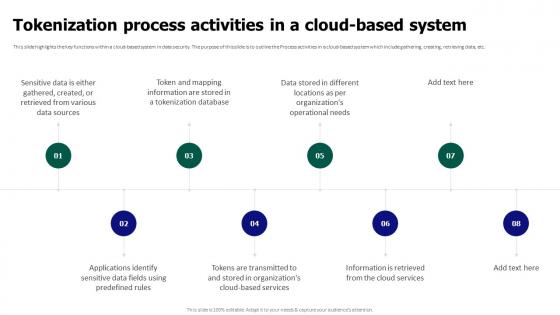 Tokenization For Improved Data Security Tokenization Process Activities In A Cloud Based System
Tokenization For Improved Data Security Tokenization Process Activities In A Cloud Based SystemThis slide highlights the key functions within a cloud-based system in data security. The purpose of this slide is to outline the Process activities in a cloud-based system which include gathering, creating, retrieving data, etc. Introducing Tokenization For Improved Data Security Tokenization Process Activities In A Cloud Based System to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Tokenization Process Activities, Cloud Based System, Retrieving Data, using this template. Grab it now to reap its full benefits.
-
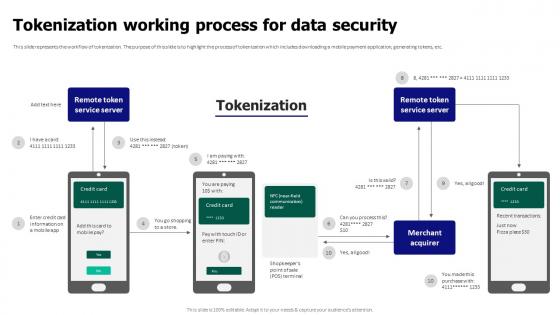 Tokenization For Improved Data Security Tokenization Working Process For Data Security
Tokenization For Improved Data Security Tokenization Working Process For Data SecurityThis slide represents the workflow of tokenization. The purpose of this slide is to highlight the process of tokenization which includes downloading a mobile payment application, generating tokens, etc. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Tokenization Working Process For Data Security. Dispense information and present a thorough explanation of Tokenization Working Process, Data Security, Mobile Payment Application, Generating Tokens using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
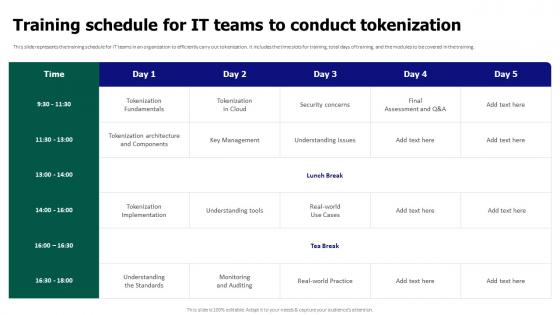 Tokenization For Improved Data Security Training Schedule For It Teams To Conduct Tokenization
Tokenization For Improved Data Security Training Schedule For It Teams To Conduct TokenizationThis slide represents the training schedule for IT teams in an organization to efficiently carry out tokenization. It includes the time slots for training, total days of training, and the modules to be covered in the training. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Training Schedule For IT Teams To Conduct Tokenization. Dispense information and present a thorough explanation of Tokenization Implementation, Tokenization Architecture, Tokenization Fundamentals using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Tokenization For Improved Data Security Transactional Tokenization Of Debit And Credit Cards
Tokenization For Improved Data Security Transactional Tokenization Of Debit And Credit CardsThis slide describes the tokenizing of debit and credit cards for transactional purposes. The purpose of this slide is to showcase the transactional tokenization of debit and credit cards. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Transactional Tokenization Of Debit And Credit Cards. This template helps you present information on six stages. You can also present information on Unique Alternate Codes, Consumer Benefits, Enhanced Security, Debit And Credit Cards using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
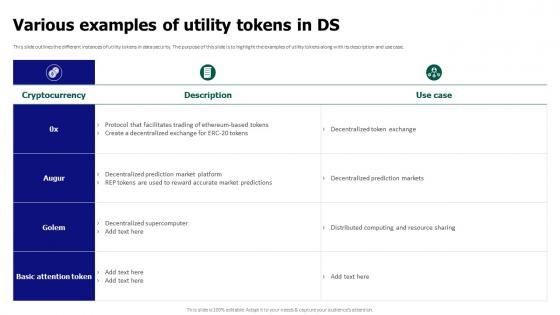 Tokenization For Improved Data Security Various Examples Of Utility Tokens In Ds
Tokenization For Improved Data Security Various Examples Of Utility Tokens In DsThis slide outlines the different instances of utility tokens in data security. The purpose of this slide is to highlight the examples of utility tokens along with its description and use case. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Various Examples Of Utility Tokens In Ds. Dispense information and present a thorough explanation of Decentralized Token Exchange, Decentralized Prediction Markets, Distributed Computing And Resource using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
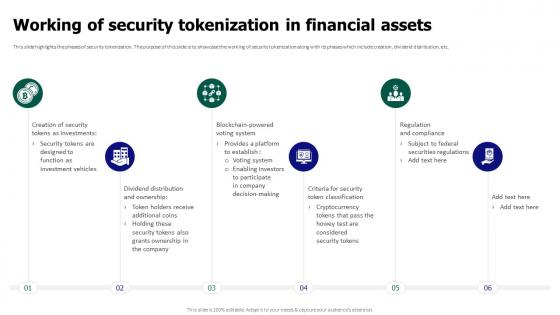 Tokenization For Improved Data Security Working Of Security Tokenization In Financial Assets
Tokenization For Improved Data Security Working Of Security Tokenization In Financial AssetsThis slide highlights the phases of security tokenization. The purpose of this slide is to showcase the working of security tokenization along with its phases which include creation, dividend distribution, etc. Introducing Tokenization For Improved Data Security Working Of Security Tokenization In Financial Assets to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Working Of Security Tokenization, Financial Assets, Dividend Distribution, Security Token Classification, using this template. Grab it now to reap its full benefits.
