Powerpoint Templates and Google slides for It Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Data security it complete data security implementation checklist
Data security it complete data security implementation checklistThis slide depicts the cyber security checklist and measures an organization should take to protect data and company assets from cyber attacks or natural disasters. Introducing Data Security IT Complete Data Security Implementation Checklist to increase your presentation threshold. Encompassed with twelve stages, this template is a great option to educate and entice your audience. Dispence information on Frequent Staff Training, Antivirus Software, Strong Passwords, Minimize Administrative Privileges, Data Backup, Recovery Planning, Strong IT Policies, Secure Communications, Device Security, using this template. Grab it now to reap its full benefits.
-
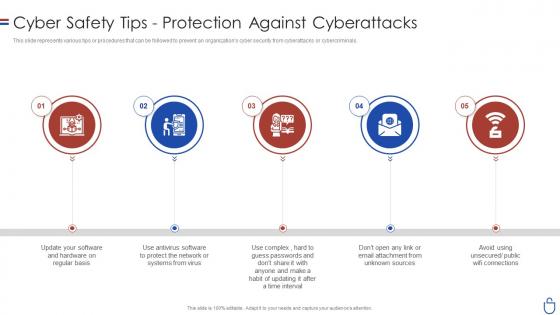 Data security it cyber safety tips protection against cyberattacks
Data security it cyber safety tips protection against cyberattacksThis slide represents various tips or procedures that can be followed to prevent an organizations cyber security from cyberattacks or cybercriminals. Increase audience engagement and knowledge by dispensing information using Data Security IT Cyber Safety Tips Protection Against Cyberattacks. This template helps you present information on five stages. You can also present information on Sources, Public Wifi Connections, Time Interval, Protect Network using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
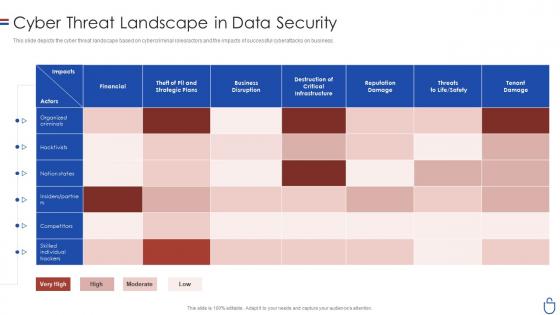 Data security it cyber threat landscape in data security
Data security it cyber threat landscape in data securityThis slide depicts the cyber threat landscape based on cybercriminal roles or actors and the impacts of successful cyberattacks on business. Present the topic in a bit more detail with this Data Security IT Cyber Threat Landscape In Data Security. Use it as a tool for discussion and navigation on Financial, Business Disruption, Reputation Damage, Tenant Damage. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
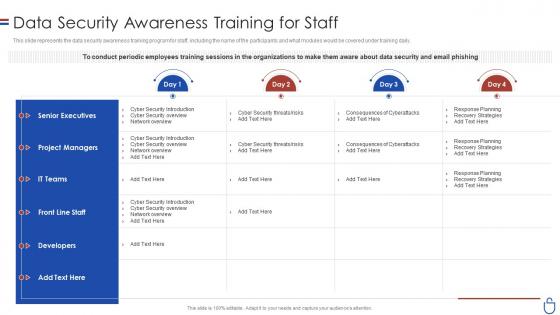 Data security it data security awareness training for staff
Data security it data security awareness training for staffThis slide represents the data security awareness training program for staff, including the name of the participants and what modules would be covered under training daily. Present the topic in a bit more detail with this Data Security IT Data Security Awareness Training For Staff. Use it as a tool for discussion and navigation on Senior Executives, Project Managers, IT Teams, Developers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
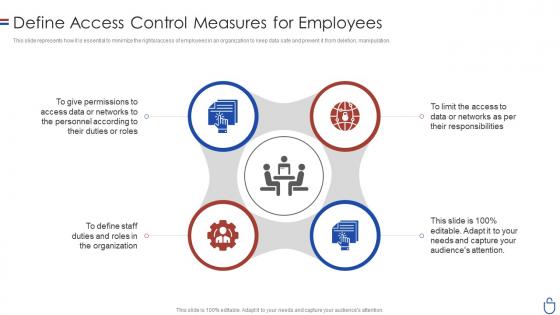 Data security it define access control measures for employees
Data security it define access control measures for employeesThis slide represents how it is essential to minimize the rights or access of employees in an organization to keep data safe and prevent it from deletion, manipulation. Increase audience engagement and knowledge by dispensing information using Data Security IT Define Access Control Measures For Employees. This template helps you present information on four stages. You can also present information on Data, Networks, Roles, Organization, Data Or Networks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data security it dispose data and equipment properly
Data security it dispose data and equipment properlyThis slide depicts the importance of disposal of the data and equipment that is not in use anymore and restricts the employees who already left the organization. Increase audience engagement and knowledge by dispensing information using Data Security IT Dispose Data And Equipment Properly. This template helps you present information on three stages. You can also present information on Employees, Organization, Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
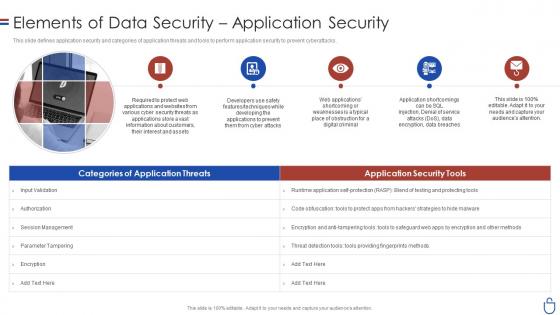 Data security it elements of data security application security
Data security it elements of data security application securityThis slide defines application security and categories of application threats and tools to perform application security to prevent cyberattacks. Introducing Data Security IT Elements Of Data Security Application Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Protect Web Applications, Input Validation, Session Management, Parameter Tampering, using this template. Grab it now to reap its full benefits.
