Powerpoint Templates and Google slides for It Infrastructure Security Budget
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Strategic Plan To Secure IT Infrastructure Powerpoint Presentation Slides Strategy CD V
Strategic Plan To Secure IT Infrastructure Powerpoint Presentation Slides Strategy CD VDeliver this complete deck to your team members and other collaborators. Encompassed with stylized slides presenting various concepts, this Strategic Plan To Secure IT Infrastructure Powerpoint Presentation Slides Strategy CD V is the best tool you can utilize. Personalize its content and graphics to make it unique and thought-provoking. All the seventy seven slides are editable and modifiable, so feel free to adjust them to your business setting. The font, color, and other components also come in an editable format making this PPT design the best choice for your next presentation. So, download now.
-
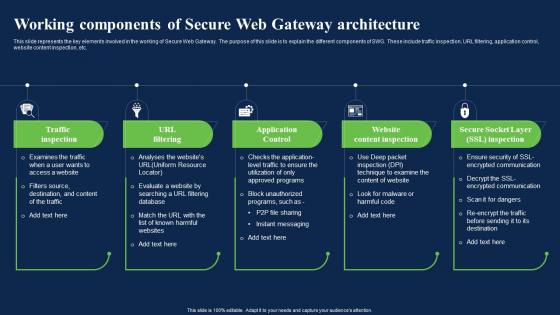 Working Components Of Secure Web Gateway Architecture Network Security Using Secure Web Gateway
Working Components Of Secure Web Gateway Architecture Network Security Using Secure Web GatewayThis slide represents the key elements involved in the working of Secure Web Gateway. The purpose of this slide is to explain the different components of SWG. These include traffic inspection, URL filtering, application control, website content inspection, etc. Increase audience engagement and knowledge by dispensing information using Working Components Of Secure Web Gateway Architecture Network Security Using Secure Web Gateway. This template helps you present information on five stages. You can also present information on Application Control, Website Content Inspection, Gateway Architecture using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
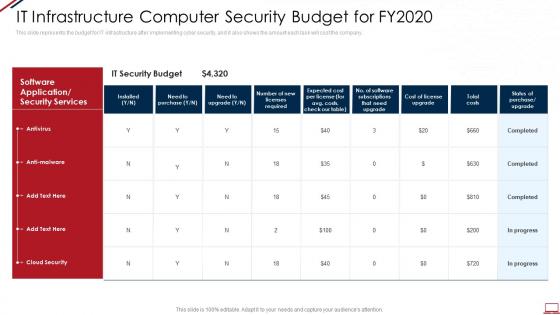 Computer system security it infrastructure computer security budget for fy2020
Computer system security it infrastructure computer security budget for fy2020This slide represents the budget for IT infrastructure after implementing cyber security, and it also shows the amount each task will cost the company. Present the topic in a bit more detail with this Computer System Security It Infrastructure Computer Security Budget For Fy2020. Use it as a tool for discussion and navigation on Cost, IT Security Budget, Software Application Or Security Services, Antivirus, Anti Malware. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
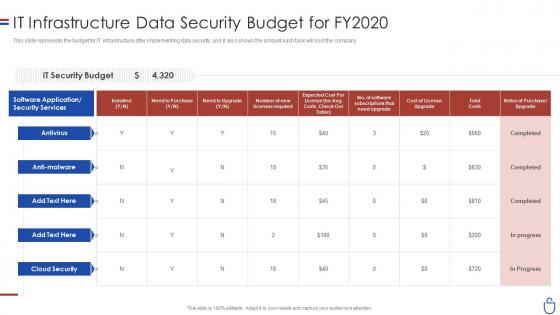 Data security it infrastructure data security budget for fy2020
Data security it infrastructure data security budget for fy2020This slide represents the budget for IT infrastructure after implementing data security, and it also shows the amount each task will cost the company. Present the topic in a bit more detail with this Data Security IT Infrastructure Data Security Budget For FY2020. Use it as a tool for discussion and navigation on IT Security Budget, Need To Purchase, Total Cost, Cost License Upgrade. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
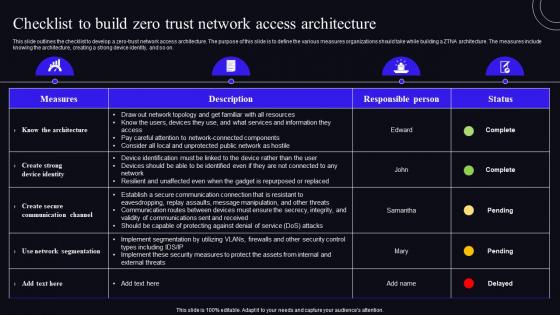 Checklist To Build Zero Trust Network Access Architecture Zero Trust Security Model
Checklist To Build Zero Trust Network Access Architecture Zero Trust Security ModelThis slide outlines the checklist to develop a zero-trust network access architecture. The purpose of this slide is to define the various measures organizations should take while building a ZTNA architecture. The measures include knowing the architecture, creating a strong device identity, and so on. Deliver an outstanding presentation on the topic using this Checklist To Build Zero Trust Network Access Architecture Zero Trust Security Model. Dispense information and present a thorough explanation of Architecture, Measures, Organizations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
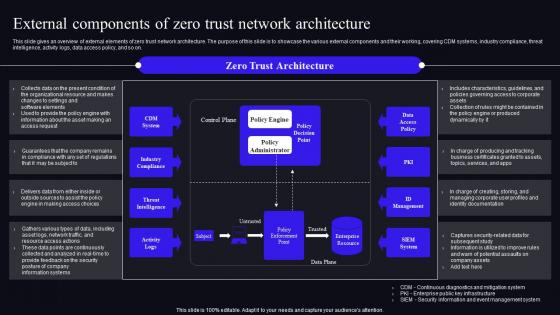 External Components Of Zero Trust Network Architecture Zero Trust Security Model
