Powerpoint Templates and Google slides for Network Process Redesign
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
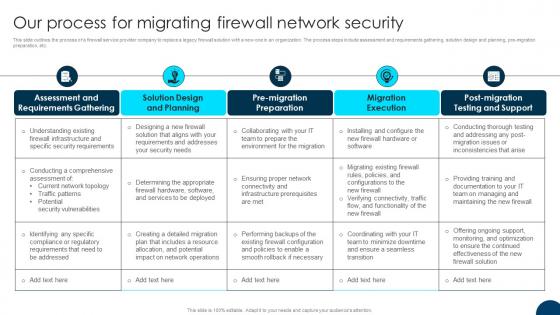 Firewall Migration Proposal Our Process For Migrating Firewall Network Security
Firewall Migration Proposal Our Process For Migrating Firewall Network SecurityThis slide outlines the process of a firewall service provider company to replace a legacy firewall solution with a new one in an organization. The process steps include assessment and requirements gathering, solution design and planning, pre-migration preparation, etc. Present the topic in a bit more detail with this Firewall Migration Proposal Our Process For Migrating Firewall Network Security. Use it as a tool for discussion and navigation on Assessment And Requirements Gathering, Solution Design And Planning, Migration Execution. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
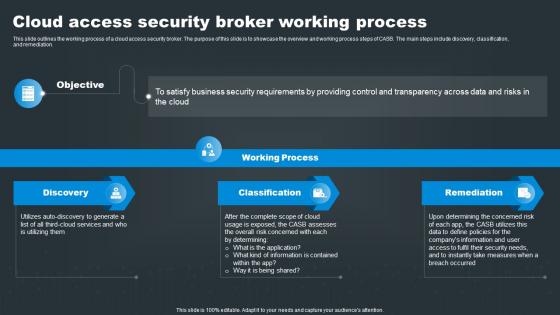 SASE Network Security Cloud Access Security Broker Working Process
SASE Network Security Cloud Access Security Broker Working ProcessThis slide outlines the working process of a cloud access security broker. The purpose of this slide is to showcase the overview and working process steps of CASB. The main steps include discovery, classification, and remediation. Increase audience engagement and knowledge by dispensing information using SASE Network Security Cloud Access Security Broker Working Process. This template helps you present information on three stages. You can also present information on Discovery, Classification, Remediation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
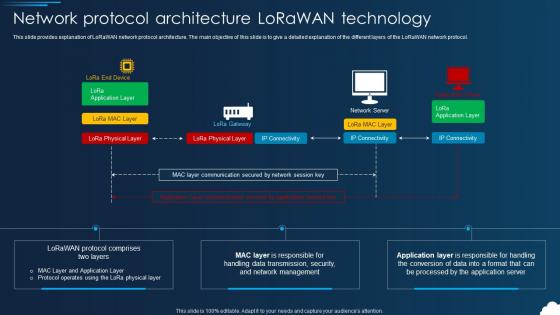 Lorawan Network Protocol Architecture Lorawan Technology
Lorawan Network Protocol Architecture Lorawan TechnologyThis slide provides explanation of LoRaWAN network protocol architecture. The main objective of this slide is to give a detailed explanation of the different layers of the LoRaWAN network protocol. Deliver an outstanding presentation on the topic using this Lorawan Network Protocol Architecture Lorawan Technology. Dispense information and present a thorough explanation of Technology, Protocol, Architecture using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
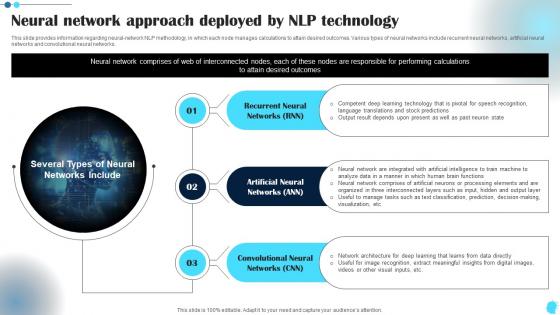 Neural Network Approach Deployed Power Of Natural Language Processing AI SS V
Neural Network Approach Deployed Power Of Natural Language Processing AI SS VThis slide provides information regarding neural network NLP methodology, in which each node manages calculations to attain desired outcomes. Various types of neural networks include recurrent neural networks, artificial neural networks convolutional neural networks. Introducing Neural Network Approach Deployed Power Of Natural Language Processing AI SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate entice your audience. Dispence information on Data Manner, Network Comprises, Organized Interconnected, using this template. Grab it now to reap its full benefits.
-
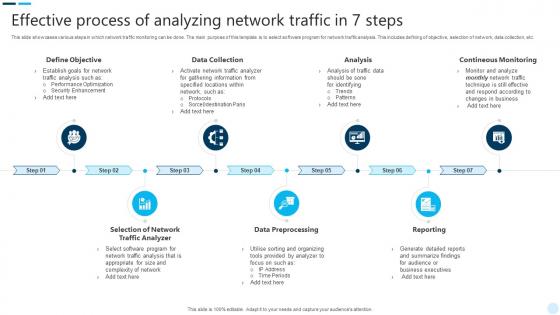 Effective Process Of Analyzing Network Traffic In 7 Steps
Effective Process Of Analyzing Network Traffic In 7 StepsThis slide showcases various steps in which network traffic monitoring can be done. The main purpose of this template is to select software program for network traffic analysis. This includes defining of objective, selection of network, data collection, etc. Introducing our premium set of slides with Effective Process Of Analyzing Network Traffic In 7 Steps. Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Define Objective, Data Collection. So download instantly and tailor it with your information.
-
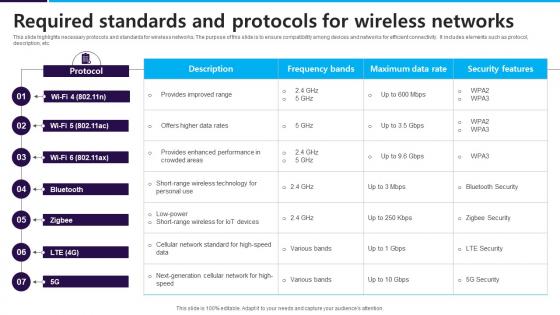 Required Standards And Protocols For Wireless Networks
Required Standards And Protocols For Wireless NetworksThis slide highlights necessary protocols and standards for wireless networks. The purpose of this slide is to ensure compatibility among devices and networks for efficient connectivity. It includes elements such as protocol, description, etc. Introducing our Required Standards And Protocols For Wireless Networks set of slides. The topics discussed in these slides are Description, Frequency Bands. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Network Protocols Router Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Network Protocols Router Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured PowerPoint icon depicts a router, the essential device for connecting to the internet. It is a vibrant blue and green, giving it a modern and professional look. Perfect for presentations on technology and networking.
-
 Network Protocols Router Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Network Protocols Router Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon of a Router is perfect for any presentation. It is a simple, black and white image that is sure to make an impact. It is easy to customize and can be used to illustrate a variety of topics. Use it to represent the internet, networking, or any other related topics.
