Powerpoint Templates and Google slides for Information Security Plan
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
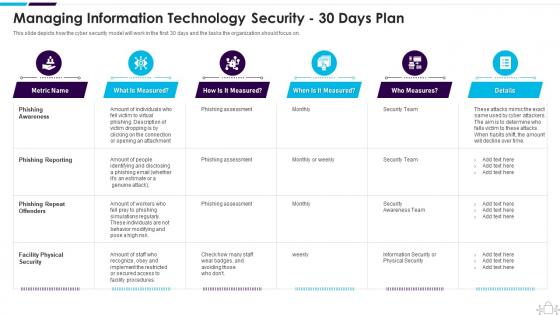 Managing Information Technology Security 30 Days Plan Information Technology Security
Managing Information Technology Security 30 Days Plan Information Technology SecurityThis slide depicts how the cyber security model will work in the first 30 days and the tasks the organization should focus on. Present the topic in a bit more detail with this Managing Information Technology Security 30 Days Plan Information Technology Security. Use it as a tool for discussion and navigation on Phishing Awareness, Phishing Reporting, Phishing Repeat Offenders. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Prepare A Disaster Recovery Plan Information Technology Security
Prepare A Disaster Recovery Plan Information Technology SecurityThis slide depicts what factors will be considered while preparing a recovery planning of an organization to come back to business quickly and effectively. Introducing Prepare A Disaster Recovery Plan Information Technology Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Assessment Report, Importance Of Assets, Recovery Plan, using this template. Grab it now to reap its full benefits.
-
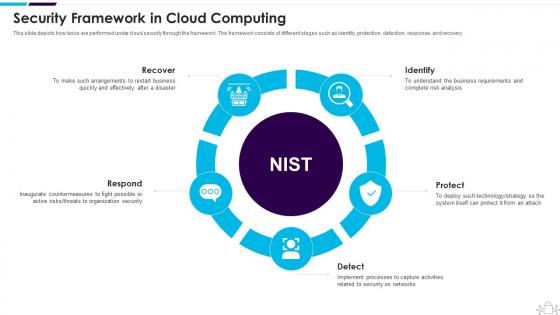 Security Framework In Cloud Computing Information Technology Security
Security Framework In Cloud Computing Information Technology SecurityThis slide depicts how tasks are performed under cloud security through the framework. The framework consists of different stages such as identity, protection, detection, response, and recovery. Increase audience engagement and knowledge by dispensing information using Security Framework In Cloud Computing Information Technology Security. This template helps you present information on five stages. You can also present information on Recover, Respond, Identify using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
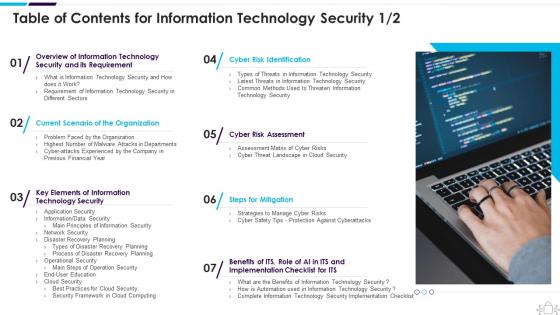 Table Of Contents For Information Technology Security
Table Of Contents For Information Technology SecurityIntroducing Table Of Contents For Information Technology Security to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Information, Technology, Security, using this template. Grab it now to reap its full benefits.
-
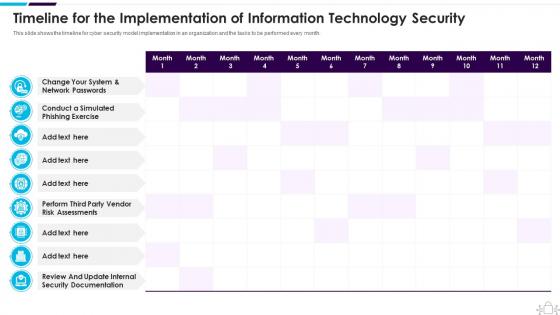 Timeline For The Implementation Of Information Technology Security
Timeline For The Implementation Of Information Technology SecurityThis slide shows the timeline for cyber security model implementation in an organization and the tasks to be performed every month. Deliver an outstanding presentation on the topic using this Timeline For The Implementation Of Information Technology Security. Dispense information and present a thorough explanation of Implementation, Information, Technology using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
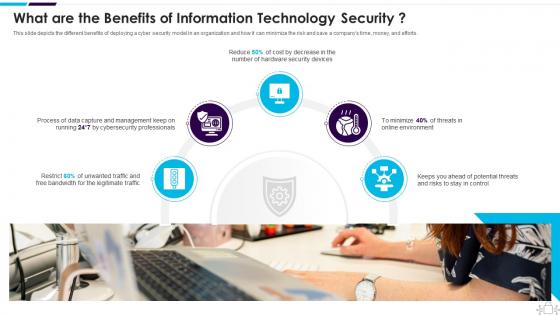 What Are The Benefits Of Information Technology Security
What Are The Benefits Of Information Technology SecurityThis slide depicts the different benefits of deploying a cyber security model in an organization and how it can minimize the risk and save a companys time, money, and efforts. Introducing What Are The Benefits Of Information Technology Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on What Are The Benefits Of Information Technology Security, using this template. Grab it now to reap its full benefits.