-
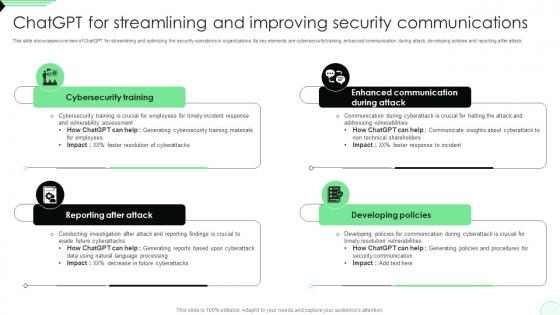 ChatGPT For Streamlining And Improving Security Opportunities And Risks Of ChatGPT AI SS V
ChatGPT For Streamlining And Improving Security Opportunities And Risks Of ChatGPT AI SS VThis slide showcases overview of ChatGPT for streamlining and optimizing the security operations in organizations. Its key elements are cybersecurity training, enhanced communication during attack, developing policies and reporting after attack. Introducing ChatGPT For Streamlining And Improving Security Opportunities And Risks Of ChatGPT AI SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Reporting After Attack, Cybersecurity Training, Developing Policies, using this template. Grab it now to reap its full benefits.
-
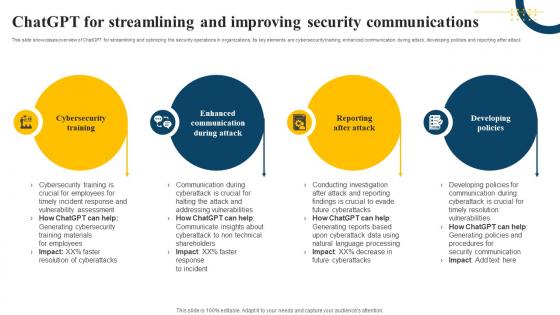 ChatGPT For Streamlining And Improving Security Communications Impact Of Generative AI SS V
ChatGPT For Streamlining And Improving Security Communications Impact Of Generative AI SS VThis slide showcases overview of ChatGPT for streamlining and optimizing the security operations in organizations. Its key elements are cybersecurity training, enhanced communication during attack, developing policies and reporting after attack. Increase audience engagement and knowledge by dispensing information using ChatGPT For Streamlining And Improving Security Communications Impact Of Generative AI SS V. This template helps you present information on four stages. You can also present information on Cybersecurity Training, Enhanced Communication, Reporting After Attack using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Methods To Improve Organizational Server Security
Methods To Improve Organizational Server SecurityFollowing slide showcases improving server security in organization through various methods, also including elements such as regularly update programs, website server backup, etc. Presenting our well structured Methods To Improve Organizational Server Security. The topics discussed in this slide are Regularly Update Programs, Website Server Backup, Digital Protection. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cyber Security Mesh Improved Scalability
Cyber Security Mesh Improved ScalabilityIntroducing our Cyber Security Mesh Improved Scalability set of slides. The topics discussed in these slides are Cyber Security Mesh, Improved Scalability. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Security incidents and improvements diagram ppt design templates
Security incidents and improvements diagram ppt design templatesPresenting security incidents and improvements diagram ppt design templates. Presenting security incidents and improvements diagram ppt design templates. This is a security incidents and improvements diagram ppt design templates. This is a three stage process. The stages in this process are prepare, detection and analysis, post incident activity.