-
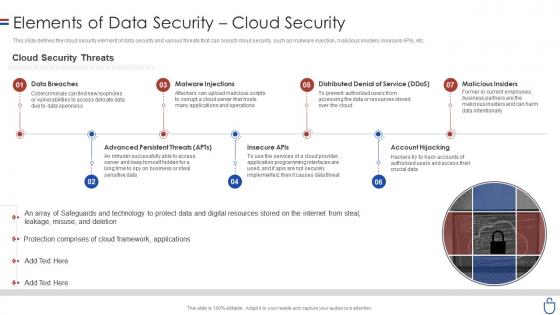 Data security it elements of data security cloud security
Data security it elements of data security cloud securityThis slide defines the cloud security element of data security and various threats that can breach cloud security, such as malware injection, malicious insiders, insecure APIs, etc. Increase audience engagement and knowledge by dispensing information using Data Security IT Elements Of Data Security Cloud Security. This template helps you present information on seven stages. You can also present information on Data Breaches, Malware Injections, Distributed Denial Service Ddos, Malicious Insiders, Account Hijacking, Advanced Persistent Threats using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
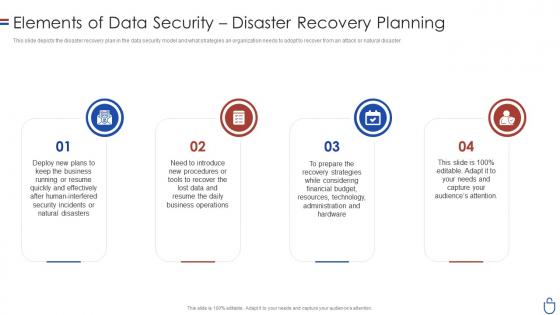 Data security it elements of data security disaster recovery planning
Data security it elements of data security disaster recovery planningThis slide depicts the disaster recovery plan in the data security model and what strategies an organization needs to adopt to recover from an attack or natural disaster. Introducing Data Security IT Elements Of Data Security Disaster Recovery Planning to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Business, Natural Disasters, Human Interfered Security Incidents, Technology, using this template. Grab it now to reap its full benefits.
-
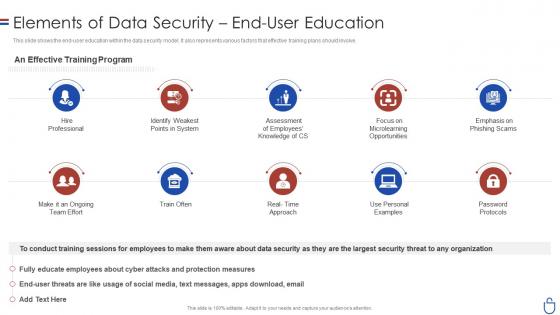 Data security it elements of data security end user education
Data security it elements of data security end user educationThis slide shows the end user education within the data security model. It also represents various factors that effective training plans should involve. Increase audience engagement and knowledge by dispensing information using Data Security IT Elements Of Data Security End User Education. This template helps you present information on ten stages. You can also present information on Hire Professional, Identify Weakest Points System, Assessment Employees Knowledge CS, Emphasis On Phishing Scams, Train Often, Password Protocols using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
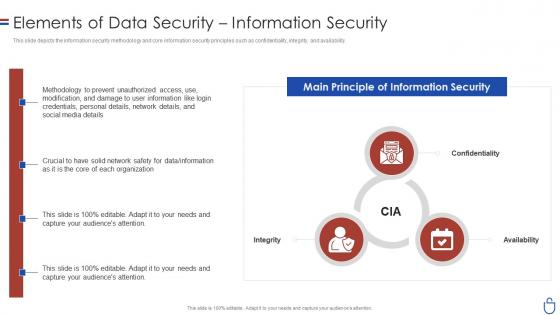 Data security it elements of data security information security
Data security it elements of data security information securityThis slide depicts the information security methodology and core information security principles such as confidentiality, integrity, and availability. Introducing Data Security IT Elements Of Data Security Information Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Main Principle, Information Security, Personal Details, Network Details, Social Media Details, using this template. Grab it now to reap its full benefits.
-
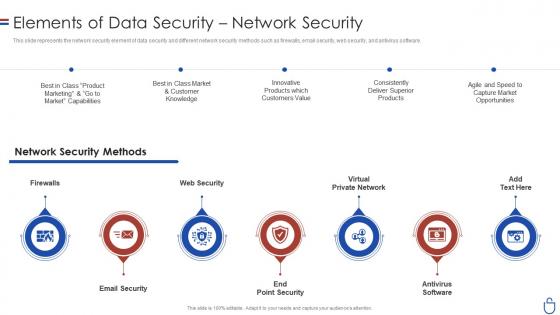 Data security it elements of data security network security
Data security it elements of data security network securityThis slide represents the network security element of data security and different network security methods such as firewalls, email security, web security, and antivirus software. Increase audience engagement and knowledge by dispensing information using Data Security IT Elements Of Data Security Network Security. This template helps you present information on seven stages. You can also present information on Email Security, End Point Security, Antivirus Software, Virtual Private Network, Web Security, Firewalls using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
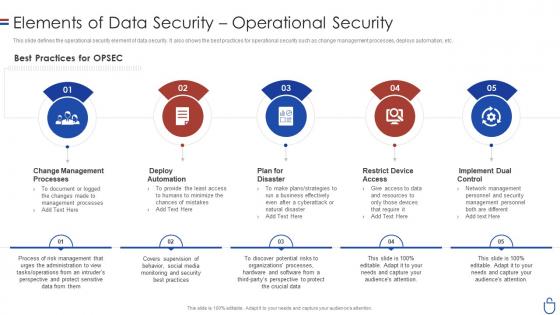 Data security it elements of data security operational security
Data security it elements of data security operational securityThis slide defines the operational security element of data security. It also shows the best practices for operational security such as change management processes, deploys automation, etc. Introducing Data Security IT Elements Of Data Security Operational Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Best Practices, OPSEC, Change Management Processes, Deploy Automation, Plan For Disaster, Restrict Device Access, Implement Dual Control, using this template. Grab it now to reap its full benefits.
