Powerpoint Templates and Google slides for It Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Contingency Plan For Threat Handling In Security Centre Enabling It Intelligence Framework
Contingency Plan For Threat Handling In Security Centre Enabling It Intelligence FrameworkThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations.Present the topic in a bit more detail with this Contingency Plan For Threat Handling In Security Centre Enabling It Intelligence Framework Use it as a tool for discussion and navigation on Local Area Network, Mainframe Systems, Distributes Systems This template is free to edit as deemed fit for your organization. Therefore download it now.
-
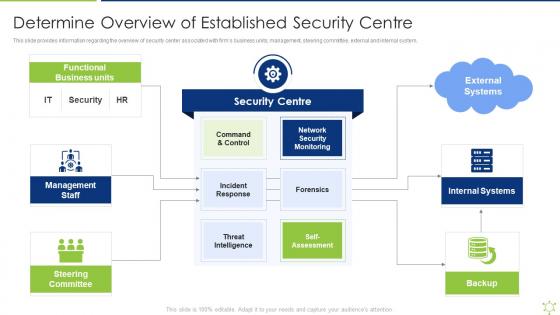 Determine Overview Of Established Security Centre Enabling It Intelligence Framework
Determine Overview Of Established Security Centre Enabling It Intelligence FrameworkThis slide provides information regarding the overview of security center associated with firms business units, management, steering committee, external and internal system.Introducing Determine Overview Of Established Security Centre Enabling It Intelligence Framework to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Functional Business, Management Staff, Steering Committee using this template. Grab it now to reap its full benefits.
-
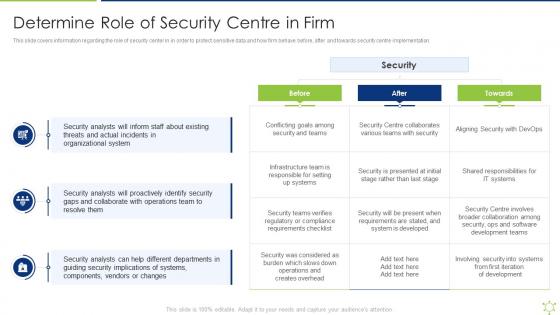 Determine Role Of Security Centre In Firm Enabling It Intelligence Framework
Determine Role Of Security Centre In Firm Enabling It Intelligence FrameworkThis slide covers information regarding the role of security center in in order to protect sensitive data and how firm behave before, after and towards security centre implementation.Present the topic in a bit more detail with this Determine Role Of Security Centre In Firm Enabling It Intelligence Framework Use it as a tool for discussion and navigation on Threats And Actual, Organizational System, Security Analysts This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Enabling Data Security Risk Management Action Plan Enabling It Intelligence Framework
Enabling Data Security Risk Management Action Plan Enabling It Intelligence FrameworkThe data security risk management action plan will help in keeping the track of potential risks that are existing and what are their level, what are the resources required to handle them.Present the topic in a bit more detail with this Enabling Data Security Risk Management Action Plan Enabling It Intelligence Framework Use it as a tool for discussion and navigation on Required Resources, Responsible Person, Communication This template is free to edit as deemed fit for your organization. Therefore download it now.
-
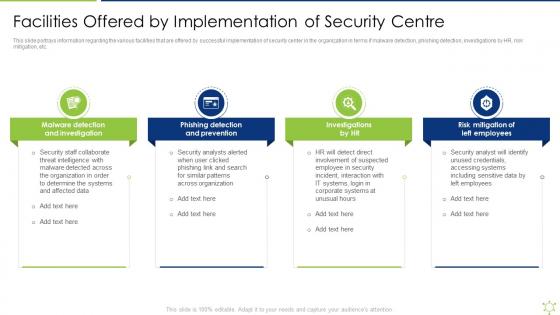 Facilities Offered By Implementation Of Security Centre Enabling It Intelligence Framework
Facilities Offered By Implementation Of Security Centre Enabling It Intelligence FrameworkThis slide portrays information regarding the various facilities that are offered by successful implementation of security center in the organization in terms if malware detection, phishing detection, investigations by HR, risk mitigation, etc.Introducing Facilities Offered By Implementation Of Security Centre Enabling It Intelligence Framework to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Phishing Detection And Prevention, Risk Mitigation Of Left Employees, Malware Detection using this template. Grab it now to reap its full benefits.
-
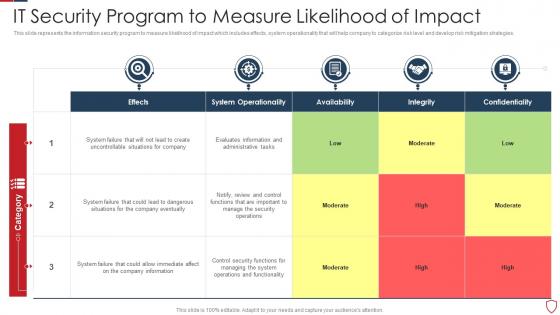 IT Security Program To Measure Likelihood Of Impact
IT Security Program To Measure Likelihood Of ImpactThis slide represents the information security program to measure likelihood of impact which includes effects, system operationality that will help company to categorize risk level and develop risk mitigation strategies. Presenting our well-structured IT Security Program To Measure Likelihood Of Impact. The topics discussed in this slide are System Operationality, Availability, Integrity. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
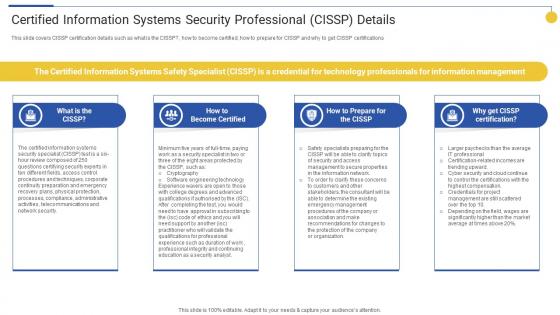 Certified Information Systems Security Professional Top 15 IT Certifications In Demand For 2022
Certified Information Systems Security Professional Top 15 IT Certifications In Demand For 2022This slide covers CISSP certification details such as what is the CISSP, how to become certified, how to prepare for CISSP and why to get CISSP certifications. Increase audience engagement and knowledge by dispensing information using Certified Information Systems Security Professional Top 15 IT Certifications In Demand For 2022. This template helps you present information on four stages. You can also present information on Become Certified, Certification, Information Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Business IT Security Framework With Safety Programs
Business IT Security Framework With Safety ProgramsThis slide outlines the strategic security framework created by an organization to overcome potential external or internal threats along with security programs. Risks include hacking and accidental data disclosure with certain protective programs like anti-spyware software and cloud security. Introducing our premium set of slides with Business IT Security Framework With Safety Programs. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Organization Strategy, Assess Potential Threats, Identify Current Safeguard. So download instantly and tailor it with your information.
