Powerpoint Templates and Google slides for Network Attacks Experienced By Company In Previous Financial Year
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
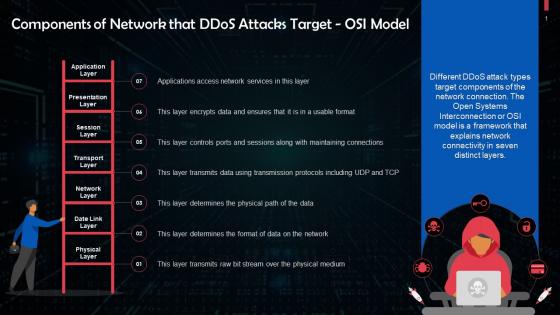 Components Of Network Targeted By DDoS Attacks OSI Model Training Ppt
Components Of Network Targeted By DDoS Attacks OSI Model Training PptPresenting Components of Network Targeted by DDoS Attacks OSI Model. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
 Anycast Network Diffusion To Prevent DDoS Attacks Training Ppt
Anycast Network Diffusion To Prevent DDoS Attacks Training PptPresenting Anycast Network Diffusion to Prevent DDoS Attacks. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
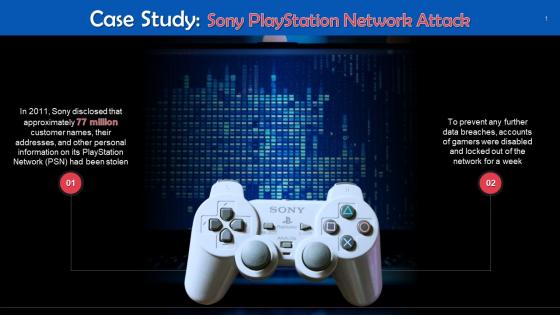 Sony Playstation Network Attack Case Study Training Ppt
Sony Playstation Network Attack Case Study Training PptPresenting Sony Playstation Network Attack Case Study. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Interesting Facts On Sony Playstation Network Attack Training Ppt
Interesting Facts On Sony Playstation Network Attack Training PptPresenting Interesting Facts on Sony Playstation Network Attack. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 User Wallet Attack On Blockchain Network Training Ppt
User Wallet Attack On Blockchain Network Training PptPresenting User Wallet Attack on Blockchain Network. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. All slides are customizable. You can add or delete the content as per your need. Download this professionally designed business presentation, add your content, and present it with confidence.
-
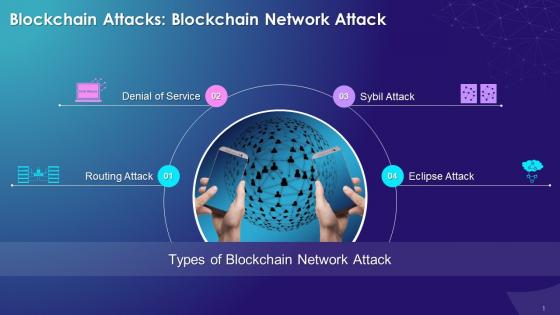 Multiple Types Of Blockchain Network Attack On Blockchain Network Training Ppt
Multiple Types Of Blockchain Network Attack On Blockchain Network Training PptPresenting Multiple Types of Blockchain Network Attack on Blockchain Network. Our PowerPoint experts have included all the necessary templates, designs, icons, graphs, and other essential material. This deck is well crafted by extensive research. Slides consist of amazing visuals and appropriate content. These PPT slides can be instantly downloaded with just a click. Compatible with all screen types and monitors. Supports Google Slides. Premium Customer Support is available. Suitable for use by managers, employees, and organizations. These slides are easily customizable. You can edit the color, text, icon, and font size to suit your requirements.
-
 Sybil Attack On Blockchain Network Training Ppt
Sybil Attack On Blockchain Network Training PptPresenting Sybil Attack on Blockchain Network. This slide is well crafted and designed by our PowerPoint specialists. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. You can add or delete the content as per your need.
-
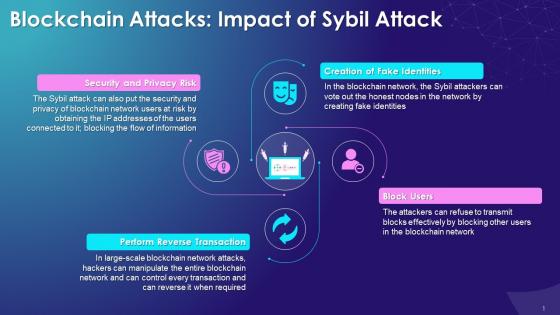 Impact Of Sybil Attack On Blockchain Network Training Ppt
Impact Of Sybil Attack On Blockchain Network Training PptPresenting Impact of Sybil Attack on Blockchain Network. These slides are 100 Percent made in PowerPoint and are compatible with all screen types and monitors. They also support Google Slides. Premium Customer Support is available. Suitable for use by managers, employees, and organizations. These slides are easily customizable. You can edit the color, text, icon, and font size to suit your requirements.
-
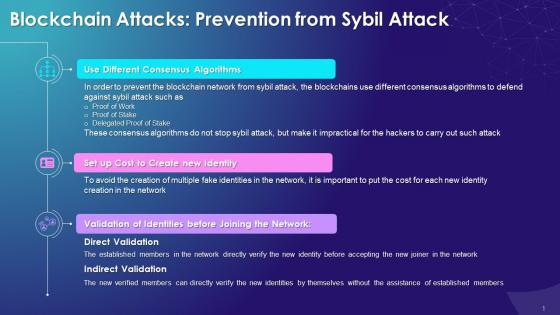 Prevention From Sybil Attack On Blockchain Network Training Ppt
Prevention From Sybil Attack On Blockchain Network Training PptPresenting Prevention from Sybil Attack on Blockchain Network. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. All slides are customizable. You can add or delete the content as per your need. Download this professionally designed business presentation, add your content, and present it with confidence.