-
 Data security it employee awareness training budget for fy2020
Data security it employee awareness training budget for fy2020This slide represents the organizations staff training budget through a graph covering trainer name, date, and capability levels. Present the topic in a bit more detail with this Data Security IT Employee Awareness Training Budget For FY2020. Use it as a tool for discussion and navigation on Provide, Protect Cardholder Data, Capability Level, Budget, Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data security it hardware and software update in company
Data security it hardware and software update in companyThis slide depicts the hardware or software update measure under the cyber security model. It also tells the current status of the devices that need to update in the organization. Introducing Data Security IT Hardware And Software Update In Company to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Peripheral Devices, Technology, Computers And Servers, using this template. Grab it now to reap its full benefits.
-
 Data security it how is automation used in data security
Data security it how is automation used in data securityThis slide depicts the cyber protection of an organization through artificial intelligence and how it can be helpful in threat detection, threat response, and human augmentation. Present the topic in a bit more detail with this Data Security IT How Is Automation Used In Data Security. Use it as a tool for discussion and navigation on Threat Detection, Threat Response, Human Augmentation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
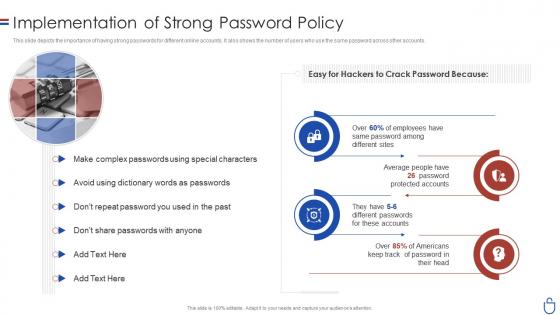 Data security it implementation of strong password policy
Data security it implementation of strong password policyThis slide depicts the importance of having strong passwords for different online accounts. It also shows the number of users who use the same password across other accounts. Introducing Data Security IT Implementation Of Strong Password Policy to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Special Characters, Employees, Protected Accounts, using this template. Grab it now to reap its full benefits.
-
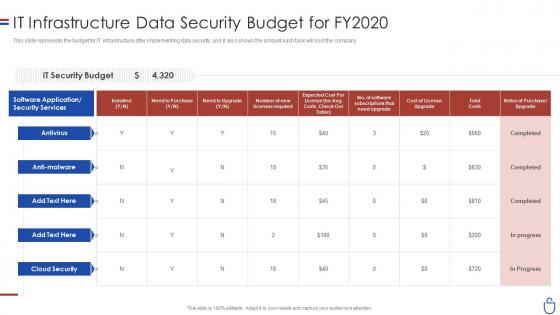 Data security it infrastructure data security budget for fy2020
Data security it infrastructure data security budget for fy2020This slide represents the budget for IT infrastructure after implementing data security, and it also shows the amount each task will cost the company. Present the topic in a bit more detail with this Data Security IT Infrastructure Data Security Budget For FY2020. Use it as a tool for discussion and navigation on IT Security Budget, Need To Purchase, Total Cost, Cost License Upgrade. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data security it key elements of data security ppt slides background
Data security it key elements of data security ppt slides backgroundThis slide represents the different elements of data security such as application security, network security, information security, etc. Introducing Data Security IT Key Elements Of Data Security Ppt Slides Background to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Application Security, Network Security, End User Education, Cloud Security, Operational Security, Disaster Recovery Planning, Information Security, using this template. Grab it now to reap its full benefits.
-
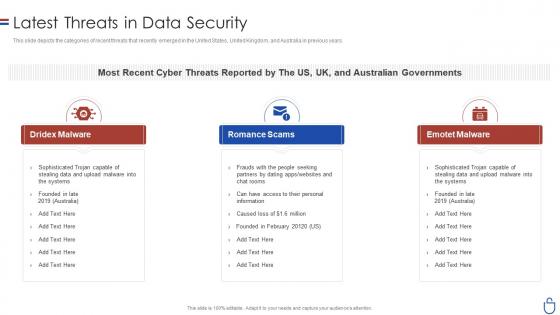 Data security it latest threats in data security ppt slides background designs
Data security it latest threats in data security ppt slides background designsThis slide depicts the categories of recent threats that recently emerged in the United States, United Kingdom, and Australia in previous years. Increase audience engagement and knowledge by dispensing information using Data Security IT Latest Threats In Data Security Ppt Slides Background Designs. This template helps you present information on three stages. You can also present information on Dridex Malware, Romance Scams, Emotet Malware using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data security it main principle of information security ppt slides topics
Data security it main principle of information security ppt slides topicsThis slide represents the main principles of information security such as confidentiality, integrity, and availability and how it makes data confidential and consistent, and available to authorized users. Introducing Data Security IT Main Principle Of Information Security Ppt Slides Topics to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Confidentiality, Integrity, Availability, Data, using this template. Grab it now to reap its full benefits.
