Powerpoint Templates and Google slides for Information Security Plan
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
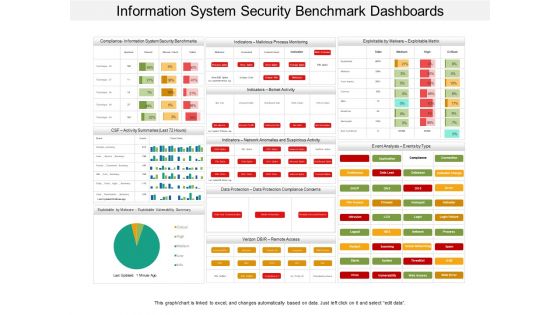 Information system security benchmark dashboards
Information system security benchmark dashboardsPresenting this set of slides with name - Information System Security Benchmark Dashboards. This is a three stage process. The stages in this process are Information Security Strategy, Information Security Plan, Information Protection Strategy.
-
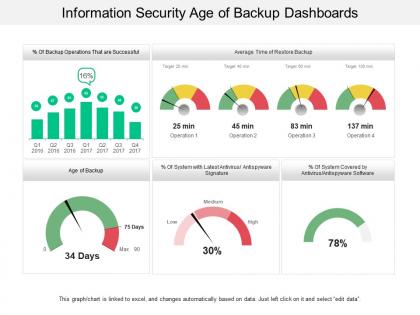 Information security age of backup dashboards
Information security age of backup dashboardsPresenting this set of slides with name - Information Security Age Of Backup Dashboards. This is a five stage process. The stages in this process are Information Security Strategy, Information Security Plan, Information Protection Strategy.
-
 Controls information security ppt powerpoint presentation file design ideas cpb
Controls information security ppt powerpoint presentation file design ideas cpbPresenting this set of slides with name - Controls Information Security Ppt Powerpoint Presentation File Design Ideas Cpb. This is an editable three stages graphic that deals with topics like Controls Information Security to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Information security management system ppt powerpoint presentation slide cpb
Information security management system ppt powerpoint presentation slide cpbPresenting this set of slides with name Information Security Management System Ppt Powerpoint Presentation Slide Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Information Security Management System to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
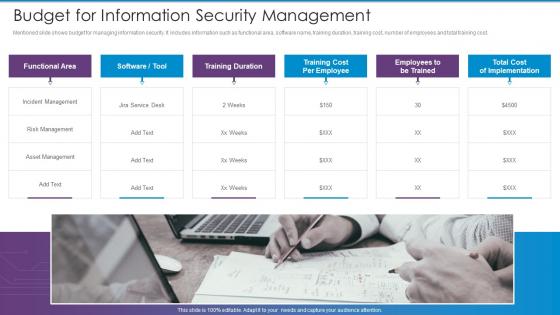 Cybersecurity Risk Management Framework Budget For Information Security Management
Cybersecurity Risk Management Framework Budget For Information Security ManagementMentioned slide shows budget for managing information security. It includes information such as functional area, software name, training duration, training cost, number of employees and total training cost. Introducing Cybersecurity Risk Management Framework Budget For Information Security Management to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Functional Area, Training Duration, Training Cost Per Employee, Employees To Be Trained, Total Cost Of Implementation, using this template. Grab it now to reap its full benefits.
-
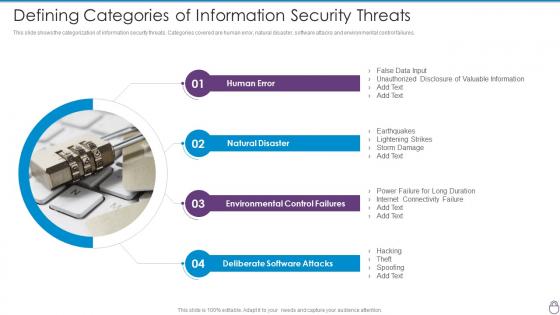 Cybersecurity Risk Management Framework Defining Categories Of Information Security
Cybersecurity Risk Management Framework Defining Categories Of Information SecurityThis slide shows the categorization of information security threats. Categories covered are human error, natural disaster, software attacks and environmental control failures. Introducing Cybersecurity Risk Management Framework Defining Categories Of Information Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Human Error, Natural Disaster, Environmental Control Failures, Deliberate Software Attacks, using this template. Grab it now to reap its full benefits.