-
 IT Security Audit With Risk Level Complete Guide To Conduct Digital Marketing Audit
IT Security Audit With Risk Level Complete Guide To Conduct Digital Marketing AuditThis slide highlights the security audit which showcase the risks related to accounts and user computers and also states the data which are at high risk. Present the topic in a bit more detail with this IT Security Audit With Risk Level Complete Guide To Conduct Digital Marketing Audit. Use it as a tool for discussion and navigation on Risks, Current Value, Risk Level. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
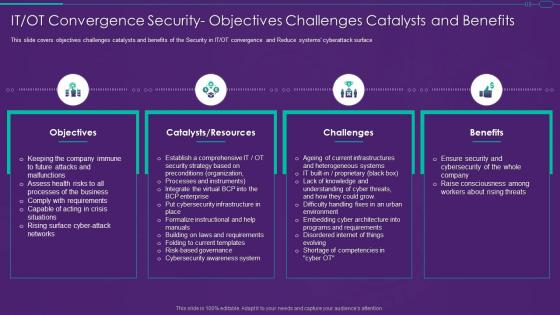 It Ot Convergence Strategy Security Objectives Challenges Catalysts And Benefits
It Ot Convergence Strategy Security Objectives Challenges Catalysts And BenefitsThis slide covers objectives challenges catalysts and benefits of the Security in IT or OT convergence and Reduce systems cyberattack surface Present the topic in a bit more detail with this It Ot Convergence Strategy Security Objectives Challenges Catalysts And Benefits. Use it as a tool for discussion and navigation on Objectives, Catalysts Resources, Challenges. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
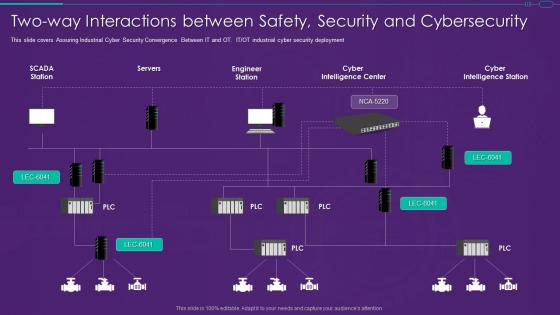 It Ot Convergence Strategy Two Way Interactions Between Safety Security And Cybersecurity
It Ot Convergence Strategy Two Way Interactions Between Safety Security And CybersecurityThis slide covers Assuring Industrial Cyber Security Convergence Between IT and OT. IT or OT industrial cyber security deployment Present the topic in a bit more detail with this It Ot Convergence Strategy Two Way Interactions Between Safety Security And Cybersecurity. Use it as a tool for discussion and navigation on Interactions, Security, Cybersecurity This template is free to edit as deemed fit for your organization. Therefore download it now.
-
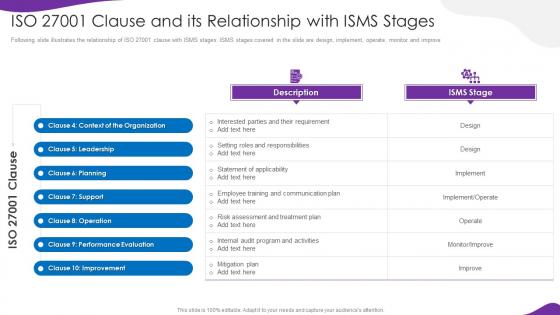 Information Security And Iso 27001 Clause And Its Relationship With Isms Stages
Information Security And Iso 27001 Clause And Its Relationship With Isms StagesFollowing slide illustrates the relationship of ISO 27001 clause with ISMS stages. ISMS stages covered in the slide are design, implement, operate, monitor and improve Deliver an outstanding presentation on the topic using this Information Security And Iso 27001 Clause And Its Relationship With Isms Stages. Dispense information and present a thorough explanation of Relationship, Leadership, Planning using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
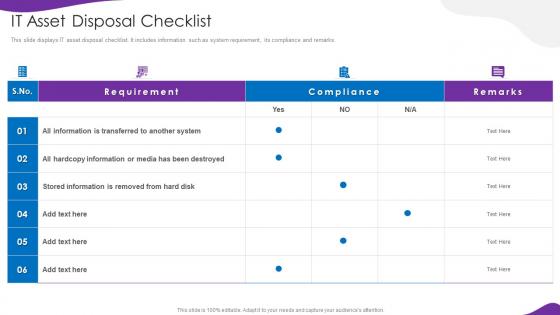 Information Security And Iso 27001 It Asset Disposal Checklist
Information Security And Iso 27001 It Asset Disposal ChecklistThis slide displays IT asset disposal checklist. It includes information such as system requirement, its compliance and remarks. Deliver an outstanding presentation on the topic using this Information Security And Iso 27001 It Asset Disposal Checklist. Dispense information and present a thorough explanation of It Asset Disposal Checklist using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Computing Security Difference Between Cloud Security Solutions And Traditional IT Solutions
Cloud Computing Security Difference Between Cloud Security Solutions And Traditional IT SolutionsThis slide represents the difference between cloud security solutions and traditional IT solutions based on information centers, cost, scalability, and expenses. Increase audience engagement and knowledge by dispensing information using Cloud Computing Security Difference Between Cloud Security Solutions And Traditional IT Solutions. This template helps you present information on two stages. You can also present information on Cloud Security, Traditional It Security, Low Efficiency using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Computing Security Zero Trust Policy And Why You Should Embrace It
