Powerpoint Templates and Google slides for Information Security Strategy
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
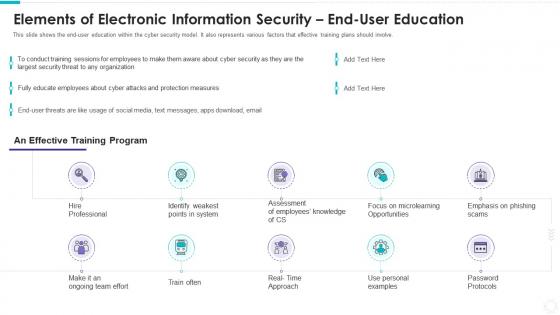 Elements of electronic information security end user education
Elements of electronic information security end user educationThis slide shows the end-user education within the cyber security model. It also represents various factors that effective training plans should involve. Present the topic in a bit more detail with this Elements Of Electronic Information Security End User Education. Use it as a tool for discussion and navigation on Hire Professional, Identify weakest points system, Password Protocols. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
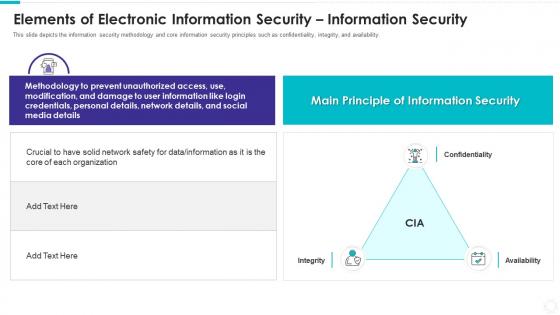 Elements of electronic information security information security
Elements of electronic information security information securityThis slide depicts the information security methodology and core information security principles such as confidentiality, integrity, and availability. Increase audience engagement and knowledge by dispensing information using Elements Of Electronic Information Security Information Security. This template helps you present information on one stages. You can also present information on Confidentiality, Integrity, Availability using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
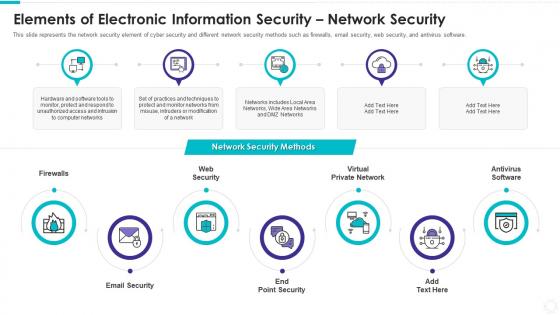 Elements of electronic information security network security
Elements of electronic information security network securityThis slide represents the network security element of cyber security and different network security methods such as firewalls, email security, web security, and antivirus software. Introducing Elements Of Electronic Information Security Network Security to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Firewalls, Web Security, Email Security, End Point Security, Virtual Private Network, Antivirus Software, using this template. Grab it now to reap its full benefits.
-
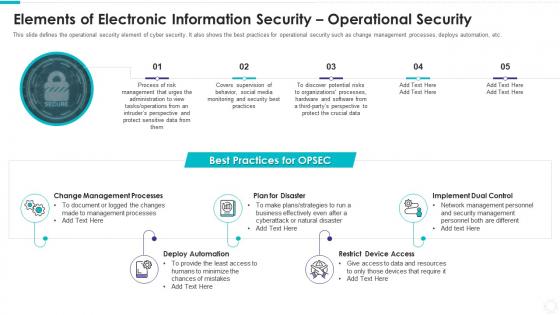 Elements of electronic information security operational security
Elements of electronic information security operational securityThis slide defines the operational security element of cyber security. It also shows the best practices for operational security such as change management processes, deploys automation, etc. Increase audience engagement and knowledge by dispensing information using Elements Of Electronic Information Security Operational Security. This template helps you present information on five stages. You can also present information on Change Management Processes, Plan Disaster, Deploy Automation, Restrict Device Access, Implement Dual Control using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
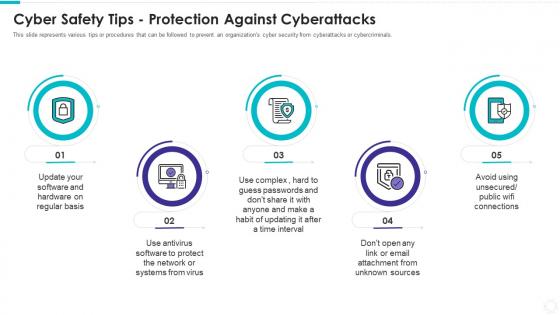 Electronic information security cyber safety tips protection against cyberattacks
Electronic information security cyber safety tips protection against cyberattacksThis slide represents various tips or procedures that can be followed to prevent an organizations cyber security from cyberattacks or cybercriminals. Introducing Electronic Information Security Cyber Safety Tips Protection Against Cyberattacks to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Regular Basis, Protect Network, Systems Virustime Interval, Email Attachment Unknown Sources, using this template. Grab it now to reap its full benefits.