-
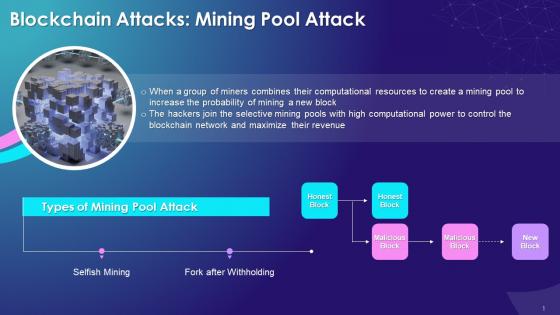 Mining Pool Attack On Blockchain Network Training Ppt
Mining Pool Attack On Blockchain Network Training PptPresenting Mining Pool Attack on Blockchain Network. Our PowerPoint experts have included all the necessary templates, designs, icons, graphs, and other essential material. This deck is well crafted by extensive research. Slides consist of amazing visuals and appropriate content. These PPT slides can be instantly downloaded with just a click. Compatible with all screen types and monitors. Supports Google Slides. Premium Customer Support is available. Suitable for use by managers, employees, and organizations. These slides are easily customizable. You can edit the color, text, icon, and font size to suit your requirements.
-
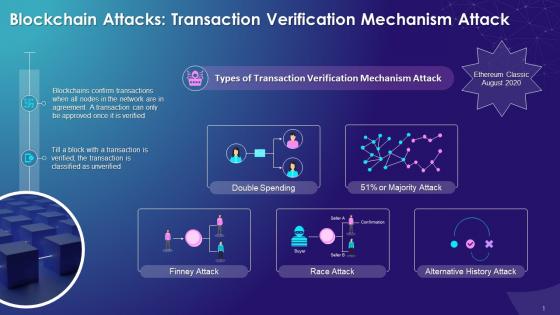 Transaction Verification Mechanism Attack On Blockchain Network Training Ppt
Transaction Verification Mechanism Attack On Blockchain Network Training PptPresenting Transaction Verification Mechanism Attack on Blockchain Network. This slide is well crafted and designed by our PowerPoint specialists. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. You can add or delete the content as per your need.
-
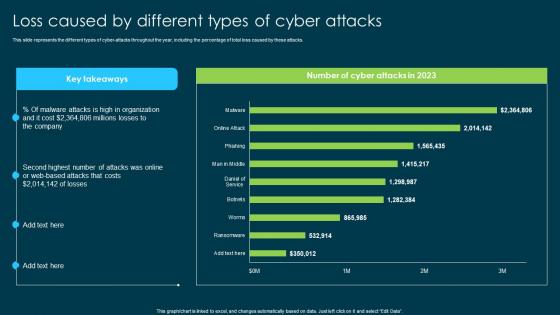 Ethical Hacking And Network Security Loss Caused By Different Types Of Cyber Attacks
Ethical Hacking And Network Security Loss Caused By Different Types Of Cyber AttacksThis slide represents the different types of cyber-attacks throughout the year, including the percentage of total loss caused by these attacks. Present the topic in a bit more detail with this Ethical Hacking And Network Security Loss Caused By Different Types Of Cyber Attacks. Use it as a tool for discussion and navigation on Cyber Attacks Throughout, Online Or Web Based Attacks, Malware Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
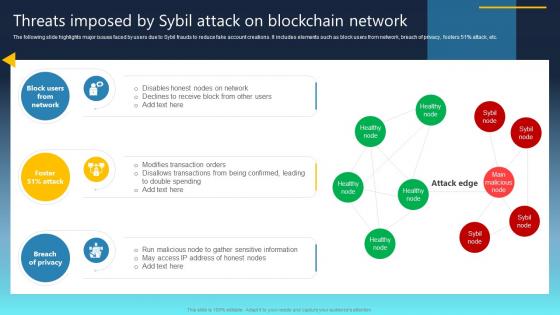 Ultimate Guide For Blockchain Threats Imposed By Sybil Attack On Blockchain Network BCT SS
Ultimate Guide For Blockchain Threats Imposed By Sybil Attack On Blockchain Network BCT SSThe following slide represents the number of cryptocurrencies theft incidents by total amount to prevent attackers from unauthorized access. It includes elements such as ronin, poly network, wormhole, bitmart, venus, cream finance, along with key insights, etc. Deliver an outstanding presentation on the topic using this Ultimate Guide For Blockchain Threats Imposed By Sybil Attack On Blockchain Network BCT SS Dispense information and present a thorough explanation of Breach Of Privacy, Block Users From Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
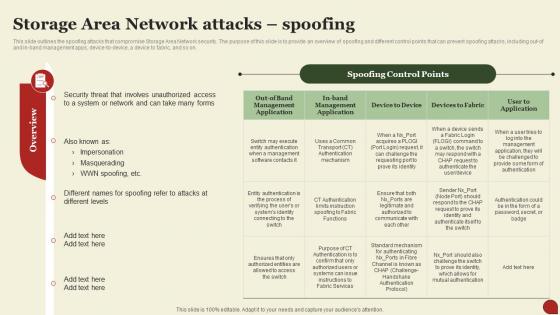 Storage Area Network San Storage Area Network Attacks Spoofing
Storage Area Network San Storage Area Network Attacks SpoofingThis Slide Outlines The Spoofing Attacks That Compromise Storage Area Network Security. The Purpose Of This Slide Is To Provide An Overview Of Spoofing And Different Control Points That Can Prevent Spoofing Attacks, Including Out-Of And In-Band Management Apps, Device-To-Device, A Device To Fabric, And So On. Deliver An Outstanding Presentation On The Topic Using This Storage Area Network San Storage Area Network Attacks Spoofing. Dispense Information And Present A Thorough Explanation Of Impersonation, Masquerading, Storage Using The Slides Given. This Template Can Be Altered And Personalized To Fit Your Needs. It Is Also Available For Immediate Download. So Grab It Now.