-
 Data security it main steps of operational security
Data security it main steps of operational securityThis slide depicts the main steps of operational security, such as describing sensitive information, identifying potential risks, and so on, by showing how these steps are operating. Increase audience engagement and knowledge by dispensing information using Data Security IT Main Steps Of Operational Security. This template helps you present information on one stages. You can also present information on Financial Details, Product Research, Exploit Data, Plan using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
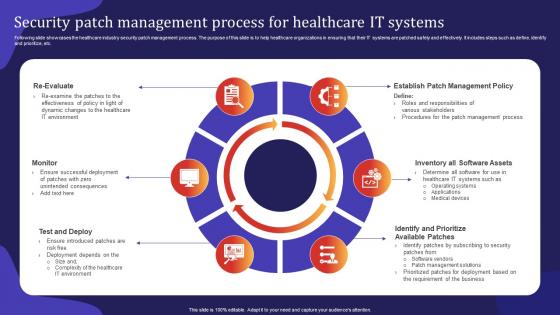 Security Patch Management Process For Healthcare IT Systems
Security Patch Management Process For Healthcare IT SystemsFollowing slide showcases the healthcare industry security patch management process. The purpose of this slide is to help healthcare organizations in ensuring that their IT systems are patched safely and effectively. It includes steps such as define, identify and prioritize, etc.Presenting our set of slides with Security Patch Management Process For Healthcare IT Systems. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Roles Responsibilities, Ensure Introduced, Deployment Depends.
-
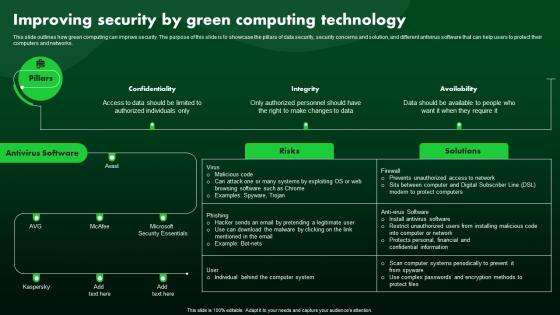 Improving Security By Green Computing Technology Green IT
Improving Security By Green Computing Technology Green ITThis slide outlines how green computing can improve security. The purpose of this slide is to showcase the pillars of data security, security concerns and solution, and different antivirus software that can help users to protect their computers and networks. Deliver an outstanding presentation on the topic using this Improving Security By Green Computing Technology Green IT. Dispense information and present a thorough explanation of Technology, Computing, Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
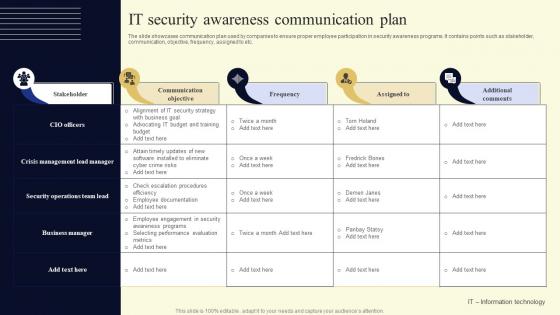 IT Security Awareness Communication Plan
IT Security Awareness Communication PlanThe slide showcases communication plan used by companies to ensure proper employee participation in security awareness programs. It contains points such as stakeholder, communication, objective, frequency, assigned to etc. Presenting our well structured IT Security Awareness Communication Plan. The topics discussed in this slide are Communication, Frequency, Additional. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Understanding Security Risk Related With Dark Data Dark Data And Its Utilization
Understanding Security Risk Related With Dark Data Dark Data And Its UtilizationThis slide focuses on the security risks associated with dark data. Some of the risks associated with dark data include vulnerability to hacking, negative impact on the business, and an increased workload for IT teams, etc. Introducing Understanding Security Risk Related With Dark Data Dark Data And Its Utilization to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Vulnerability To Hacking, Negative Impact On Business, Increased Workload For IT Teams, using this template. Grab it now to reap its full benefits.
-
 IT In Manufacturing Industry V2 Managing Cyber Security In Manufacturing 90 Days Plan
IT In Manufacturing Industry V2 Managing Cyber Security In Manufacturing 90 Days PlanThis slide depicts the next 90 days of managing cyber security in the manufacturing operations plan. It includes metric names, items to be measured, measurement method, time, and teams who are responsible and details. Deliver an outstanding presentation on the topic using this IT In Manufacturing Industry V2 Managing Cyber Security In Manufacturing 90 Days Plan. Dispense information and present a thorough explanation of Managing Cyber Security, Manufacturing Operations Plan, Security Training Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
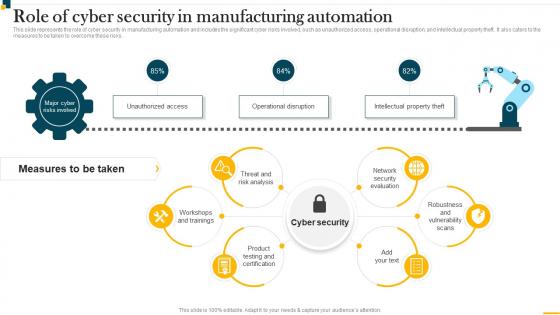 IT In Manufacturing Industry V2 Role Of Cyber Security In Manufacturing Automation
IT In Manufacturing Industry V2 Role Of Cyber Security In Manufacturing AutomationThis slide represents the role of cyber security in manufacturing automation and includes the significant cyber risks involved, such as unauthorized access, operational disruption, and intellectual property theft. It also caters to the measures to be taken to overcome these risks. Introducing IT In Manufacturing Industry V2 Role Of Cyber Security In Manufacturing Automation to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Network Security Evaluation, Threat And Risk Analysis, Workshops And Trainings, Product Testing And Certification, using this template. Grab it now to reap its full benefits.