-
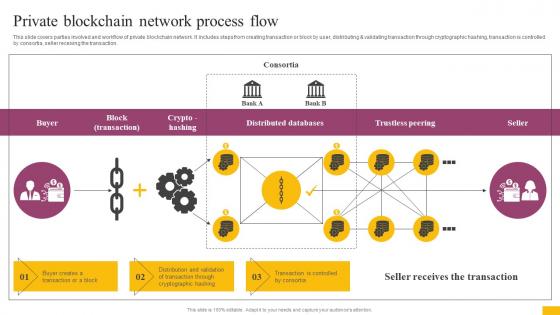 Private Blockchain Network Process Flow Complete Guide To Understand BCT SS
Private Blockchain Network Process Flow Complete Guide To Understand BCT SSThis slide covers parties involved and workflow of private blockchain network. It includes steps from creating transaction or block by user, distributing and validating transaction through cryptographic hashing, transaction is controlled by consortia, seller receiving the transaction. Deliver an outstanding presentation on the topic using this Private Blockchain Network Process Flow Complete Guide To Understand BCT SS Dispense information and present a thorough explanation of Distributed Databases, Trustless Peering, Crypto Hashing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
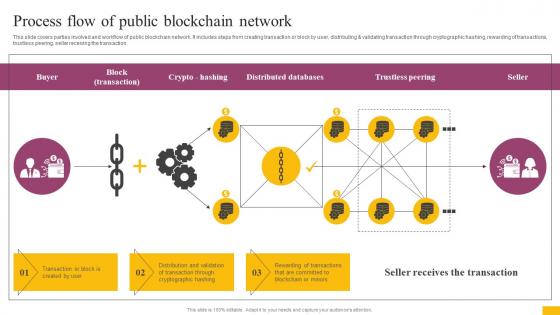 Process Flow Of Public Blockchain Network Complete Guide To Understand BCT SS
Process Flow Of Public Blockchain Network Complete Guide To Understand BCT SSThis slide covers parties involved and workflow of public blockchain network. It includes steps from creating transaction or block by user, distributing and validating transaction through cryptographic hashing, rewarding of transactions, trustless peering, seller receiving the transaction. Deliver an outstanding presentation on the topic using this Process Flow Of Public Blockchain Network Complete Guide To Understand BCT SS Dispense information and present a thorough explanation of Crypto Hashing, Distributed Databases, Trustless Peering using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
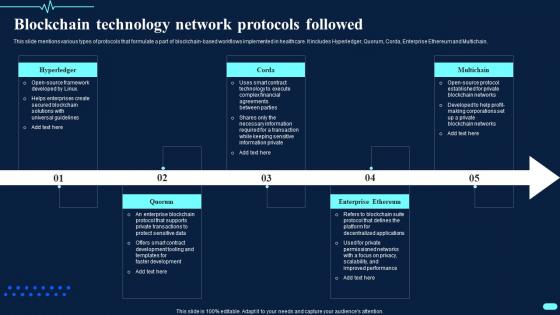 Blockchain Technology Network Protocols Followed Transforming Healthcare BCT SS
Blockchain Technology Network Protocols Followed Transforming Healthcare BCT SSThis slide mentions various types of protocols that formulate a part of blockchain based workflows implemented in healthcare. It includes Hyperledger, Quorum, Corda, Enterprise Ethereum and Multichain.a Introducing Blockchain Technology Network Protocols Followed Transforming Healthcare BCT SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Hyperledger, Quorum, using this template. Grab it now to reap its full benefits.
-
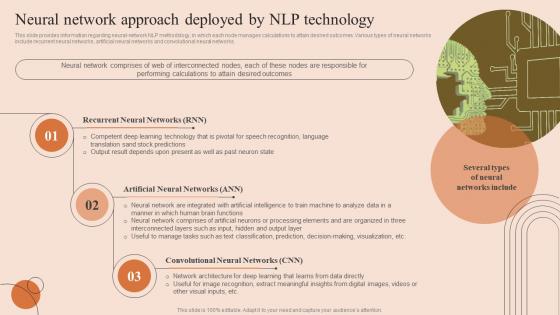 Natural Language Processing Neural Network Approach Deployed By NLP Technology AI SS V
Natural Language Processing Neural Network Approach Deployed By NLP Technology AI SS VThis slide provides information regarding neural-network NLP methodology, in which each node manages calculations to attain desired outcomes. Various types of neural networks include recurrent neural networks, artificial neural networks and convolutional neural networks. Introducing Natural Language Processing Neural Network Approach Deployed By NLP Technology AI SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Recurrent Neural Networks, Artificial Neural Networks, Convolutional Neural Networks, using this template. Grab it now to reap its full benefits.
-
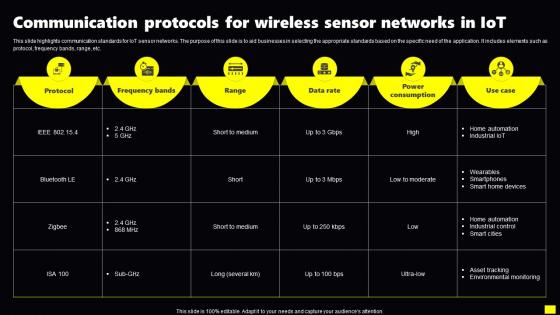 Communication Protocols For Wireless Sensor Networks In IoT
Communication Protocols For Wireless Sensor Networks In IoTThis slide highlights communication standards for IoT sensor networks. The purpose of this slide is to aid businesses in selecting the appropriate standards based on the specific need of the application. It includes elements such as protocol, frequency bands, range, etc.Introducing our Communication Protocols For Wireless Sensor Networks In IoT set of slides. The topics discussed in these slides are Power Consumption, Wearables Smartphones, Home Automation. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Icon For Real Time Data Processing For Sensor Networks In IoT
Icon For Real Time Data Processing For Sensor Networks In IoTPresenting our well structured Icon For Real Time Data Processing For Sensor Networks In IoT. The topics discussed in this slide are Icon Real Time, Data Processing, Sensor Networks In Iot. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
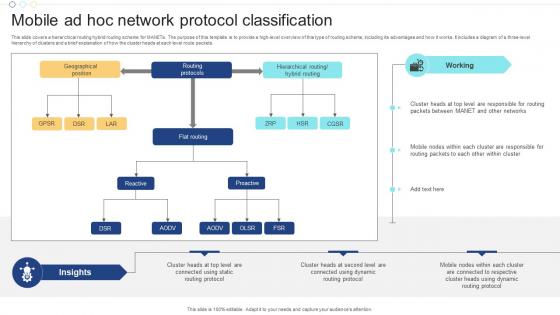 Mobile Ad Hoc Network Protocol Classification
Mobile Ad Hoc Network Protocol ClassificationThis slide covers a hierarchical routing hybrid routing scheme for MANETs. The purpose of this template is to provide a high level overview of this type of routing scheme, including its advantages and how it works. It includes a diagram of a three level hierarchy of clusters and a brief explanation of how the cluster heads at each level route packets. Introducing our Mobile Ad Hoc Network Protocol Classification set of slides. The topics discussed in these slides are Geographical, Position, Routing Protocols, Hierarchical Routing. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
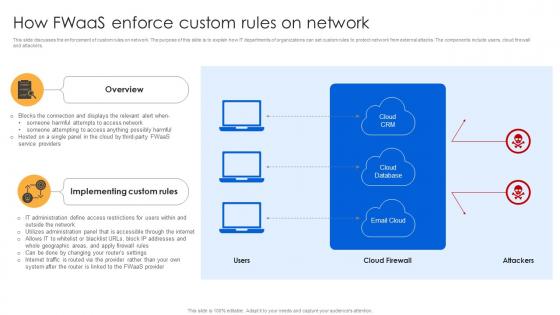 How Fwaas Enforce Custom Rules On Network Firewall Virtualization
How Fwaas Enforce Custom Rules On Network Firewall VirtualizationThis slide discusses the enforcement of custom rules on network. The purpose of this slide is to explain how IT departments of organizations can set custom rules to protect network from external attacks. The components include users, cloud firewall and attackers. Introducing How Fwaas Enforce Custom Rules On Network Firewall Virtualization to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Overview, Implementing Custom Rules, Service Providers, using this template. Grab it now to reap its full benefits.