-
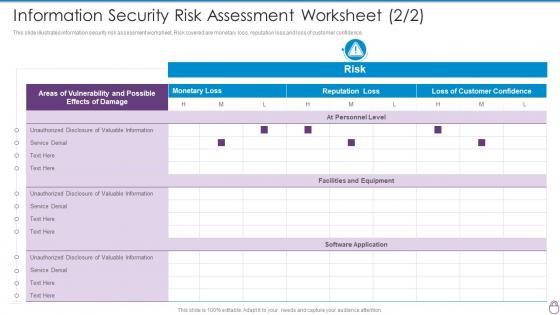 F28 Cybersecurity Risk Management Framework Information Security Risk Assessment
F28 Cybersecurity Risk Management Framework Information Security Risk AssessmentThis slide illustrates information security risk assessment worksheet. Risk covered are monetary loss, reputation loss and loss of customer confidence. Present the topic in a bit more detail with this F28 Cybersecurity Risk Management Framework Information Security Risk Assessment. Use it as a tool for discussion and navigation on Valuable Information, Facilities And Equipment, Software Application, At Personnel Level. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
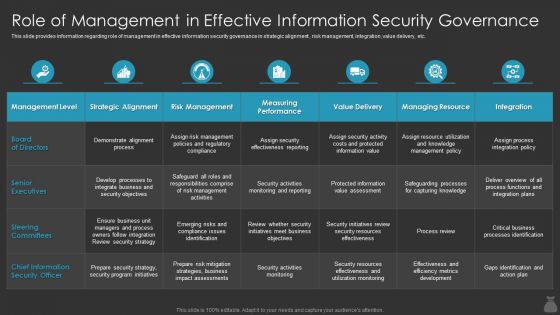 F472 Role Of Management In Effective Information Security It Cost Optimization Priorities By Cios
F472 Role Of Management In Effective Information Security It Cost Optimization Priorities By CiosThis slide provides information regarding role of management in effective information security governance in strategic alignment , risk management, integration, value delivery, etc. Deliver an outstanding presentation on the topic using this F472 Role Of Management In Effective Information Security It Cost Optimization Priorities By Cioss. Dispense information and present a thorough explanation of Information, Security, Governance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Collateral Loan Personal Secured Ppt Powerpoint Presentation Slides Information Cpb
Collateral Loan Personal Secured Ppt Powerpoint Presentation Slides Information CpbPresenting Collateral Loan Personal Secured Ppt Powerpoint Presentation Slides Information Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Collateral Loan Personal Secured. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
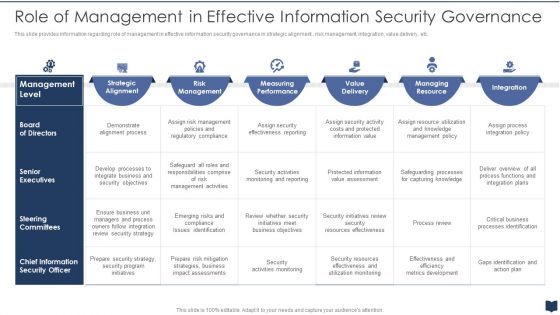 Cios Cost Optimization Playbook Role Of Management Effective Information Security Governance
Cios Cost Optimization Playbook Role Of Management Effective Information Security GovernanceThis slide provides information regarding role of management in effective information security governance in strategic alignment , risk management, integration, value delivery, etc. Deliver an outstanding presentation on the topic using this Cios Cost Optimization Playbook Role Of Management Effective Information Security Governance. Dispense information and present a thorough explanation of Information, Security, Governance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
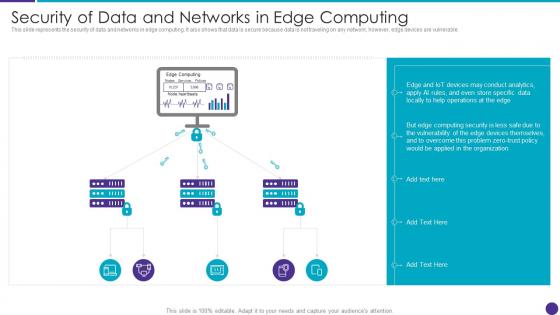 Security Of Data And Networks In Edge Computing Distributed Information Technology
Security Of Data And Networks In Edge Computing Distributed Information TechnologyThis slide represents the security of data and networks in edge computing. It also shows that data is secure because data is not traveling on any network however, edge devices are vulnerable. Deliver an outstanding presentation on the topic using this Security Of Data And Networks In Edge Computing Distributed Information Technology. Dispense information and present a thorough explanation of Security Of Data And Networks In Edge Computing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Difference Computer Security Information Security Ppt Powerpoint Presentation Deck Cpb
Difference Computer Security Information Security Ppt Powerpoint Presentation Deck CpbPresenting Difference Computer Security Information Security Ppt Powerpoint Presentation Deck Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Difference Computer Security Information Security. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Siem For Security Analysis Information And Event Management Logging Process
Siem For Security Analysis Information And Event Management Logging ProcessThis slide covers the process of SIEM which cover 4 steps of logging process such as data collection, normalization and aggregation, data discover, and alerts investigation Introducing Siem For Security Analysis Information And Event Management Logging Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Information, Management, Process, using this template. Grab it now to reap its full benefits.
-
 Siem For Security Analysis Security Information And Event Management Services
Siem For Security Analysis Security Information And Event Management ServicesThis slide covers the SIEM services offered by our company such as data aggregation, correlation, security alerts, dashboards, retention, forensic analysis, IT compliance, threat detection, etc. Increase audience engagement and knowledge by dispensing information using Siem For Security Analysis Security Information And Event Management Services. This template helps you present information on eight stages. You can also present information on Data Aggregation, Data Correlation, Security Alert using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Access Control Methods Information Security Ppt Powerpoint Presentation Pictures Visual Aids Cpb