External Components Of Zero Trust Network Architecture Zero Trust Security ModelThis slide gives an overview of external elements of zero trust network architecture. The purpose of this slide is to showcase the various external components and their working, covering CDM systems, industry compliance, threat intelligence, activity logs, data access policy, and so on. Deliver an outstanding presentation on the topic using this External Components Of Zero Trust Network Architecture Zero Trust Security Model. Dispense information and present a thorough explanation of Architecture, Documentation, Potential using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
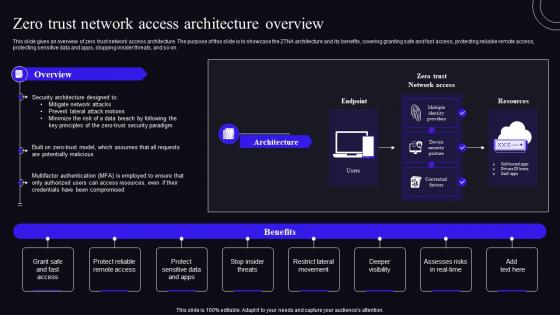 F1586 Zero Trust Network Access Architecture Overview Zero Trust Security Model
F1586 Zero Trust Network Access Architecture Overview Zero Trust Security ModelThis slide gives an overview of zero trust network access architecture. The purpose of this slide is to showcase the ZTNA architecture and its benefits, covering granting safe and fast access, protecting reliable remote access, protecting sensitive data and apps, stopping insider threats, and so on. Present the topic in a bit more detail with this F1586 Zero Trust Network Access Architecture Overview Zero Trust Security Model. Use it as a tool for discussion and navigation on Resources, Architecture, Overview. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
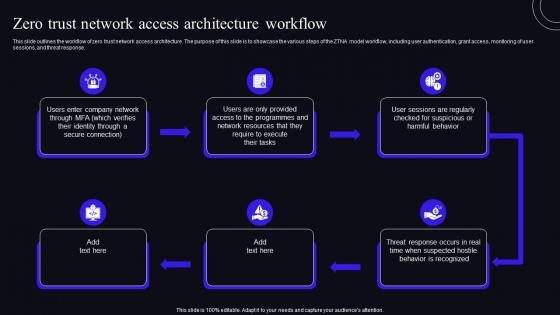 F1587 Zero Trust Network Access Architecture Workflow Zero Trust Security Model
F1587 Zero Trust Network Access Architecture Workflow Zero Trust Security ModelThis slide outlines the workflow of zero trust network access architecture. The purpose of this slide is to showcase the various steps of the ZTNA model workflow, including user authentication, grant access, monitoring of user sessions, and threat response. Increase audience engagement and knowledge by dispensing information using F1587 Zero Trust Network Access Architecture Workflow Zero Trust Security Model. This template helps you present information on six stages. You can also present information on Architecture, Workflow, Resources using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
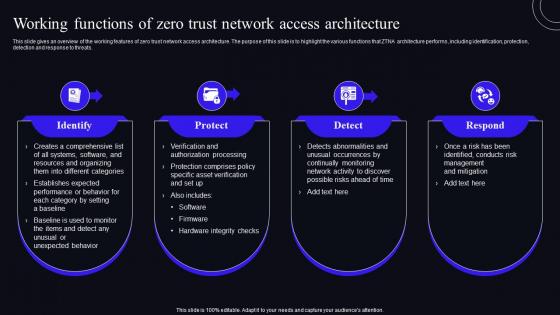 Working Functions Of Zero Trust Network Access Architecture Zero Trust Security Model
Working Functions Of Zero Trust Network Access Architecture Zero Trust Security ModelThis slide gives an overview of the working features of zero trust network access architecture. The purpose of this slide is to highlight the various functions that ZTNA architecture performs, including identification, protection, detection and response to threats. Introducing Working Functions Of Zero Trust Network Access Architecture Zero Trust Security Model to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Architecture, Abnormalities, Processing, using this template. Grab it now to reap its full benefits.
-
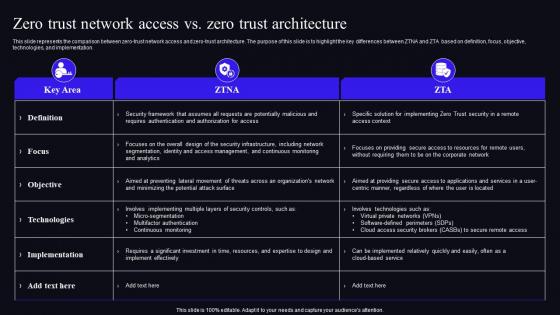 Zero Trust Network Access Vs Zero Trust Architecture Zero Trust Security Model
Zero Trust Network Access Vs Zero Trust Architecture Zero Trust Security ModelThis slide represents the comparison between zero-trust network access and zero-trust architecture. The purpose of this slide is to highlight the key differences between ZTNA and ZTA based on definition, focus, objective, technologies, and implementation. Deliver an outstanding presentation on the topic using this Zero Trust Network Access Vs Zero Trust Architecture Zero Trust Security Model. Dispense information and present a thorough explanation of Architecture, Implementation, Technologies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
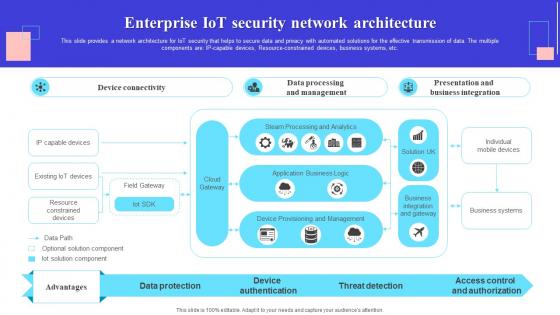 Enterprise IoT Security Network Architecture
Enterprise IoT Security Network ArchitectureThis slide provides a network architecture for IoT security that helps to secure data and privacy with automated solutions for the effective transmission of data. The multiple components are IP capable devices, Resource constrained devices, business systems, etc.Introducing our Enterprise IoT Security Network Architecture set of slides. The topics discussed in these slides are Data Processing, Device Authentication, Business Systems. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 IoT Network Security Architecture Image
IoT Network Security Architecture ImagePresenting our set of slides with IoT Network Security Architecture Image. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Iot Network Security, Architecture Image.