-
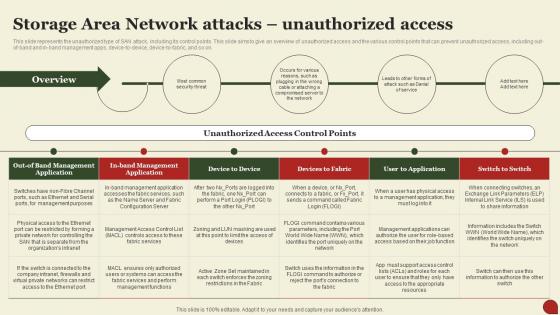 Storage Area Network San Storage Area Network Attacks Unauthorized Access
Storage Area Network San Storage Area Network Attacks Unauthorized AccessThis Slide Represents The Unauthorized Type Of SAN Attack, Including Its Control Points. This Slide Aims To Give An Overview Of Unauthorized Access And The Various Control Points That Can Prevent Unauthorized Access, Including Out-Of-Band And In-Band Management Apps, Device-To-Device, Device-To-Fabric, And So On. Present The Topic In A Bit More Detail With This Storage Area Network San Storage Area Network Attacks Unauthorized Access. Use It As A Tool For Discussion And Navigation On Unauthorized, Overview, Service. This Template Is Free To Edit As Deemed Fit For Your Organization. Therefore Download It Now.
-
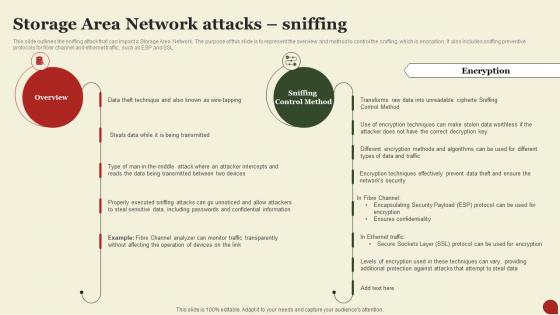 Storage Area Network Attacks Sniffing Storage Area Network San
Storage Area Network Attacks Sniffing Storage Area Network SanThis Slide Outlines The Sniffing Attack That Can Impact A Storage Area Network. The Purpose Of This Slide Is To Represent The Overview And Method To Control The Sniffing, Which Is Encryption. It Also Includes Sniffing Preventive Protocols For Fiber Channel And Ethernet Traffic, Such As ESP And SSL. Present The Topic In A Bit More Detail With This Storage Area Network Attacks Sniffing Storage Area Network San. Use It As A Tool For Discussion And Navigation On Encryption, Techniques, Confidentiality. This Template Is Free To Edit As Deemed Fit For Your Organization. Therefore Download It Now.
-
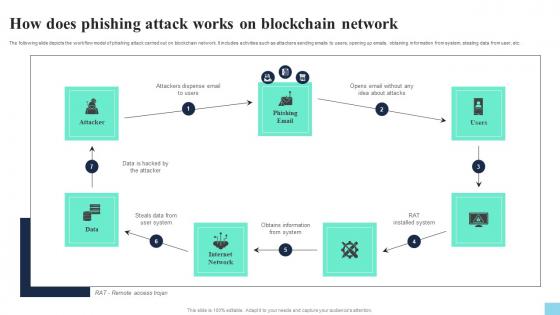 How Does Phishing Attack Works On Blockchain Network Hands On Blockchain Security Risk BCT SS V
How Does Phishing Attack Works On Blockchain Network Hands On Blockchain Security Risk BCT SS VThe following slide depicts the workflow model of phishing attack carried out on blockchain network. It includes activities such as attackers sending emails to users, opening up emails, obtaining information from system, stealing data from user, etc. Present the topic in a bit more detail with this How Does Phishing Attack Works On Blockchain Network Hands On Blockchain Security Risk BCT SS V. Use it as a tool for discussion and navigation on Attacker, Phishing Email, Internet Network. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Impact Of Eclipse Attack On Peer To Peer Network Hands On Blockchain Security Risk BCT SS V
Impact Of Eclipse Attack On Peer To Peer Network Hands On Blockchain Security Risk BCT SS VThe following slide illustrates the impact of eclipse attack on functioning of blockchain network to plan strategies and action steps. It includes elements such as leading to double spending, centralization, disrupting mining power, network instability, monetary loss, etc. Introducing Impact Of Eclipse Attack On Peer To Peer Network Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Centralization, Disrupts Mining Power, Network Instability, using this template. Grab it now to reap its full benefits.
-
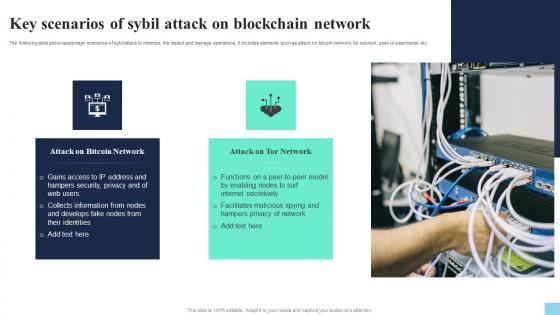 Key Scenarios Of Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS V
Key Scenarios Of Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS VThe following slide showcases major scenarios of sybil attack to minimize the impact and manage operations. It includes elements such as attack on bitcoin network, tor network, peer-to-peer model, etc. Introducing Key Scenarios Of Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Attack On Bitcoin Network, Attack On Tor Network, using this template. Grab it now to reap its full benefits.