Access Control Methods Information Security Ppt Powerpoint Presentation Pictures Visual Aids CpbPresenting our Access Control Methods Information Security Ppt Powerpoint Presentation Pictures Visual Aids Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Access Control Methods Information Security. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Employees Build Sense Security Ppt Powerpoint Presentation Infographic Template Information Cpb
Employees Build Sense Security Ppt Powerpoint Presentation Infographic Template Information CpbPresenting Employees Build Sense Security Ppt Powerpoint Presentation Infographic Template Information Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Employees Build Sense Security This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
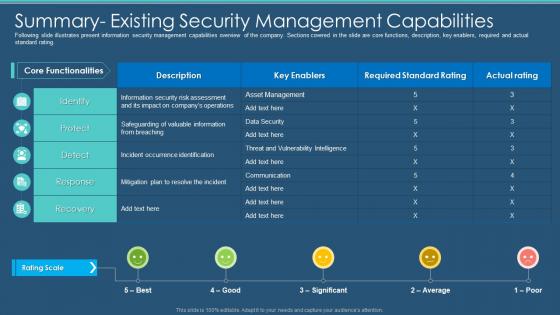 Information Program Cybersecurity Summary Existing Security Management Capabilities
Information Program Cybersecurity Summary Existing Security Management CapabilitiesFollowing slide illustrates present information security management capabilities overview of the company. Sections covered in the slide are core functions, description, key enablers, required and actual standard rating. Present the topic in a bit more detail with this Information Program Cybersecurity Summary Existing Security Management Capabilities. Use it as a tool for discussion and navigation on Management, Capabilities, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
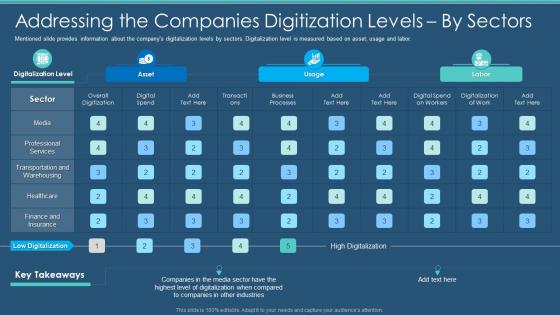 Information Security Program Addressing The Companies Digitization Levels By Sectors
Information Security Program Addressing The Companies Digitization Levels By SectorsMentioned slide provides information about the companys digitalization levels by sectors. Digitalization level is measured based on asset, usage and labor. Deliver an outstanding presentation on the topic using this Information Security Program Addressing The Companies Digitization Levels By Sectors. Dispense information and present a thorough explanation of Companies, Digitization, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
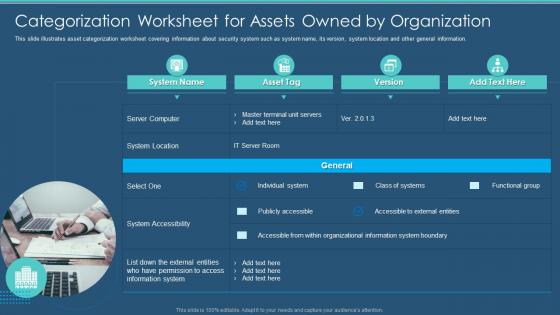 Information Security Program Categorization Worksheet For Assets Owned Organization
Information Security Program Categorization Worksheet For Assets Owned OrganizationThis slide illustrates asset categorization worksheet covering information about security system such as system name, its version, system location and other general information. Present the topic in a bit more detail with this Information Security Program Categorization Worksheet For Assets Owned Organization. Use it as a tool for discussion and navigation on Categorization, Worksheet, Organization. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
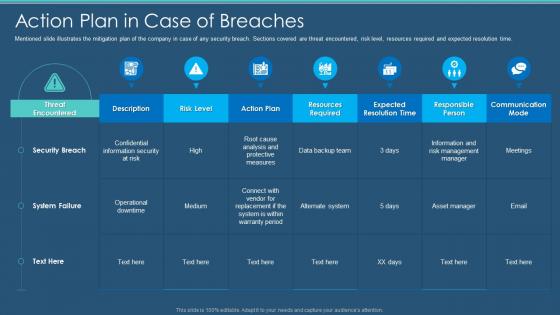 Information Security Program Cybersecurity Action Plan In Case Of Breaches
Information Security Program Cybersecurity Action Plan In Case Of BreachesMentioned slide illustrates the mitigation plan of the company in case of any security breach. Sections covered are threat encountered, risk level, resources required and expected resolution time. Deliver an outstanding presentation on the topic using this Information Security Program Cybersecurity Action Plan In Case Of Breaches. Dispense information and present a thorough explanation of Action Plan In Case Of Breaches using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Security Program Cybersecurity Checklist Effectively Managing Asset Security
Information Security Program Cybersecurity Checklist Effectively Managing Asset SecurityFollowing slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them. Present the topic in a bit more detail with this Information Security Program Cybersecurity Checklist Effectively Managing Asset Security. Use it as a tool for discussion and navigation on Checklist For Effectively Managing Asset Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
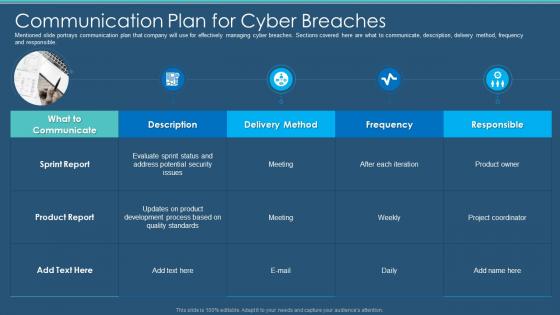 Information Security Program Cybersecurity Communication Plan For Cyber Breaches
Information Security Program Cybersecurity Communication Plan For Cyber BreachesMentioned slide portrays communication plan that company will use for effectively managing cyber breaches. Sections covered here are what to communicate, description, delivery method, frequency and responsible. Deliver an outstanding presentation on the topic using this Information Security Program Cybersecurity Communication Plan For Cyber Breaches. Dispense information and present a thorough explanation of Communication Plan For Cyber Breaches using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
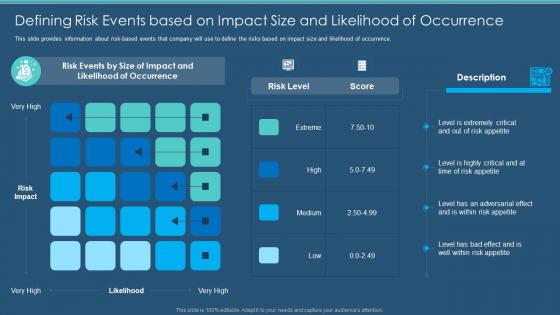 Information Security Program Cybersecurity Defining Risk Events Based On Impact Size
