Powerpoint Templates and Google slides for Information Security Strategy
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Roles And Responsibilities In Information Security Formulating Cybersecurity Plan
Roles And Responsibilities In Information Security Formulating Cybersecurity PlanThis slide showcases challenges involved in formulating risk management program for information security. It also shows solutions to tackle the challenges and impact of implementing them. Introducing Roles And Responsibilities In Information Security Formulating Cybersecurity Plan to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Information Security Manager, Risk Management Officer, Chief Information Officer, using this template. Grab it now to reap its full benefits.
-
 Steps For Information Security Risk Management Formulating Cybersecurity Plan
Steps For Information Security Risk Management Formulating Cybersecurity PlanThis slide showcase steps which can help organization to implement information security risk management program in organization. Its key steps are identify, protect, detect and respond. Deliver an outstanding presentation on the topic using this Steps For Information Security Risk Management Formulating Cybersecurity Plan. Dispense information and present a thorough explanation of Asset Identification, Risk Assessment, Awareness And Training using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
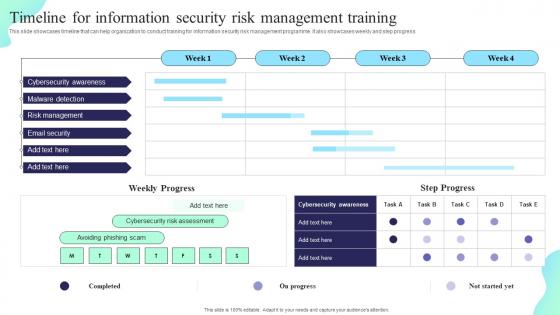 Timeline For Information Security Risk Management Training Formulating Cybersecurity Plan
Timeline For Information Security Risk Management Training Formulating Cybersecurity PlanThis slide showcases timeline that can help organization to conduct training for information security risk management programme. It also showcases weekly and step progress. Deliver an outstanding presentation on the topic using this Timeline For Information Security Risk Management Training Formulating Cybersecurity Plan. Dispense information and present a thorough explanation of Cybersecurity Awareness, Malware Detection, Risk Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Risk Information Security In Powerpoint And Google Slides Cpb
Risk Information Security In Powerpoint And Google Slides CpbPresenting our Risk Information Security In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Risk Information Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Information Security Cybersecurity In Powerpoint And Google Slides Cpb
Information Security Cybersecurity In Powerpoint And Google Slides CpbPresenting Information Security Cybersecurity In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Information Security Cybersecurity. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Availability Information Security In Powerpoint And Google Slides cpb
Availability Information Security In Powerpoint And Google Slides cpbPresenting Availability Information Security In Powerpoint And Google Slides cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Availability Information Security. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Information Security In Powerpoint And Google Slides Cpb
Information Security In Powerpoint And Google Slides CpbPresenting our Information Security In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Information Security. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Information Security Principles In Powerpoint And Google Slides Cpb
Information Security Principles In Powerpoint And Google Slides CpbPresenting Information Security Principles In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Information Security Principles. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Insider Threats Information Security In Powerpoint And Google Slides Cpb
Insider Threats Information Security In Powerpoint And Google Slides CpbPresenting our Insider Threats Information Security In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Insider Threats Information Security. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
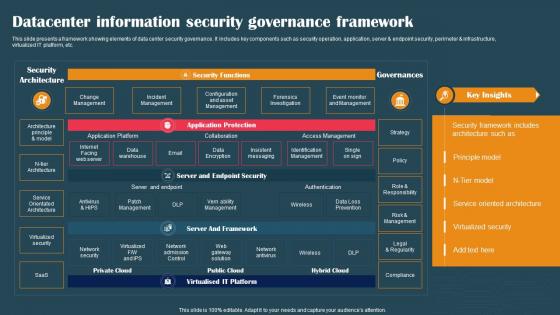 Datacenter Information Security Governance Framework
Datacenter Information Security Governance FrameworkThis slide presents a framework showing elements of data center security governance. It includes key components such as security operation, application, server and endpoint security, perimeter and infrastructure, virtualized IT platform, etc. Presenting our well structured Datacenter Information Security Governance Framework. The topics discussed in this slide are Data Warehouse, Data Encryption, Network Security. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Information Security Governance And Management Program Framework
Information Security Governance And Management Program FrameworkThis slide showcases a framework of information security governance and management to develop business specific risk control program. It includes key components such as identify security, infrastructure security, HR security, detection, response and recovery, measurement, etc. Introducing our Information Security Governance And Management Program Framework set of slides. The topics discussed in these slides are Information Security Charter, Evaluation And Direction. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Information Security Governance Best Practices
Information Security Governance Best PracticesThis slide presents various best practices for information security governance to effectively manage and mitigate IT risks. It includes key practices such as reflect business objectives, develop and enforce security program, embrace organizations culture, etc. Presenting our set of slides with Information Security Governance Best Practices. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Develop, Enforce Security Program.