-
 Managing Cyber Security In Manufacturing 30 Days IT In Manufacturing Industry V2
Managing Cyber Security In Manufacturing 30 Days IT In Manufacturing Industry V2This slide describes the first 30 days of managing cyber security in the manufacturing operations plan. It includes metric names, items to be measured, measurement method, time, and teams who are responsible and details. Deliver an outstanding presentation on the topic using this Managing Cyber Security In Manufacturing 30 Days IT In Manufacturing Industry V2. Dispense information and present a thorough explanation of Phishing Awareness, Phishing Reporting, Phishing Repeat Offenders, Facility Physical Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Managing Cyber Security In Manufacturing 60 Days IT In Manufacturing Industry V2
Managing Cyber Security In Manufacturing 60 Days IT In Manufacturing Industry V2This slide represents the next 60 days of managing cyber security in the manufacturing operations plan. It includes metric names, items to be measured, measurement method, time, and teams who are responsible and details. Present the topic in a bit more detail with this Managing Cyber Security In Manufacturing 60 Days IT In Manufacturing Industry V2. Use it as a tool for discussion and navigation on Managing Cyber Security, Manufacturing Operations Plan, Data Loss Incidents. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
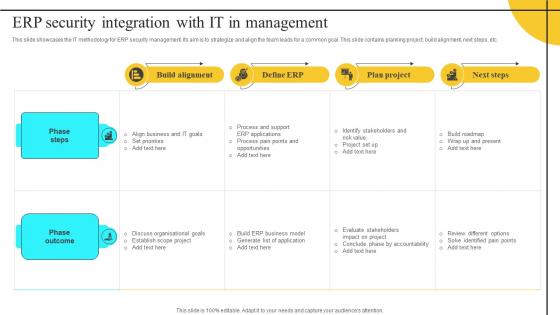 ERP Security Integration With It In Management
ERP Security Integration With It In ManagementThis slide showcases the IT methodology for ERP security management. Its aim is to strategize and align the team leads for a common goal. This slide contains planning project, build alignment, next steps, etc. Introducing our ERP Security Integration With It In Management set of slides. The topics discussed in these slides are Phase Steps, Phase Outcome. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cloud Access Security Broker CASB V2 Shadow IT Management Lifecycle Overview
Cloud Access Security Broker CASB V2 Shadow IT Management Lifecycle OverviewThis slide outlines the lifecycle of shadow IT management for safely adopting cloud apps. The purpose of this slide is to showcase the various stages of the lifecycle, such as discovering shadow IT, knowing the risk level of apps, evaluating compliance, analyzing usage, governing cloud apps, and continuous monitoring. Introducing Cloud Access Security Broker CASB V2 Shadow IT Management Lifecycle Overview to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Evaluate Compliance, Govern Cloud Apps, Continuous Monitoring, Network Ecosystem, using this template. Grab it now to reap its full benefits.
-
 Comparative Analysis Of It Security And Compliance
Comparative Analysis Of It Security And ComplianceThis slide shows It security and compliance comparative analysis to implement effective technical controls to protect company assets. It further includes details such as it security Practiced by business for personal gain etc. Introducing our premium set of slides with Comparative Analysis Of It Security And Compliance. Ellicudate the two stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like It Security, It Compliance. So download instantly and tailor it with your information.
-
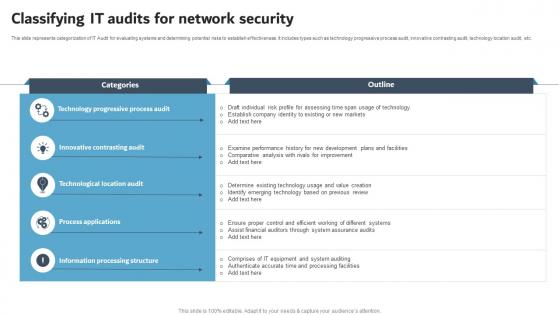 Classifying IT Audits For Network Security
Classifying IT Audits For Network SecurityThis slide represents categorization of IT Audit for evaluating systems and determining potential risks to establish effectiveness. It includes types such as technology progressive process audit, innovative contrasting audit, technology location audit, etc. Presenting our well structured Classifying IT Audits For Network Security. The topics discussed in this slide are Technology Progressive Process Audit, Innovative Contrasting Audit, Technological Location Audit. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 IT Audit Evaluation Icon For Data Security
IT Audit Evaluation Icon For Data SecurityIntroducing our premium set of slides with IT Audit Evaluation Icon For Data Security. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like IT Audit, Evaluation Icon, Data Security. So download instantly and tailor it with your information.
-
 IT Cyber Security Strategy Action Plan Icon
IT Cyber Security Strategy Action Plan IconIntroducing our premium set of slides with IT Cyber Security Strategy Action Plan Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber, Action, Strategy. So download instantly and tailor it with your information.
-
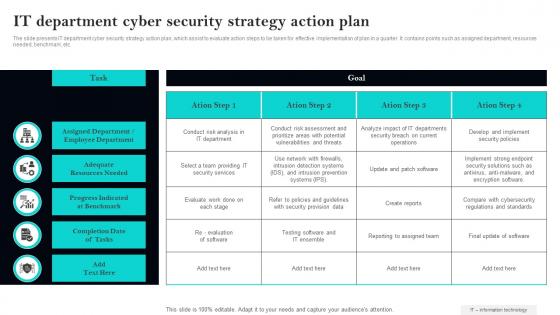 IT Department Cyber Security Strategy Action Plan
IT Department Cyber Security Strategy Action PlanThe slide presents IT department cyber security strategy action plan, which assist to evaluate action steps to be taken for effective implementation of plan in a quarter. It contains points such as assigned department, resources needed, benchmark, etc. Introducing our IT Department Cyber Security Strategy Action Plan set of slides. The topics discussed in these slides are Assigned, Department, Resources. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
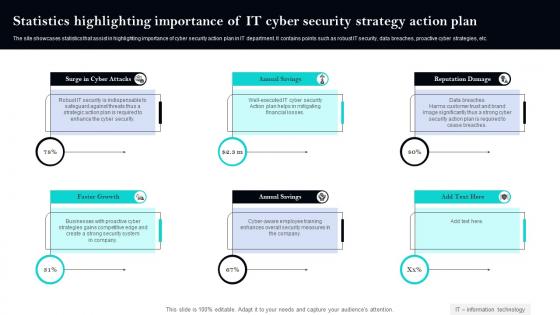 Statistics Highlighting Importance Of IT Cyber Security Strategy Action Plan
Statistics Highlighting Importance Of IT Cyber Security Strategy Action PlanThe site showcases statistics that assist in highlighting importance of cyber security action plan in IT department. It contains points such as robust IT security, data breaches, proactive cyber strategies, etc. Introducing our premium set of slides with Statistics Highlighting Importance Of IT Cyber Security Strategy Action Plan. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Annual, Reputation, Annual. So download instantly and tailor it with your information.