Information Security Program Cybersecurity Defining Risk Events Based On Impact SizeThis slide provides information about risk based events that company will use to define the risks based on impact size and likelihood of occurrence. Deliver an outstanding presentation on the topic using this Information Security Program Cybersecurity Defining Risk Events Based On Impact Size. Dispense information and present a thorough explanation of Occurrence, Likelihood, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
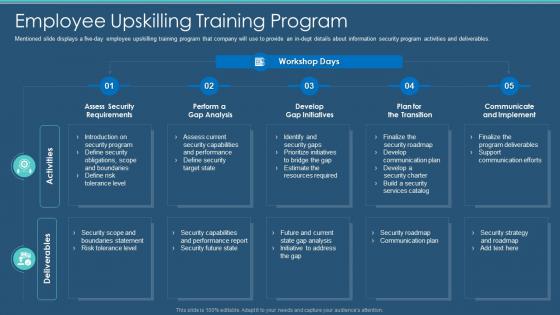 Information Security Program Cybersecurity Employee Upskilling Training Program
Information Security Program Cybersecurity Employee Upskilling Training ProgramMentioned slide displays a five day employee upskilling training program that company will use to provide an in-dept details about information security program activities and deliverables. Present the topic in a bit more detail with this Information Security Program Cybersecurity Employee Upskilling Training Program. Use it as a tool for discussion and navigation on Introduction, Obligations, Capabilities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
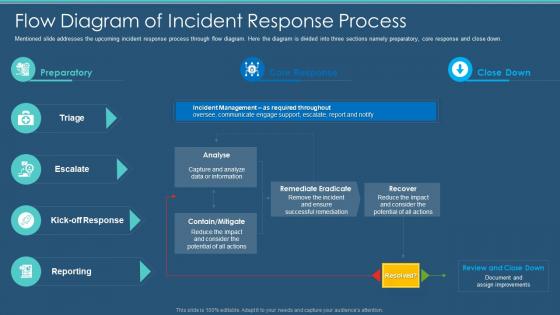 Information Security Program Cybersecurity Flow Diagram Of Incident Response Process
Information Security Program Cybersecurity Flow Diagram Of Incident Response ProcessMentioned slide addresses the upcoming incident response process through flow diagram. Here the diagram is divided into three sections namely preparatory, core response and close down. Deliver an outstanding presentation on the topic using this Information Security Program Cybersecurity Flow Diagram Of Incident Response Process. Dispense information and present a thorough explanation of Flow Diagram Of Incident Response Process using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Security Program Cybersecurity Information Security Program Values To Business
Information Security Program Cybersecurity Information Security Program Values To BusinessFollowing slide displays the major program values to companys business. Values here are divided in two areas namely detection and response and attack surface management. Deliver an outstanding presentation on the topic using this Information Security Program Cybersecurity Information Security Program Values To Business. Dispense information and present a thorough explanation of Information, Business, Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
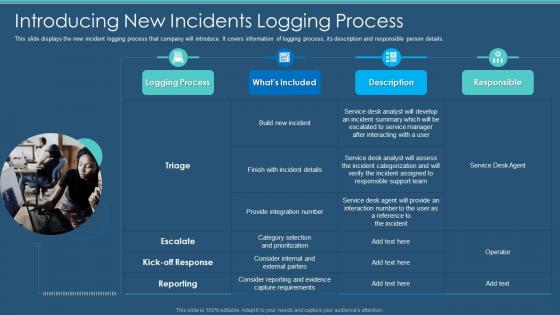 Information Security Program Cybersecurity Introducing New Incidents Logging Process
Information Security Program Cybersecurity Introducing New Incidents Logging ProcessThis slide displays the new incident logging process that company will introduce. It covers information of logging process, its description and responsible person details. Present the topic in a bit more detail with this Information Security Program Cybersecurity Introducing New Incidents Logging Process. Use it as a tool for discussion and navigation on Introducing New Incidents Logging Process. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
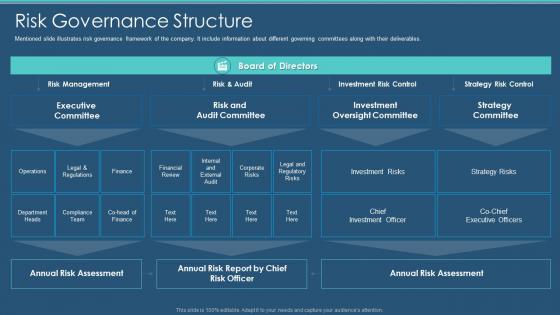 Information Security Program Cybersecurity Management Risk Governance Structure
Information Security Program Cybersecurity Management Risk Governance StructureMentioned slide illustrates risk governance framework of the company. It include information about different governing committees along with their deliverables. Present the topic in a bit more detail with this Information Security Program Cybersecurity Management Risk Governance Structure. Use it as a tool for discussion and navigation on Risk Governance Structure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Security Program Cybersecurity Management Security Lifecycle
Information Security Program Cybersecurity Management Security LifecycleIncrease audience engagement and knowledge by dispensing information using Information Security Program Cybersecurity Management Security Lifecycle. This template helps you present information on six stages. You can also present information on Categorize, Implement, Authorize using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Information Security Program Cybersecurity Management Threat Vulnerability Asset Matrix
Information Security Program Cybersecurity Management Threat Vulnerability Asset MatrixMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least. Deliver an outstanding presentation on the topic using this Information Security Program Cybersecurity Management Threat Vulnerability Asset Matrix. Dispense information and present a thorough explanation of Threat Vulnerability Asset Matrix using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
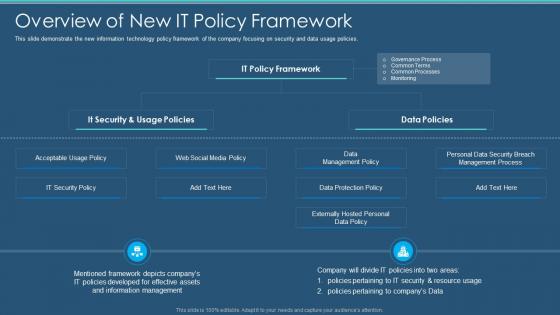 Information Security Program Cybersecurity Overview Of New It Policy Framework