-
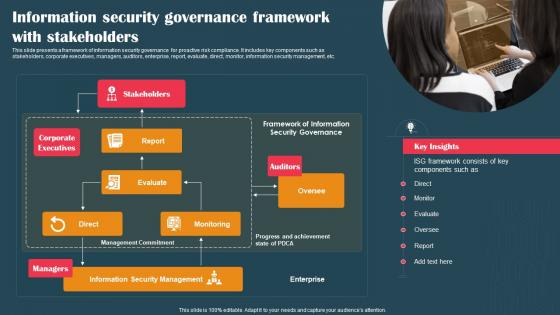 Information Security Governance Framework With Stakeholders
Information Security Governance Framework With StakeholdersThis slide presents a framework of information security governance for proactive risk compliance. It includes key components such as stakeholders, corporate executives, managers, auditors, enterprise, report, evaluate, direct, monitor, information security management, etc. Introducing our premium set of slides with Information Security Governance Framework With Stakeholders. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Stakeholders, Auditors, Corporate Executives. So download instantly and tailor it with your information.
-
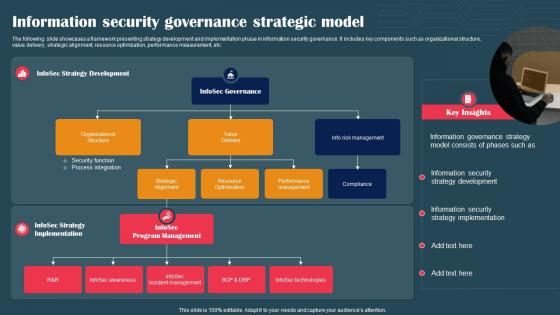 Information Security Governance Strategic Model
Information Security Governance Strategic ModelThe following slide showcases a framework presenting strategy development and implementation phase in information security governance. It includes key components such as organizational structure, value delivery, strategic alignment, resource optimization, performance measurement, etc. Presenting our set of slides with Information Security Governance Strategic Model. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Organizational Structure, Strategic Alignment, Compliance.
-
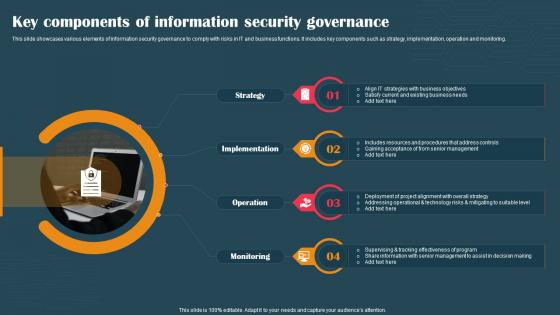 Key Components Of Information Security Governance
Key Components Of Information Security GovernanceThis slide showcases various elements of information security governance to comply with risks in IT and business functions. It includes key components such as strategy, implementation, operation and monitoring. Presenting our set of slides with Key Components Of Information Security Governance. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Implementation, Monitoring, Strategy.