-
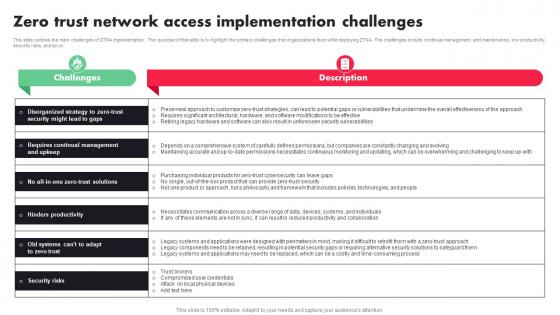 Zero Trust Network Access Implementation Challenges Ppt File Rules
Zero Trust Network Access Implementation Challenges Ppt File RulesThis slide outlines the main challenges of ZTNA implementation. The purpose of this slide is to highlight the primary challenges that organizations face while deploying ZTNA. The challenges include continual management and maintenance, low productivity, security risks, and so on. Present the topic in a bit more detail with this Zero Trust Network Access Implementation Challenges Ppt File Rules. Use it as a tool for discussion and navigation on Hardware, Security Vulnerabilities, Software Modifications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
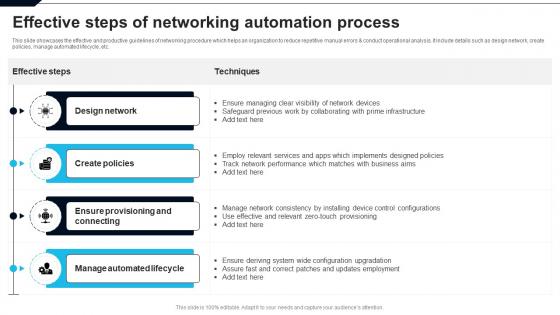 Effective Steps Of Networking Automation Process
Effective Steps Of Networking Automation ProcessThis slide showcases the effective and productive guidelines of networking procedure which helps an organization to reduce repetitive manual errors and conduct operational analysis. It include details such as design network, create policies, manage automated lifecycle, etc. Introducing our Effective Steps Of Networking Automation Process set of slides. The topics discussed in these slides are Design Network, Manage Automated Lifecycle, Create Policies. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
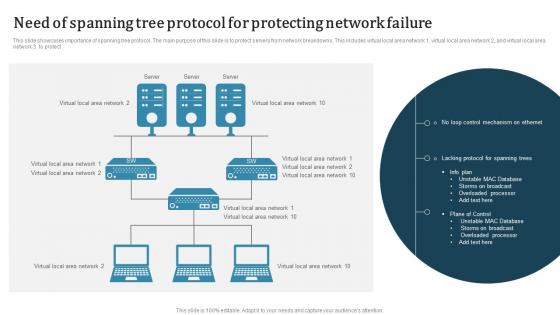 Need Of Spanning Tree Protocol For Protecting Network Failure
Need Of Spanning Tree Protocol For Protecting Network FailureThis slide showcases importance of spanning tree protocol. The main purpose of this slide is to protect servers from network breakdowns. This includes virtual local area network 1, virtual local area network 2 and virtual local area network 3 to protect. Introducing our Need Of Spanning Tree Protocol For Protecting Network Failure set of slides. The topics discussed in these slides are Need Of Spanning, Tree Protocol, Protecting Network Failure. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
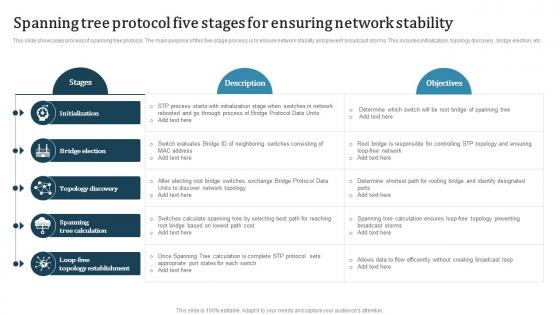 Spanning Tree Protocol Five Stages For Ensuring Network Stability
Spanning Tree Protocol Five Stages For Ensuring Network StabilityThis slide showcases process of spanning tree protocol. The main purpose of this five-stage process is to ensure network stability and prevent broadcast storms. This includes initialization, topology discovery, bridge election, etc. Presenting our well structured Spanning Tree Protocol Five Stages For Ensuring Network Stability. The topics discussed in this slide are Bridge Election, Topology Discovery, Topology Establishment. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Spanning Tree Protocol Icon For Increasing Efficiency Of Network
Spanning Tree Protocol Icon For Increasing Efficiency Of NetworkIntroducing our Spanning Tree Protocol Icon For Increasing Efficiency Of Network set of slides. The topics discussed in these slides are Spanning Tree, Protocol Icon, Increasing Efficiency Of Network. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Spanning Tree Protocol Icon For Monitoring Network
Spanning Tree Protocol Icon For Monitoring NetworkPresenting our well structured Spanning Tree Protocol Icon For Monitoring Network. The topics discussed in this slide are Spanning Tree, Protocol Icon, Monitoring Network. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
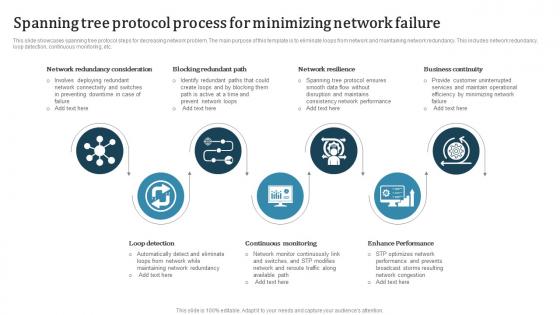 Spanning Tree Protocol Process For Minimizing Network Failure
Spanning Tree Protocol Process For Minimizing Network FailureThis slide showcases spanning tree protocol steps for decreasing network problem. The main purpose of this template is to eliminate loops from network and maintaining network redundancy. This includes network redundancy, loop detection, continuous monitoring, etc. Presenting our set of slides with name Spanning Tree Protocol Process For Minimizing Network Failure. This exhibits information on seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Network Resilience, Business Continuity, Continuous Monitoring.