-
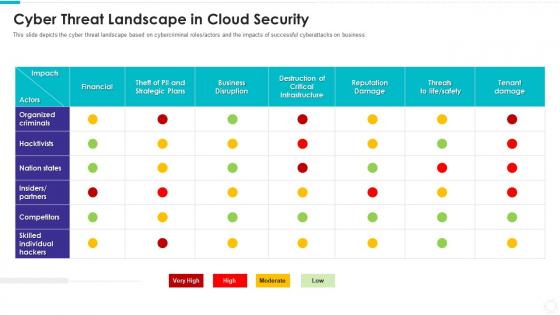 Electronic information security cyber threat landscape in cloud security
Electronic information security cyber threat landscape in cloud securityThis slide depicts the cyber threat landscape based on cybercriminal roles or actors and the impacts of successful cyberattacks on business. Present the topic in a bit more detail with this Electronic Information Security Cyber Threat Landscape In Cloud Security. Use it as a tool for discussion and navigation on Organized Criminals, Hacktivists, Nation States, Insiders Partners, Competitors. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
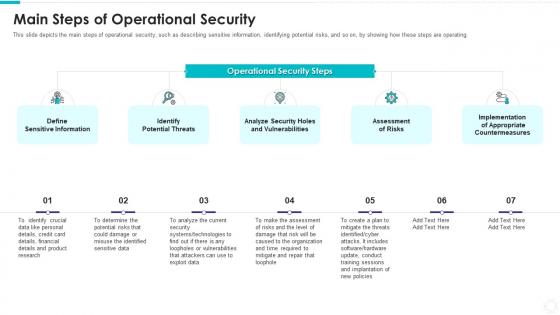 Electronic information security main steps of operational security
Electronic information security main steps of operational securityThis slide depicts the main steps of operational security, such as describing sensitive information, identifying potential risks, and so on, by showing how these steps are operating. Introducing Electronic Information Security Main Steps Of Operational Security to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Define Sensitive Information, Identify Potential Threats, Analyze Security Holes And Vulnerabilities, Assessment Risks, Implementation Appropriate Countermeasures, using this template. Grab it now to reap its full benefits.
-
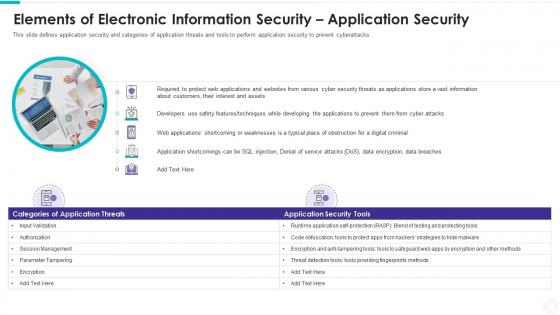 Elements of electronic information security application security
Elements of electronic information security application securityThis slide defines application security and categories of application threats and tools to perform application security to prevent cyberattacks. Increase audience engagement and knowledge by dispensing information using Elements Of Electronic Information Security Application Security. This template helps you present information on one stages. You can also present information on Interest And Assets, Protect Web Applications, Various Cyber Security, Vast Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
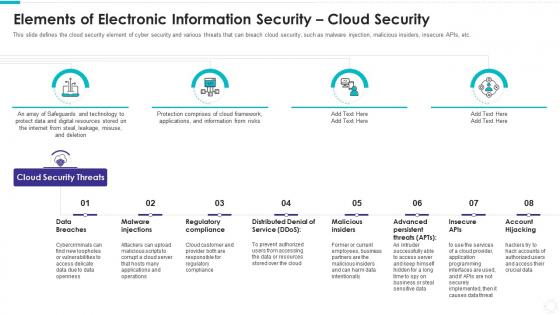 Elements of electronic information security cloud security
Elements of electronic information security cloud securityThis slide defines the cloud security element of cyber security and various threats that can breach cloud security, such as malware injection, malicious insiders, insecure APIs, etc. Introducing Elements Of Electronic Information Security Cloud Security to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Data Breaches, Malware Injections, Regulatory Compliance, Distributed Denial Service, Malicious Insiders, Account Hijacking, using this template. Grab it now to reap its full benefits.
-
 How is automation used in electronic information security
How is automation used in electronic information securityThis slide depicts the cyber protection of an organization through artificial intelligence and how it can be helpful in threat detection, threat response, and human augmentation. Increase audience engagement and knowledge by dispensing information using How Is Automation Used In Electronic Information Security. This template helps you present information on three stages. You can also present information on Threat Detection, Threat Response, Human Augmentation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
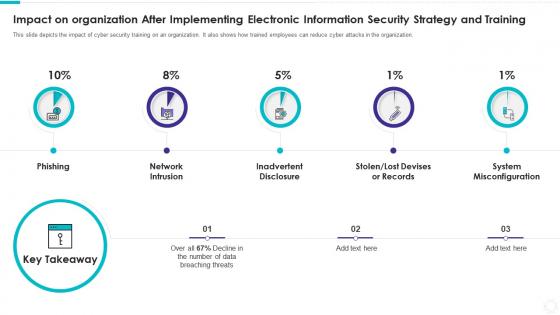 Impact on organization after implementing electronic information security strategy
Impact on organization after implementing electronic information security strategyThis slide depicts the impact of cyber security training on an organization. It also shows how trained employees can reduce cyber attacks in the organization. Introducing Impact On Organization After Implementing Electronic Information Security Strategy to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Phishing, Network Intrusion, Inadvertent Disclosure, Stolen, Lost Devises Or Records, System Misconfiguration, using this template. Grab it now to reap its full benefits.