-
 Information Security Dashboard Template In Powerpoint And Google Slides Cpb
Information Security Dashboard Template In Powerpoint And Google Slides CpbPresenting our Information Security Dashboard Template In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Information Security Dashboard Template. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Steps Building Information Security Team In Powerpoint And Google Slides Cpb
Steps Building Information Security Team In Powerpoint And Google Slides CpbPresenting Steps Building Information Security Team In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Steps Building Information Security Team. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Business Information Security Structural Framework
Business Information Security Structural FrameworkThis slide covers business information security structural framework which includes chief information security officer with guidelines for control process. Introducing our Business Information Security Structural Framework set of slides. The topics discussed in these slides are Business Information, Security, Structural Framework. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
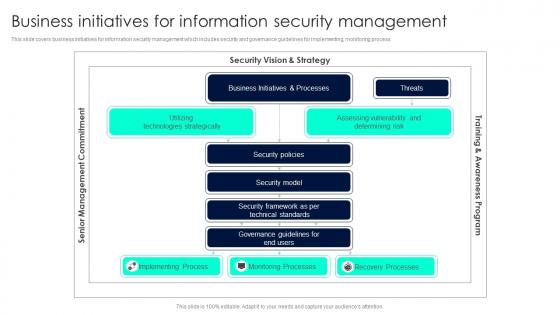 Business Initiatives For Information Security Management
Business Initiatives For Information Security ManagementThis slide covers business initiatives for information security management which includes security and governance guidelines for implementing, monitoring process. Presenting our well structured Business Initiatives For Information Security Management. The topics discussed in this slide are Security Vision, Business Initiatives, Implementing Process. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
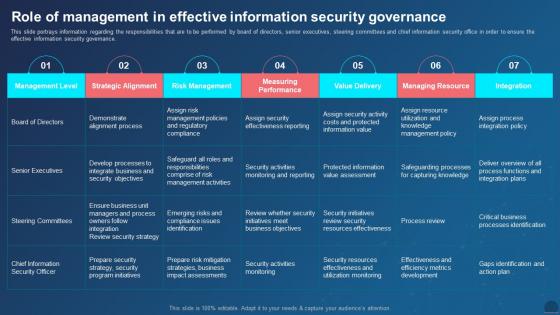 Managing Mobile Devices Role Of Management In Effective Information Security Governance
Managing Mobile Devices Role Of Management In Effective Information Security GovernanceThis slide portrays information regarding the responsibilities that are to be performed by board of directors, senior executives, steering committees and chief information security office in order to ensure the effective information security governance. Present the topic in a bit more detail with this Managing Mobile Devices Role Of Management In Effective Information Security Governance. Use it as a tool for discussion and navigation on Demonstrate Alignment Process, Critical Business Processes Identification, Steering Committees. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cloud Digital Certificate Icon For Information Security
Cloud Digital Certificate Icon For Information SecurityIntroducing our premium set of slides with Cloud Digital Certificate Icon For Information Security. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cloud Digital Certificate, Icon Information Security. So download instantly and tailor it with your information.
-
 Awareness Information Security In Powerpoint And Google Slides Cpb
Awareness Information Security In Powerpoint And Google Slides CpbPresenting Awareness Information Security In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Awareness Information Security. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Information Security Organization In Powerpoint And Google Slides Cpb
Information Security Organization In Powerpoint And Google Slides CpbPresenting Information Security Organization In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Information Security Organization. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
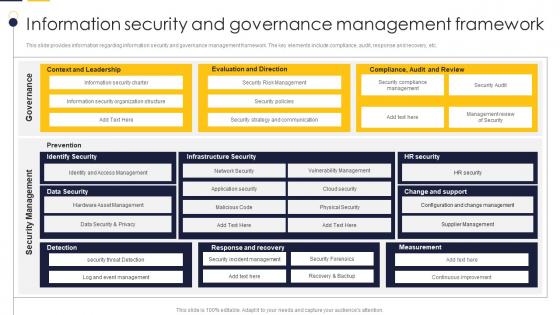 Information Security And Governance Guide To Build It Strategy Plan For Organizational Growth
Information Security And Governance Guide To Build It Strategy Plan For Organizational GrowthThis slide provides information regarding information security and governance management framework. The key elements include compliance, audit, response and recovery, etc. Present the topic in a bit more detail with this Information Security And Governance Guide To Build It Strategy Plan For Organizational Growth. Use it as a tool for discussion and navigation on Governance, Management, Framework. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Agenda Enterprise Risk Management And Information Technology Security
Agenda Enterprise Risk Management And Information Technology SecurityIntroducing Agenda Enterprise Risk Management And Information Technology Security to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Organization, IT Networks, IT Risk Management, using this template. Grab it now to reap its full benefits.