Cloud Computing Security Zero Trust Policy And Why You Should Embrace ItThis slide represents the zero trust policy and why organizations should embrace it, and how user access control is managed under the zero trust policy. Increase audience engagement and knowledge by dispensing information using Cloud Computing Security Zero Trust Policy And Why You Should Embrace It. This template helps you present information on three stages. You can also present information on Authentication, Device Validation, Restrict Access using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Difference Between Cloud Security Solutions It Solutions Cloud Information Security
Difference Between Cloud Security Solutions It Solutions Cloud Information SecurityThis slide represents the difference between cloud security solutions and traditional IT solutions based on information centers, cost, scalability, and expenses.Deliver an outstanding presentation on the topic using this Difference Between Cloud Security Solutions It Solutions Cloud Information Security Dispense information and present a thorough explanation of Manage Accounts, Services Proactively, Business Operation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
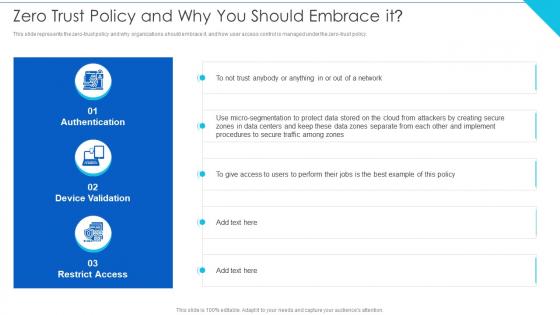 Zero Trust Policy And Why You Should Embrace It Cloud Information Security
Zero Trust Policy And Why You Should Embrace It Cloud Information SecurityThis slide represents the zero trust policy and why organizations should embrace it, and how user access control is managed under the zero trust policy.Deliver an outstanding presentation on the topic using this Zero Trust Policy And Why You Should Embrace It Cloud Information Security Dispense information and present a thorough explanation of Zones Separate, Give Access, Best Example using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
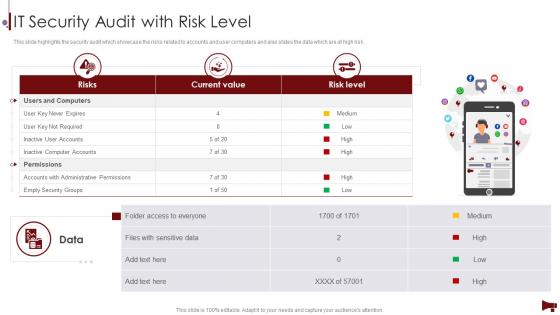 Digital Marketing Audit Of Website IT Security Audit With Risk Level
Digital Marketing Audit Of Website IT Security Audit With Risk LevelThis slide highlights the security audit which showcase the risks related to accounts and user computers and also states the data which are at high risk. Increase audience engagement and knowledge by dispensing information using Digital Marketing Audit Of Website IT Security Audit With Risk Level. This template helps you present information on three stages. You can also present information on Current Value, Risk Level, Inactive Computer Accounts using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
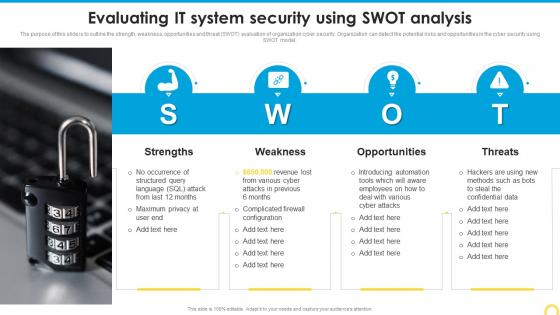 Evaluating It System Security Using Swot Analysis Building A Security Awareness Program
Evaluating It System Security Using Swot Analysis Building A Security Awareness ProgramThe purpose of this slide is to outline the strength, weakness, opportunities and threat SWOT evaluation of organization cyber security. Organization can detect the potential risks and opportunities in the cyber security using SWOT model. Increase audience engagement and knowledge by dispensing information using Evaluating It System Security Using Swot Analysis Building A Security Awareness Program. This template helps you present information on four stages. You can also present information on Strengths, Weakness, Opportunities, Threats using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Major Saas Security Challenges For It Department
Major Saas Security Challenges For It DepartmentThe following slide highlights some SaaS security challenges faced by IT team to plan mitigation actions. It mainly includes file security, insider threat, privilege access etc. Introducing our premium set of slides with Major Saas Security Challenges For It Department. Elucidate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Department, Neglecting Employees, Permissions. So download instantly and tailor it with your information.