-
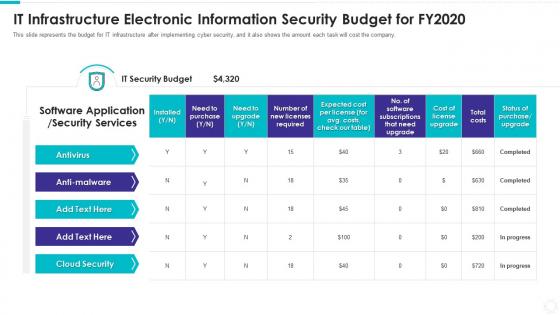 It infrastructure electronic information security budget for fy2020
It infrastructure electronic information security budget for fy2020This slide represents the budget for IT infrastructure after implementing cyber security, and it also shows the amount each task will cost the company. Deliver an outstanding presentation on the topic using this IT Infrastructure Electronic Information Security Budget For FY2020. Dispense information and present a thorough explanation of Antivirus, Anti Malware, IT Security Budget, Total Costs using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
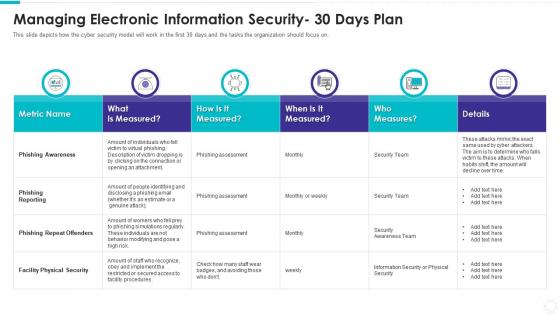 Managing electronic information security 30 days plan
Managing electronic information security 30 days planThis slide depicts how the cyber security model will work in the first 30 days and the tasks the organization should focus on. Present the topic in a bit more detail with this Managing Electronic Information Security 30 Days Plan. Use it as a tool for discussion and navigation on Phishing Awareness, Phishing Reporting, Phishing Repeat Offenders, Facility Physical Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
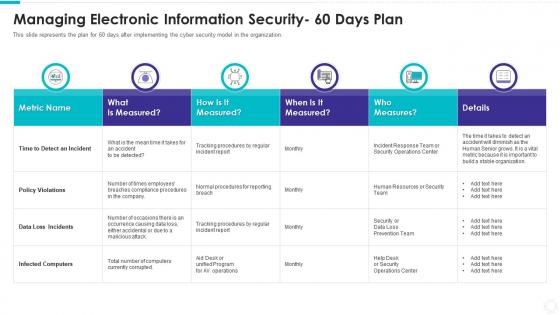 Managing electronic information security 60 days plan
Managing electronic information security 60 days planThis slide represents the plan for 60 days after implementing the cyber security model in the organization. Deliver an outstanding presentation on the topic using this Managing Electronic Information Security 60 Days Plan. Dispense information and present a thorough explanation of Time To Detect An Incident, Policy Violations, Data Loss Incidents, Infected Computers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
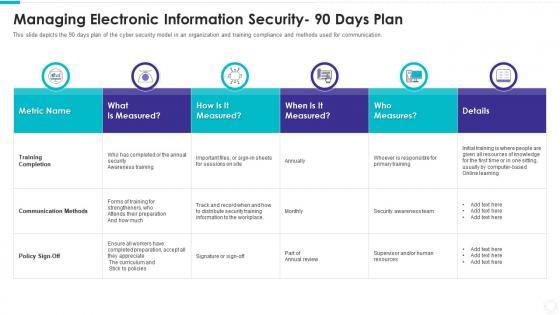 Managing electronic information security 90 days plan
Managing electronic information security 90 days planThis slide depicts the 90 days plan of the cyber security model in an organization and training compliance and methods used for communication. Present the topic in a bit more detail with this Managing Electronic Information Security 90 Days Plan. Use it as a tool for discussion and navigation on Training Completion, Communication Methods, Policy Sign Off, Measured, Metric. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
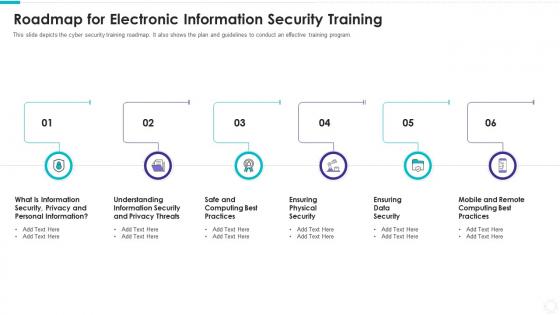 Roadmap for electronic information security training
Roadmap for electronic information security trainingThis slide depicts the cyber security training roadmap. It also shows the plan and guidelines to conduct an effective training program. Introducing Roadmap For Electronic Information Security Training to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Information Security, Privacy And Personal Information, Understanding Information Security And Privacy Threats, Safe And Computing Best Practices, Ensuring Physical Security, using this template. Grab it now to reap its full benefits.