Information Security Program Cybersecurity Overview Of New It Policy FrameworkThis slide demonstrate the new information technology policy framework of the company focusing on security and data usage policies. Present the topic in a bit more detail with this Information Security Program Cybersecurity Overview Of New It Policy Framework. Use it as a tool for discussion and navigation on Information, Management, Framework. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
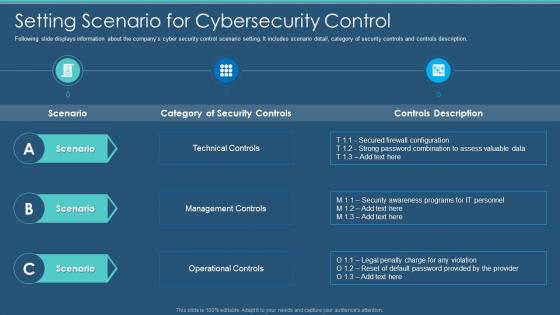 Information Security Program Cybersecurity Setting Scenario For Cybersecurity Control
Information Security Program Cybersecurity Setting Scenario For Cybersecurity ControlFollowing slide displays information about the companys cyber security control scenario setting. It includes scenario detail, category of security controls and controls description. Deliver an outstanding presentation on the topic using this Information Security Program Cybersecurity Setting Scenario For Cybersecurity Control. Dispense information and present a thorough explanation of Technical Controls, Management Controls, Operational Controls using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Security Program Defining Business Priorities To Ensure Information Security
Information Security Program Defining Business Priorities To Ensure Information SecurityThis slide illustrates the key business priorities of the organization such as efficient risk management, standardized incident management process to ensure information security. Increase audience engagement and knowledge by dispensing information using Information Security Program Defining Business Priorities To Ensure Information Security. This template helps you present information on three stages. You can also present information on Efficient Risk Management, Transparent Communication, Management Process using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
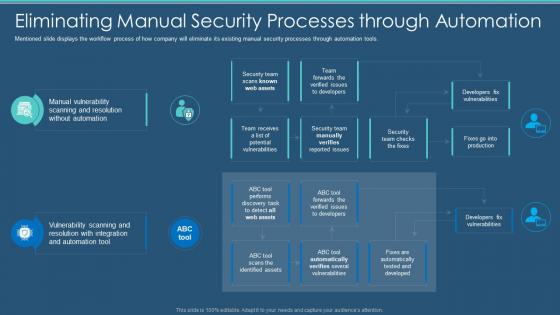 Information Security Program Eliminating Manual Security Processes Through Automation
Information Security Program Eliminating Manual Security Processes Through AutomationMentioned slide displays the workflow process of how company will eliminate its existing manual security processes through automation tools. Deliver an outstanding presentation on the topic using this Information Security Program Eliminating Manual Security Processes Through Automation. Dispense information and present a thorough explanation of Processes, Automation, Vulnerabilities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
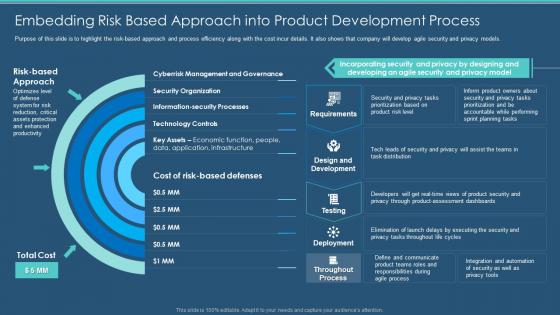 Information Security Program Embedding Risk Based Approach Product Development Process
Information Security Program Embedding Risk Based Approach Product Development ProcessPurpose of this slide is to highlight the risk based approach and process efficiency along with the cost incur details. It also shows that company will develop agile security and privacy models. Present the topic in a bit more detail with this Information Security Program Embedding Risk Based Approach Product Development Process. Use it as a tool for discussion and navigation on Product, Development, Process. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
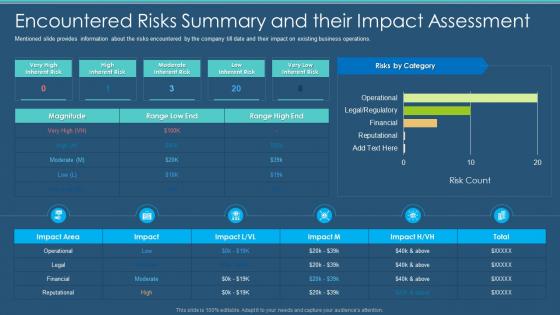 Information Security Program Encountered Risks Summary And Their Impact Assessment
Information Security Program Encountered Risks Summary And Their Impact AssessmentMentioned slide provides information about the risks encountered by the company till date and their impact on existing business operations. Deliver an outstanding presentation on the topic using this Information Security Program Encountered Risks Summary And Their Impact Assessment. Dispense information and present a thorough explanation of Assessment, Encountered, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
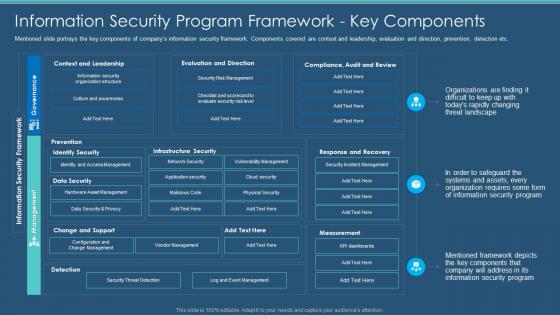 Information Security Program Framework Key Components information Security Program
Information Security Program Framework Key Components information Security ProgramMentioned slide portrays the key components of companys information security framework. Components covered are context and leadership, evaluation and direction, prevention, detection etc. Deliver an outstanding presentation on the topic using this Information Security Program Framework Key Components information Security Program. Dispense information and present a thorough explanation of Information, Framework, Components using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
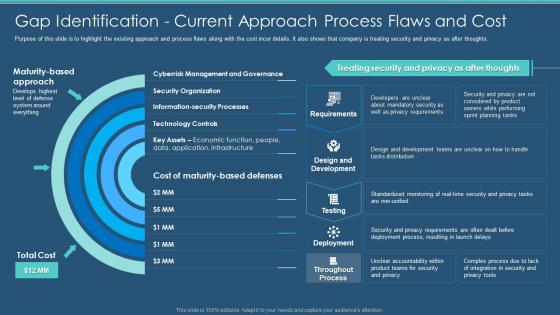 Information Security Program Gap Identification Current Approach Process Flaws And Cost
Information Security Program Gap Identification Current Approach Process Flaws And CostPurpose of this slide is to highlight the existing approach and process flaws along with the cost incur details. It also shows that company is treating security and privacy as after thoughts. Present the topic in a bit more detail with this Information Security Program Gap Identification Current Approach Process Flaws And Cost. Use it as a tool for discussion and navigation on Identification, Current Approach, Process. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Security Program Key Security Controls To Be Addressed In The Program