-
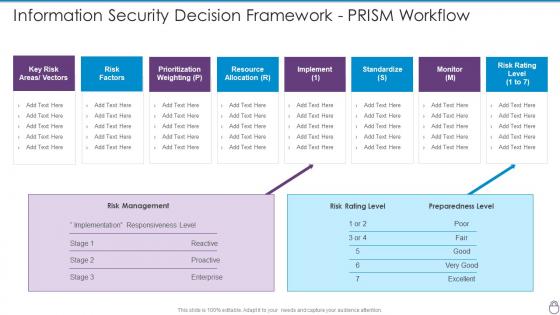 Cybersecurity Risk Management Framework Information Security Decision Framework PRISM
Cybersecurity Risk Management Framework Information Security Decision Framework PRISMPresent the topic in a bit more detail with this Cybersecurity Risk Management Framework Information Security Decision Framework PRISM. Use it as a tool for discussion and navigation on Risk Management, Risk Rating Level, Preparedness Level, Resource Allocation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
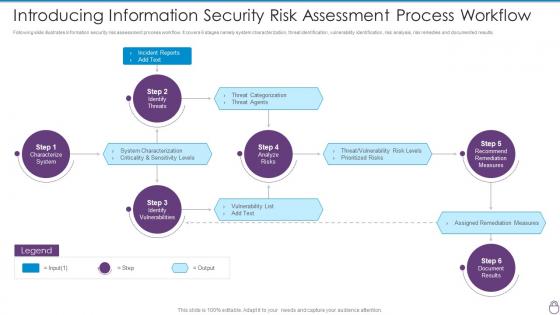 Cybersecurity Risk Management Framework Introducing Information Security Risk Assessment
Cybersecurity Risk Management Framework Introducing Information Security Risk AssessmentFollowing slide illustrates information security risk assessment process workflow. It covers 6 stages namely system characterization, threat identification, vulnerability identification, risk analysis, risk remedies and documented results. Increase audience engagement and knowledge by dispensing information using Cybersecurity Risk Management Framework Introducing Information Security Risk Assessment. This template helps you present information on six stages. You can also present information on Incident Reports, Characterize System, Identify Vulnerabilities, Identify Threats, Analyze Risks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
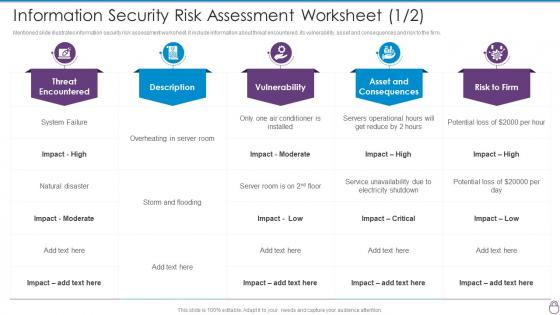 Information Security Risk Assessment Worksheet Cybersecurity Risk Management Framework
Information Security Risk Assessment Worksheet Cybersecurity Risk Management FrameworkMentioned slide illustrates information security risk assessment worksheet. It include information about threat encountered, its vulnerability, asset and consequences and risk to the firm. Present the topic in a bit more detail with this Information Security Risk Assessment Worksheet Cybersecurity Risk Management Framework. Use it as a tool for discussion and navigation on Threat Encountered, Vulnerability, Asset And Consequences, Risk To Firm. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
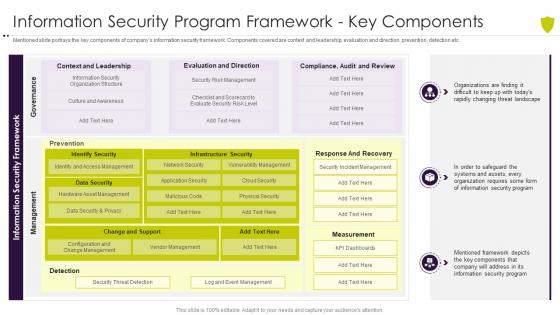 Information security program framework managing cyber risk in a digital age
Information security program framework managing cyber risk in a digital ageMentioned slide portrays the key components of companys information security framework. Components covered are context and leadership, evaluation and direction, prevention, detection etc. Deliver an outstanding presentation on the topic using this Information Security Program Framework Managing Cyber Risk In A Digital Age. Dispense information and present a thorough explanation of Information Security Program Framework Key Components using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
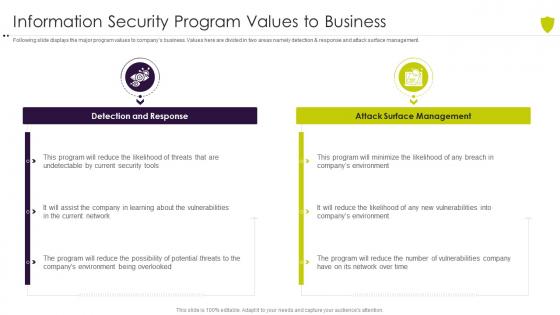 Managing cyber risk in a digital age information security program values to business
Managing cyber risk in a digital age information security program values to businessFollowing slide displays the major program values to companys business. Values here are divided in two areas namely detection and response and attack surface management. Introducing Managing Cyber Risk In A Digital Age Information Security Program Values To Business to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Response, Management, Vulnerabilities, using this template. Grab it now to reap its full benefits.
-
 Cyber threat security icon to capture sensitive information
Cyber threat security icon to capture sensitive informationIntroducing our premium set of slides with Cyber Threat Security Icon To Capture Sensitive Information. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Threat Security Icon To Capture Sensitive Information. So download instantly and tailor it with your information.
-
 Icons Slide Information Security Program For Effective Cybersecurity Risk Management
Icons Slide Information Security Program For Effective Cybersecurity Risk ManagementIntroducing our well researched set of slides titled Icons Slide Information Security Program For Effective Cybersecurity Risk Management. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
 Agenda Of Risk Based Methodology To Cyberand Information Security
Agenda Of Risk Based Methodology To Cyberand Information SecurityPresent the topic in a bit more detail with this Agenda Of Risk Based Methodology To Cyberand Information Security. Use it as a tool for discussion and navigation on Agenda. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
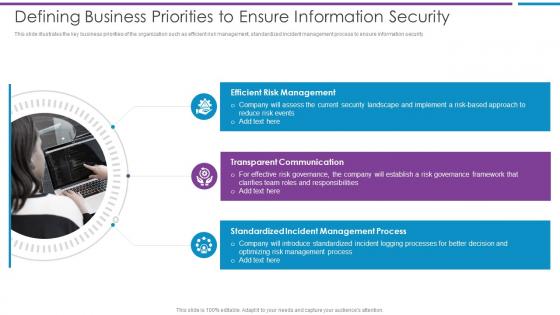 Defining Business Priorities To Ensure Information Security Risk Based Methodology To Cyber
Defining Business Priorities To Ensure Information Security Risk Based Methodology To CyberThis slide illustrates the key business priorities of the organization such as efficient risk management, standardized incident management process to ensure information security.Increase audience engagement and knowledge by dispensing information using Defining Business Priorities To Ensure Information Security Risk Based Methodology To Cyber This template helps you present information on three stages. You can also present information on Efficient Risk Management, Transparent Communication, Standardized Incident using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons Slide For Risk Based Methodology To Cyber and Information Security
Icons Slide For Risk Based Methodology To Cyber and Information SecurityPresenting our well crafted Icons Slide For Risk Based Methodology To Cyber and Information Security set of slides. The slides include icons that are innovatively designed by our team of experts. The icons are easy to edit so you can conveniently increase or decrease their size without any loss in resolution. Therefore, grab them instantly
-
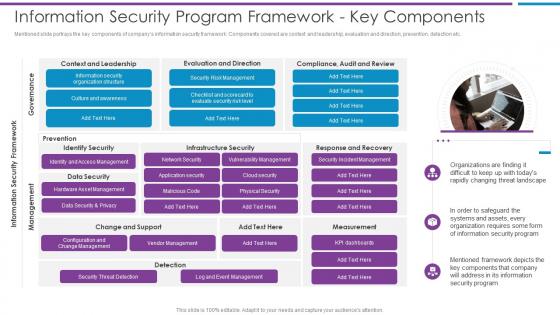 Information Security Program Framework Key Components Risk Based Methodology To Cyber
Information Security Program Framework Key Components Risk Based Methodology To CyberMentioned slide portrays the key components of companys information security framework. Components covered are context and leadership, evaluation and direction, prevention, detection etc.Introducing Information Security Program Framework Key Components Risk Based Methodology To Cyber to increase your presentation threshold. Encompassed with one stage this template is a great option to educate and entice your audience. Dispence information on Culture And Awareness, Security Risk Management, Data Security And Privacy using this template. Grab it now to reap its full benefits.