-
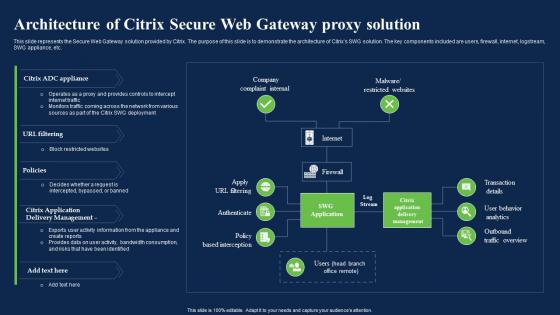 Architecture Of Citrix Secure Web Gateway Proxy Solution Network Security Using Secure Web Gateway
Architecture Of Citrix Secure Web Gateway Proxy Solution Network Security Using Secure Web GatewayThis slide represents the Secure Web Gateway solution provided by Citrix. The purpose of this slide is to demonstrate the architecture of Citrixs SWG solution. The key components included are users, firewall, internet, logstream, SWG appliance, etc. Deliver an outstanding presentation on the topic using this Architecture Of Citrix Secure Web Gateway Proxy Solution Network Security Using Secure Web Gateway. Dispense information and present a thorough explanation of Architecture, Company Complaint Internal, Malware Restricted Websites using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
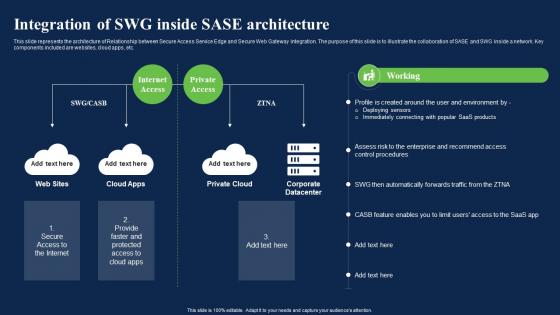 Integration Of Swg Inside Sase Architecture Network Security Using Secure Web Gateway
Integration Of Swg Inside Sase Architecture Network Security Using Secure Web GatewayThis slide represents the architecture of Relationship between Secure Access Service Edge and Secure Web Gateway integration. The purpose of this slide is to illustrate the collaboration of SASE and SWG inside a network. Key components included are websites, cloud apps, etc. Deliver an outstanding presentation on the topic using this Integration Of Swg Inside Sase Architecture Network Security Using Secure Web Gateway. Dispense information and present a thorough explanation of Architecture, Integration, Environment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
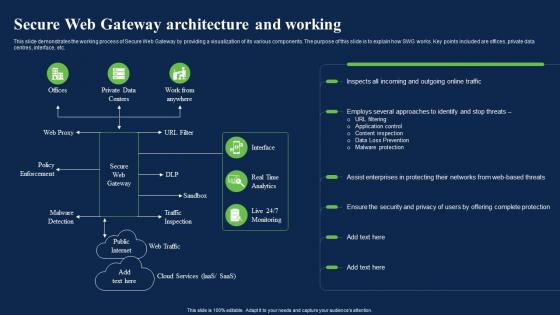 Secure Web Gateway Architecture And Working Network Security Using Secure Web Gateway
Secure Web Gateway Architecture And Working Network Security Using Secure Web GatewayThis slide demonstrates the working process of Secure Web Gateway by providing a visualization of its various components. The purpose of this slide is to explain how SWG works. Key points included are offices, private data centres, interface, etc. Present the topic in a bit more detail with this Secure Web Gateway Architecture And Working Network Security Using Secure Web Gateway. Use it as a tool for discussion and navigation on Architecture, Approaches, Enterprises. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
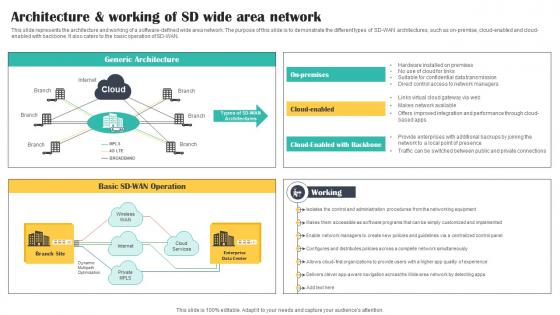 Architecture And Working Of SD Wide Area Network Cloud Security Model
Architecture And Working Of SD Wide Area Network Cloud Security ModelThis slide represents the architecture and working of a software defined wide area network. The purpose of this slide is to demonstrate the different types of SD WAN architectures, such as on premise, cloud enabled and cloud enabled with backbone. It also caters to the basic operation of SD WAN. Increase audience engagement and knowledge by dispensing information using Architecture And Working Of SD Wide Area Network Cloud Security Model. This template helps you present information on three stages. You can also present information on Working, Architecture, Network using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
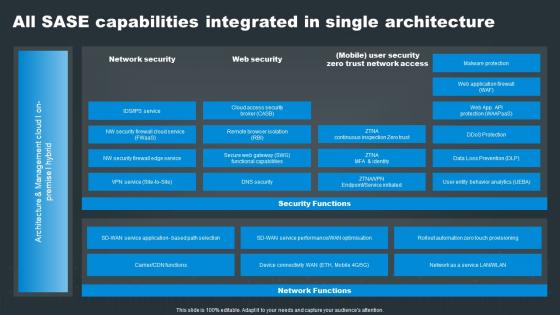 SASE Network Security All SASE Capabilities Integrated In Single Architecture
SASE Network Security All SASE Capabilities Integrated In Single ArchitectureDeliver an outstanding presentation on the topic using this SASE Network Security All SASE Capabilities Integrated In Single Architecture. Dispense information and present a thorough explanation of Network, Security, Access using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
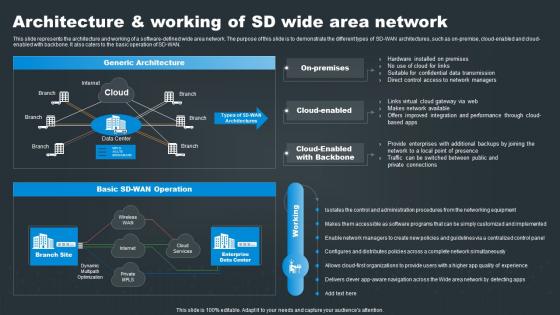 SASE Network Security Architecture And Working Of SD Wide Area Network
SASE Network Security Architecture And Working Of SD Wide Area NetworkThis slide represents the architecture and working of a software defined wide area network. The purpose of this slide is to demonstrate the different types of SD WAN architectures, such as on premise, cloud enabled and cloud enabled with backbone. It also caters to the basic operation of SD WAN. Present the topic in a bit more detail with this SASE Network Security Architecture And Working Of SD Wide Area Network. Use it as a tool for discussion and navigation on Architecture, Operation, Network. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
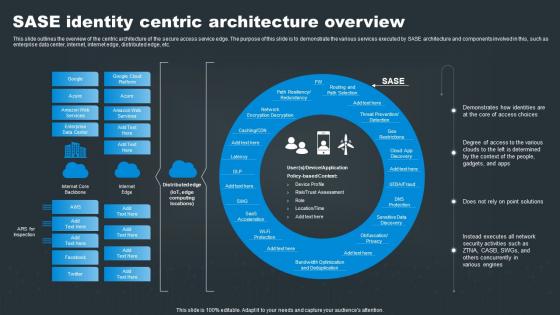 SASE Network Security SASE Identity Centric Architecture Overview
SASE Network Security SASE Identity Centric Architecture OverviewThis slide outlines the overview of the centric architecture of the secure access service edge. The purpose of this slide is to demonstrate the various services executed by SASE architecture and components involved in this, such as enterprise data center, internet, internet edge, distributed edge, etc. Present the topic in a bit more detail with this SASE Network Security SASE Identity Centric Architecture Overview. Use it as a tool for discussion and navigation on Identities, Solutions, Activities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
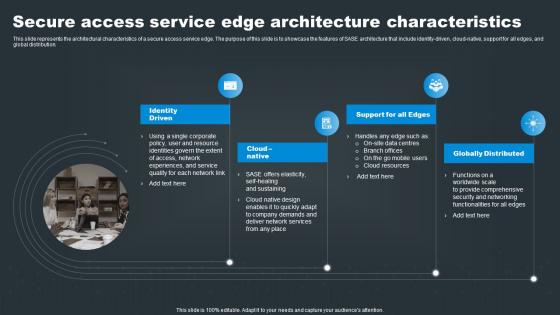 Secure Access Service Edge Architecture Characteristics SASE Network Security
Secure Access Service Edge Architecture Characteristics SASE Network SecurityThis slide represents the architectural characteristics of a secure access service edge. The purpose of this slide is to showcase the features of SASE architecture that include identity driven, cloud native, support for all edges, and global distribution. Introducing Secure Access Service Edge Architecture Characteristics SASE Network Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Native, Support, Globally, using this template. Grab it now to reap its full benefits.