-
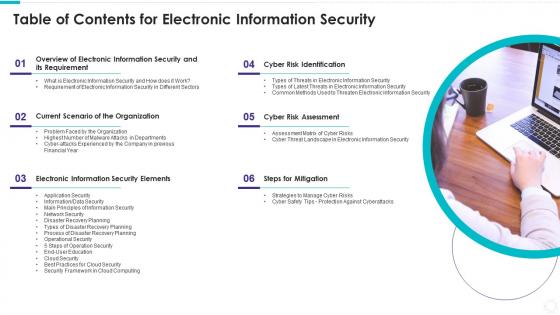 Table of contents for electronic information security
Table of contents for electronic information securityIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Electronic Information Security. This template helps you present information on six stages. You can also present information on Overview Electronic Information Security Requirement, Current Scenario Organization, Cyber Risk Identification, Cyber Risk Assessment, Steps For Mitigation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
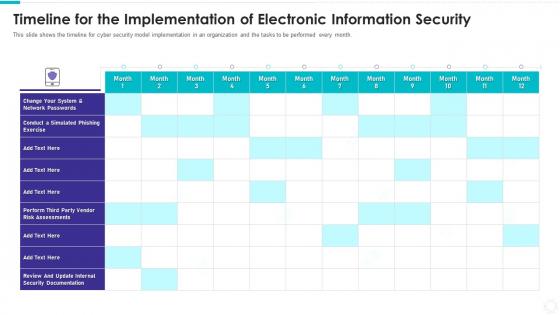 Timeline for the implementation of electronic information security
Timeline for the implementation of electronic information securityThis slide shows the timeline for cyber security model implementation in an organization and the tasks to be performed every month. Deliver an outstanding presentation on the topic using this Timeline For The Implementation Of Electronic Information Security. Dispense information and present a thorough explanation of Conduct Simulated Phishing Exercise, Change System, Network Passwords, Perform Third Party Vendor Risk Assessments using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Types of latest threats in electronic information security
Types of latest threats in electronic information securityThis slide depicts the categories of recent threats that recently emerged in the United States, United Kingdom, and Australia in previous years. Increase audience engagement and knowledge by dispensing information using Types Of Latest Threats In Electronic Information Security. This template helps you present information on eight stages. You can also present information on Dridex Malware, Romance Scams, Emotet Malware, Business using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Types of threats in electronic information security
Types of threats in electronic information securityThis slide depicts the main types of threats in cyber security, such as cybercrime, cyber terrorism, and cyberattacks to an organization and the purpose of each category threat. Introducing Types Of Threats In Electronic Information Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Cyber Crime, Cyber Terrorism, using this template. Grab it now to reap its full benefits.
-
 What is electronic information security and how does it work
What is electronic information security and how does it workThis slide defines the meaning of cyber security and how it helps to prevent data through different methods and techniques. Introducing What Is Electronic Information Security And How Does IT Work to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Caused Natural Disasters, Collective Methods, Techniques And Procedures, Protect Data, using this template. Grab it now to reap its full benefits.
-
 Security system society ppt powerpoint presentation layouts information cpb
Security system society ppt powerpoint presentation layouts information cpbPresenting Security System Society Ppt Powerpoint Presentation Layouts Information Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Security System Society. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Information gathering cyber security ppt powerpoint presentation portfolio display cpb
Information gathering cyber security ppt powerpoint presentation portfolio display cpbIncrease audience engagement and knowledge by dispensing information using Information Gathering Cyber Security Ppt Powerpoint Presentation Portfolio Display Cpb. This template helps you present information on five stages. You can also present information on Information Gathering Cyber Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
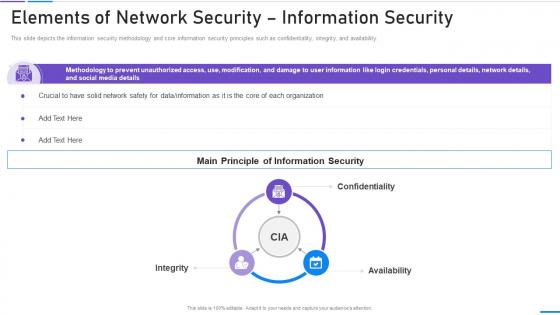 Elements Of Network Security Information Security Ppt Slides Objects
Elements Of Network Security Information Security Ppt Slides ObjectsThis slide depicts the information security methodology and core information security principles such as confidentiality, integrity, and availability. Introducing Elements Of Network Security Information Security Ppt Slides Objects to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Information, Principle, Security, Confidentiality, using this template. Grab it now to reap its full benefits.
-
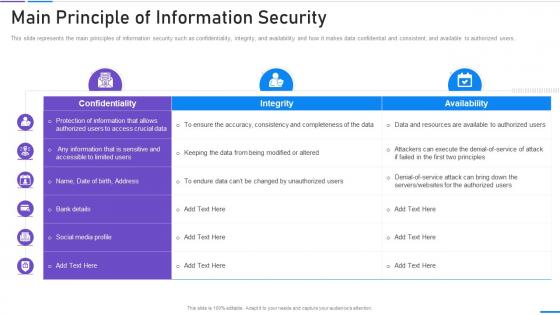 Network Security Main Principle Of Information Security
Network Security Main Principle Of Information SecurityThis slide represents the main principles of information security such as confidentiality, integrity, and availability and how it makes data confidential and consistent, and available to authorized users. Deliver an outstanding presentation on the topic using this Network Security Main Principle Of Information Security. Dispense information and present a thorough explanation of Main Principle Of Information Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
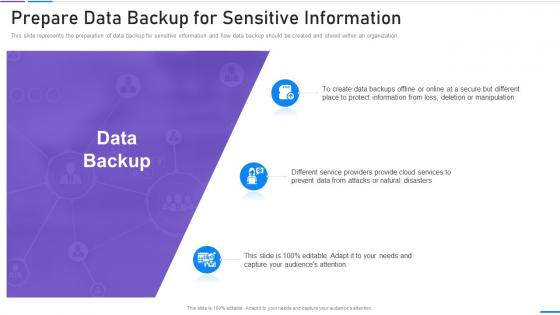 Network Security Prepare Data Backup For Sensitive Information
Network Security Prepare Data Backup For Sensitive InformationThis slide represents the preparation of data backup for sensitive information and how data backup should be created and stored within an organization. Increase audience engagement and knowledge by dispensing information using Network Security Prepare Data Backup For Sensitive Information. This template helps you present information on three stages. You can also present information on Information, Protect, Manipulation, Service using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 30 60 90 Days Plan Information System Security And Risk Administration Plan Ppt Styles Ideas
30 60 90 Days Plan Information System Security And Risk Administration Plan Ppt Styles IdeasIntroducing 30 60 90 Days Plan Information System Security And Risk Administration Plan Ppt Styles Ideas to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on 30 60 90 Days Plan, using this template. Grab it now to reap its full benefits.