-
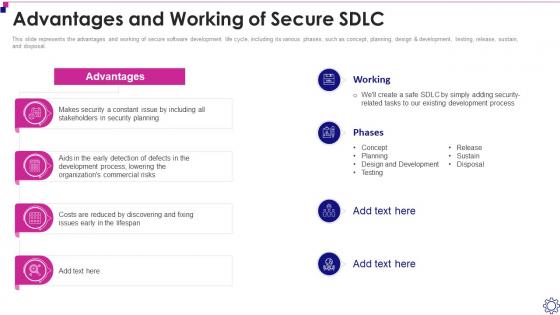 Advantages And Working Of Secure Sdlc Software Development Life Cycle It
Advantages And Working Of Secure Sdlc Software Development Life Cycle ItThis slide represents the advantages and working of secure software development life cycle, including its various phases, such as concept, planning, design and development, testing, release, sustain, and disposal. Present the topic in a bit more detail with this Advantages And Working Of Secure Sdlc Software Development Life Cycle It. Use it as a tool for discussion and navigation on Organizations, Commercial, Development. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
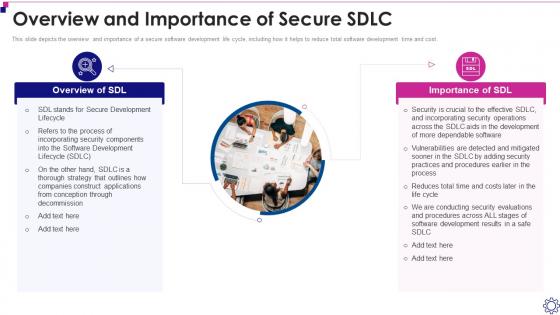 Overview And Importance Of Secure Sdlc Software Development Life Cycle It
Overview And Importance Of Secure Sdlc Software Development Life Cycle ItThis slide depicts the overview and importance of a secure software development life cycle, including how it helps to reduce total software development time and cost. Deliver an outstanding presentation on the topic using this Overview And Importance Of Secure Sdlc Software Development Life Cycle It. Dispense information and present a thorough explanation of Secure, Development, Components using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
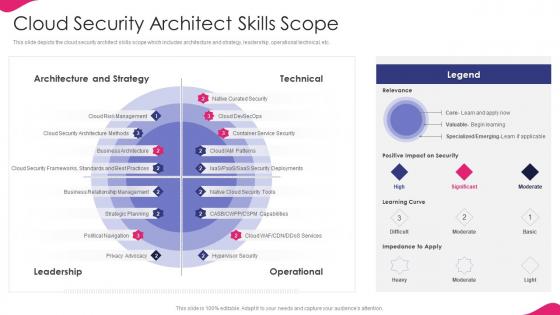 It Strategy For Digitalization In Business Cloud Security Architect Skills Scope
It Strategy For Digitalization In Business Cloud Security Architect Skills ScopeThis slide depicts the cloud security architect skills scope which includes architecture and strategy, leadership, operational technical, etc. Deliver an outstanding presentation on the topic using this It Strategy For Digitalization In Business Cloud Security Architect Skills Scope. Dispense information and present a thorough explanation of Architecture, Strategy, Leadership using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Role Of Chief Information Security Officer It Strategy For Digitalization In Business
Role Of Chief Information Security Officer It Strategy For Digitalization In BusinessThis slide covers the role of chief information security officer which includes embed security information, stay informed, hire solid security staff, etc. Introducing Role Of Chief Information Security Officer It Strategy For Digitalization In Business to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Business Advisor, Team Members, Security Information, using this template. Grab it now to reap its full benefits.
-
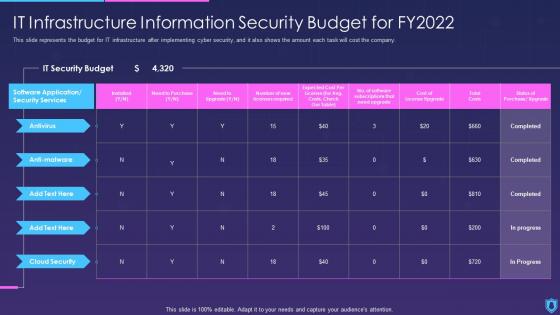 Information Security It Infrastructure Information Security Budget For Fy2022
Information Security It Infrastructure Information Security Budget For Fy2022This slide represents the budget for IT infrastructure after implementing cyber security, and it also shows the amount each task will cost the company. Present the topic in a bit more detail with this Information Security It Infrastructure Information Security Budget For Fy2022. Use it as a tool for discussion and navigation on Infrastructure, Information, Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Security What Is Information Security And How Does It Work
Information Security What Is Information Security And How Does It WorkThis slide defines the meaning of cyber security and how it helps to prevent data through different methods and techniques. Increase audience engagement and knowledge by dispensing information using Information Security What Is Information Security And How Does It Work. This template helps you present information on five stages. You can also present information on Techniques, Procedures, Approach using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 It Security Audit With Risk Level Procedure To Perform Digital Marketing Audit
It Security Audit With Risk Level Procedure To Perform Digital Marketing AuditThis slide highlights the security audit which showcase the risks related to accounts and user computers and also states the data which are at high risk. Present the topic in a bit more detail with this It Security Audit With Risk Level Procedure To Perform Digital Marketing Audit. Use it as a tool for discussion and navigation on Inactive User Accounts, Inactive Computer Accounts, Empty Security Groups. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
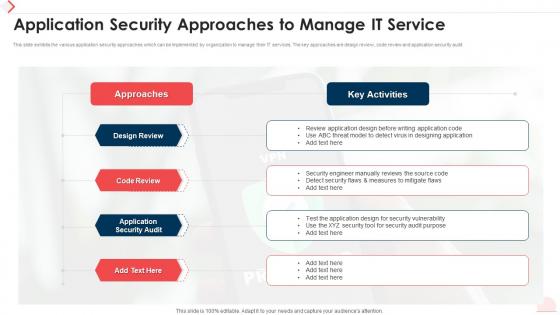 Application Security Approaches To Manage IT Service
Application Security Approaches To Manage IT ServiceThis slide exhibits the various application security approaches which can be implemented by organization to manage their IT services. The key approaches are design review, code review and application security audit. Introducing our Application Security Approaches To Manage IT Service set of slides. The topics discussed in these slides are Approaches, Design Review, Code Review, Key Activities. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Icon For Managed IT Security Service
Icon For Managed IT Security ServicePresenting our set of slides with Icon For Managed IT Security Service. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Icon For Managed, IT Security Service.
-
 Response plan of it security incident
Response plan of it security incidentThis slide covers the response plan of information security incident which shows sections and their description such as introduction, using incident response plan, event handling, incident topology, post-incident procedures, etc. Introducing our premium set of slides with Response Plan Of It Security Incident. Ellicudate the eight stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Response Plan Of It Security Incident. So download instantly and tailor it with your information.