-
 Enterprise Risk Management And Information Technology Security Table Of Contents
Enterprise Risk Management And Information Technology Security Table Of ContentsIncrease audience engagement and knowledge by dispensing information using Enterprise Risk Management And Information Technology Security Table Of Contents. This template helps you present information on one stages. You can also present information on Security Criteria, Control Measures, IT System Vulnerabilities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons Slide For Enterprise Risk Management And Information Technology Security
Icons Slide For Enterprise Risk Management And Information Technology SecurityIntroducing our well researched set of slides titled Icons Slide For Enterprise Risk Management And Information Technology Security. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
 Table Of Contents For Enterprise Risk Management And Information Technology Security
Table Of Contents For Enterprise Risk Management And Information Technology SecurityIntroducing Table Of Contents For Enterprise Risk Management And Information Technology Security to increase your presentation threshold. Encompassed with eleven stages, this template is a great option to educate and entice your audience. Dispence information on IT Risks, Threat Evaluation, IT Risk Management, Cost Estimation, using this template. Grab it now to reap its full benefits.
-
 Information Security Risk Indicators Examples In Powerpoint And Google Slides Cpb
Information Security Risk Indicators Examples In Powerpoint And Google Slides CpbPresenting our Information Security Risk Indicators Examples In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Information Security Risk Indicators Examples This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Key Risk Indicators Examples Information Security In Powerpoint And Google Slides Cpb
Key Risk Indicators Examples Information Security In Powerpoint And Google Slides CpbPresenting our Key Risk Indicators Examples Information Security In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Key Risk Indicators Examples Information Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Information Security Policy For Employees Information Technology Policy
Information Security Policy For Employees Information Technology PolicyThis slide depicts the information security policy that critical topics covered in this policy. It also covers the reasons for frequent changes in the policy. Introducing Information Security Policy For Employees Information Technology Policy to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Company Infrastructure, IT Infrastructure, Data Processing Activities And Purposes, using this template. Grab it now to reap its full benefits.
-
 Overview Of Network Security Policy For Workers Information Technology Policy
Overview Of Network Security Policy For Workers Information Technology PolicyThis slide describes the network security policy, which ensures systems have the proper hardware, software, and auditing processes. It logs details of activities such as failed log in attempts, information starts up or shutdown, etc. Introducing Overview Of Network Security Policy For Workers Information Technology Policy to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Organizations, Network Security, Information, using this template. Grab it now to reap its full benefits.
-
 Security Awareness And Training Policy Overview Information Technology Policy
Security Awareness And Training Policy Overview Information Technology PolicyThis slide represents the security awareness and training policy. It covers that the training program should be designed by management, and employees will sign a confidentiality agreement after getting the training. Increase audience engagement and knowledge by dispensing information using Security Awareness And Training Policy Overview Information Technology Policy. This template helps you present information on six stages. You can also present information on Corporate Data, Security, Employees using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
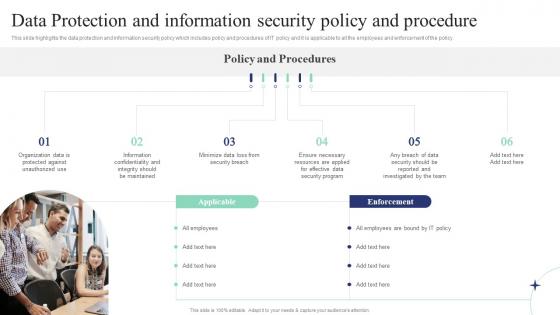 Data Protection And Information Security Policy And Procedure Corporate Induction Program For New Staff
Data Protection And Information Security Policy And Procedure Corporate Induction Program For New StaffThis slide highlights the data protection and information security policy which includes policy and procedures of IT policy and it is applicable to all the employees and enforcement of the policy. Introducing Data Protection And Information Security Policy And Procedure Corporate Induction Program For New Staff to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Protection, Information, Procedure, using this template. Grab it now to reap its full benefits.