-
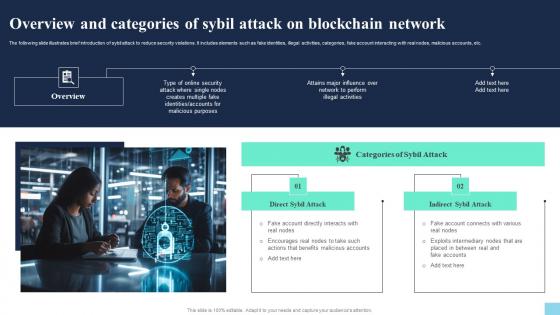 Overview And Categories Of Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS V
Overview And Categories Of Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS VThe following slide illustrates brief introduction of sybil attack to reduce security violations. It includes elements such as fake identities, illegal activities, categories, fake account interacting with real nodes, malicious accounts, etc. Introducing Overview And Categories Of Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Direct Sybil Attack, Indirect Sybil Attack, using this template. Grab it now to reap its full benefits.
-
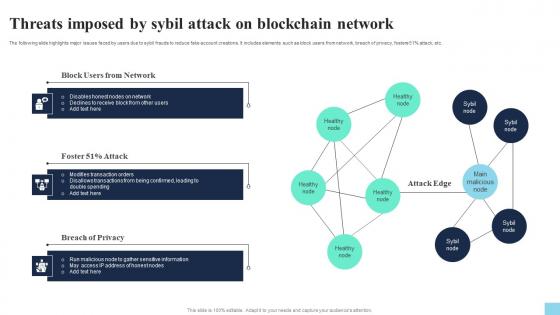 Threats Imposed By Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS V
Threats Imposed By Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS VThe following slide highlights major issues faced by users due to sybil frauds to reduce fake account creations. It includes elements such as block users from network, breach of privacy, fosters 51percentage attack, etc. Increase audience engagement and knowledge by dispensing information using Threats Imposed By Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS V. This template helps you present information on three stages. You can also present information on Block Users From Network, Attack, Breach Of Privacy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
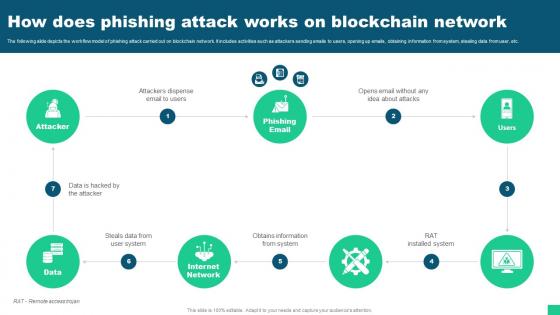 How Does Phishing Attack Works On Blockchain Network Guide For Blockchain BCT SS V
How Does Phishing Attack Works On Blockchain Network Guide For Blockchain BCT SS VThe following slide depicts the workflow model of phishing attack carried out on blockchain network. It includes activities such as attackers sending emails to users, opening up emails, obtaining information from system, stealing data from user, etc. Introducing How Does Phishing Attack Works On Blockchain Network Guide For Blockchain BCT SS V to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Attacker, Phishing Email, Internet Network using this template. Grab it now to reap its full benefits.
-
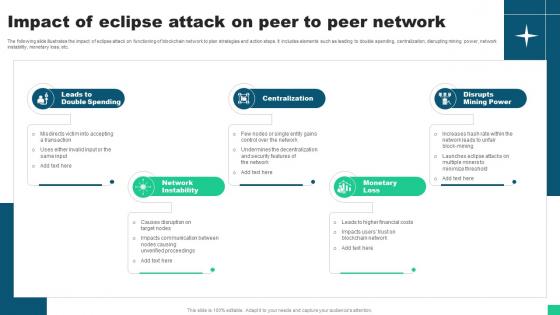 Impact Of Eclipse Attack On Peer To Peer Network Guide For Blockchain BCT SS V
Impact Of Eclipse Attack On Peer To Peer Network Guide For Blockchain BCT SS VThe following slide illustrates the impact of eclipse attack on functioning of blockchain network to plan strategies and action steps. It includes elements such as leading to double spending, centralization, disrupting mining power, network instability, monetary loss, etc. Introducing Impact Of Eclipse Attack On Peer To Peer Network Guide For Blockchain BCT SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Double Spending, Network Instability, Centralization using this template. Grab it now to reap its full benefits.
-
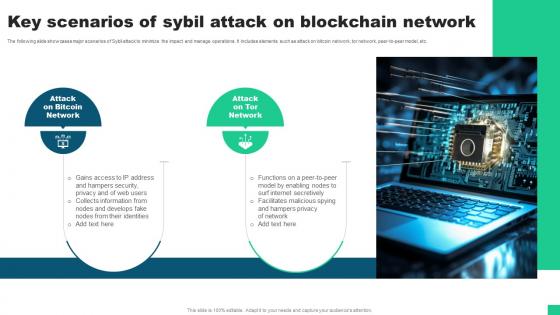 Key Scenarios Of Sybil Attack On Blockchain Network Guide For Blockchain BCT SS V
Key Scenarios Of Sybil Attack On Blockchain Network Guide For Blockchain BCT SS VThe following slide showcases major scenarios of Sybil attack to minimize the impact and manage operations. It includes elements such as attack on bitcoin network, tor network, peer-to-peer model, etc. Introducing Key Scenarios Of Sybil Attack On Blockchain Network Guide For Blockchain BCT SS V to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Attack On Bitcoin Network, Attack On Tor Network using this template. Grab it now to reap its full benefits.