-
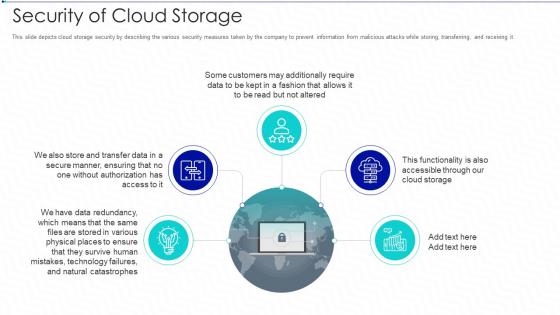 Cloud storage it security of cloud storage ppt slides vector
Cloud storage it security of cloud storage ppt slides vectorThis slide depicts cloud storage security by describing the various security measures taken by the company to prevent information from malicious attacks while storing, transferring, and receiving it. Increase audience engagement and knowledge by dispensing information using Cloud Storage IT Security Of Cloud Storage Ppt Slides Vector. This template helps you present information on five stages. You can also present information on Customers Access, Cloud Storage, Technology Failures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
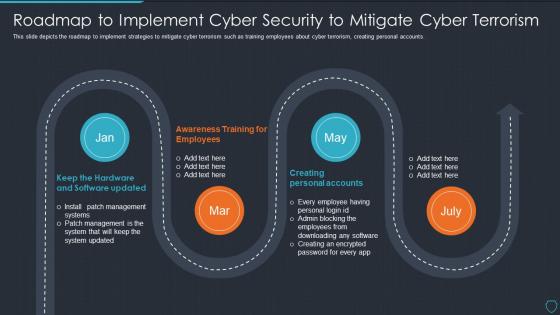 Cyberterrorism it roadmap to implement cyber security to mitigate cyber terrorism
Cyberterrorism it roadmap to implement cyber security to mitigate cyber terrorismThis slide depicts the roadmap to implement strategies to mitigate cyber terrorism such as training employees about cyber terrorism, creating personal accounts. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Roadmap To Implement Cyber Security To Mitigate Cyber Terrorism. This template helps you present information on four stages. You can also present information on Creating Personal Accounts, Awareness Training Employees, Keep Hardware And Software Updated using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
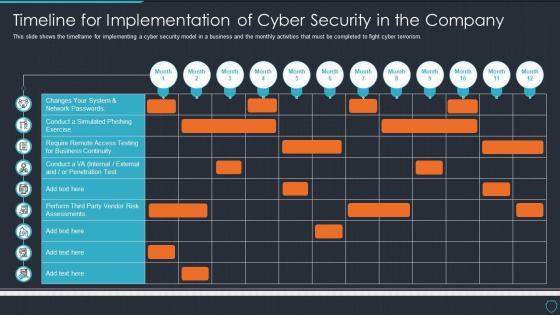 Cyberterrorism it timeline for implementation of cyber security in the company
Cyberterrorism it timeline for implementation of cyber security in the companyThis slide shows the timeframe for implementing a cyber security model in a business and the monthly activities that must be completed to fight cyber terrorism. Present the topic in a bit more detail with this Cyberterrorism IT Timeline For Implementation Of Cyber Security In The Company. Use it as a tool for discussion and navigation on Changes System, Network Passwords, Penetration Test. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
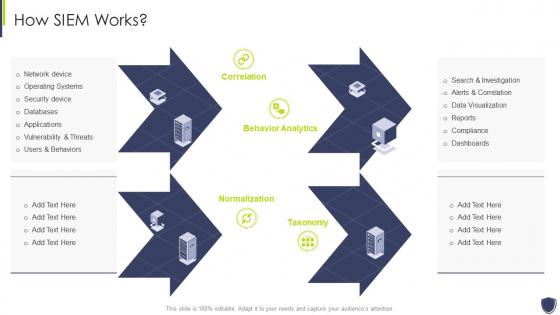 Improve it security with vulnerability management how siem works
Improve it security with vulnerability management how siem worksIncrease audience engagement and knowledge by dispensing information using Improve It Security With Vulnerability Management How Siem Works. This template helps you present information on four stages. You can also present information on Databases, Applications, Security Device using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
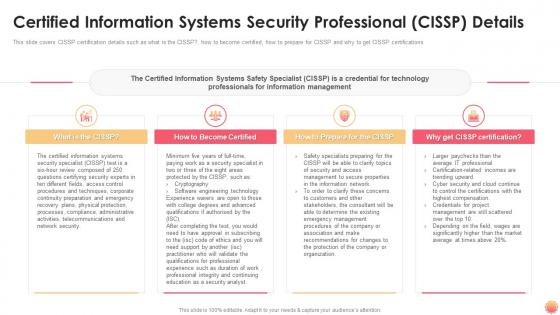 It certification collections certified information systems security professional cissp details
It certification collections certified information systems security professional cissp detailsThis slide covers CISSP certification details such as what is the CISSP, how to become certified, how to prepare for CISSP and why to get CISSP certifications Increase audience engagement and knowledge by dispensing information using IT Certification Collections Certified Information Systems Security Professional CISSP Details. This template helps you present information on four stages. You can also present information on Certified Information Systems Security Professional CISSP Details using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Hacking it roadmap to implement new security strategies
Hacking it roadmap to implement new security strategiesThis slide represents the roadmap to implement new security strategies, including hiring new professionals, new software or hardware installation, employee awareness sessions, etc. Increase audience engagement and knowledge by dispensing information using Hacking It Roadmap To Implement New Security Strategies. This template helps you present information on five stages. You can also present information on Roadmap To Implement New Security Strategies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Hacking it use of security programs ppt slides design templates
Hacking it use of security programs ppt slides design templatesThis slide represents the usage of security programs such as secure socket layer, web application firewall, website, and software scanners that will secure and help detect malicious attacks. Increase audience engagement and knowledge by dispensing information using Hacking It Use Of Security Programs Ppt Slides Design Templates. This template helps you present information on three stages. You can also present information on Secure Sockets Layer, Web Application Firewall, Website And Software Scanners using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Agenda of improve it security with vulnerability management
Agenda of improve it security with vulnerability managementIntroducing Agenda Of Improve It Security With Vulnerability Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Vulnerability, Management, Agenda, using this template. Grab it now to reap its full benefits.