-
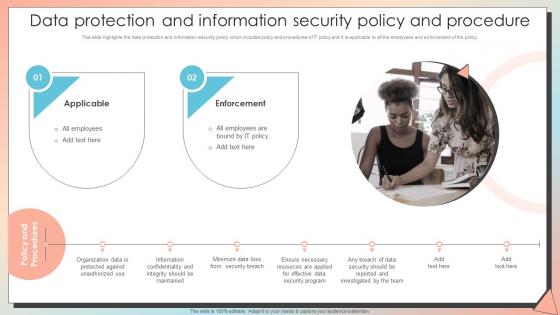 Data Protection And Information Security Policy New Employee Induction Programme
Data Protection And Information Security Policy New Employee Induction ProgrammeThis slide highlights the data protection and information security policy which includes policy and procedures of IT policy and it is applicable to all the employees and enforcement of the policy.Increase audience engagement and knowledge by dispensing information using Data Protection And Information Security Policy New Employee Induction Programme. This template helps you present information on two stages. You can also present information on Information Confidentiality, Security Program, Ensure Necessary using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
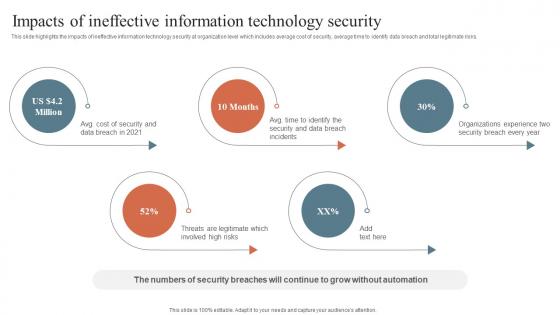 Impacts Of Ineffective Information Technology Security Security Orchestration Automation
Impacts Of Ineffective Information Technology Security Security Orchestration AutomationThis slide highlights the impacts of ineffective information technology security at organization level which includes average cost of security, average time to identify data breach and total legitimate risks. Introducing Impacts Of Ineffective Information Technology Security Security Orchestration Automation to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Impacts Of Ineffective, Information Technology, Security, using this template. Grab it now to reap its full benefits.
-
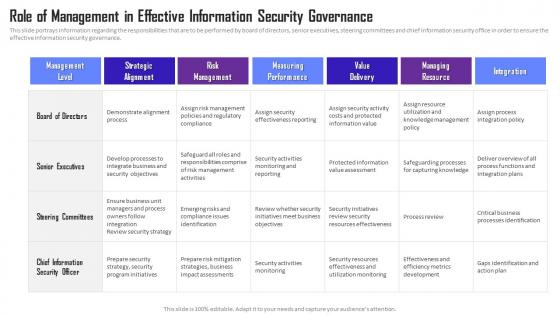 Managing Mobile Device Solutions Role Of Management In Effective Information Security Governance
Managing Mobile Device Solutions Role Of Management In Effective Information Security GovernanceThis slide portrays information regarding the responsibilities that are to be performed by board of directors, senior executives, steering committees and chief information security office in order to ensure the effective information security governance. Present the topic in a bit more detail with this Managing Mobile Device Solutions Role Of Management In Effective Information Security Governance. Use it as a tool for discussion and navigation on Role Of Management, Effective Information, Security Governance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Traditional Vs Cloud Information Security Icon
Traditional Vs Cloud Information Security IconPresenting our set of slides with name Traditional Vs Cloud Information Security Icon. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Traditional, Cloud Information Security, Icon.