-
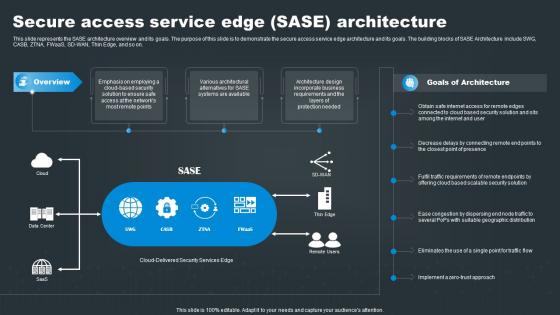 Secure Access Service Edge SASE Architecture SASE Network Security
Secure Access Service Edge SASE Architecture SASE Network SecurityThis slide represents the SASE architecture overview and its goals. The purpose of this slide is to demonstrate the secure access service edge architecture and its goals. The building blocks of SASE Architecture include SWG, CASB, ZTNA, FWaaS, SD WAN, Thin Edge, and so on. Present the topic in a bit more detail with this Secure Access Service Edge SASE Architecture SASE Network Security. Use it as a tool for discussion and navigation on Connected, Presence, Scalable. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Icon For Network Security Through Zero Trust Architecture
Icon For Network Security Through Zero Trust ArchitecturePresenting our set of slides with Icon For Network Security Through Zero Trust Architecture. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Icon Network Security, Zero Trust Architecture.
-
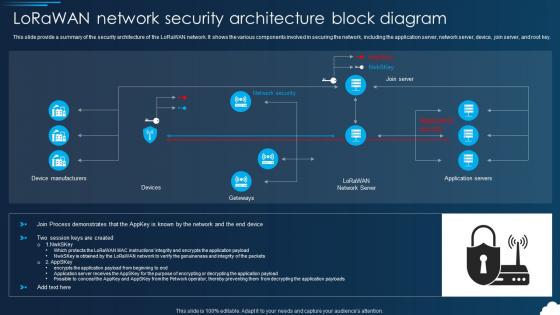 Lorawan Lorawan Network Security Architecture Block Diagram
Lorawan Lorawan Network Security Architecture Block DiagramThis slide provide a summary of the security architecture of the LoRaWAN network. It shows the various components involved in securing the network, including the application server, network server, device, join server, and root key. Present the topic in a bit more detail with this Lorawan Lorawan Network Security Architecture Block Diagram. Use it as a tool for discussion and navigation on Device Manufacturers, Architecture, Application Servers . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
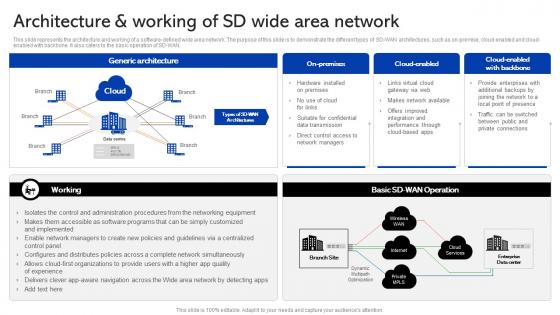 Sase Security Architecture And Working Of Sd Wide Area Network
Sase Security Architecture And Working Of Sd Wide Area NetworkThis slide represents the architecture and working of a software-defined wide area network. The purpose of this slide is to demonstrate the different types of SD-WAN architectures, such as on-premise, cloud-enabled and cloud-enabled with backbone. It also caters to the basic operation of SD-WAN. Present the topic in a bit more detail with this Sase Security Architecture And Working Of Sd Wide Area Network. Use it as a tool for discussion and navigation on Architecture, Enterprises, Connections. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
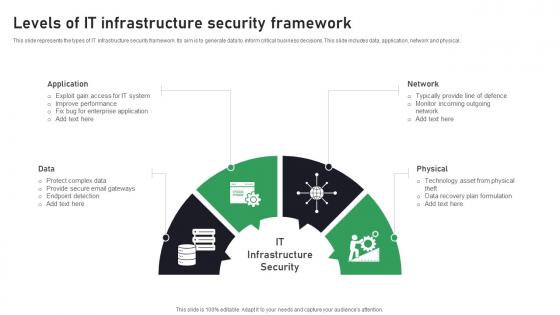 Levels Of IT Infrastructure Security Framework
Levels Of IT Infrastructure Security FrameworkThis slide represents the types of IT infrastructure security framework. Its aim is to generate data to inform critical business decisions. This slide includes data, application, network and physical. Introducing our premium set of slides with Levels Of IT Infrastructure Security Framework. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Protect, Secure, Application. So download instantly and tailor it with your information.
-
 Types Of Threats In IT Infrastructure Security
Types Of Threats In IT Infrastructure SecurityThis slide showcases the common threats faced in infrastructure security. Its aim is to identify threats and eliminate them. This slide includes phishing, ransomware, botnet and physical theft. Presenting our set of slides with Types Of Threats In IT Infrastructure Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Infrastructure, Personal, Exploitation.
-
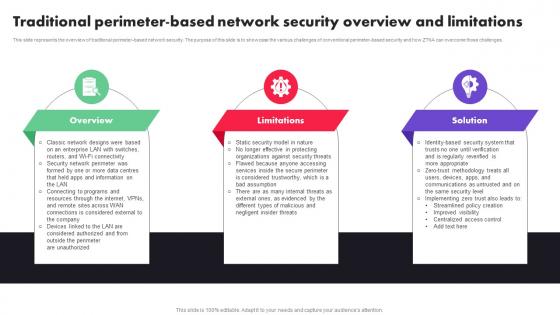 Zero Trust Architecture Traditional Perimeter Based Network Security Overview And Limitations Ppt File Guide
Zero Trust Architecture Traditional Perimeter Based Network Security Overview And Limitations Ppt File GuideThis slide represents the overview of traditional perimeter-based network security. The purpose of this slide is to showcase the various challenges of conventional perimeter-based security and how ZTNA can overcome those challenges. Introducing Zero Trust Architecture Traditional Perimeter Based Network Security Overview And Limitations Ppt File Guide to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Overview, Limitations, Solution, using this template. Grab it now to reap its full benefits.