-
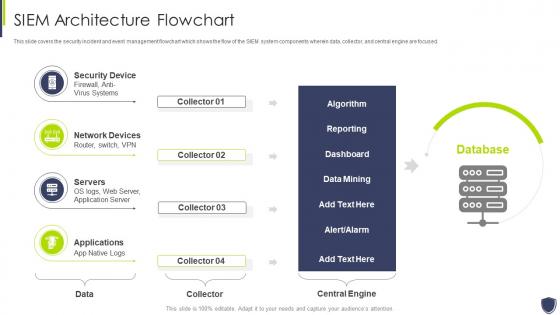 Architecture flowchart improve it security with vulnerability management
Architecture flowchart improve it security with vulnerability managementThis slide covers the security incident and event management flowchart which shows the flow of the SIEM system components wherein data, collector, and central engine are focused. Present the topic in a bit more detail with this Architecture Flowchart Improve It Security With Vulnerability Management. Use it as a tool for discussion and navigation on Security Device, Network Devices, Servers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
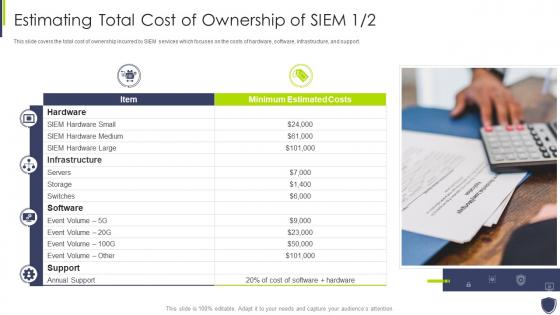 Estimating total cost of ownership improve it security vulnerability management
Estimating total cost of ownership improve it security vulnerability managementThis slide covers the total cost of ownership incurred by SIEM services which focuses on the costs of hardware, software, infrastructure, and support. Deliver an outstanding presentation on the topic using this Estimating Total Cost Of Ownership Improve It Security Vulnerability Management. Dispense information and present a thorough explanation of Estimating Total Cost Of Ownership Of SIEM using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Icons slide for improve it security with vulnerability management
Icons slide for improve it security with vulnerability managementIntroducing our well researched set of slides titled Icons Slide For Improve It Security With Vulnerability Management. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
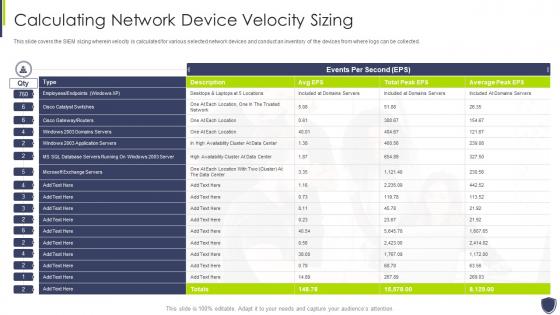 Improve it security vulnerability management calculating network device velocity sizing
Improve it security vulnerability management calculating network device velocity sizingThis slide covers the SIEM sizing wherein velocity is calculated for various selected network devices and conduct an inventory of the devices from where logs can be collected. Present the topic in a bit more detail with this Improve It Security Vulnerability Management Calculating Network Device Velocity Sizing. Use it as a tool for discussion and navigation on Calculating Network Device Velocity Sizing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
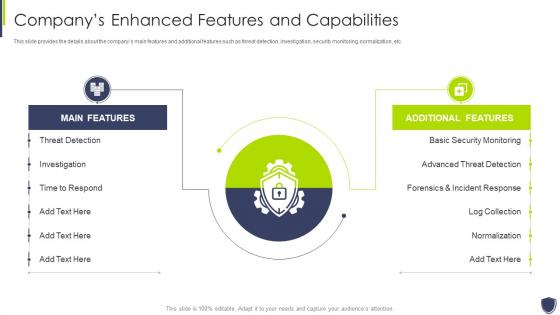 Improve it security vulnerability management companys enhanced features capabilities
Improve it security vulnerability management companys enhanced features capabilitiesThis slide provides the details about the companys main features and additional features such as threat detection, investigation, security monitoring, normalization, etc. Deliver an outstanding presentation on the topic using this Improve It Security Vulnerability Management Companys Enhanced Features Capabilities. Dispense information and present a thorough explanation of Threat Detection, Investigation, Time To Respond using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
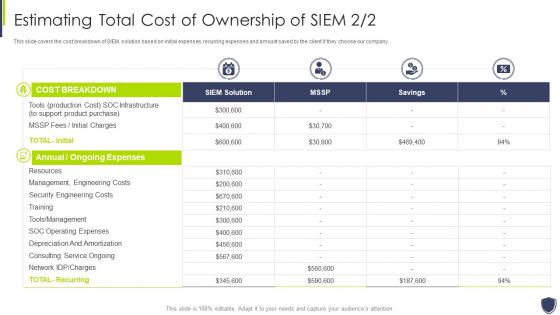 Improve it security vulnerability management estimating total cost ownership siem
Improve it security vulnerability management estimating total cost ownership siemThis slide covers the cost breakdown of SIEM solution based on initial expenses, recurring expenses and amount saved by the client if they choose our company. Present the topic in a bit more detail with this Improve It Security Vulnerability Management Estimating Total Cost Ownership Siem. Use it as a tool for discussion and navigation on Management, Engineering, Ownership. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
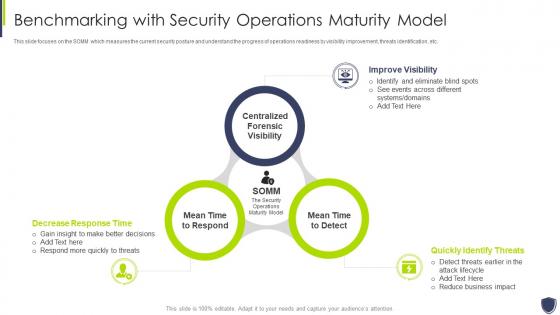 Improve it security with vulnerability benchmarking security operations maturity model
Improve it security with vulnerability benchmarking security operations maturity modelThis slide focuses on the SOMM which measures the current security posture and understand the progress of operations readiness by visibility improvement, threats identification, etc. Introducing Improve It Security With Vulnerability Benchmarking Security Operations Maturity Model to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Improve Visibility, Quickly Identify Threats, Decrease Response Time, using this template. Grab it now to reap its full benefits.