-
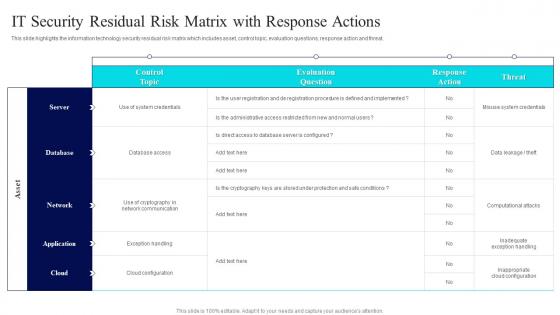 IT Security Residual Risk Matrix With Risk Management Guide For Information Technology Systems
IT Security Residual Risk Matrix With Risk Management Guide For Information Technology SystemsThis slide highlights the information technology security residual risk matrix which includes asset, control topic, evaluation questions, response action and threat. Deliver an outstanding presentation on the topic using this IT Security Residual Risk Matrix With Risk Management Guide For Information Technology Systems. Dispense information and present a thorough explanation of Database Access, Evaluation Question, Response Action using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
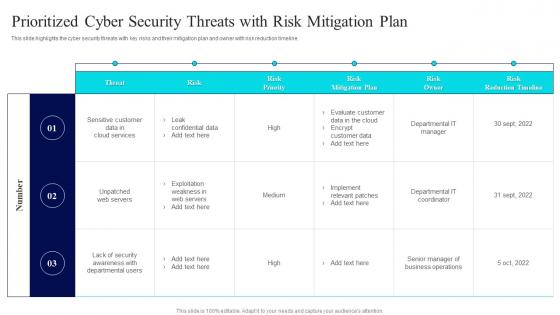 Prioritized Cyber Security Threats With Risk Risk Management Guide For Information Technology Systems
Prioritized Cyber Security Threats With Risk Risk Management Guide For Information Technology SystemsThis slide highlights the cyber security threats with key risks and their mitigation plan and owner with risk reduction timeline. Present the topic in a bit more detail with this Prioritized Cyber Security Threats With Risk Risk Management Guide For Information Technology Systems. Use it as a tool for discussion and navigation on Threat Risk, Risk Mitigation Plan, Risk Owner. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
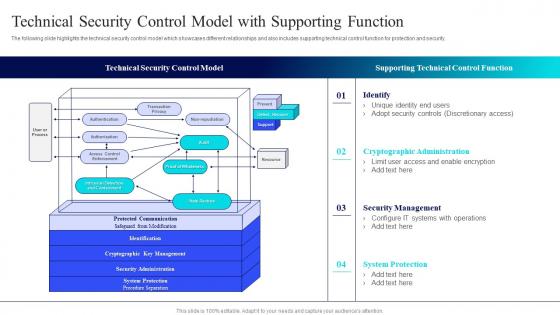 Technical Security Control Model With Isk Management Guide For Information Technology Systems
Technical Security Control Model With Isk Management Guide For Information Technology SystemsThe following slide highlights the technical security control model which showcases different relationships and also includes supporting technical control function for protection and security. Deliver an outstanding presentation on the topic using this Technical Security Control Model With Isk Management Guide For Information Technology Systems. Dispense information and present a thorough explanation of Technical Security, Control Model, Supporting Technical, Control Function using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Elements IT Information Security Element Of Cyber Security Ppt Microsoft
Cyber Security Elements IT Information Security Element Of Cyber Security Ppt MicrosoftThis slide depicts the information security methodology and core information security principles such as confidentiality, integrity, and availability. These are also known as cyber security objectives. Increase audience engagement and knowledge by dispensing information using Cyber Security Elements IT Information Security Element Of Cyber Security Ppt Microsoft. This template helps you present information on three stages. You can also present information on Confidentiality, Availability, Integrity, Information Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Risk Management Icon In Information Technology
Cyber Security Risk Management Icon In Information TechnologyPresent the topic in a bit more detail with this Cyber Security Risk Management Icon In Information Technology. Use it as a tool for discussion and navigation on Cyber Security, Risk Management, Icon In Information Technology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