-
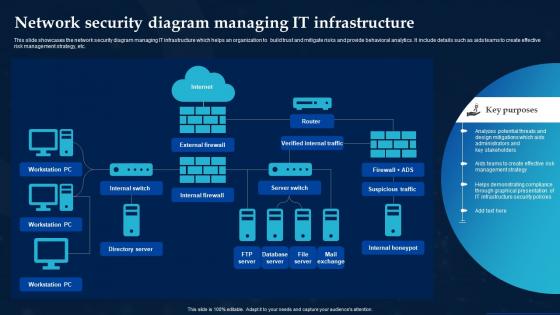 Network Security Diagram Managing It Infrastructure
Network Security Diagram Managing It InfrastructureThis slide showcases the network security diagram managing IT infrastructure which helps an organization to build trust and mitigate risks and provide behavioral analytics. It include details such as aids teams to create effective risk management strategy, etc. Introducing our Network Security Diagram Managing It Infrastructure set of slides. The topics discussed in these slides are Internal Switch, Internal Firewall, Server Switch. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
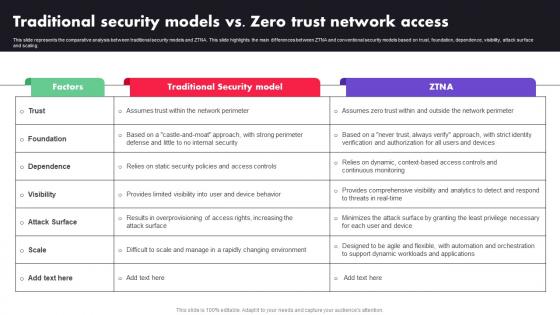 M72 Traditional Security Models Vs Zero Trust Network Access Zero Trust Architecture ZTA
M72 Traditional Security Models Vs Zero Trust Network Access Zero Trust Architecture ZTAThis slide represents the comparative analysis between traditional security models and ZTNA. This slide highlights the main differences between ZTNA and conventional security models based on trust, foundation, dependence, visibility, attack surface and scaling. Deliver an outstanding presentation on the topic using this M72 Traditional Security Models Vs Zero Trust Network Access Zero Trust Architecture ZTA. Dispense information and present a thorough explanation of Factors, Traditional Security Model, ZTNA using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
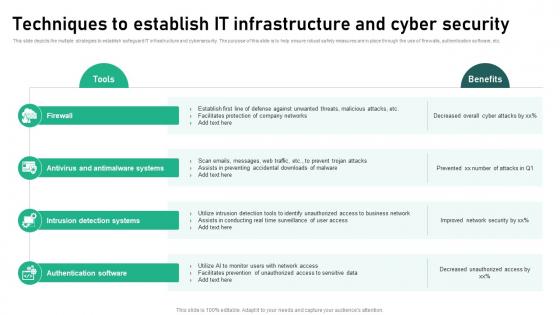 Techniques To Establish It Infrastructure And Cyber Security
Techniques To Establish It Infrastructure And Cyber SecurityThis slide depicts the multiple strategies to establish safeguard IT infrastructure and cybersecurity. The purpose of this slide is to help ensure robust safety measures are in place through the use of firewalls, authentication software, etc. Presenting our set of slides with Techniques To Establish It Infrastructure And Cyber Security This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Firewall, Antivirus And Antimalware Systems
-
 Types Of Cyber Security Measures To Safeguard It Infrastructure
Types Of Cyber Security Measures To Safeguard It InfrastructureThis slide depicts the kinds of cyber security approaches to safeguard companys IT infrastructure. The purpose of this slide is to help the business improve its cybersecurity measures in order to prevent online attacks. It includes operational security, network security, etc. Introducing our premium set of slides with Types Of Cyber Security Measures To Safeguard It Infrastructure Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Operational Security, Information Security, Network Security So download instantly and tailor it with your information.
-
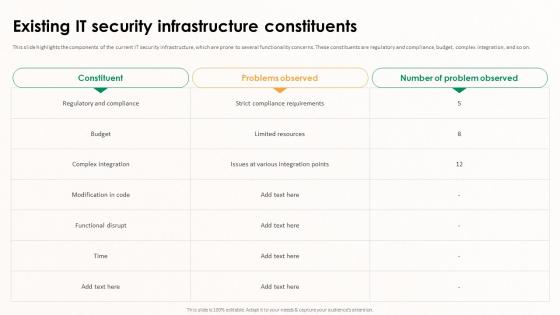 Implementing Effective Software Testing Existing IT Security Infrastructure Constituents
Implementing Effective Software Testing Existing IT Security Infrastructure ConstituentsThis slide highlights the components of the current IT security infrastructure, which are prone to several functionality concerns. These constituents are regulatory and compliance, budget, complex integration, and so on. Present the topic in a bit more detail with this Implementing Effective Software Testing Existing IT Security Infrastructure Constituents. Use it as a tool for discussion and navigation on Complex Integration, Strict Compliance Requirements, Functional Disrupt, IT Security Infrastructure Constituents. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
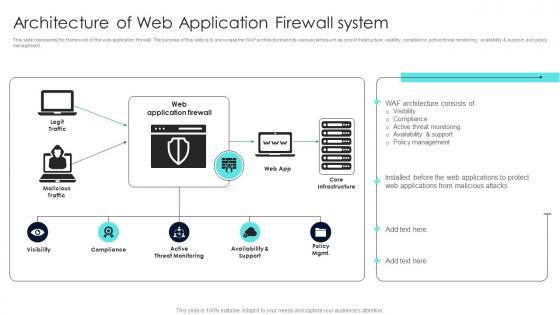 Firewall Network Security Architecture Of Web Application Firewall System
Firewall Network Security Architecture Of Web Application Firewall SystemThis slide represents the framework of the web application firewall. The purpose of this slide is to showcase the WAF architecture and its various parts such as core infrastructure, visibility, compliance, active threat monitoring, availability and support, and policy management. Present the topic in a bit more detail with this Firewall Network Security Architecture Of Web Application Firewall System Use it as a tool for discussion and navigation on Policy Management, Malicious Attacks This template is free to edit as deemed fit for your organization. Therefore download it now.
-
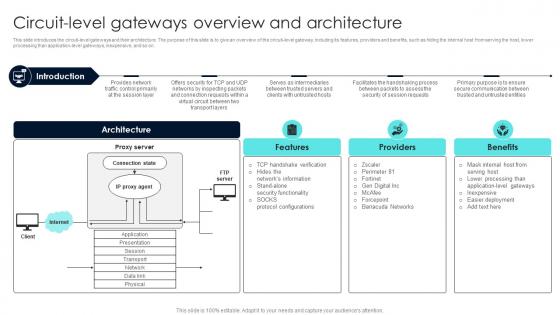 Firewall Network Security Circuit Level Gateways Overview And Architecture
Firewall Network Security Circuit Level Gateways Overview And ArchitectureThis slide introduces the circuit-level gateways and their architecture. The purpose of this slide is to give an overview of the circuit-level gateway, including its features, providers and benefits, such as hiding the internal host from serving the host, lower processing than application-level gateways, inexpensive, and so on. Introducing Firewall Network Security Circuit Level Gateways Overview And Architecture to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Features, Providers, Benefits using this template. Grab it now to reap its full benefits.