-
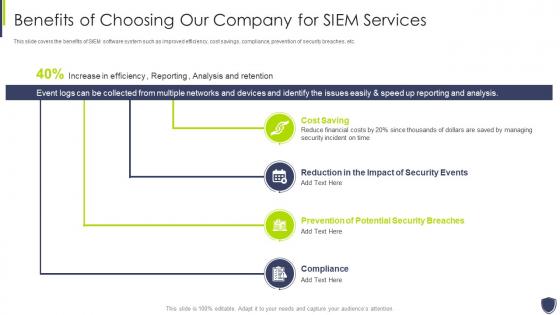 Improve it security with vulnerability benefits of choosing our company siem services
Improve it security with vulnerability benefits of choosing our company siem servicesThis slide covers the benefits of SIEM software system such as improved efficiency, cost savings, compliance, prevention of security breaches, etc. Increase audience engagement and knowledge by dispensing information using Improve It Security With Vulnerability Benefits Of Choosing Our Company Siem Services. This template helps you present information on four stages. You can also present information on Cost Saving, Reduction In The Impact Of Security Events, Compliance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
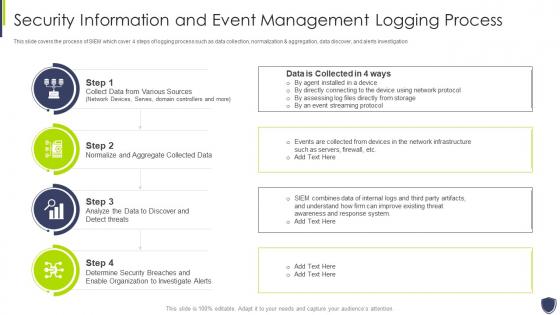 Improve it security with vulnerability information and event management logging process
Improve it security with vulnerability information and event management logging processThis slide covers the process of SIEM which cover 4 steps of logging process such as data collection, normalization and aggregation, data discover, and alerts investigation Introducing Improve It Security With Vulnerability Information And Event Management Logging Process to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Information, Management, Process, using this template. Grab it now to reap its full benefits.
-
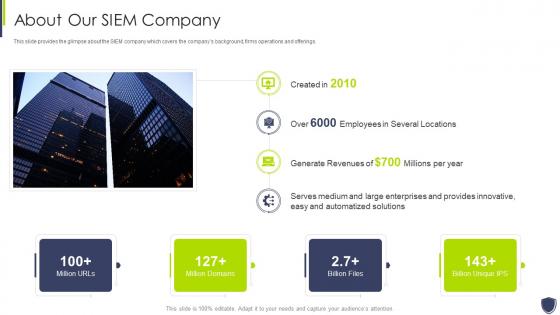 Improve it security with vulnerability management about our siem company
Improve it security with vulnerability management about our siem companyThis slide provides the glimpse about the SIEM company which covers the companys background, firms operations and offerings. Present the topic in a bit more detail with this Improve It Security With Vulnerability Management About Our Siem Company. Use it as a tool for discussion and navigation on Automatized, Solutions, Innovative. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
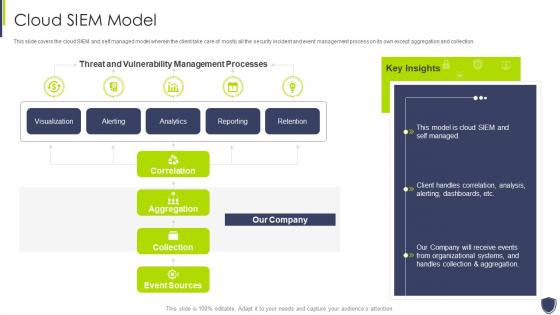 Improve it security with vulnerability management cloud siem model
Improve it security with vulnerability management cloud siem modelThis slide covers the cloud SIEM and self managed model wherein the client take care of mostly all the security incident and event management process on its own except aggregation and collection. Deliver an outstanding presentation on the topic using this Improve It Security With Vulnerability Management Cloud Siem Model. Dispense information and present a thorough explanation of Vulnerability, Management, Processes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Improve it security with vulnerability management competitive advantage
Improve it security with vulnerability management competitive advantageThis slide covers the competitive advantage scoring for security information and event management based on different factors such as value, deployment, ease of use, support, etc. Present the topic in a bit more detail with this Improve It Security With Vulnerability Management Competitive Advantage. Use it as a tool for discussion and navigation on Siem Competitive Advantage. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Improve it security with vulnerability management event management services
Improve it security with vulnerability management event management servicesThis slide covers the SIEM services offered by our company such as data aggregation, correlation, security alerts, dashboards, retention, forensic analysis, IT compliance, threat detection, etc. Increase audience engagement and knowledge by dispensing information using Improve It Security With Vulnerability Management Event Management Services. This template helps you present information on eight stages. You can also present information on Data Aggregation, Data Correlation, Security Alert using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
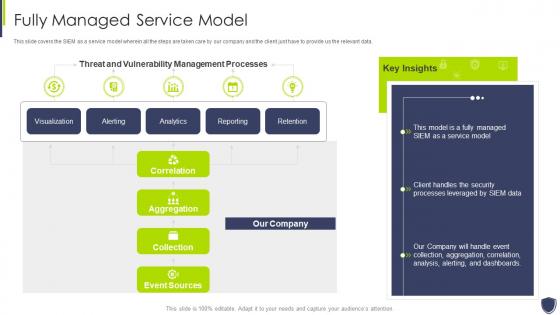 Improve it security with vulnerability management fully managed service model
Improve it security with vulnerability management fully managed service modelThis slide covers the SIEM as a service model wherein all the steps are taken care by our company and the client just have to provide us the relevant data. Deliver an outstanding presentation on the topic using this Improve It Security With Vulnerability Management Fully Managed Service Model. Dispense information and present a thorough explanation of Vulnerability, Management, Processes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
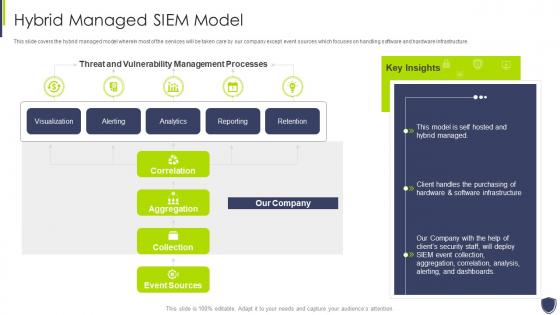 Improve it security with vulnerability management hybrid managed siem model