Information Security Program Key Security Controls To Be Addressed In The ProgramPurpose of this slide is to provide information about key security controls that are to be addressed in companys information security program. Security controls covered are user application hardening, daily backups and patch applications. Deliver an outstanding presentation on the topic using this Information Security Program Key Security Controls To Be Addressed In The Program. Dispense information and present a thorough explanation of Prevents Attacks, Limits Extent Of Attacks, Data Recovery using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
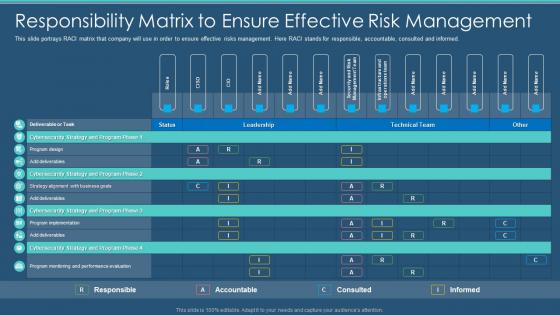 Information Security Program Responsibility Matrix To Ensure Effective Risk Management
Information Security Program Responsibility Matrix To Ensure Effective Risk ManagementThis slide portrays RACI matrix that company will use in order to ensure effective risks management. Here RACI stands for responsible, accountable, consulted and informed. Present the topic in a bit more detail with this Information Security Program Responsibility Matrix To Ensure Effective Risk Management. Use it as a tool for discussion and navigation on Responsibility, Management, Accountable. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Security Program Scorecard To Check Cybersecurity And Digital Risk Preparedness
Information Security Program Scorecard To Check Cybersecurity And Digital Risk PreparednessFollowing slide illustrates a scorecard that company will use to check its preparedness against various cyber security and digital risk events. Sections covered here are fraud prevention considerations, score and notes. Present the topic in a bit more detail with this Information Security Program Scorecard To Check Cybersecurity And Digital Risk Preparedness. Use it as a tool for discussion and navigation on Preparedness, Cybersecurity, Scorecard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
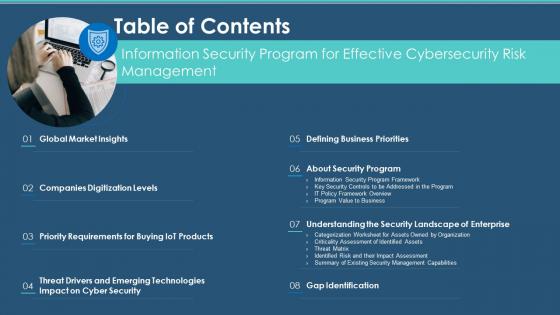 Table Of Contents Information Security Program For Effective Cybersecurity Risk Management
Table Of Contents Information Security Program For Effective Cybersecurity Risk ManagementIncrease audience engagement and knowledge by dispensing information using Table Of Contents Information Security Program For Effective Cybersecurity Risk Management. This template helps you present information on eight stages. You can also present information on Requirements, Technologies, Gap Identification using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
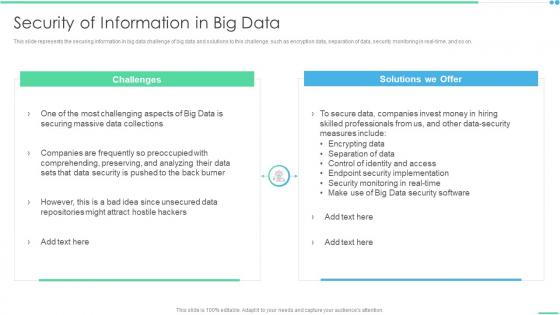 Security Of Information In Big Data Ppt Layouts Layouts
Security Of Information In Big Data Ppt Layouts LayoutsThis slide represents the securing information in big data challenge of big data and solutions to this challenge, such as encryption data, separation of data, security monitoring in real-time, and so on. Increase audience engagement and knowledge by dispensing information using Security Of Information In Big Data Ppt Layouts Layouts. This template helps you present information on two stages. You can also present information on Challenges, Solutions We Offer using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Security Of Information In Big Data Ppt Sample
Security Of Information In Big Data Ppt SampleThis slide represents the securing information in big data challenge of big data and solutions to this challenge, such as encryption data, separation of data, security monitoring in real time, and so on.Increase audience engagement and knowledge by dispensing information using Security Of Information In Big Data Ppt Sample This template helps you present information on one stage. You can also present information on Securing Massive, Data Collections, Comprehending, Preserving using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Agenda For Risk Management Framework For Information Security
Agenda For Risk Management Framework For Information SecurityIntroducing Agenda For Risk Management Framework For Information Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Threats And Vulnerabilities, Organizational Risks, Information Security, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Risk Management Framework For Information Security
Icons Slide For Risk Management Framework For Information SecurityPresenting our well crafted Icons Slide For Risk Management Framework For Information Security set of slides. The slides include icons that are innovatively designed by our team of experts. The icons are easy to edit so you can conveniently increase or decrease their size without any loss in resolution. Therefore, grab them instantly.