-
 Training And Development Plan Icon For IT Security Staff
Training And Development Plan Icon For IT Security StaffPresenting our set of slides with Training And Development Plan Icon For IT Security Staff. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Training, Development, Security.
-
 Security Incidents And Mitigation Solutions In IT Industry
Security Incidents And Mitigation Solutions In IT IndustryThis slide highlights mitigation solutions to various types of security threats that disrupts business operations. The purpose of this slide is to help organizations in strengthening their network and data security system. It covers mitigation solutions such as detecting security incidents, assessing user account activity, etc. Presenting our set of slides with Security Incidents And Mitigation Solutions In IT Industry This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Insider Threats, Phishing Attacks, Viruses.
-
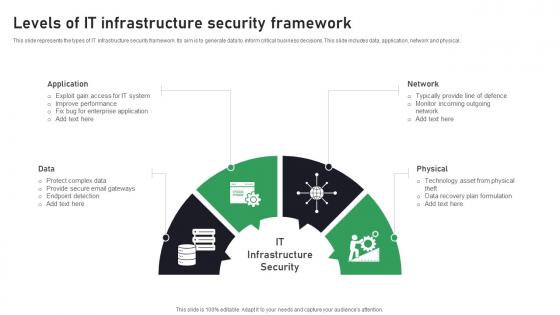 Levels Of IT Infrastructure Security Framework
Levels Of IT Infrastructure Security FrameworkThis slide represents the types of IT infrastructure security framework. Its aim is to generate data to inform critical business decisions. This slide includes data, application, network and physical. Introducing our premium set of slides with Levels Of IT Infrastructure Security Framework. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Protect, Secure, Application. So download instantly and tailor it with your information.
-
 Types Of Threats In IT Infrastructure Security
Types Of Threats In IT Infrastructure SecurityThis slide showcases the common threats faced in infrastructure security. Its aim is to identify threats and eliminate them. This slide includes phishing, ransomware, botnet and physical theft. Presenting our set of slides with Types Of Threats In IT Infrastructure Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Infrastructure, Personal, Exploitation.
-
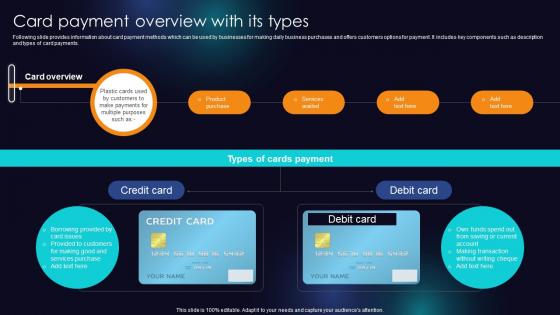 Card Payment Overview With Its Types Enhancing Transaction Security With E Payment
Card Payment Overview With Its Types Enhancing Transaction Security With E PaymentFollowing slide provides information about card payment methods which can be used by businesses for making daily business purchases and offers customers options for payment. It includes key components such as description and types of card payments. Deliver an outstanding presentation on the topic using this Card Payment Overview With Its Types Enhancing Transaction Security With E Payment Dispense information and present a thorough explanation of Credit Card, Debit Card, Services Purchase using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security In IT Industry Icon
Cyber Security In IT Industry IconIntroducing our premium set of slides with Cyber Security In IT Industry Icon. Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Security In IT Industry Icon. So download instantly and tailor it with your information.
-
 Cyber Security And It Audit Trends
Cyber Security And It Audit TrendsThis slide covers emerging trends in cyber audit and provides details about market situation in global level cybersecurity audit. It includes elements such as advisory auditing, skilled employee shortage, etc. Introducing our premium set of slides with Cyber Security And It Audit Trends. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Skilled Employee Shortage, Advisory Auditing, Automation Analytics. So download instantly and tailor it with your information.
-
 It Network Security Management Requirements
It Network Security Management RequirementsThis slide showcases the information technology network security management requirements which helps an organization to address ever expanding matrix of users and locations. It include details such as network deployment, configuration, security, etc. Presenting our well structured It Network Security Management Requirements. The topics discussed in this slide are Network Deployment, Feature Configuration, Network Security. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
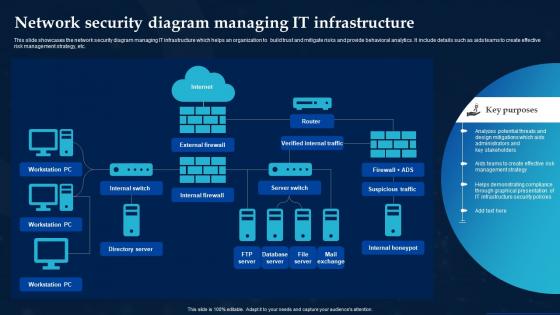 Network Security Diagram Managing It Infrastructure
Network Security Diagram Managing It InfrastructureThis slide showcases the network security diagram managing IT infrastructure which helps an organization to build trust and mitigate risks and provide behavioral analytics. It include details such as aids teams to create effective risk management strategy, etc. Introducing our Network Security Diagram Managing It Infrastructure set of slides. The topics discussed in these slides are Internal Switch, Internal Firewall, Server Switch. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Advantages Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It
Advantages Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age ItThis slide outlines the benefits of utilizing Hypertext Transfer Protocol Secure HTTPS for website encryption. The advantages discussed in this slide are secure interaction, data integrity, privacy and security, better performance, user experience, etc. Introducing Advantages Of Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Secure Interaction, Data Integrity, Better Performance, using this template. Grab it now to reap its full benefits.