Improve it security with vulnerability management hybrid managed siem modelThis slide covers the hybrid managed model wherein most of the services will be taken care by our company except event sources which focuses on handling software and hardware infrastructure. Deliver an outstanding presentation on the topic using this Improve It Security With Vulnerability Management Hybrid Managed Siem Model. Dispense information and present a thorough explanation of Vulnerability, Management, Processes using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Improve it security with vulnerability management integrations
Improve it security with vulnerability management integrationsPresent the topic in a bit more detail with this Improve It Security With Vulnerability Management Integrations. Use it as a tool for discussion and navigation on Applications And Devices, Network Logs, Security Events. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
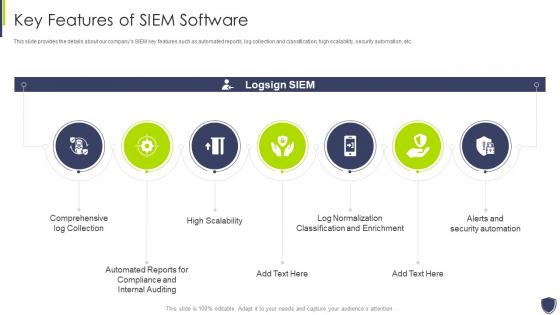 Improve it security with vulnerability management key features of siem software
Improve it security with vulnerability management key features of siem softwareThis slide provides the details about our companys SIEM key features such as automated reports, log collection and classification, high scalability, security automation, etc. Increase audience engagement and knowledge by dispensing information using Improve It Security With Vulnerability Management Key Features Of Siem Software. This template helps you present information on seven stages. You can also present information on Comprehensive, Compliance, Classification using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Improve it security with vulnerability management log management services
Improve it security with vulnerability management log management servicesThis slide covers the log management services offered by our company such as collection and normalization, search speed, real time analysis, decision making process etc. Introducing Improve It Security With Vulnerability Management Log Management Services to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Collection And Normalization, Search Speed, Real Time Analysis, using this template. Grab it now to reap its full benefits.
-
 Improve it security with vulnerability management logging sources
Improve it security with vulnerability management logging sourcesThis slide covers the logging sources for SIEM which uses different devices such as security, network, servers, and applications. Increase audience engagement and knowledge by dispensing information using Improve It Security With Vulnerability Management Logging Sources. This template helps you present information on four stages. You can also present information on Security Devices, Network Devices, Servers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Improve it security with vulnerability management need for siem software company
Improve it security with vulnerability management need for siem software companyThis slide covers the need for the SIEM software which focuses on detecting incidents, compliance regulations, and incident management Introducing Improve It Security With Vulnerability Management Need For Siem Software Company to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Detecting Incidents, Compliance With Regulations, Efficient Incident Management, using this template. Grab it now to reap its full benefits.
-
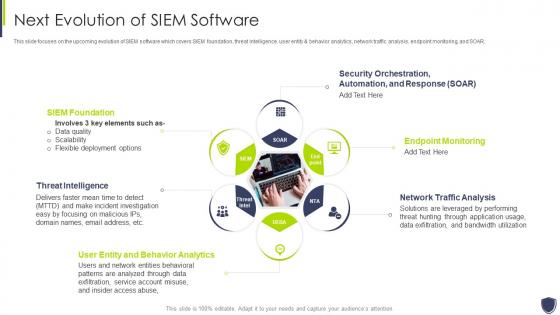 Improve it security with vulnerability management next evolution of siem software
Improve it security with vulnerability management next evolution of siem softwareThis slide focuses on the upcoming evolution of SIEM software which covers SIEM foundation, threat intelligence, user entity and behavior analytics, network traffic analysis, endpoint monitoring, and SOAR. Increase audience engagement and knowledge by dispensing information using Improve It Security With Vulnerability Management Next Evolution Of Siem Software. This template helps you present information on six stages. You can also present information on Foundation, Threat Intelligence, Analytics using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
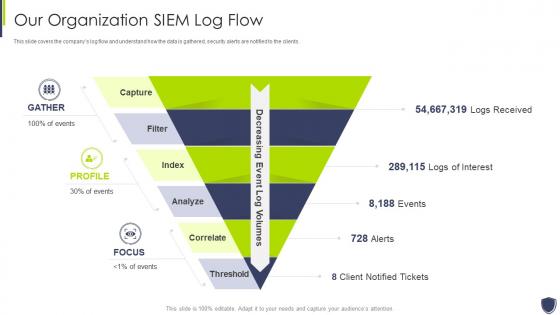 Improve it security with vulnerability management organization siem log flow
Improve it security with vulnerability management organization siem log flowThis slide covers the companys log flow and understand how the data is gathered, security alerts are notified to the clients. Introducing Improve It Security With Vulnerability Management Organization Siem Log Flow to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Our Organization Siem Log Flow, using this template. Grab it now to reap its full benefits.