-
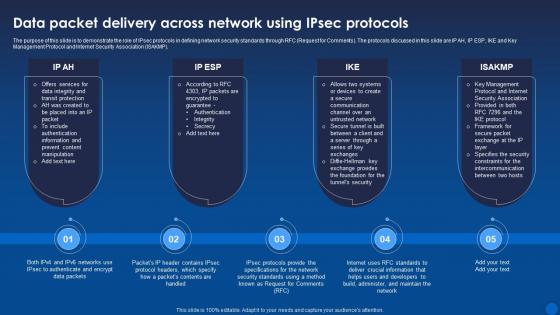 Data Packet Delivery Across Network Using Ipsec Protocols Encryption For Data Privacy In Digital Age It
Data Packet Delivery Across Network Using Ipsec Protocols Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to demonstrate the role of IPsec protocols in defining network security standards through RFC Request for Comments. The protocols discussed in this slide are IP AH, IP ESP, IKE and Key Management Protocol and Internet Security Association ISAKMP. Increase audience engagement and knowledge by dispensing information using Data Packet Delivery Across Network Using Ipsec Protocols Encryption For Data Privacy In Digital Age It. This template helps you present information on four stages. You can also present information on Communication, Information, Authentication using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
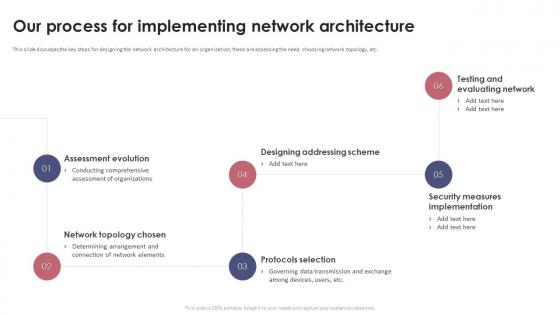 Our Process For Implementing Network Architecture Proposal
Our Process For Implementing Network Architecture ProposalThis slide discusses the key steps for designing the network architecture for an organization, these are assessing the need, choosing network topology, etc. Increase audience engagement and knowledge by dispensing information using Our Process For Implementing Network Architecture Proposal. This template helps you present information on six stages. You can also present information on Testing And Evaluating Network, Security Measures Implementation, Protocols Selection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
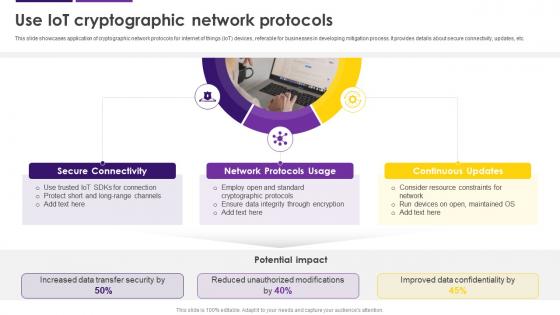 Use IoT Cryptographic Network Protocols Internet Of Things IoT Security Cybersecurity SS
Use IoT Cryptographic Network Protocols Internet Of Things IoT Security Cybersecurity SSThis slide showcases application of cryptographic network protocols for internet of things IoT devices, referable for businesses in developing mitigation process. It provides details about secure connectivity, updates, etc. Increase audience engagement and knowledge by dispensing information using Use IoT Cryptographic Network Protocols Internet Of Things IoT Security Cybersecurity SS. This template helps you present information on three stages. You can also present information on Secure Connectivity, Network Protocols Usage, Continuous Updates, Cryptographic Network Protocols using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
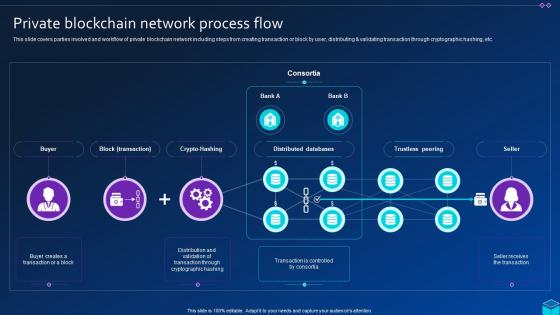 Private Blockchain Network Process Flow Comprehensive Approach To Privacy BCT SS
Private Blockchain Network Process Flow Comprehensive Approach To Privacy BCT SSThis slide covers parties involved and workflow of private blockchain network including steps from creating transaction or block by user, distributing and validating transaction through cryptographic hashing, etc. Deliver an outstanding presentation on the topic using this Private Blockchain Network Process Flow Comprehensive Approach To Privacy BCT SS. Dispense information and present a thorough explanation of Crypto Hashing, Distributed Databases, Trustless Peering using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
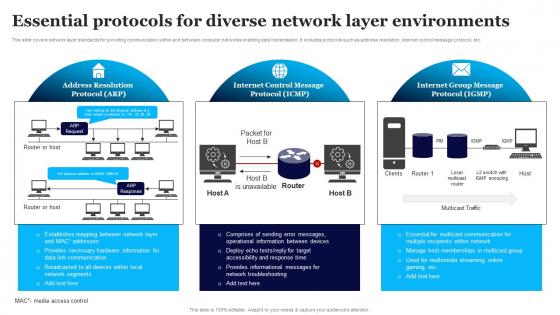 Essential Protocols For Diverse Network Layer Environments
Essential Protocols For Diverse Network Layer EnvironmentsThis slide covers network layer standards for providing communication within and between computer networks enabling data transmission. It includes protocols such as address resolution, internet control message protocol, etc. Presenting our well structured Essential Protocols For Diverse Network Layer Environments. The topics discussed in this slide are Address Resolution Protocol, Internet Control Message Protocol, Internet Group Message Protocol. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
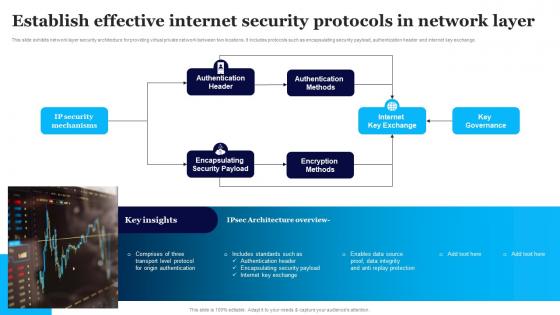 Establish Effective Internet Security Protocols In Network Layer
Establish Effective Internet Security Protocols In Network LayerThis slide exhibits network layer security architecture for providing virtual private network between two locations. It includes protocols such as encapsulating security payload, authentication header and internet key exchange. Presenting our set of slides with Establish Effective Internet Security Protocols In Network Layer. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Authentication Header, Authentication Methods, Encapsulating Security Payload.
-
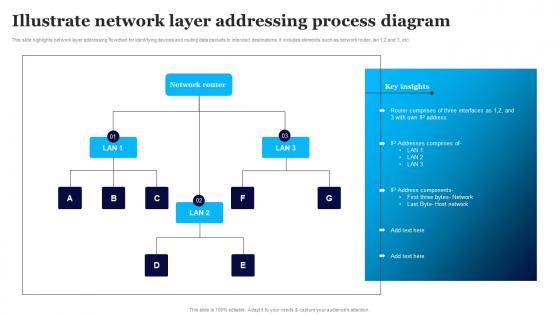 Illustrate Network Layer Addressing Process Diagram
Illustrate Network Layer Addressing Process DiagramThis slide highlights network layer addressing flowchart for identifying devices and routing data packets to intended destinations. It includes elements such as network router, lan 1,2 and 3, etc. Introducing our Illustrate Network Layer Addressing Process Diagram set of slides. The topics discussed in these slides are Network Router, Address Components, Router Comprises. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
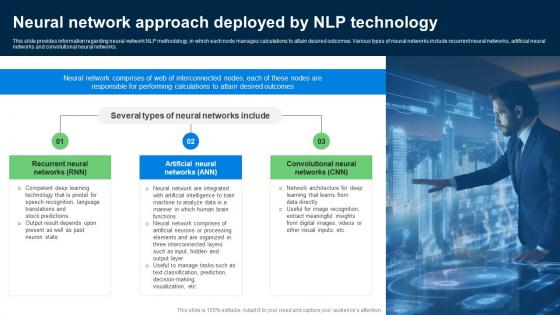 Neural Network Approach Deployed Explore Natural Language Processing NLP AI SS V
Neural Network Approach Deployed Explore Natural Language Processing NLP AI SS VThis slide provides information regarding neural network NLP methodology, in which each node manages calculations to attain desired outcomes. Various types of neural networks include recurrent neural networks, artificial neural networks and convolutional neural networks. Introducing Neural Network Approach Deployed Explore Natural Language Processing NLP AI SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Networks, Artificial, Convolutional, using this template. Grab it now to reap its full benefits.