-
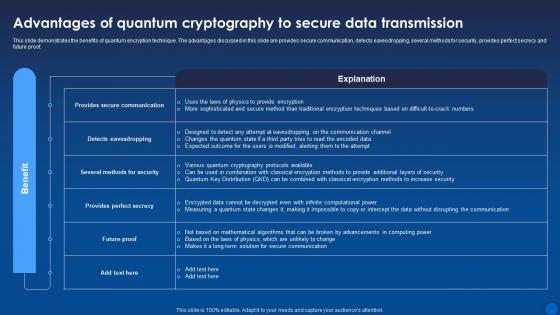 Advantages Of Quantum Cryptography To Secure Data Encryption For Data Privacy In Digital Age It
Advantages Of Quantum Cryptography To Secure Data Encryption For Data Privacy In Digital Age ItThis slide demonstrates the benefits of quantum encryption technique. The advantages discussed in this slide are provides secure communication, detects eavesdropping, several methods for security, provides perfect secrecy and future proof. Present the topic in a bit more detail with this Advantages Of Quantum Cryptography To Secure Data Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Quantum, Cryptography, Data Transmission. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
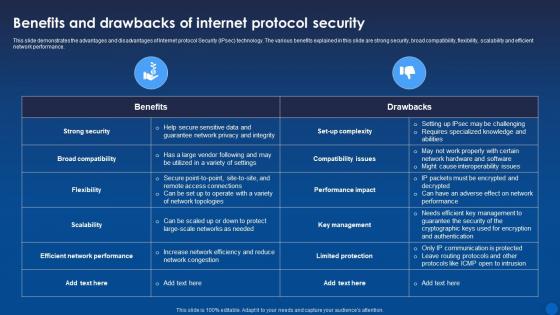 Benefits Of Internet Protocol Security Encryption For Data Privacy In Digital Age It
Benefits Of Internet Protocol Security Encryption For Data Privacy In Digital Age ItThis slide demonstrates the advantages and disadvantages of Internet protocol Security IPsec technology. The various benefits explained in this slide are strong security, broad compatibility, flexibility, scalability and efficient network performance. Deliver an outstanding presentation on the topic using this Benefits Of Internet Protocol Security Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Key Management, Performance Impact, Compatibility Issues using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
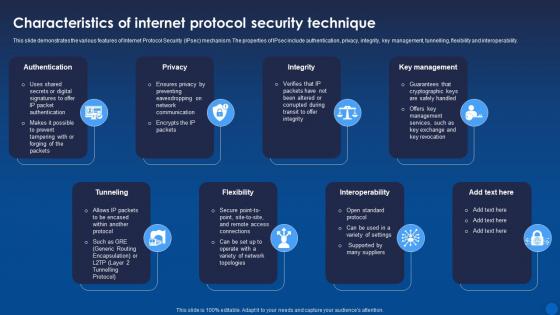 Characteristics Of Internet Protocol Security Technique Encryption For Data Privacy In Digital Age It
Characteristics Of Internet Protocol Security Technique Encryption For Data Privacy In Digital Age ItThis slide demonstrates the various features of Internet Protocol Security IPsec mechanism. The properties of IPsec include authentication, privacy, integrity, key management, tunnelling, flexibility and interoperability. Introducing Characteristics Of Internet Protocol Security Technique Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Authentication, Key Management, Interoperability, using this template. Grab it now to reap its full benefits.
-
 Emerging Trends In Cryptographic Cloud Security Encryption For Data Privacy In Digital Age It
Emerging Trends In Cryptographic Cloud Security Encryption For Data Privacy In Digital Age ItThis slide describes the cloud cryptography trends. The purpose of this slide is to highlight the emerging trends in the field of cloud encryption. These include homomorphic encryption, quantum-safe cryptography, secure multi-party computation, etc. Introducing Emerging Trends In Cryptographic Cloud Security Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Homomorphic Encryption, Quantum Safe Cryptography, Secure Multi Party Computation, using this template. Grab it now to reap its full benefits.
-
 Encryption Adaptability To Tackle Recent Security Challenges Encryption For Data Privacy In Digital Age It
Encryption Adaptability To Tackle Recent Security Challenges Encryption For Data Privacy In Digital Age ItThis slide discusses about the increasing adoption of encryption to solve current cyber security issues. The key points discussed are more use of cloud encryption in banking sector, introduction of homomorphic encryption, increase in BYOE adoption, etc. Increase audience engagement and knowledge by dispensing information using Encryption Adaptability To Tackle Recent Security Challenges Encryption For Data Privacy In Digital Age It. This template helps you present information on five stages. You can also present information on Homomorphic, Encryption, Introduction using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Factors Responsible For Cloud Security Failures Encryption For Data Privacy In Digital Age It
Factors Responsible For Cloud Security Failures Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to explain the various misconceptions and mistakes of organization while integrating cryptographic solutions into cloud. These include dependence on low-level encryption, reliance on cloud service providers for data protection, poor key management, etc. Introducing Factors Responsible For Cloud Security Failures Encryption For Data Privacy In Digital Age It to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Data Protection, Poor Key Management, Software Engineers, using this template. Grab it now to reap its full benefits.