-
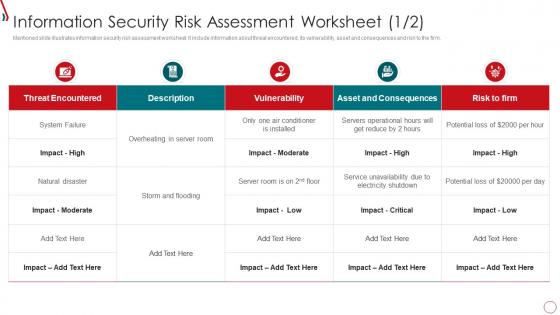 Information Security Risk Assessment Worksheet Risk Management Framework For
Information Security Risk Assessment Worksheet Risk Management Framework ForMentioned slide illustrates information security risk assessment worksheet. It include information about threat encountered, its vulnerability, asset and consequences and risk to the firm. Present the topic in a bit more detail with this Information Security Risk Assessment Worksheet Risk Management Framework For. Use it as a tool for discussion and navigation on Threat Encountered, Vulnerability, Asset And Consequences, Risk To Firm. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
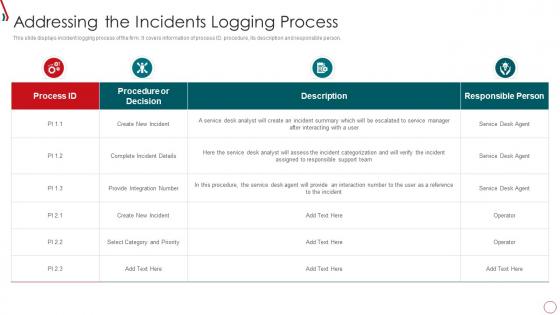 Risk Management Framework For Information Security Addressing The Incidents Logging
Risk Management Framework For Information Security Addressing The Incidents LoggingThis slide displays incident logging process of the firm. It covers information of process ID, procedure, its description and responsible person. Deliver an outstanding presentation on the topic using this Risk Management Framework For Information Security Addressing The Incidents Logging. Dispense information and present a thorough explanation of Create New Incident, Complete Incident Details, Provide Integration Number using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
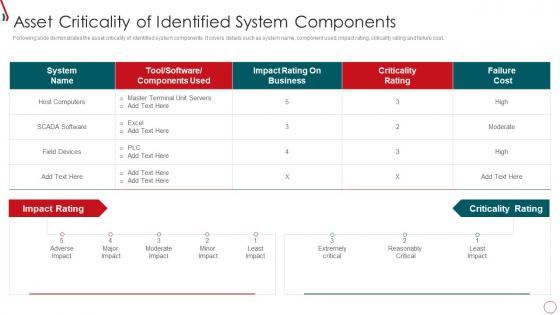 Risk Management Framework For Information Security Asset Criticality Of Identified System
Risk Management Framework For Information Security Asset Criticality Of Identified SystemFollowing slide demonstrates the asset criticality of identified system components. It covers details such as system name, component used, impact rating, criticality rating and failure cost. Present the topic in a bit more detail with this Risk Management Framework For Information Security Asset Criticality Of Identified System. Use it as a tool for discussion and navigation on Host Computers, Impact Rating, Criticality Rating, Failure Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risk Management Framework For Information Security Budget For Information Security
Risk Management Framework For Information Security Budget For Information SecurityMentioned slide shows budget for managing information security. It includes information such as functional area, software name, training duration, training cost, number of employees and total training cost. Deliver an outstanding presentation on the topic using this Risk Management Framework For Information Security Budget For Information Security. Dispense information and present a thorough explanation of Risk Management, Incident Management, Asset Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
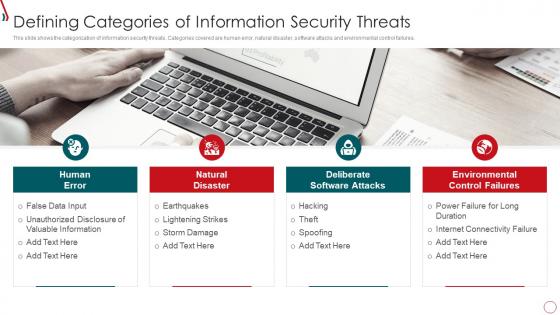 Risk Management Framework For Information Security Defining Categories Of Information
Risk Management Framework For Information Security Defining Categories Of InformationThis slide shows the categorization of information security threats. Categories covered are human error, natural disaster, software attacks and environmental control failures. Increase audience engagement and knowledge by dispensing information using Risk Management Framework For Information Security Defining Categories Of Information. This template helps you present information on four stages. You can also present information on Human Error, Natural Disaster, Deliberate Software Attacks, Environmental Control Failures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
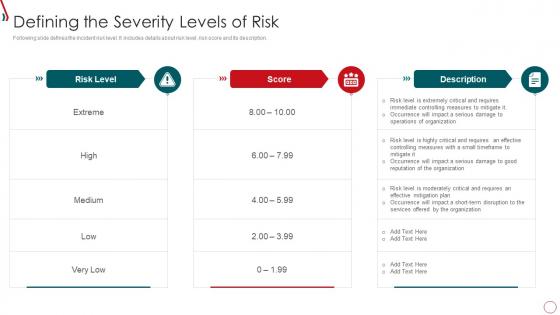 Risk Management Framework For Information Security Defining The Severity Levels Of Risk
Risk Management Framework For Information Security Defining The Severity Levels Of RiskFollowing slide defines the incident risk level. It includes details about risk level, risk score and its description. Introducing Risk Management Framework For Information Security Defining The Severity Levels Of Risk to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Extreme, High, Medium, Low, using this template. Grab it now to reap its full benefits.