-
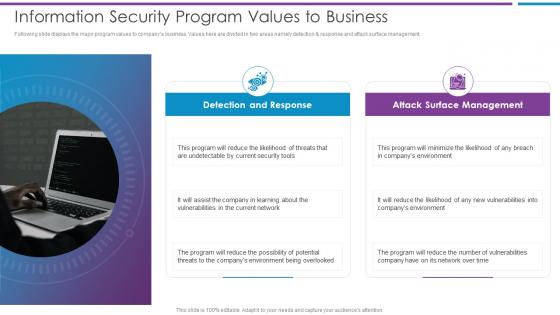 Information Security Program Values To Business Risk Based Methodology To Cyber
Information Security Program Values To Business Risk Based Methodology To CyberFollowing slide displays the major program values to companys business. Values here are divided in two areas namely detection and response and attack surface management.Increase audience engagement and knowledge by dispensing information using Information Security Program Values To Business Risk Based Methodology To Cyber This template helps you present information on two stages. You can also present information on Undetectable By Current, Vulnerabilities In The Current, Threats To The Companys Environment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
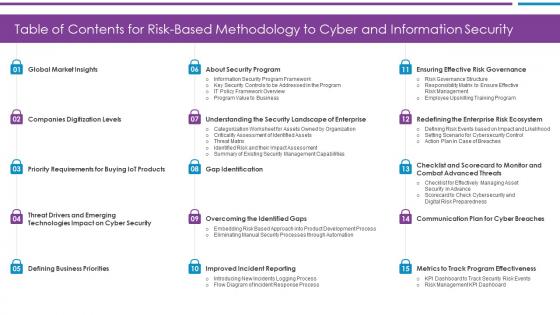 Table Of Contents For Risk Based Methodology To Cyber and Information Security
Table Of Contents For Risk Based Methodology To Cyber and Information SecurityPresent the topic in a bit more detail with this Table Of Contents For Risk Based Methodology To Cyber and Information Security Use it as a tool for discussion and navigation on Defining Business Priorities, Global Market Insights, Companies Digitization Levels This template is free to edit as deemed fit for your organization. Therefore download it now.
-
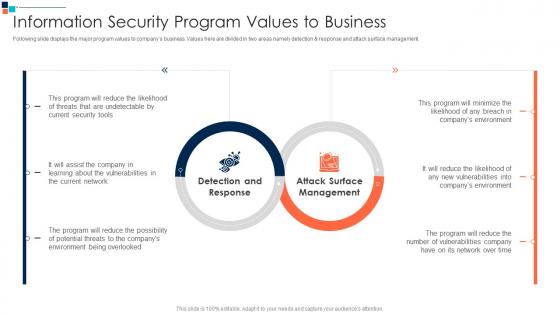 Information Security Program Values To Business Introducing A Risk Based Approach To Cyber
Information Security Program Values To Business Introducing A Risk Based Approach To CyberFollowing slide displays the major program values to companys business. Values here are divided in two areas namely detection AND response and attack surface management.Deliver an outstanding presentation on the topic using this Information Security Program Values To Business Introducing A Risk Based Approach To Cyber Dispense information and present a thorough explanation of Detection And Response, Attack Surface Management, Program Will Reduce using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Agenda For Information Technology Security
Agenda For Information Technology SecurityIntroducing Agenda For Information Technology Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Information, Technology, Cybersecurity, using this template. Grab it now to reap its full benefits.