-
 Overview And Categories Of Sybil Attack On Blockchain Network Guide For Blockchain BCT SS V
Overview And Categories Of Sybil Attack On Blockchain Network Guide For Blockchain BCT SS VThe following slide illustrates brief introduction of Sybil attack to reduce security violations. It includes elements such as fake identities, illegal activities, categories, fake account interacting with real nodes, malicious accounts, etc. Increase audience engagement and knowledge by dispensing information using Overview And Categories Of Sybil Attack On Blockchain Network Guide For Blockchain BCT SS V This template helps you present information on two stages. You can also present information on Direct Sybil Attack, Categories Of Sybil Attack using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
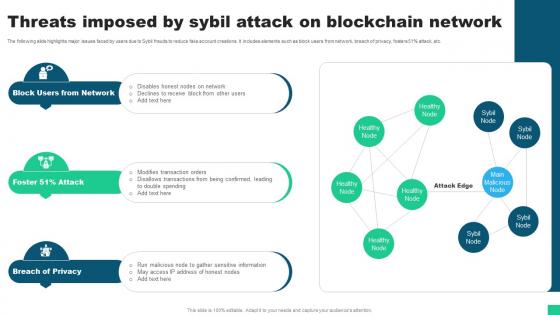 Threats Imposed By Sybil Attack On Blockchain Network Guide For Blockchain BCT SS V
Threats Imposed By Sybil Attack On Blockchain Network Guide For Blockchain BCT SS VThe following slide highlights major issues faced by users due to Sybil frauds to reduce fake account creations. It includes elements such as block users from network, breach of privacy, fosters 51 percent attack, etc. Increase audience engagement and knowledge by dispensing information using Threats Imposed By Sybil Attack On Blockchain Network Guide For Blockchain BCT SS V This template helps you present information on three stages. You can also present information on Block Users From Network, Breach Of Privacy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
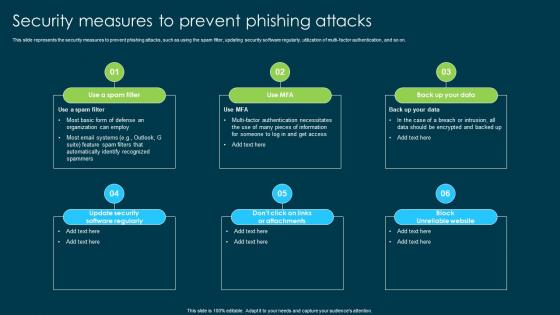 Ethical Hacking And Network Security Security Measures To Prevent Phishing Attacks
Ethical Hacking And Network Security Security Measures To Prevent Phishing AttacksThis slide represents the security measures to prevent phishing attacks, such as using the spam filter, updating security software regularly, utilization of multi-factor authentication, and so on. Introducing Ethical Hacking And Network Security Security Measures To Prevent Phishing Attacks to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Prevent Phishing Attacks, Spam Filter, Updating Security Software Regularly, Utilization Of Multi Factor Authentication, using this template. Grab it now to reap its full benefits.
-
 Ethical Hacking And Network Security Types Of Phishing Attack
Ethical Hacking And Network Security Types Of Phishing AttackThis slide represents the types of phishing attacks such a spear-phishing, clone phishing, whaling, BEC, vishing, and snowshoeing phishing. Increase audience engagement and knowledge by dispensing information using Ethical Hacking And Network Security Types Of Phishing Attack. This template helps you present information on three stages. You can also present information on Business Email Compromise, Clone Phishing, Snowshoeing, Phishing Attack using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
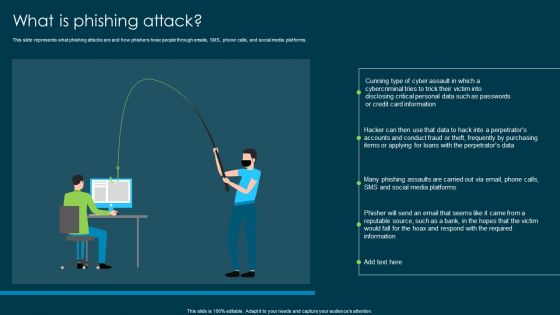 Ethical Hacking And Network Security What Is Phishing Attack
Ethical Hacking And Network Security What Is Phishing AttackThis slide represents what phishing attacks are and how phishers hoax people through emails, SMS, phone calls, and social media platforms. Introducing Ethical Hacking And Network Security What Is Phishing Attack to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Phishing Attacks, Phishers Hoax, Social Media Platforms, System Hacking, Corporate Or Personal Data, using this template. Grab it now to reap its full benefits.
-
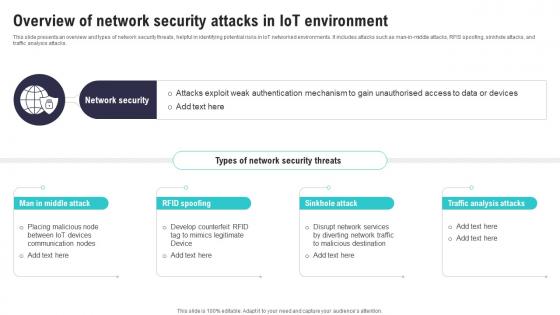 Overview Of Network Security Attacks In IoT Environment IoT Security And Privacy Safeguarding IoT SS
Overview Of Network Security Attacks In IoT Environment IoT Security And Privacy Safeguarding IoT SSThis slide presents an overview and types of network security threats, helpful in identifying potential risks in IoT networked environments. It includes attacks such as man in middle attacks, RFIS spoofing, sinkhole attacks, and traffic analysis attacks. Introducing Overview Of Network Security Attacks In IoT Environment IoT Security And Privacy Safeguarding IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Communication Nodes, Mimics Legitimate, Malicious Destination, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Attacks Prevention Social Engineering Prevention Strategies For Safe Network Use
Social Engineering Attacks Prevention Social Engineering Prevention Strategies For Safe Network UseThis slide represents the protective measures for users to practice safe networking. The best practices mentioned in this slide are restrict others from connecting to primary wi-fi network, use a VPN, security of network-connected devices, etc. Introducing Social Engineering Attacks Prevention Social Engineering Prevention Strategies For Safe Network Use to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Practice Safe Networking, Primary Wifi Network, Security Of Network Connected Devices, Social Engineering Prevention Strategies, using this template. Grab it now to reap its full benefits.