-
 Practices To Improve Security Building A Security Awareness Program
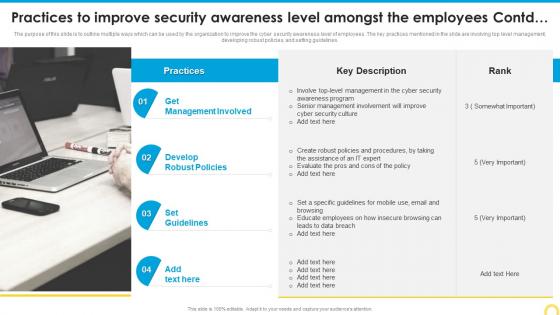
Practices To Improve Security Building A Security Awareness ProgramThe purpose of this slide is to outline multiple ways which can be used by the organization to improve the cyber security awareness level of employees. The key practices mentioned in the slide are involving top level management, developing robust policies, and setting guidelines. Introducing Practices To Improve Security Building A Security Awareness Program to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Management Involved, Develop Robust Policies, Set Guidelines, using this template. Grab it now to reap its full benefits.
-
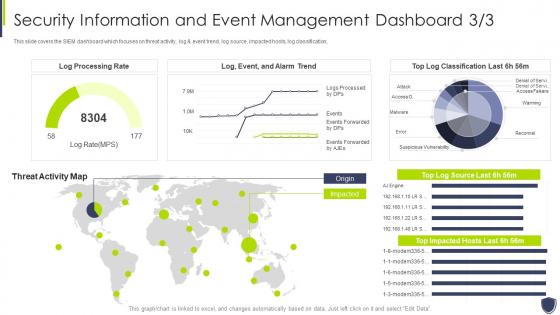 Improve it security vulnerability security information event management dashboard
Improve it security vulnerability security information event management dashboardThis slide covers the SIEM dashboard which focuses on threat activity, log and event trend, log source, impacted hosts, log classification, Deliver an outstanding presentation on the topic using this Improve It Security Vulnerability Security Information Event Management Dashboard. Dispense information and present a thorough explanation of Information, Management, Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
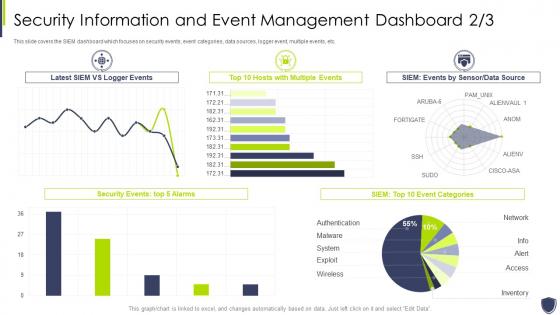 Improve it security with vulnerability event management dashboard snapshot
Improve it security with vulnerability event management dashboard snapshotThis slide covers the SIEM dashboard which focuses on security events, event categories, data sources, logger event, multiple events, etc. Deliver an outstanding presentation on the topic using this Improve It Security With Vulnerability Event Management Dashboard snapshot. Dispense information and present a thorough explanation of Information, Management, Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Practices To Improve Security Awareness Level Amongst Implementing Security Awareness Training
Practices To Improve Security Awareness Level Amongst Implementing Security Awareness TrainingThe purpose of this slide is to outline different approaches used to enhance the cyber security awareness level. Creating security awareness program, conducting quarterly training session and implementing cyber security drills are some of the major approaches which are highlighted in the slide. Deliver an outstanding presentation on the topic using this Practices To Improve Security Awareness Level Amongst Implementing Security Awareness Training. Dispense information and present a thorough explanation of Create Security, Awareness Program, Cyber Security Training using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Practices To Improve Security Awareness Level Amongst The Preventing Data Breaches Through Cyber Security
Practices To Improve Security Awareness Level Amongst The Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to outline multiple ways which can be used by the organization to improve the cyber security awareness level of employees. The key practices mentioned in the slide are involving top level management, developing robust policies, and setting guidelines. Increase audience engagement and knowledge by dispensing information using Practices To Improve Security Awareness Level Amongst The Preventing Data Breaches Through Cyber Security. This template helps you present information on four stages. You can also present information on Get Management Involved, Develop Robust Policies, Set Guidelines using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
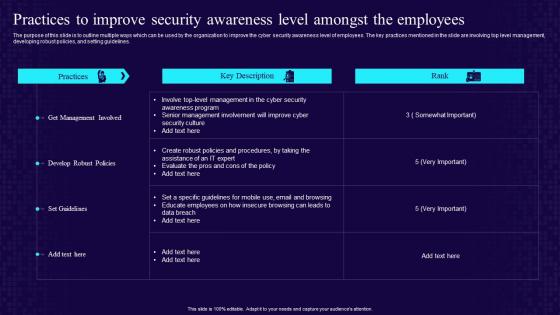 Practices To Improve Security Awareness Level Amongst The Employees Developing Cyber Security Awareness