-
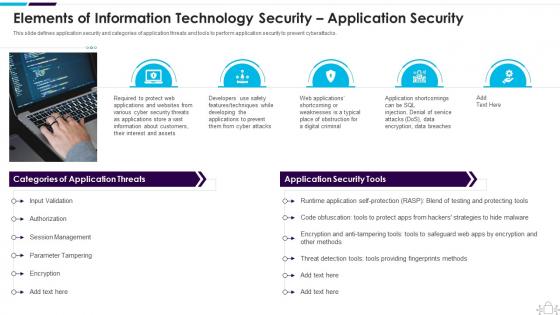 Elements Of Information Technology Security Application Security Information Technology Security
Elements Of Information Technology Security Application Security Information Technology SecurityThis slide defines application security and categories of application threats and tools to perform application security to prevent cyberattacks. Increase audience engagement and knowledge by dispensing information using Elements Of Information Technology Security Application Security Information Technology Security. This template helps you present information on five stages. You can also present information on Session Management, Parameter Tampering, Authorization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons Slide For Information Technology Security
Icons Slide For Information Technology SecurityIntroducing our well researched set of slides titled Icons Slide For Information Technology Security. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
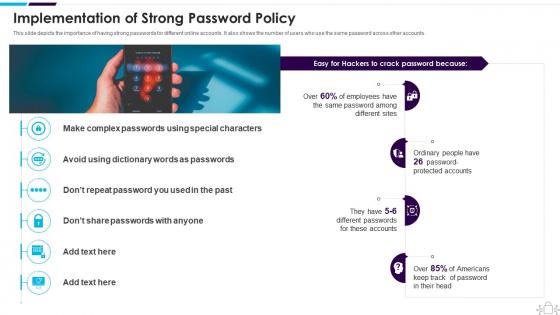 Implementation Of Strong Password Policy Information Technology Security
Implementation Of Strong Password Policy Information Technology SecurityThis slide depicts the importance of having strong passwords for different online accounts. It also shows the number of users who use the same password across other accounts. Introducing Implementation Of Strong Password Policy Information Technology Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Americans, Implementation, Passwords, using this template. Grab it now to reap its full benefits.
-
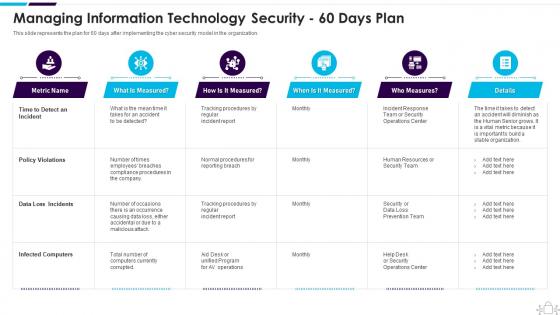 Information Technology Security 60 Days Plan
Information Technology Security 60 Days PlanThis slide represents the plan for 60 days after implementing the cyber security model in the organization. Present the topic in a bit more detail with this Information Technology Security 60 Days Plan. Use it as a tool for discussion and navigation on Managing, Information, Technology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
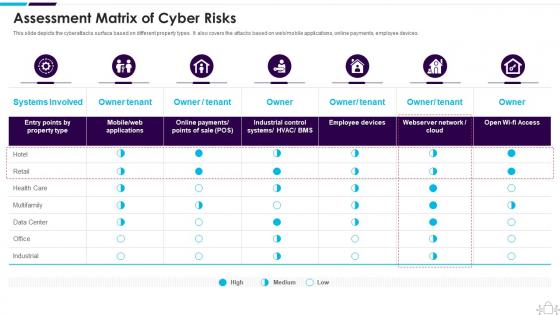 Information Technology Security Assessment Matrix Of Cyber Risks
Information Technology Security Assessment Matrix Of Cyber RisksThis slide depicts the cyberattacks surface based on different property types. It also covers the attacks based on web or mobile applications, online payments, employee devices. Deliver an outstanding presentation on the topic using this Information Technology Security Assessment Matrix Of Cyber Risks. Dispense information and present a thorough explanation of Assessment Matrix Of Cyber Risks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
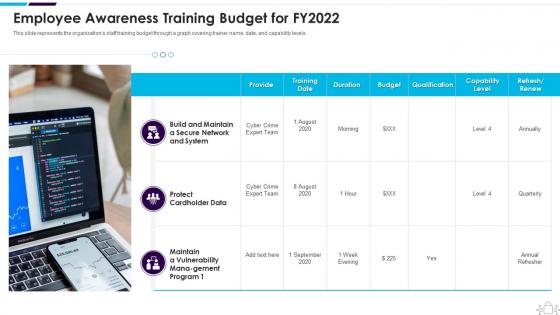 Information Technology Security Awareness Training Budget For Fy2022
Information Technology Security Awareness Training Budget For Fy2022This slide represents the organizations staff training budget through a graph covering trainer name, date, and capability levels. Present the topic in a bit more detail with this Information Technology Security Awareness Training Budget For Fy2022. Use it as a tool for discussion and navigation on Employee Awareness Training Budget For FY2022. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
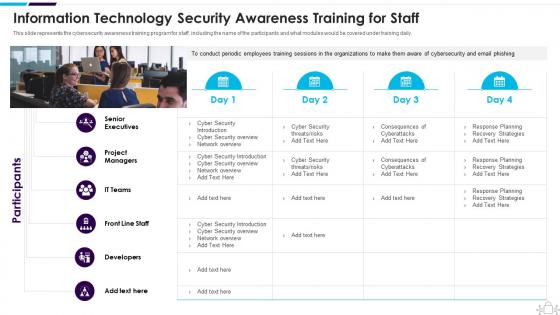 Information Technology Security Awareness Training For Staff
Information Technology Security Awareness Training For StaffThis slide represents the cybersecurity awareness training program for staff, including the name of the participants and what modules would be covered under training daily. Deliver an outstanding presentation on the topic using this Information Technology Security Awareness Training For Staff. Dispense information and present a thorough explanation of Senior Executives, Project Managers, Developers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
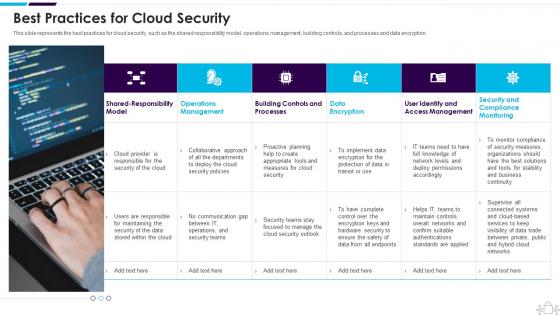 Information Technology Security Best Practices For Cloud Security
Information Technology Security Best Practices For Cloud SecurityThis slide represents the best practices for cloud security, such as the shared responsibility model, operations management, building controls, and processes and data encryption. Present the topic in a bit more detail with this Information Technology Security Best Practices For Cloud Security. Use it as a tool for discussion and navigation on Operations, Management, Processes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
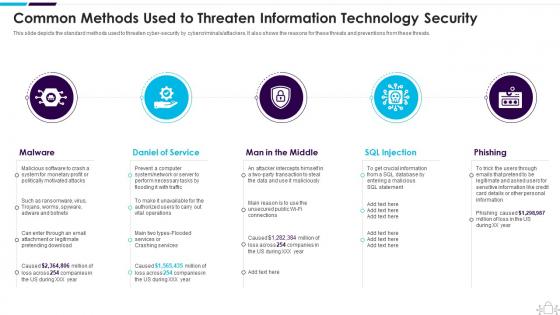 Information Technology Security Common Methods Used Threaten Information Security
Information Technology Security Common Methods Used Threaten Information SecurityThis slide depicts the standard methods used to threaten cyber security by cybercriminals or attackers. It also shows the reasons for these threats and preventions from these threats. Introducing Information Technology Security Common Methods Used Threaten Information Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Daniel Of Service, Man In The Middle, SQL Injection , using this template. Grab it now to reap its full benefits.