-
 Application Security Implementation Plan Existing IT Security Infrastructure Threats
Application Security Implementation Plan Existing IT Security Infrastructure ThreatsThis slide highlights the components of the current IT security infrastructure, which are prone to several functionality concerns. Deliver an outstanding presentation on the topic using this Application Security Implementation Plan Existing IT Security Infrastructure Threats. Dispense information and present a thorough explanation of Broken Authentication, Cross Site Scripting, Denial Of Service, Infrastructure Threats using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
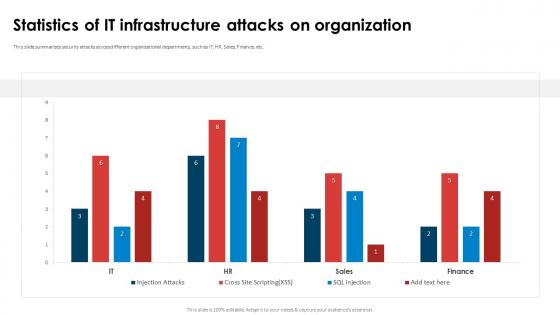 Application Security Implementation Plan Statistics Of It Infrastructure Attacks On Organization
Application Security Implementation Plan Statistics Of It Infrastructure Attacks On OrganizationThis slide summarizes security attacks across different organizational departments, such as IT, HR, Sales, Finance, etc. Deliver an outstanding presentation on the topic using this Application Security Implementation Plan Statistics Of IT Infrastructure Attacks On Organization. Dispense information and present a thorough explanation of Statistics Of IT Infrastructure, Attacks On Organization, Organizational Departments, Finance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Implementing Effective Tokenization Existing IT Security Infrastructure Threats
Implementing Effective Tokenization Existing IT Security Infrastructure ThreatsThis slide highlights the components of the current IT security infrastructure, which are prone to several functionality concerns. Present the topic in a bit more detail with this Implementing Effective Tokenization Existing IT Security Infrastructure Threats. Use it as a tool for discussion and navigation on Compliance Challenges, Resource Intensiveness, Faced Security Vulnerabilities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
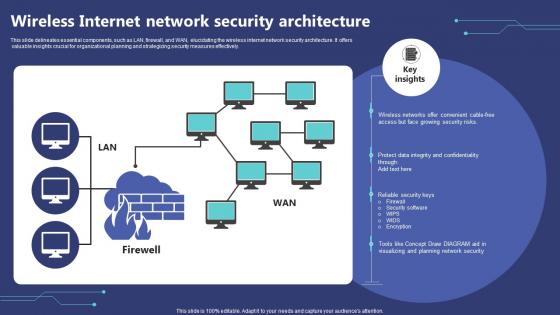 Wireless Internet Network Security Architecture
Wireless Internet Network Security ArchitectureThis slide delineates essential components, such as LAN, firewall, and WAN, elucidating the wireless internet network security architecture. It offers valuable insights crucial for organizational planning and strategizing security measures effectively. Introducing our Wireless Internet Network Security Architecture set of slides. The topics discussed in these slides are Network Security, Architecture, Confidentiality. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
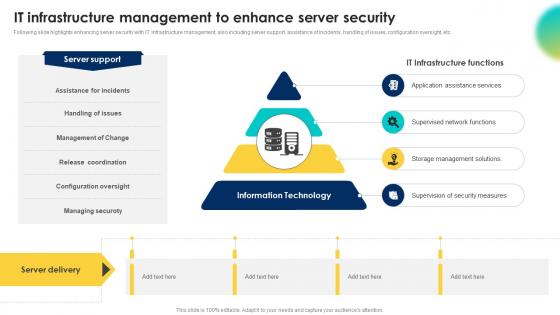 It Infrastructure Management To Enhance Server Security
It Infrastructure Management To Enhance Server SecurityFollowing slide highlights enhancing server security with IT infrastructure management, also including server support, assistance of incidents, handling of issues, configuration oversight, etc. Introducing our premium set of slides with It Infrastructure Management To Enhance Server Security. Ellicudate the fourstages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Supervised Network Functions, Storage Management Solutions, Management Of Change. So download instantly and tailor it with your information.
-
 Network security architecture sample diagram ppt powerpoint slides
Network security architecture sample diagram ppt powerpoint slidesPresenting network security architecture sample diagram ppt powerpoint slides. This is a network security architecture sample diagram ppt powerpoint slides. This is a nine stage process. The stages in this process are mail, maintenance, testing, design, content, web, backup, database, development.
-
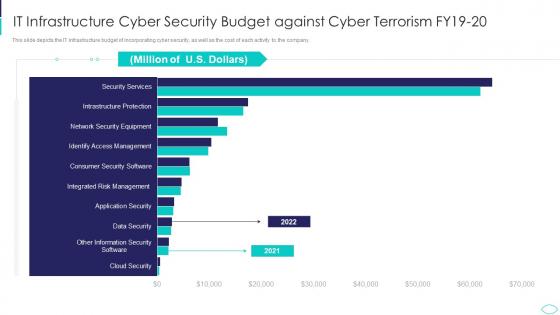 IT Infrastructure Cyber Security Budget Against Cyber Terrorism Attacks
IT Infrastructure Cyber Security Budget Against Cyber Terrorism AttacksThis slide depicts the IT infrastructure budget of incorporating cyber security, as well as the cost of each activity to the company. Present the topic in a bit more detail with this IT Infrastructure Cyber Security Budget Against Cyber Terrorism Attacks. Use it as a tool for discussion and navigation on It Infrastructure Cyber Security Budget Against Cyber Terrorism Fy19 20. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Effective It Cost Optimization Initiatives Strategic Plan To Secure It Infrastructure Strategy SS V
Effective It Cost Optimization Initiatives Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding effective IT cost optimization strategies for IT executives such as revamping technology procurement, DevOps deployment, enabling business process reengineering, etc. Increase audience engagement and knowledge by dispensing information using Effective It Cost Optimization Initiatives Strategic Plan To Secure It Infrastructure Strategy SS V. This template helps you present information on four stages. You can also present information on Revamping Technology Procurement, Enabling Business Process Reengineering, Optimization Initiatives using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
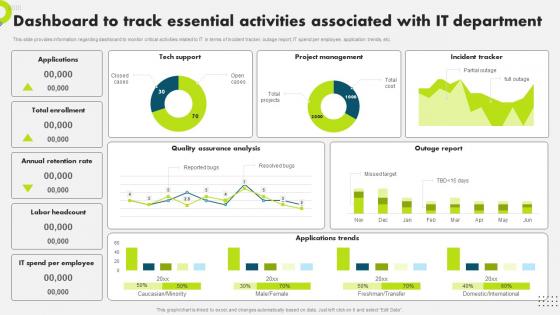 F1471 Dashboard To Track Essential Activities Strategic Plan To Secure It Infrastructure Strategy SS V