Practices To Improve Security Awareness Level Amongst The Employees Developing Cyber Security AwarenessThe purpose of this slide is to outline multiple ways which can be used by the organization to improve the cyber security awareness level of employees. The key practices mentioned in the slide are involving top level management, developing robust policies, and setting guidelines. Deliver an outstanding presentation on the topic using this Practices To Improve Security Awareness Level Amongst The Employees Developing Cyber Security Awareness. Dispense information and present a thorough explanation of Develop Robust Policies,Get Management Involved,Security Awareness,Level Amongst using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
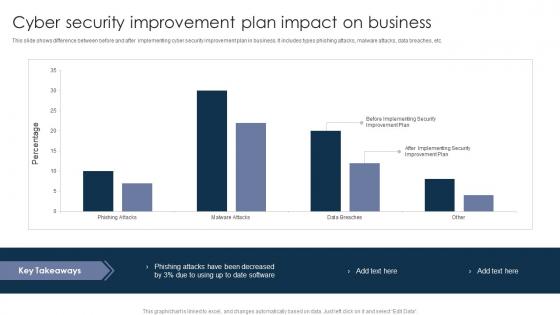 Cyber Security Improvement Plan Impact On Business
Cyber Security Improvement Plan Impact On BusinessThis slide shows difference between before and after implementing cyber security improvement plan in business. It includes types phishing attacks, malware attacks, data breaches, etc. Introducing our Cyber Security Improvement Plan Impact On Business set of slides. The topics discussed in these slides are Phishing Attacks, Malware Attacks, Data Breaches. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
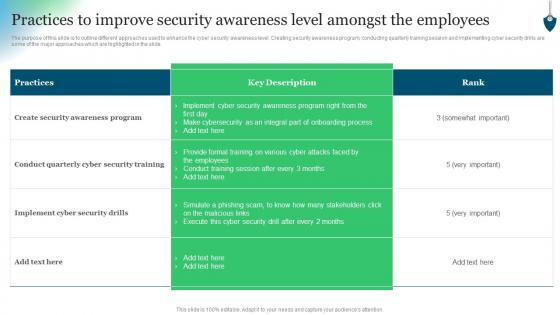 Conducting Security Awareness Practices To Improve Security Awareness Level Amongst
Conducting Security Awareness Practices To Improve Security Awareness Level AmongstThe purpose of this slide is to outline different approaches used to enhance the cyber security awareness level. Creating security awareness program, conducting quarterly training session and implementing cyber security drills are some of the major approaches which are highlighted in the slide. Present the topic in a bit more detail with this Conducting Security Awareness Practices To Improve Security Awareness Level Amongst. Use it as a tool for discussion and navigation on Create Security, Awareness Program, Provide Formal Training. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Security information event management dashboard improve security vulnerability management
Security information event management dashboard improve security vulnerability managementThis slide covers the SIEM dashboard which focuses on server status, log sources, total logs, last log, collectors, log sources etc. Deliver an outstanding presentation on the topic using this Security Information Event Management Dashboard Improve Security Vulnerability Management. Dispense information and present a thorough explanation of Management, Dashboard, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
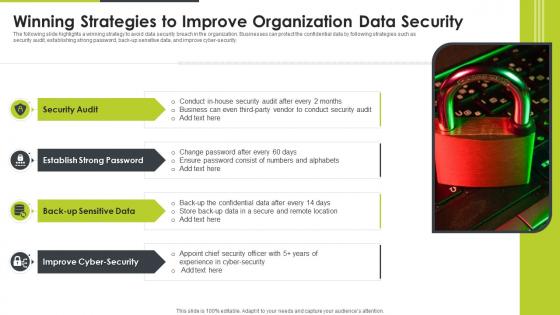 Winning Strategies To Improve Organization Data Security
Winning Strategies To Improve Organization Data SecurityThe following slide highlights a winning strategy to avoid data security breach in the organization. Businesses can protect the confidential data by following strategies such as security audit, establishing strong password, back up sensitive data, and improve cyber-security. Introducing our premium set of slides with Winning Strategies To Improve Organization Data Security. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security Audit, Improve Cyber Security, Back Up Sensitive Data. So download instantly and tailor it with your information.
-
 Three Step Plan Icon To Improve Cyber Security Measures
Three Step Plan Icon To Improve Cyber Security MeasuresPresenting our set of slides with Three Step Plan Icon To Improve Cyber Security Measures. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Three Step, Plan Icon, To Improve, Cyber Security, Measures.