-
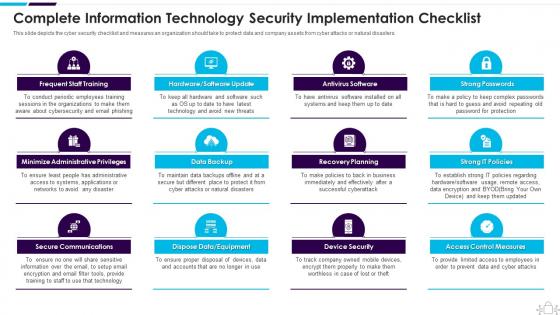 Information Technology Security Complete Information Security Implementation Checklist
Information Technology Security Complete Information Security Implementation ChecklistThis slide depicts the cyber security checklist and measures an organization should take to protect data and company assets from cyber attacks or natural disasters. Introducing Information Technology Security Complete Information Security Implementation Checklist to increase your presentation threshold. Encompassed with twelve stages, this template is a great option to educate and entice your audience. Dispence information on Frequent Staff Training, Administrative Privileges, Data Backup, using this template. Grab it now to reap its full benefits.
-
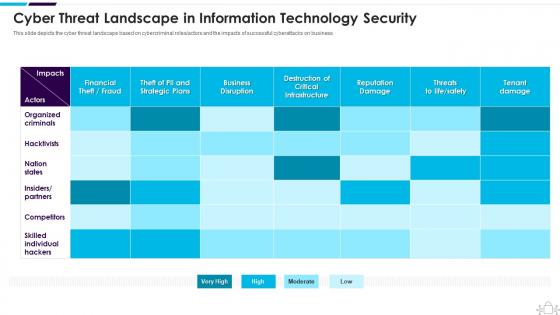 Information Technology Security Cyber Threat Landscape In Information Technology Security
Information Technology Security Cyber Threat Landscape In Information Technology SecurityThis slide depicts the cyber threat landscape based on cybercriminal roles or actors and the impacts of successful cyberattacks on business. Deliver an outstanding presentation on the topic using this Information Technology Security Cyber Threat Landscape In Information Technology Security. Dispense information and present a thorough explanation of Landscape, Information, Technology using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Technology Security Data Backup For Sensitive Information
Information Technology Security Data Backup For Sensitive InformationThis slide represents the preparation of data backup for sensitive information and how data backup should be created and stored within an organization. Introducing Information Technology Security Data Backup For Sensitive Information to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Prepare Data Backup For Sensitive Information, using this template. Grab it now to reap its full benefits.
-
 Information Technology Security Define Access Control Measures For Employees
Information Technology Security Define Access Control Measures For EmployeesThis slide represents how it is essential to minimize the rights or access of employees in an organization to keep data safe and prevent it from deletion, manipulation. Increase audience engagement and knowledge by dispensing information using Information Technology Security Define Access Control Measures For Employees. This template helps you present information on four stages. You can also present information on Organization, Permissions, Responsibilities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Information Technology Security Dispose Data And Equipment Properly
Information Technology Security Dispose Data And Equipment ProperlyThis slide depicts the importance of disposal of the data and equipment that is not in use anymore and restricts the employees who already left the organization. Introducing Information Technology Security Dispose Data And Equipment Properly to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Dispose Data And Equipment Properly, using this template. Grab it now to reap its full benefits.
-
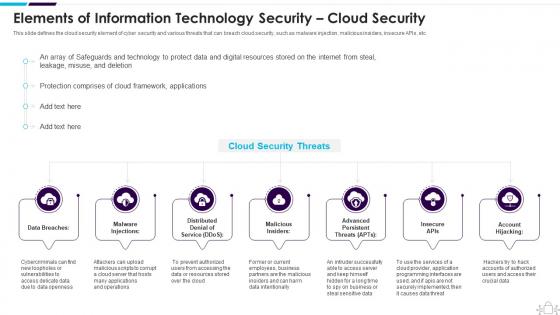 Information Technology Security Elements Information Technology Security Cloud Security
Information Technology Security Elements Information Technology Security Cloud SecurityThis slide defines the cloud security element of cyber security and various threats that can breach cloud security, such as malware injection, malicious insiders, insecure APIs, etc. Introducing Information Technology Security Elements Information Technology Security Cloud Security to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Elements, Information, Technology, using this template. Grab it now to reap its full benefits.