-
 About Us Information System Security And Risk Administration Plan Ppt Styles Gallery
About Us Information System Security And Risk Administration Plan Ppt Styles GalleryIncrease audience engagement and knowledge by dispensing information using About Us Information System Security And Risk Administration Plan Ppt Styles Gallery. This template helps you present information on three stages. You can also present information on Target Audiences, Creative, Value Clients using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Agenda For Information System Security And Risk Administration Plan Ppt Styles Model
Agenda For Information System Security And Risk Administration Plan Ppt Styles ModelIntroducing Agenda For Information System Security And Risk Administration Plan Ppt Styles Model to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Information System Security, Current Information Security, Information Security Risks, using this template. Grab it now to reap its full benefits.
-
 Analysing The Impact Of Security Threats Information System Security And Risk Administration Plan
Analysing The Impact Of Security Threats Information System Security And Risk Administration PlanIncrease audience engagement and knowledge by dispensing information using Analysing The Impact Of Security Threats Information System Security And Risk Administration Plan. This template helps you present information on one stages. You can also present information on Security Threats, Malware, Phishing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
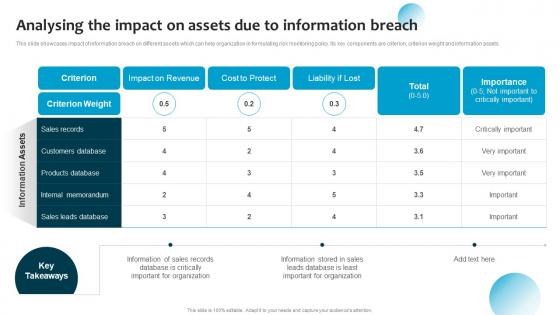 Analysing The Impact On Assets Information Breach Information System Security And Risk Administration
Analysing The Impact On Assets Information Breach Information System Security And Risk AdministrationThis slide showcases impact of information breach on different assets which can help organization in formulating risk monitoring policy. Its key components are criterion, criterion weight and information assets. Deliver an outstanding presentation on the topic using this Analysing The Impact On Assets Information Breach Information System Security And Risk Administration. Dispense information and present a thorough explanation of Cost To Protect, Sales Records, Products Database using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
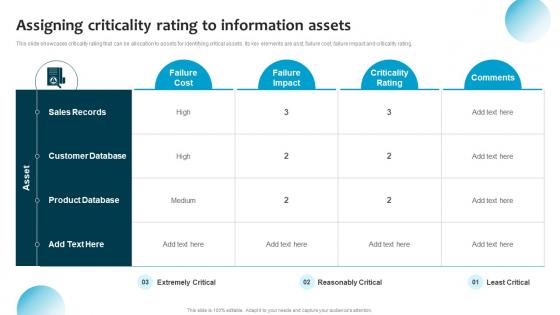 Assigning Criticality Rating To Assets Information System Security And Risk Administration Plan
Assigning Criticality Rating To Assets Information System Security And Risk Administration PlanThis slide showcases criticality rating that can be allocation to assets for identifying critical assets. Its key elements are asst, failure cost, failure impact and criticality rating. Deliver an outstanding presentation on the topic using this Assigning Criticality Rating To Assets Information System Security And Risk Administration Plan. Dispense information and present a thorough explanation of Failure Cost, Criticality Rating, Product Database using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Budget For Information Security Risk Management Information System Security And Risk Administration
Budget For Information Security Risk Management Information System Security And Risk AdministrationThis slide showcases budget that can should be allocated for different information security risk management activities. It provides information about employees training, software implementation, risk monitoring and data backup. Introducing Budget For Information Security Risk Management Information System Security And Risk Administration to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Training Of Employees, Software Implementation, Risk Monitoring, using this template. Grab it now to reap its full benefits.
-
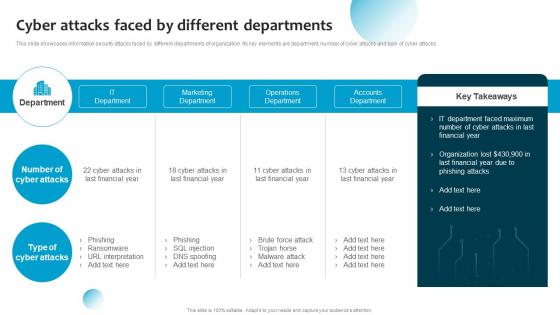 Cyber Attacks Faced By Different Departments Information System Security And Risk Administration Plan
Cyber Attacks Faced By Different Departments Information System Security And Risk Administration PlanThis slide showcases information security attacks faced by different departments of organization. Its key elements are department, number of cyber attacks and type of cyber attacks. Present the topic in a bit more detail with this Cyber Attacks Faced By Different Departments Information System Security And Risk Administration Plan. Use it as a tool for discussion and navigation on It Department, Marketing Department, Operations Department. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
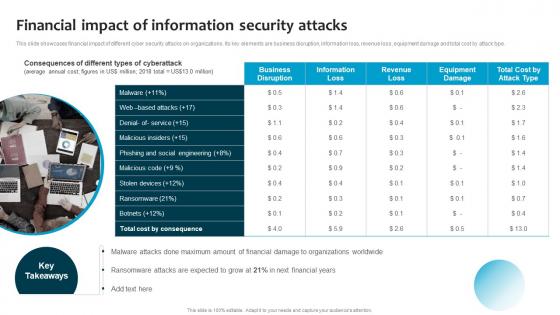 Financial Impact Of Information Security Attacks Information System Security And Risk Administration Plan
Financial Impact Of Information Security Attacks Information System Security And Risk Administration PlanThis slide showcases financial impact of different cyber security attacks on organizations. Its key elements are business disruption, information loss, revenue loss, equipment damage and total cost by attack type. Introducing Financial Impact Of Information Security Attacks Information System Security And Risk Administration Plan to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Social Engineering, Web Based Attacks, Stolen Devices, using this template. Grab it now to reap its full benefits.