-
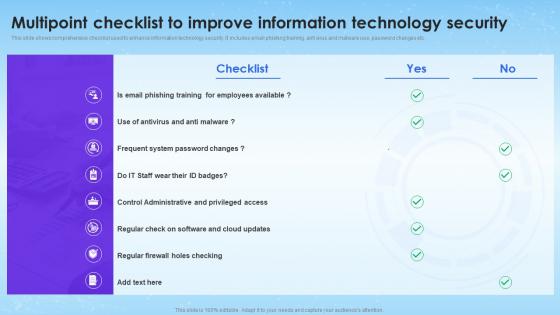 Multipoint Checklist To Improve Information Technology Security
Multipoint Checklist To Improve Information Technology SecurityThis slide shows comprehensive checklist used to enhance information technology security. It includes email phishing training, anti virus and malware use, password changes etc. Presenting our well structured Multipoint Checklist To Improve Information Technology Security. The topics discussed in this slide are Control Administrative, Antivirus And Anti Malware, Email Phishing Training. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Tips Improve Job Security In Powerpoint And Google Slides Cpb
Tips Improve Job Security In Powerpoint And Google Slides CpbPresenting our Tips Improve Job Security In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Tips Improve Job Security. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
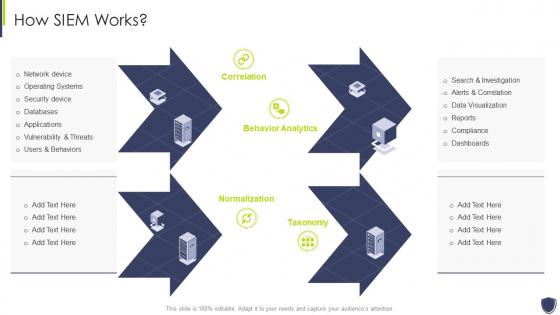 Improve it security with vulnerability management how siem works
Improve it security with vulnerability management how siem worksIncrease audience engagement and knowledge by dispensing information using Improve It Security With Vulnerability Management How Siem Works. This template helps you present information on four stages. You can also present information on Databases, Applications, Security Device using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Agenda of improve it security with vulnerability management
Agenda of improve it security with vulnerability managementIntroducing Agenda Of Improve It Security With Vulnerability Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Vulnerability, Management, Agenda, using this template. Grab it now to reap its full benefits.
-
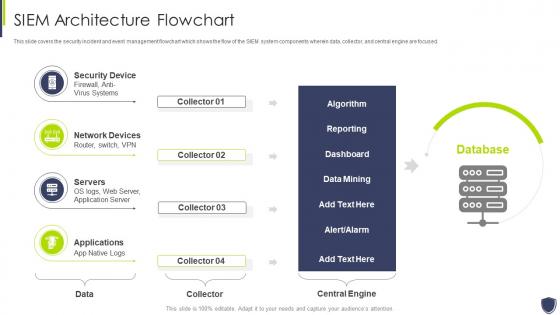 Architecture flowchart improve it security with vulnerability management
Architecture flowchart improve it security with vulnerability managementThis slide covers the security incident and event management flowchart which shows the flow of the SIEM system components wherein data, collector, and central engine are focused. Present the topic in a bit more detail with this Architecture Flowchart Improve It Security With Vulnerability Management. Use it as a tool for discussion and navigation on Security Device, Network Devices, Servers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
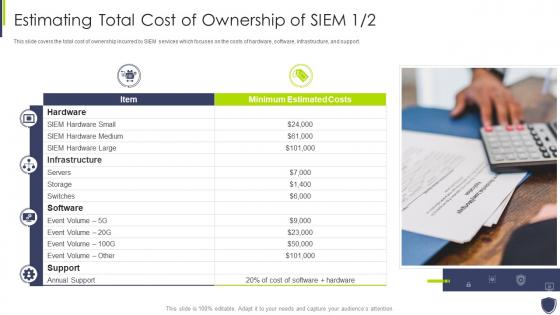 Estimating total cost of ownership improve it security vulnerability management
Estimating total cost of ownership improve it security vulnerability managementThis slide covers the total cost of ownership incurred by SIEM services which focuses on the costs of hardware, software, infrastructure, and support. Deliver an outstanding presentation on the topic using this Estimating Total Cost Of Ownership Improve It Security Vulnerability Management. Dispense information and present a thorough explanation of Estimating Total Cost Of Ownership Of SIEM using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Icons slide for improve it security with vulnerability management