-
 Information Technology Security Employees Devices
Information Technology Security Employees DevicesThis slide depicts that the security of employees hardware or devices is also essential while applying the cyber security model. Increase audience engagement and knowledge by dispensing information using Information Technology Security Employees Devices. This template helps you present information on four stages. You can also present information on Security Of Employees Devices using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
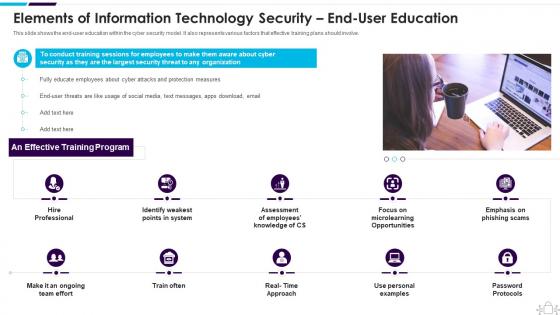 Information Technology Security End User Education Information Technology Security
Information Technology Security End User Education Information Technology SecurityThis slide shows the end user education within the cyber security model. It also represents various factors that effective training plans should involve. Introducing Information Technology Security End User Education Information Technology Security to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Assessment, Microlearning, Opportunities, using this template. Grab it now to reap its full benefits.
-
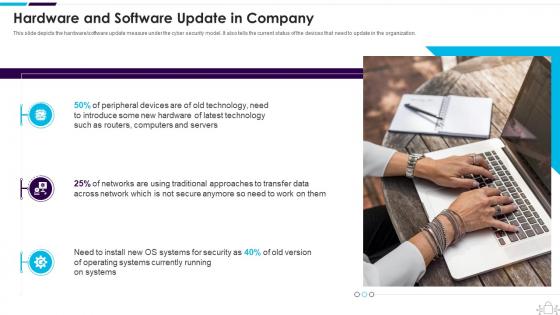 Information Technology Security Hardware And Software Update In Company
Information Technology Security Hardware And Software Update In CompanyThis slide depicts the hardware or software update measure under the cyber security model. It also tells the current status of the devices that need to update in the organization. Increase audience engagement and knowledge by dispensing information using Information Technology Security Hardware And Software Update In Company. This template helps you present information on three stages. You can also present information on Hardware And Software Update In Company using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Information Technology Security How Is Automation Used In Information Technology Security
Information Technology Security How Is Automation Used In Information Technology SecurityThis slide depicts the cyber protection of an organization through artificial intelligence and how it can be helpful in threat detection, threat response, and human augmentation. Introducing Information Technology Security How Is Automation Used In Information Technology Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Threat Detection, Threat Response, Human Augmentation, using this template. Grab it now to reap its full benefits.
-
 Information Technology Security Information Technology Security Elements
Information Technology Security Information Technology Security ElementsThis slide represents the different elements of cyber security such as application security, network security, information security, etc. Introducing Information Technology Security Information Technology Security Elements to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on End User Education, Operational Security, Information Security, using this template. Grab it now to reap its full benefits.
-
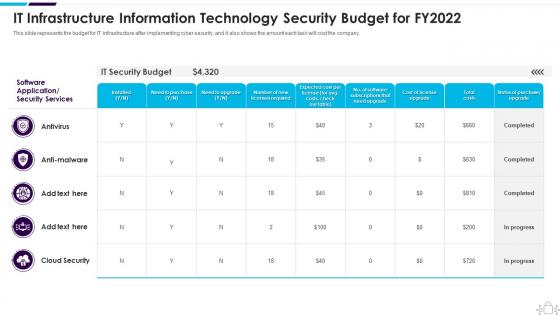 Information Technology Security It Infrastructure Information Budget For Fy2022
Information Technology Security It Infrastructure Information Budget For Fy2022This slide represents the budget for IT infrastructure after implementing cyber security, and it also shows the amount each task will cost the company. Present the topic in a bit more detail with this Information Technology Security It Infrastructure Information Budget For Fy2022. Use it as a tool for discussion and navigation on Infrastructure, Information, Technology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Technology Security Latest Threats In Information Technology Security
Information Technology Security Latest Threats In Information Technology SecurityThis slide depicts the categories of recent threats that recently emerged in the United States, United Kingdom, and Australia in previous years. Deliver an outstanding presentation on the topic using this Information Technology Security Latest Threats In Information Technology Security. Dispense information and present a thorough explanation of Latest Threats In Information Technology Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
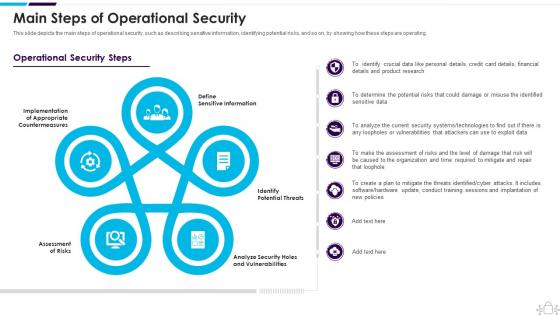 Information Technology Security Main Steps Of Operational Security
Information Technology Security Main Steps Of Operational SecurityThis slide depicts the main steps of operational security, such as describing sensitive information, identifying potential risks, and so on, by showing how these steps are operating. Present the topic in a bit more detail with this Information Technology Security Main Steps Of Operational Security. Use it as a tool for discussion and navigation on Assessment Of Risks, Define Sensitive Information, Identify Potential Threats This template is free to edit as deemed fit for your organization. Therefore download it now.