-
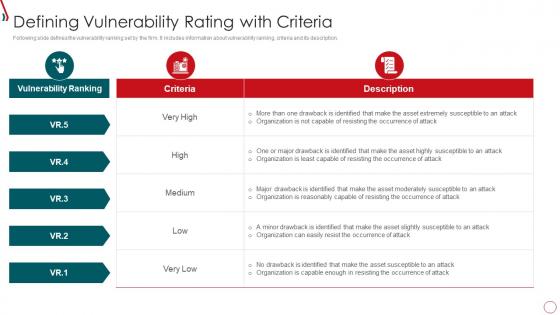 Risk Management Framework For Information Security Defining Vulnerability Rating With Criteria
Risk Management Framework For Information Security Defining Vulnerability Rating With CriteriaFollowing slide defines the vulnerability ranking set by the firm. It includes information about vulnerability ranking, criteria and its description. Present the topic in a bit more detail with this Risk Management Framework For Information Security Defining Vulnerability Rating With Criteria. Use it as a tool for discussion and navigation on Vulnerability Ranking, Organization, High, Low, Medium. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
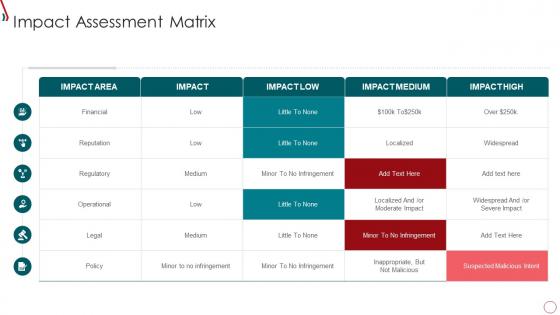 Risk Management Framework For Information Security Impact Assessment Matrix
Risk Management Framework For Information Security Impact Assessment MatrixPresent the topic in a bit more detail with this Risk Management Framework For Information Security Impact Assessment Matrix. Use it as a tool for discussion and navigation on Financial, Operational, Suspected Malicious Intent. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
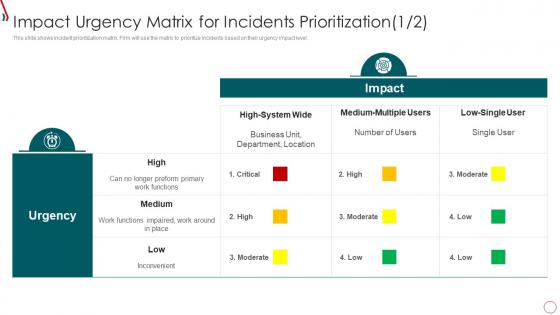 Risk Management Framework For Information Security Impact Urgency Matrix For Incidents
Risk Management Framework For Information Security Impact Urgency Matrix For IncidentsThis slide shows incident prioritization matrix. Firm will use the matrix to prioritize incidents based on their urgency impact level. Present the topic in a bit more detail with this Risk Management Framework For Information Security Impact Urgency Matrix For Incidents. Use it as a tool for discussion and navigation on Business Unit, Department, Location, High, Medium, Low. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
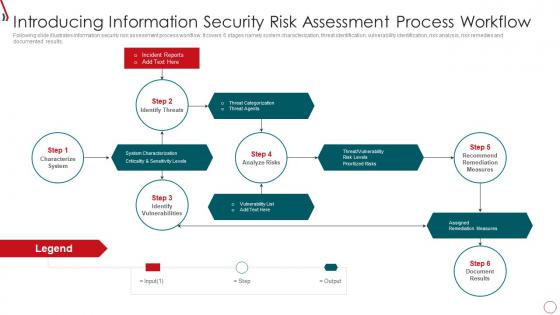 Risk Management Framework For Information Security Introducing Information Security Risk
Risk Management Framework For Information Security Introducing Information Security RiskFollowing slide illustrates information security risk assessment process workflow. It covers 6 stages namely system characterization, threat identification, vulnerability identification, risk analysis, risk remedies and documented results. Increase audience engagement and knowledge by dispensing information using Risk Management Framework For Information Security Introducing Information Security Risk. This template helps you present information on six stages. You can also present information on Identify Threats, Incident Reports, Identify Vulnerabilities, Characterize System, Recommend Remediation Measures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
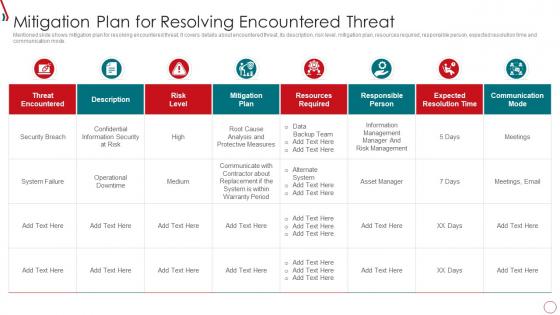 Risk Management Framework For Information Security Mitigation Plan For Resolving Encountered
Risk Management Framework For Information Security Mitigation Plan For Resolving EncounteredMentioned slide shows mitigation plan for resolving encountered threat. It covers details about encountered threat, its description, risk level, mitigation plan, resources required, responsible person, expected resolution time and communication mode. Present the topic in a bit more detail with this Risk Management Framework For Information Security Mitigation Plan For Resolving Encountered. Use it as a tool for discussion and navigation on Threat Encountered, Risk Level, Mitigation Plan, Resources Required. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
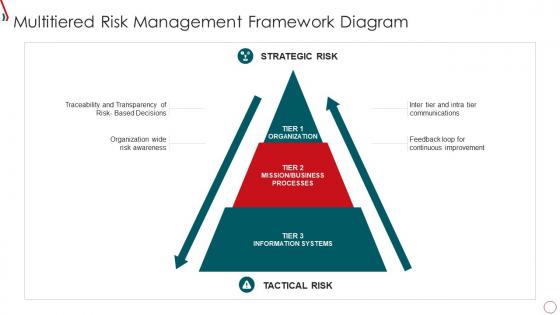 Risk Management Framework For Information Security Multitiered Risk Management Framework
Risk Management Framework For Information Security Multitiered Risk Management FrameworkIncrease audience engagement and knowledge by dispensing information using Risk Management Framework For Information Security Multitiered Risk Management Framework. This template helps you present information on three stages. You can also present information on Strategic Risk, Tactical Risk, Organization, Communications using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Risk Management Framework For Information Security Online And Onsite Training Schedule
Risk Management Framework For Information Security Online And Onsite Training ScheduleThis slide illustrates employee training schedule. It covers details about employee name, its position, software name, course type, training mode and duration. Present the topic in a bit more detail with this Risk Management Framework For Information Security Online And Onsite Training Schedule. Use it as a tool for discussion and navigation on Employee, Training Mode, Intermediate, Online And Onsite. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
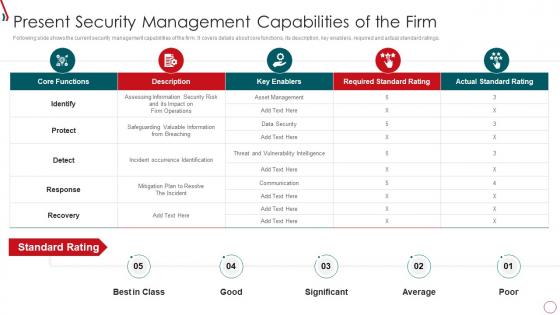 Risk Management Framework For Information Security Present Security Management Capabilities
Risk Management Framework For Information Security Present Security Management CapabilitiesFollowing slide shows the current security management capabilities of the firm. It covers details about core functions, its description, key enablers, required and actual standard ratings. Deliver an outstanding presentation on the topic using this Risk Management Framework For Information Security Present Security Management Capabilities. Dispense information and present a thorough explanation of Core Functions, Incident Occurrence Identification, Asset Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.