-
 Framework For Information Security Risk Management Ppt Powerpoint Presentation File Topics
Framework For Information Security Risk Management Ppt Powerpoint Presentation File TopicsThis slide showcases framework that can help organization to formulate plan for information security risk management. Its key elements are identify risks, analyse risks, evaluate and treat risks. Deliver an outstanding presentation on the topic using this Framework For Information Security Risk Management Ppt Powerpoint Presentation File Topics. Dispense information and present a thorough explanation of Identify Risks, Analyze Risks, Evaluate Risks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Icons Slide For Information System Security And Risk Administration Plan Ppt Styles Summary
Icons Slide For Information System Security And Risk Administration Plan Ppt Styles SummaryDeliver an outstanding presentation on the topic using this Icons Slide For Information System Security And Risk Administration Plan Ppt Styles Summary. Dispense information and present a thorough explanation of Icons Slide using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
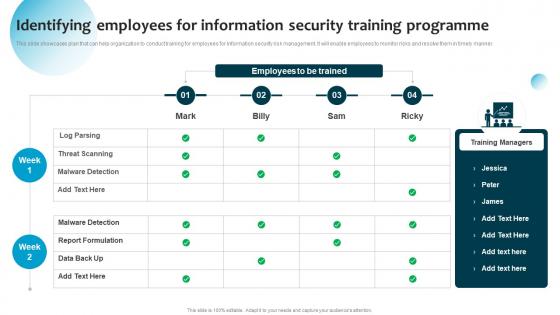 Identifying Employees For Information Security Training Information System Security And Risk Administration
Identifying Employees For Information Security Training Information System Security And Risk AdministrationThis slide showcases plan that can help organization to conduct training for employees for information security risk management. It will enable employees to monitor risks and resolve them in timely manner. Present the topic in a bit more detail with this Identifying Employees For Information Security Training Information System Security And Risk Administration. Use it as a tool for discussion and navigation on Threat Scanning, Malware Detection, Report Formulation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
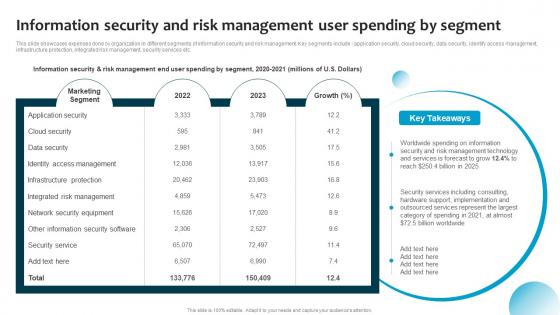 Information Security And Risk Management User Spending By Segment Information System Security And Risk
Information Security And Risk Management User Spending By Segment Information System Security And RiskThis slide showcases expenses done by organization in different segments of information security and risk management. Key segments include application security, cloud security, data security, identify access management, infrastructure protection, integrated risk management, security services etc. Present the topic in a bit more detail with this Information Security And Risk Management User Spending By Segment Information System Security And Risk. Use it as a tool for discussion and navigation on Marketing Segment, Network Security Equipment, Integrated Risk Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
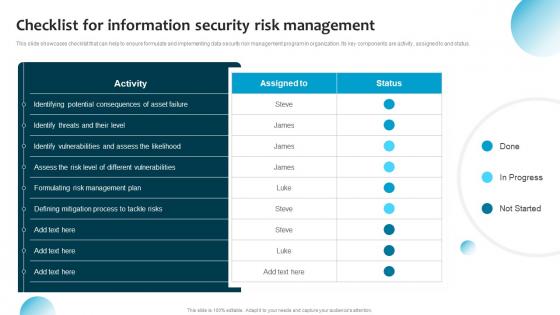 Information System Security And Risk Administration Plan Checklist For Information Security Risk
Information System Security And Risk Administration Plan Checklist For Information Security RiskThis slide showcases checklist that can help to ensure formulate and implementing data security risk management program in organization. Its key components are activity, assigned to and status. Deliver an outstanding presentation on the topic using this Information System Security And Risk Administration Plan Checklist For Information Security Risk. Dispense information and present a thorough explanation of Process To Tackle Risks, Identify Vulnerabilities, Formulating Risk Management Plan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 KPIS To Measure Information Security Risk Information System Security And Risk Administration Plan
KPIS To Measure Information Security Risk Information System Security And Risk Administration PlanThis slide showcases KPIs that can help organization to measure the impact of cybersecurity risk management programme. It showcases estimated figures before and after implementation of plan. Deliver an outstanding presentation on the topic using this KPIS To Measure Information Security Risk Information System Security And Risk Administration Plan. Dispense information and present a thorough explanation of Intrusion Attempts, Risk Management Programme, Cost Per Incident using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Matrix For Threat Solution And Risk Management Information System Security And Risk Administration Plan
Matrix For Threat Solution And Risk Management Information System Security And Risk Administration PlanThis slide showcases matrix that can help organization to formulate solutions for different types of information security attacks. It can help organization to mitigate the risks and safeguard information in case of any attack. Deliver an outstanding presentation on the topic using this Matrix For Threat Solution And Risk Management Information System Security And Risk Administration Plan. Dispense information and present a thorough explanation of Monitor Database Activity, Validate Database Protocols, Capture Detailed Transactions using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Meet Our Team Information System Security And Risk Administration Plan Ppt Styles Visual Aids
Meet Our Team Information System Security And Risk Administration Plan Ppt Styles Visual AidsIntroducing Meet Our Team Information System Security And Risk Administration Plan Ppt Styles Visual Aids to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Meet Our Team, using this template. Grab it now to reap its full benefits.