-
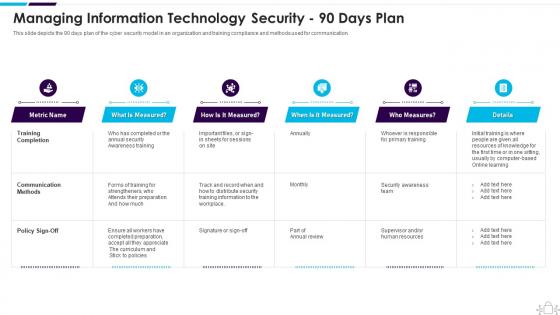 Information Technology Security Managing Information Technology Security 90 Days Plan
Information Technology Security Managing Information Technology Security 90 Days PlanThis slide depicts the 90 days plan of the cyber security model in an organization and training compliance and methods used for communication. Deliver an outstanding presentation on the topic using this Information Technology Security Managing Information Technology Security 90 Days Plan. Dispense information and present a thorough explanation of Managing, Information, Technology using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
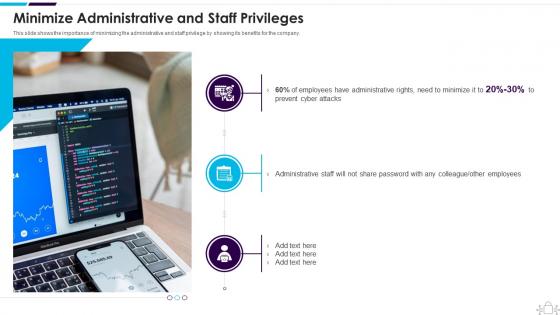 Information Technology Security Minimize Administrative And Staff Privileges
Information Technology Security Minimize Administrative And Staff PrivilegesThis slide shows the importance of minimizing the administrative and staff privilege by showing its benefits for the company. Introducing Information Technology Security Minimize Administrative And Staff Privileges to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Minimize Administrative And Staff Privileges, using this template. Grab it now to reap its full benefits.
-
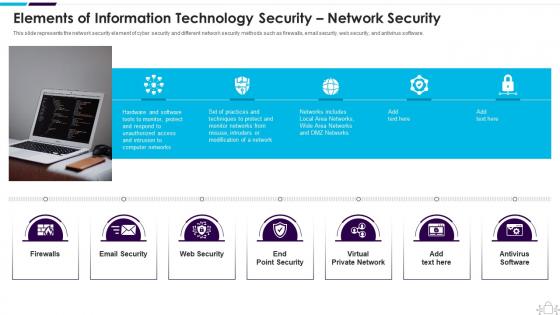 Information Technology Security Network Security
Information Technology Security Network SecurityThis slide represents the network security element of cyber security and different network security methods such as firewalls, email security, web security, and antivirus software. Increase audience engagement and knowledge by dispensing information using Information Technology Security Network Security. This template helps you present information on seven stages. You can also present information on Information, Technology, Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Information Technology Security Of Information Technology Security Disaster Recovery Planning
Information Technology Security Of Information Technology Security Disaster Recovery PlanningThis slide depicts the disaster recovery plan in the cyber security model and what strategies an organization needs to adopt to recover from an attack or natural disaster. Introducing Information Technology Security Of Information Technology Security Disaster Recovery Planning to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Information, Technology, Security using this template. Grab it now to reap its full benefits.
-
 Information Technology Security Operational Security
Information Technology Security Operational SecurityThis slide defines the operational security element of cyber security. It also shows the best practices for operational security such as change management processes, deploys automation, etc. Increase audience engagement and knowledge by dispensing information using Information Technology Security Operational Security. This template helps you present information on five stages. You can also present information on Change Management, Processes, Deploy Automation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
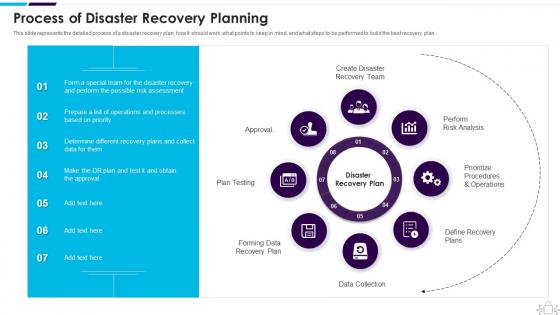 Information Technology Security Process Of Disaster Recovery Planning
Information Technology Security Process Of Disaster Recovery PlanningThis slide represents the detailed process of a disaster recovery plan, how it should work, what points to keep in mind, and what steps to be performed to build the best recovery plan. Introducing Information Technology Security Process Of Disaster Recovery Planning to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Process Of Disaster Recovery Planning, using this template. Grab it now to reap its full benefits.
-
 Information Technology Security Roadmap For Information Technology Security Training
Information Technology Security Roadmap For Information Technology Security TrainingThis slide depicts the cyber security training roadmap. It also shows the plan and guidelines to conduct an effective training program. Introducing Information Technology Security Roadmap For Information Technology Security Training to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Roadmap, Information, Technology, using this template. Grab it now to reap its full benefits.
-
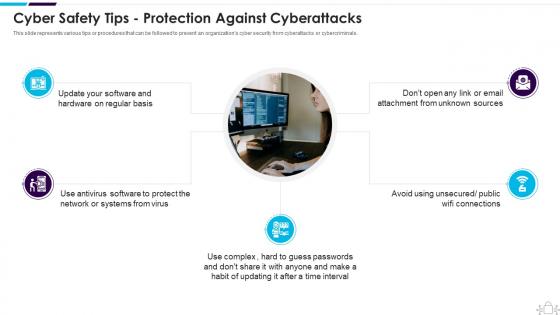 Information Technology Security Safety Tips Protection Against Cyberattacks
Information Technology Security Safety Tips Protection Against CyberattacksThis slide represents various tips or procedures that can be followed to prevent an organizations cyber security from cyberattacks or cybercriminals. Increase audience engagement and knowledge by dispensing information using Information Technology Security Safety Tips Protection Against Cyberattacks. This template helps you present information on five stages. You can also present information on Cyber Safety Tips Protection Against Cyberattacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Information Technology Security Set Measures For Secure Communication
Information Technology Security Set Measures For Secure CommunicationThis slide depicts secure communication within an organization and the technology to encrypt emails or data while sending or receiving them. Introducing Information Technology Security Set Measures For Secure Communication to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Organization, Measures, Communication, using this template. Grab it now to reap its full benefits.