Icons slide for improve it security with vulnerability managementIntroducing our well researched set of slides titled Icons Slide For Improve It Security With Vulnerability Management. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
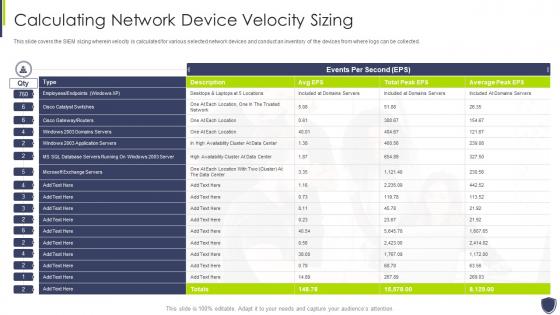 Improve it security vulnerability management calculating network device velocity sizing
Improve it security vulnerability management calculating network device velocity sizingThis slide covers the SIEM sizing wherein velocity is calculated for various selected network devices and conduct an inventory of the devices from where logs can be collected. Present the topic in a bit more detail with this Improve It Security Vulnerability Management Calculating Network Device Velocity Sizing. Use it as a tool for discussion and navigation on Calculating Network Device Velocity Sizing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
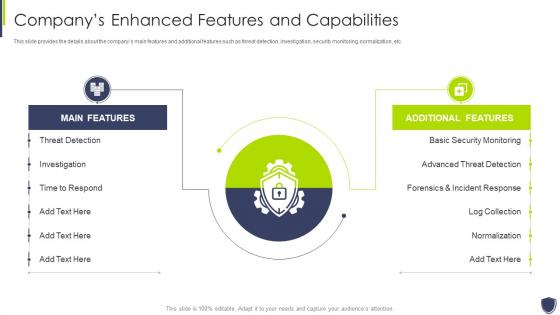 Improve it security vulnerability management companys enhanced features capabilities
Improve it security vulnerability management companys enhanced features capabilitiesThis slide provides the details about the companys main features and additional features such as threat detection, investigation, security monitoring, normalization, etc. Deliver an outstanding presentation on the topic using this Improve It Security Vulnerability Management Companys Enhanced Features Capabilities. Dispense information and present a thorough explanation of Threat Detection, Investigation, Time To Respond using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
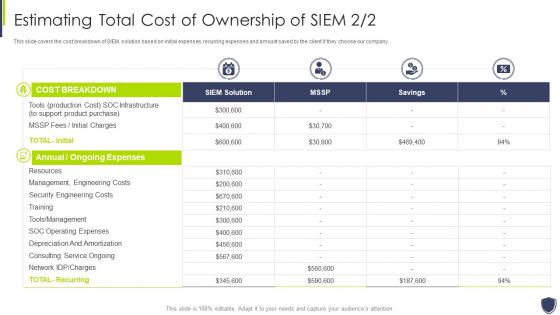 Improve it security vulnerability management estimating total cost ownership siem
Improve it security vulnerability management estimating total cost ownership siemThis slide covers the cost breakdown of SIEM solution based on initial expenses, recurring expenses and amount saved by the client if they choose our company. Present the topic in a bit more detail with this Improve It Security Vulnerability Management Estimating Total Cost Ownership Siem. Use it as a tool for discussion and navigation on Management, Engineering, Ownership. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
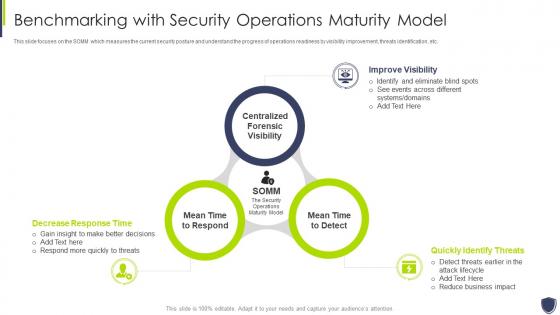 Improve it security with vulnerability benchmarking security operations maturity model
Improve it security with vulnerability benchmarking security operations maturity modelThis slide focuses on the SOMM which measures the current security posture and understand the progress of operations readiness by visibility improvement, threats identification, etc. Introducing Improve It Security With Vulnerability Benchmarking Security Operations Maturity Model to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Improve Visibility, Quickly Identify Threats, Decrease Response Time, using this template. Grab it now to reap its full benefits.