-
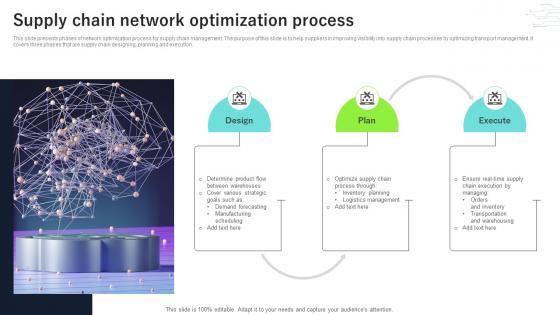 Supply Chain Network Optimization Process
Supply Chain Network Optimization ProcessThis slide presents phases of network optimization process for supply chain management. The purpose of this slide is to help suppliers in improving visibility into supply chain processes by optimizing transport management. It covers three phases that are supply chain designing, planning and execution. Introducing our premium set of slides with Supply Chain Network Optimization Process. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Design, Execute, Plan. So download instantly and tailor it with your information.
-
 Change Agent Network Process Flow
Change Agent Network Process FlowThis slide showcases the change agent network process flow which helps an organization to enhance collaboration, mitigate resistance for future business growth. It include details such as set and clear roles and responsibilities, state eligibility and selection criteria, etc. Introducing our premium set of slides with Change Agent Network Process Flow Ellicudate the Eight stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Change Agents, Their Commitment Volunteer, Candidates Agent Network So download instantly and tailor it with your information.
-
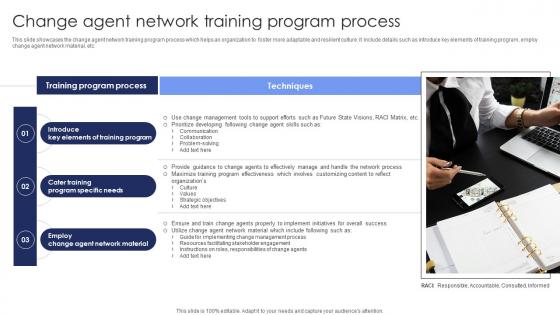 Change Agent Network Training Program Process
Change Agent Network Training Program ProcessIntroducing our premium set of slides with Change Agent Network Training Program Process Ellicudate the Three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Key Elements Of Training Program, Program Specific Needs, Change Agent Network Material So download instantly and tailor it with your information.
-
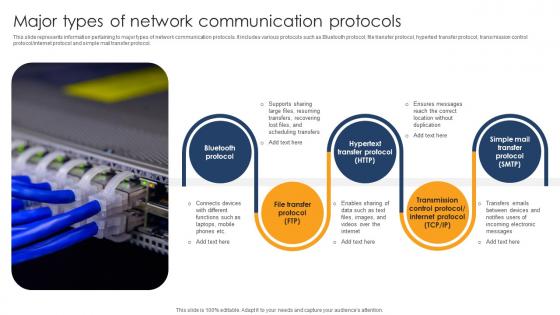 Major Types Of Network Communication Protocols
Major Types Of Network Communication ProtocolsThis slide represents information pertaining to major types of network communication protocols. It includes various protocols such as Bluetooth protocol, file transfer protocol, hypertext transfer protocol, transmission control protocolinternet protocol and simple mail transfer protocol. Presenting our set of slides with Major Types Of Network Communication Protocols. This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Bluetooth Protocol, File Transfer Protocol, Hypertext Transfer Protocol.
-
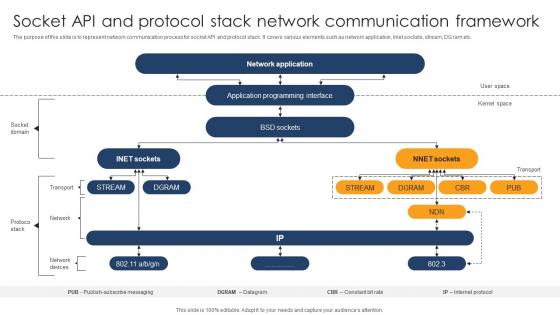 Socket API And Protocol Stack Network Communication Framework
Socket API And Protocol Stack Network Communication FrameworkThe purpose of this slide is to represent network communication process for socket API and protocol stack. It covers various elements such as network application, Inlet sockets, stream, DG ram etc. Presenting our well structured Socket API And Protocol Stack Network Communication Framework. The topics discussed in this slide are Network Application, Application Programming Interface, BSD Sockets. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
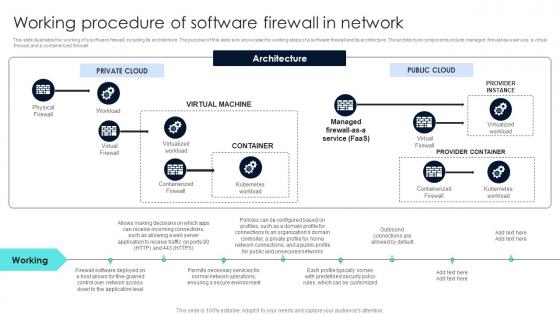 Firewall Network Security Working Procedure Of Software Firewall In Network
Firewall Network Security Working Procedure Of Software Firewall In NetworkThis slide illustrates the working of a software firewall, including its architecture. The purpose of this slide is to showcase the working steps of a software firewall and its architecture. The architecture components include managed firewall as a service, a virtual firewall, and a containerized firewall. Present the topic in a bit more detail with this Firewall Network Security Working Procedure Of Software Firewall In Network Use it as a tool for discussion and navigation on Virtual Machine, Container, Private Cloud This template is free to edit as deemed fit for your organization. Therefore download it now.
-
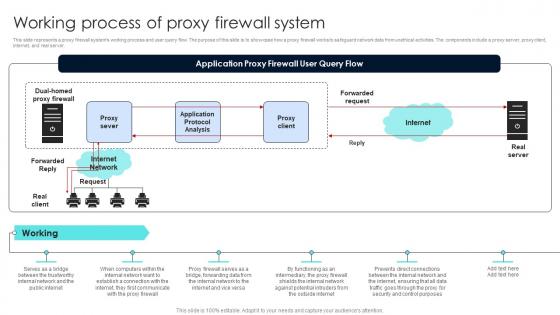 Firewall Network Security Working Process Of Proxy Firewall System
Firewall Network Security Working Process Of Proxy Firewall SystemThis slide represents a proxy firewall systems working process and user query flow. The purpose of this slide is to showcase how a proxy firewall works to safeguard network data from unethical activities. The components include a proxy server, proxy client, internet, and real server. Present the topic in a bit more detail with this Firewall Network Security Working Process Of Proxy Firewall System Use it as a tool for discussion and navigation on Working, Technologies Used, Firewall Architecture This template is free to edit as deemed fit for your organization. Therefore download it now.
-
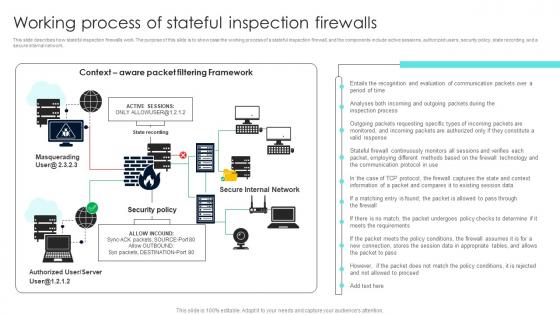 Firewall Network Security Working Process Of Stateful Inspection Firewalls
Firewall Network Security Working Process Of Stateful Inspection FirewallsThis slide describes how stateful inspection firewalls work. The purpose of this slide is to showcase the working process of a stateful inspection firewall, and the components include active sessions, authorized users, security policy, state recording, and a secure internal network. Present the topic in a bit more detail with this Firewall Network Security Working Process Of Stateful Inspection Firewalls Use it as a tool for discussion and navigation on Filtering Framework, Inspection Process, Valid Response This template is free to edit as deemed fit for your organization. Therefore download it now.