-
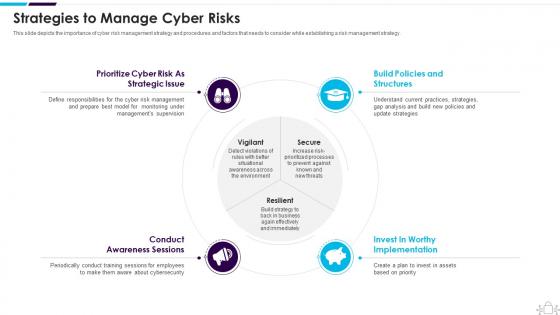 Information Technology Security Strategies To Manage Cyber Risks
Information Technology Security Strategies To Manage Cyber RisksThis slide depicts the importance of cyber risk management strategy and procedures and factors that needs to consider while establishing a risk management strategy. Increase audience engagement and knowledge by dispensing information using Information Technology Security Strategies To Manage Cyber Risks. This template helps you present information on four stages. You can also present information on Strategic, Structures, Implementation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
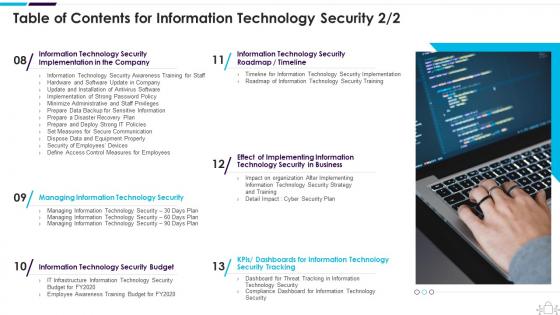 Information Technology Security Table Of Contents
Information Technology Security Table Of ContentsIntroducing Information Technology Security Table Of Contents to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Information, Technology, Security, using this template. Grab it now to reap its full benefits.
-
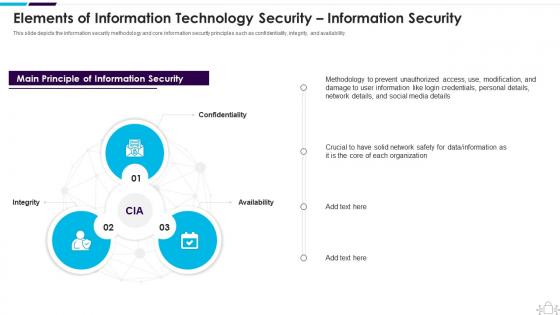 Information Technology Security Technology Security Information Security
Information Technology Security Technology Security Information SecurityThis slide depicts the information security methodology and core information security principles such as confidentiality, integrity, and availability. Increase audience engagement and knowledge by dispensing information using Information Technology Security Technology Security Information Security. This template helps you present information on three stages. You can also present information on Confidentiality, Availability, Integrity using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Information Technology Security Threats In Information Technology Security
Information Technology Security Threats In Information Technology SecurityThis slide depicts the main types of threats in cyber security, such as cybercrime, cyber terrorism, and cyberattacks to an organization and the purpose of each category threat. Introducing Information Technology Security Threats In Information Technology Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Types Of Threats In Information Technology Security, using this template. Grab it now to reap its full benefits.
-
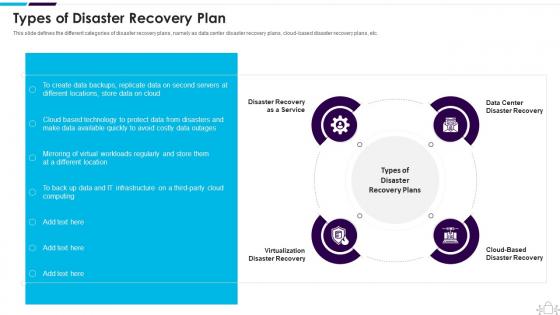 Information Technology Security Types Of Disaster Recovery Plan
Information Technology Security Types Of Disaster Recovery PlanThis slide defines the different categories of disaster recovery plans, namely as data center disaster recovery plans, cloud based disaster recovery plans, etc. Increase audience engagement and knowledge by dispensing information using Information Technology Security Types Of Disaster Recovery Plan. This template helps you present information on four stages. You can also present information on Disaster, Recovery, Virtualization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Information Technology Security What Is Information Technology Security And How Does It Work
Information Technology Security What Is Information Technology Security And How Does It WorkThis slide defines the meaning of cyber security and how it helps to prevent data through different methods and techniques. Introducing Information Technology Security What Is Information Technology Security And How Does It Work to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Information, Technology, Security, using this template. Grab it now to reap its full benefits.
-
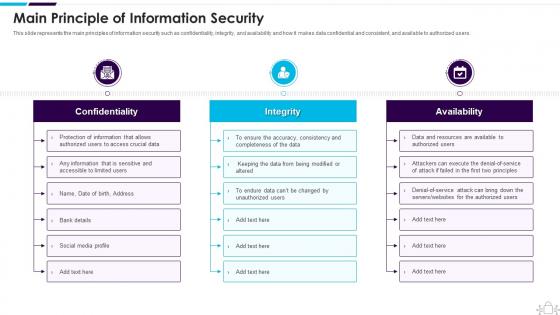 Main Principle Of Information Security Information Technology Security
Main Principle Of Information Security Information Technology SecurityThis slide represents the main principles of information security such as confidentiality, integrity, and availability and how it makes data confidential and consistent, and available to authorized users. Deliver an outstanding presentation on the topic using this Main Principle Of Information Security Information Technology Security. Dispense information and present a thorough explanation of Main Principle Of Information Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.