F1471 Dashboard To Track Essential Activities Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding dashboard to monitor critical activities related to IT in terms of incident tracker, outage report, IT spend per employee, application trends, etc. Present the topic in a bit more detail with this F1471 Dashboard To Track Essential Activities Strategic Plan To Secure It Infrastructure Strategy SS V. Use it as a tool for discussion and navigation on Dashboard, Associated, Department. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 It Performance Dashboard To Track Customer Strategic Plan To Secure It Infrastructure Strategy SS V
It Performance Dashboard To Track Customer Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding the dashboard to monitor overall IT performance. The dashboard tracks occupancy rate, net promoter score, avg. first contact resolution rate, etc. Present the topic in a bit more detail with this It Performance Dashboard To Track Customer Strategic Plan To Secure It Infrastructure Strategy SS V. Use it as a tool for discussion and navigation on Performance, Dashboard, Satisfaction. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
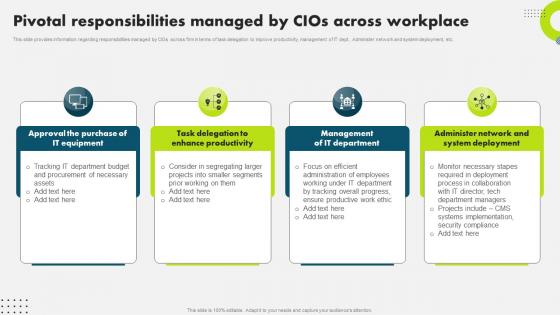 Pivotal Responsibilities Managed By Cios Across Strategic Plan To Secure It Infrastructure Strategy SS V
Pivotal Responsibilities Managed By Cios Across Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding responsibilities managed by CIOs across firm in terms of task delegation to improve productivity, management of IT dept., Administer network and system deployment, etc. Present the topic in a bit more detail with this Pivotal Responsibilities Managed By Cios Across Strategic Plan To Secure It Infrastructure Strategy SS V. Use it as a tool for discussion and navigation on Responsibilities, Management, Department. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
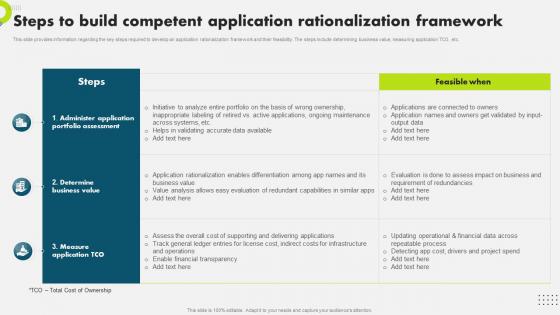 Steps To Build Competent Application Rationalization Strategic Plan To Secure It Infrastructure Strategy SS V
Steps To Build Competent Application Rationalization Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding the key steps required to develop an application rationalization framework and their feasibility. The steps include determining business value, measuring application TCO, etc. Present the topic in a bit more detail with this Steps To Build Competent Application Rationalization Strategic Plan To Secure It Infrastructure Strategy SS V. Use it as a tool for discussion and navigation on Application, Rationalization, Framework. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Steps To Develop Targeted Marketing Initiatives Strategic Plan To Secure It Infrastructure Strategy SS V
Steps To Develop Targeted Marketing Initiatives Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information various steps required to develop target marketing initiatives for IT department. The initiatives include detect target market, conduct market research, develop objectives and goals, etc. Introducing Steps To Develop Targeted Marketing Initiatives Strategic Plan To Secure It Infrastructure Strategy SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Marketing, Initiatives, Department, using this template. Grab it now to reap its full benefits.
-
 Table Of Contents For Strategic Plan To Secure It Infrastructure Strategy SS V
Table Of Contents For Strategic Plan To Secure It Infrastructure Strategy SS VPresent the topic in a bit more detail with this Table Of Contents For Strategic Plan To Secure It Infrastructure Strategy SS V. Use it as a tool for discussion and navigation on Strategic Business Alignment, Workforce And Cost Management, Deploy Application Rationalization . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
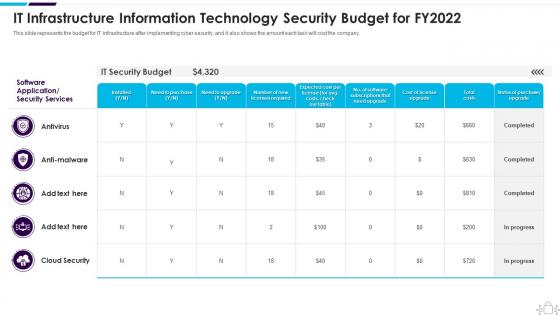 Information Technology Security It Infrastructure Information Budget For Fy2022
Information Technology Security It Infrastructure Information Budget For Fy2022This slide represents the budget for IT infrastructure after implementing cyber security, and it also shows the amount each task will cost the company. Present the topic in a bit more detail with this Information Technology Security It Infrastructure Information Budget For Fy2022. Use it as a tool for discussion and navigation on Infrastructure, Information, Technology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Network Security Planning Architecture Ppt Powerpoint Presentation Gallery Portrait Cpb
Network Security Planning Architecture Ppt Powerpoint Presentation Gallery Portrait CpbPresenting Network Security Planning Architecture Ppt Powerpoint Presentation Gallery Portrait Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Network Security Planning Architecture. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
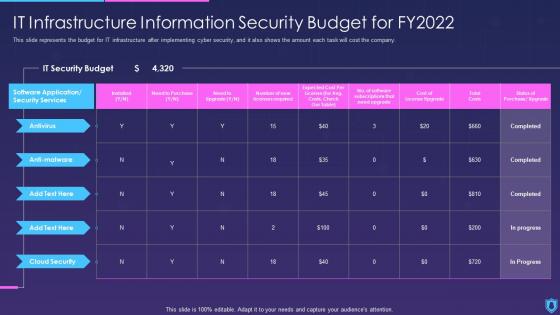 Information Security It Infrastructure Information Security Budget For Fy2022
Information Security It Infrastructure Information Security Budget For Fy2022This slide represents the budget for IT infrastructure after implementing cyber security, and it also shows the amount each task will cost the company. Present the topic in a bit more detail with this Information Security It Infrastructure Information Security Budget For Fy2022. Use it as a tool for discussion and navigation on Infrastructure, Information, Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 5g Network Architecture Guidelines Key Security Considerations For 5g For Threat Handling
5g Network Architecture Guidelines Key Security Considerations For 5g For Threat HandlingThis slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. Present the topic in a bit more detail with this 5g Network Architecture Guidelines Key Security Considerations For 5g For Threat Handling. Use it as a tool for discussion and navigation on Considerations, Associated, Unauthorized. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