-
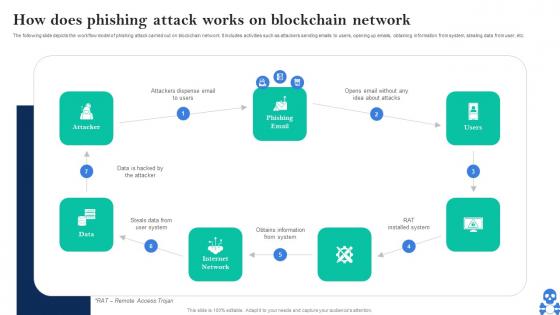 Cyber Threats In Blockchain How Does Phishing Attack Works On Blockchain Network BCT SS V
Cyber Threats In Blockchain How Does Phishing Attack Works On Blockchain Network BCT SS VThe following slide depicts the workflow model of phishing attack carried out on blockchain network. It includes activities such as attackers sending emails to users, opening up emails, obtaining information from system, stealing data from user, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain How Does Phishing Attack Works On Blockchain Network BCT SS V This template helps you present information on Seven stages. You can also present information on Steals Data From User System, Obtains Information From System using this PPT design. This layout is completely editable so personaize it now
-
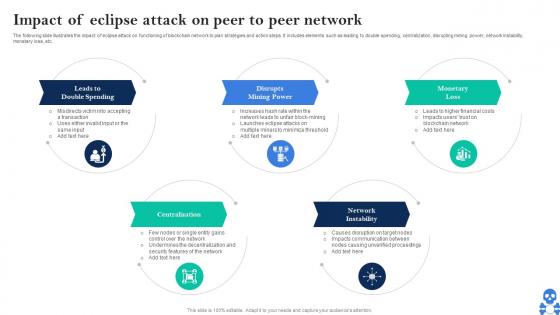 Cyber Threats In Blockchain Impact Of Eclipse Attack On Peer To Peer Network BCT SS V
Cyber Threats In Blockchain Impact Of Eclipse Attack On Peer To Peer Network BCT SS VThe following slide illustrates the impact of eclipse attack on functioning of blockchain network to plan strategies and action steps. It includes elements such as leading to double spending, centralization, disrupting mining power, network instability, monetary loss, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Impact Of Eclipse Attack On Peer To Peer Network BCT SS V This template helps you present information on Five stages. You can also present information on Leads To Double Spending, Disrupts, Mining Power using this PPT design. This layout is completely editable so personaize it now
-
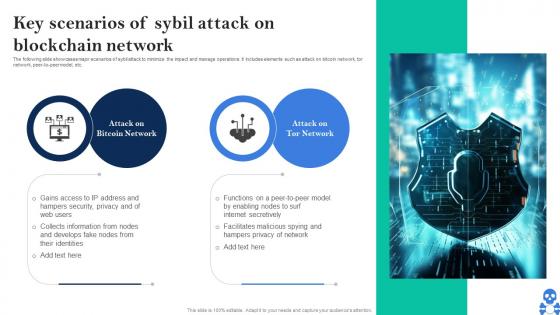 Cyber Threats In Blockchain Key Scenarios Of Sybil Attack On Blockchain Network BCT SS V
Cyber Threats In Blockchain Key Scenarios Of Sybil Attack On Blockchain Network BCT SS VThe following slide showcases major scenarios of sybil attack to minimize the impact and manage operations. It includes elements such as attack on bitcoin network, tor network, peer-to-peer model, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Key Scenarios Of Sybil Attack On Blockchain Network BCT SS V Dispense information and present a thorough explanation of Bitcoin Network, Attack On Tor Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
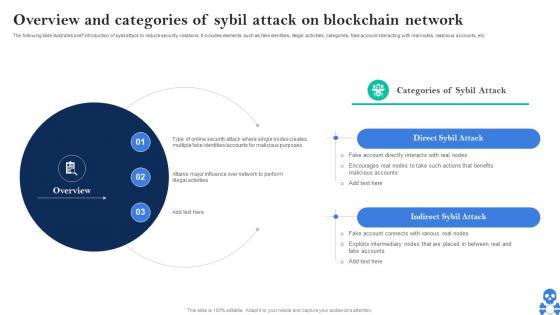 Cyber Threats In Blockchain Overview And Categories Of Sybil Attack On Blockchain Network BCT SS V
Cyber Threats In Blockchain Overview And Categories Of Sybil Attack On Blockchain Network BCT SS VThe following slide illustrates brief introduction of sybil attack to reduce security violations. It includes elements such as fake identities, illegal activities, categories, fake account interacting with real nodes, malicious accounts, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Overview And Categories Of Sybil Attack On Blockchain Network BCT SS V This template helps you present information on Two stages. You can also present information on Direct Sybil Attack, Indirect Sybil Attack using this PPT design. This layout is completely editable so personaize it now
-
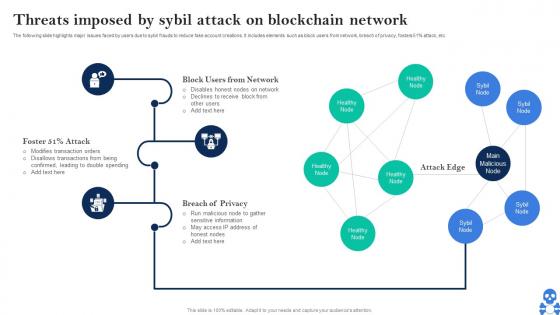 Cyber Threats In Blockchain Threats Imposed By Sybil Attack On Blockchain Network BCT SS V
Cyber Threats In Blockchain Threats Imposed By Sybil Attack On Blockchain Network BCT SS VThe following slide highlights major issues faced by users due to sybil frauds to reduce fake account creations. It includes elements such as block users from network, breach of privacy, fosters 51percent attack, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Threats Imposed By Sybil Attack On Blockchain Network BCT SS V Dispense information and present a thorough explanation of Block Users From Network, Breach Of Privacy, Attack Edge using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
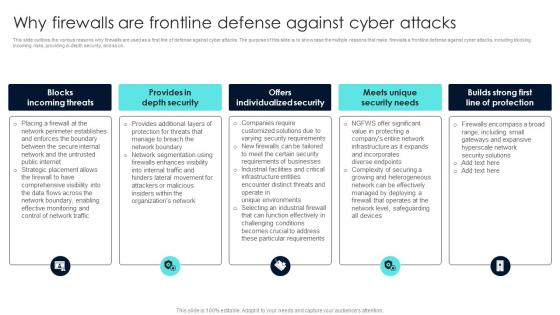 Firewall Network Security Why Firewalls Are Frontline Defense Against Cyber Attacks