-
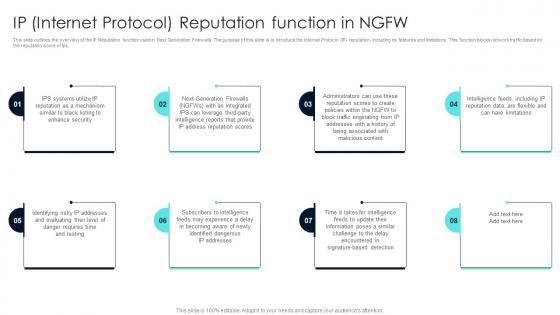 Firewall Network Security IP Internet Protocol Reputation Function In NGFW
Firewall Network Security IP Internet Protocol Reputation Function In NGFWThis slide outlines the overview of the IP Reputation function used in Next Generation Firewalls. The purpose of this slide is to introduce the Internet Protocol IP reputation, including its features and limitations. This function blocks network traffic based on the reputation score of Ips. Introducing Firewall Network Security IP Internet Protocol Reputation Function In NGFW to increase your presentation threshold. Encompassed with Eight stages, this template is a great option to educate and entice your audience. Dispence information on Policy Enforcement, Network Visibility, Streamlined Adaptability using this template. Grab it now to reap its full benefits.
-
 Workflow Process Of Health Care Asset Tracking Guide To Networks For IoT Healthcare IoT SS V
Workflow Process Of Health Care Asset Tracking Guide To Networks For IoT Healthcare IoT SS VFollowing slide exhibits architecture framework to explain working process of medical asset tracking using technology. It includes elements such as RFID tags, readers, firewall, cloud server etc. Present the topic in a bit more detail with this Workflow Process Of Health Care Asset Tracking Guide To Networks For IoT Healthcare IoT SS V. Use it as a tool for discussion and navigation on Streaming Data Processor, Data Lake, Data Warehouse. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
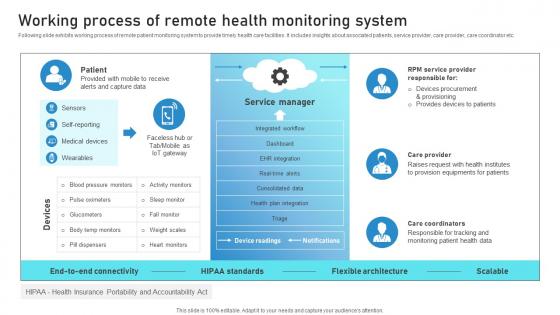 Working Process Of Remote Health Monitoring System Guide To Networks For IoT Healthcare IoT SS V
Working Process Of Remote Health Monitoring System Guide To Networks For IoT Healthcare IoT SS VFollowing slide exhibits working process of remote patient monitoring system to provide timely health care facilities. It includes insights about associated patients, service provider, care provider, care coordinator etc. Introducing Working Process Of Remote Health Monitoring System Guide To Networks For IoT Healthcare IoT SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Service Provider, Care Provider, Care Coordinators, using this template. Grab it now to reap its full benefits.
-
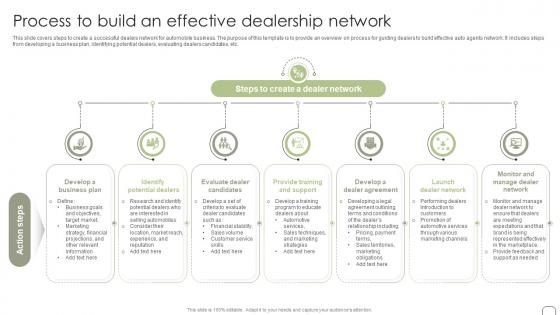 Process To Build An Effective Dealership Network Guide To Dealer Development Strategy SS
Process To Build An Effective Dealership Network Guide To Dealer Development Strategy SSThis slide covers steps to create a successful dealers network for automobile business. The purpose of this template is to provide an overview on process for guiding dealers to build effective auto agents network. It includes steps from developing a business plan, identifying potential dealers, evaluating dealers candidates, etc. Increase audience engagement and knowledge by dispensing information using Process To Build An Effective Dealership Network Guide To Dealer Development Strategy SS. This template helps you present information on seven stages. You can also present information on Identify Potential Dealers, Evaluate Dealer Candidates, Provide Training And Support using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
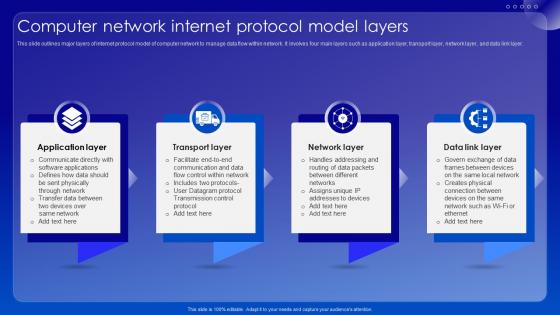 Computer Network Internet Protocol Model Layers
Computer Network Internet Protocol Model LayersThis slide outlines major layers of internet protocol model of computer network to manage data flow within network. It involves four main layers such as application layer, transport layer, network layer, and data link layer. Presenting our set of slides with Computer Network Internet Protocol Model Layers. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Application Layer, Transport Layer, Network Layer.
-
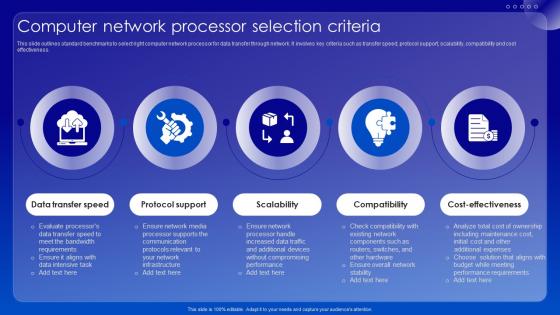 Computer Network Processor Selection Criteria
Computer Network Processor Selection CriteriaThis slide outlines standard benchmarks to select right computer network processor for data transfer through network. It involves key criteria such as transfer speed, protocol support, scalability, compatibility and cost effectiveness. Presenting our set of slides with Computer Network Processor Selection Criteria. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Protocol Support, Data Transfer Speed, Cost Effectiveness.