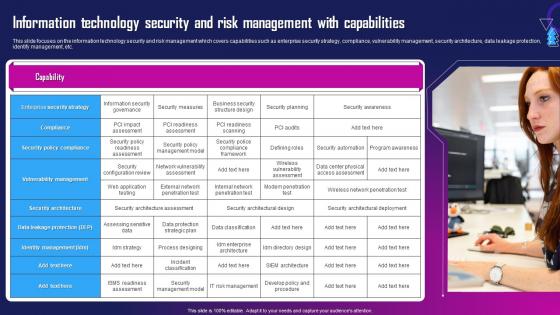 Information Technology Security And Risk Management With Capabilities
Information Technology Security And Risk Management With CapabilitiesThis slide focuses on the information technology security and risk management which covers capabilities such as enterprise security strategy, compliance, vulnerability management, security architecture, data leakage protection, identify management, etc. Deliver an outstanding presentation on the topic using this Information Technology Security And Risk Management With Capabilities. Dispense information and present a thorough explanation of Security Policy Compliance, Compliance, Enterprise Security Strategy using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Model For Information Technology Security Risk Management
Model For Information Technology Security Risk ManagementThis slide shows the model that depicts IT security risk management which focuses on identification, protection, detection, response and recovery planning with security asset management, governance, data security, detection processes, risk analysis and planning, etc. Introducing Model For Information Technology Security Risk Management to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Identifying, Protecting, Detecting, using this template. Grab it now to reap its full benefits.
-
 Risk Management Matrix For Information Technology Security
Risk Management Matrix For Information Technology SecurityThis slide shows the risk management matrix for information technology security which covers the business workflow and technical systems with IT risks and threats such as software security, business controls, control risk modelling, penetration testing, attack modelling, etc. Present the topic in a bit more detail with this Risk Management Matrix For Information Technology Security. Use it as a tool for discussion and navigation on Corporate Workflow, Risks, Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Risk Management Methodology In Information Technology Security
Risk Management Methodology In Information Technology SecurityThis slide focuses on the risk management methodology in information technology security which includes three different phases such as assessment, mitigation and continual evaluation assessment that are helpful in effective management of security risks and hazards. Deliver an outstanding presentation on the topic using this Risk Management Methodology In Information Technology Security. Dispense information and present a thorough explanation of Assessment, Mitigation, Continual Evaluation Assessment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Security Program Manager Roles And Responsibilities
Information Security Program Manager Roles And ResponsibilitiesThis slide covers information security program manager roles and responsibilities. It involves information owner, security administrator and IT management. Introducing our premium set of slides with Information Security Program Manager Roles And Responsibilities. Elucidate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Information Owner, Security Administrator, IT Management. So download instantly and tailor it with your information.