-
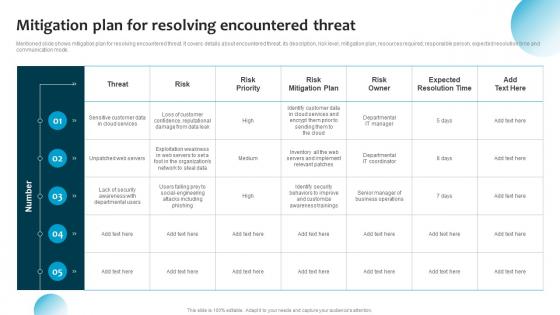 Mitigation Plan For Resolving Encountered Threat Information System Security And Risk Administration Plan
Mitigation Plan For Resolving Encountered Threat Information System Security And Risk Administration PlanMentioned slide shows mitigation plan for resolving encountered threat. It covers details about encountered threat, its description, risk level, mitigation plan, resources required, responsible person, expected resolution time and communication mode. Present the topic in a bit more detail with this Mitigation Plan For Resolving Encountered Threat Information System Security And Risk Administration Plan. Use it as a tool for discussion and navigation on Risk Mitigation Plan, Customer Data, Web Servers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
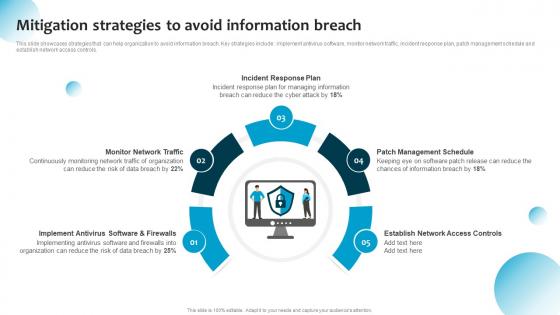 Mitigation Strategies To Avoid Information Breach Information System Security And Risk Administration Plan
Mitigation Strategies To Avoid Information Breach Information System Security And Risk Administration PlanThis slide showcases strategies that can help organization to avoid information breach. Key strategies include implement antivirus software, monitor network traffic, incident response plan, patch management schedule and establish network access controls. Increase audience engagement and knowledge by dispensing information using Mitigation Strategies To Avoid Information Breach Information System Security And Risk Administration Plan. This template helps you present information on five stages. You can also present information on Incident Response Plan, Monitor Network Traffic, Patch Management Schedule using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Mitigation Strategies To Tackle Information Security Information System Security And Risk Administration Plan
Mitigation Strategies To Tackle Information Security Information System Security And Risk Administration PlanThis slide showcases mitigation strategies that can help organization to tackle the cybersecurity attacks. It can help organization to minimize the financial loss and main reputation of business. Introducing Mitigation Strategies To Tackle Information Security Information System Security And Risk Administration Plan to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Malware, Phishing, SQL Injection, using this template. Grab it now to reap its full benefits.
-
 Our Mission Information System Security And Risk Administration Plan Ppt Styles Visuals
Our Mission Information System Security And Risk Administration Plan Ppt Styles VisualsIncrease audience engagement and knowledge by dispensing information using Our Mission Information System Security And Risk Administration Plan Ppt Styles Visuals. This template helps you present information on three stages. You can also present information on Vision, Mission, Goal using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Post It Notes Information System Security And Risk Administration Plan Ppt Styles Background
Post It Notes Information System Security And Risk Administration Plan Ppt Styles BackgroundIntroducing Post It Notes Information System Security And Risk Administration Plan Ppt Styles Background to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Post It Notes, using this template. Grab it now to reap its full benefits.
-
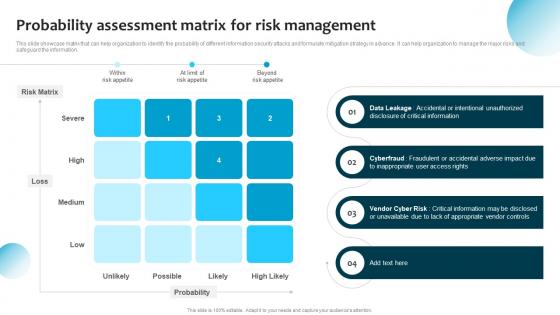 Probability Assessment Matrix For Risk Management Information System Security And Risk Administration Plan
Probability Assessment Matrix For Risk Management Information System Security And Risk Administration PlanThis slide showcase matrix that can help organization to identify the probability of different information security attacks and formulate mitigation strategy in advance. It can help organization to manage the major risks and safeguard the information. Deliver an outstanding presentation on the topic using this Probability Assessment Matrix For Risk Management Information System Security And Risk Administration Plan. Dispense information and present a thorough explanation of Risk Matrix, Data Leakage, Vendor Cyber Risk using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Process For Information Security Risk Assessment Information System Security And Risk Administration Plan
Process For Information Security Risk Assessment Information System Security And Risk Administration PlanThis slide showcases process that can help organization to perform information security risk assessment. It can help identify security threats and allocate vulnerability rating to information assets. Increase audience engagement and knowledge by dispensing information using Process For Information Security Risk Assessment Information System Security And Risk Administration Plan. This template helps you present information on four stages. You can also present information on Security Threats, Information Assets, Risk Associated using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Quotes Information System Security And Risk Administration Plan Ppt Styles Graphics Download
Quotes Information System Security And Risk Administration Plan Ppt Styles Graphics DownloadIntroducing Quotes Information System Security And Risk Administration Plan Ppt Styles Graphics Download to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Quotes, using this template. Grab it now to reap its full benefits.