-
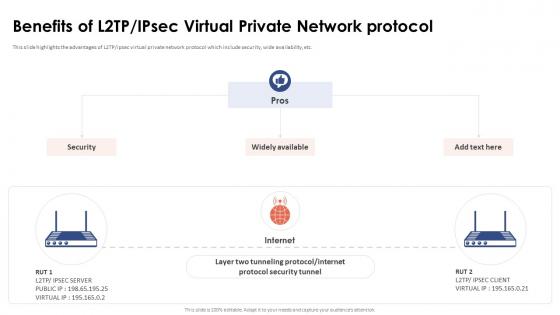 Benefits Of L2tp Ipsec Virtual Private Network Protocol
Benefits Of L2tp Ipsec Virtual Private Network ProtocolThis slide highlights the advantages of L2TP or ipsec virtual private network protocol which include security, wide availability, etc. Increase audience engagement and knowledge by dispensing information using Benefits Of L2tp Ipsec Virtual Private Network Protocol. This template helps you present information on three stages. You can also present information on Internet Protocol Security Tunnel, Widely Available, Virtual Private Network Protocol using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
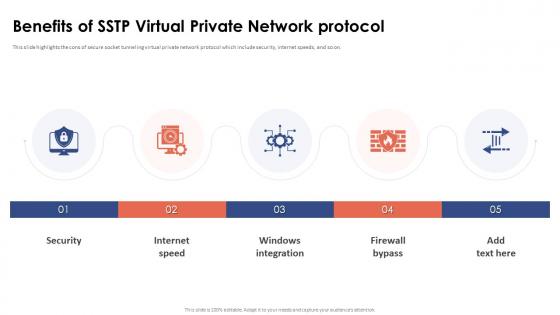 Benefits Of Sstp Virtual Private Network Protocol
Benefits Of Sstp Virtual Private Network ProtocolThis slide highlights the cons of secure socket tunneling virtual private network protocol which include security, internet speeds, and so on. Increase audience engagement and knowledge by dispensing information using Benefits Of Sstp Virtual Private Network Protocol. This template helps you present information on five stages. You can also present information on Internet Speed, Windows Integration, Firewall Bypass, Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
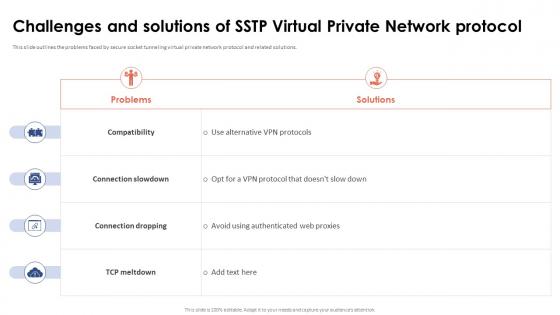 Challenges And Solutions Of Sstp Virtual Private Network Protocol
Challenges And Solutions Of Sstp Virtual Private Network ProtocolThis slide outlines the problems faced by secure socket tunneling virtual private network protocol and related solutions. Present the topic in a bit more detail with this Challenges And Solutions Of Sstp Virtual Private Network Protocol. Use it as a tool for discussion and navigation on Connection Slowdown, Connection Dropping, Virtual Private Network Protocol. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
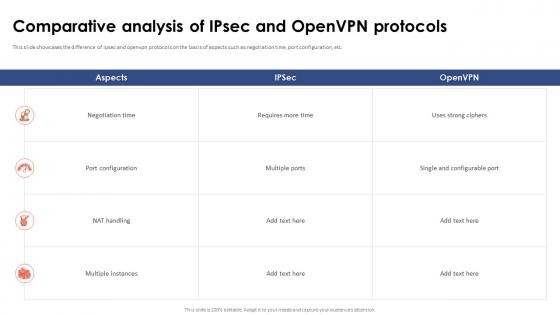 Comparative Analysis Of Ipsec And OpenVPN Protocols Virtual Private Network VPN
Comparative Analysis Of Ipsec And OpenVPN Protocols Virtual Private Network VPNThis slide showcases the difference of ipsec and openvpn protocols on the basis of aspects such as negotiation time, port configuration, etc. Present the topic in a bit more detail with this Comparative Analysis Of Ipsec And OpenVPN Protocols Virtual Private Network VPN. Use it as a tool for discussion and navigation on Comparative Analysis, Openvpn Protocols, Negotiation Time, Port Configuration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
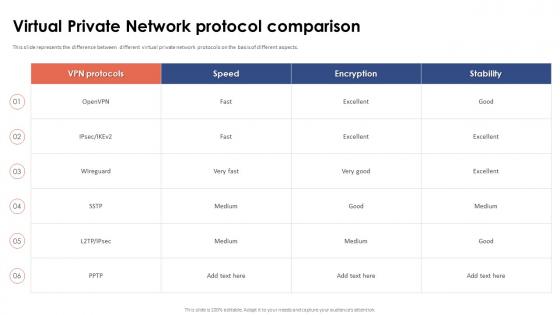 Virtual Private Network Protocol Comparison
Virtual Private Network Protocol ComparisonThis slide represents the difference between different virtual private network protocols on the basis of different aspects. Deliver an outstanding presentation on the topic using this Virtual Private Network Protocol Comparison. Dispense information and present a thorough explanation of Virtual Private Network, Protocol Comparison, Wireguard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
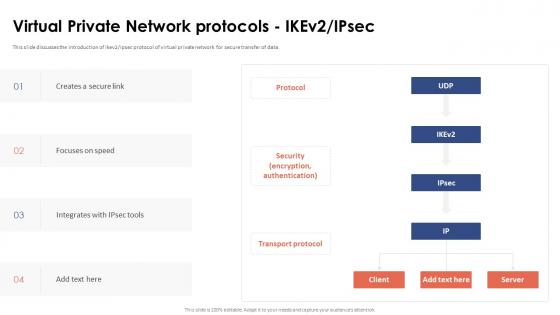 Virtual Private Network Protocols Ikev2 Ipsec
Virtual Private Network Protocols Ikev2 IpsecThis slide discusses the introduction of ikev2 or ipsec protocol of virtual private network for secure transfer of data. Present the topic in a bit more detail with this Virtual Private Network Protocols Ikev2 Ipsec. Use it as a tool for discussion and navigation on Protocol, Security, Encryption, Authentication, Transport Protocol. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
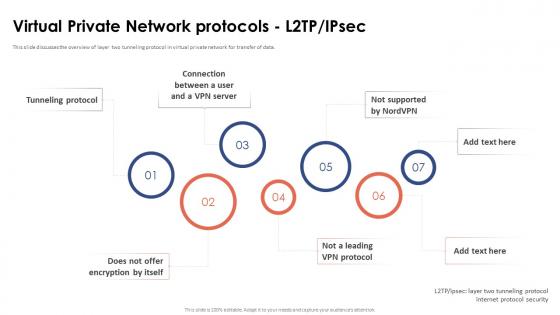 Virtual Private Network Protocols L2tp Ipsec
Virtual Private Network Protocols L2tp IpsecThis slide discusses the overview of layer two tunneling protocol in virtual private network for transfer of data. Increase audience engagement and knowledge by dispensing information using Virtual Private Network Protocols L2tp Ipsec. This template helps you present information on seven stages. You can also present information on Virtual Private, Network Protocols, Tunneling Protocol using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
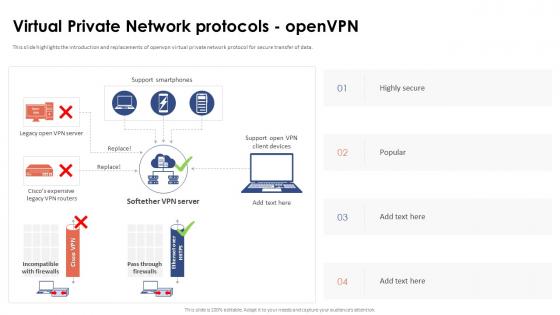 Virtual Private Network Protocols OpenVPN
Virtual Private Network Protocols OpenVPNThis slide highlights the introduction and replacements of openvpn virtual private network protocol for secure transfer of data. Deliver an outstanding presentation on the topic using this Virtual Private Network Protocols OpenVPN. Dispense information and present a thorough explanation of Replacements Of Openvpn, Virtual Private Network Protocol, Secure Transfer Of Data using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
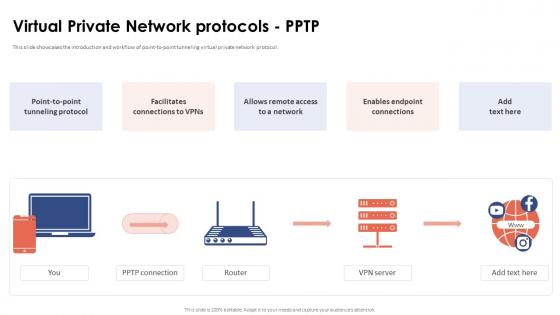 Virtual Private Network Protocols Pptp
Virtual Private Network Protocols PptpThis slide showcases the introduction and workflow of point-to-point tunneling virtual private network protocol. Introducing Virtual Private Network Protocols Pptp to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Facilitates Connections, Point To Point Tunneling Protocol, Remote Access To A Network, using this template. Grab it now to reap its full benefits.