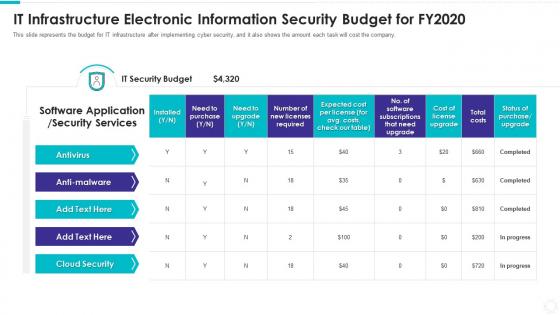 It infrastructure electronic information security budget for fy2020
It infrastructure electronic information security budget for fy2020This slide represents the budget for IT infrastructure after implementing cyber security, and it also shows the amount each task will cost the company. Deliver an outstanding presentation on the topic using this IT Infrastructure Electronic Information Security Budget For FY2020. Dispense information and present a thorough explanation of Antivirus, Anti Malware, IT Security Budget, Total Costs using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
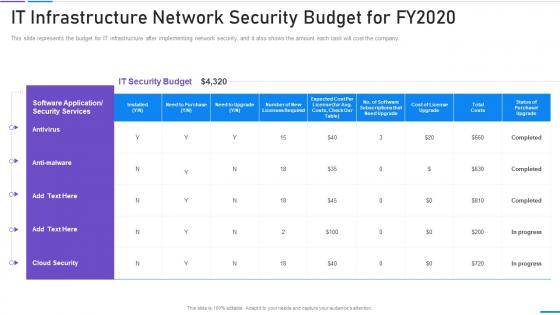 Network Security It Infrastructure Network Security Budget For Fy2020
Network Security It Infrastructure Network Security Budget For Fy2020This slide represents the budget for IT infrastructure after implementing network security, and it also shows the amount each task will cost the company. Present the topic in a bit more detail with this Network Security It Infrastructure Network Security Budget For Fy2020. Use it as a tool for discussion and navigation on It Infrastructure Network Security Budget For Fy2020. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
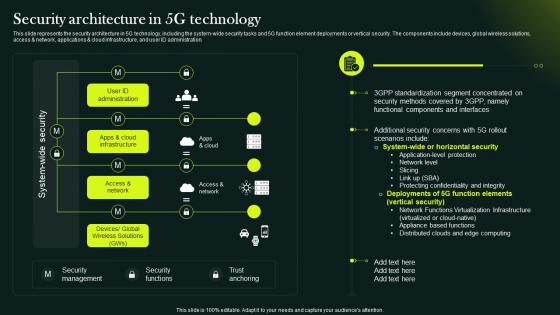 5G Network Technology Architecture Security Architecture In 5G Technology
5G Network Technology Architecture Security Architecture In 5G TechnologyThis slide represents the security architecture in 5G technology, including the system wide security tasks and 5G function element deployments or vertical security. The components include devices, global wireless solutions, access and network, applications and cloud infrastructure, and user ID administration. Present the topic in a bit more detail with this 5G Network Technology Architecture Security Architecture In 5G Technology. Use it as a tool for discussion and navigation on System Wide Security, Security Functions, Trust Anchoring. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 5G Network Technology Architecture Security In 5G Technology Architecture
5G Network Technology Architecture Security In 5G Technology ArchitectureThis slide depicts the security in 5G architecture, including the standards detailed by 3GPP 3rd Generation Partnership Project, such as SUPI, unified authentication, extensible authentication standards, and flexible security policies. Introducing 5G Network Technology Architecture Security In 5G Technology Architecture to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Mobile Technologys Security, Service Delivery Process, 5G Security Features, using this template. Grab it now to reap its full benefits.
-
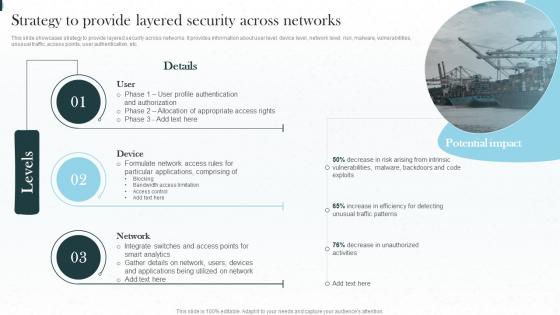 Strategy To Provide Layered Security Across Networks Implementing Iot Architecture In Shipping Business
Strategy To Provide Layered Security Across Networks Implementing Iot Architecture In Shipping BusinessThis slide showcases strategy to provide layered security across networks. It provides information about user level, device level, network level, risk, malware, vulnerabilities, unusual traffic, access points, user authentication, etc. Present the topic in a bit more detail with this Strategy To Provide Layered Security Across Networks Implementing Iot Architecture In Shipping Business. Use it as a tool for discussion and navigation on Strategy, Authentication, Appropriate Access. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Agenda For Strategic Plan To Secure It Infrastructure Strategy SS V
Agenda For Strategic Plan To Secure It Infrastructure Strategy SS VIntroducing Agenda For Strategic Plan To Secure It Infrastructure Strategy SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on IT Infrastructure Management, IT Automation, IT Risk Management , using this template. Grab it now to reap its full benefits.
-
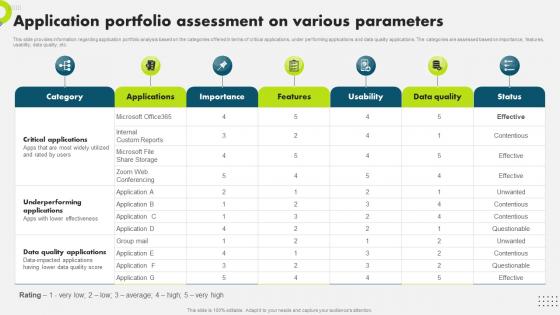 Application Portfolio Assessment On Various Strategic Plan To Secure It Infrastructure Strategy SS V
Application Portfolio Assessment On Various Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding application portfolio analysis based on the categories offered in terms of critical applications, under performing applications and data quality applications. The categories are assessed based on importance, features, usability, data quality, etc. Present the topic in a bit more detail with this Application Portfolio Assessment On Various Strategic Plan To Secure It Infrastructure Strategy SS V. Use it as a tool for discussion and navigation on Application, Portfolio, Assessment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
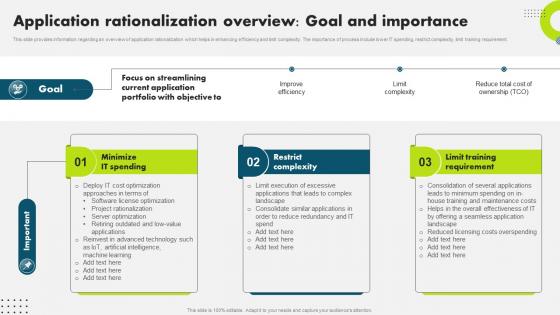 Application Rationalization Overview Goal Strategic Plan To Secure It Infrastructure Strategy SS V
Application Rationalization Overview Goal Strategic Plan To Secure It Infrastructure Strategy SS VThis slide provides information regarding an overview of application rationalization which helps in enhancing efficiency and limit complexity. The importance of process include lower IT spending, restrict complexity, limit training requirement. Deliver an outstanding presentation on the topic using this Application Rationalization Overview Goal Strategic Plan To Secure It Infrastructure Strategy SS V. Dispense information and present a thorough explanation of Restrict Complexity, Limit Training, Application Rationalization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.