-
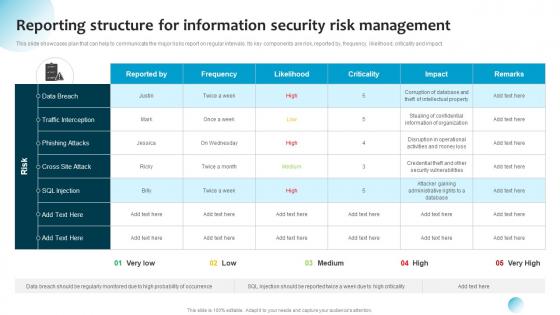 Reporting Structure For Information Security Risk Information System Security And Risk Administration Plan
Reporting Structure For Information Security Risk Information System Security And Risk Administration PlanThis slide showcases plan that can help to communicate the major risks report on regular intervals. Its key components are risk, reported by, frequency, likelihood, criticality and impact. Present the topic in a bit more detail with this Reporting Structure For Information Security Risk Information System Security And Risk Administration Plan. Use it as a tool for discussion and navigation on Data Breach, Sql Injection, Data Breach . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Roadmap Information System Security And Risk Administration Plan Ppt Styles Background Designs
Roadmap Information System Security And Risk Administration Plan Ppt Styles Background DesignsIncrease audience engagement and knowledge by dispensing information using Roadmap Information System Security And Risk Administration Plan Ppt Styles Background Designs. This template helps you present information on four stages. You can also present information on Roadmap using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Steps For Information Security Risk Management Ppt Powerpoint Presentation File Aids
Steps For Information Security Risk Management Ppt Powerpoint Presentation File AidsThis slide steps which can help organization to implement information security risk management program in organization. Its key steps are identify, protect, detect and respond. Increase audience engagement and knowledge by dispensing information using Steps For Information Security Risk Management Ppt Powerpoint Presentation File Aids. This template helps you present information on five stages. You can also present information on Protect, Respond, Detect using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Swot Analysis Information System Security And Risk Administration Plan Ppt Styles Clipart
Swot Analysis Information System Security And Risk Administration Plan Ppt Styles ClipartIncrease audience engagement and knowledge by dispensing information using Swot Analysis Information System Security And Risk Administration Plan Ppt Styles Clipart. This template helps you present information on four stages. You can also present information on SWOT Analysis using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Table Of Contents For Information System Security And Risk Administration Plan Ppt Styles Designs
Table Of Contents For Information System Security And Risk Administration Plan Ppt Styles DesignsIntroducing Table Of Contents For Information System Security And Risk Administration Plan Ppt Styles Designs to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Information Security, Risk Management Plan, Risk Assessment, using this template. Grab it now to reap its full benefits.
-
 Table Of Contents Information System Security And Risk Administration Plan Ppt Styles Example
Table Of Contents Information System Security And Risk Administration Plan Ppt Styles ExamplePresent the topic in a bit more detail with this Table Of Contents Information System Security And Risk Administration Plan Ppt Styles Example. Use it as a tool for discussion and navigation on Security Capabilities, Security Industry, Security Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Threat Identification And Vulnerability Assessment For Information System Security And Risk Administration Plan
Threat Identification And Vulnerability Assessment For Information System Security And Risk Administration PlanThis slide showcases identification of threat and assessment of vulnerability and can help organization to identify the information breach risk. Its key components are vulnerability, severity, threat, threat source, likelihood, impact and risk rating. Deliver an outstanding presentation on the topic using this Threat Identification And Vulnerability Assessment For Information System Security And Risk Administration Plan. Dispense information and present a thorough explanation of Vulnerability Severity, Threat Source, Risk Rating using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
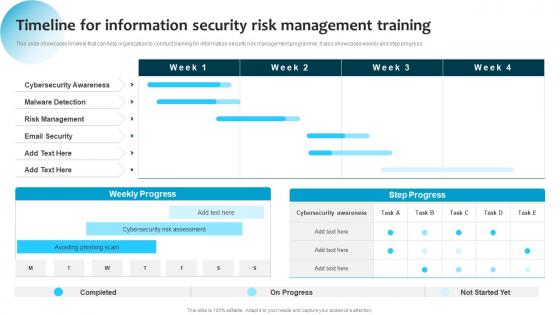 Timeline For Information Security Risk Management Training Ppt Professional Layout Ideas
Timeline For Information Security Risk Management Training Ppt Professional Layout IdeasThis slide showcases timeline that can help organization to conduct training for information security risk management programme. It also showcases weekly and step progress. Present the topic in a bit more detail with this Timeline For Information Security Risk Management Training Ppt Professional Layout Ideas. Use it as a tool for discussion and navigation on Risk Management, Email Security, Cybersecurity Awareness. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Timeline Information System Security And Risk Administration Plan Ppt Professional Master Slide
Timeline Information System Security And Risk Administration Plan Ppt Professional Master SlideIncrease audience engagement and knowledge by dispensing information using Timeline Information System Security And Risk Administration Plan Ppt Professional Master Slide. This template helps you present information on seven stages. You can also present information on Timeline using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.