-
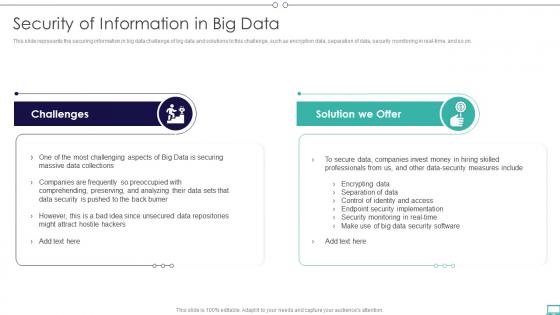 Big Data And Its Types Security Of Information In Big Data Ppt PowerPoint Presentation gallery
Big Data And Its Types Security Of Information In Big Data Ppt PowerPoint Presentation galleryThis slide represents the securing information in big data challenge of big data and solutions to this challenge, such as encryption data, separation of data, security monitoring in real-time, and so on. Increase audience engagement and knowledge by dispensing information using Big Data And Its Types Security Of Information In Big Data Ppt PowerPoint Presentation gallery. This template helps you present information on two stages. You can also present information on Challenges, Solution, Data Collections using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
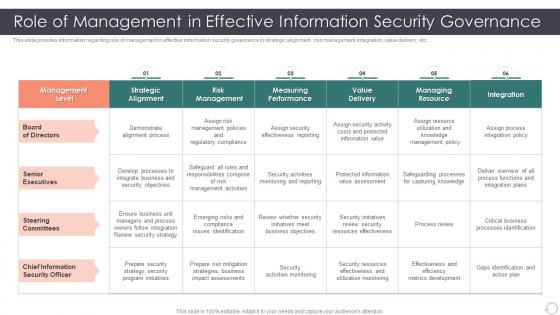 Role Enhancing Capability Cost Reduction Role Of Management In Effective Information Security
Role Enhancing Capability Cost Reduction Role Of Management In Effective Information SecurityThis slide provides information regarding role of management in effective information security governance in strategic alignment , risk management, integration, value delivery, etc. Deliver an outstanding presentation on the topic using this Role Enhancing Capability Cost Reduction Role Of Management In Effective Information Security. Dispense information and present a thorough explanation of Management, Information, Governance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Systems Security Officer Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Information Systems Security Officer Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Information systems security officer colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Information Systems Security Officer Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Information Systems Security Officer Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Information systems security officer monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Checklist To Improve Information Technology Security
Checklist To Improve Information Technology SecurityThis slide shows comprehensive checklist used to enhance information technology security. It includes email phishing training, anti virus and malware use, password changes etc. Presenting our set of slides with Checklist To Improve Information Technology Security. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Change Passwords Frequently, Email Phishing Training, Regular Firewall Holes Checking.
-
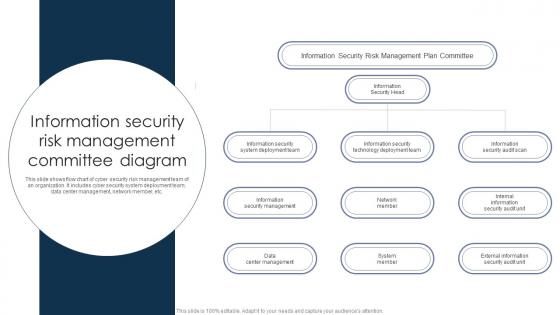 Information Security Risk Management Committee Diagram
Information Security Risk Management Committee DiagramThis slide shows flow chart of cyber security risk management team of an organization. It includes cyber security system deployment team, data center management, network member, etc. Presenting our set of slides with Information Security Risk Management Committee Diagram. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Information Security Head, Network Member, System Member.
-
 Information Technology Security Icon To Reduce Threats
Information Technology Security Icon To Reduce ThreatsIntroducing our premium set of slides with Information Technology Security Icon To Reduce Threats. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Information Technology Security Icon, Reduce Threats. So download instantly and tailor it with your information.
-
 Organizational Information Security Management Icon
Organizational Information Security Management IconPresenting our set of slides with Organizational Information Security Management Icon. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Organizational Information, Security Management Icon.
-
 Q308 IT Professionals Certification Collection Certified Information Systems Security Professional
Q308 IT Professionals Certification Collection Certified Information Systems Security ProfessionalThis slide covers CISSP certification details such as what is the CISSP, how to become certified, how to prepare for CISSP and why to get CISSP certifications. Introducing Q308 IT Professionals Certification Collection Certified Information Systems Security Professional to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on CISS Certification, Network Security, Administrative Activities, using this template. Grab it now to reap its full benefits.
-
 Information Security Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Information Security Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Information security colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Information Security Lock Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Information Security Lock Colored Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Information security lock colored icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Information Security Lock Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Information Security Lock Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Information security lock monotone icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.