-
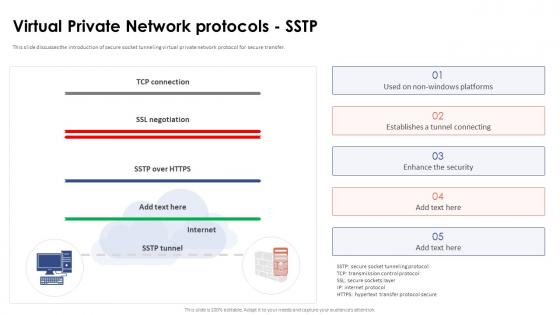 Virtual Private Network Protocols Sstp
Virtual Private Network Protocols SstpThis slide discusses the introduction of secure socket tunneling virtual private network protocol for secure transfer. Present the topic in a bit more detail with this Virtual Private Network Protocols Sstp. Use it as a tool for discussion and navigation on Facilitates Connections, Point To Point Tunneling Protocol, Remote Access To A Network. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
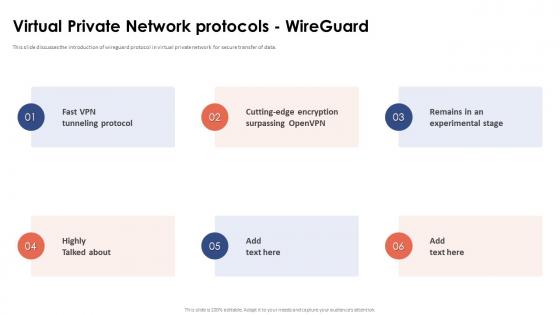 Virtual Private Network Protocols Wireguard
Virtual Private Network Protocols WireguardThis slide discusses the introduction of wireguard protocol in virtual private network for secure transfer of data. Increase audience engagement and knowledge by dispensing information using Virtual Private Network Protocols Wireguard. This template helps you present information on six stages. You can also present information on Tunneling Protocol, Cutting Edge Encryption, Experimental Stage, Virtual Private Network Protocols using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
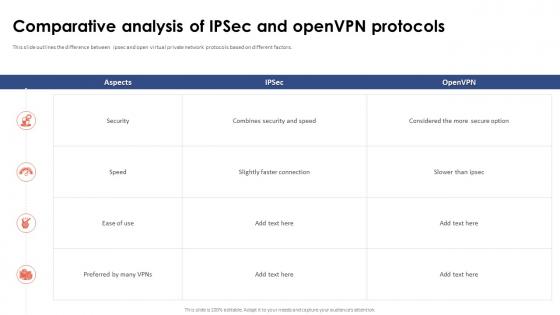 Virtual Private Network VPN Comparative Analysis Of Ipsec And OpenVPN Protocols
Virtual Private Network VPN Comparative Analysis Of Ipsec And OpenVPN ProtocolsThis slide outlines the difference between ipsec and open virtual private network protocols based on different factors. Present the topic in a bit more detail with this Virtual Private Network VPN Comparative Analysis Of Ipsec And OpenVPN Protocols. Use it as a tool for discussion and navigation on Virtual Private, Network Protocols, Comparative Analysis, Slightly Faster Connection. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
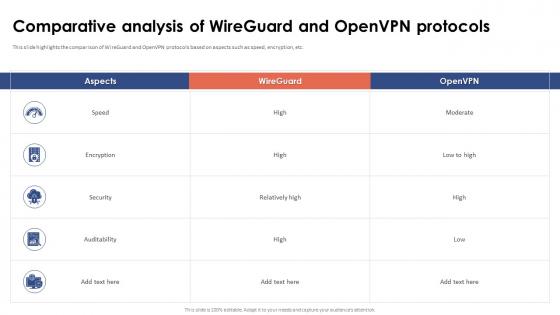 Virtual Private Network VPN Comparative Analysis Of Wireguard And OpenVPN Protocols
Virtual Private Network VPN Comparative Analysis Of Wireguard And OpenVPN ProtocolsThis slide highlights the comparison of WireGuard and OpenVPN protocols based on aspects such as speed, encryption, etc. Present the topic in a bit more detail with this Virtual Private Network VPN Comparative Analysis Of Wireguard And OpenVPN Protocols. Use it as a tool for discussion and navigation on Operational Environment, Supported Protocols, Network Simulation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
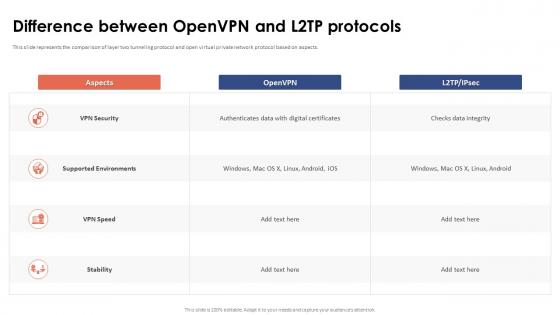 Virtual Private Network VPN Difference Between OpenVPN And L2tp Protocols
Virtual Private Network VPN Difference Between OpenVPN And L2tp ProtocolsThis slide represents the comparison of layer two tunneling protocol and open virtual private network protocol based on aspects. Present the topic in a bit more detail with this Virtual Private Network VPN Difference Between OpenVPN And L2tp Protocols. Use it as a tool for discussion and navigation on Supported Environments, Checks Data Integrity, Authenticates Data, Digital Certificates. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
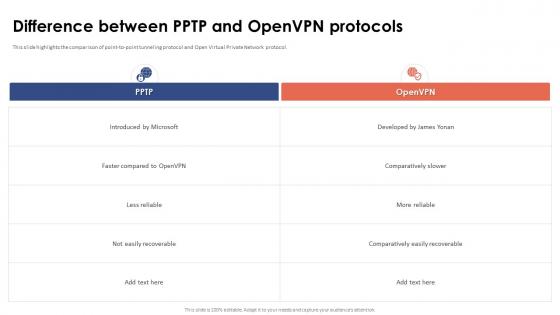 Virtual Private Network VPN Difference Between PPTP And OpenVPN Protocols
Virtual Private Network VPN Difference Between PPTP And OpenVPN ProtocolsThis slide highlights the comparison of point-to-point tunneling protocol and Open Virtual Private Network protocol. Deliver an outstanding presentation on the topic using this Virtual Private Network VPN Difference Between PPTP And OpenVPN Protocols. Dispense information and present a thorough explanation of Point To Point Tunneling Protocol, Open Virtual Private, Network Protocol using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.