-
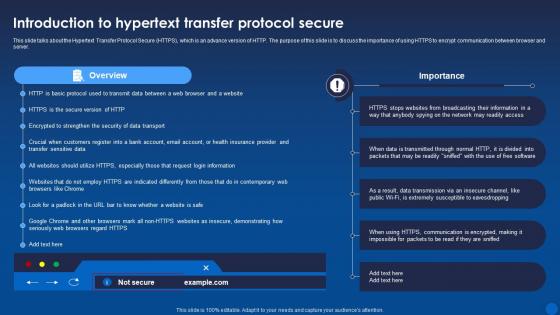 Introduction To Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It
Introduction To Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age ItThis slide talks about the Hypertext Transfer Protocol Secure HTTPS, which is an advance version of HTTP. The purpose of this slide is to discuss the importance of using HTTPS to encrypt communication between browser and server. Present the topic in a bit more detail with this Introduction To Hypertext Transfer Protocol Secure Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Introduction, Overview, Protocol Secure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
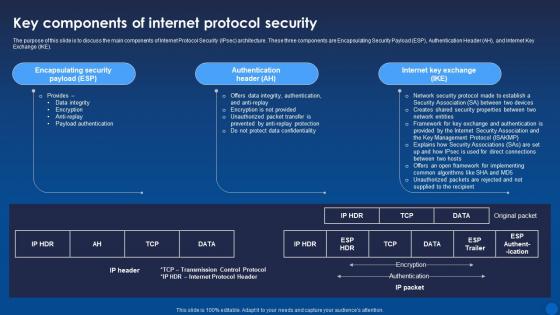 Key Components Of Internet Protocol Security Encryption For Data Privacy In Digital Age It
Key Components Of Internet Protocol Security Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to discuss the main components of Internet Protocol Security IPsec architecture. These three components are Encapsulating Security Payload ESP, Authentication Header AH, and Internet Key Exchange IKE. Deliver an outstanding presentation on the topic using this Key Components Of Internet Protocol Security Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Authentication Header, Internet Key Exchange, Encapsulating Security Payload using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
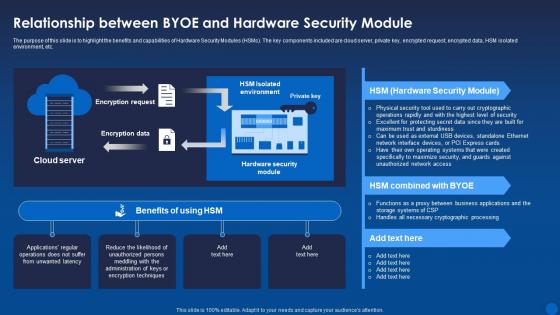 Relationship Between Byoe And Hardware Security Module Encryption For Data Privacy In Digital Age It
Relationship Between Byoe And Hardware Security Module Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to highlight the benefits and capabilities of Hardware Security Modules HSMs. The key components included are cloud server, private key, encrypted request, encrypted data, HSM isolated environment, etc. Deliver an outstanding presentation on the topic using this Relationship Between Byoe And Hardware Security Module Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Relationship, Hardware, Cryptographic using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
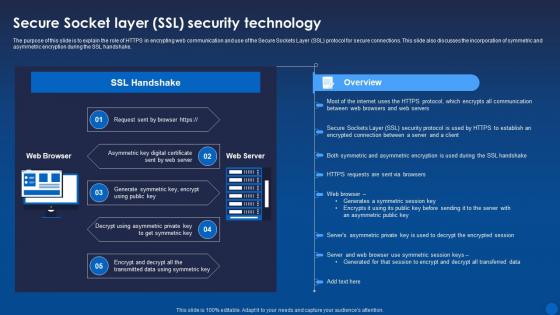 Secure Socket Layer Ssl Security Technology Encryption For Data Privacy In Digital Age It
Secure Socket Layer Ssl Security Technology Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to explain the role of HTTPS in encrypting web communication and use of the Secure Sockets Layer SSL protocol for secure connections. This slide also discusses the incorporation of symmetric and asymmetric encryption during the SSL handshake. Deliver an outstanding presentation on the topic using this Secure Socket Layer Ssl Security Technology Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Technology, Asymmetric, Symmetric using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
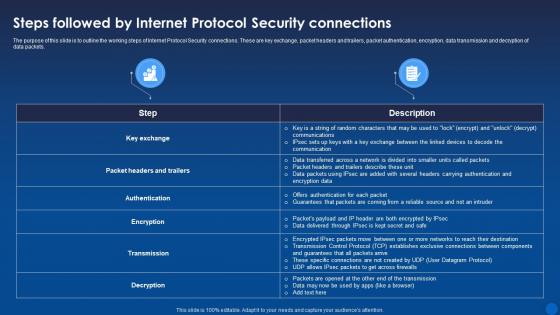 Steps Followed By Internet Protocol Security Connections Encryption For Data Privacy In Digital Age It
Steps Followed By Internet Protocol Security Connections Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to outline the working steps of Internet Protocol Security connections. These are key exchange, packet headers and trailers, packet authentication, encryption, data transmission and decryption of data packets. Deliver an outstanding presentation on the topic using this Steps Followed By Internet Protocol Security Connections Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Connections, Protocol Security, Data Transmission using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
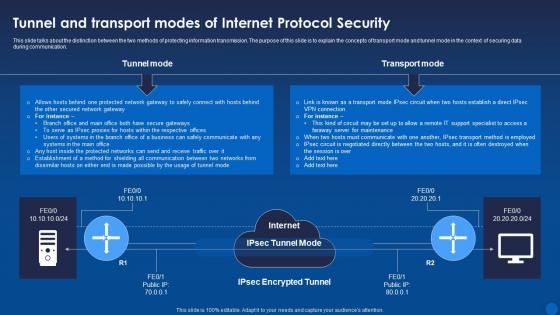 Tunnel And Transport Modes Of Internet Protocol Security Encryption For Data Privacy In Digital Age It
Tunnel And Transport Modes Of Internet Protocol Security Encryption For Data Privacy In Digital Age ItThis slide talks about the distinction between the two methods of protecting information transmission. The purpose of this slide is to explain the concepts of transport mode and tunnel mode in the context of securing data during communication. Present the topic in a bit more detail with this Tunnel And Transport Modes Of Internet Protocol Security Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Transport Mode, Protocol Security, Transmission. This template is free to edit as deemed fit for your organization. Therefore download it now.