-
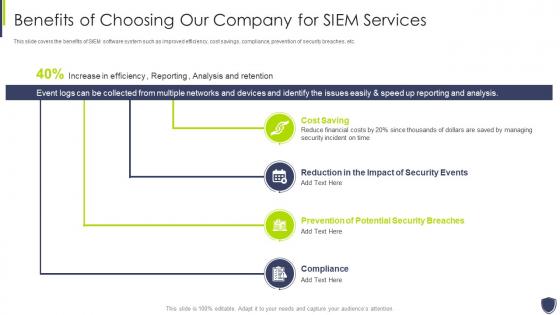 Improve it security with vulnerability benefits of choosing our company siem services
Improve it security with vulnerability benefits of choosing our company siem servicesThis slide covers the benefits of SIEM software system such as improved efficiency, cost savings, compliance, prevention of security breaches, etc. Increase audience engagement and knowledge by dispensing information using Improve It Security With Vulnerability Benefits Of Choosing Our Company Siem Services. This template helps you present information on four stages. You can also present information on Cost Saving, Reduction In The Impact Of Security Events, Compliance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
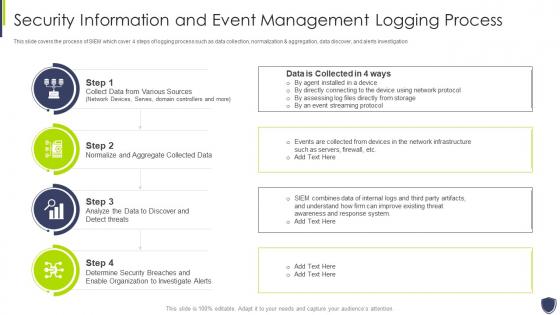 Improve it security with vulnerability information and event management logging process
Improve it security with vulnerability information and event management logging processThis slide covers the process of SIEM which cover 4 steps of logging process such as data collection, normalization and aggregation, data discover, and alerts investigation Introducing Improve It Security With Vulnerability Information And Event Management Logging Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Information, Management, Process, using this template. Grab it now to reap its full benefits.
-
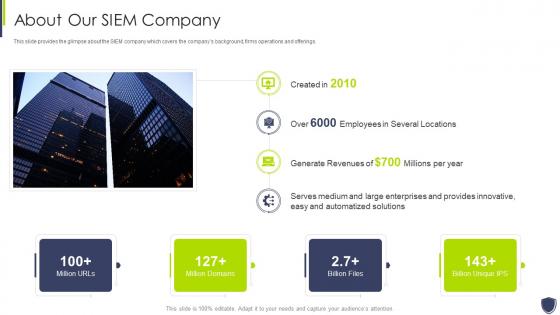 Improve it security with vulnerability management about our siem company
Improve it security with vulnerability management about our siem companyThis slide provides the glimpse about the SIEM company which covers the companys background, firms operations and offerings. Present the topic in a bit more detail with this Improve It Security With Vulnerability Management About Our Siem Company. Use it as a tool for discussion and navigation on Automatized, Solutions, Innovative. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
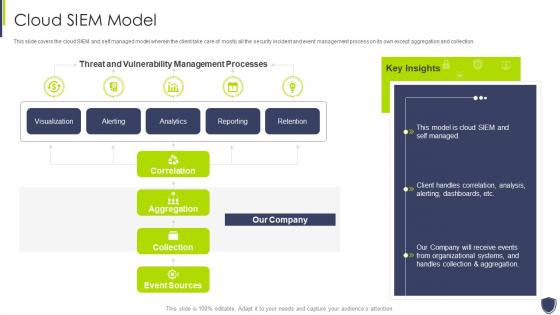 Improve it security with vulnerability management cloud siem model
Improve it security with vulnerability management cloud siem modelThis slide covers the cloud SIEM and self managed model wherein the client take care of mostly all the security incident and event management process on its own except aggregation and collection. Deliver an outstanding presentation on the topic using this Improve It Security With Vulnerability Management Cloud Siem Model. Dispense information and present a thorough explanation of Vulnerability, Management, Processes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Improve it security with vulnerability management competitive advantage
Improve it security with vulnerability management competitive advantageThis slide covers the competitive advantage scoring for security information and event management based on different factors such as value, deployment, ease of use, support, etc. Present the topic in a bit more detail with this Improve It Security With Vulnerability Management Competitive Advantage. Use it as a tool for discussion and navigation on Siem Competitive Advantage. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Improve it security with vulnerability management event management services
Improve it security with vulnerability management event management servicesThis slide covers the SIEM services offered by our company such as data aggregation, correlation, security alerts, dashboards, retention, forensic analysis, IT compliance, threat detection, etc. Increase audience engagement and knowledge by dispensing information using Improve It Security With Vulnerability Management Event Management Services. This template helps you present information on eight stages. You can also present information on Data Aggregation, Data Correlation, Security Alert using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
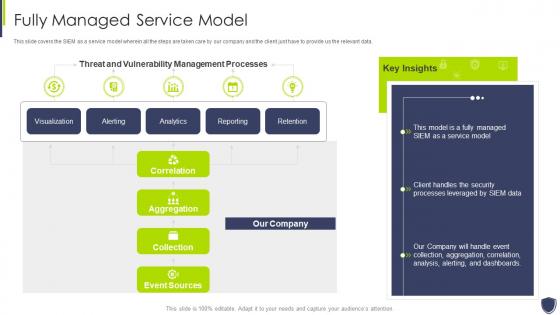 Improve it security with vulnerability management fully managed service model
Improve it security with vulnerability management fully managed service modelThis slide covers the SIEM as a service model wherein all the steps are taken care by our company and the client just have to provide us the relevant data. Deliver an outstanding presentation on the topic using this Improve It Security With Vulnerability Management Fully Managed Service Model. Dispense information and present a thorough explanation of Vulnerability, Management, Processes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