Firewall Network Security Why Firewalls Are Frontline Defense Against Cyber AttacksThis slide outlines the various reasons why firewalls are used as a first line of defense against cyber attacks. The purpose of this slide is to showcase the multiple reasons that make firewalls a frontline defense against cyber attacks, including blocking incoming risks, providing in-depth security, and so on. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Why Firewalls Are Frontline Defense Against Cyber Attacks This template helps you present information on Five stages. You can also present information on Blocks Incoming Threats, Provides In Depth Security, Offers Individualized Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
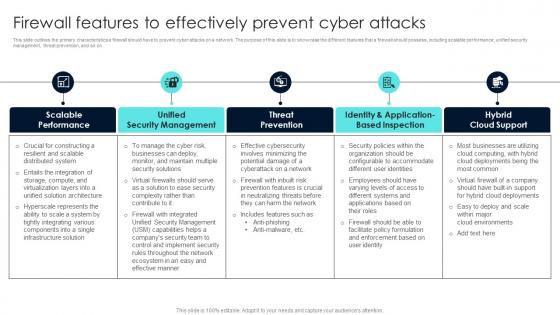 Firewall Network Security Firewall Features To Effectively Prevent Cyber Attacks
Firewall Network Security Firewall Features To Effectively Prevent Cyber AttacksThis slide outlines the primary characteristics a firewall should have to prevent cyber attacks on a network. The purpose of this slide is to showcase the different features that a firewall should possess, including scalable performance, unified security management, threat prevention, and so on. Introducing Firewall Network Security Firewall Features To Effectively Prevent Cyber Attacks to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on URL Categories By Traffic, Traffic Source IP, Traffic Desintation IP using this template. Grab it now to reap its full benefits.
-
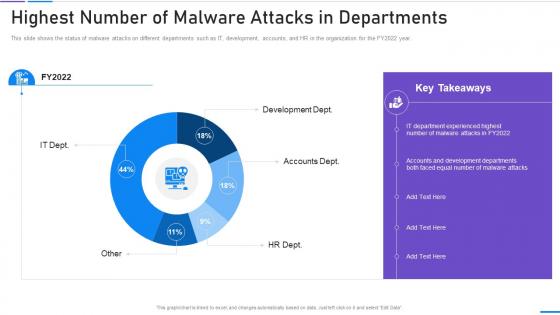 Network Security Highest Number Of Malware Attacks In Departments
Network Security Highest Number Of Malware Attacks In DepartmentsThis slide shows the status of malware attacks on different departments such as IT, development, accounts, and HR in the organization for the FY2022 year. Present the topic in a bit more detail with this Network Security Highest Number Of Malware Attacks In Departments. Use it as a tool for discussion and navigation on Highest Number Of Malware Attacks In Departments. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
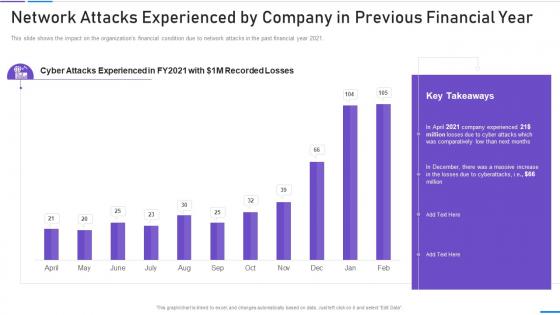 Network Security Network Attacks Experienced By Company
Network Security Network Attacks Experienced By CompanyThis slide shows the impact on the organizations financial condition due to network attacks in the past financial year 2021. Deliver an outstanding presentation on the topic using this Network Security Network Attacks Experienced By Company. Dispense information and present a thorough explanation of Network Attacks Experienced By Company In Previous Financial Year using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Routing Network Attacks Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Routing Network Attacks Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Routing network attacks colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Routing Network Attacks Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Routing Network Attacks Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Routing network attacks monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Sybil Attack Network Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Sybil Attack Network Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Sybil attack network colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Sybil Attack Network Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Sybil Attack Network Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Sybil attack network monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Types network security attack ppt powerpoint presentation pictures examples cpb
Types network security attack ppt powerpoint presentation pictures examples cpbPresenting Types Network Security Attack Ppt Powerpoint Presentation Pictures Examples Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Types Network Security Attack. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Drag network attack techniques ppt powerpoint presentation summary gallery cpb
Drag network attack techniques ppt powerpoint presentation summary gallery cpbPresenting our Drag Network Attack Techniques Ppt Powerpoint Presentation Summary Gallery Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Drag Network Attack Techniques. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Botnet Hacking Network Attack Icon
Botnet Hacking Network Attack IconPresenting our set of slides with Botnet Hacking Network Attack Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Botnet Hacking Network, Attack Icon.
-
 Network Security Practices To Prevent Cyber Attacks
Network Security Practices To Prevent Cyber AttacksThe given slide highlights some of the best practices to mitigate cyber attacks. Some of them are as backing up the data, training employees, preparing cyber incident response plan, securing sites and updating systems and software. Presenting our set of slides with Network Security Practices To Prevent Cyber Attacks. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Train Employees, Secure Sites.
-
 Concerned Sniffing Attacks Wireless Network In Powerpoint And Google Slides Cpb
Concerned Sniffing Attacks Wireless Network In Powerpoint And Google Slides CpbPresenting Concerned Sniffing Attacks Wireless Network In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Concerned Sniffing Attacks Wireless Network. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Virtual Terrorism Threat Attacking Network Icon
Virtual Terrorism Threat Attacking Network IconIntroducing our premium set of slides with Virtual Terrorism Threat Attacking Network Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Virtual Terrorism, Threat Attacking Network. So download instantly and tailor it with your information.
-
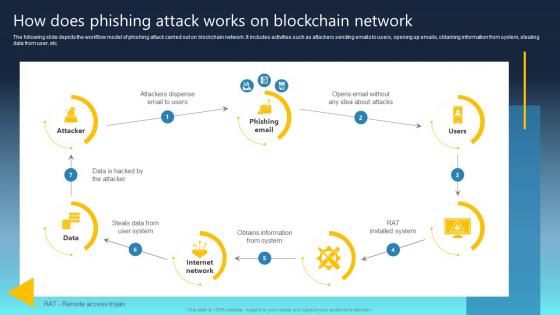 Ultimate Guide For Blockchain How Does Phishing Attack Works On Blockchain Network BCT SS
Ultimate Guide For Blockchain How Does Phishing Attack Works On Blockchain Network BCT SSThe following slide depicts the workflow model of phishing attack carried out on blockchain network. It includes activities such as attackers sending emails to users, opening up emails, obtaining information from system, stealing data from user, etc. Increase audience engagement and knowledge by dispensing information using Ultimate Guide For Blockchain How Does Phishing Attack Works On Blockchain Network BCT SS This template helps you present information on Seven stages. You can also present information on Phishing Email, Attacker, Internet Network using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ultimate Guide For Blockchain Impact Of Eclipse Attack On Peer To Peer Network BCT SS
Ultimate Guide For Blockchain Impact Of Eclipse Attack On Peer To Peer Network BCT SSIntroducing Ultimate Guide For Blockchain Impact Of Eclipse Attack On Peer To Peer Network BCT SS to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Double Spending, Centralization, Disrupts Mining Power using this template. Grab it now to reap its full benefits.
-
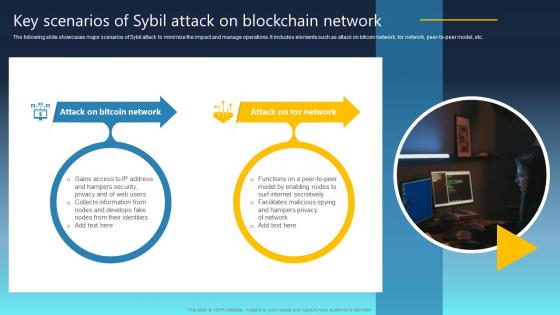 Ultimate Guide For Blockchain Key Scenarios Of Sybil Attack On Blockchain Network BCT SS
Ultimate Guide For Blockchain Key Scenarios Of Sybil Attack On Blockchain Network BCT SSThe following slide showcases major scenarios of Sybil attack to minimize the impact and manage operations. It includes elements such as attack on bitcoin network, tor network, peer-to-peer model, etc. Increase audience engagement and knowledge by dispensing information using Ultimate Guide For Blockchain Key Scenarios Of Sybil Attack On Blockchain Network BCT SS This template helps you present information on Two stages. You can also present information on Attack On Bitcoin Network, Attack On Tor Network using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Network Security Internet Attacks Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Network Security Internet Attacks Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis colourful PowerPoint icon is the perfect visual representation of reducing internet attacks. It features a shield with a green checkmark, showing that security is in place and that the user is protected. It is a great way to show the importance of online security in a visually appealing way.
-
 Network Security Internet Attacks Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Network Security Internet Attacks Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint icon is the perfect visual aid to help reduce Internet attacks. It features a shield with a check mark, representing the protection of data and networks from malicious cyber threats. It is a simple yet powerful way to communicate the importance of cybersecurity.
-
 Types attacks network security ppt powerpoint presentation diagram templates cpb
Types attacks network security ppt powerpoint presentation diagram templates cpbPresenting this set of slides with name Types Attacks Network Security Ppt Powerpoint Presentation Diagram Templates Cpb. This is an editable Powerpoint four stages graphic that deals with topics like Types Attacks Network Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Classification attacks network security ppt powerpoint presentation pictures demonstration cpb
Classification attacks network security ppt powerpoint presentation pictures demonstration cpbPresenting this set of slides with name Classification Attacks Network Security Ppt Powerpoint Presentation Pictures Demonstration Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Classification Attacks Network Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Computer network security against hackers and cyber attacks
Computer network security against hackers and cyber attacksPresenting our well-structured Government Web Portal For Citizens Services. The topics discussed in this slide are Government Web Portal For Citizens Services. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Hackers breaching network security through cyber attack
Hackers breaching network security through cyber attackPresenting our set of slides with Web Portal For Providing Job Vacancies Alerts. This exhibits information on two stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Web Portal For Providing Job Vacancies Alerts.
-
 Inter connected network bomb depicting cyber attack
Inter connected network bomb depicting cyber attackIntroducing our Web Portal For Supporting Customer Experience Initiatives set of slides. The topics discussed in these slides are Web Portal For Supporting Customer Experience Initiatives. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.