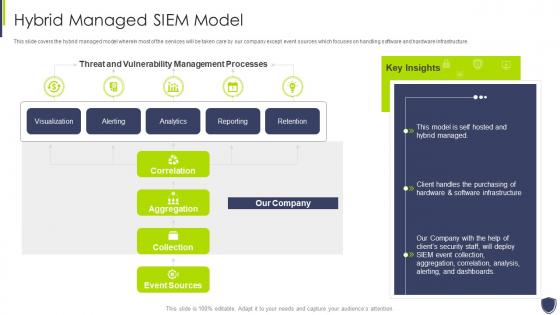 Improve it security with vulnerability management hybrid managed siem model
Improve it security with vulnerability management hybrid managed siem modelThis slide covers the hybrid managed model wherein most of the services will be taken care by our company except event sources which focuses on handling software and hardware infrastructure. Deliver an outstanding presentation on the topic using this Improve It Security With Vulnerability Management Hybrid Managed Siem Model. Dispense information and present a thorough explanation of Vulnerability, Management, Processes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Improve it security with vulnerability management integrations
Improve it security with vulnerability management integrationsPresent the topic in a bit more detail with this Improve It Security With Vulnerability Management Integrations. Use it as a tool for discussion and navigation on Applications And Devices, Network Logs, Security Events. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
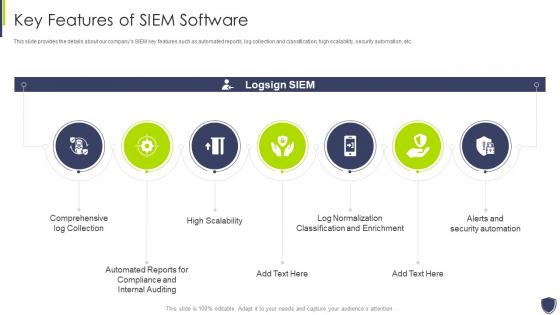 Improve it security with vulnerability management key features of siem software
Improve it security with vulnerability management key features of siem softwareThis slide provides the details about our companys SIEM key features such as automated reports, log collection and classification, high scalability, security automation, etc. Increase audience engagement and knowledge by dispensing information using Improve It Security With Vulnerability Management Key Features Of Siem Software. This template helps you present information on seven stages. You can also present information on Comprehensive, Compliance, Classification using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Improve it security with vulnerability management log management services
Improve it security with vulnerability management log management servicesThis slide covers the log management services offered by our company such as collection and normalization, search speed, real time analysis, decision making process etc. Introducing Improve It Security With Vulnerability Management Log Management Services to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Collection And Normalization, Search Speed, Real Time Analysis, using this template. Grab it now to reap its full benefits.
-
 Improve it security with vulnerability management logging sources
Improve it security with vulnerability management logging sourcesThis slide covers the logging sources for SIEM which uses different devices such as security, network, servers, and applications. Increase audience engagement and knowledge by dispensing information using Improve It Security With Vulnerability Management Logging Sources. This template helps you present information on four stages. You can also present information on Security Devices, Network Devices, Servers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Improve it security with vulnerability management need for siem software company
Improve it security with vulnerability management need for siem software companyThis slide covers the need for the SIEM software which focuses on detecting incidents, compliance regulations, and incident management Introducing Improve It Security With Vulnerability Management Need For Siem Software Company to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Detecting Incidents, Compliance With Regulations, Efficient Incident Management, using this template. Grab it now to reap its full benefits.
-
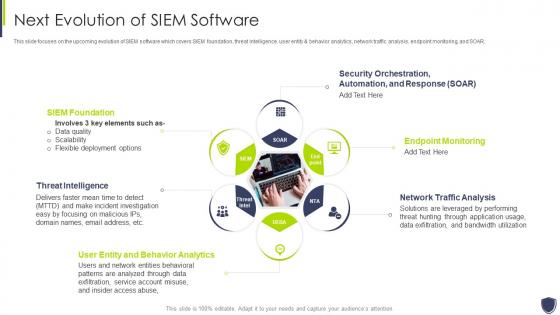 Improve it security with vulnerability management next evolution of siem software
Improve it security with vulnerability management next evolution of siem softwareThis slide focuses on the upcoming evolution of SIEM software which covers SIEM foundation, threat intelligence, user entity and behavior analytics, network traffic analysis, endpoint monitoring, and SOAR. Increase audience engagement and knowledge by dispensing information using Improve It Security With Vulnerability Management Next Evolution Of Siem Software. This template helps you present information on six stages. You can also present information on Foundation, Threat Intelligence, Analytics using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.



